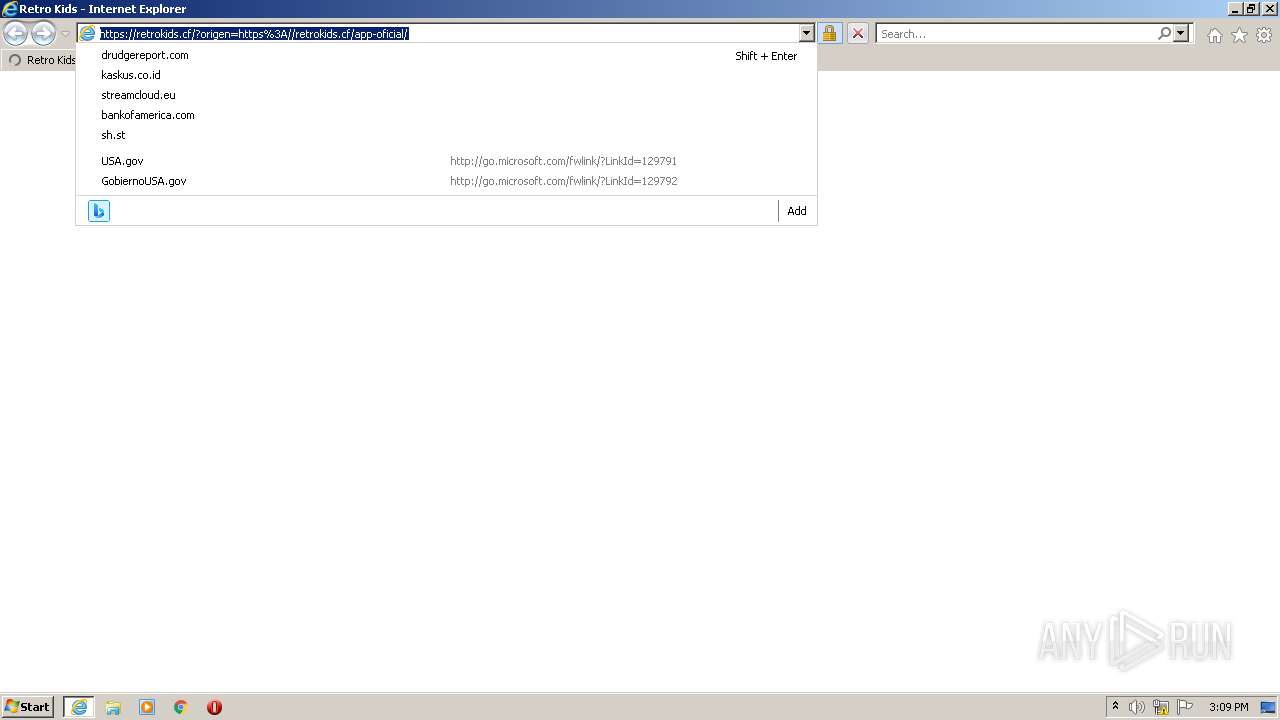
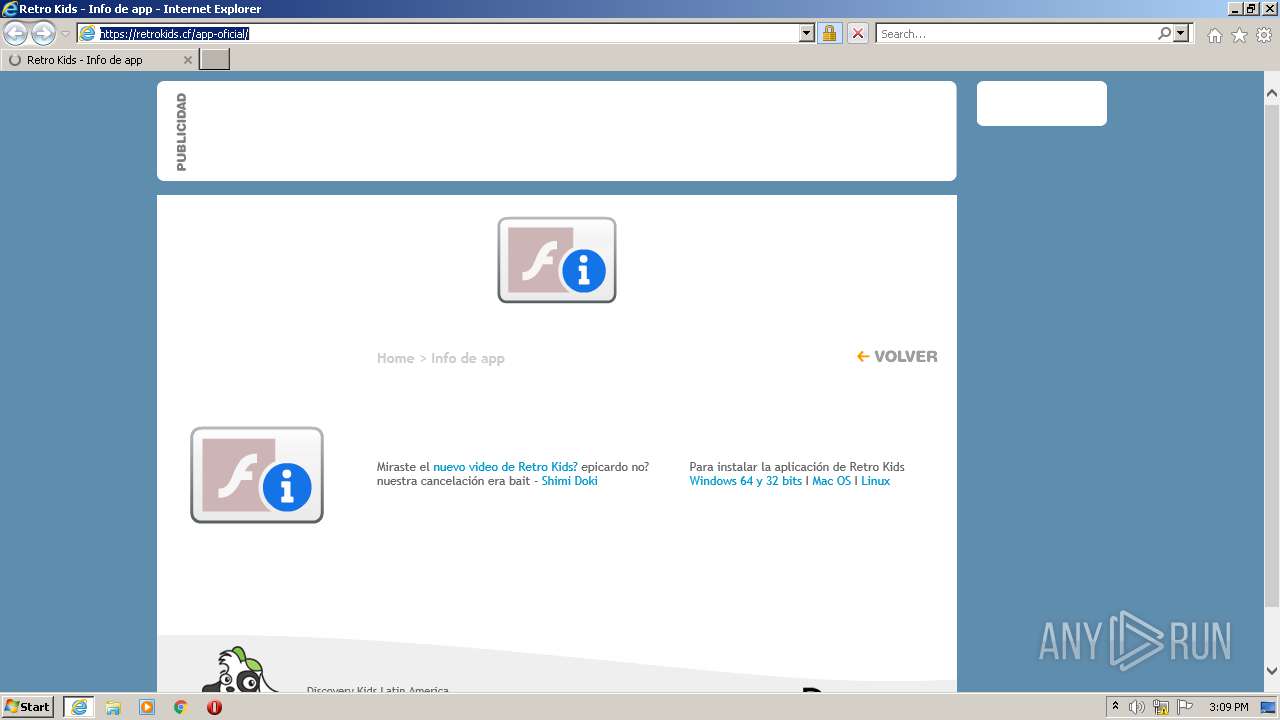
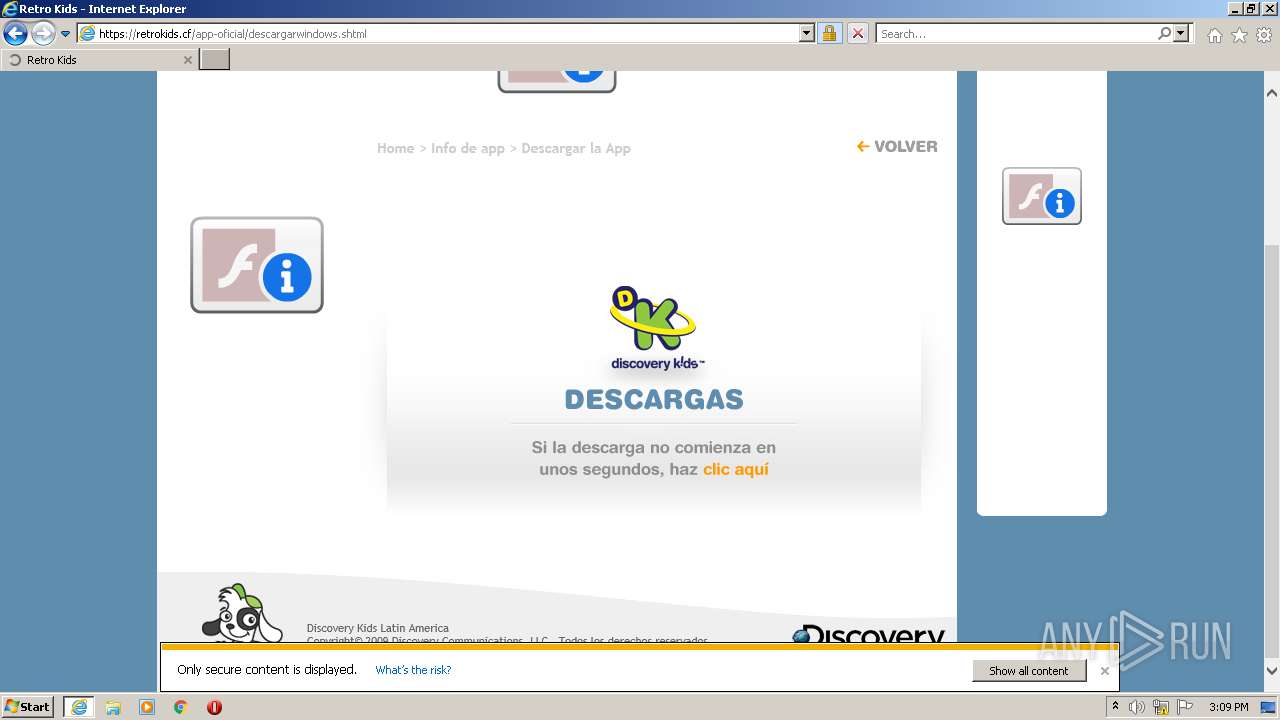
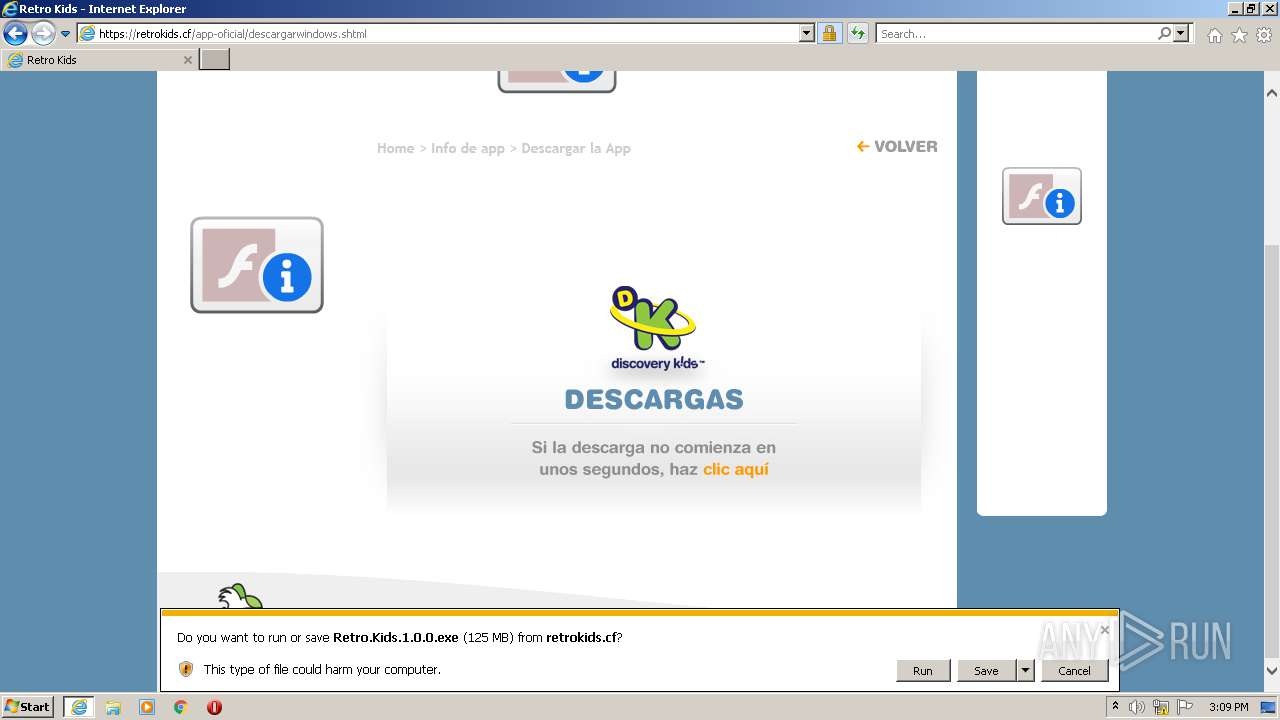
| URL: | https://retrokids.cf/app-oficial/ |
| Full analysis: | https://app.any.run/tasks/405e6d87-e09b-4eb3-b8cb-fdb541eabe10 |
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2021, 15:09:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F5AE848C9BF043DF0161D8C9690232DE |
| SHA1: | 4C9549E1BCA2DFFB5B6EB980025E9A2148ED7259 |
| SHA256: | 9EFBC568258705740E181591F6D40424F0065AB471C7F01C4932CFDD00349DB9 |
| SSDEEP: | 3:N8uzQ4hgJK:2JC |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3896)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3072)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3072)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3072)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3072)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3896)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 2176)
- iexplore.exe (PID: 3896)
Creates files in the user directory
- iexplore.exe (PID: 3896)
- iexplore.exe (PID: 2176)
Checks Windows Trust Settings
- iexplore.exe (PID: 2176)
- iexplore.exe (PID: 3896)
Changes internet zones settings
- iexplore.exe (PID: 2176)
Checks supported languages
- iexplore.exe (PID: 2176)
- iexplore.exe (PID: 3896)
Reads the computer name
- iexplore.exe (PID: 3896)
- iexplore.exe (PID: 2176)
Application launched itself
- iexplore.exe (PID: 2176)
Reads internet explorer settings
- iexplore.exe (PID: 3896)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2176)
Reads CPU info
- iexplore.exe (PID: 3896)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2176)
Changes settings of System certificates
- iexplore.exe (PID: 2176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2176 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://retrokids.cf/app-oficial/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3072 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3896 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2176 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
21 565
Read events
21 421
Write events
142
Delete events
2
Modification events
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30925728 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30925728 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
11
Text files
84
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\regionmap[1].js | text | |
MD5:20DF53C7AC823366C2157F832537B032 | SHA256:FCFF9ED4BC832D52F402549A64809EA7FB9DA91409DEF9FE710B9253A1FAB3DB | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\fb-sdk-en_GB[1].js | text | |
MD5:25A9274C40D7DFE146F8C863071F49DC | SHA256:6F503ABA755124095E7F4847088D2BFB3A69AD7C739FC1873A6B85D9439186E5 | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\scripts[1].js | text | |
MD5:016EF43CC554EA57D0491647C6E587C9 | SHA256:6F538971ED6B7BA0A4C962A3FEF0E8935E3589D5B4EC3D74583D7A44BB79D1E0 | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\estilos_kids[1].css | text | |
MD5:3C7BFF4734782A801580299FA1855376 | SHA256:FCA2874D86A0E49236F60EE3EB3CB17FB0270AB8F70D09787DD870A25A5E1613 | |||
| 2176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:B7B896FAF221C49B0A63EB3EF40B924E | SHA256:1E9C1A6EFB968F3F254FCB5839CF8F93BE7BFE9757B3CC922B0369AB39C122B6 | |||
| 2176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:2DD01E565613FCE373341A8938EF3D2B | SHA256:064B1D5D45F938B912E33F78417F20D60B30FDF2875F5D76782DB775C7CC159D | |||
| 2176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:260F5881E8DE18560D439F0C72C73D20 | SHA256:C276F62D721B98E36DDECEF8A757CB6D2DA06685A7AF271DAF6097613407A83F | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:C0D097521BE82728111D02382F57C7EB | SHA256:2F5AB811E91C7D3A3124506857B60A7EE04D74C45A39190706982D56EB56706F | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:52FC085B626B5E851AC6C22F21C6DFF9 | SHA256:451F28A6D94B40BFDA3EDBBB4CA22A1E42C6B1F287AFAAA7DC65552FF1B051F8 | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\app-oficial[1].htm | html | |
MD5:4FCCDD50ED8411FF51AE53071856E528 | SHA256:2F88A8B2DCF781B6601905D48D1B73259FA310306A0572E8E79AA307DAD92DA6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
42
DNS requests
25
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | iexplore.exe | GET | 200 | 92.123.13.139:80 | http://x1.c.lencr.org/ | FR | der | 717 b | whitelisted |
2176 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3896 | iexplore.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3896 | iexplore.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2176 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3896 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
3896 | iexplore.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3896 | iexplore.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2176 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2176 | iexplore.exe | GET | 200 | 8.253.95.249:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?29222b86f09572fb | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2176 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2176 | iexplore.exe | 95.100.146.43:80 | ctldl.windowsupdate.com | Akamai Technologies, Inc. | — | unknown |
2176 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2176 | iexplore.exe | 8.253.95.249:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
3896 | iexplore.exe | 95.100.146.43:80 | ctldl.windowsupdate.com | Akamai Technologies, Inc. | — | unknown |
2176 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3896 | iexplore.exe | 92.123.13.139:80 | x1.c.lencr.org | Telia Company AB | FR | unknown |
3896 | iexplore.exe | 104.102.28.179:443 | geo2.adobe.com | Akamai Technologies, Inc. | US | unknown |
3896 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
retrokids.cf |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
geo2.adobe.com |
| whitelisted |
fpdownload.macromedia.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |
3896 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.cf) in TLS SNI |
3896 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.cf) |
3896 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.cf) |
3896 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.cf) |
3896 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.cf) |
3896 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.cf) |
3896 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.cf) |
3896 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.cf) |