| File name: | as.exe |
| Full analysis: | https://app.any.run/tasks/2f7fd1c1-0eaf-4998-978e-e0583a4930b7 |
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2021, 02:22:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 91E68FA8E4C75B83E5404ED1A14953CF |
| SHA1: | 532530AC30275F7F793D8464510D23F321597C91 |
| SHA256: | 9EBF7C257CC8CEB87CB9549B105908B2B584834E7A825A5D74657AAF5C0FA972 |
| SSDEEP: | 192:9591g+lBW5B5pr5aIbsPfA9+8stYcFASVc03KY:9z1PBipr57AfA9+ptYcFASVc03K |
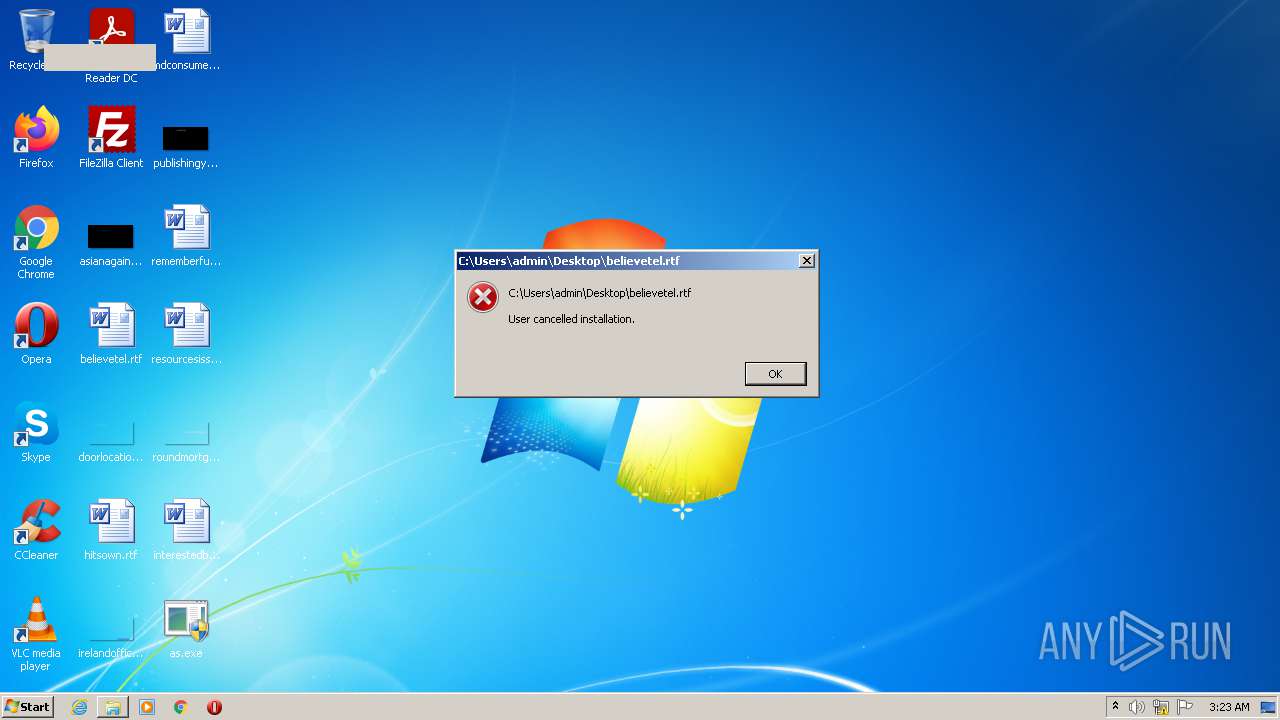
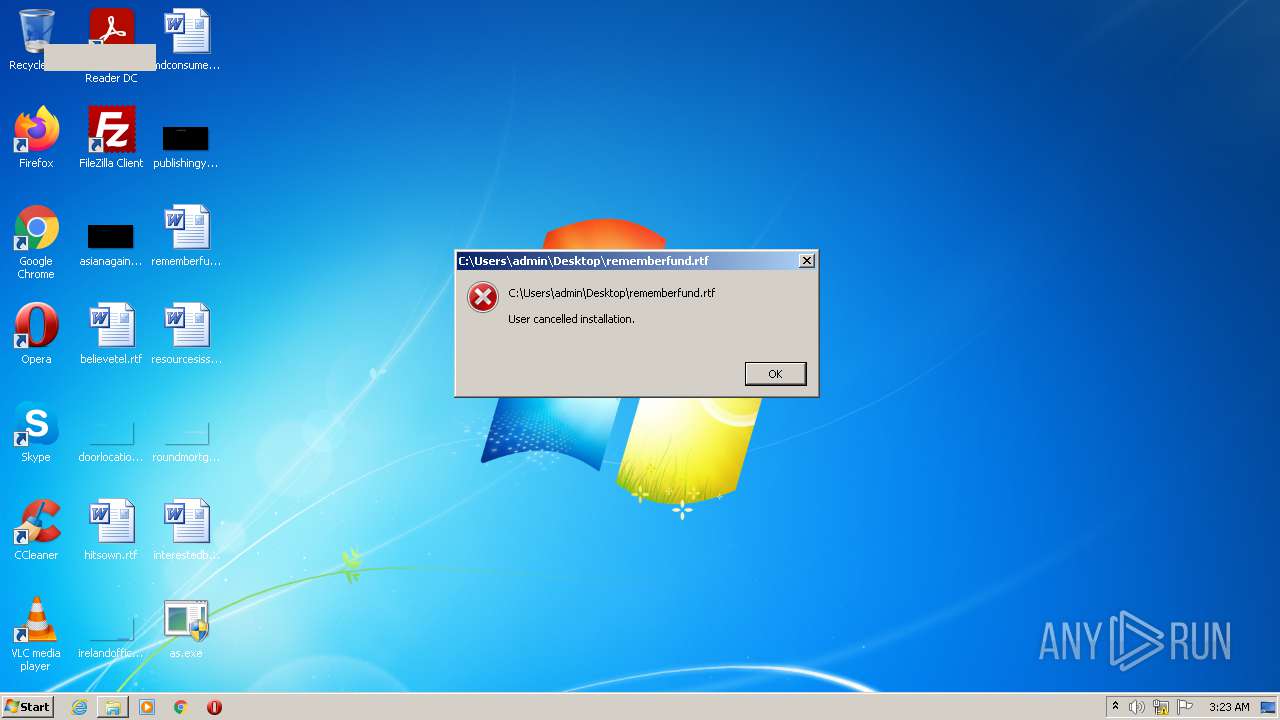
MALICIOUS
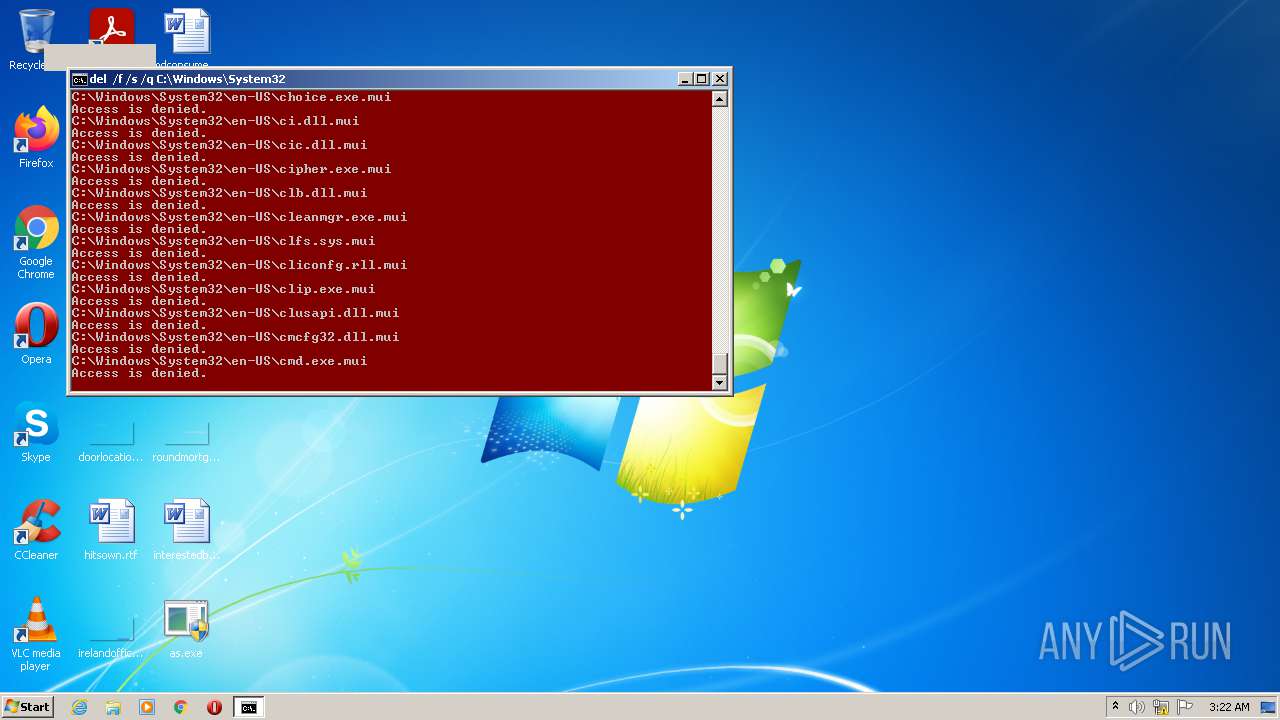
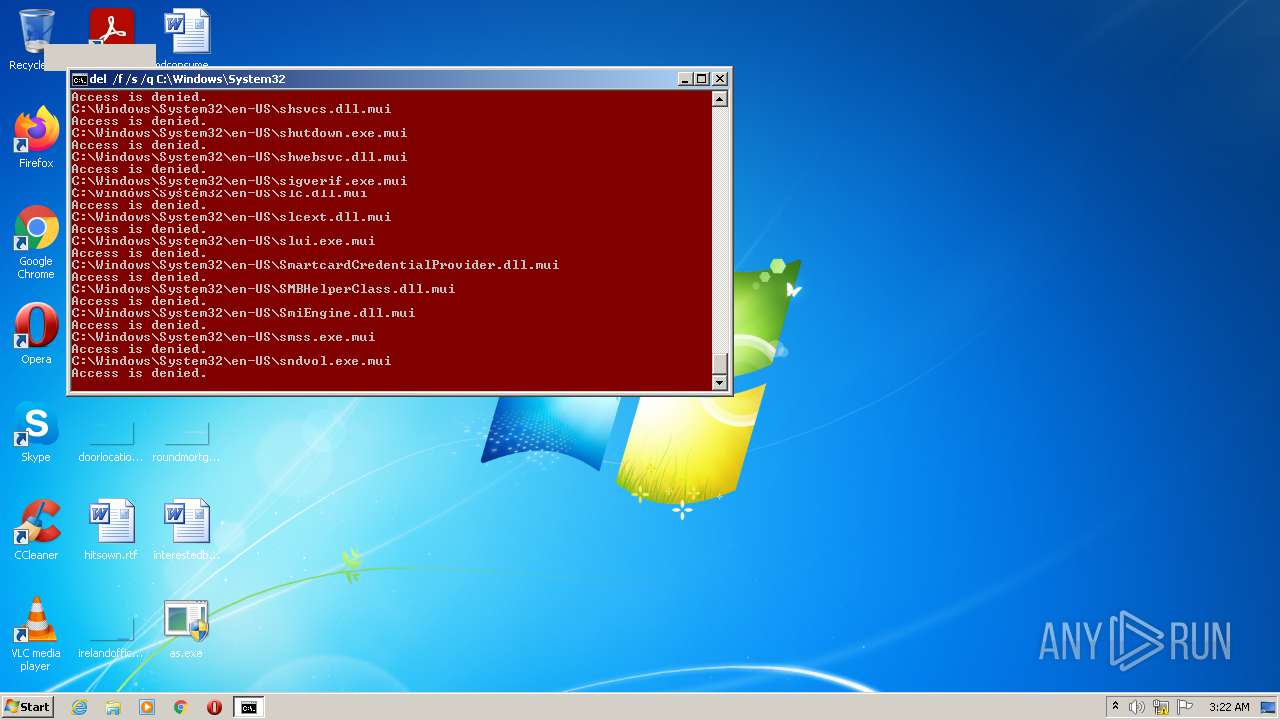
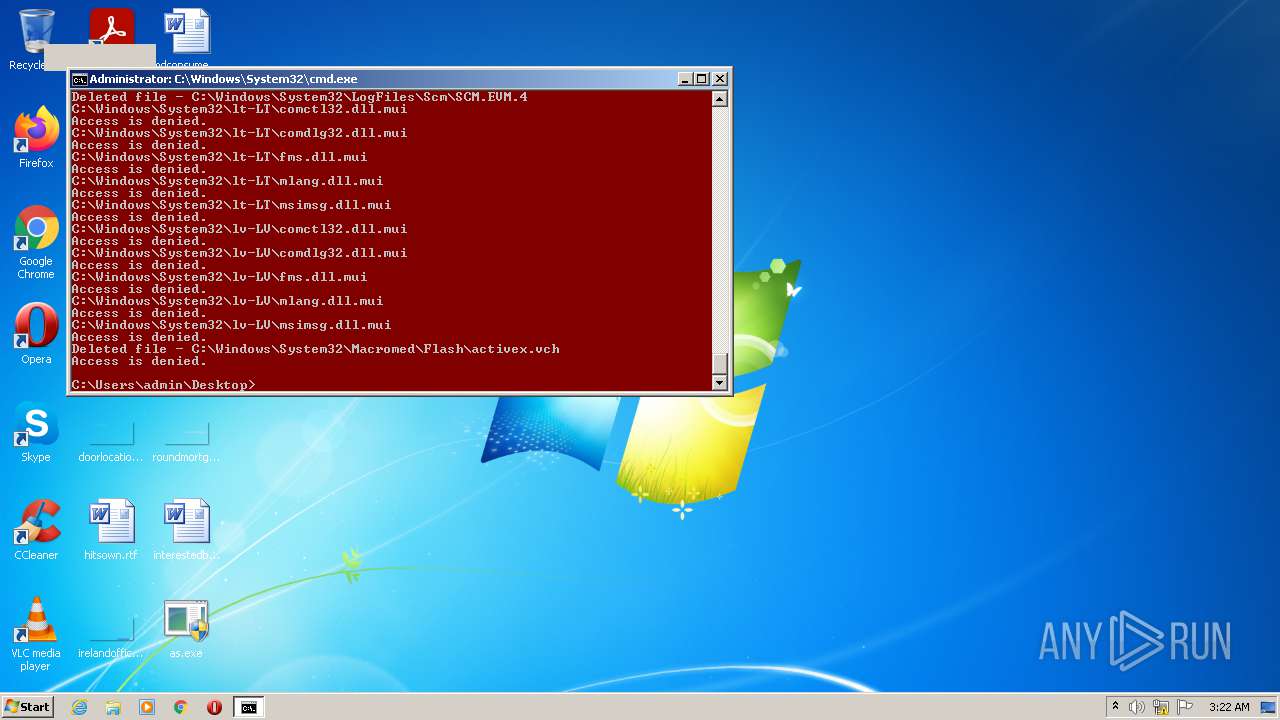
Tries to delete the host file
- cmd.exe (PID: 2660)
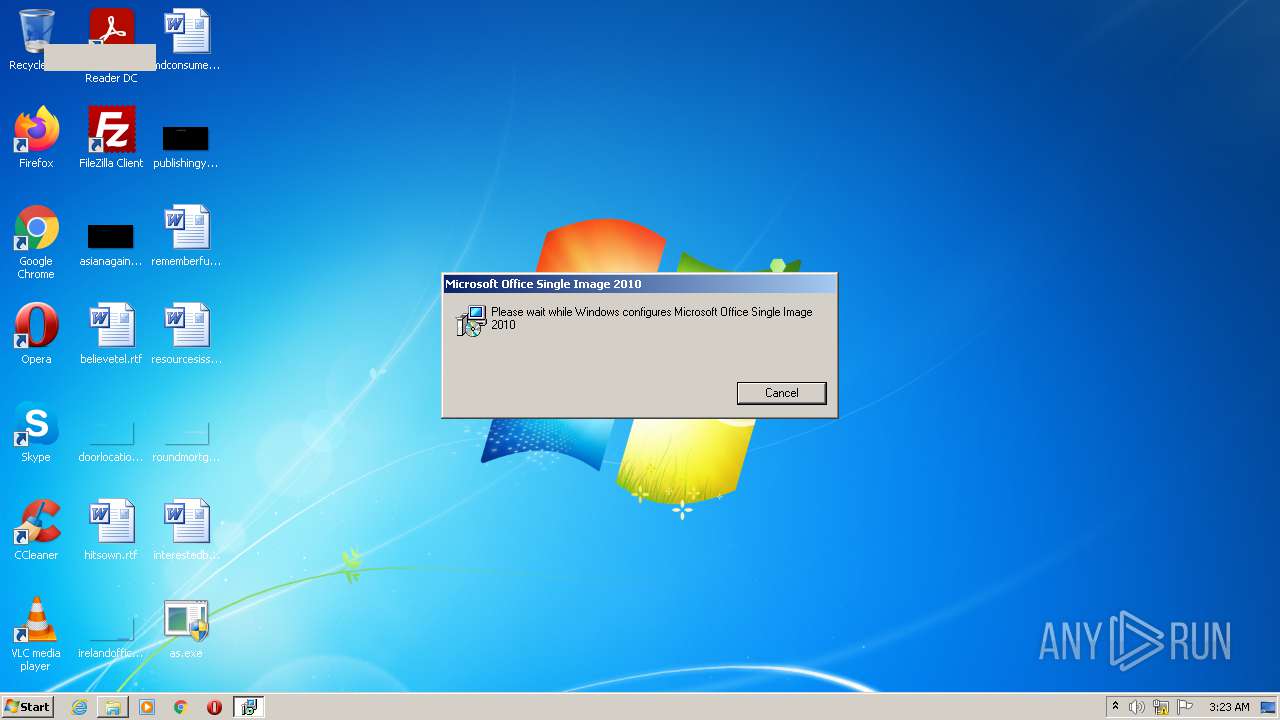
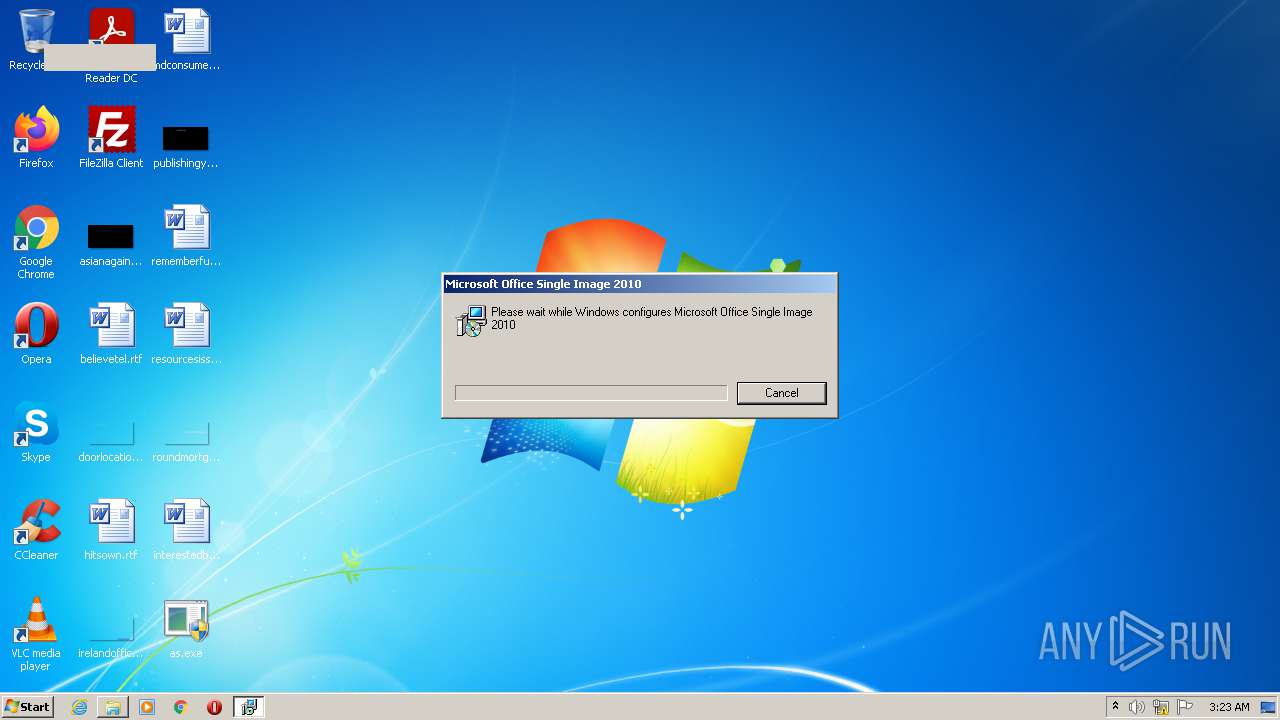
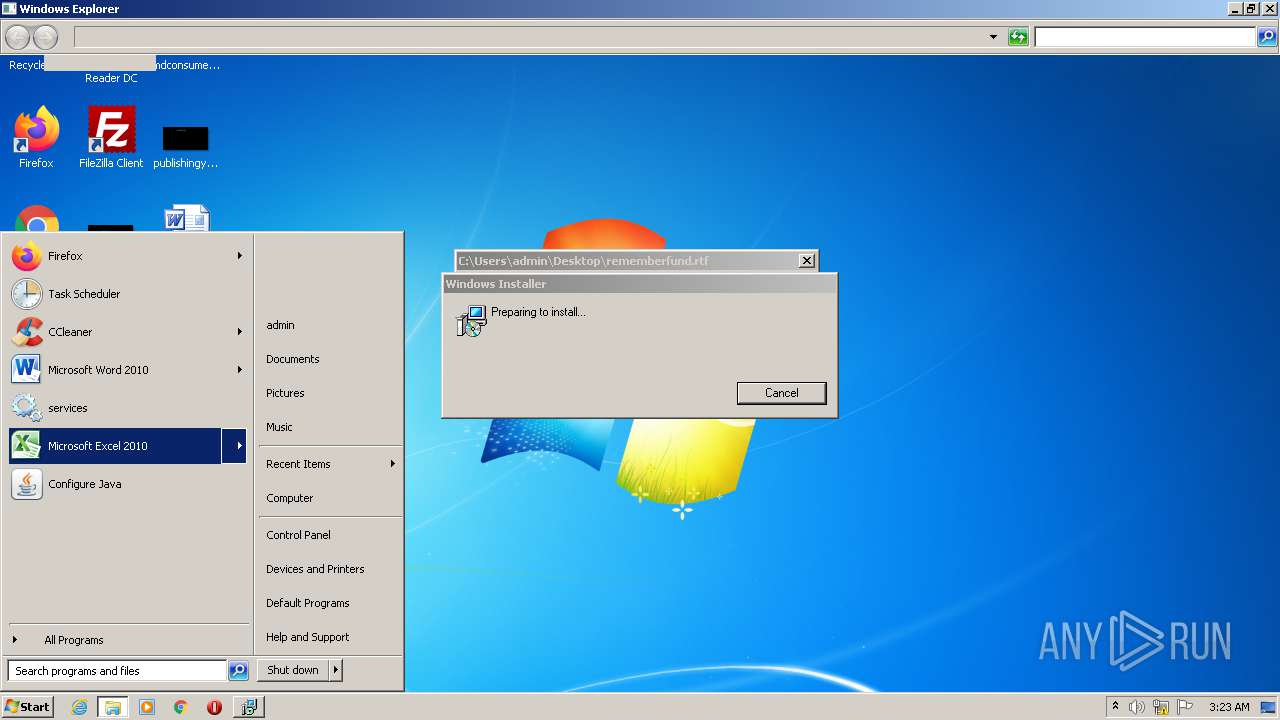
Drops executable file immediately after starts
- msiexec.exe (PID: 3468)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3456)
- msiexec.exe (PID: 3468)
- MsiExec.exe (PID: 656)
- MsiExec.exe (PID: 1448)
- MsiExec.exe (PID: 3176)
- MsiExec.exe (PID: 3688)
- MsiExec.exe (PID: 2472)
SUSPICIOUS
Starts CMD.EXE for commands execution
- as.exe (PID: 1052)
Checks supported languages
- as.exe (PID: 1052)
- cmd.exe (PID: 2660)
Reads the computer name
- as.exe (PID: 1052)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 2660)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3468)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 3468)
- MsiExec.exe (PID: 1448)
- MsiExec.exe (PID: 3176)
- MsiExec.exe (PID: 3456)
Searches for installed software
- msiexec.exe (PID: 3468)
Drops a file with too old compile date
- MsiExec.exe (PID: 3456)
- msiexec.exe (PID: 3468)
- MsiExec.exe (PID: 1448)
- MsiExec.exe (PID: 3176)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3468)
- MsiExec.exe (PID: 3456)
- MsiExec.exe (PID: 1448)
- MsiExec.exe (PID: 3176)
Creates files in the program directory
- MsiExec.exe (PID: 656)
- MsiExec.exe (PID: 2472)
- MsiExec.exe (PID: 3688)
Changes default file association
- msiexec.exe (PID: 3468)
Application launched itself
- msiexec.exe (PID: 3468)
Reads the Windows organization settings
- msiexec.exe (PID: 3468)
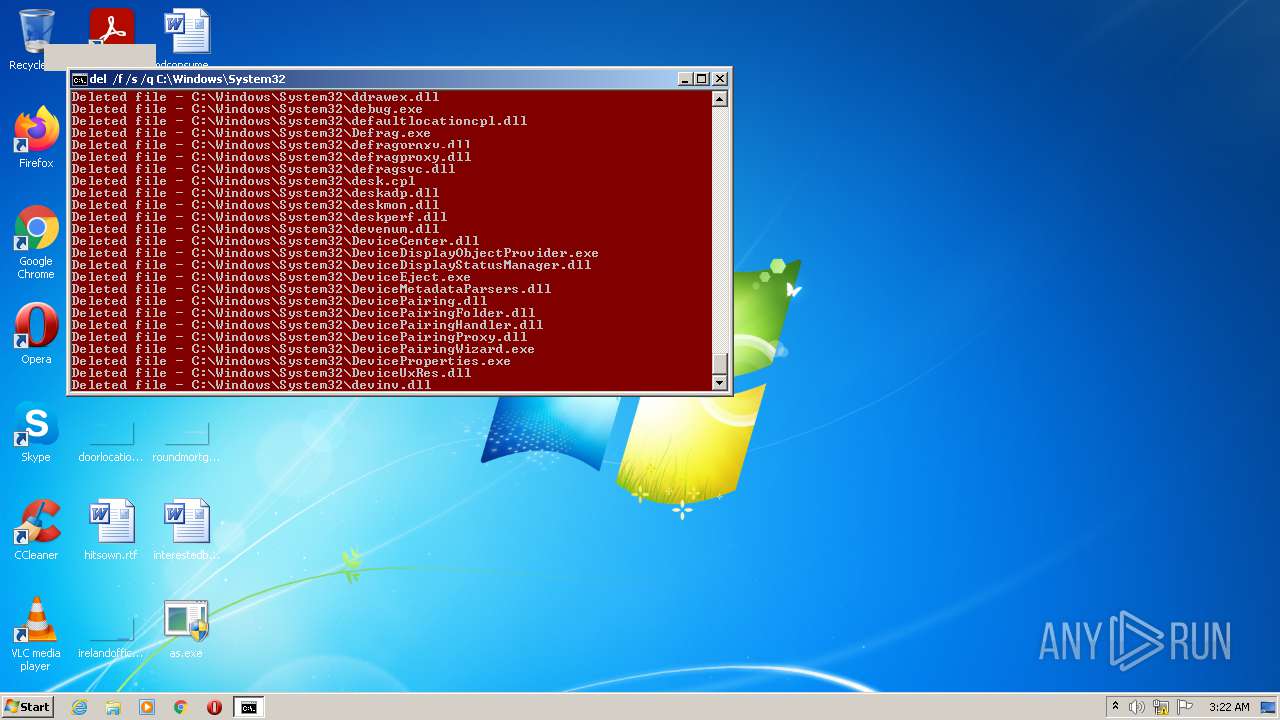
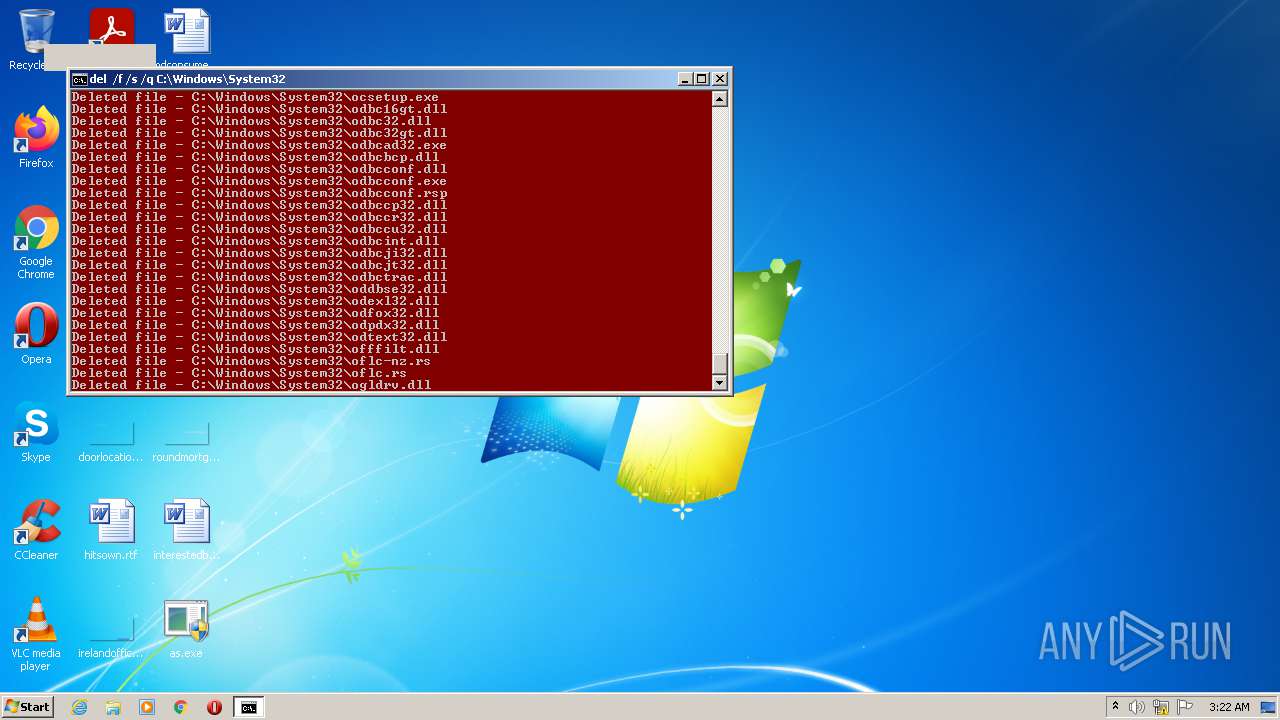
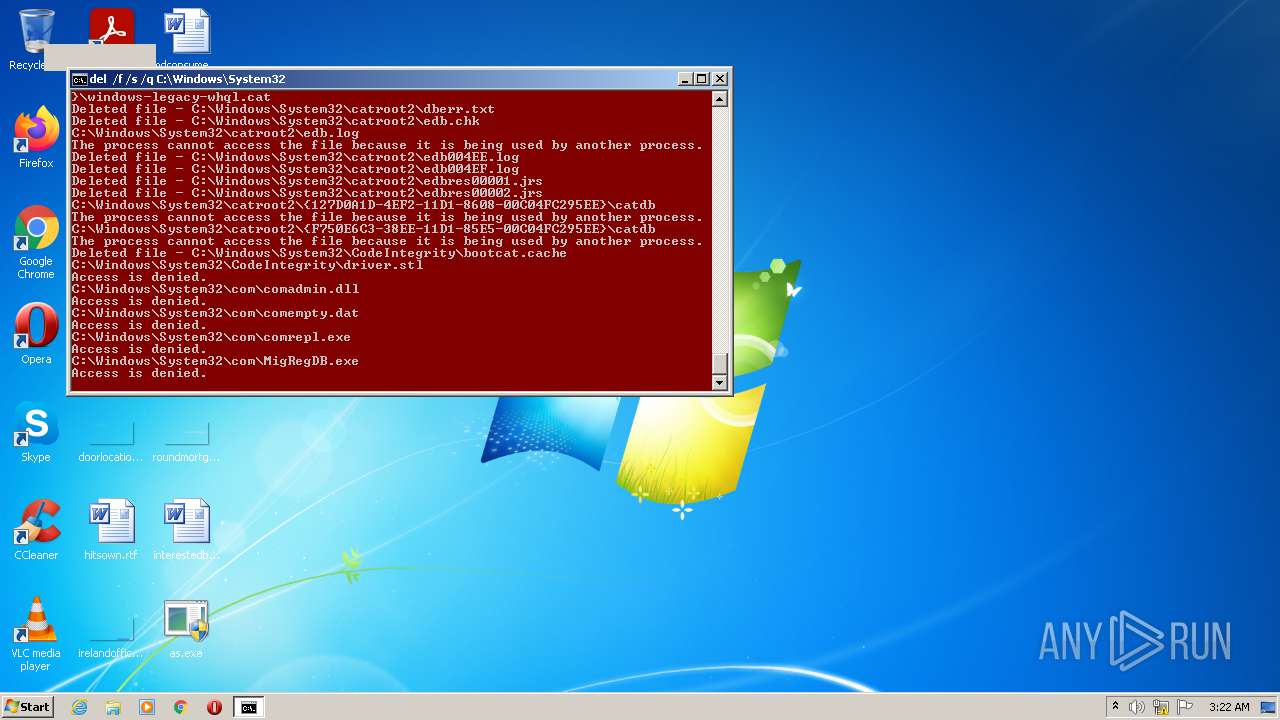
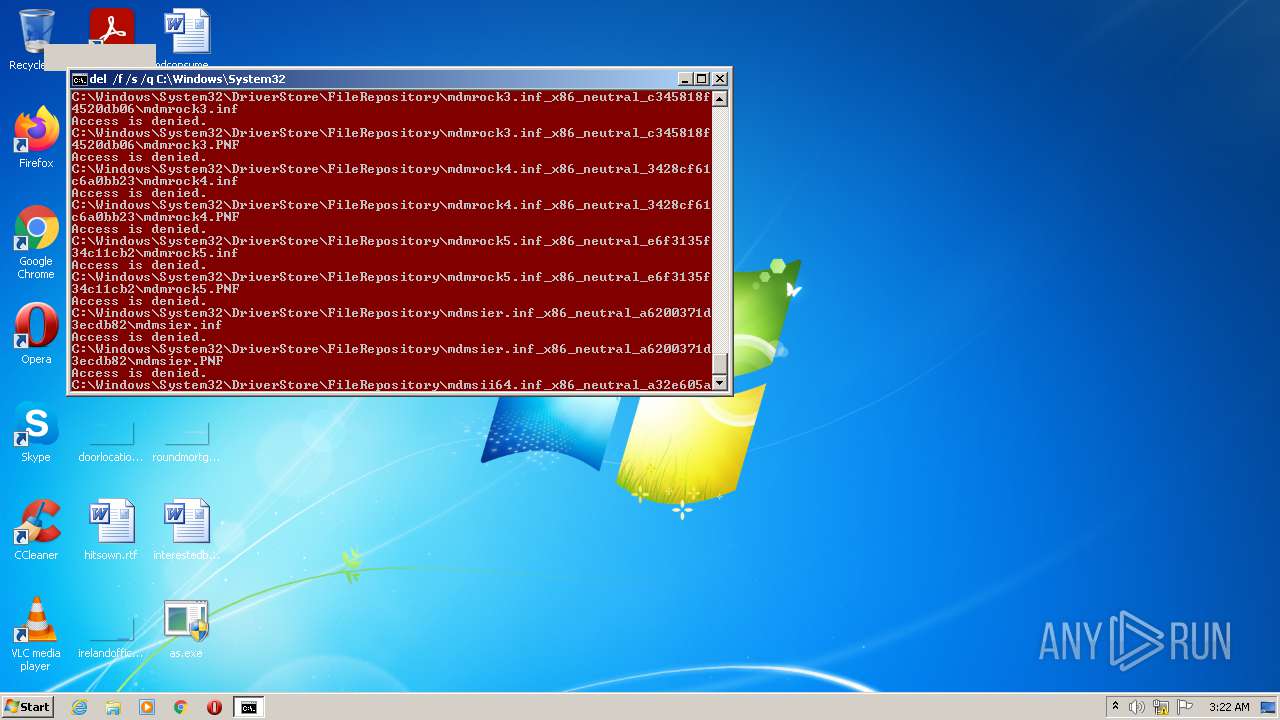
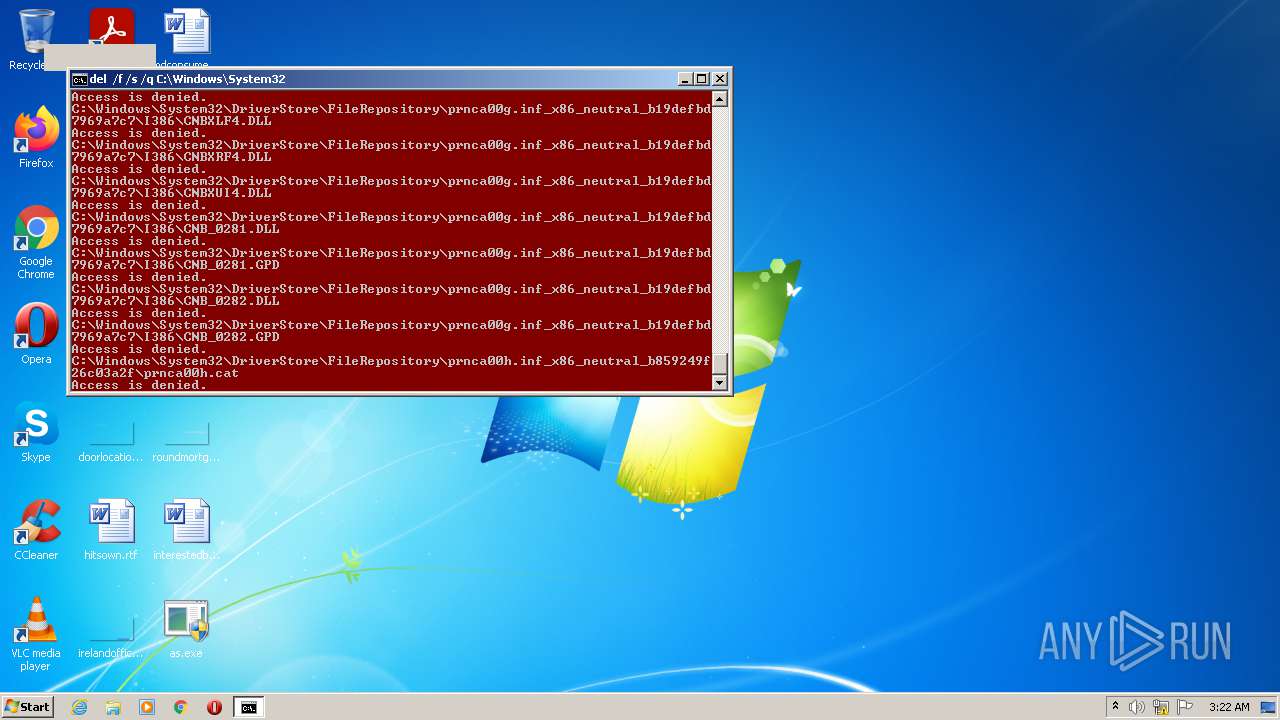
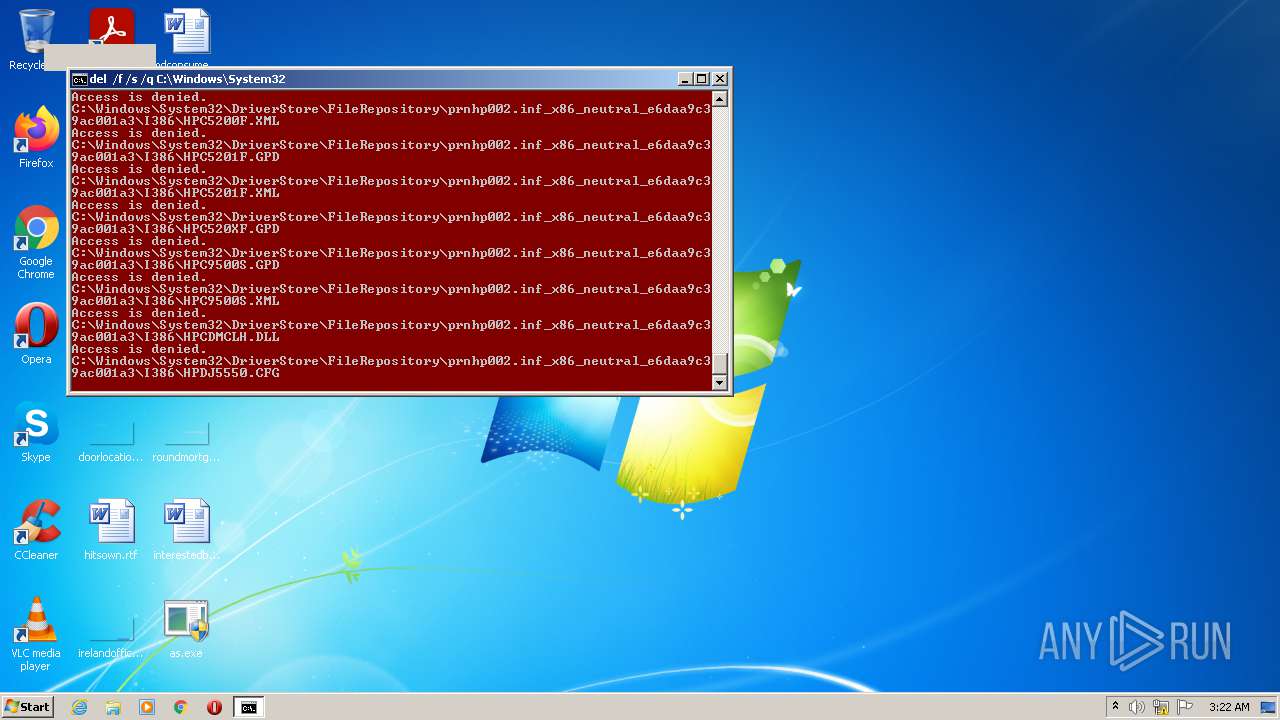
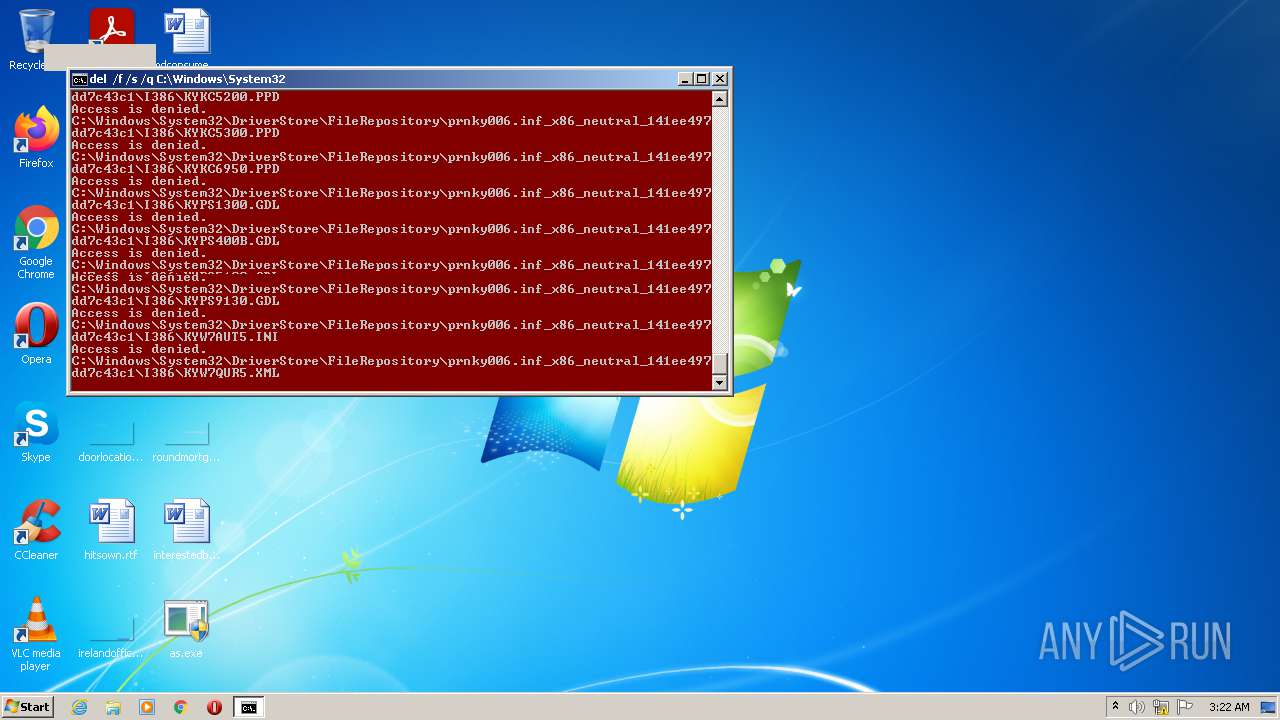
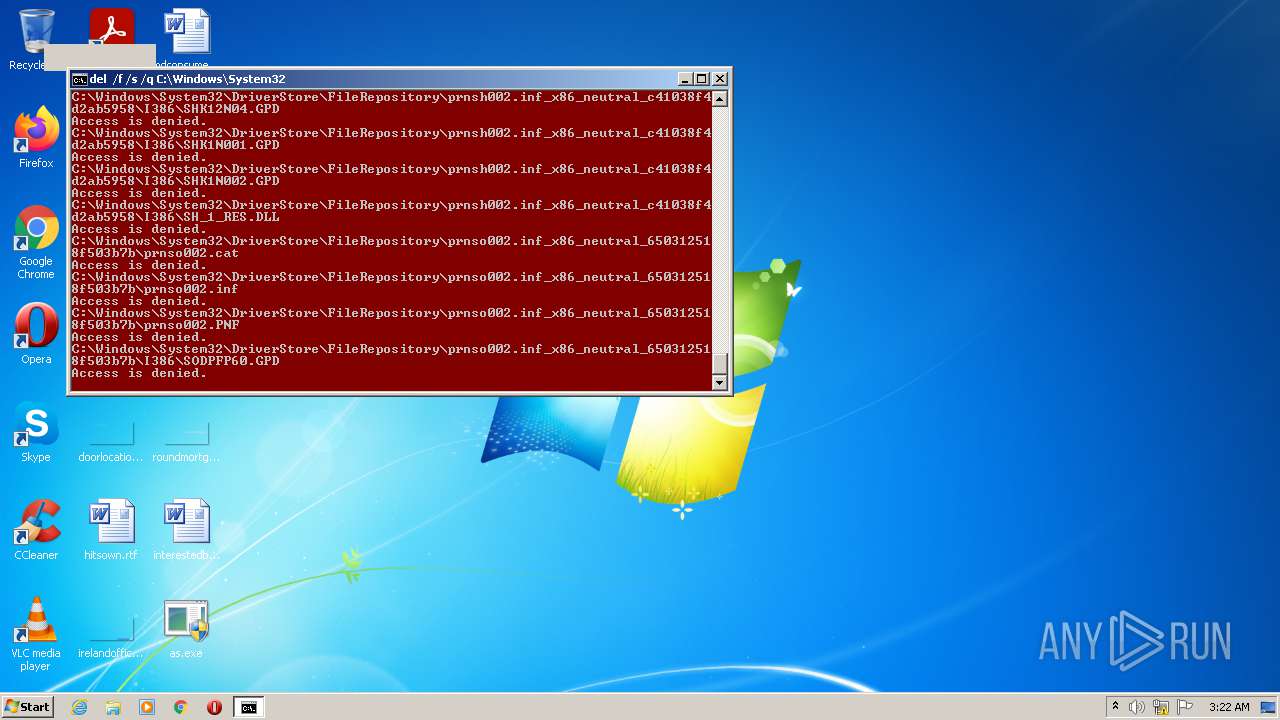
Removes files from Windows directory
- cmd.exe (PID: 2660)
INFO
Reads the computer name
- takeown.exe (PID: 2828)
- icacls.exe (PID: 2832)
- takeown.exe (PID: 3648)
- icacls.exe (PID: 3684)
- explorer.exe (PID: 2364)
- MsiExec.exe (PID: 3456)
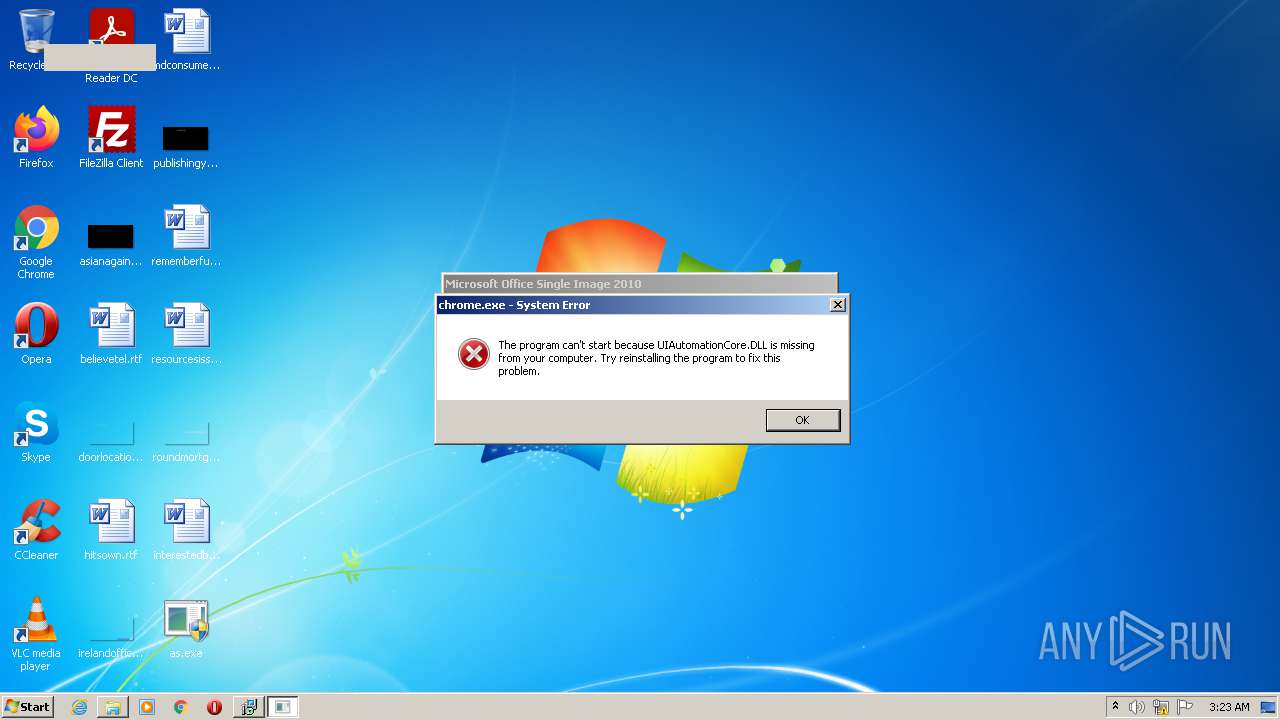
- chrome.exe (PID: 3548)
- MsiExec.exe (PID: 656)
- MsiExec.exe (PID: 1448)
- MsiExec.exe (PID: 2472)
- MsiExec.exe (PID: 3688)
- MsiExec.exe (PID: 3176)
Checks supported languages
- takeown.exe (PID: 2828)
- icacls.exe (PID: 3684)
- icacls.exe (PID: 2832)
- takeown.exe (PID: 3648)
- msiexec.exe (PID: 3468)
- explorer.exe (PID: 2364)
- MsiExec.exe (PID: 3456)
- chrome.exe (PID: 3548)
- MsiExec.exe (PID: 656)
- chrome.exe (PID: 1288)
- MsiExec.exe (PID: 1448)
- MsiExec.exe (PID: 2472)
- MsiExec.exe (PID: 3176)
- MsiExec.exe (PID: 3688)
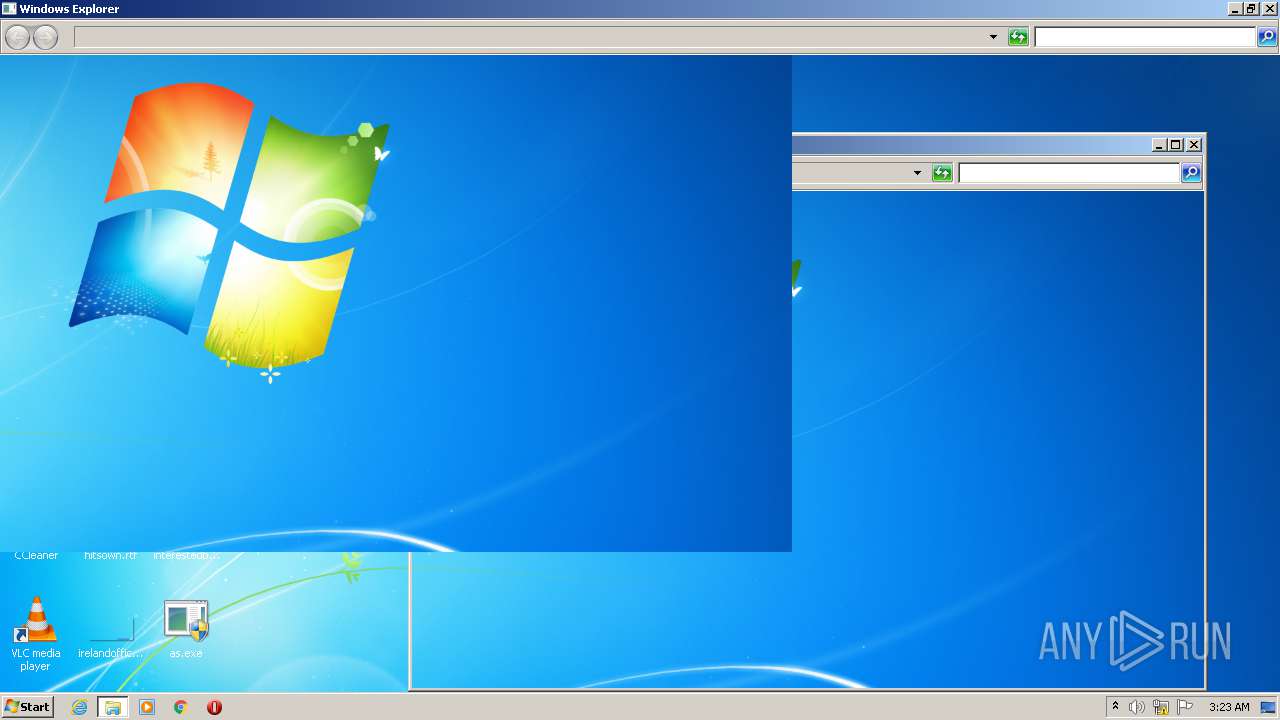
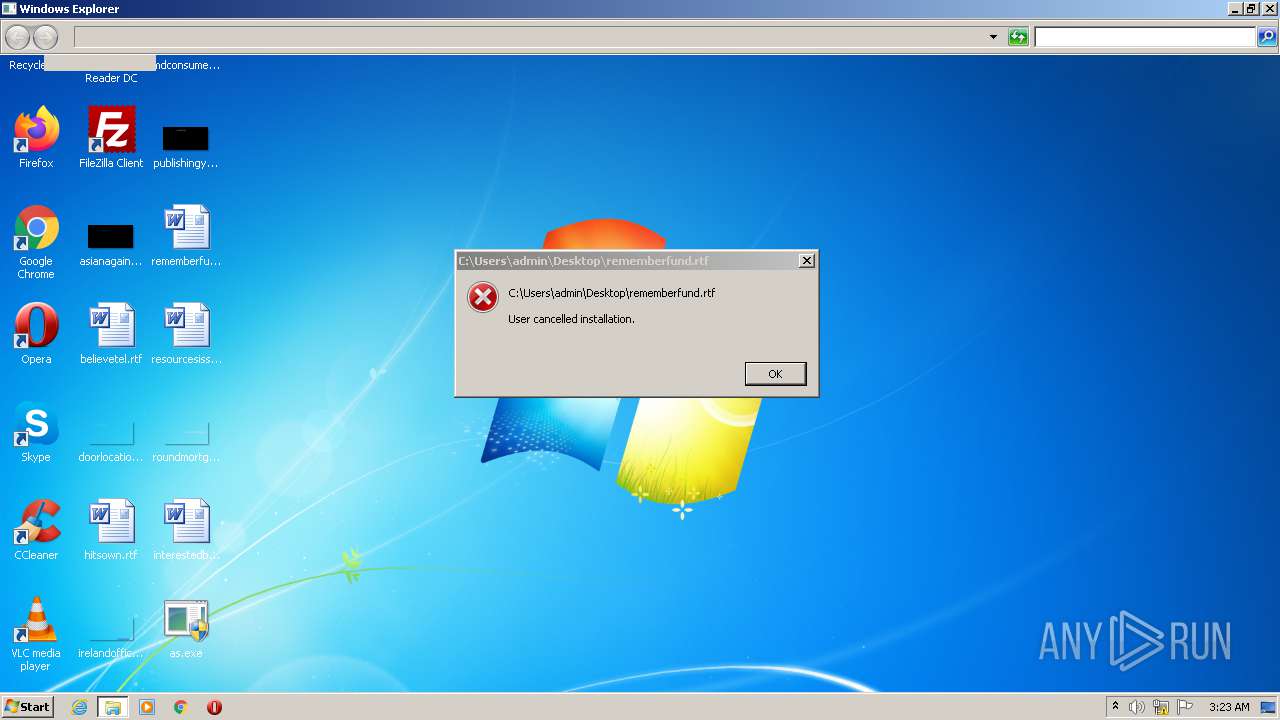
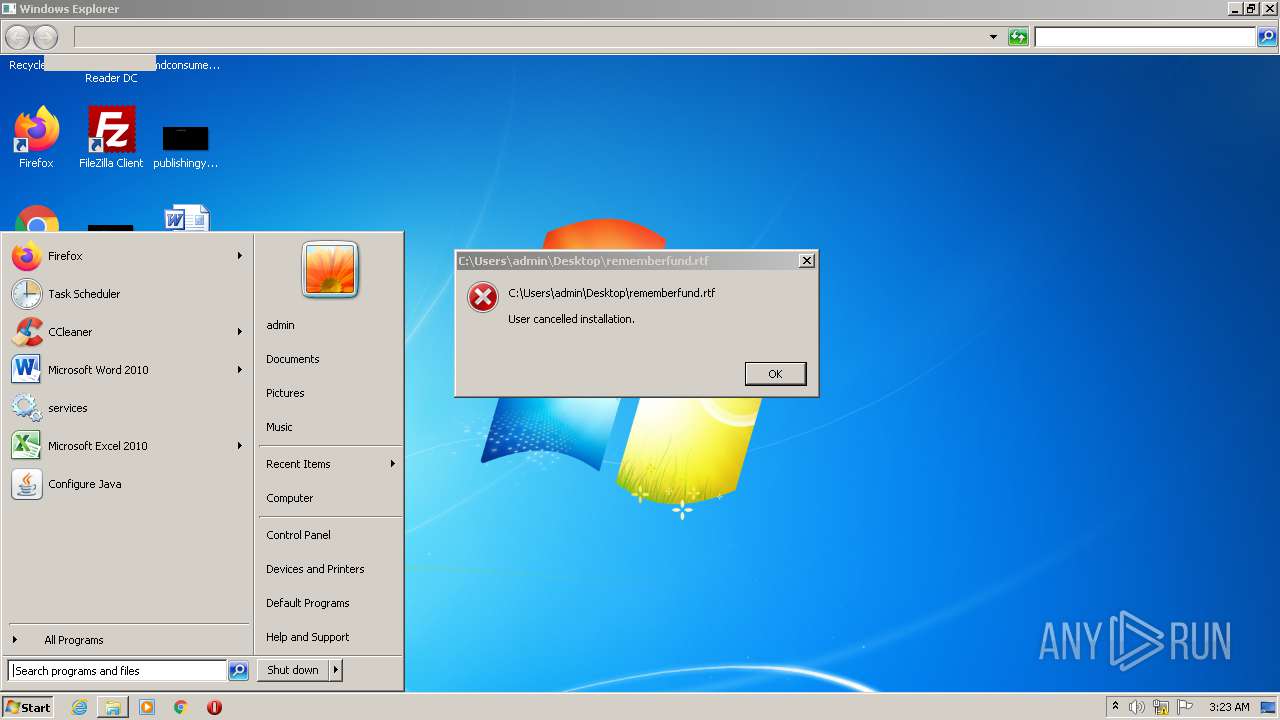
Manual execution by user
- chrome.exe (PID: 3548)
- explorer.exe (PID: 2364)
Reads Microsoft Office registry keys
- msiexec.exe (PID: 3468)
- MsiExec.exe (PID: 3456)
- MsiExec.exe (PID: 1448)
- MsiExec.exe (PID: 3176)
Application launched itself
- chrome.exe (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | as |
| OriginalFileName: | as.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2021 |
| InternalName: | as.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | as |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x3426 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4608 |
| CodeSize: | 5632 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2087:07:17 21:42:03+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Jun-1951 13:13:47 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | as |
| FileVersion: | 1.0.0.0 |
| InternalName: | as.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | as.exe |
| ProductName: | as |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 11-Jun-1951 13:13:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0000142C | 0x00001600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.09555 |
.rsrc | 0x00004000 | 0x00000FEC | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04767 |
.reloc | 0x00006000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01754 | 3161 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
54
Monitored processes
17
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Users\admin\Desktop\as.exe" | C:\Users\admin\Desktop\as.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: as Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 656 | C:\Windows\system32\MsiExec.exe -Embedding A75C29F1DFC9C60F85866AA1D07686E2 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1052 | "C:\Users\admin\Desktop\as.exe" | C:\Users\admin\Desktop\as.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: as Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6a5dd988,0x6a5dd998,0x6a5dd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1448 | C:\Windows\system32\MsiExec.exe -Embedding FEB1C0A49B0DFCFC9511185F9F81AA9F | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | C:\Windows\system32\MsiExec.exe -Embedding C7A089E96EC1EF15220031CC8C01B2F3 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | "C:\Windows\System32\cmd.exe" /k color 47 && takeown /f C:\Windows\System32 && icacls C:\Windows\System32 /grant %username%:F && takeown /f C:\Windows\System32\drivers && icacls C:\Windows\System32\drivers /grant %username%:F && del /f /s /q C:\Windows\System32 && Exit | C:\Windows\System32\cmd.exe | — | as.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2828 | takeown /f C:\Windows\System32 | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2832 | icacls C:\Windows\System32 /grant admin:F | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 392
Read events
10 054
Write events
263
Delete events
75
Modification events
| (PID) Process: | (1052) as.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1052) as.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1052) as.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1052) as.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3468) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 8C0D000003FE7DA14C67D701 | |||
| (PID) Process: | (3468) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 0F234E3281BF049CBD283E07B984B419D47FCF40BF960FCAAAC5828BB4211CD4 | |||
| (PID) Process: | (3468) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3468) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | (default) |
Value: C:\Windows\Installer\fb254.ipi | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
93
Suspicious files
11
Text files
0
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | msiexec.exe | C:\Windows\Installer\MSI4466.tmp | executable | |
MD5:B725ED06D71DAAB1B944F500481C96BE | SHA256:506A9B72C2C1C10C21E95DAE471E5A7EE27479495D8B0F71BC563BBE3D02EB91 | |||
| 3468 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFE69D2E00277E3AEC.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3468 | msiexec.exe | C:\Windows\Installer\MSI4210.tmp | executable | |
MD5:B725ED06D71DAAB1B944F500481C96BE | SHA256:506A9B72C2C1C10C21E95DAE471E5A7EE27479495D8B0F71BC563BBE3D02EB91 | |||
| 3468 | msiexec.exe | C:\Windows\Installer\MSI40F1.tmp | executable | |
MD5:81511E09AE2A522A8BE16891BA657302 | SHA256:8DEE9A3335A9BE4114AA544BA361A4508CFCD0320121E4C6A30849EAA9E031B8 | |||
| 3468 | msiexec.exe | C:\Windows\Installer\MSI4200.tmp | executable | |
MD5:81511E09AE2A522A8BE16891BA657302 | SHA256:8DEE9A3335A9BE4114AA544BA361A4508CFCD0320121E4C6A30849EAA9E031B8 | |||
| 3468 | msiexec.exe | C:\Windows\Installer\MSI461C.tmp | executable | |
MD5:CB6AAB53E5D4893327ADE765CFF283F2 | SHA256:A0DBBA68F7B3FBFF7FE368F5478AE60D2D840158ED0E70FF0A1C48C305D8F986 | |||
| 3468 | msiexec.exe | C:\Windows\Installer\MSI4160.tmp | executable | |
MD5:9CADBFA797783FF9E7FC60301DE9E1FF | SHA256:C1EDA5C42BE64CFC08408A276340C9082F424EC1A4E96E78F85E9F80D0634141 | |||
| 3468 | msiexec.exe | C:\Windows\Installer\MSI4446.tmp | executable | |
MD5:9CAF5E1999A4BD6AB8C4D4EA07818A7D | SHA256:813EBC09BB3144D76F6F3A1550877C21590E0776F893915CA1178672E84CA1E7 | |||
| 3456 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\Hx4DEE.tmp | executable | |
MD5:23FDB0C309E188A5E3C767F8FC557D83 | SHA256:1A0F889CA5FFA151CCD8D4C210682C33C567E20DB50E9091E664D9493D2B3980 | |||
| 3468 | msiexec.exe | C:\Windows\Installer\MSI4241.tmp | executable | |
MD5:8D4C7E2792F92D8E7CBA3098A54C8E66 | SHA256:AAF3E53A1A1AEADAC1339B20E256EABC29502A9A583A7C18B29D6BBA2ADB1AB0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report