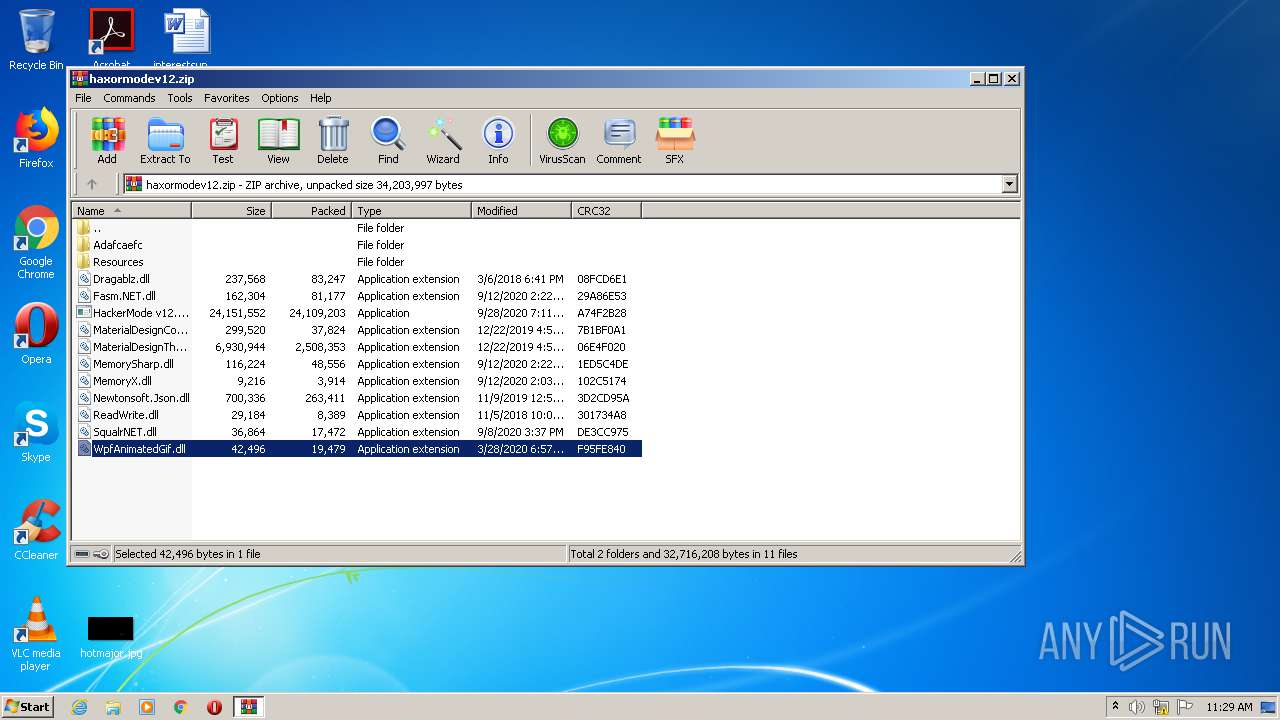
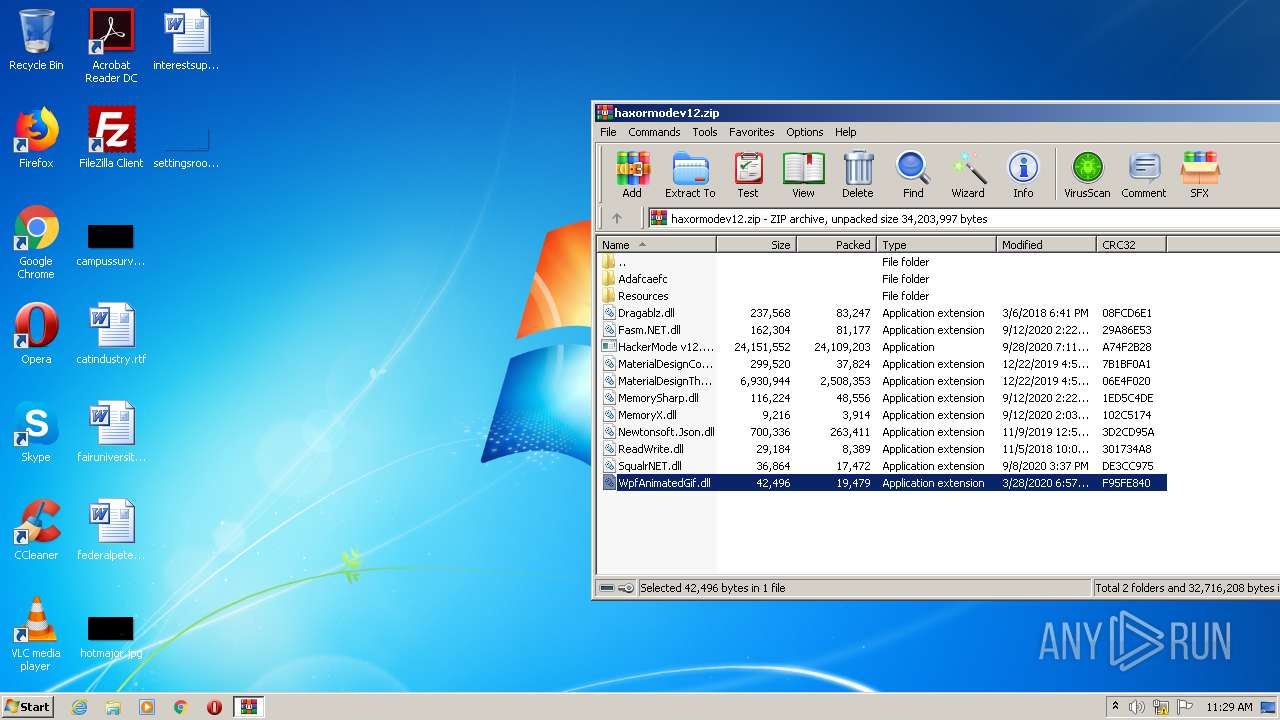
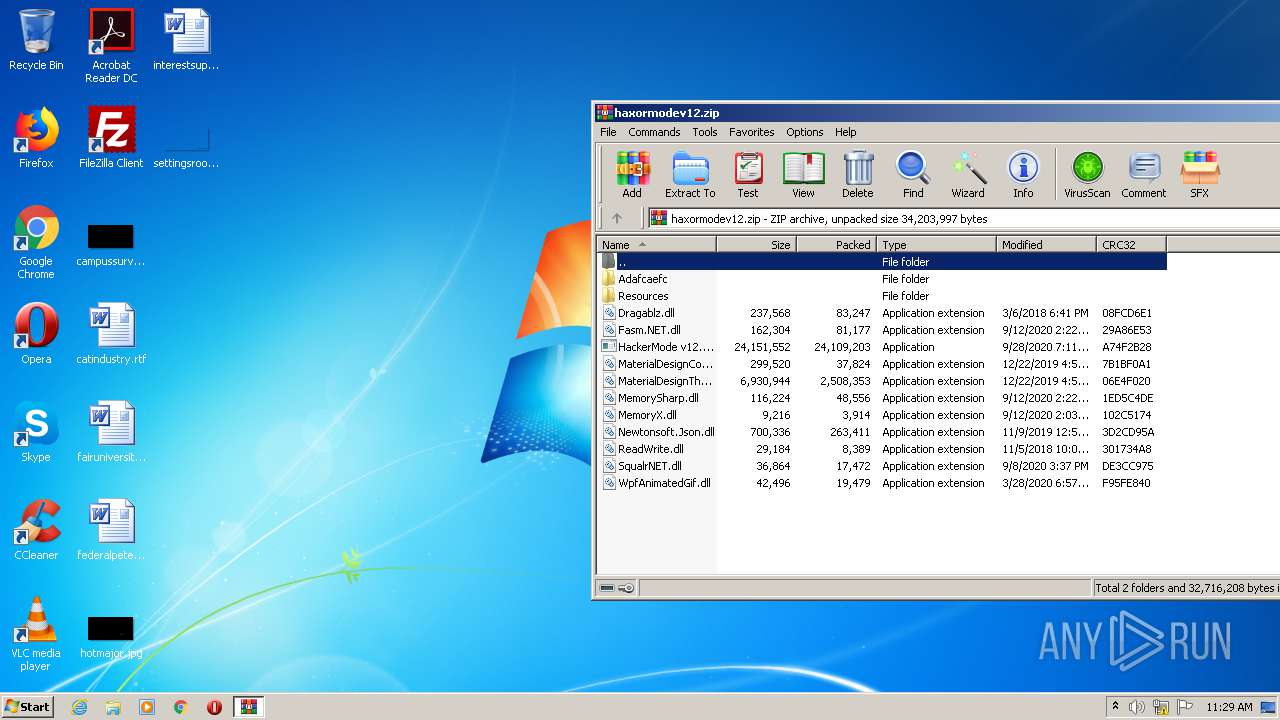
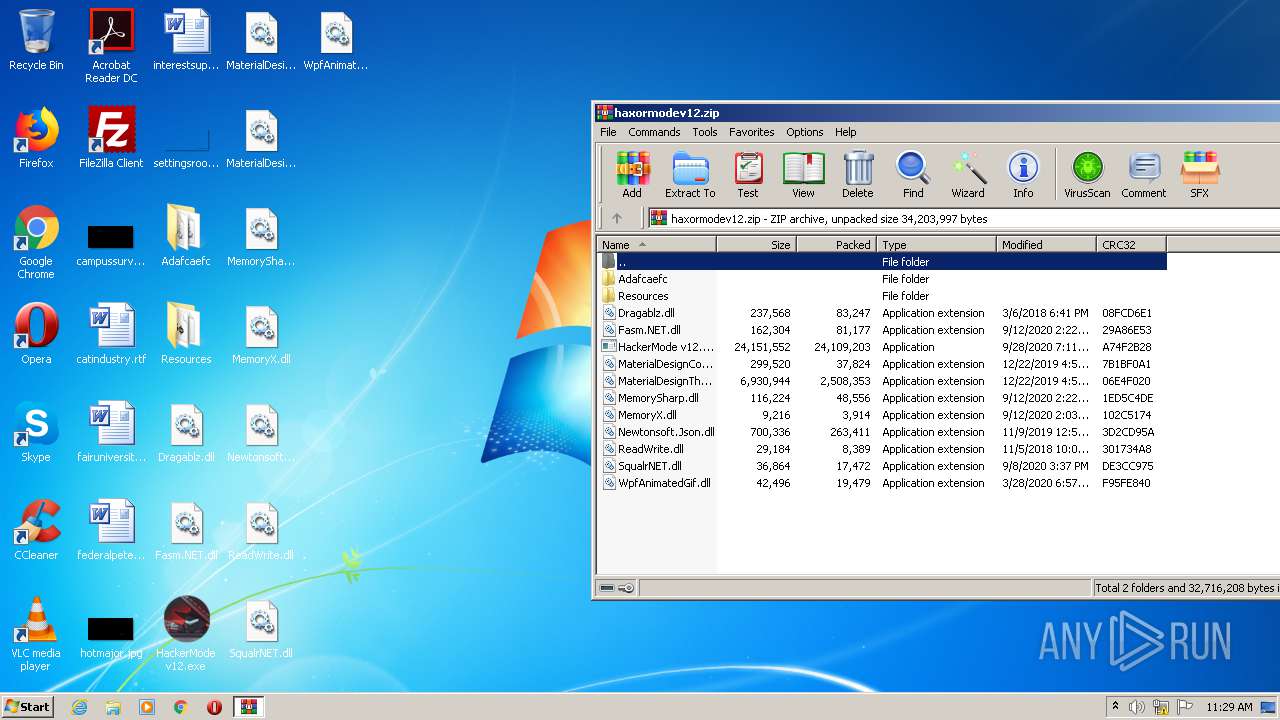
| download: | haxormodev12.zip |
| Full analysis: | https://app.any.run/tasks/26b6208c-3dcd-4fbb-8eda-aaf987e5f4d6 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 10:28:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
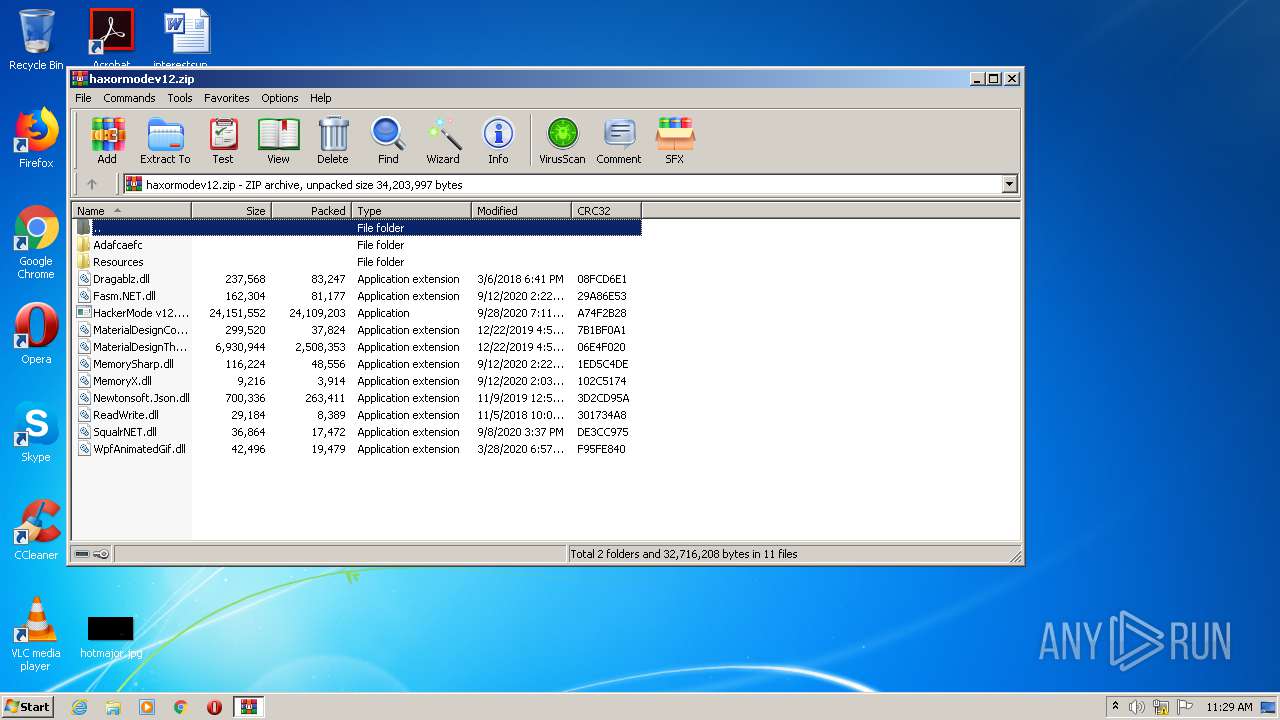
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 029288BE4CE222E44901ECEBF199AD91 |
| SHA1: | 5300D3BDC48322C4EB62C778D91E379BD47B721D |
| SHA256: | 9EAA334B0B2FE3F1EDAD2E70EEBBDC868BC3E4684BEEA5EA6494E98C2FB31560 |
| SSDEEP: | 786432:DsWkW8/M3PE86KtKh4+mSH9nMsnPB+eZPY:AWkWdfEeKh7VMsnPQ4Q |
MALICIOUS
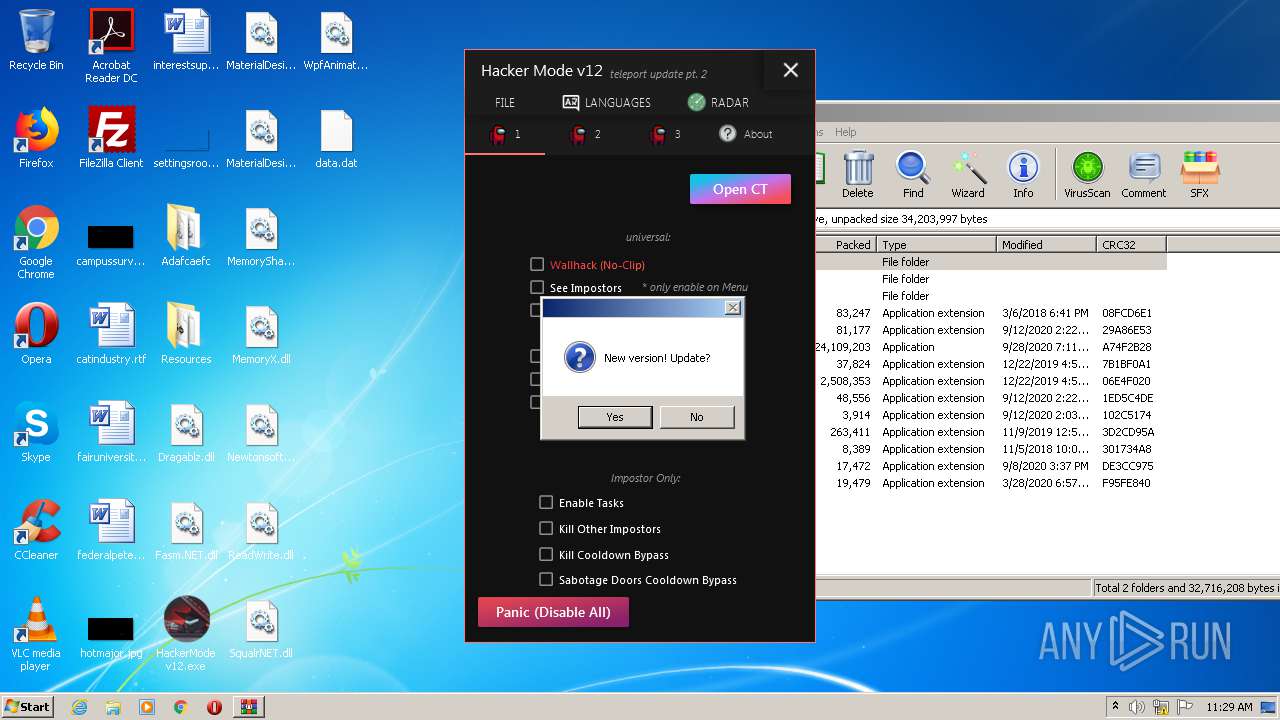
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3056)
- HackerMode v12.exe (PID: 4092)
Application was dropped or rewritten from another process
- HackerMode v12.exe (PID: 4092)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3400)
Reads Environment values
- HackerMode v12.exe (PID: 4092)
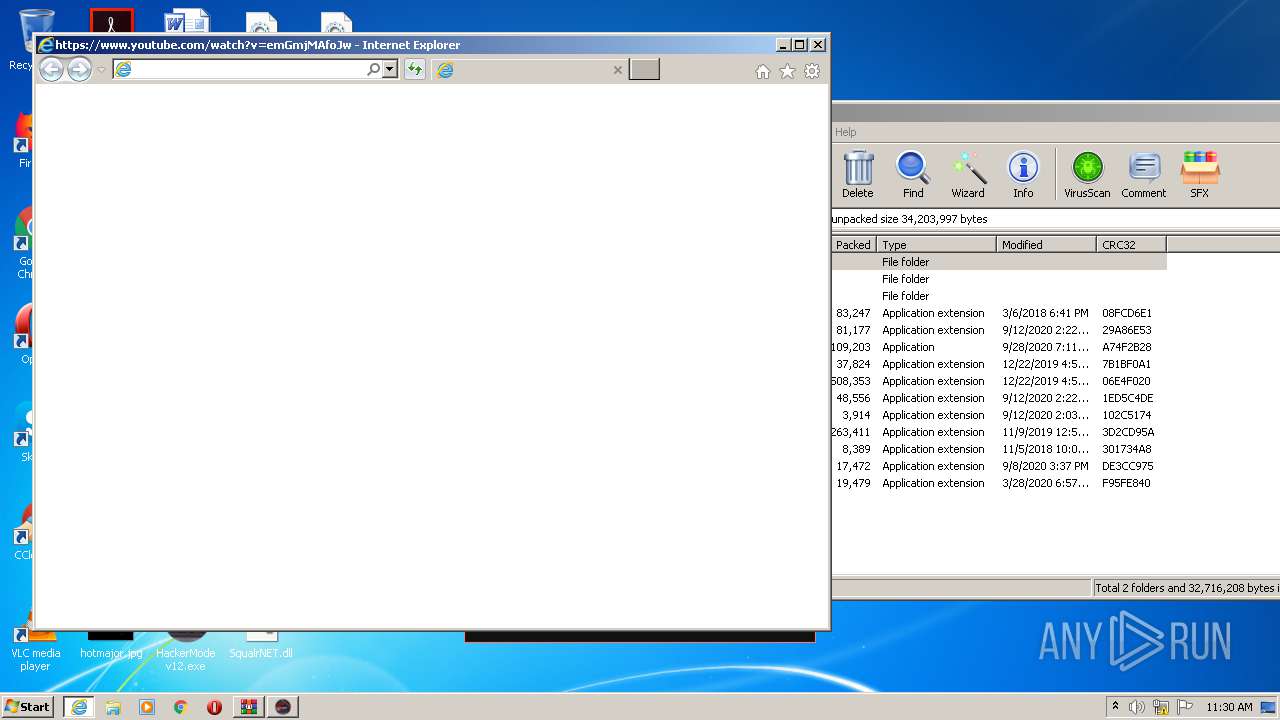
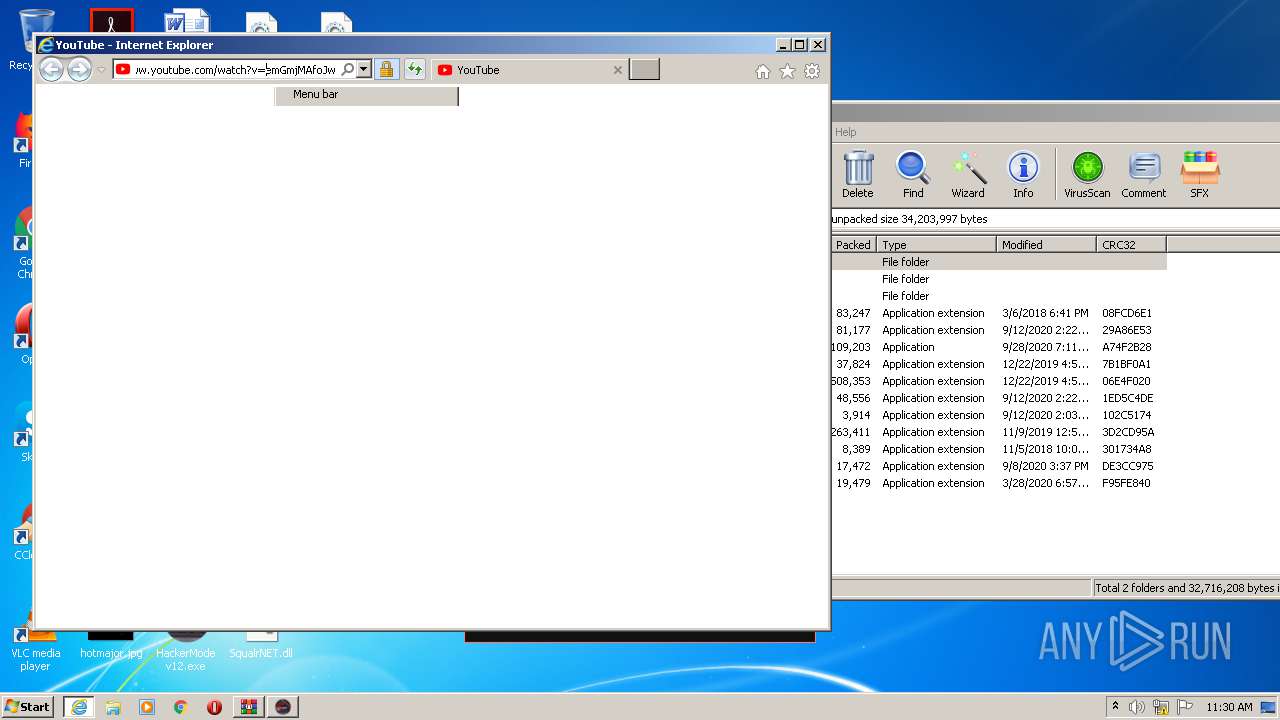
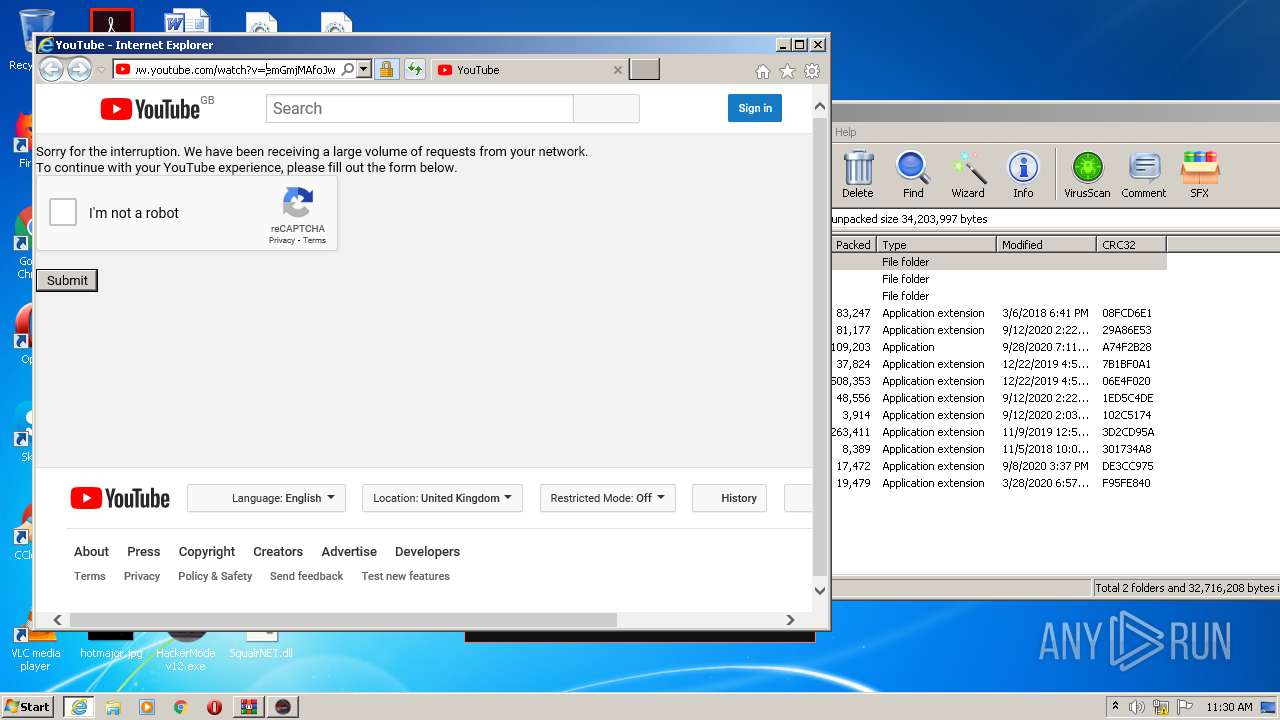
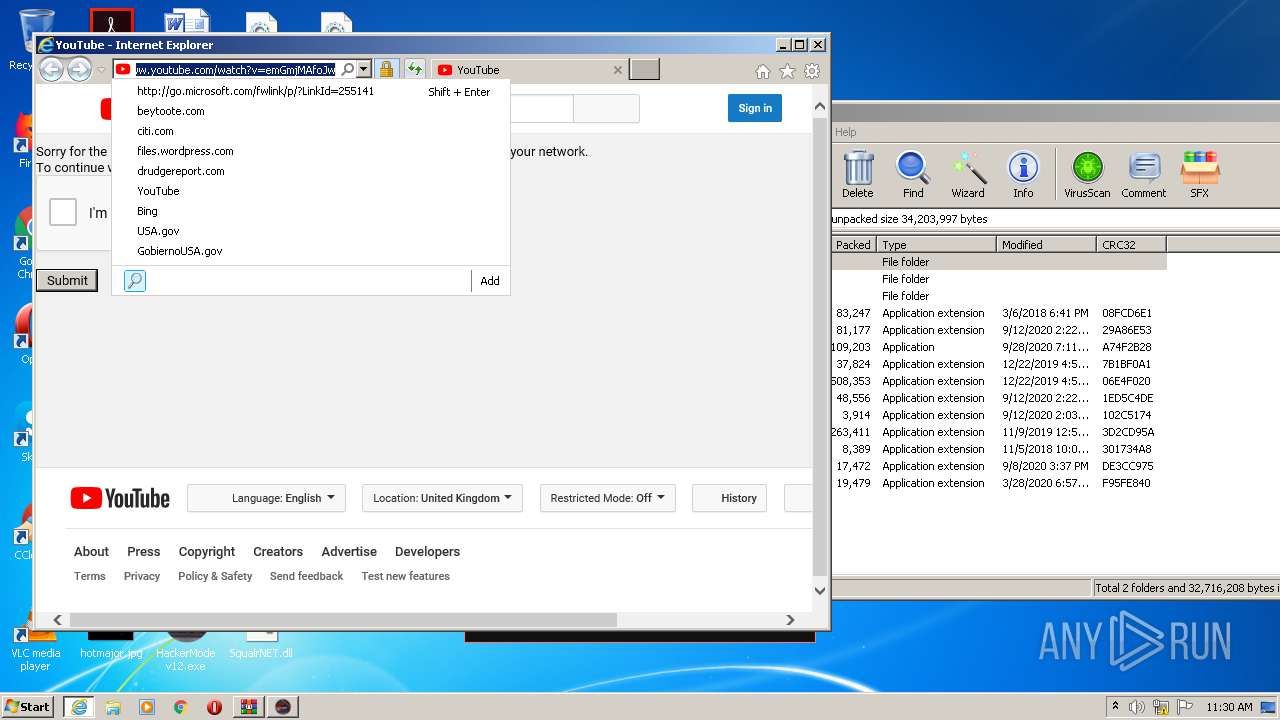
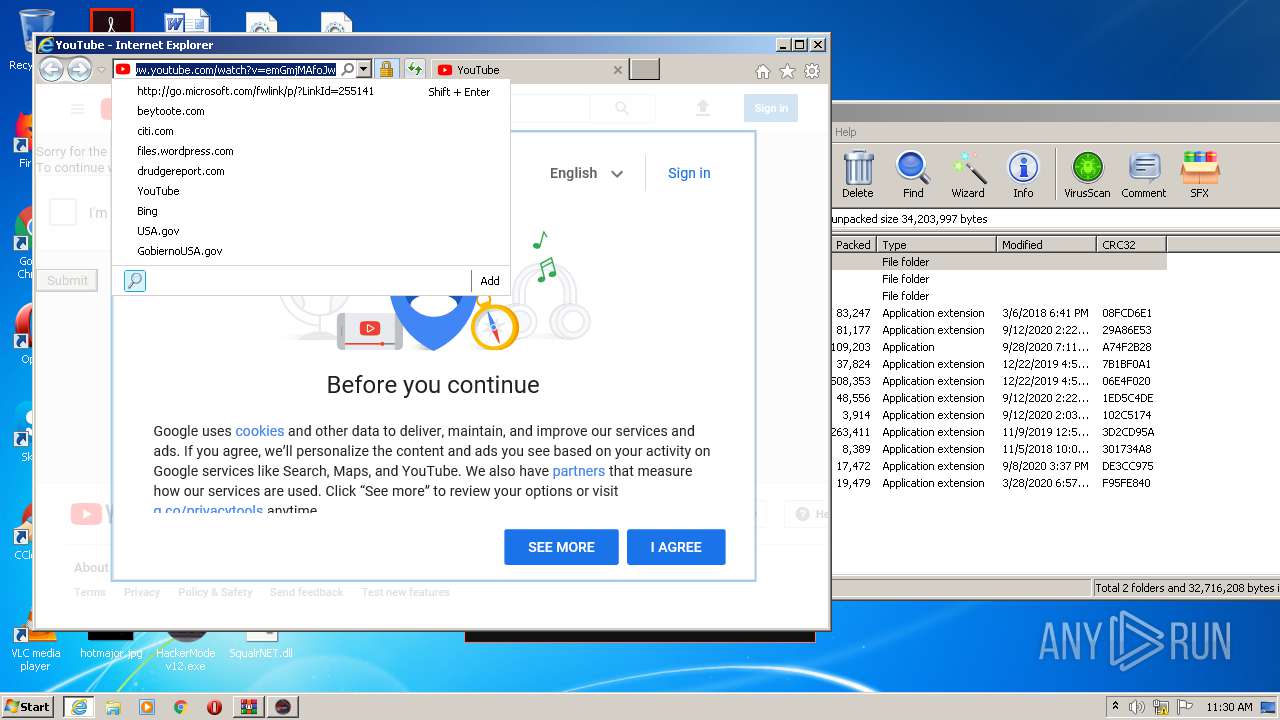
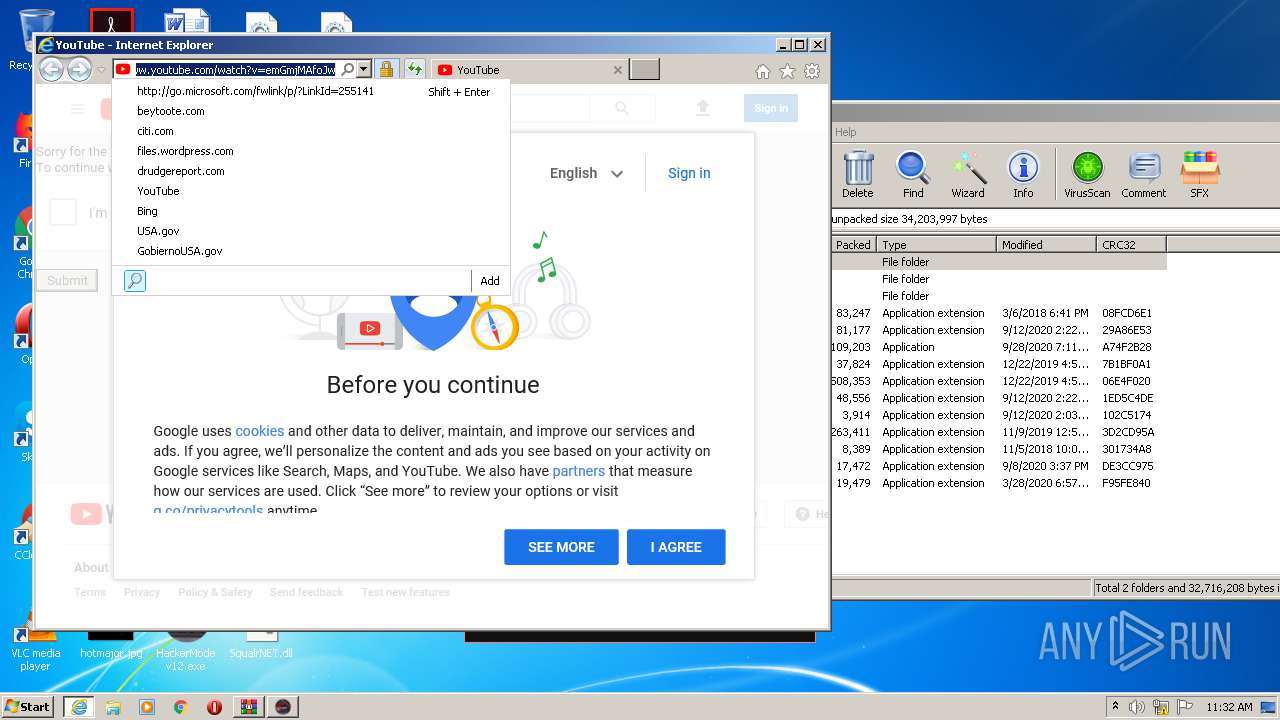
Starts Internet Explorer
- HackerMode v12.exe (PID: 4092)
INFO
Manual execution by user
- HackerMode v12.exe (PID: 4092)
Reads Internet Cache Settings
- iexplore.exe (PID: 3360)
- iexplore.exe (PID: 924)
Changes internet zones settings
- iexplore.exe (PID: 3360)
Application launched itself
- iexplore.exe (PID: 3360)
Reads settings of System Certificates
- iexplore.exe (PID: 924)
- iexplore.exe (PID: 3360)
Reads internet explorer settings
- iexplore.exe (PID: 924)
Creates files in the user directory
- iexplore.exe (PID: 924)
- iexplore.exe (PID: 3360)
Changes settings of System certificates
- iexplore.exe (PID: 3360)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .kmz | | | Google Earth saved working session (60) |
|---|---|---|
| .zip | | | ZIP compressed archive (40) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:09:09 12:32:11 |
| ZipCRC: | 0x862e9b63 |
| ZipCompressedSize: | 101932 |
| ZipUncompressedSize: | 188928 |
| ZipFileName: | Adafcaefc/FermentedMango.dll |
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3360 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3056 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/watch?v=emGmjMAfoJw | C:\Program Files\Internet Explorer\iexplore.exe | HackerMode v12.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
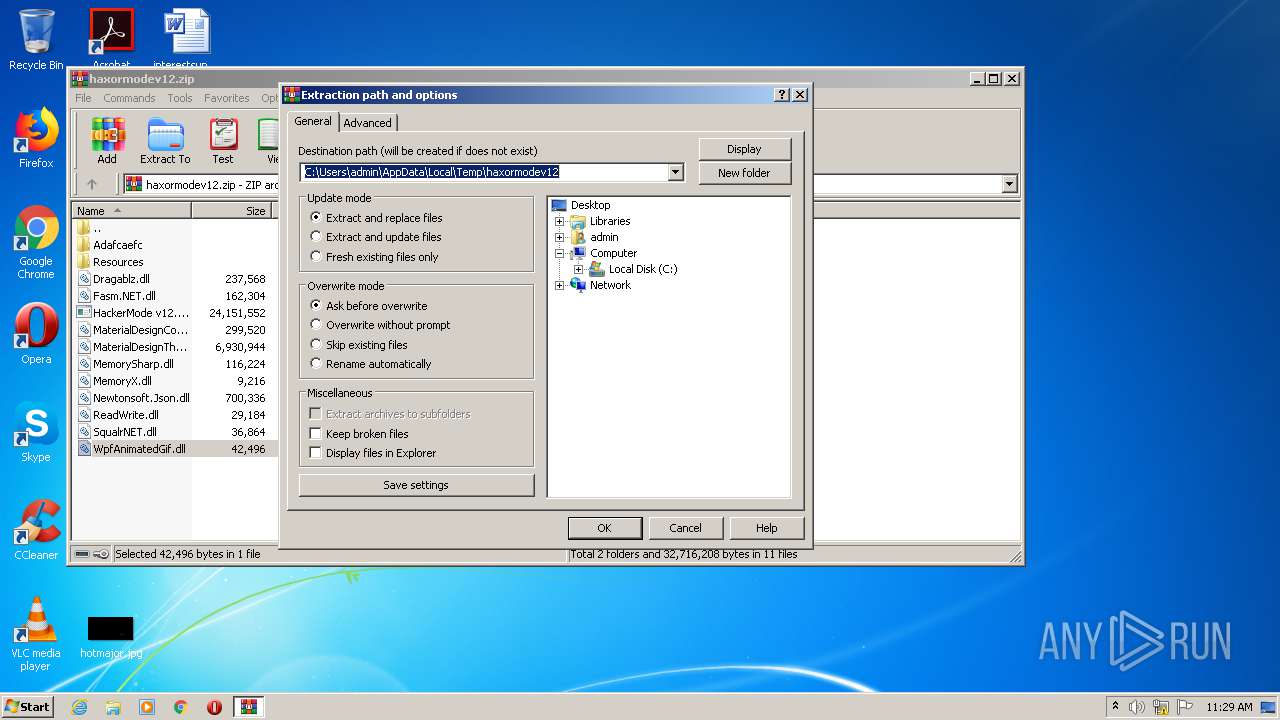
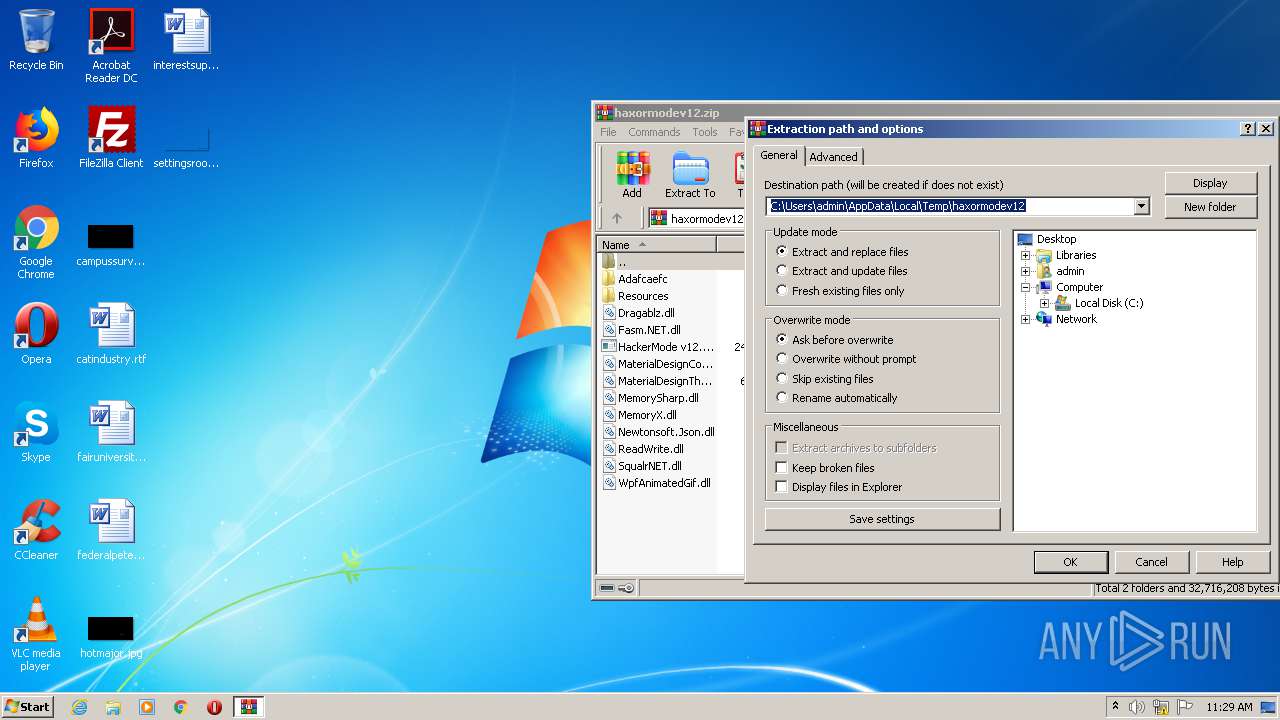
| 3400 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\haxormodev12.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 4092 | "C:\Users\admin\Desktop\HackerMode v12.exe" | C:\Users\admin\Desktop\HackerMode v12.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Hacker Mode (Among Us) Exit code: 0 Version: 1.0.9.0 Modules
| |||||||||||||||
Total events
1 421
Read events
1 266
Write events
152
Delete events
3
Modification events
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\haxormodev12.zip | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\haxormodev12 | |||
| (PID) Process: | (3400) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\AppData\Local\Temp\haxormodev12 | |||
Executable files
15
Suspicious files
24
Text files
42
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | WinRAR.exe | C:\Users\admin\Desktop\HackerMode v12.exe | executable | |
MD5:— | SHA256:— | |||
| 3400 | WinRAR.exe | C:\Users\admin\Desktop\Adafcaefc\FermentedMango.dll | executable | |
MD5:— | SHA256:— | |||
| 3400 | WinRAR.exe | C:\Users\admin\Desktop\Adafcaefc\ToastedMarshmellow.dll | executable | |
MD5:— | SHA256:— | |||
| 3400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\haxormodev12\WpfAnimatedGif.dll | executable | |
MD5:F591261C6D85601764B3B8AEA8DF8B2E | SHA256:4498D8D1A0549717852507993B7C0350D1DA408D22943ED8244D16441ABFAF99 | |||
| 924 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab6F8E.tmp | — | |
MD5:— | SHA256:— | |||
| 924 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar6F8F.tmp | — | |
MD5:— | SHA256:— | |||
| 924 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\U2WY0L26.txt | — | |
MD5:— | SHA256:— | |||
| 924 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 3400 | WinRAR.exe | C:\Users\admin\Desktop\Adafcaefc\RoastedMelon.dll | executable | |
MD5:— | SHA256:— | |||
| 3400 | WinRAR.exe | C:\Users\admin\Desktop\MemoryX.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
46
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDOs%2FDKHsIMiAIAAAAAeksR | US | der | 472 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBedu0%2BUKJj8CAAAAABXoSI%3D | US | der | 471 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCoziyTHasflwIAAAAAekur | US | der | 472 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjqTAc%2FHIGOD%2BaUx0%3D | US | der | 492 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAKXB1YM1Knrv%2BJy8eCW2II%3D | US | der | 471 b | whitelisted |
924 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDOs%2FDKHsIMiAIAAAAAeksR | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4092 | HackerMode v12.exe | 104.23.98.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
924 | iexplore.exe | 216.58.205.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
924 | iexplore.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
924 | iexplore.exe | 172.217.23.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
924 | iexplore.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3360 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
924 | iexplore.exe | 216.58.207.46:443 | www.youtube.com | Google Inc. | US | whitelisted |
1056 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1056 | svchost.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3360 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
www.youtube.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
s.ytimg.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |