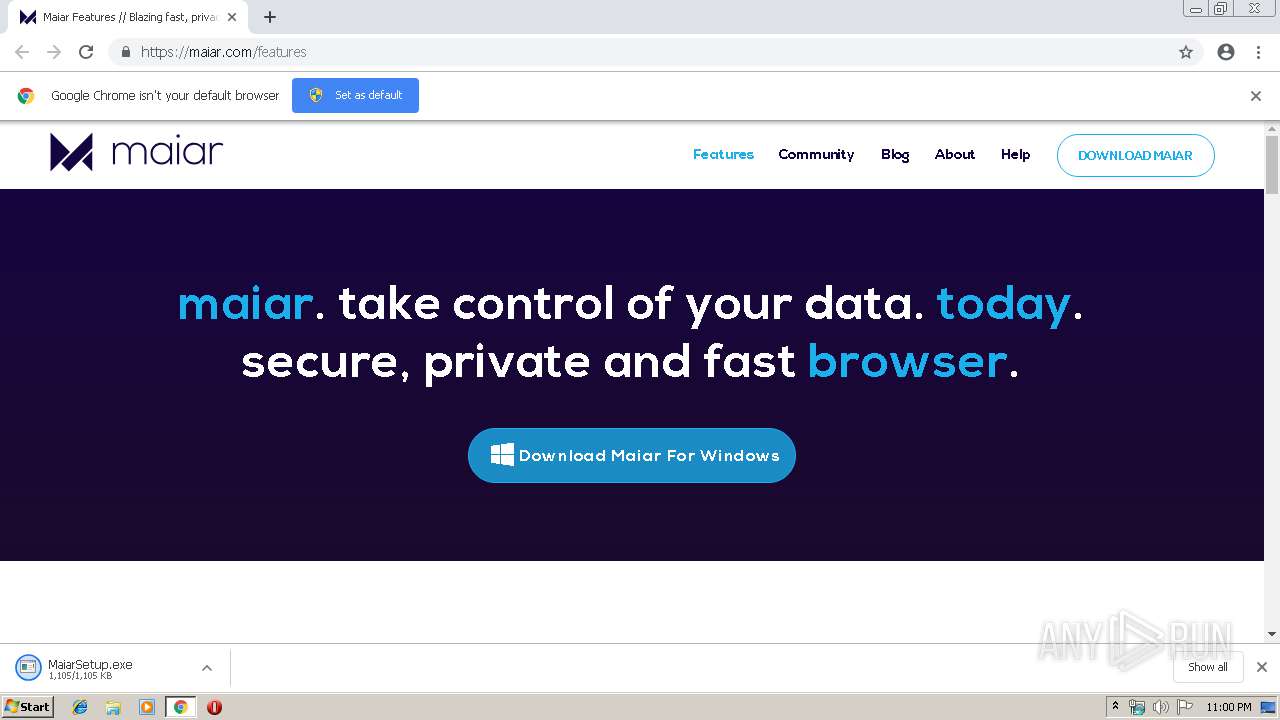
| URL: | https://maiar.com/features |
| Full analysis: | https://app.any.run/tasks/491e9c33-b689-422f-91eb-bd2bbcb815fd |
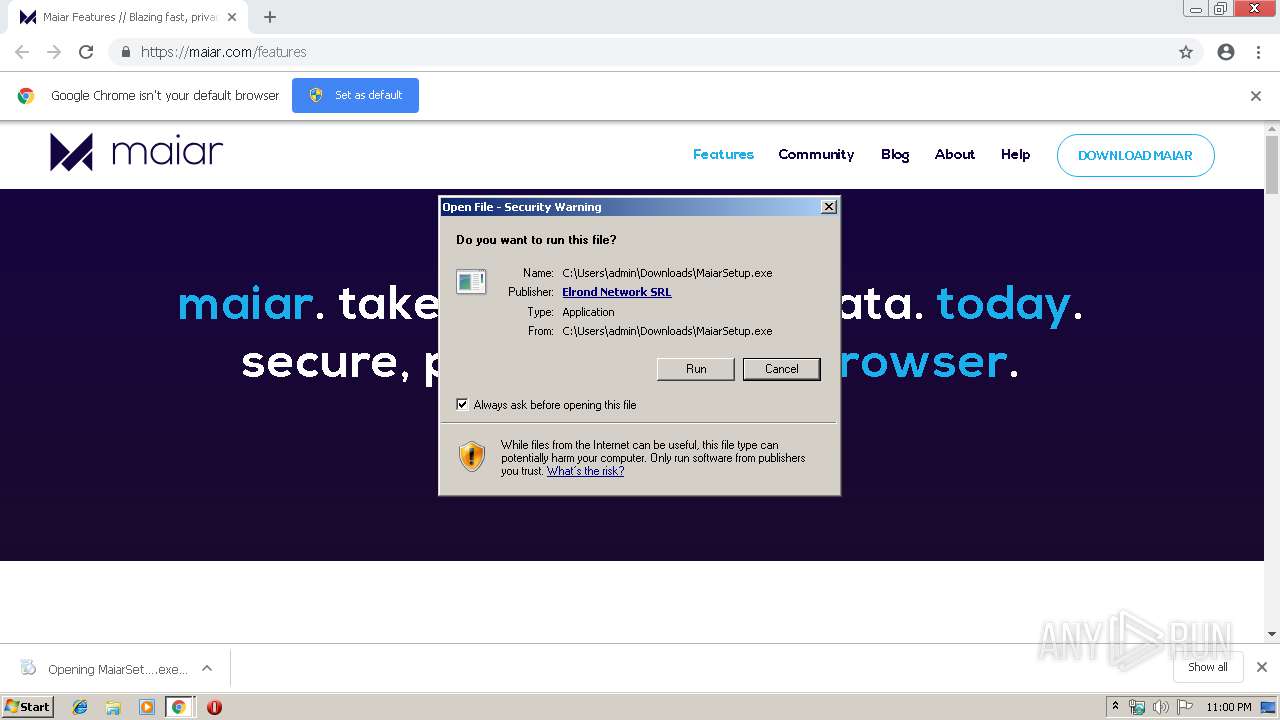
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2019, 22:00:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F020E980BDBD15CF0603F89D96CAF734 |
| SHA1: | 3B81F5E63FCCEACE452DA975B2282BD338643577 |
| SHA256: | 9F07A85E48AD19DDFEBF645A03814A5134A4014B1988E5ED1746C5956A31CD65 |
| SSDEEP: | 3:N802CAWn:20z |
MALICIOUS
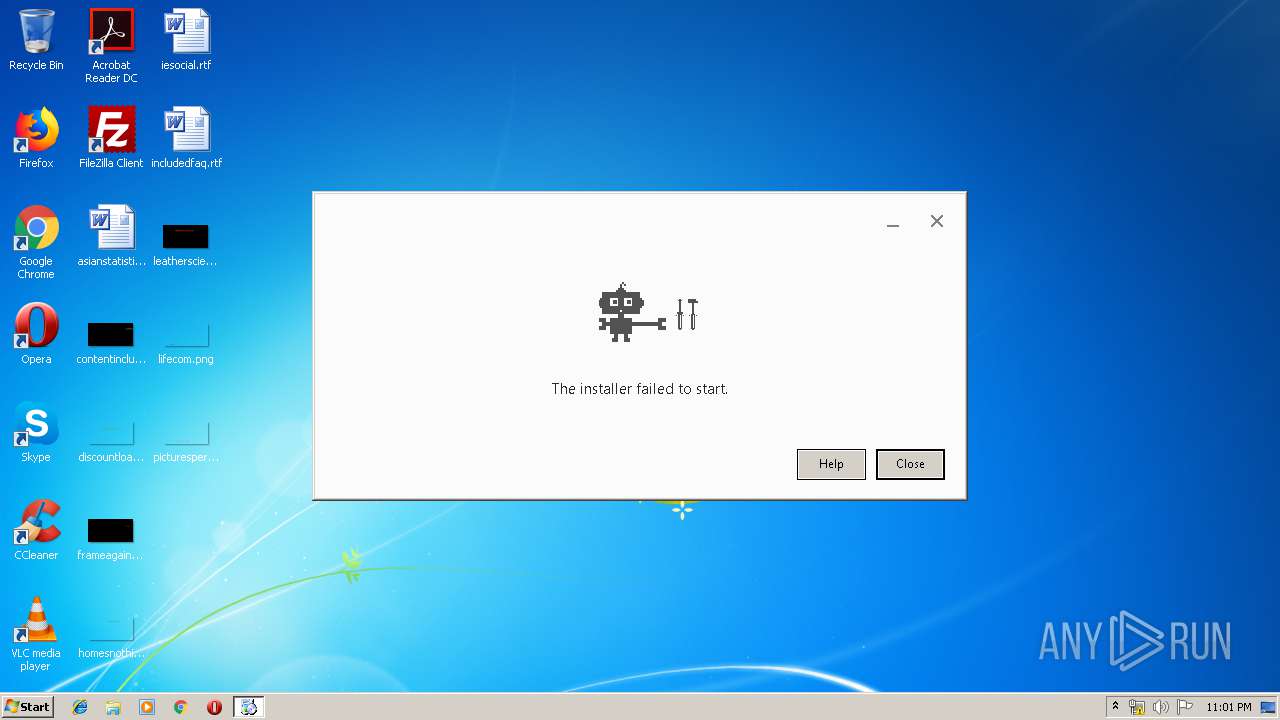
Application was dropped or rewritten from another process
- MaiarUpdate.exe (PID: 2564)
- MaiarSetup.exe (PID: 2908)
- MaiarUpdate.exe (PID: 2860)
- MaiarUpdateSetup.exe (PID: 3604)
- MaiarUpdate.exe (PID: 868)
- MaiarUpdate.exe (PID: 2244)
- MaiarUpdate.exe (PID: 2324)
- MaiarUpdate.exe (PID: 3360)
- MaiarUpdate.exe (PID: 2572)
- MaiarUpdate.exe (PID: 3240)
Loads dropped or rewritten executable
- MaiarUpdate.exe (PID: 2860)
- MaiarUpdate.exe (PID: 868)
- MaiarUpdate.exe (PID: 2244)
- MaiarUpdate.exe (PID: 2564)
- MaiarUpdate.exe (PID: 2324)
- MaiarUpdate.exe (PID: 2572)
- MaiarUpdate.exe (PID: 3360)
- MaiarUpdate.exe (PID: 3240)
Loads the Task Scheduler COM API
- MaiarUpdate.exe (PID: 868)
Changes settings of System certificates
- MaiarUpdate.exe (PID: 2244)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2956)
- chrome.exe (PID: 2096)
- MaiarSetup.exe (PID: 2908)
- MaiarUpdateSetup.exe (PID: 3604)
- MaiarUpdate.exe (PID: 868)
Creates files in the program directory
- MaiarUpdateSetup.exe (PID: 3604)
- MaiarUpdate.exe (PID: 868)
- MaiarUpdate.exe (PID: 2572)
Starts itself from another location
- MaiarUpdate.exe (PID: 868)
Disables SEHOP
- MaiarUpdate.exe (PID: 868)
Creates COM task schedule object
- MaiarUpdate.exe (PID: 2564)
- MaiarUpdate.exe (PID: 868)
Adds / modifies Windows certificates
- MaiarUpdate.exe (PID: 2244)
Application launched itself
- MaiarUpdate.exe (PID: 2572)
INFO
Application launched itself
- chrome.exe (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
24
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | "C:\Program Files\GUM4E23.tmp\MaiarUpdate.exe" /installsource taggedmi /install "appguid={AFE6A462-C574-4B8A-AF43-4CC60DF4563B}&appname=Maiar&needsadmin=prefers&lang=en&usagestats=1" /installelevated | C:\Program Files\GUM4E23.tmp\MaiarUpdate.exe | MaiarUpdateSetup.exe | ||||||||||||
User: admin Company: Elrond Ltd. Integrity Level: HIGH Description: Elrond Update Exit code: 2147748097 Version: 1.3.97.0 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6538527062471319232 --mojo-platform-channel-handle=1504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Elrond\Update\MaiarUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB2ZXJzaW9uPSIxLjMuOTcuMCIgc2hlbGxfdmVyc2lvbj0iMS4zLjk3LjAiIGlzbWFjaGluZT0iMSIgc2Vzc2lvbmlkPSJ7N0E4NUQ2RUQtOThFQi00MTNGLUIyQUUtRTA2RUJEQjgzRkNFfSIgdXNlcmlkPSJ7QzhENDI3REItOEUwNi00NEJCLUEyRkEtNjNEMDY0MzM0Njk5fSIgaW5zdGFsbHNvdXJjZT0idGFnZ2VkbWkiIHRlc3Rzb3VyY2U9ImF1dG8iIHJlcXVlc3RpZD0ie0RDNjcyRjkwLUQxNUUtNDI5NC05QkYwLTREMDRDMTVBQjZFMX0iIGRlZHVwPSJjciI-PGh3IHBoeXNtZW1vcnk9IjMiIHNzZT0iMSIgc3NlMj0iMSIgc3NlMz0iMSIgc3NzZTM9IjEiIHNzZTQxPSIxIiBzc2U0Mj0iMSIgYXZ4PSIxIi8-PG9zIHBsYXRmb3JtPSJ3aW4iIHZlcnNpb249IjYuMS43NjAxLjAiIHNwPSJTZXJ2aWNlIFBhY2sgMSIgYXJjaD0ieDg2Ii8-PGFwcCBhcHBpZD0ie0IxMzFDOTM1LTlCRTYtNDFEQS05NTk5LTFGNzc2QkVCODAxOX0iIHZlcnNpb249IiIgbmV4dHZlcnNpb249IjEuMy45Ny4wIiBsYW5nPSJlbiIgYnJhbmQ9IiIgY2xpZW50PSIiPjxldmVudCBldmVudHR5cGU9IjIiIGV2ZW50cmVzdWx0PSIxIiBlcnJvcmNvZGU9IjAiIGV4dHJhY29kZTE9IjAiIGluc3RhbGxfdGltZV9tcz0iMTQ2OSIvPjwvYXBwPjwvcmVxdWVzdD4 | C:\Program Files\Elrond\Update\MaiarUpdate.exe | MaiarUpdate.exe | ||||||||||||
User: admin Company: Elrond Ltd. Integrity Level: HIGH Description: Elrond Update Exit code: 0 Version: 1.3.97.0 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12005571563935577244 --mojo-platform-channel-handle=3172 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Elrond\Update\MaiarUpdate.exe" /handoff "appguid={AFE6A462-C574-4B8A-AF43-4CC60DF4563B}&appname=Maiar&needsadmin=prefers&lang=en&usagestats=1" /installsource taggedmi /sessionid "{7A85D6ED-98EB-413F-B2AE-E06EBDB83FCE}" | C:\Program Files\Elrond\Update\MaiarUpdate.exe | — | MaiarUpdate.exe | |||||||||||
User: admin Company: Elrond Ltd. Integrity Level: HIGH Description: Elrond Update Exit code: 2147748097 Version: 1.3.97.0 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --service-pipe-token=14929232735656079842 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14929232735656079842 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1960 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Elrond\Update\MaiarUpdate.exe" /regserver | C:\Program Files\Elrond\Update\MaiarUpdate.exe | — | MaiarUpdate.exe | |||||||||||
User: admin Company: Elrond Ltd. Integrity Level: HIGH Description: Elrond Update Exit code: 0 Version: 1.3.97.0 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Elrond\Update\MaiarUpdate.exe" /svc | C:\Program Files\Elrond\Update\MaiarUpdate.exe | services.exe | ||||||||||||
User: SYSTEM Company: Elrond Ltd. Integrity Level: SYSTEM Description: Elrond Update Exit code: 0 Version: 1.3.97.0 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2960 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7807277494032003276 --mojo-platform-channel-handle=4404 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 763
Read events
1 021
Write events
1 721
Delete events
21
Modification events
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2956-13199752824782000 |
Value: 259 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2956) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
218
Suspicious files
45
Text files
129
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\05e144ed-8856-4285-a5f6-714c88e4f1da.tmp | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
29
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2096 | chrome.exe | GET | 200 | 194.9.24.113:80 | http://r6---sn-5uh5o-f5fd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.217.54&mm=28&mn=sn-5uh5o-f5fd&ms=nvh&mt=1555279173&mv=m&pl=21&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
2096 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 507 b | whitelisted |
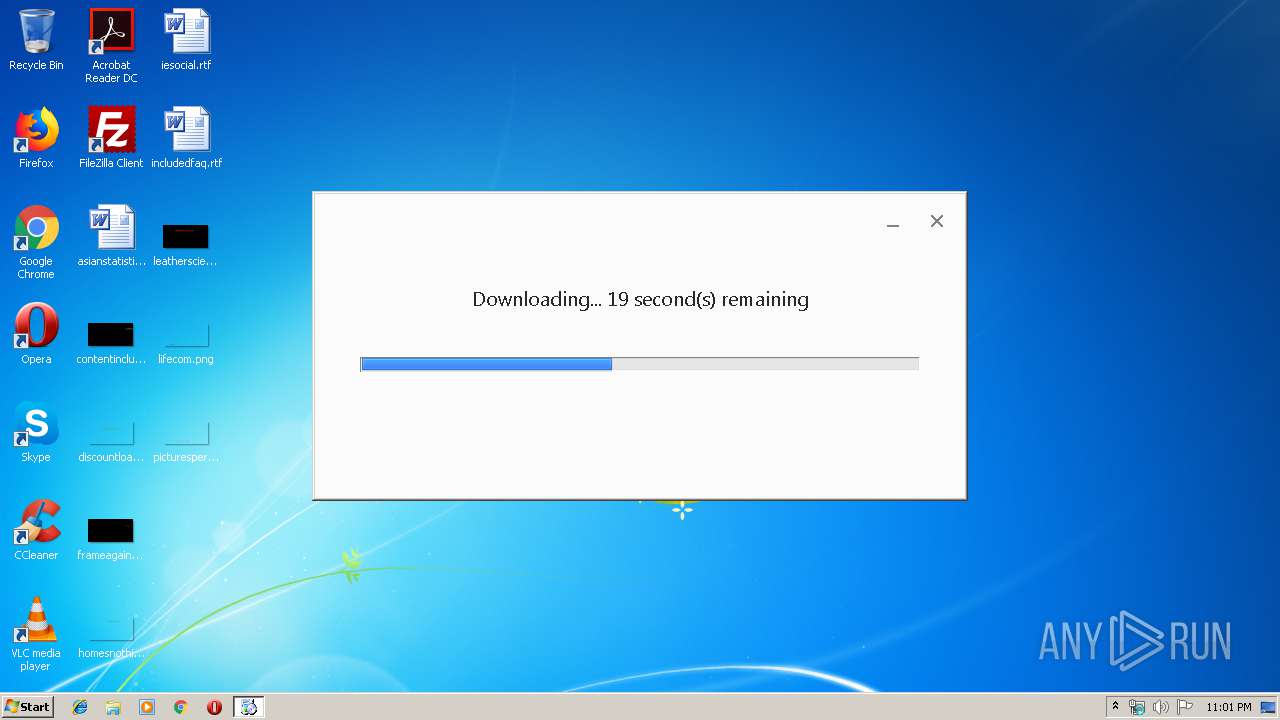
— | — | HEAD | 200 | 52.222.162.11:80 | http://downloads.maiar.com/static/media/build/Maiar/stable/win/79164841066596/72.0.59.100.exe | US | — | — | malicious |
— | — | GET | 200 | 52.222.162.11:80 | http://downloads.maiar.com/static/media/build/Maiar/stable/win/79164841066596/72.0.59.100.exe | US | executable | 57.8 Mb | malicious |
2096 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
2096 | chrome.exe | GET | 200 | 52.222.168.106:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2096 | chrome.exe | 172.217.16.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 172.217.23.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 52.222.168.106:80 | x.ss2.us | Amazon.com, Inc. | US | suspicious |
2096 | chrome.exe | 52.222.162.70:443 | downloads.maiar.com | Amazon.com, Inc. | US | unknown |
— | — | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2244 | MaiarUpdate.exe | 52.29.248.124:443 | updates.maiar.com | Amazon.com, Inc. | DE | unknown |
2096 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 194.9.24.113:80 | r6---sn-5uh5o-f5fd.gvt1.com | ATM S.A. | PL | whitelisted |
2572 | MaiarUpdate.exe | 52.29.248.124:443 | updates.maiar.com | Amazon.com, Inc. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
maiar.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |