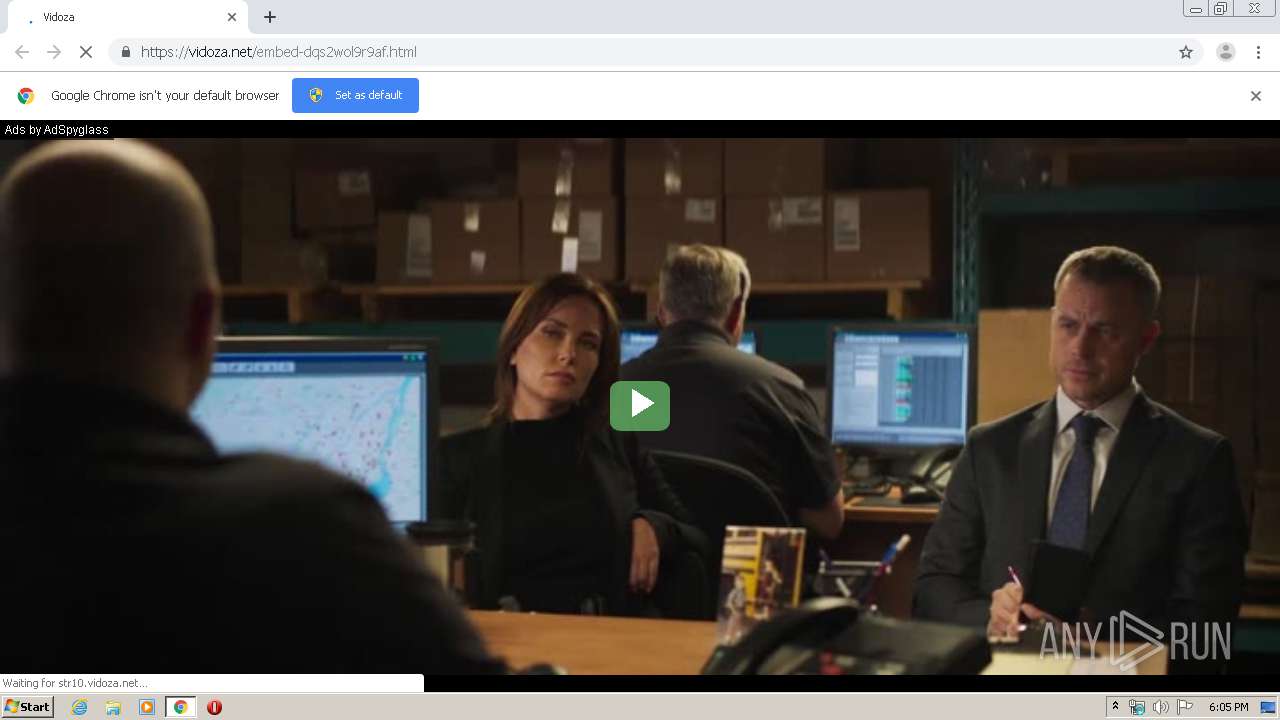
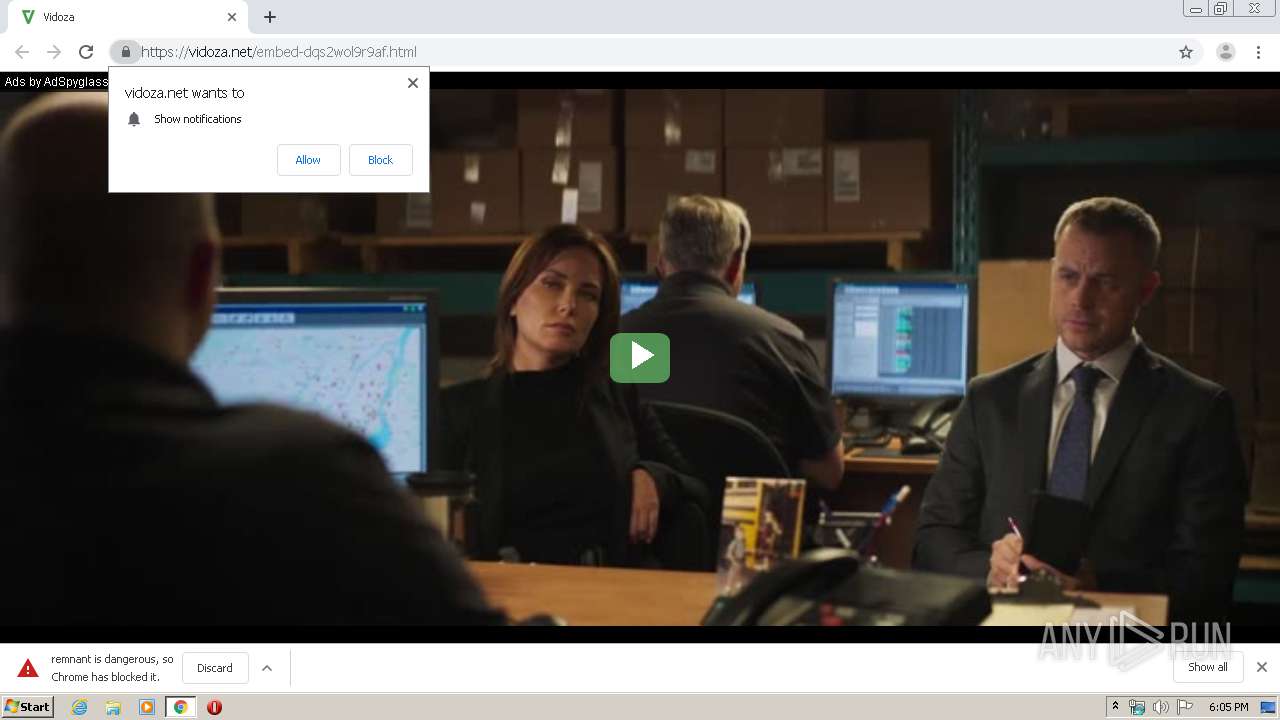
| URL: | http://vidoza.net/embed-dqs2wol9r9af.html |
| Full analysis: | https://app.any.run/tasks/60630e4a-24f6-4d86-81e7-cedfacfae000 |
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2020, 18:05:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4E6291C6ADAEC6E4C8AB3010B5D4922D |
| SHA1: | D23028DCDFEED8103252C672D65913EA3D21EA38 |
| SHA256: | 9EF7F464F10C205C9BE403DD7014A3BC6E2C92F0C5982F16D13098406E993DF1 |
| SSDEEP: | 3:N1KIvK+1gn:CIyzn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2784)
INFO
Reads the hosts file
- chrome.exe (PID: 2784)
- chrome.exe (PID: 3868)
Creates files in the user directory
- chrome.exe (PID: 2784)
Application launched itself
- chrome.exe (PID: 2784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
45
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9594026530749301752,5125283947738166816,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2060883287201056518 --mojo-platform-channel-handle=5812 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9594026530749301752,5125283947738166816,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6614888599738285352 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9594026530749301752,5125283947738166816,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16412374563009936431 --mojo-platform-channel-handle=5088 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9594026530749301752,5125283947738166816,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14974391946102480839 --mojo-platform-channel-handle=5268 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9594026530749301752,5125283947738166816,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14098836790860123131 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9594026530749301752,5125283947738166816,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=667150193506449927 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2580 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9594026530749301752,5125283947738166816,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10102082030878789851 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9594026530749301752,5125283947738166816,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2646536285068898119 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9594026530749301752,5125283947738166816,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=930129361263949779 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
981
Read events
877
Write events
99
Delete events
5
Modification events
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2784-13226695522677625 |
Value: 259 | |||
Executable files
0
Suspicious files
140
Text files
269
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E4ECA63-AE0.pma | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cadac9bd-2c7b-4276-a4fe-c2dfd122197a.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66d49.TMP | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66d49.TMP | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa66dc6.TMP | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66faa.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
107
DNS requests
82
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
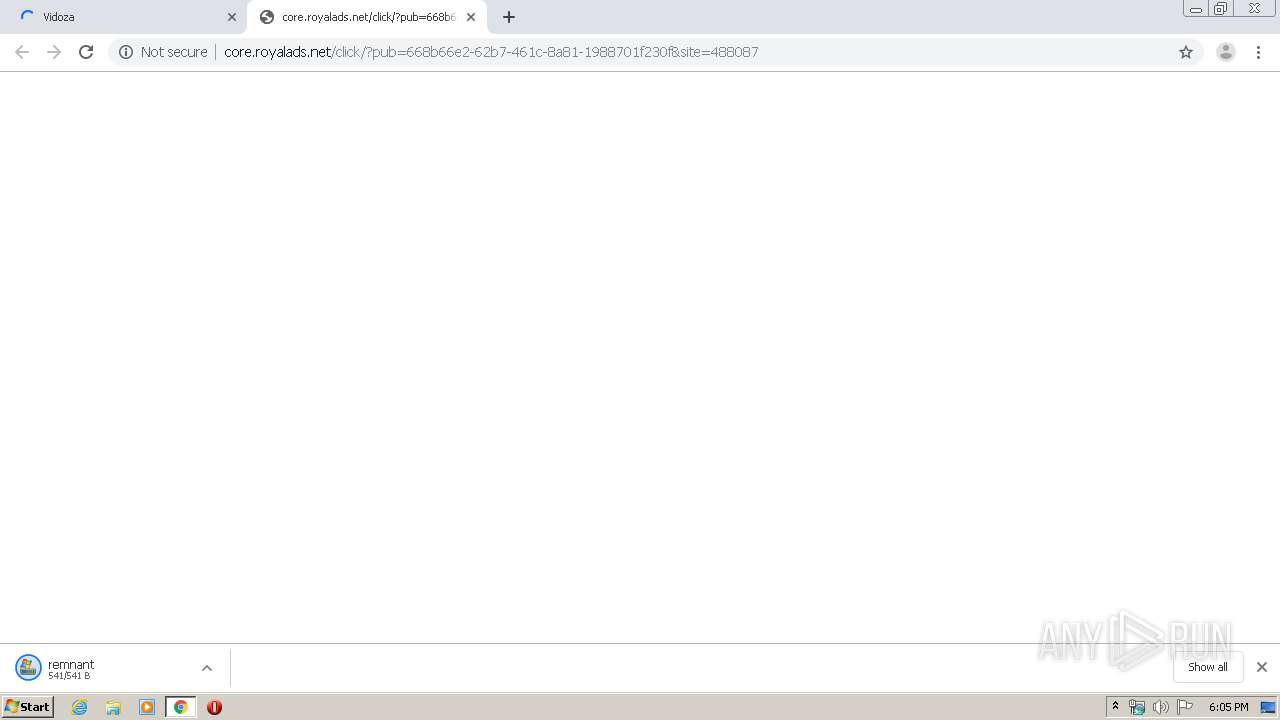
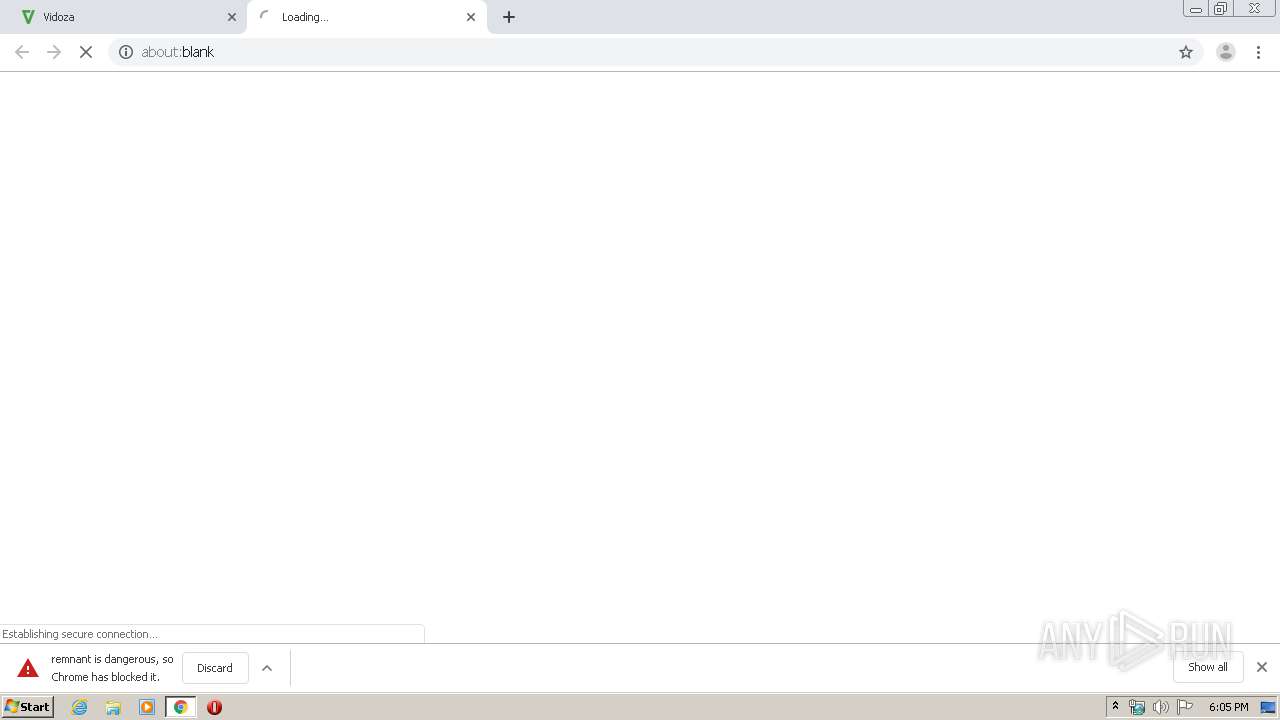
3868 | chrome.exe | GET | 302 | 147.135.243.181:80 | http://core.royalads.net/go/?pub=668b66e2-62b7-461c-8a81-1988701f230f&site=540928&ref=http%3A%2F%2Fps.popcash.net%2Fgo%2F135886%2F540928&scrw=1280&scrh=720&nlc=GZd695uj5n531rMi&ven=WebKit&ver=WebGL%201.0%20(OpenGL%20ES%202.0%20Chromium)&p=falsexundefined&iif=0 | NL | compressed | 611 b | unknown |
3868 | chrome.exe | GET | 200 | 147.135.243.181:80 | http://core.royalads.net/click/?pub=668b66e2-62b7-461c-8a81-1988701f230f&site=465699 | NL | html | 609 b | unknown |
3868 | chrome.exe | GET | 200 | 35.168.149.183:80 | http://ps.popcash.net/go/135886/540928 | US | html | 271 b | shared |
3868 | chrome.exe | GET | 303 | 35.168.149.183:80 | http://ps.popcash.net/ad/ad?p=135886&w=540928&t=0d6c633a59f665cb&r=&vw=1280&vh=620 | US | html | 115 b | shared |
3868 | chrome.exe | GET | 200 | 147.135.243.181:80 | http://core.royalads.net/click/?pub=668b66e2-62b7-461c-8a81-1988701f230f&site=488087 | NL | html | 594 b | unknown |
3868 | chrome.exe | GET | 302 | 147.135.243.181:80 | http://core.royalads.net/go/?pub=668b66e2-62b7-461c-8a81-1988701f230f&site=465699&ref=http%3A%2F%2Fps.popcash.net%2Fgo%2F79141%2F465699&scrw=1280&scrh=720&nlc=61zR9p7F5n531rMi&ven=WebKit&ver=WebGL%201.0%20(OpenGL%20ES%202.0%20Chromium)&p=falsexundefined&iif=0 | NL | compressed | 609 b | unknown |
3868 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTIyCPRUzvKHRw7iRE1lF%2BfcLu%2FjgQUypJnUmHervy6Iit%2FHIdMJftvmVgCEA8U5EqxnJKPhgtu86L%2BgMk%3D | US | der | 471 b | whitelisted |
3868 | chrome.exe | GET | 303 | 35.168.149.183:80 | http://ps.popcash.net/ad/ad?p=201730&w=488087&d=821f52f841fd93b97d45-1556198054488087 | US | html | 115 b | shared |
3868 | chrome.exe | GET | 200 | 188.164.249.105:80 | http://adsremnant.com/remnant | NL | html | 541 b | unknown |
3868 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3868 | chrome.exe | 91.235.142.9:80 | vidoza.net | FOP Smirnov V'yacheslav Valentunovuch | UA | unknown |
3868 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3868 | chrome.exe | 91.235.142.9:443 | vidoza.net | FOP Smirnov V'yacheslav Valentunovuch | UA | unknown |
3868 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3868 | chrome.exe | 172.217.22.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3868 | chrome.exe | 49.12.12.32:443 | vd.7vid.net | — | IN | suspicious |
3868 | chrome.exe | 104.17.64.4:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3868 | chrome.exe | 104.20.111.39:443 | static.addtoany.com | Cloudflare Inc | US | shared |
3868 | chrome.exe | 205.185.216.42:443 | cdn.o333o.com | Highwinds Network Group, Inc. | US | whitelisted |
3868 | chrome.exe | 216.58.207.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vidoza.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
vd.7vid.net |
| suspicious |
maxcdn.bootstrapcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cdn.o333o.com |
| suspicious |
static.addtoany.com |
| whitelisted |
assampant.club |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .world TLD |