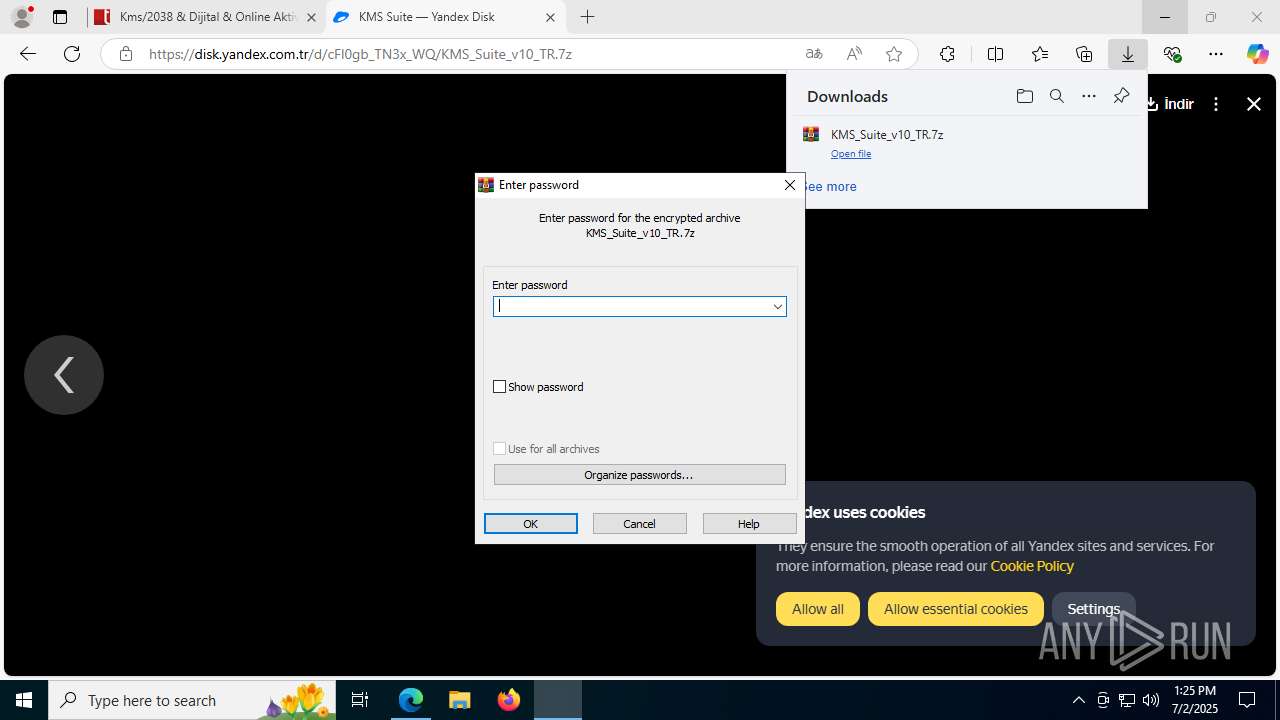
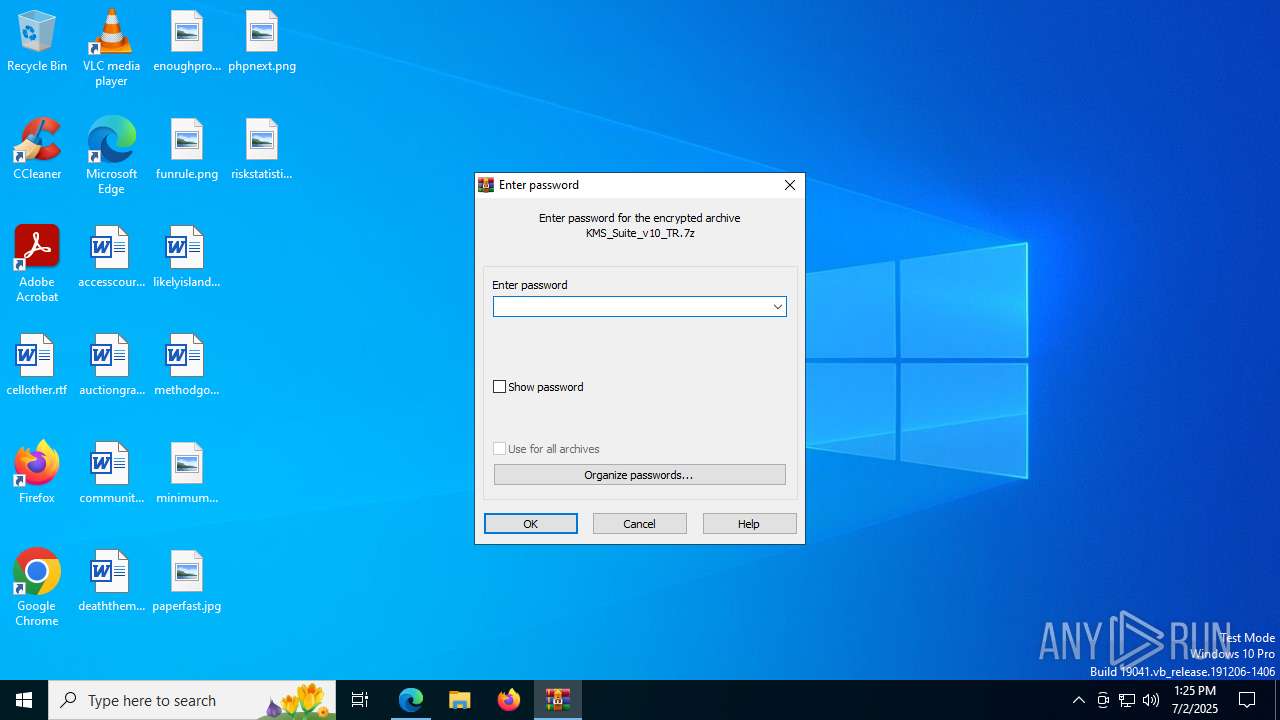
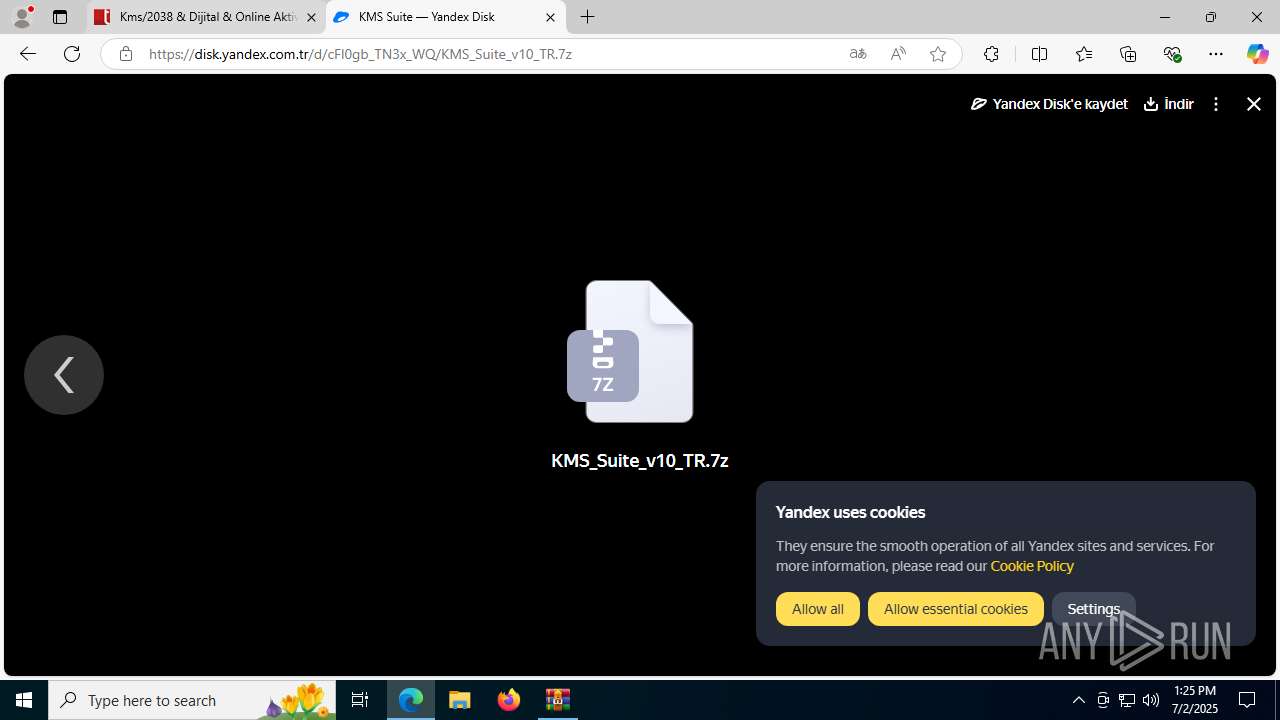
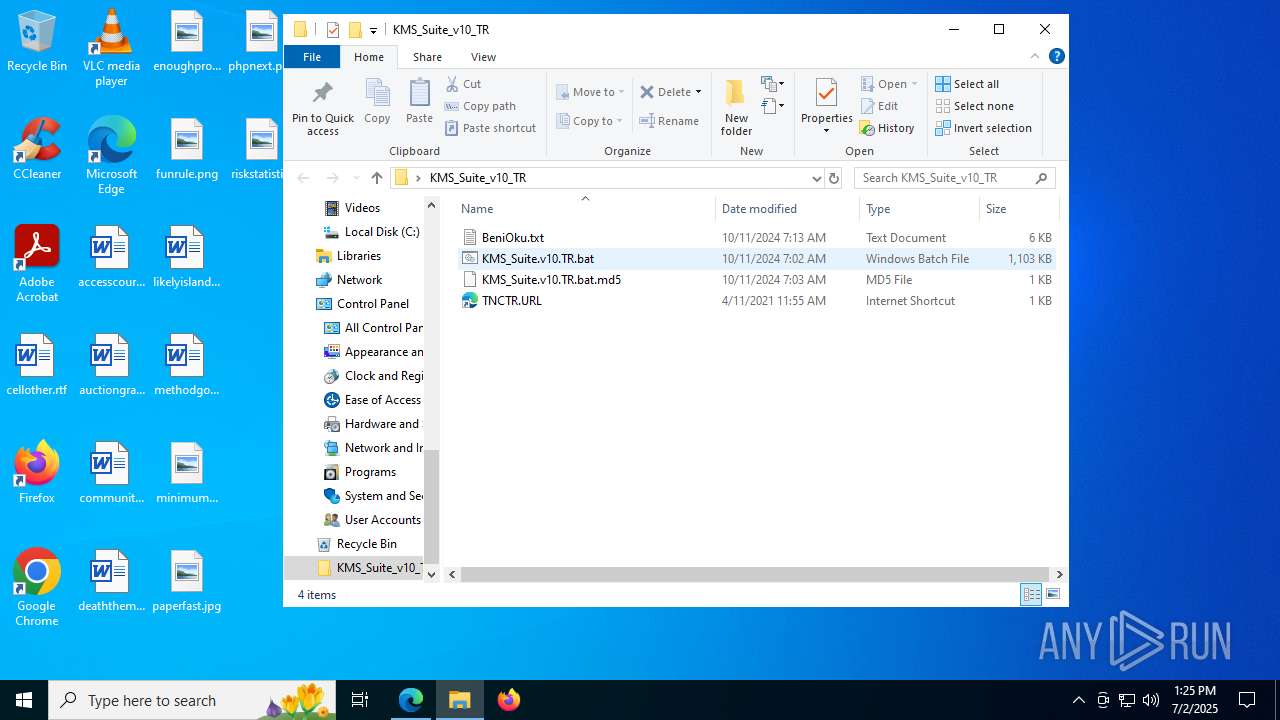
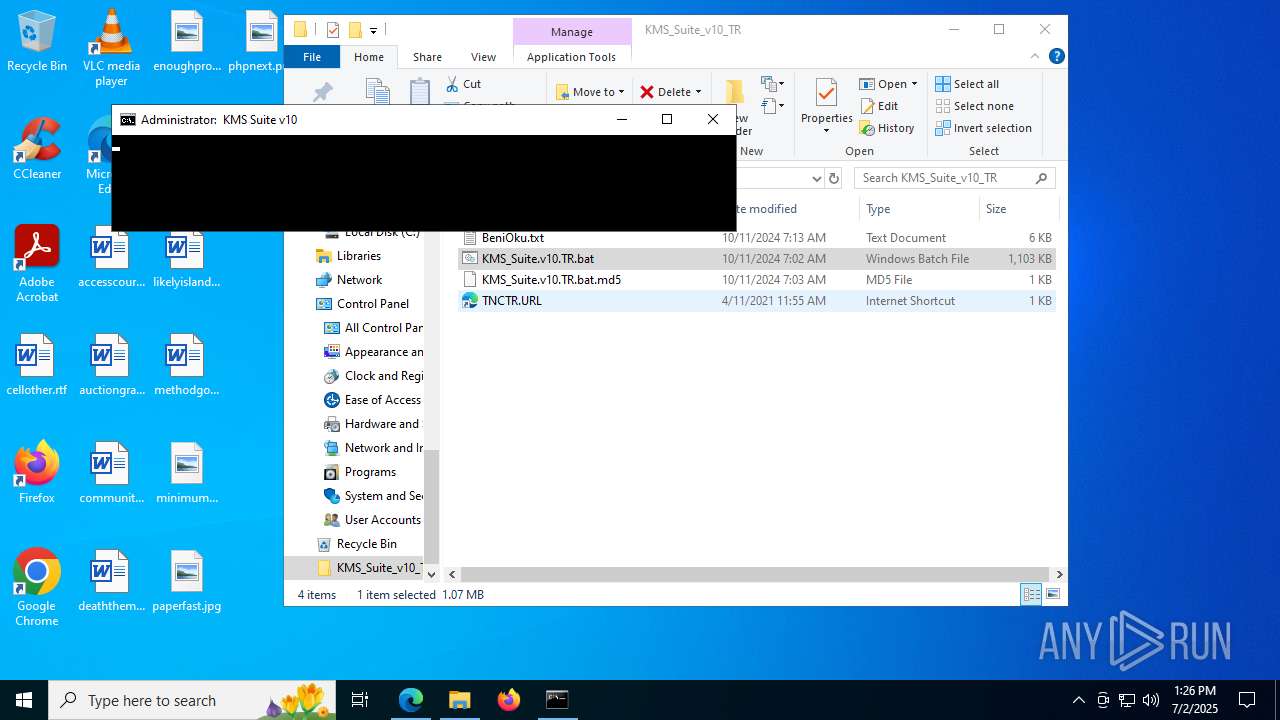
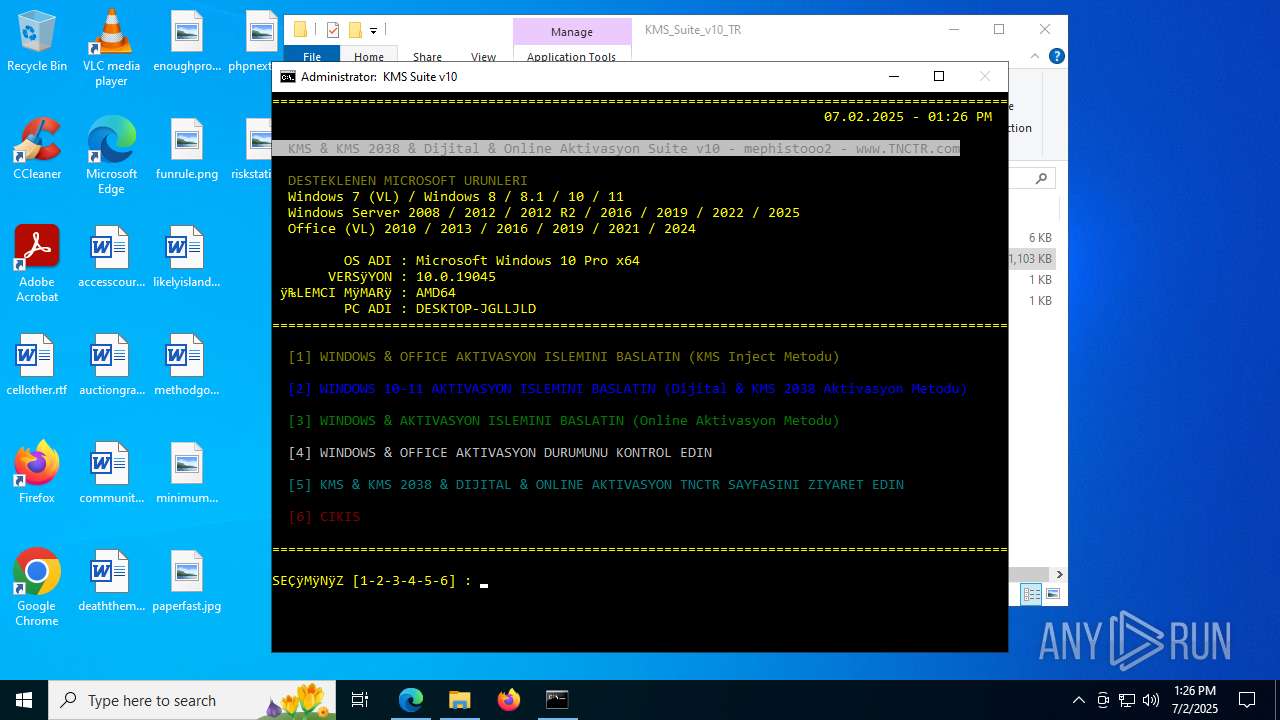
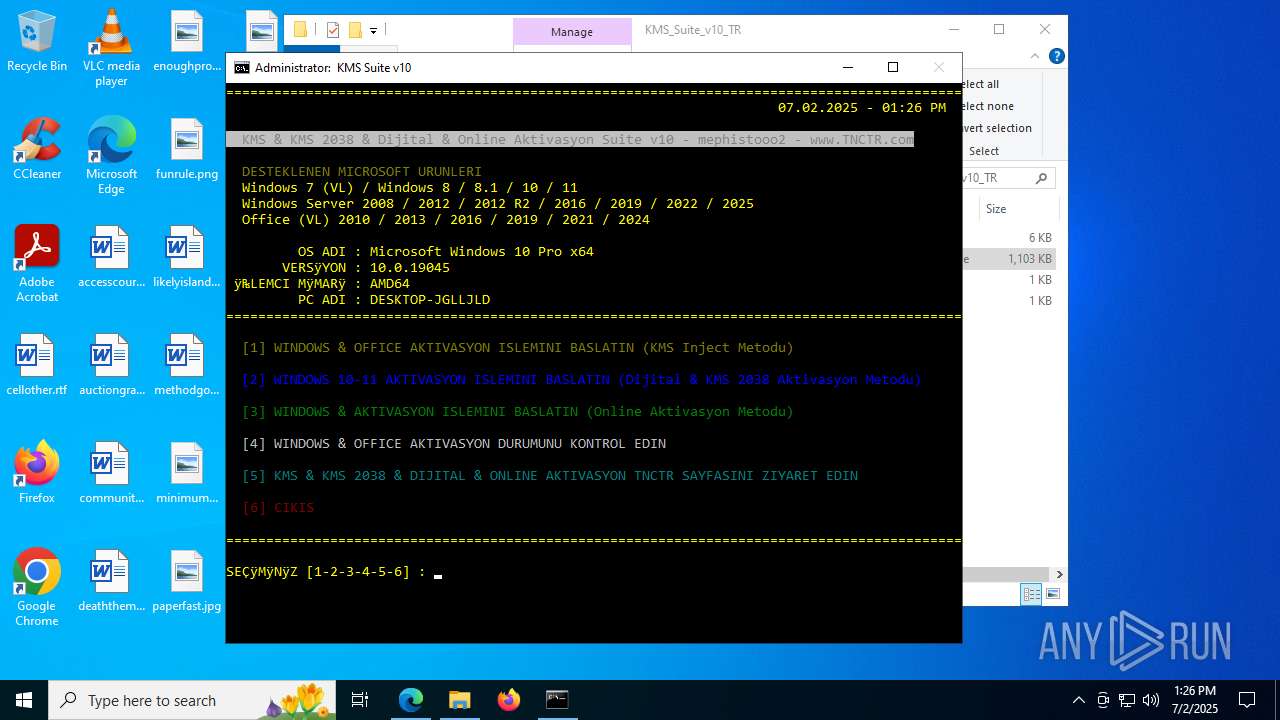
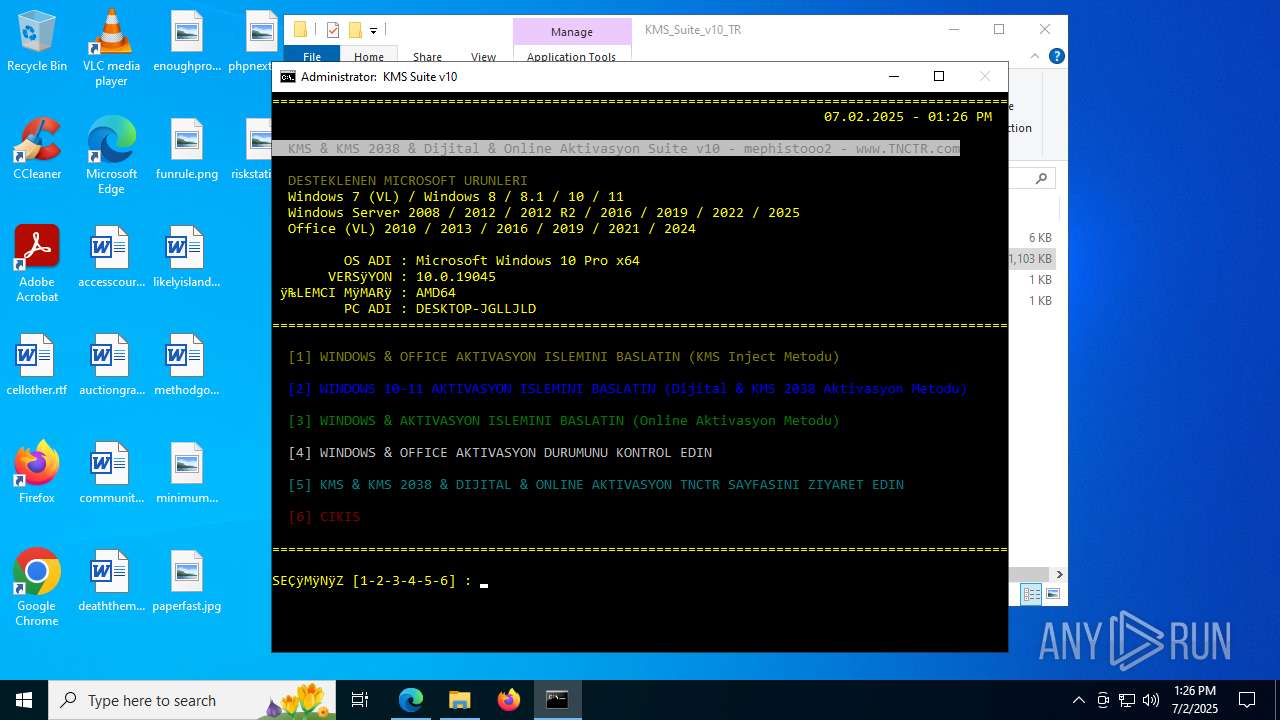
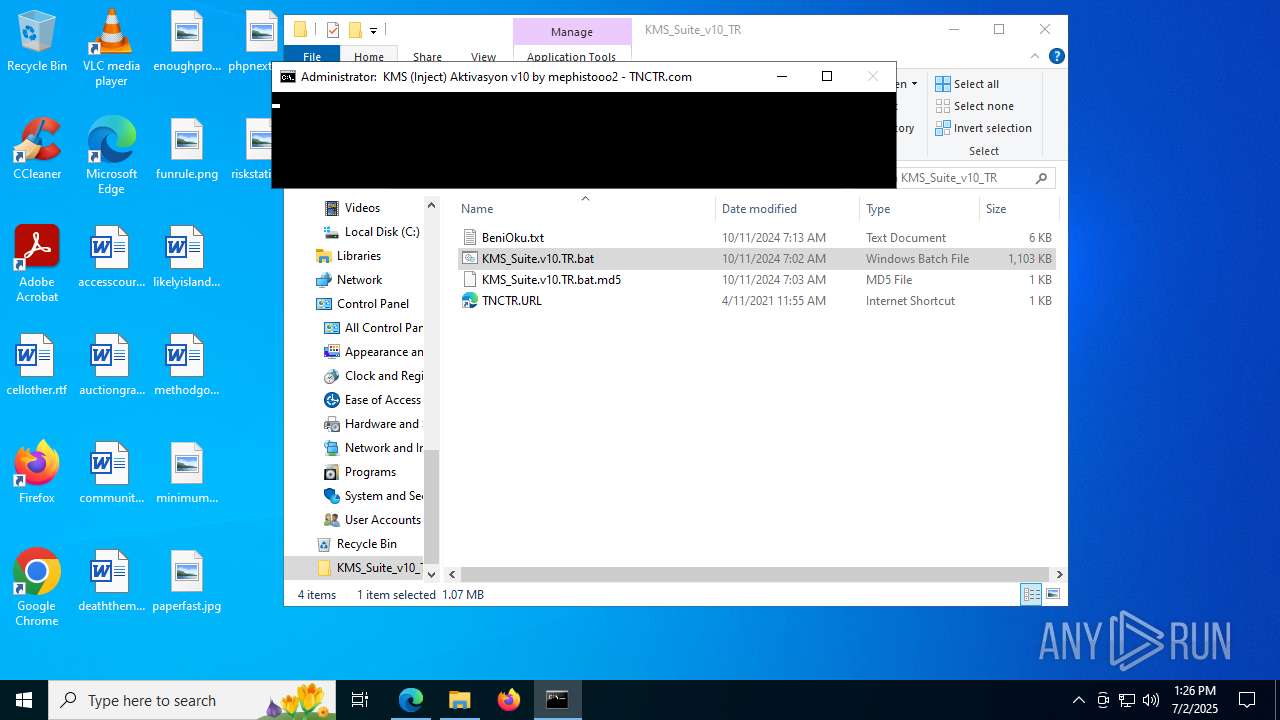
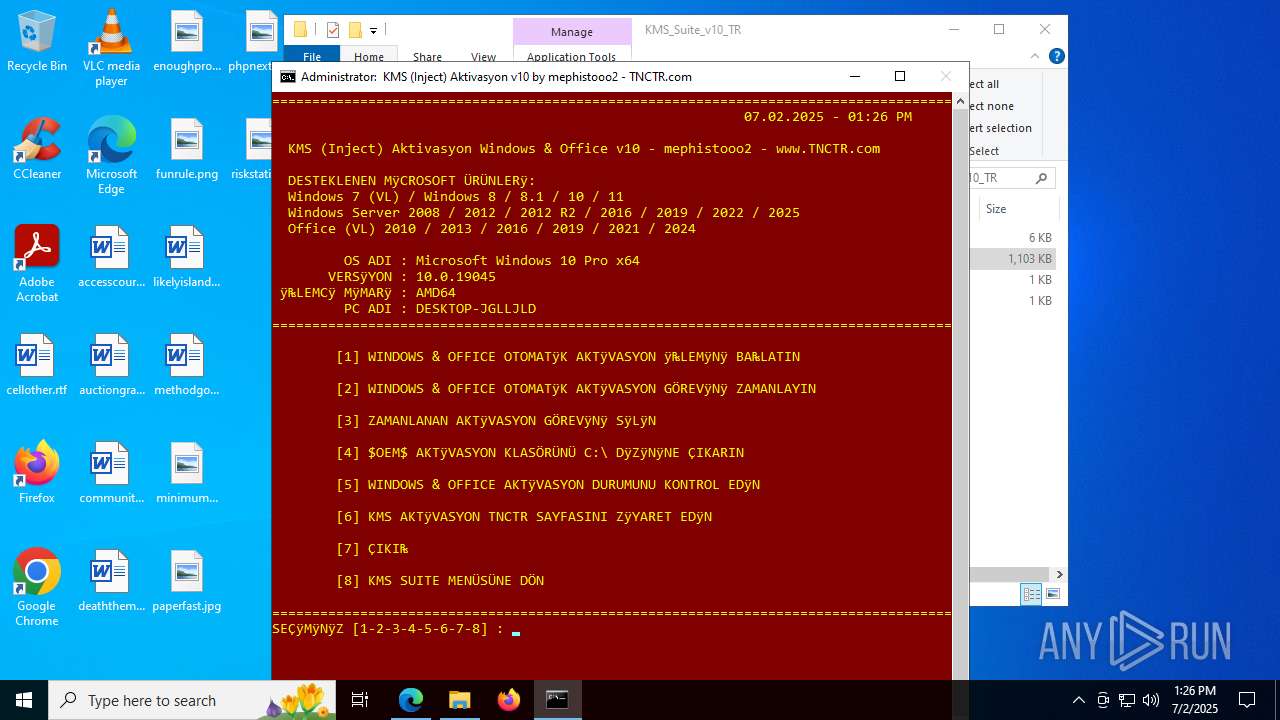
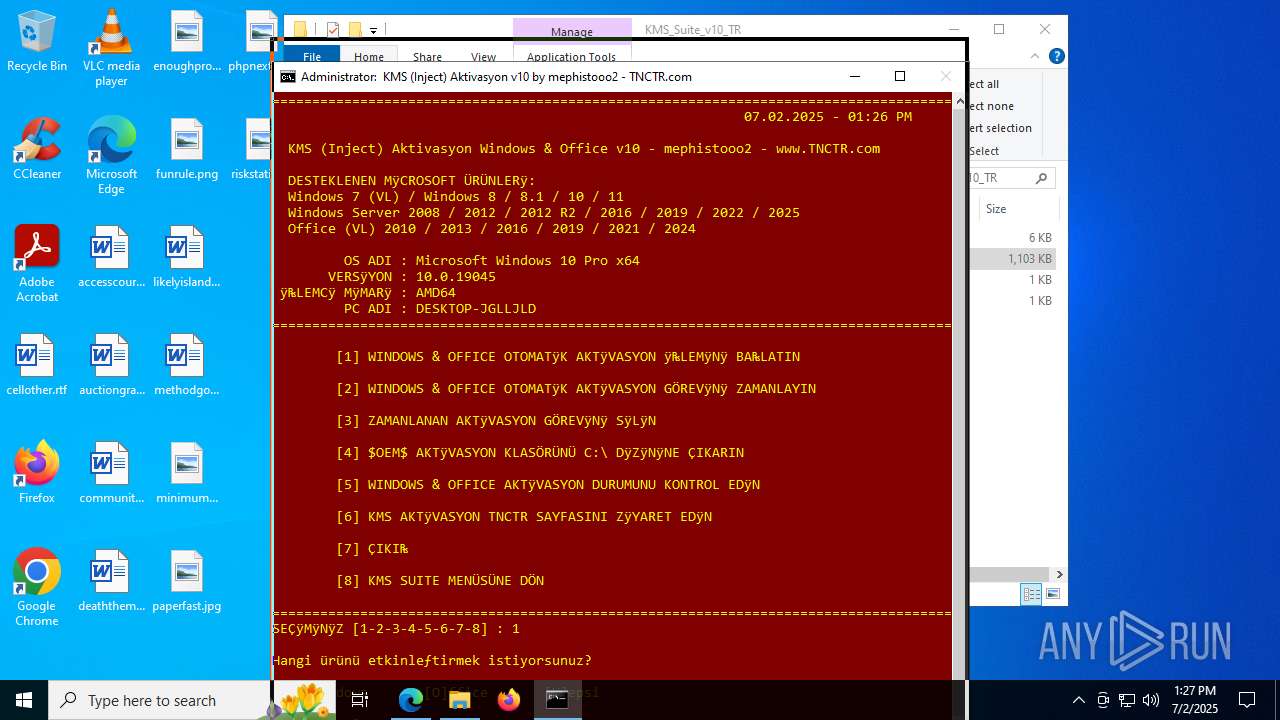
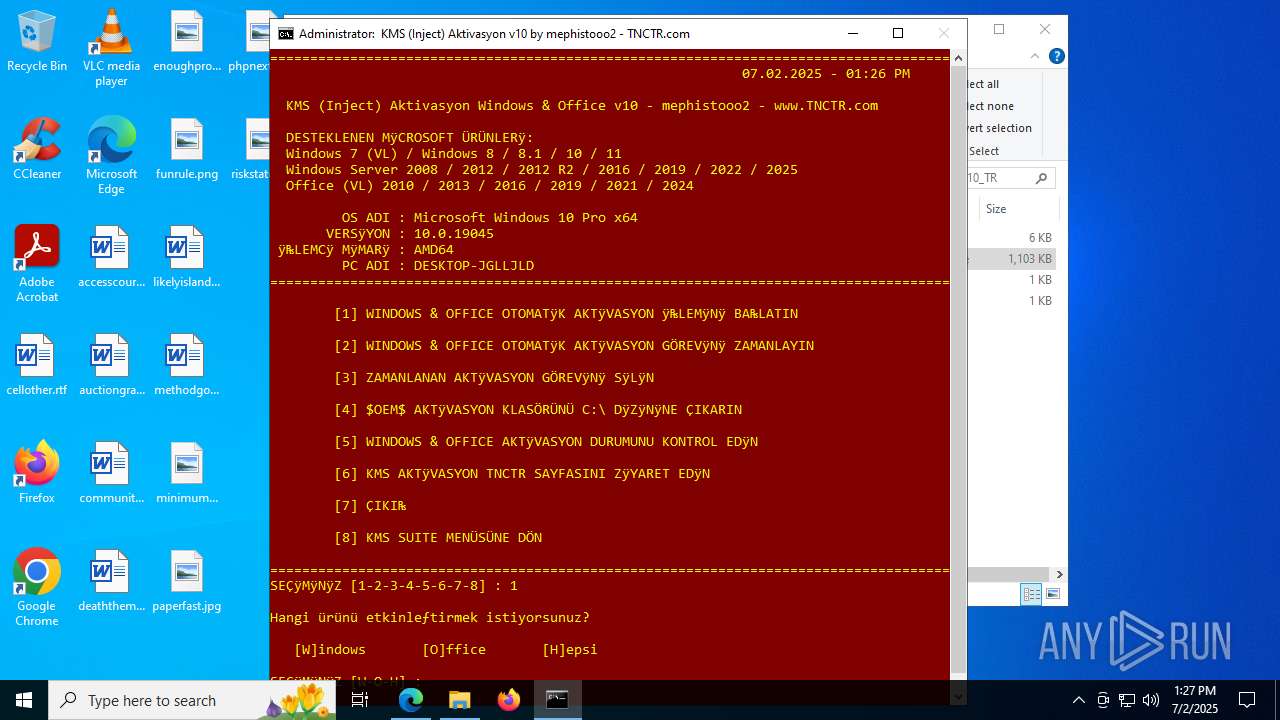
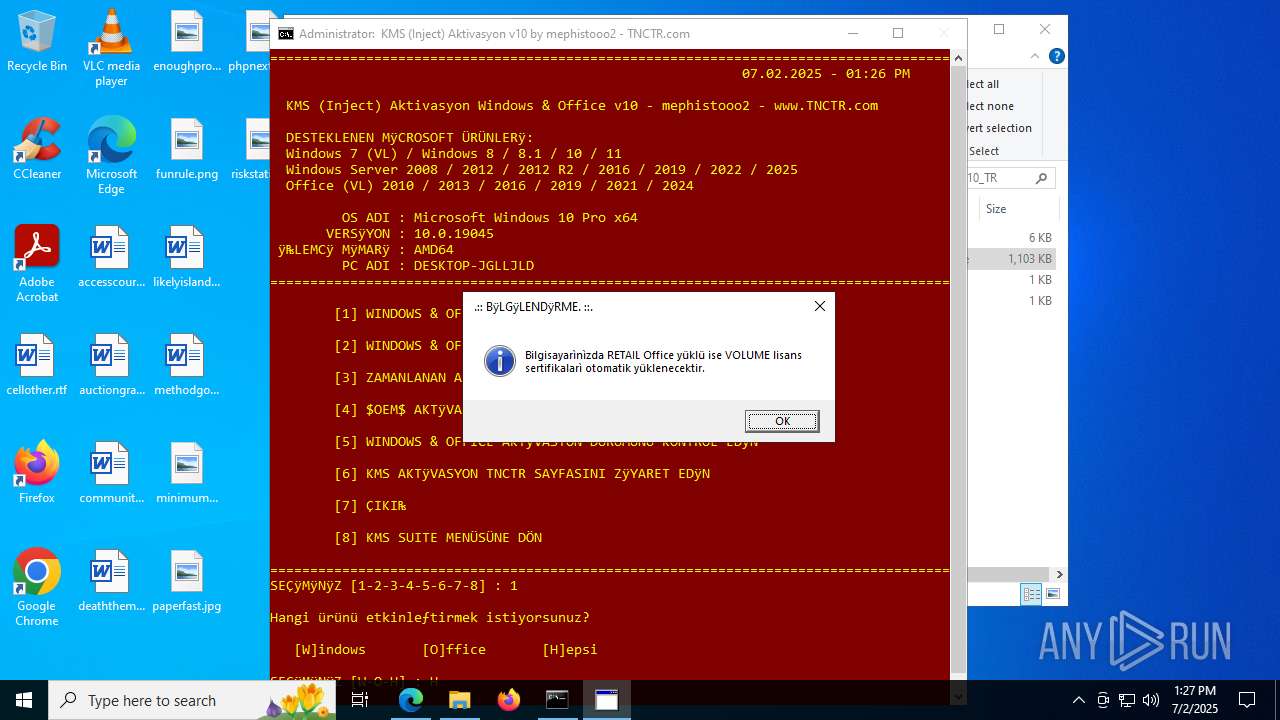
| URL: | https://www.tnctr.com/topic/450916-kms2038-dijital-online-aktivasyon-suite-v64/ |
| Full analysis: | https://app.any.run/tasks/05a9df63-b1c3-488c-bf70-027f1de31c79 |
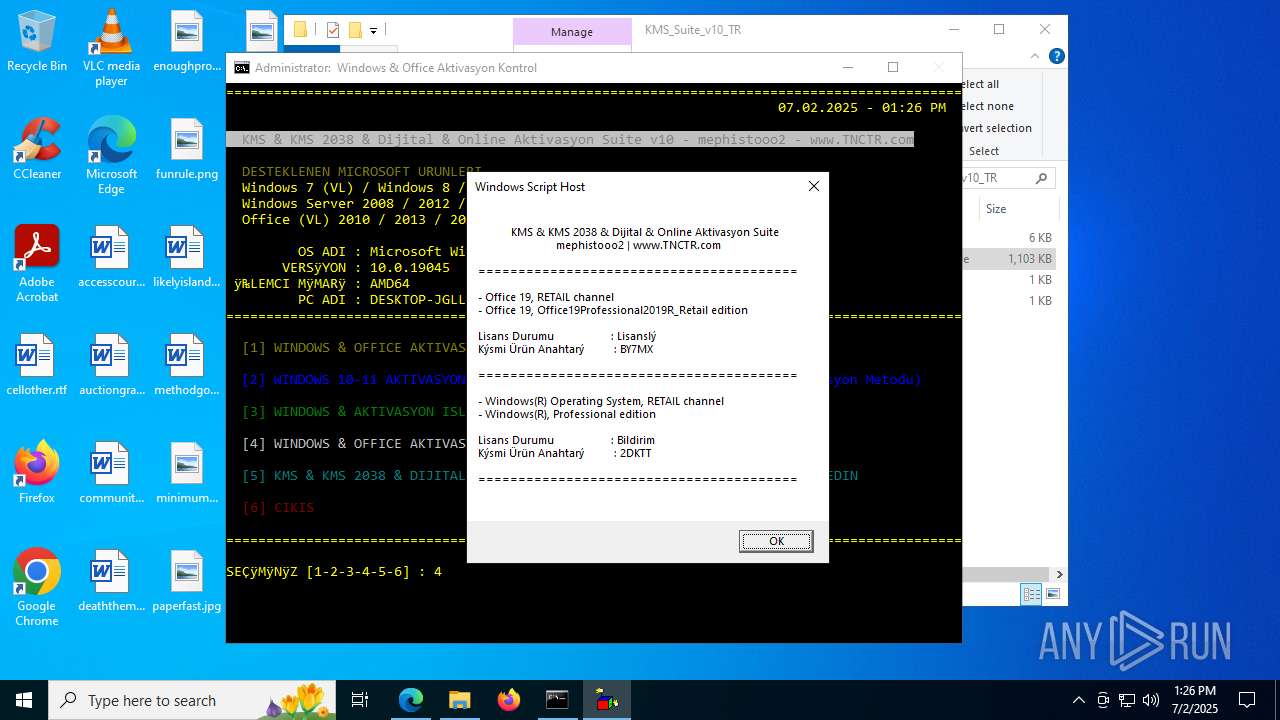
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2025, 13:24:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
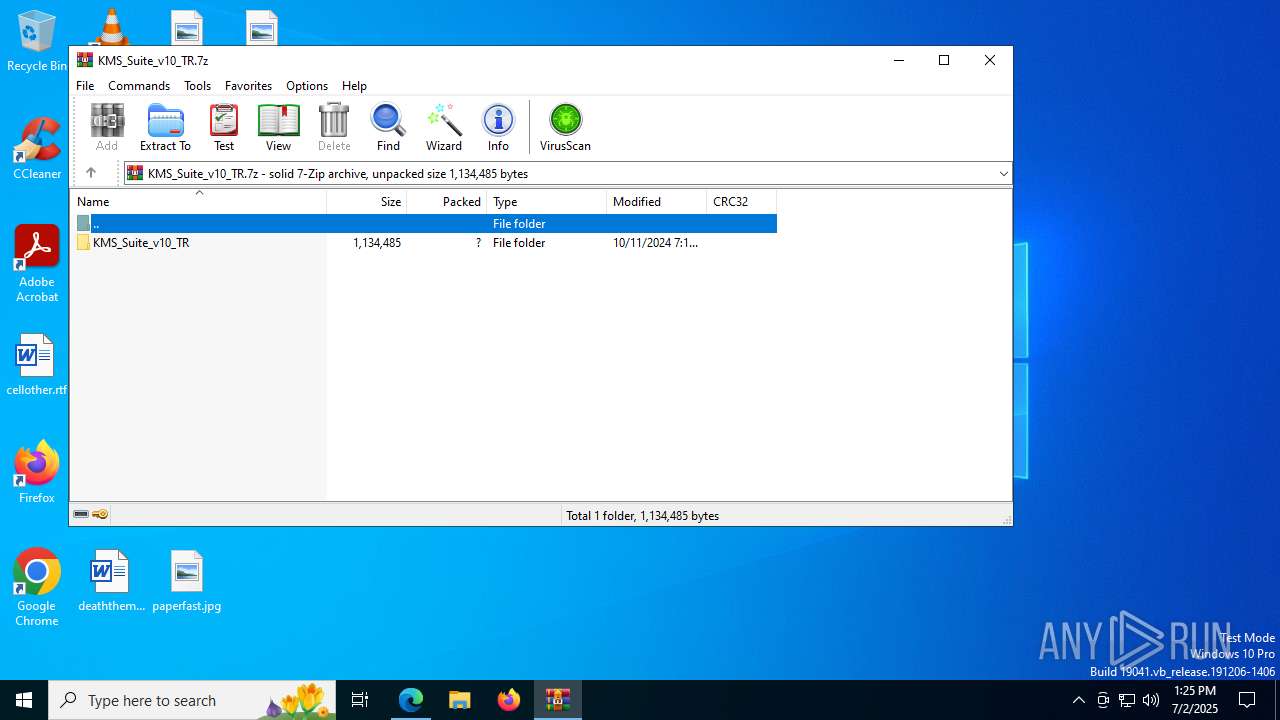
| MD5: | 4848D12284F7B43507ED64EC65CCFBE8 |
| SHA1: | CFA2607860AA4D522717AD34F5BFE0C81E9C591A |
| SHA256: | 9EFE72C14FC882468109DDCFA54B8DDBD63531F99B96E521B6429DA6B93AD8E5 |
| SSDEEP: | 3:N8DSLomQQX8vRJ39lzTEEx5K:2OLZQBvRJPTvK |
MALICIOUS
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4916)
Changes Windows Defender settings
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4916)
Changes powershell execution policy (RemoteSigned)
- cmd.exe (PID: 4916)
Starts NET.EXE for service management
- net.exe (PID: 6940)
- cmd.exe (PID: 4916)
- net.exe (PID: 2764)
- net.exe (PID: 1580)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4916)
SUSPICIOUS
The process executes via Task Scheduler
- updater.exe (PID: 7540)
Application launched itself
- updater.exe (PID: 7540)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4916)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4916)
- mshta.exe (PID: 1984)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4916)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4916)
- cmd.exe (PID: 4864)
- cmd.exe (PID: 7520)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 480)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 504)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4916)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4916)
Executes script without checking the security policy
- powershell.exe (PID: 1852)
- powershell.exe (PID: 952)
- powershell.exe (PID: 7700)
- powershell.exe (PID: 7552)
- powershell.exe (PID: 7680)
- powershell.exe (PID: 3836)
- powershell.exe (PID: 2272)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 5652)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 8184)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 8076)
- powershell.exe (PID: 1828)
- powershell.exe (PID: 6308)
Manipulates environment variables
- powershell.exe (PID: 1852)
- powershell.exe (PID: 7700)
- powershell.exe (PID: 5652)
CSC.EXE is used to compile C# code
- csc.exe (PID: 2468)
- csc.exe (PID: 3756)
- csc.exe (PID: 7952)
- csc.exe (PID: 7676)
- csc.exe (PID: 7712)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4916)
- cmd.exe (PID: 7520)
- cmd.exe (PID: 4864)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 480)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 504)
- cmd.exe (PID: 8004)
Executable content was dropped or overwritten
- csc.exe (PID: 2468)
- expand.exe (PID: 768)
- csc.exe (PID: 3756)
- csc.exe (PID: 7952)
- csc.exe (PID: 7676)
- csc.exe (PID: 7712)
- xcopy.exe (PID: 5960)
Unpacks CAB file
- expand.exe (PID: 768)
- expand.exe (PID: 8056)
- expand.exe (PID: 3756)
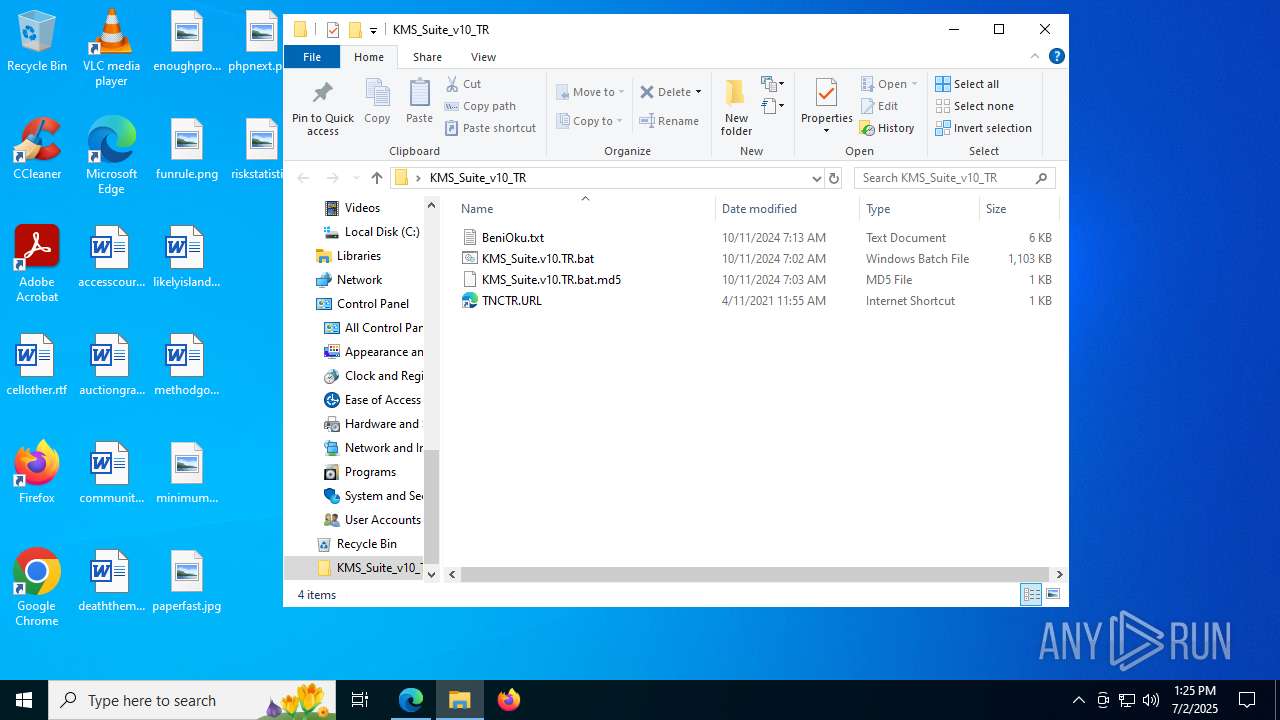
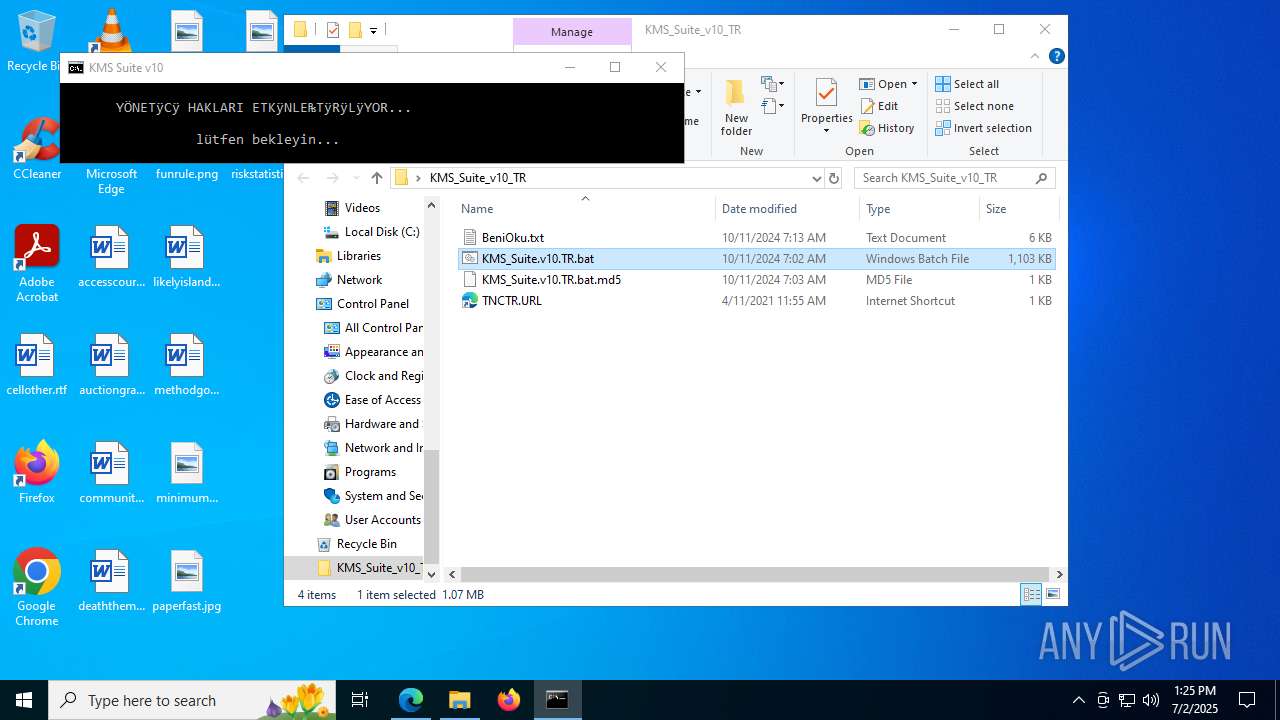
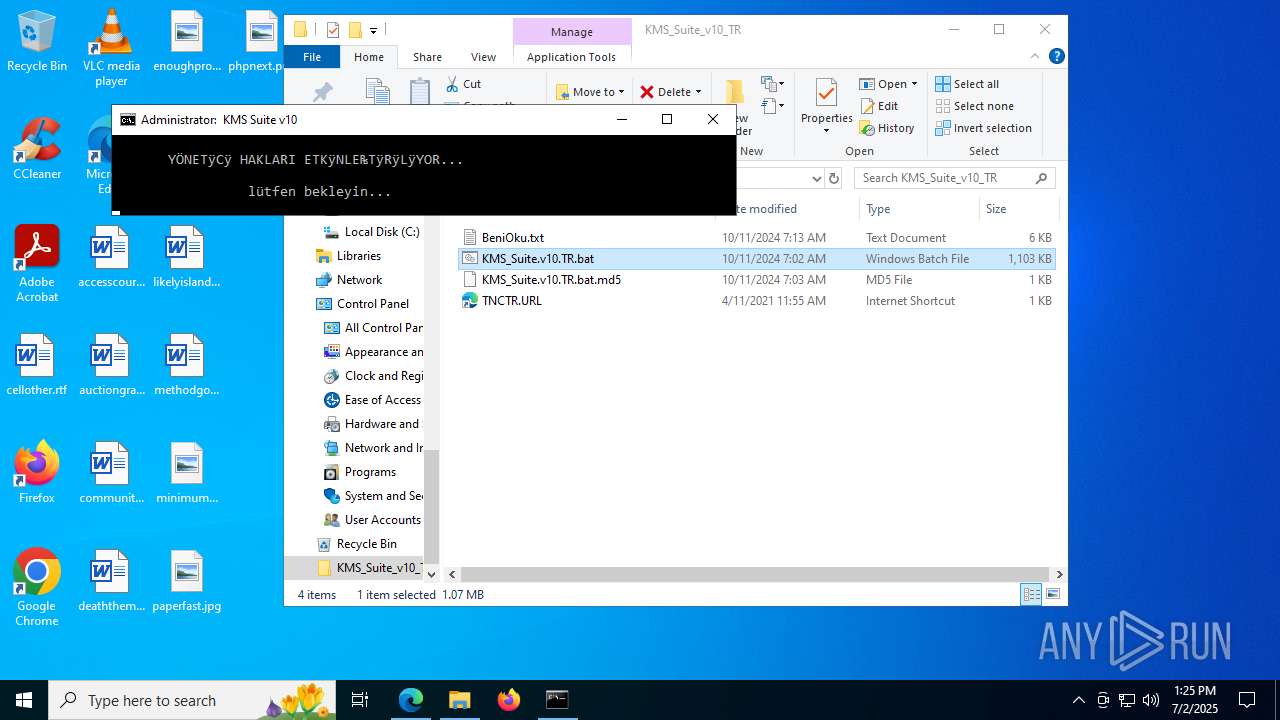
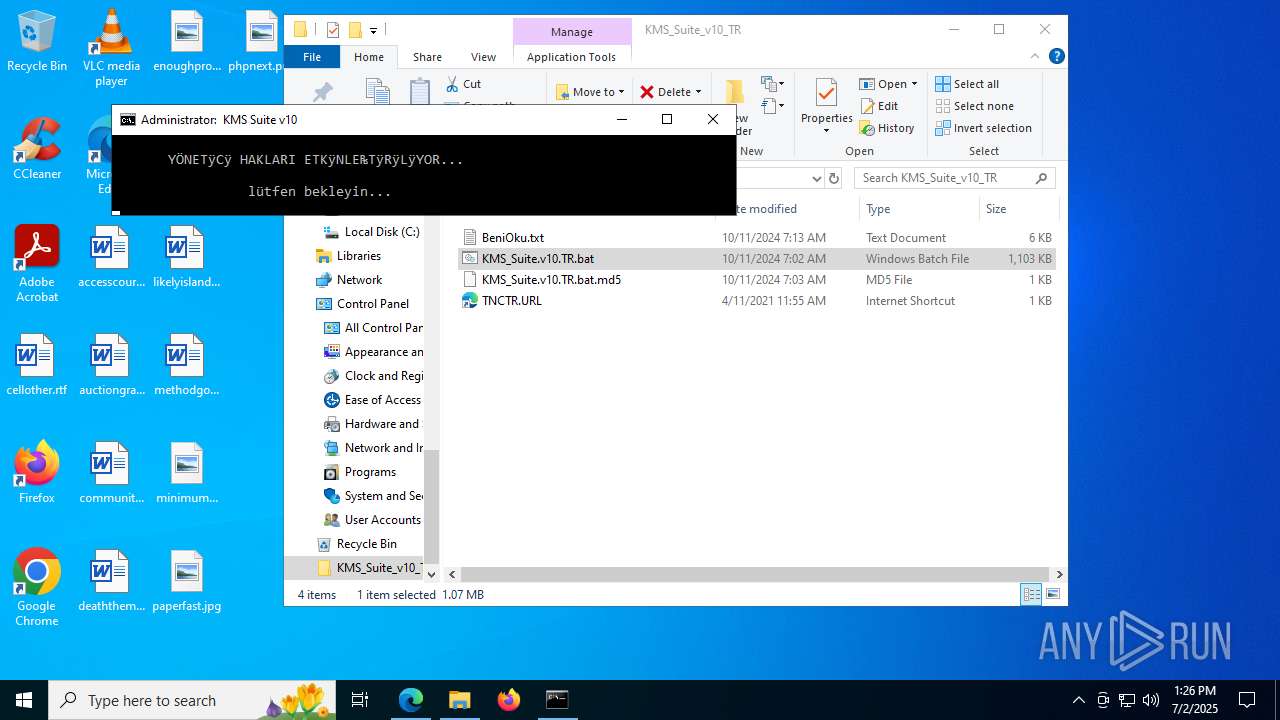
Executing commands from a ".bat" file
- cmd.exe (PID: 8092)
- mshta.exe (PID: 1984)
The process executes Powershell scripts
- cmd.exe (PID: 4916)
The executable file from the user directory is run by the CMD process
- center.exe (PID: 7804)
- center.exe (PID: 5576)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4916)
The process executes VB scripts
- cmd.exe (PID: 4916)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 6776)
- cscript.exe (PID: 6124)
Runs shell command (SCRIPT)
- mshta.exe (PID: 1984)
There is functionality for communication dyndns network (YARA)
- cmd.exe (PID: 4916)
Hides command output
- cmd.exe (PID: 3648)
- cmd.exe (PID: 72)
- cmd.exe (PID: 8164)
- cmd.exe (PID: 7552)
- cmd.exe (PID: 1852)
- cmd.exe (PID: 2388)
- cmd.exe (PID: 7680)
- cmd.exe (PID: 3568)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 8104)
- cmd.exe (PID: 4948)
- cmd.exe (PID: 6124)
- cmd.exe (PID: 868)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 5716)
- cmd.exe (PID: 3576)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 7188)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 4796)
Starts NET.EXE to map network drives
- cmd.exe (PID: 4916)
Starts SC.EXE for service management
- cmd.exe (PID: 4916)
Windows service management via SC.EXE
- sc.exe (PID: 7268)
- sc.exe (PID: 7240)
- sc.exe (PID: 7208)
- sc.exe (PID: 1200)
- sc.exe (PID: 7828)
- sc.exe (PID: 7328)
- sc.exe (PID: 5768)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 4916)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4916)
- cmd.exe (PID: 4948)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 1232)
- cmd.exe (PID: 1136)
- cmd.exe (PID: 7060)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 7904)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 4916)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 6124)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 6124)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 6124)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 6124)
There is functionality for taking screenshot (YARA)
- slui.exe (PID: 8164)
Lists all scheduled tasks
- schtasks.exe (PID: 4648)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4916)
INFO
Checks supported languages
- identity_helper.exe (PID: 7888)
- updater.exe (PID: 7540)
- updater.exe (PID: 7568)
- mode.com (PID: 6780)
- mode.com (PID: 8056)
- expand.exe (PID: 768)
- csc.exe (PID: 2468)
- cvtres.exe (PID: 4040)
- mode.com (PID: 2292)
- cvtres.exe (PID: 8008)
- csc.exe (PID: 3756)
- mode.com (PID: 8088)
- mode.com (PID: 7792)
- center.exe (PID: 7804)
- mode.com (PID: 2296)
- csc.exe (PID: 7952)
- cvtres.exe (PID: 7356)
- expand.exe (PID: 8056)
- csc.exe (PID: 7676)
- cvtres.exe (PID: 7548)
- center.exe (PID: 5576)
- mode.com (PID: 7560)
- mode.com (PID: 6732)
- mode.com (PID: 8184)
- csc.exe (PID: 7712)
- mode.com (PID: 7160)
- mode.com (PID: 7472)
- cvtres.exe (PID: 8112)
- expand.exe (PID: 3756)
- mode.com (PID: 5652)
Reads the computer name
- identity_helper.exe (PID: 7888)
- updater.exe (PID: 7540)
Application launched itself
- msedge.exe (PID: 6720)
Reads Environment values
- identity_helper.exe (PID: 7888)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6720)
- reg.exe (PID: 7824)
- reg.exe (PID: 5560)
- reg.exe (PID: 1296)
- reg.exe (PID: 6312)
- reg.exe (PID: 8008)
- reg.exe (PID: 6736)
- reg.exe (PID: 7536)
- reg.exe (PID: 4048)
- reg.exe (PID: 5708)
- reg.exe (PID: 7272)
- reg.exe (PID: 6352)
- reg.exe (PID: 7200)
- reg.exe (PID: 2508)
- reg.exe (PID: 7576)
Process checks whether UAC notifications are on
- updater.exe (PID: 7540)
Manual execution by a user
- cmd.exe (PID: 7480)
Starts MODE.COM to configure console settings
- mode.com (PID: 8056)
- mode.com (PID: 2292)
- mode.com (PID: 8088)
- mode.com (PID: 7792)
- mode.com (PID: 2296)
- mode.com (PID: 6780)
- mode.com (PID: 7560)
- mode.com (PID: 6732)
- mode.com (PID: 7472)
- mode.com (PID: 8184)
- mode.com (PID: 7160)
- mode.com (PID: 5652)
Checks proxy server information
- mshta.exe (PID: 1984)
- slui.exe (PID: 3800)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6680)
- powershell.exe (PID: 6648)
- powershell.exe (PID: 7992)
Checks operating system version
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4916)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6648)
- powershell.exe (PID: 6680)
- powershell.exe (PID: 7700)
- powershell.exe (PID: 7992)
Reads the machine GUID from the registry
- csc.exe (PID: 2468)
- expand.exe (PID: 768)
- csc.exe (PID: 3756)
- csc.exe (PID: 7952)
- expand.exe (PID: 8056)
- csc.exe (PID: 7676)
- csc.exe (PID: 7712)
- expand.exe (PID: 3756)
Create files in a temporary directory
- csc.exe (PID: 2468)
- expand.exe (PID: 768)
- csc.exe (PID: 3756)
- cvtres.exe (PID: 4040)
- cvtres.exe (PID: 8008)
- csc.exe (PID: 7952)
- cvtres.exe (PID: 7356)
- expand.exe (PID: 8056)
- csc.exe (PID: 7676)
- cvtres.exe (PID: 7548)
- csc.exe (PID: 7712)
- cvtres.exe (PID: 8112)
- expand.exe (PID: 3756)
The sample compiled with english language support
- expand.exe (PID: 768)
- xcopy.exe (PID: 5960)
Reads Internet Explorer settings
- mshta.exe (PID: 1984)
- mshta.exe (PID: 7880)
Reads the software policy settings
- slui.exe (PID: 3800)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 1080)
- WMIC.exe (PID: 6176)
- WMIC.exe (PID: 1480)
- WMIC.exe (PID: 5908)
- WMIC.exe (PID: 7520)
- WMIC.exe (PID: 2272)
- WMIC.exe (PID: 2996)
- WMIC.exe (PID: 6688)
- WMIC.exe (PID: 6836)
- WMIC.exe (PID: 6312)
- WMIC.exe (PID: 8112)
- WMIC.exe (PID: 7888)
- WMIC.exe (PID: 8008)
- WMIC.exe (PID: 7204)
- WMIC.exe (PID: 8088)
- WMIC.exe (PID: 5896)
- WMIC.exe (PID: 3656)
- WMIC.exe (PID: 1332)
- WMIC.exe (PID: 7184)
- WMIC.exe (PID: 2552)
- WMIC.exe (PID: 728)
- WMIC.exe (PID: 7324)
- WMIC.exe (PID: 2280)
- WMIC.exe (PID: 1212)
- WMIC.exe (PID: 7560)
- WMIC.exe (PID: 7784)
- cscript.exe (PID: 6124)
- WMIC.exe (PID: 2160)
- WMIC.exe (PID: 3940)
- WMIC.exe (PID: 7256)
- WMIC.exe (PID: 6308)
- WMIC.exe (PID: 1388)
- WMIC.exe (PID: 7188)
- WMIC.exe (PID: 7156)
- WMIC.exe (PID: 4312)
- WMIC.exe (PID: 2072)
- WMIC.exe (PID: 8100)
- WMIC.exe (PID: 7500)
- WMIC.exe (PID: 7484)
- WMIC.exe (PID: 1872)
- WMIC.exe (PID: 4560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
847
Monitored processes
697
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | C:\WINDOWS\system32\cmd.exe /c dir /b /ad C:\WINDOWS\System32\spp\tokens\addons 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 72 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion" /v ProductName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 72 | findstr /I /C:"ExcelRetail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 72 | findstr /I /C:"ProjectPro2019Retail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | findstr /I /C:"Word2019Volume" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | findstr /I /C:"HomeBusinessRetail" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | reg query HKLM\SOFTWARE\Microsoft\Office\ClickToRun\ProductReleaseIDs\5B9936B4-3789-47CD-A7E1-A479148E7D7F\ProPlusVolume.16 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | C:\WINDOWS\system32\net1 stop sppsvc /y | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 480 | C:\WINDOWS\system32\cmd.exe /c powershell -nop -c "(([WMISEARCHER]'Select Caption from Win32_OperatingSystem').Get()).Caption" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 504 | reg query HKLM\SOFTWARE\Microsoft\Office\ClickToRun\Configuration /v ProductReleaseIds | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
126 878
Read events
126 777
Write events
95
Delete events
6
Modification events
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F343AF7888972F00 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394036 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1FDF9B27-DDA1-496F-96C6-5052AD5AA805} | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394036 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {020EFDBF-ED62-4CB1-AE9E-0A84249CD53D} | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394036 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DE5AD012-0D85-459D-A03E-177C3B48A89E} | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394036 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6DE0B664-E9AA-43BF-9F76-61E373470118} | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394036 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {259FB1B4-4BAE-4B7E-B211-7A165C5BD09B} | |||
Executable files
16
Suspicious files
377
Text files
195
Unknown types
63
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1762e0.TMP | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1762f0.TMP | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1762f0.TMP | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17631f.TMP | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17633e.TMP | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
138
DNS requests
144
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6380 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:ARVjGkraQNYOTP0XK0BnmgK-ovmMNelsU89vCIm1cfQ&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4580 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7328 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7328 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3392 | svchost.exe | HEAD | 200 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751762401&P2=404&P3=2&P4=nilNZD4sxAAiAtgjeyx8wIgOGX35aGLuP5mSyI45mi%2fOGo3yZoxybhi7JocZw6hxdc8Ycje%2fgEV0Dw3QcXMgbQ%3d%3d | unknown | — | — | whitelisted |
3392 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751762401&P2=404&P3=2&P4=nilNZD4sxAAiAtgjeyx8wIgOGX35aGLuP5mSyI45mi%2fOGo3yZoxybhi7JocZw6hxdc8Ycje%2fgEV0Dw3QcXMgbQ%3d%3d | unknown | — | — | whitelisted |
3392 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751762401&P2=404&P3=2&P4=nilNZD4sxAAiAtgjeyx8wIgOGX35aGLuP5mSyI45mi%2fOGo3yZoxybhi7JocZw6hxdc8Ycje%2fgEV0Dw3QcXMgbQ%3d%3d | unknown | — | — | whitelisted |
3392 | svchost.exe | HEAD | 200 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751762403&P2=404&P3=2&P4=WEbjze3OQe5WeDpyb26DBxbORQrht4bAT3x25hpce%2b9RjPeCBKtkqcCiuHb5V7h2d3eo2za3PCXj3%2bmQuKZdbQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1352 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6380 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6380 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6380 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6380 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
6380 | msedge.exe | 188.114.96.3:443 | www.tnctr.com | CLOUDFLARENET | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.tnctr.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |