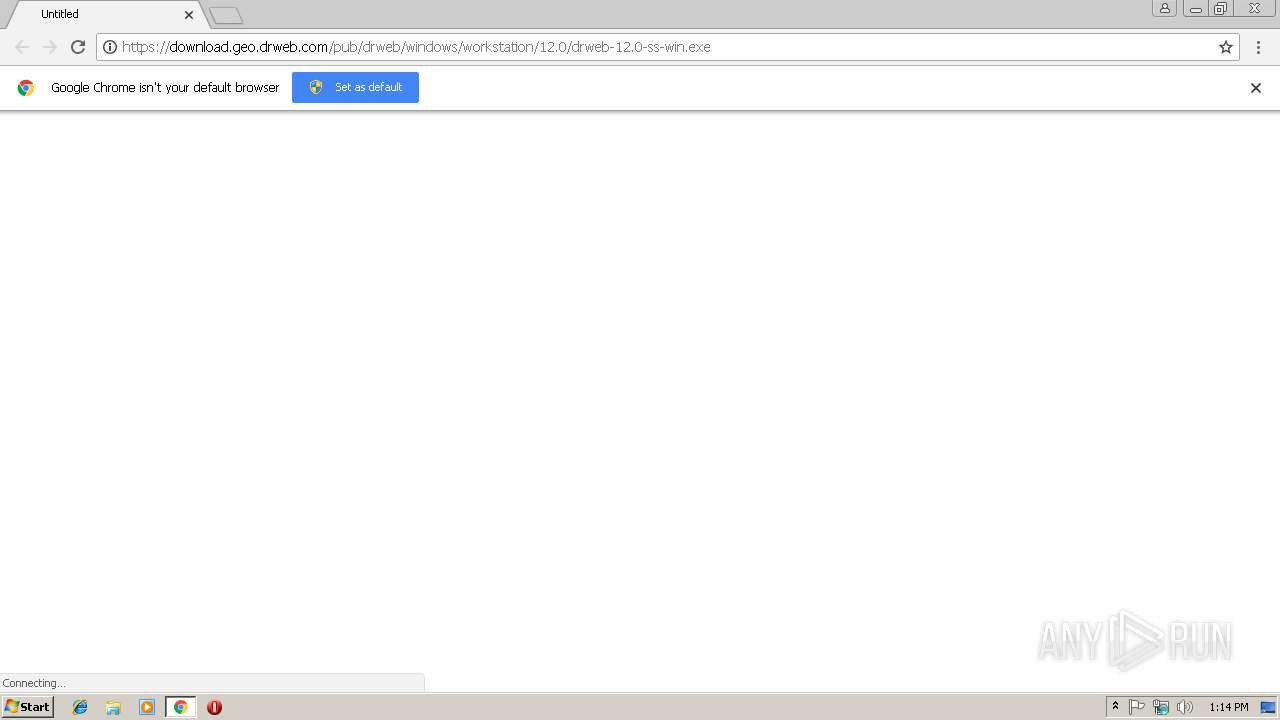
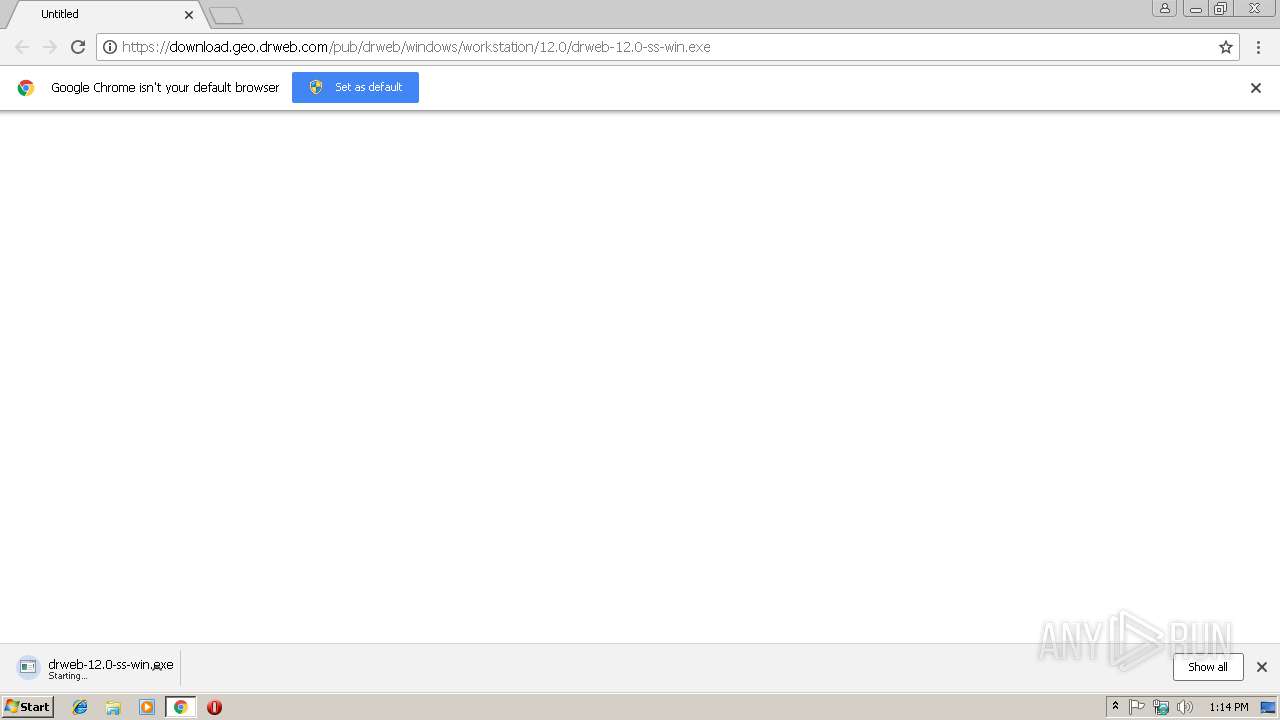
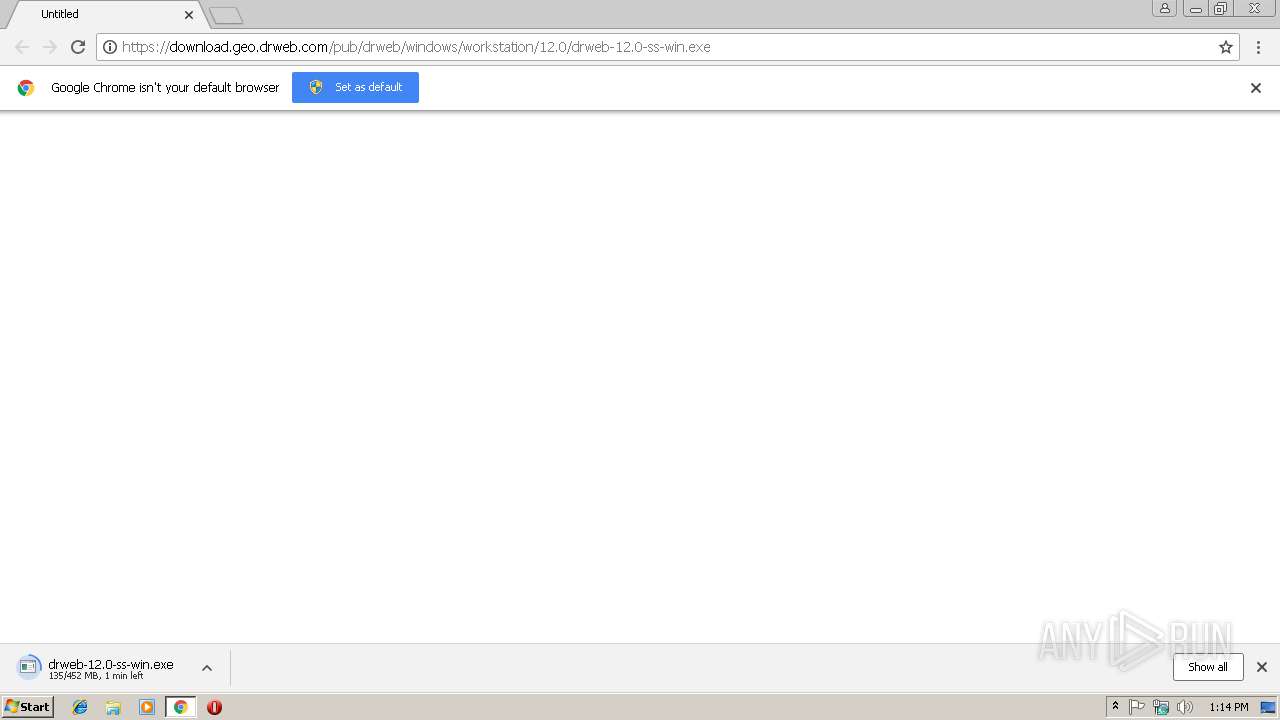
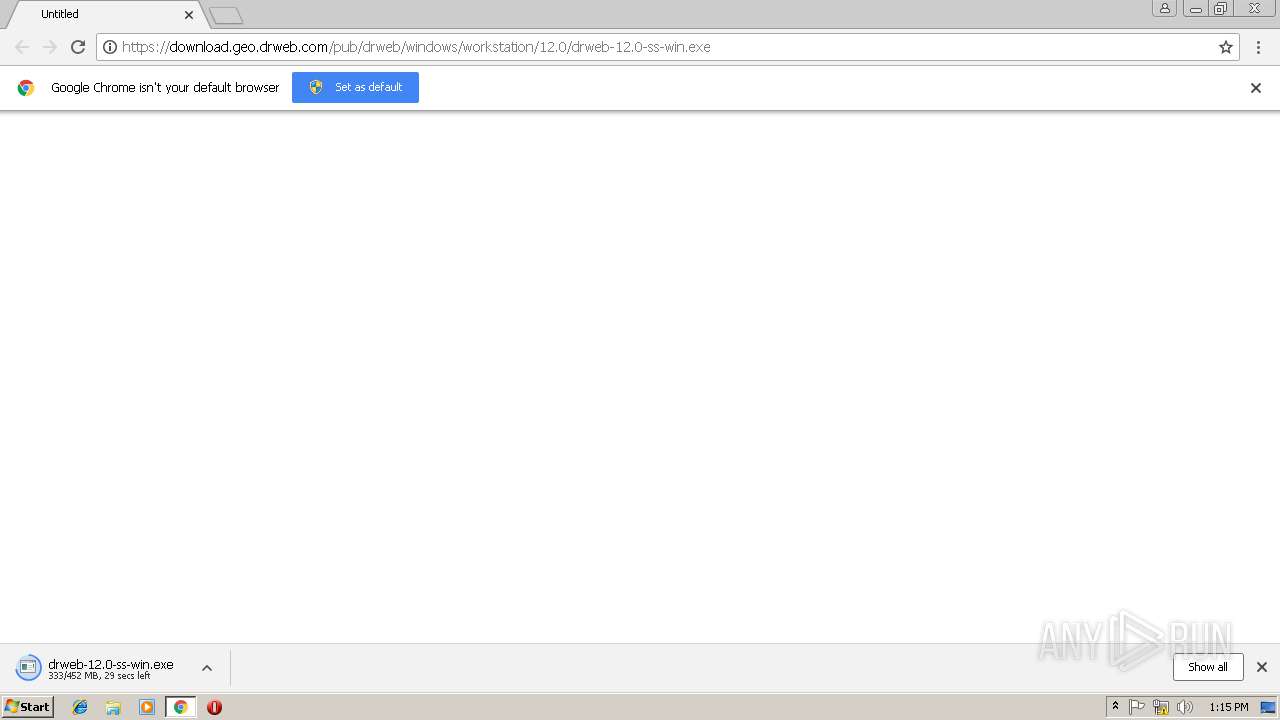
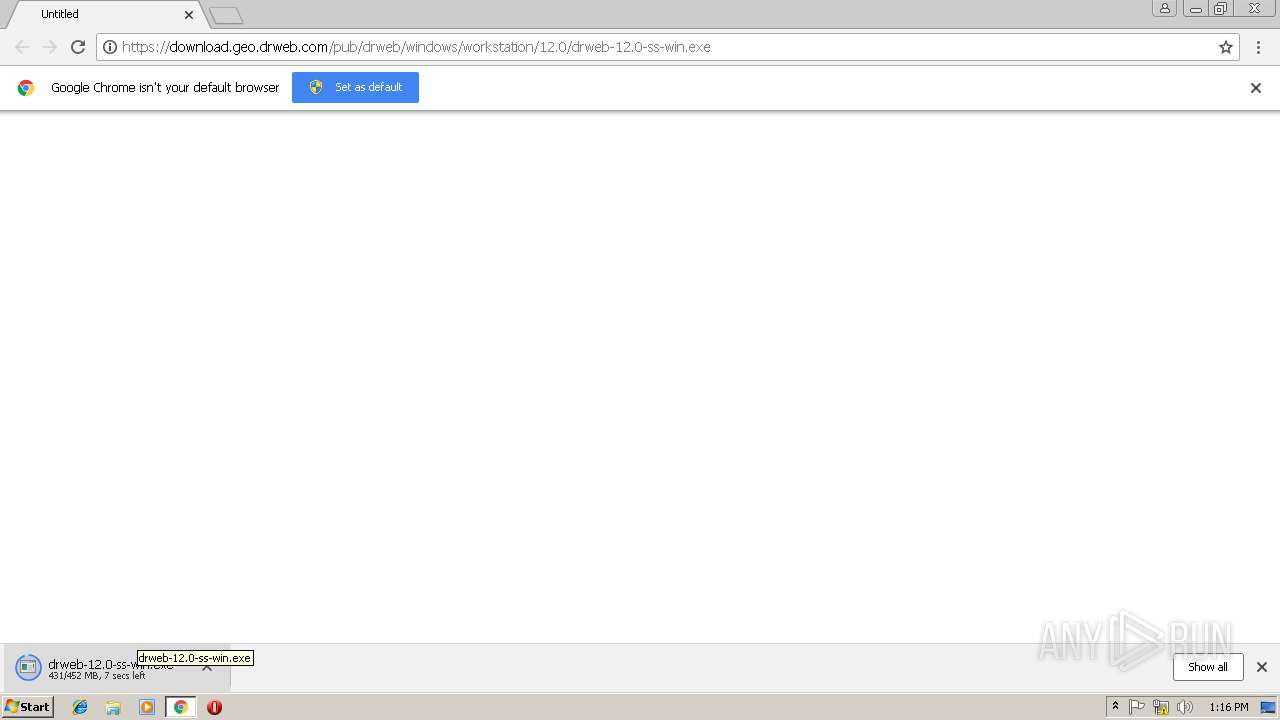
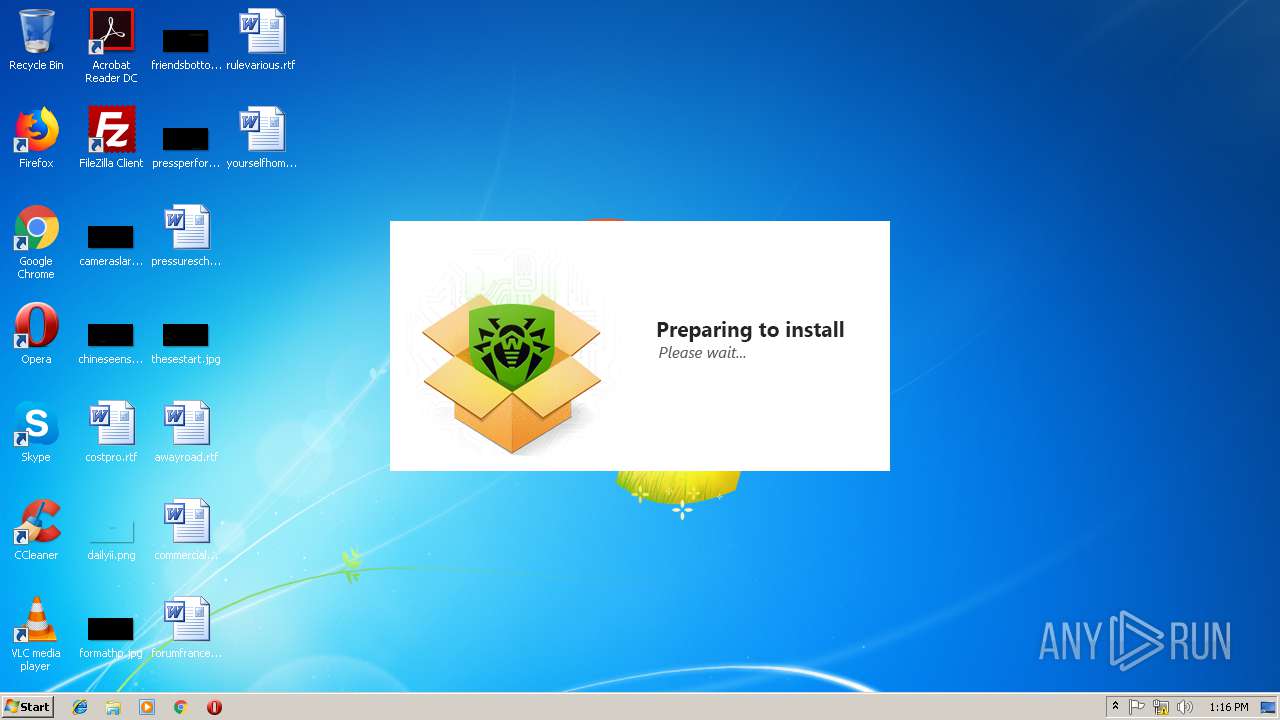
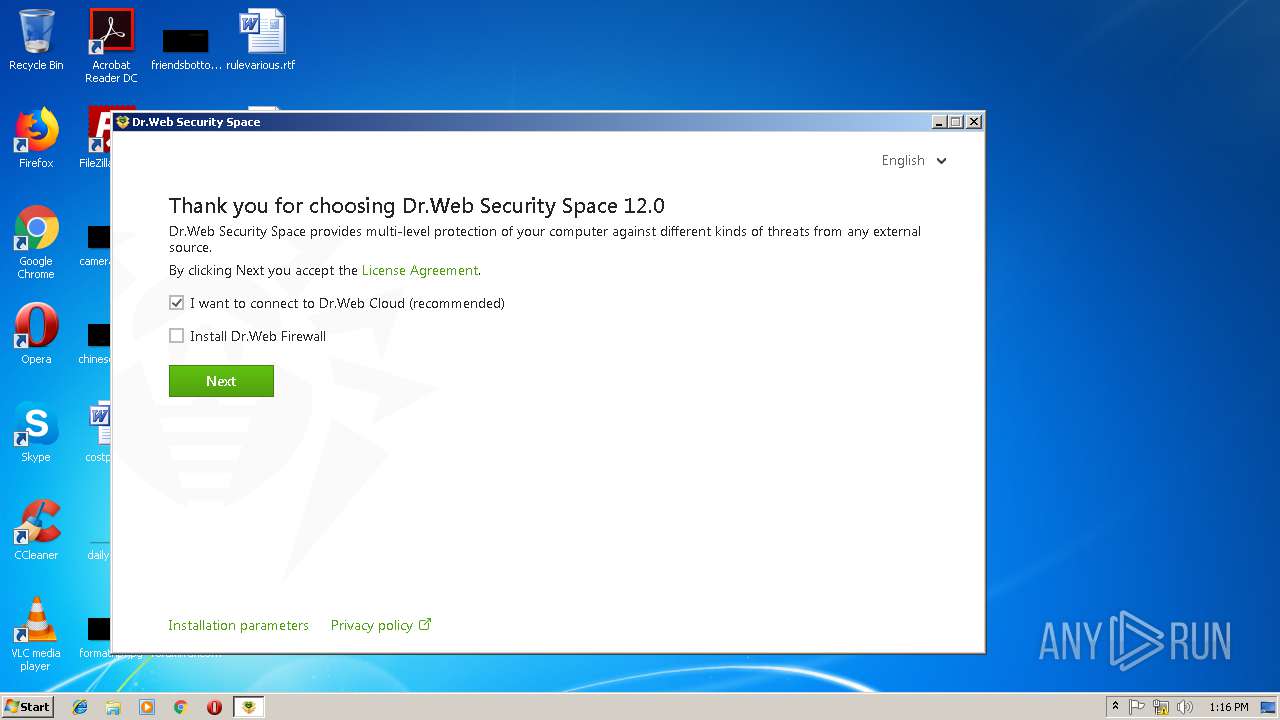
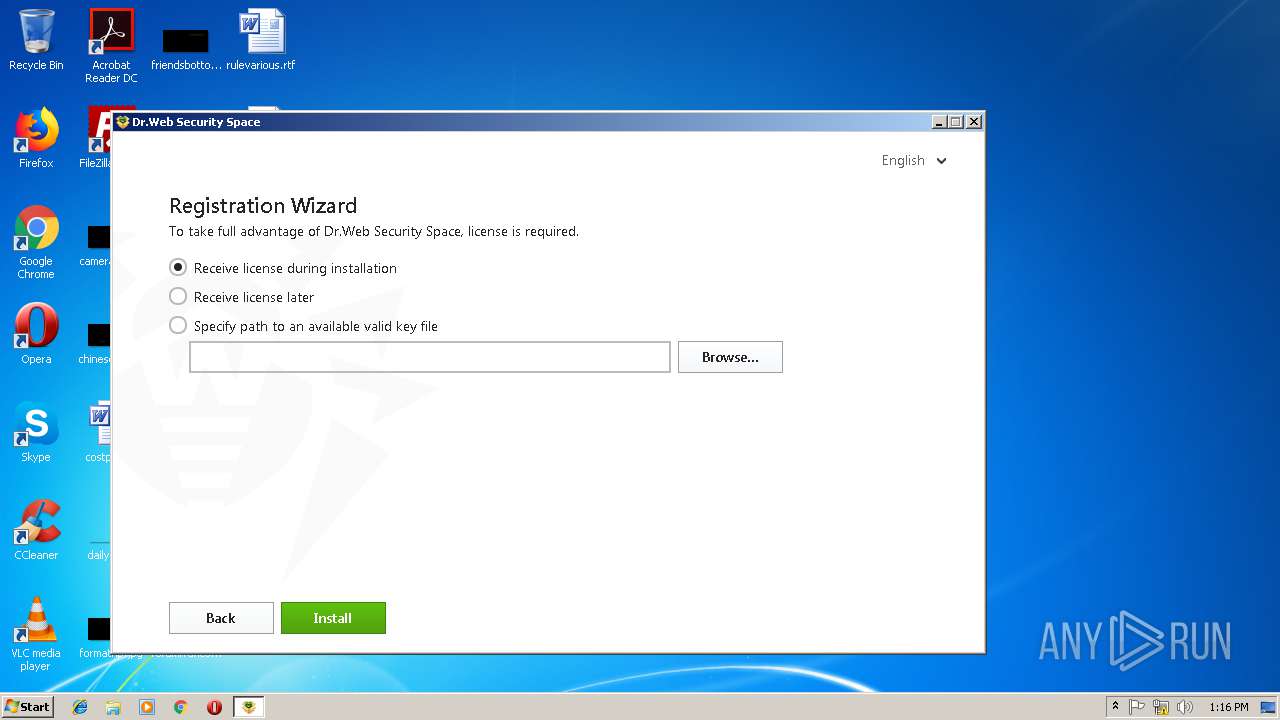
| URL: | https://download.geo.drweb.com/pub/drweb/windows/workstation/12.0/drweb-12.0-ss-win.exe |
| Full analysis: | https://app.any.run/tasks/b3a8f48c-35f9-4121-a769-bd688524db27 |
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2019, 13:13:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B566A6E00A7C8393E043FAFF727AC306 |
| SHA1: | FAD19F7D61D6C6847E5E4159CF9B390E0C3FB2C1 |
| SHA256: | 9EF46AEF442C15C78C3A0CDB0A97E2B4E900AF47CC6F6F91AF9FEA82DF349B9E |
| SSDEEP: | 3:N8SElWtyCQHaXrCL8HKXPBK+caDHARUIdA:2SKWtQHaOL8HMJcxC |
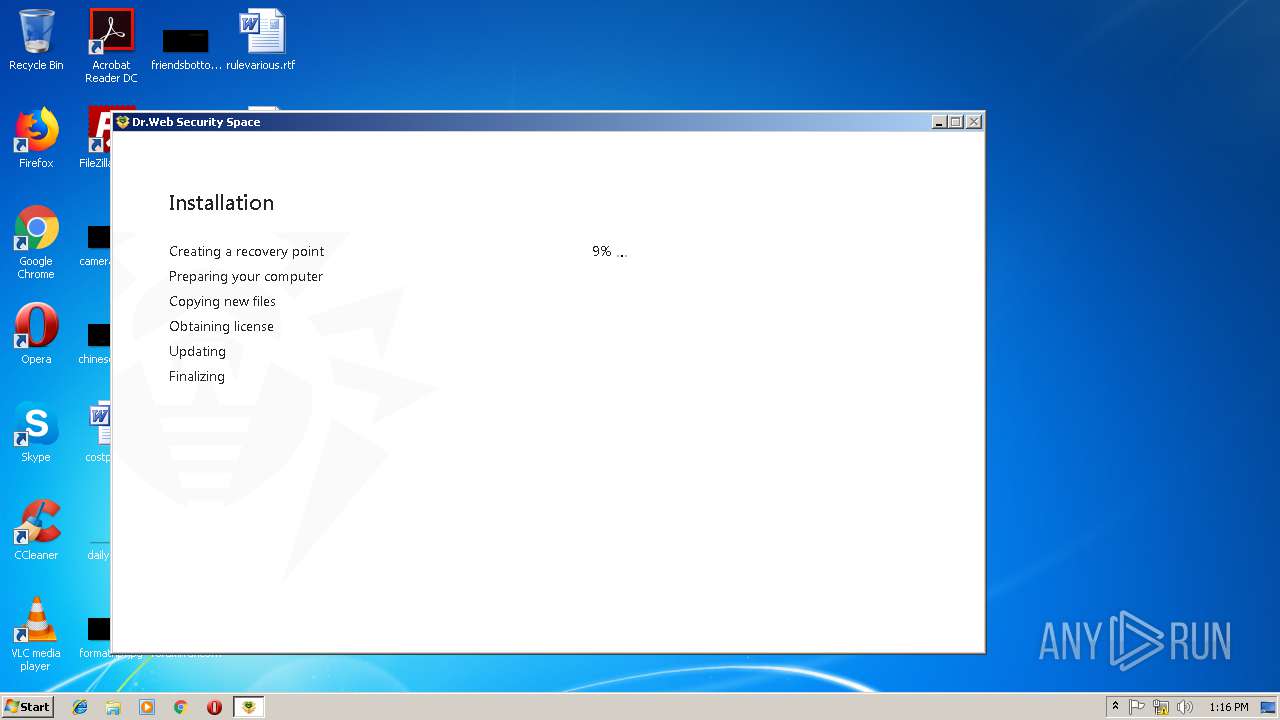
MALICIOUS
Application was dropped or rewritten from another process
- win-space-setup.exe (PID: 3944)
- drwupsrv.exe (PID: 3952)
- drwupsrv.exe (PID: 3624)
- dwengine.exe (PID: 2144)
- dwservice.exe (PID: 2324)
- dwengine.exe (PID: 3408)
- dwantispam.exe (PID: 2984)
- dwarkdaemon.exe (PID: 2756)
- dwservice.exe (PID: 4004)
- dwservice.exe (PID: 2488)
- dwnetfilter.exe (PID: 2460)
- spideragent.exe (PID: 1852)
- frwl_svc.exe (PID: 3764)
Loads dropped or rewritten executable
- dwservice.exe (PID: 2324)
- dwarkdaemon.exe (PID: 2756)
- regsvr32.exe (PID: 4068)
- dwengine.exe (PID: 3408)
- regsvr32.exe (PID: 2904)
Registers / Runs the DLL via REGSVR32.EXE
- drwupsrv.exe (PID: 3624)
Changes the autorun value in the registry
- drwupsrv.exe (PID: 3624)
SUSPICIOUS
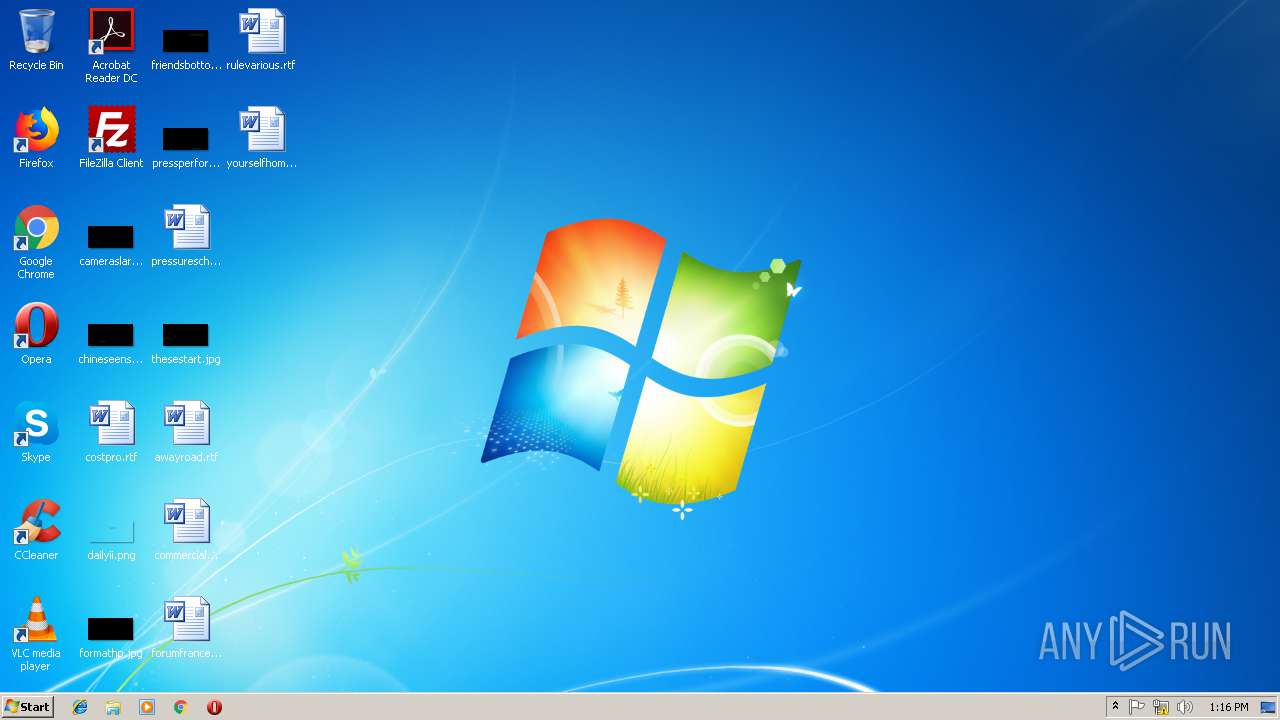
Creates files in the program directory
- drweb-12.0-ss-win.exe (PID: 3168)
- drwupsrv.exe (PID: 3952)
- dwservice.exe (PID: 4004)
- win-space-setup.exe (PID: 3944)
- dwnetfilter.exe (PID: 2460)
- dwservice.exe (PID: 2324)
- dwarkdaemon.exe (PID: 2756)
- drwupsrv.exe (PID: 3624)
Creates or modifies windows services
- drweb-12.0-ss-win.exe (PID: 3168)
- dwengine.exe (PID: 2144)
- drwupsrv.exe (PID: 3624)
- dwservice.exe (PID: 2324)
Searches for installed software
- win-space-setup.exe (PID: 3944)
Executable content was dropped or overwritten
- drweb-12.0-ss-win.exe (PID: 3168)
- win-space-setup.exe (PID: 3944)
- drwupsrv.exe (PID: 3624)
- dwservice.exe (PID: 2324)
Low-level read access rights to disk partition
- drwupsrv.exe (PID: 3952)
- drwupsrv.exe (PID: 3624)
Creates a software uninstall entry
- drwupsrv.exe (PID: 3624)
Removes files from Windows directory
- dwservice.exe (PID: 2324)
Creates files in the Windows directory
- drwupsrv.exe (PID: 3624)
- dwarkdaemon.exe (PID: 2756)
- dwservice.exe (PID: 2324)
Creates files in the driver directory
- drwupsrv.exe (PID: 3624)
Creates COM task schedule object
- regsvr32.exe (PID: 4068)
- regsvr32.exe (PID: 2904)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 3024)
Application launched itself
- chrome.exe (PID: 3024)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3824)
Dropped object may contain Bitcoin addresses
- drwupsrv.exe (PID: 3624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
28
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000003C0" "00000544" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | "C:\Program Files\DrWeb\spideragent.exe" -register | C:\Program Files\DrWeb\spideragent.exe | win-space-setup.exe | ||||||||||||
User: admin Company: Doctor Web, Ltd. Integrity Level: HIGH Description: SpIDer Agent for Windows Exit code: 0 Version: 12.0.2.11161 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AA494380577D90A2CDEFA9D0D1E41C19 --mojo-platform-channel-handle=988 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Common Files\Doctor Web\Scanning Engine\dwengine.exe" -install:"" | C:\Program Files\Common Files\Doctor Web\Scanning Engine\dwengine.exe | — | drwupsrv.exe | |||||||||||
User: admin Company: Doctor Web, Ltd. Integrity Level: HIGH Description: Dr.Web Scanning Engine Exit code: 0 Version: 12.0.1.11280 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\DrWeb\dwservice.exe" --logfile="C:\ProgramData\Doctor Web\Logs\dwservice.log" | C:\Program Files\DrWeb\dwservice.exe | services.exe | ||||||||||||
User: SYSTEM Company: Doctor Web, Ltd. Integrity Level: SYSTEM Description: Dr.Web Control Service Exit code: 0 Version: 12.0.2.11210 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\DrWeb\dwnetfilter.exe" --ats | C:\Program Files\DrWeb\dwnetfilter.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Doctor Web, Ltd. Integrity Level: SYSTEM Description: Net filtering service Exit code: 0 Version: 12.0.1.10260 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\DrWeb\dwservice.exe" --update -o "C:\ProgramData\Doctor Web\Logs\dwservice.log" | C:\Program Files\DrWeb\dwservice.exe | — | drwupsrv.exe | |||||||||||
User: admin Company: Doctor Web, Ltd. Integrity Level: HIGH Description: Dr.Web Control Service Exit code: 0 Version: 12.0.2.11210 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Common Files\Doctor Web\Scanning Engine\dwarkdaemon.exe" -arkpipe:\pipe\ARServer1549199831 -arkinitflags:93 -sesrvname:DrWebEngine | C:\Program Files\Common Files\Doctor Web\Scanning Engine\dwarkdaemon.exe | dwengine.exe | ||||||||||||
User: SYSTEM Company: Doctor Web, Ltd. Integrity Level: SYSTEM Description: Dr.Web Anti-Rootkit Server Exit code: 0 Version: 12.0.1.11280 Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=79E4F7A4D598143E575939F9828AA17D --mojo-platform-channel-handle=520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2836 | "C:\Users\admin\Downloads\drweb-12.0-ss-win.exe" | C:\Users\admin\Downloads\drweb-12.0-ss-win.exe | — | chrome.exe | |||||||||||
User: admin Company: Doctor Web, Ltd. Integrity Level: MEDIUM Description: Dr.Web Security Space Exit code: 3221226540 Version: 12.0.0.12140 Modules
| |||||||||||||||
Total events
1 880
Read events
1 345
Write events
518
Delete events
17
Modification events
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3024-13193673246224875 |
Value: 259 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3024-13193673246224875 |
Value: 259 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
38
Suspicious files
122
Text files
353
Unknown types
572
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\58dc8277-d57c-4b8a-b261-55a9bf7497c9.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\34440f55-737f-44ae-ac27-3c50a45b0218.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6548138d-470d-40c8-ae95-45d68f5aca7d.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\Downloads\e5ccdf4a-4820-4771-96f4-08b6ba31bbdc.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\Downloads\Unconfirmed 649603.crdownload | — | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3024 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 217.67.177.164:443 | download.geo.drweb.com | JSC Mastertel | RU | unknown |
3024 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.23.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
download.geo.drweb.com |
| suspicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |