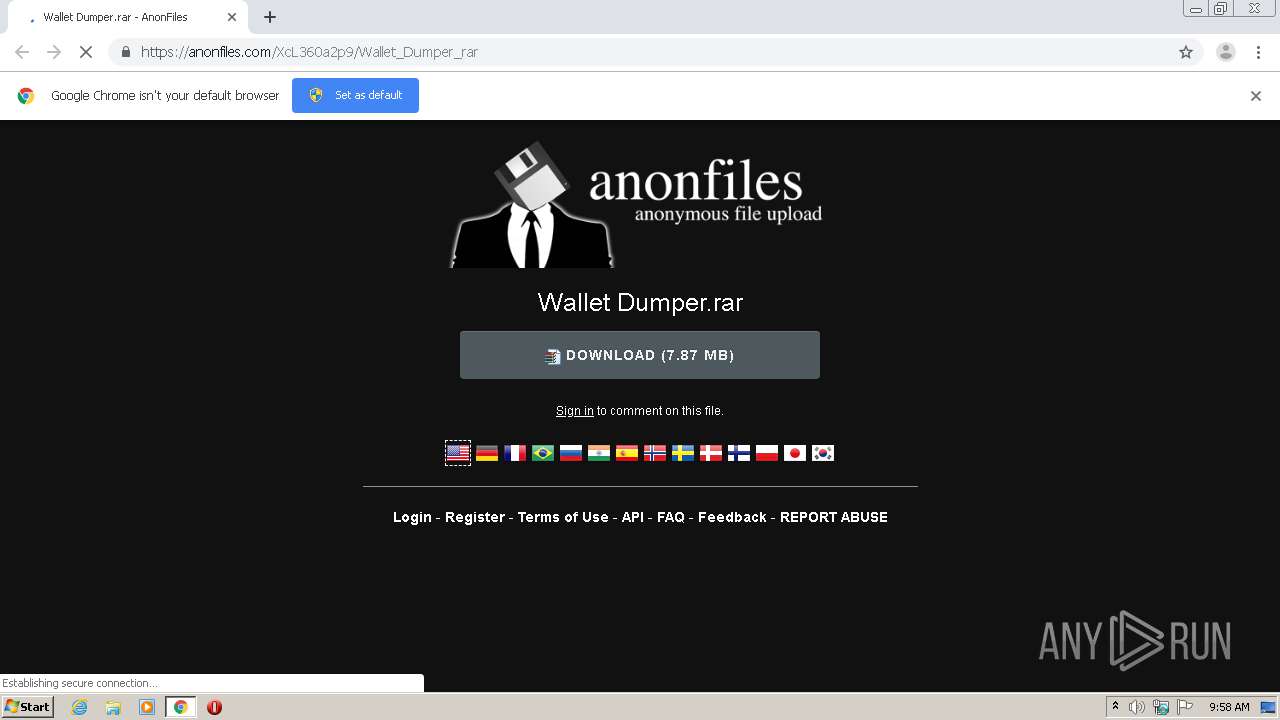
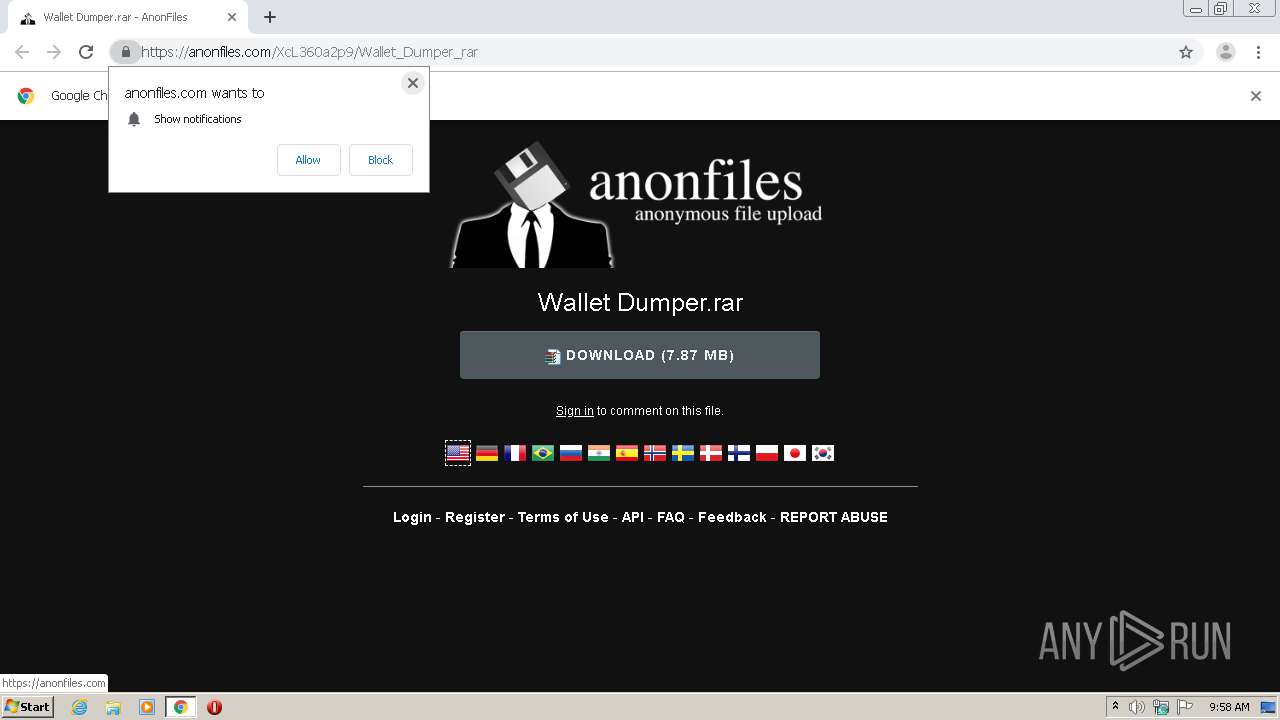
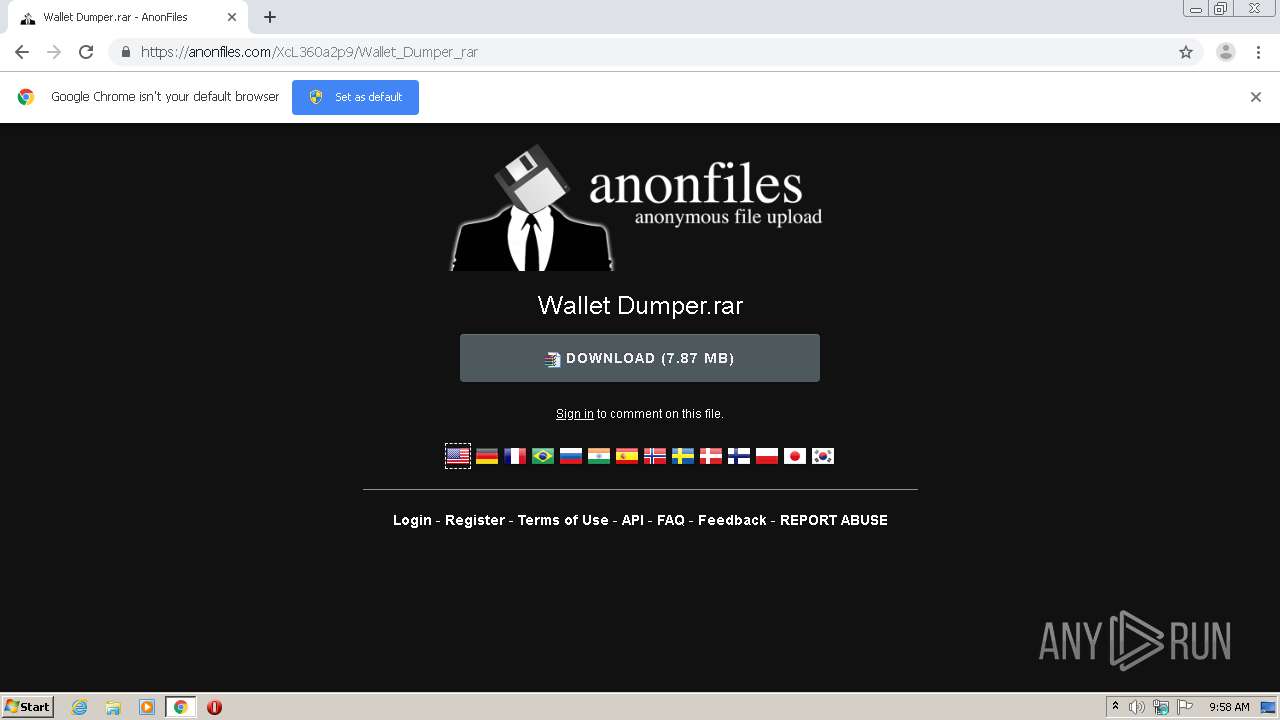
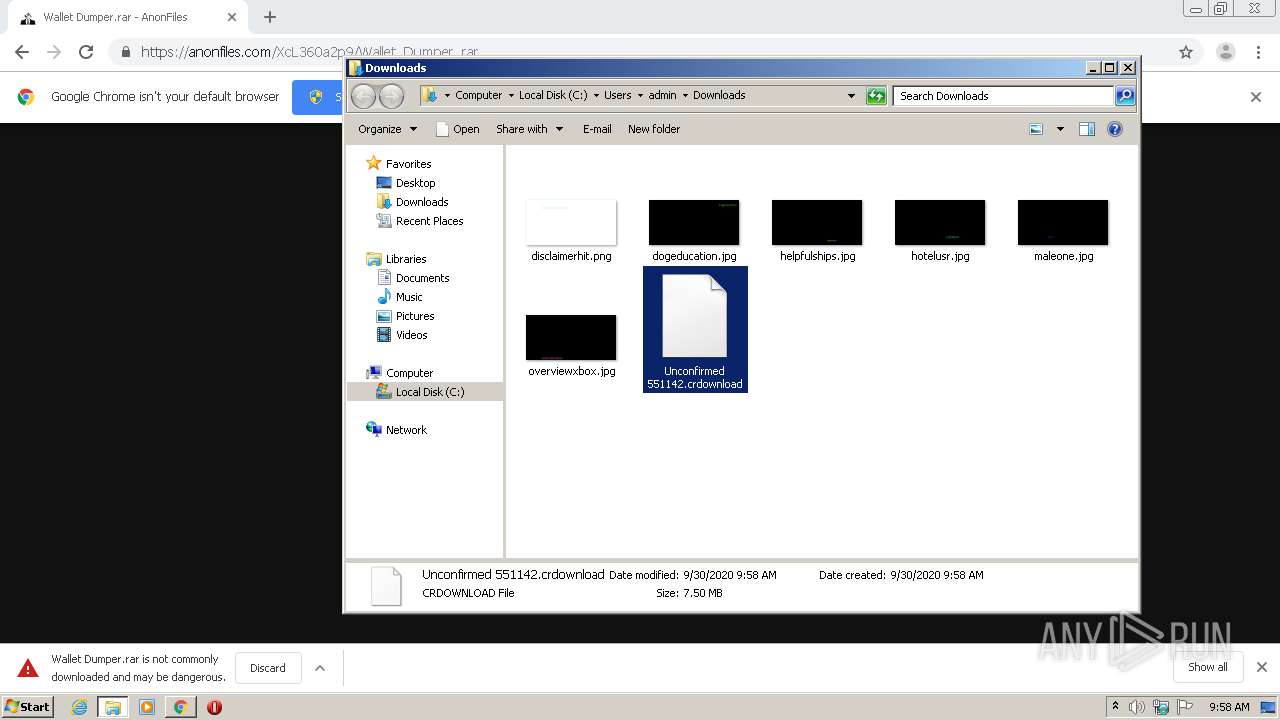
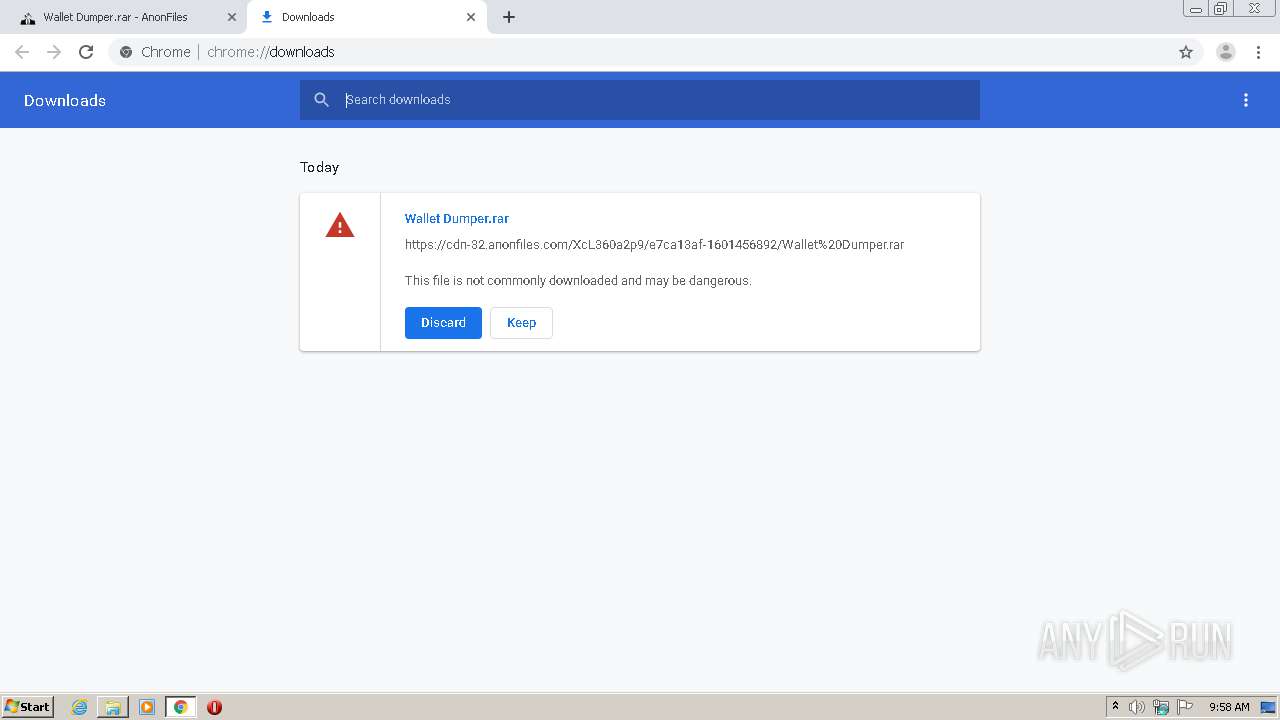
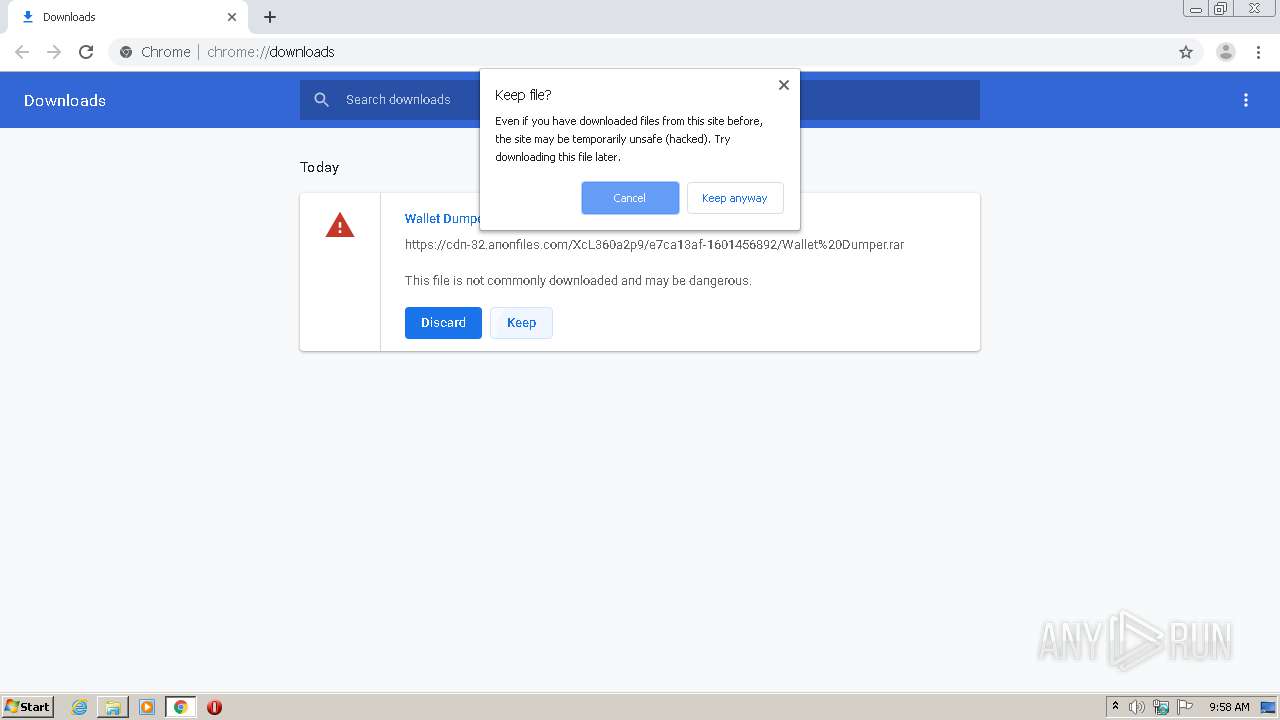
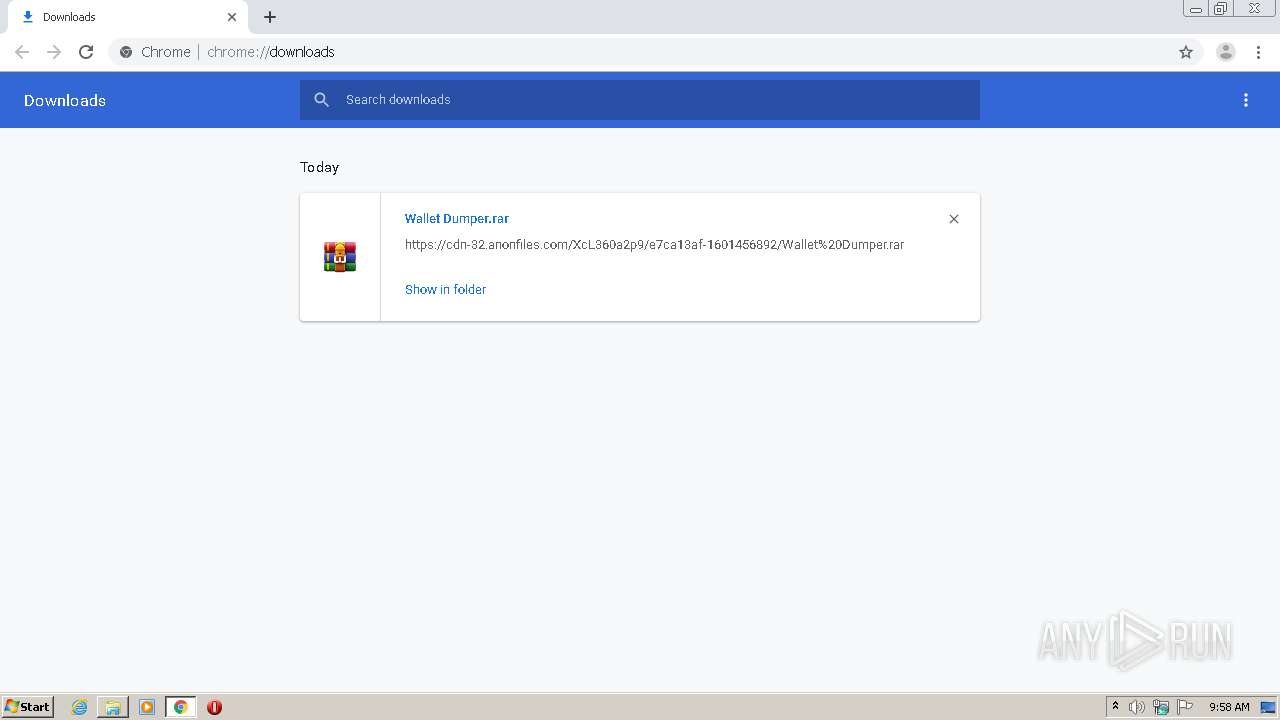
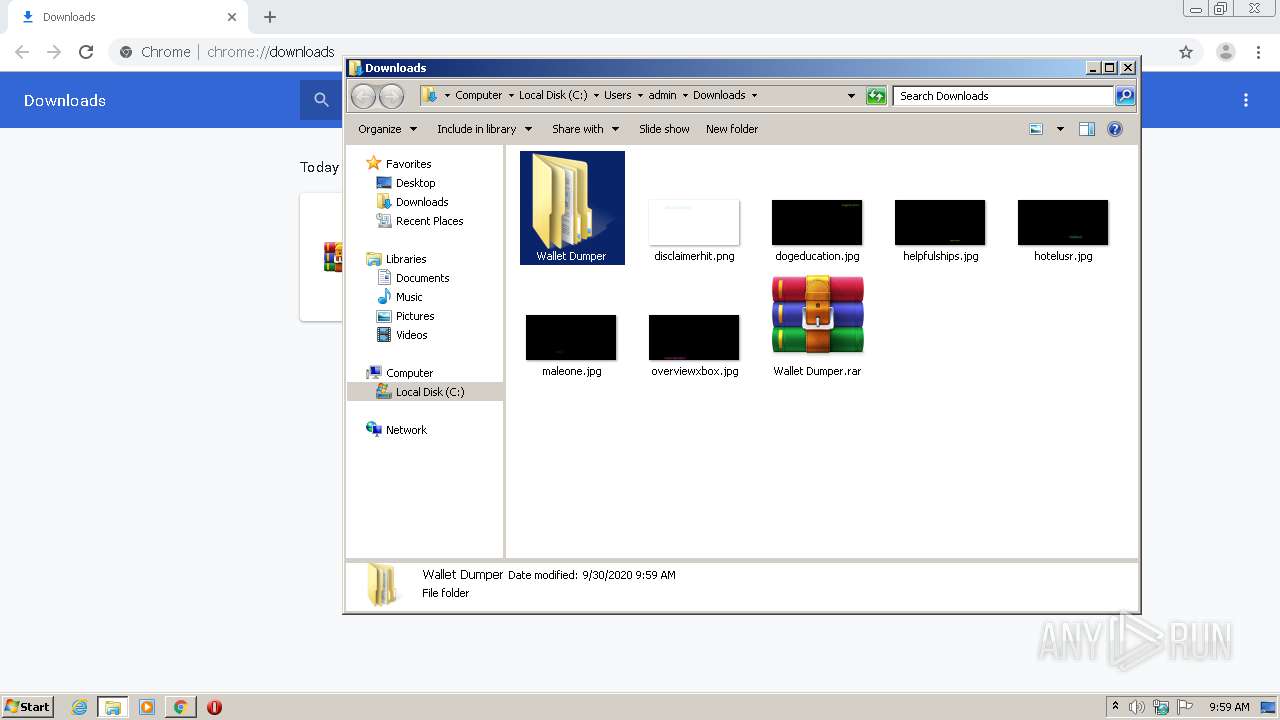
| URL: | https://anonfiles.com/XcL360a2p9/Wallet_Dumper_rar |
| Full analysis: | https://app.any.run/tasks/16435d0a-95eb-4f95-a57c-2a66825147d1 |
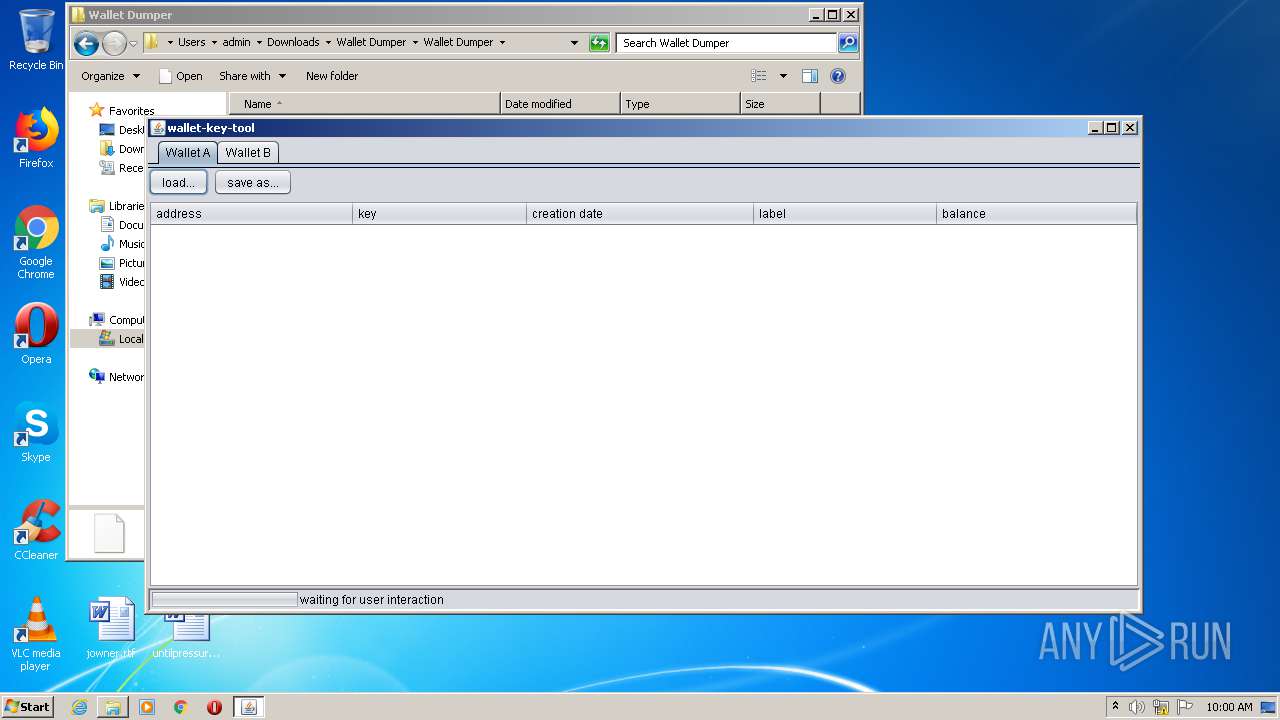
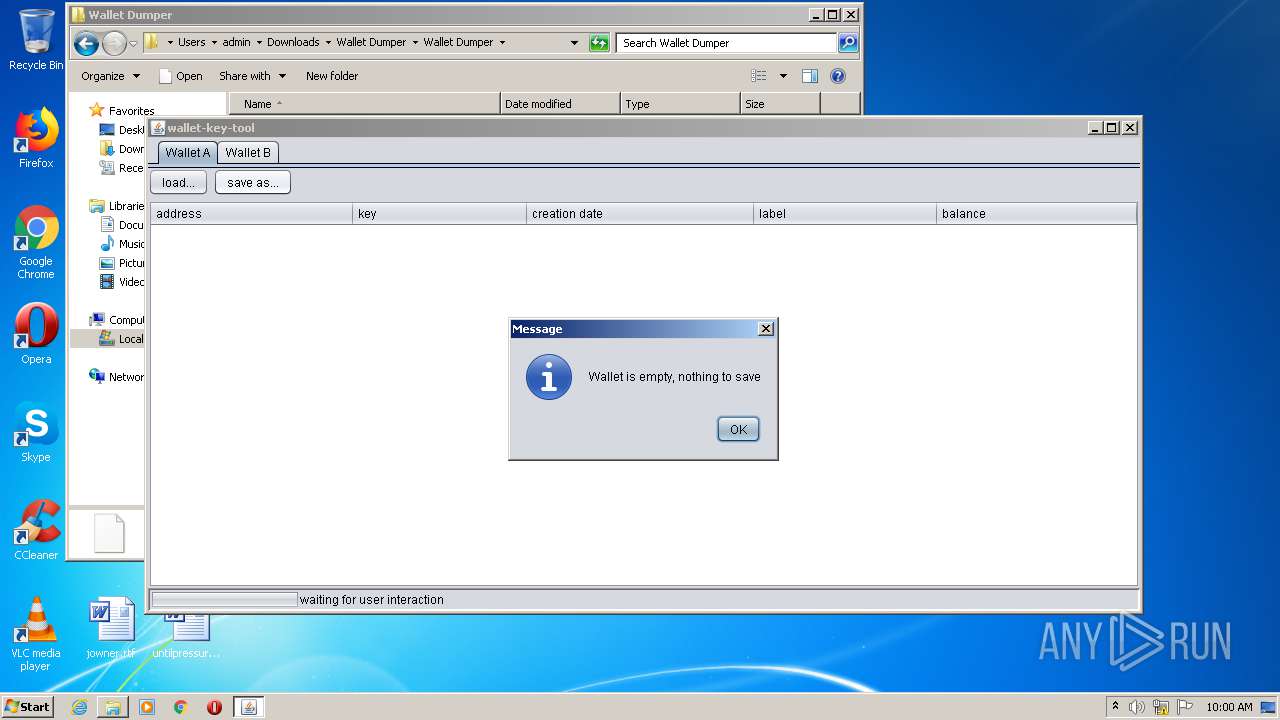
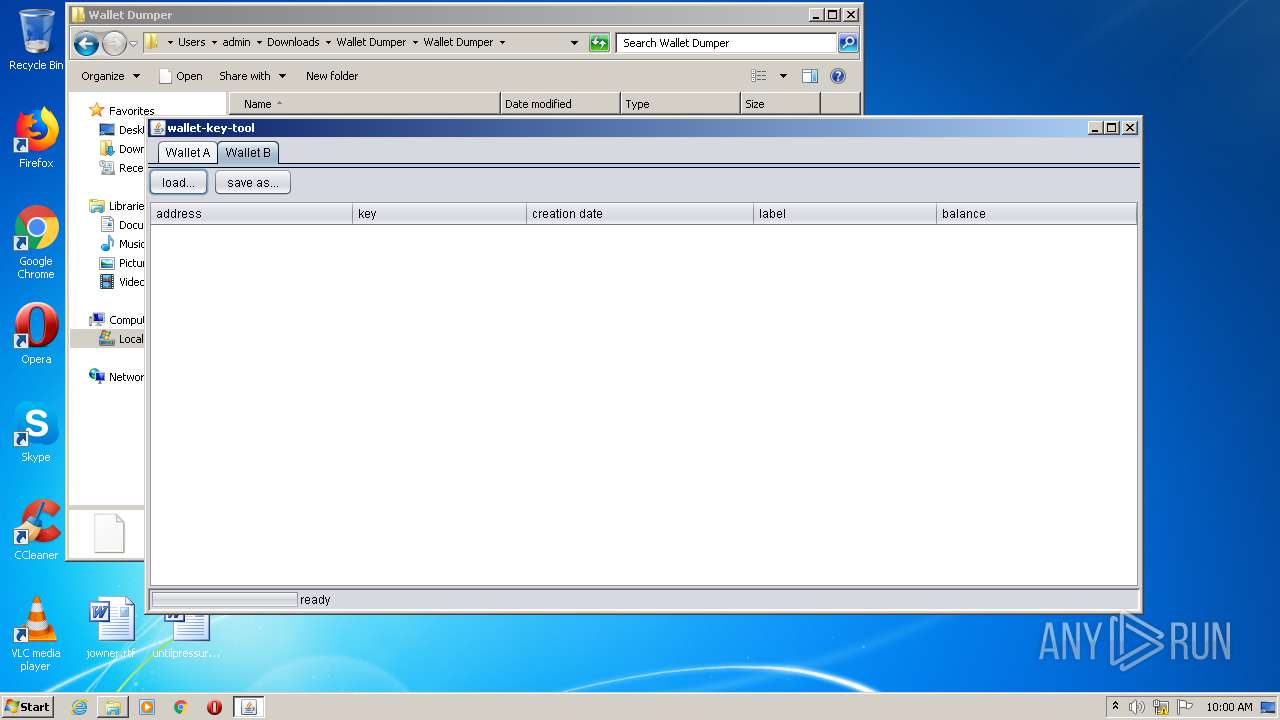
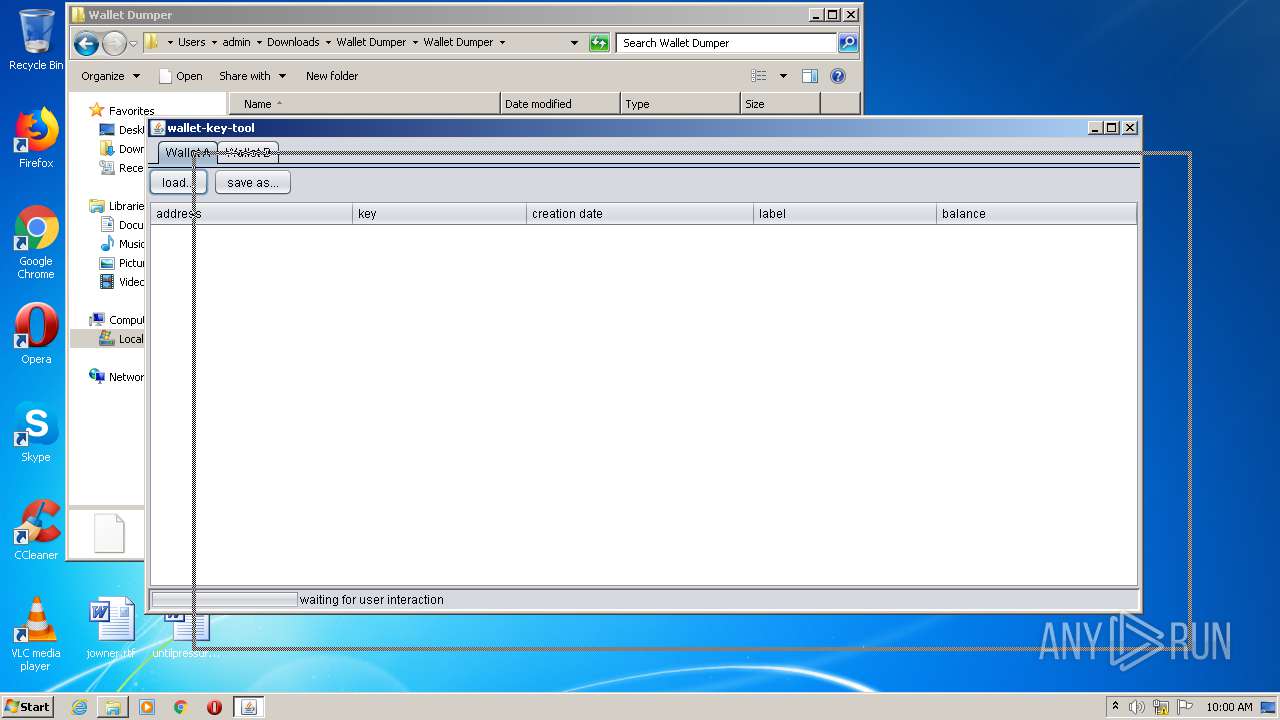
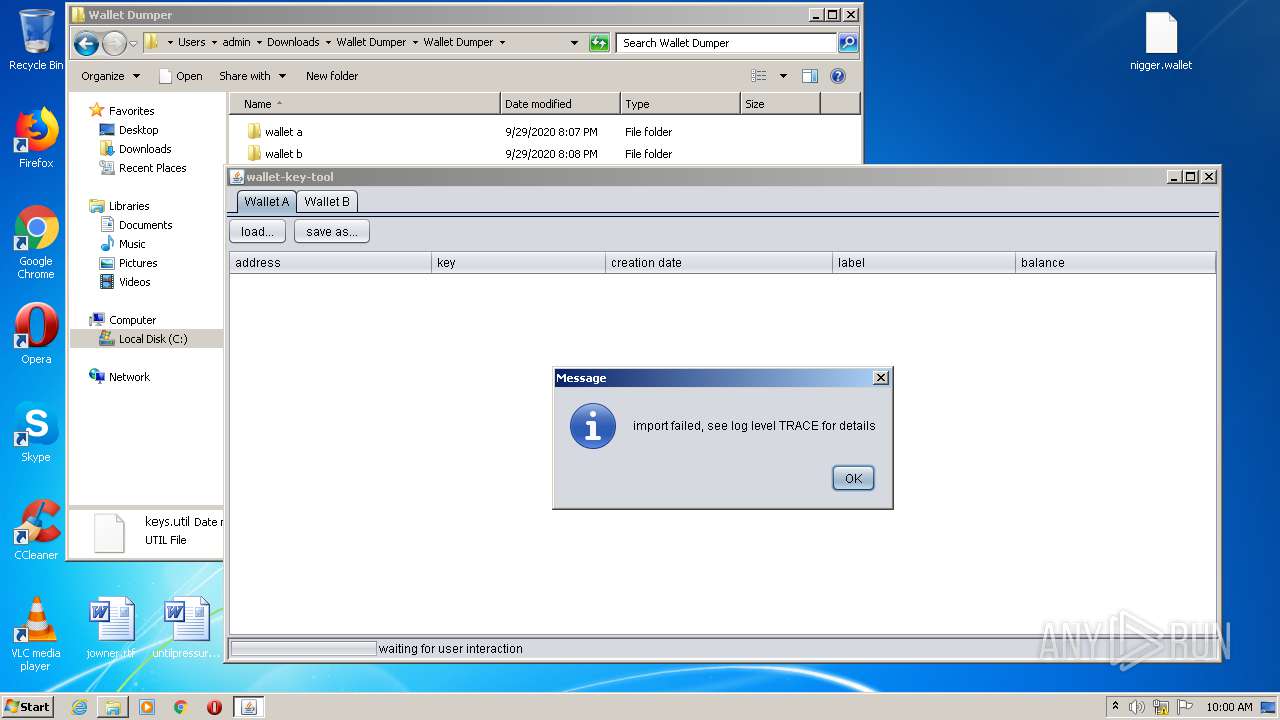
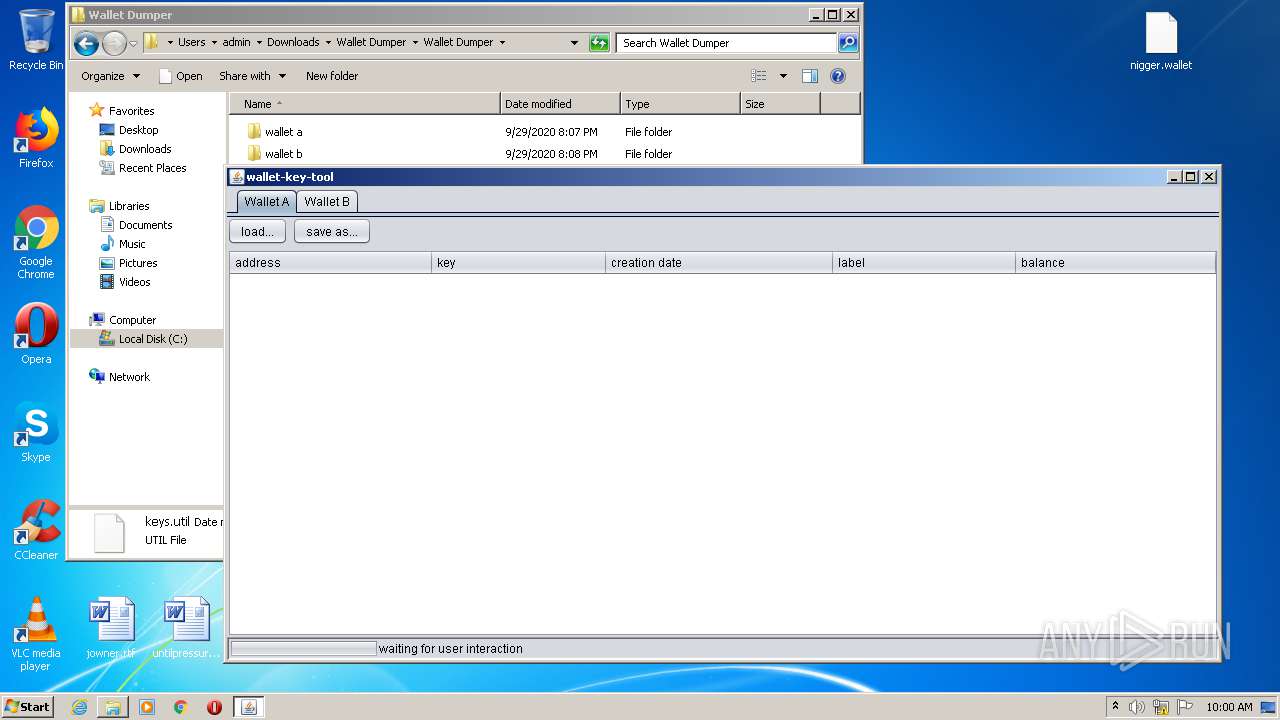
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 08:57:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FE3A38270AE53F9D656CA02E2EFDE83D |
| SHA1: | 2B3060EFF594EA230C3C9F5770A18D0382B7C744 |
| SHA256: | 9EA6C284C1AEE182DB4CDA1A4B6E3D54E5714B5783E9152C508CE82F0B8044B7 |
| SSDEEP: | 3:N8M2vcKXUKQIqX6X+:2M2vjSds+ |
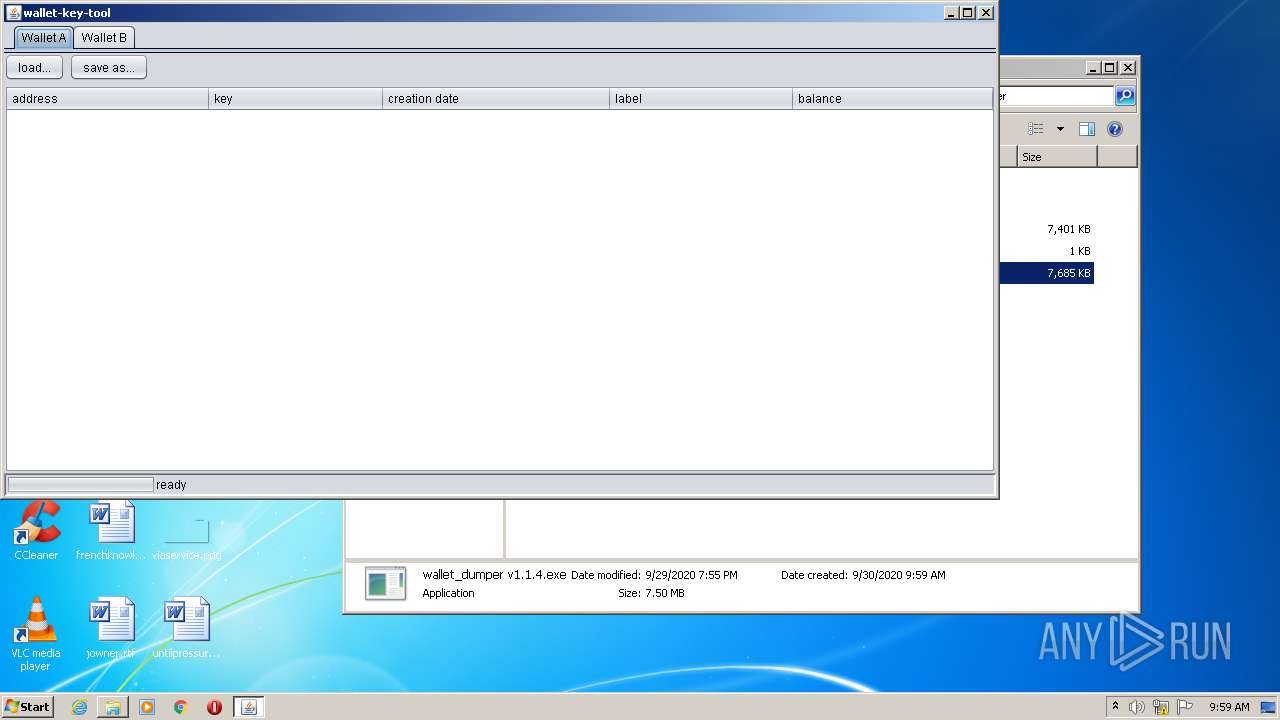
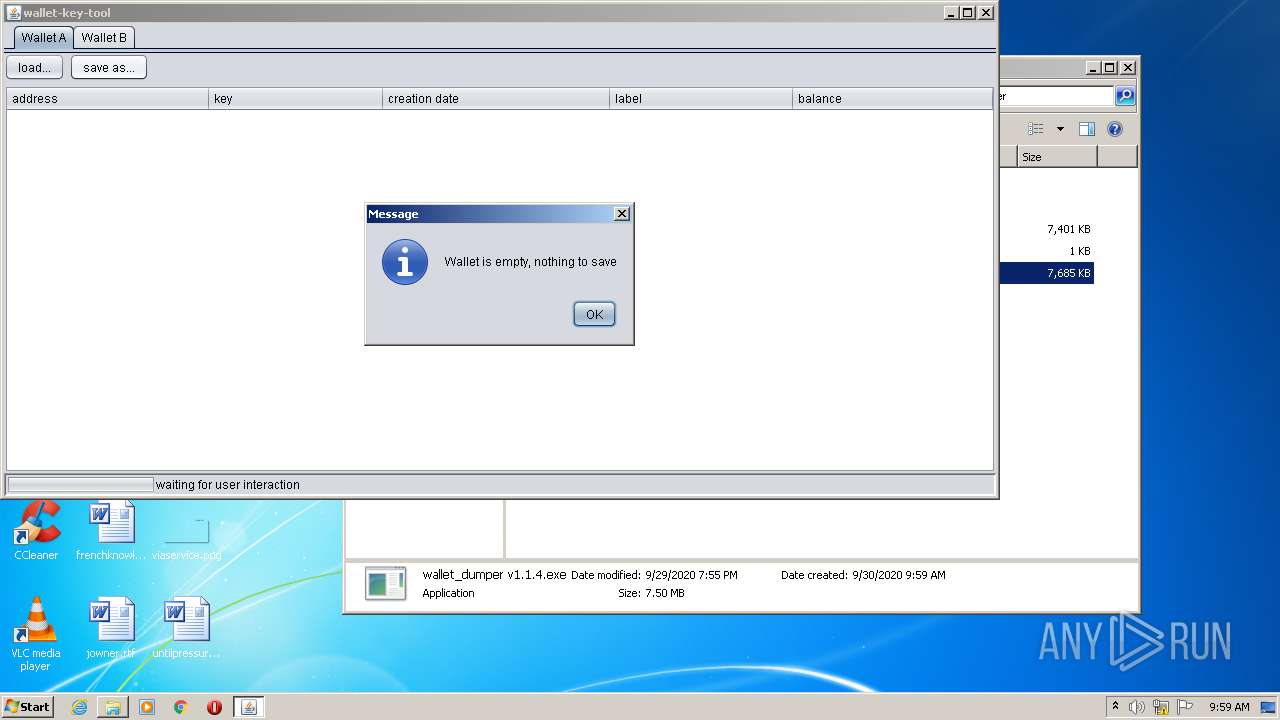
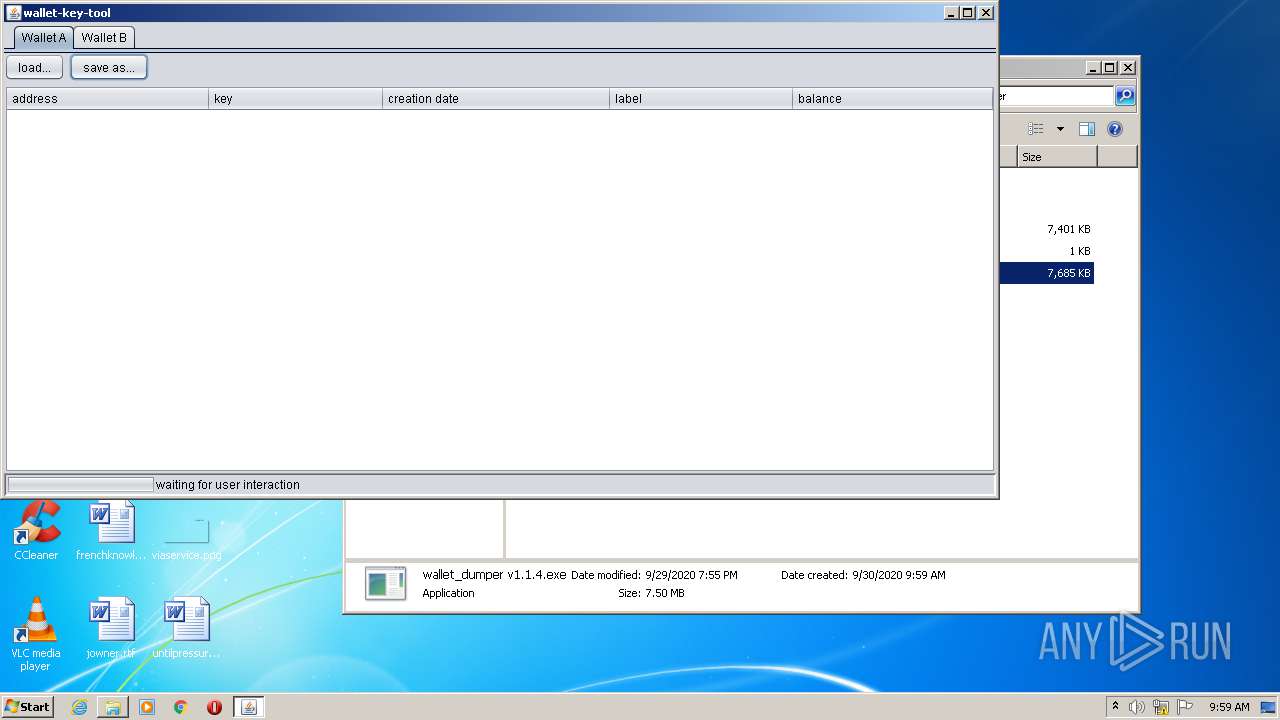
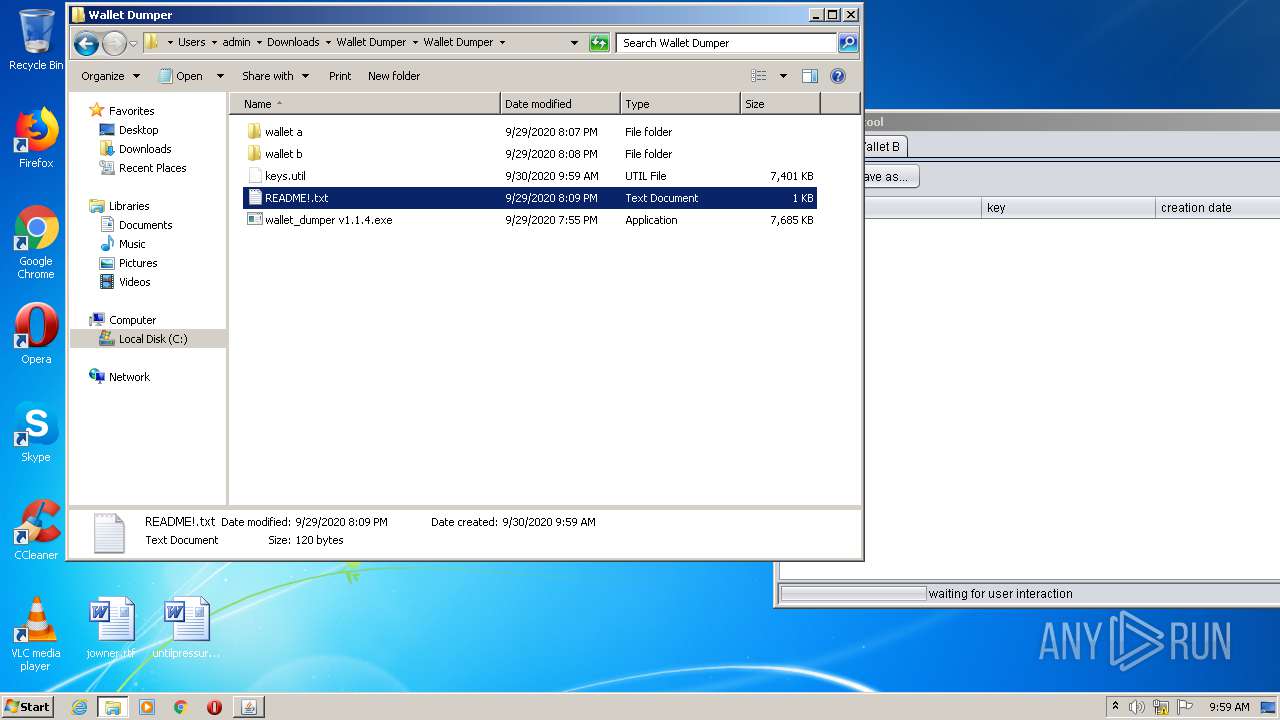
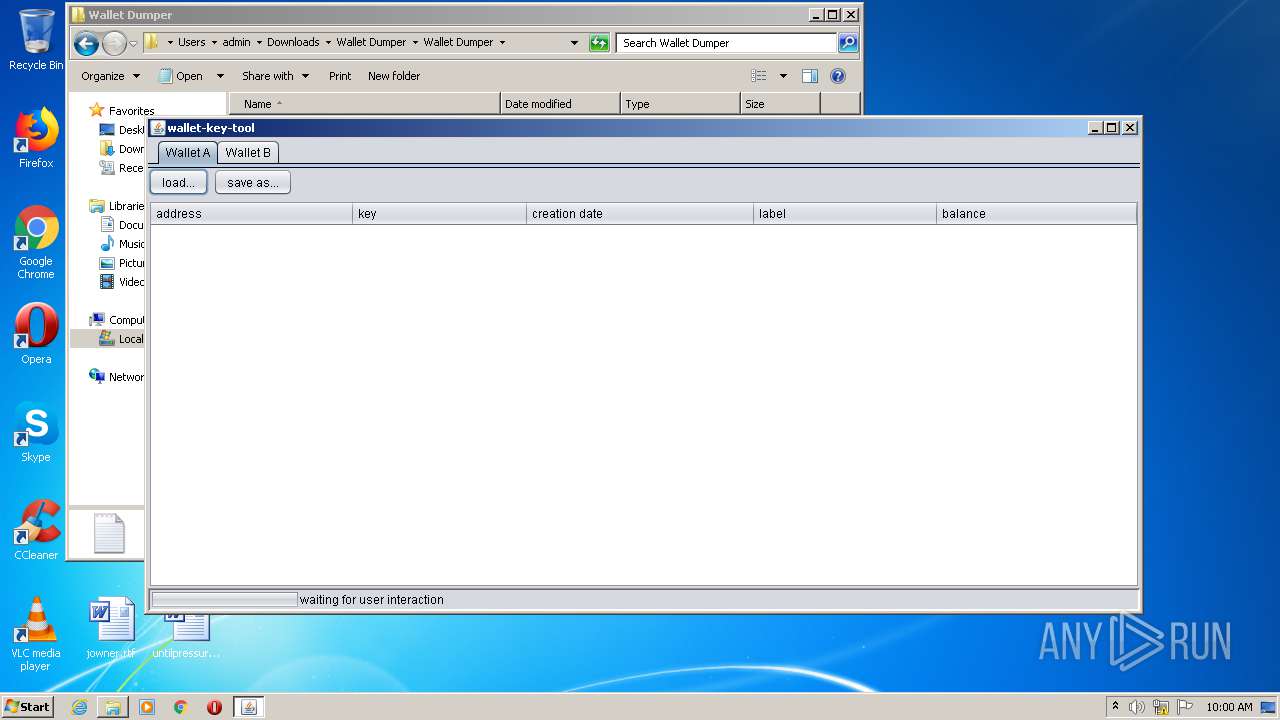
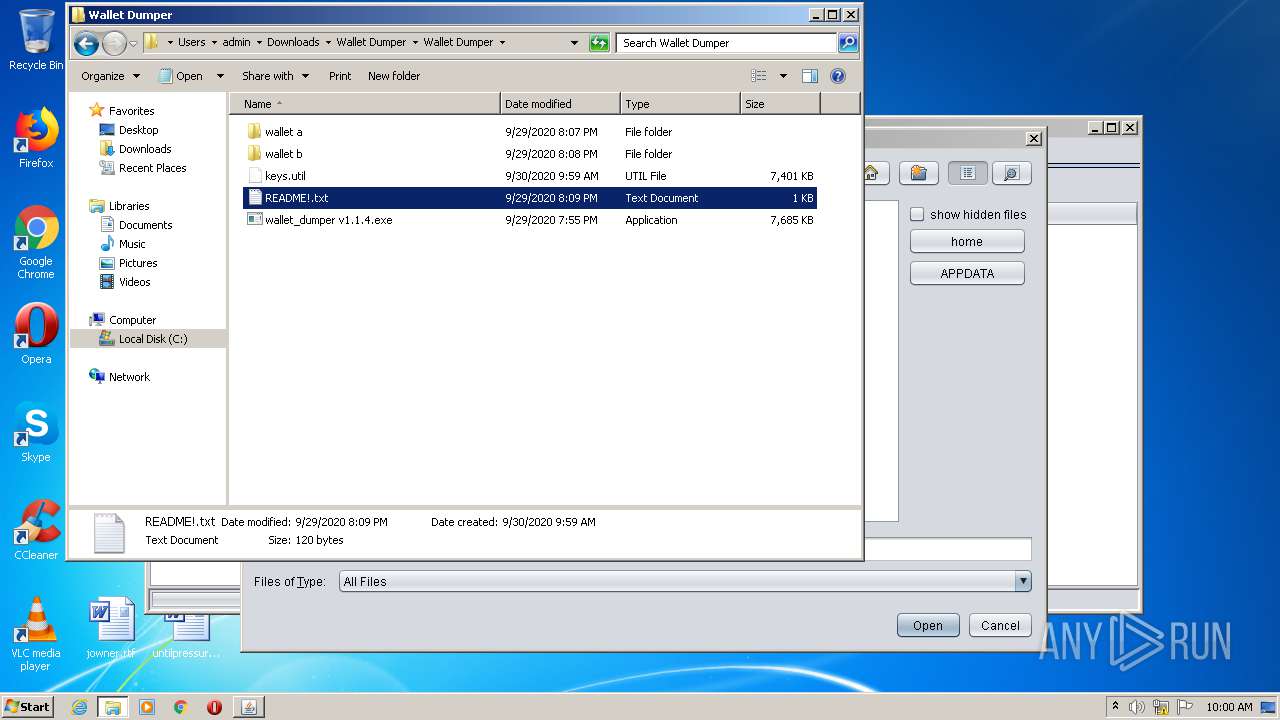
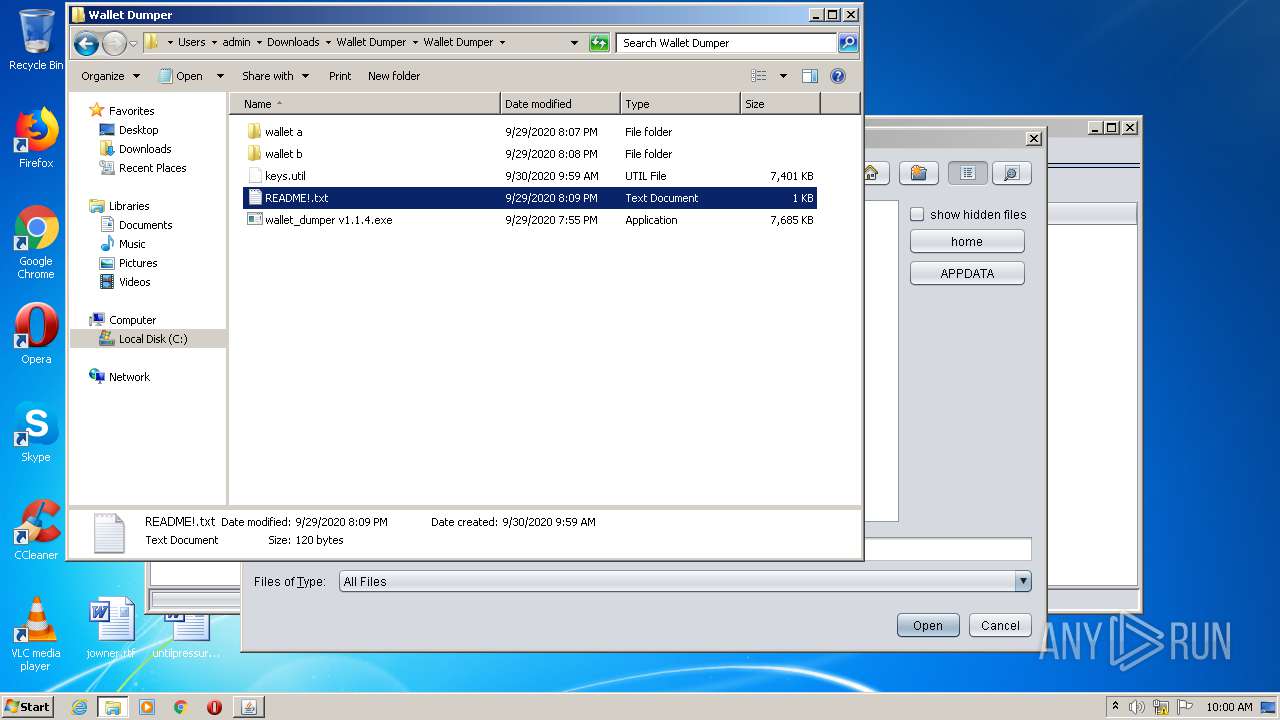
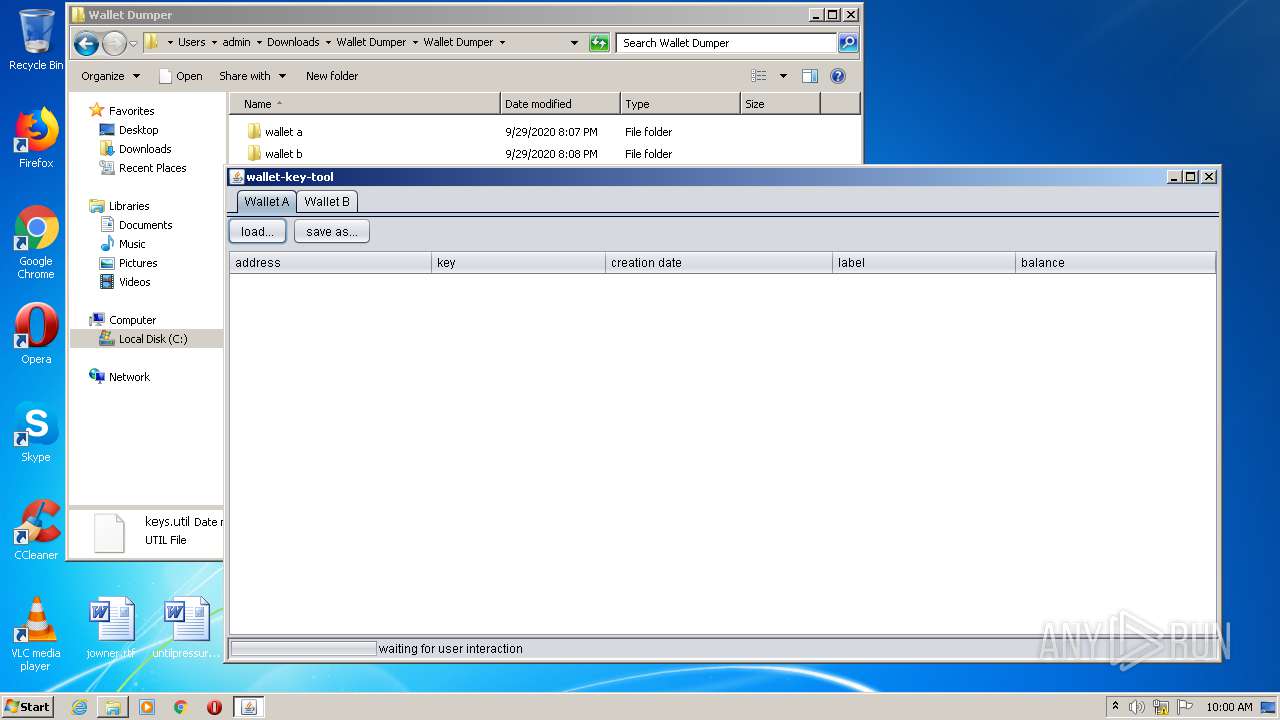
MALICIOUS
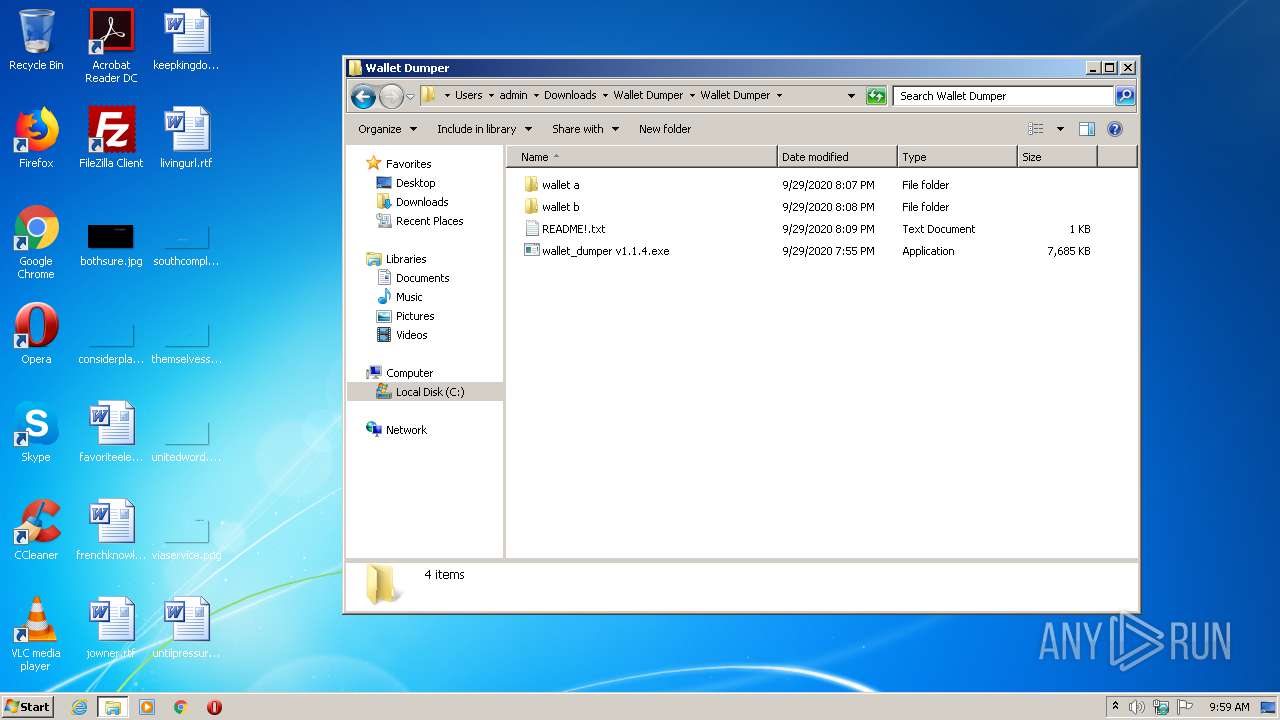
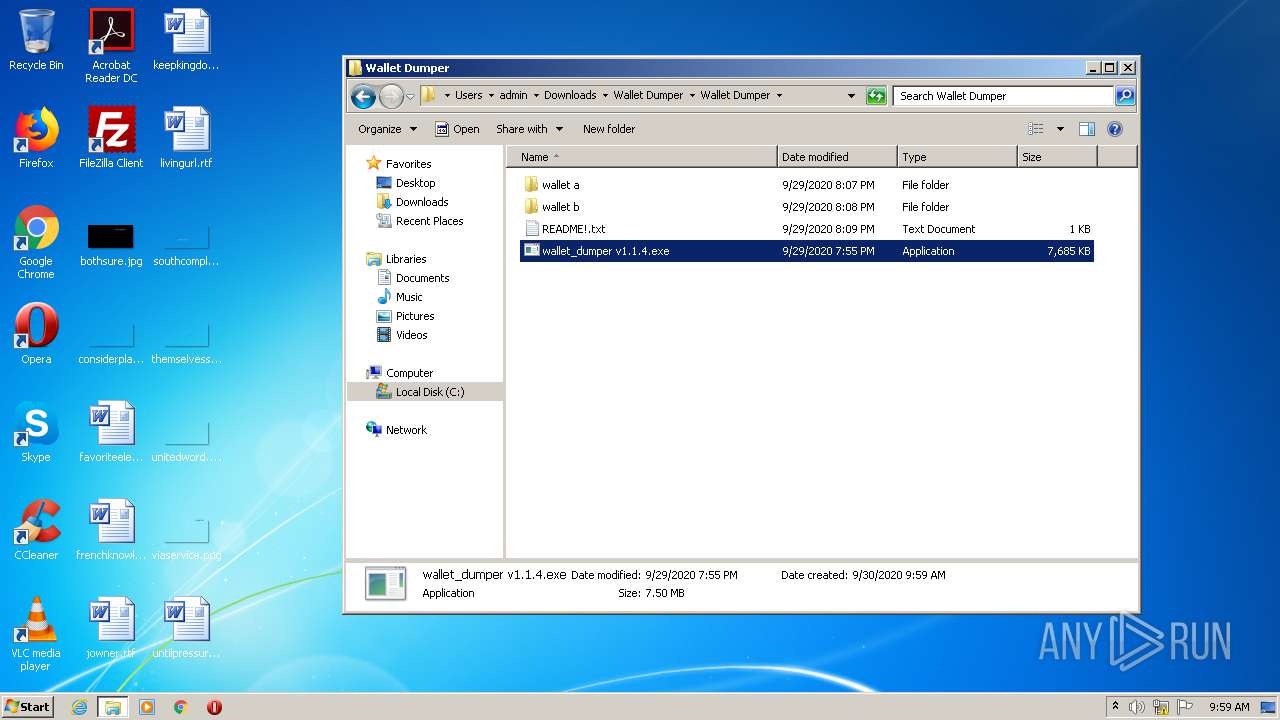
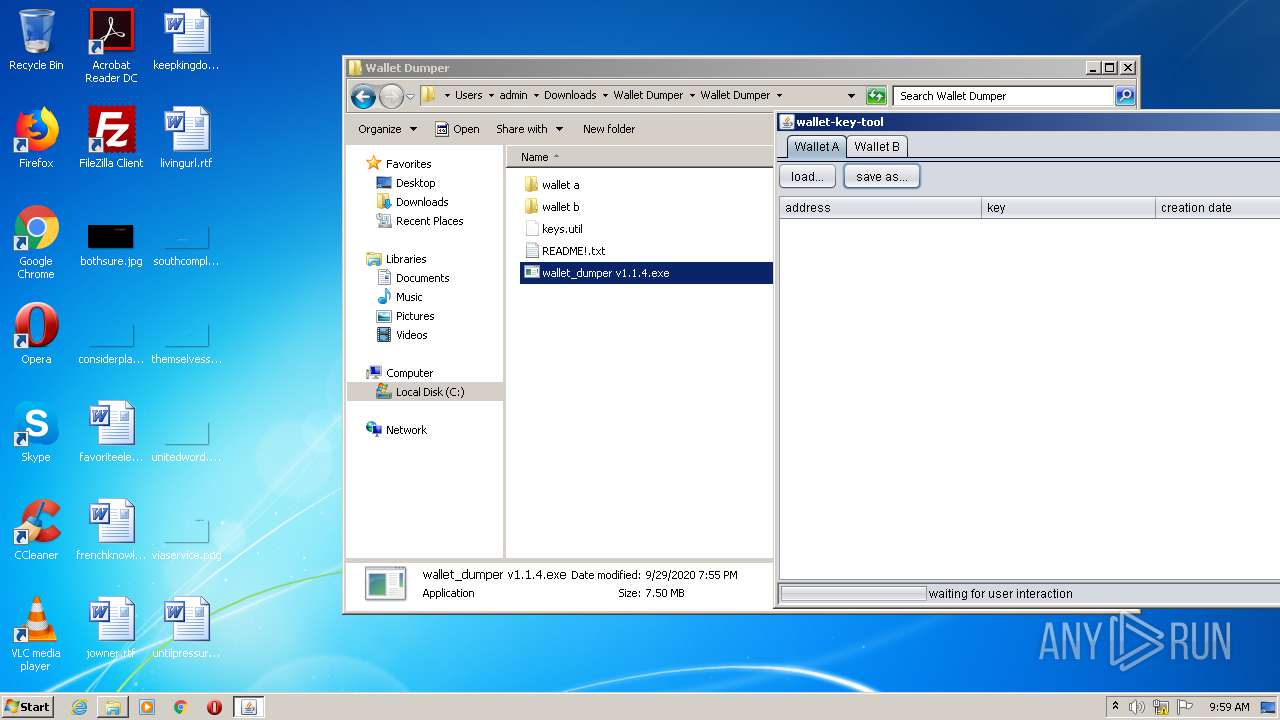
Application was dropped or rewritten from another process
- wallet_dumper v1.1.4.exe (PID: 2384)
- keys.util (PID: 4016)
SUSPICIOUS
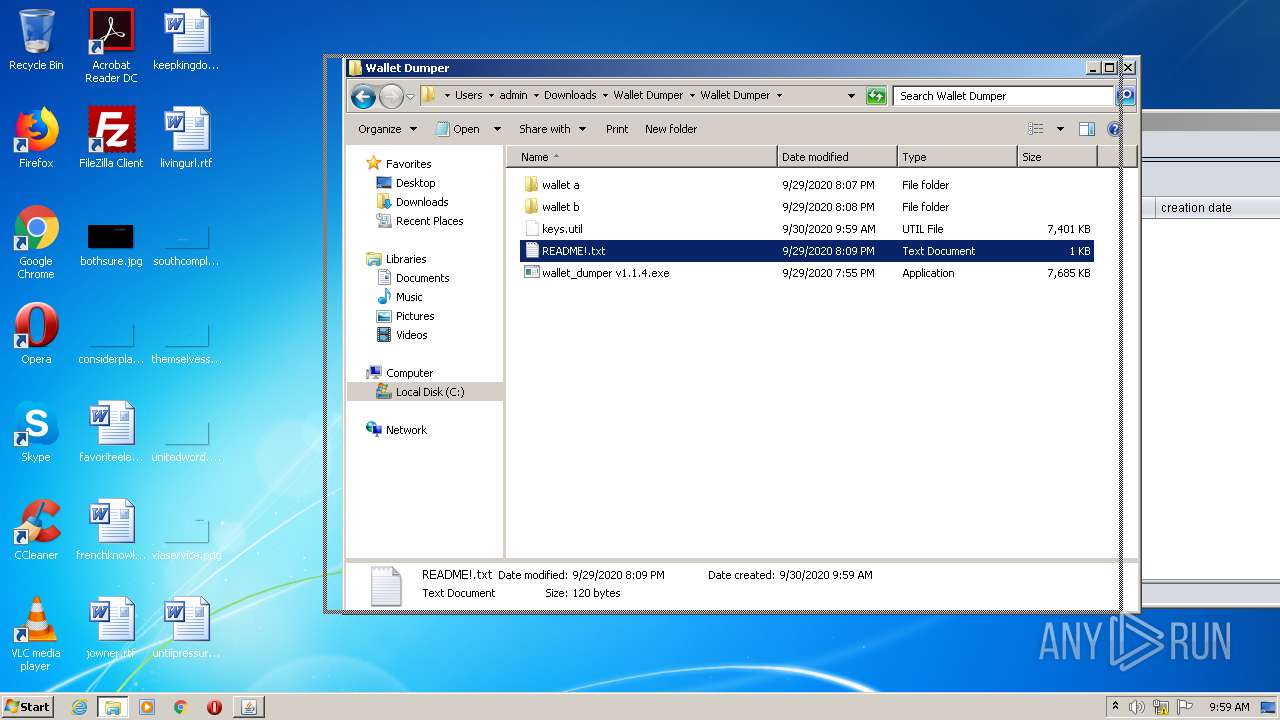
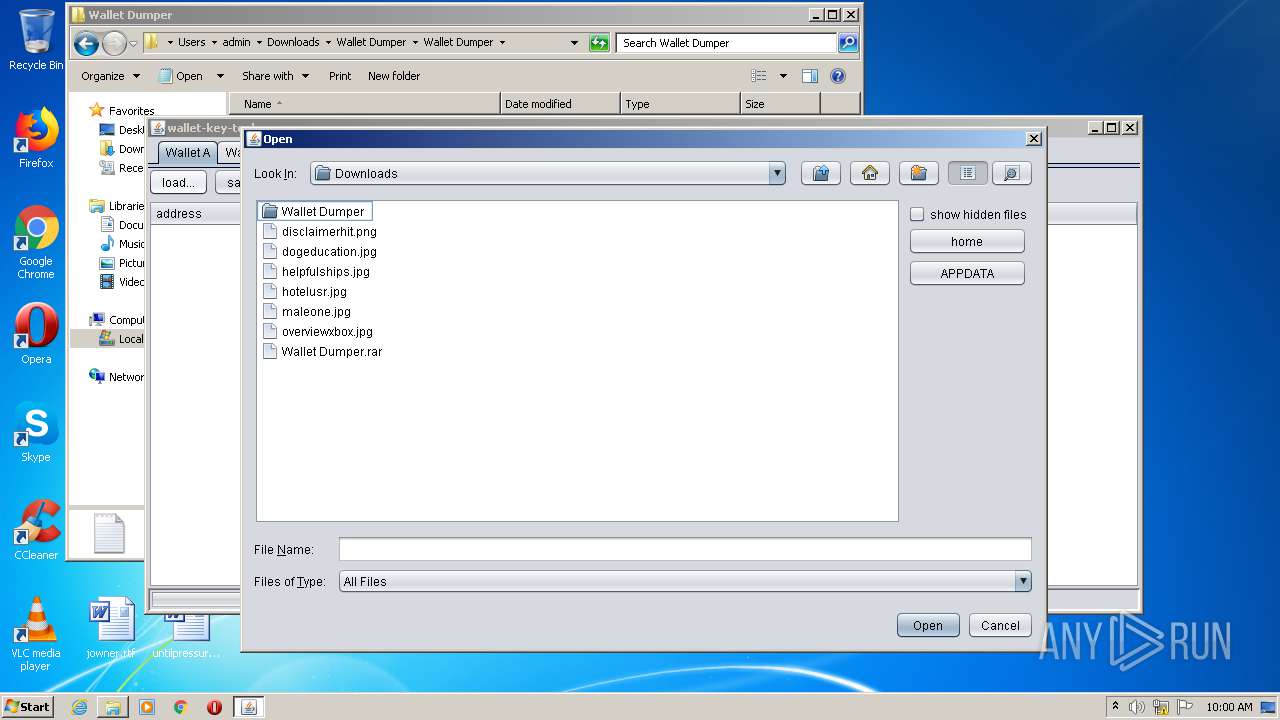
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3232)
- wallet_dumper v1.1.4.exe (PID: 2384)
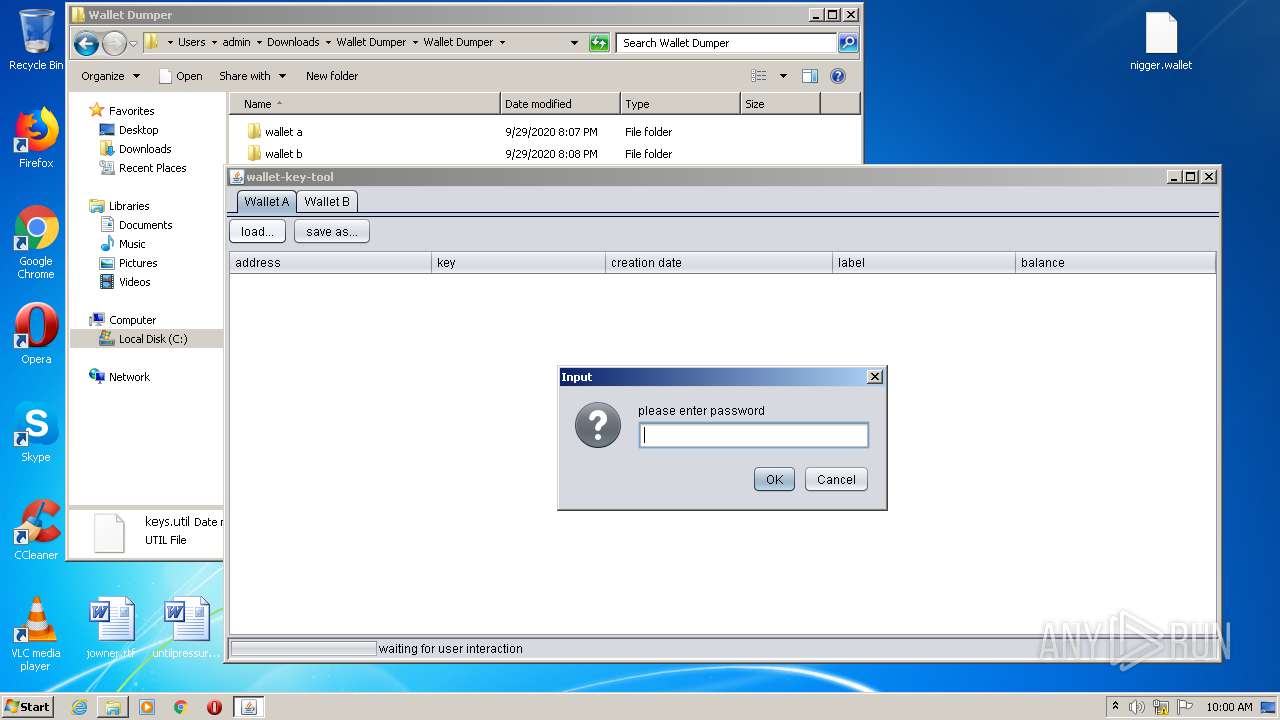
Starts application with an unusual extension
- cmd.exe (PID: 824)
Starts CMD.EXE for commands execution
- wallet_dumper v1.1.4.exe (PID: 2384)
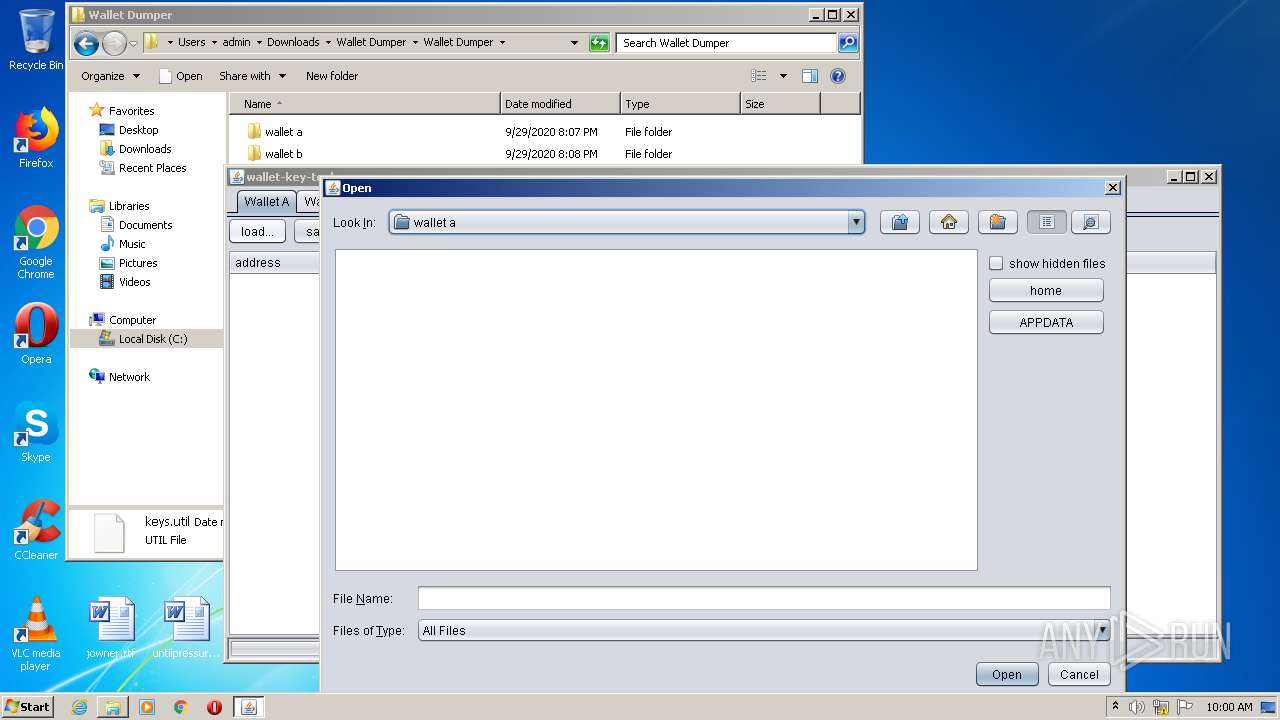
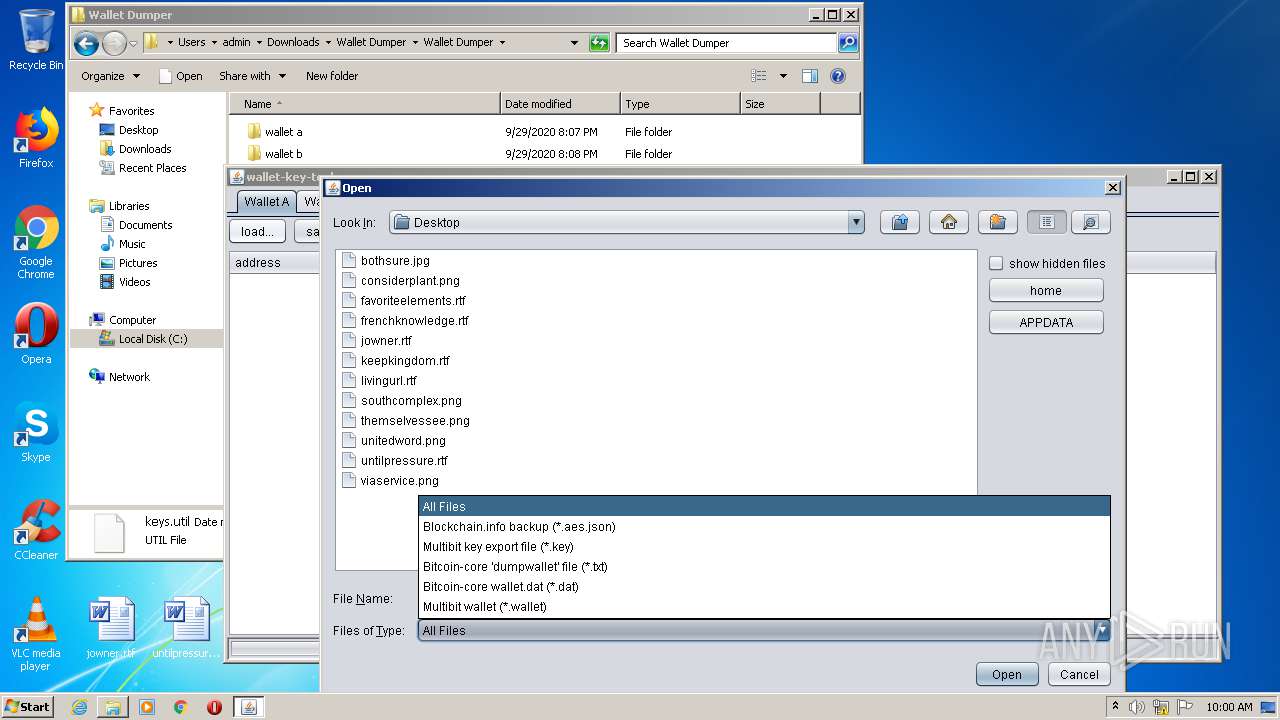
Executes JAVA applets
- keys.util (PID: 4016)
INFO
Reads the hosts file
- chrome.exe (PID: 1888)
- chrome.exe (PID: 2492)
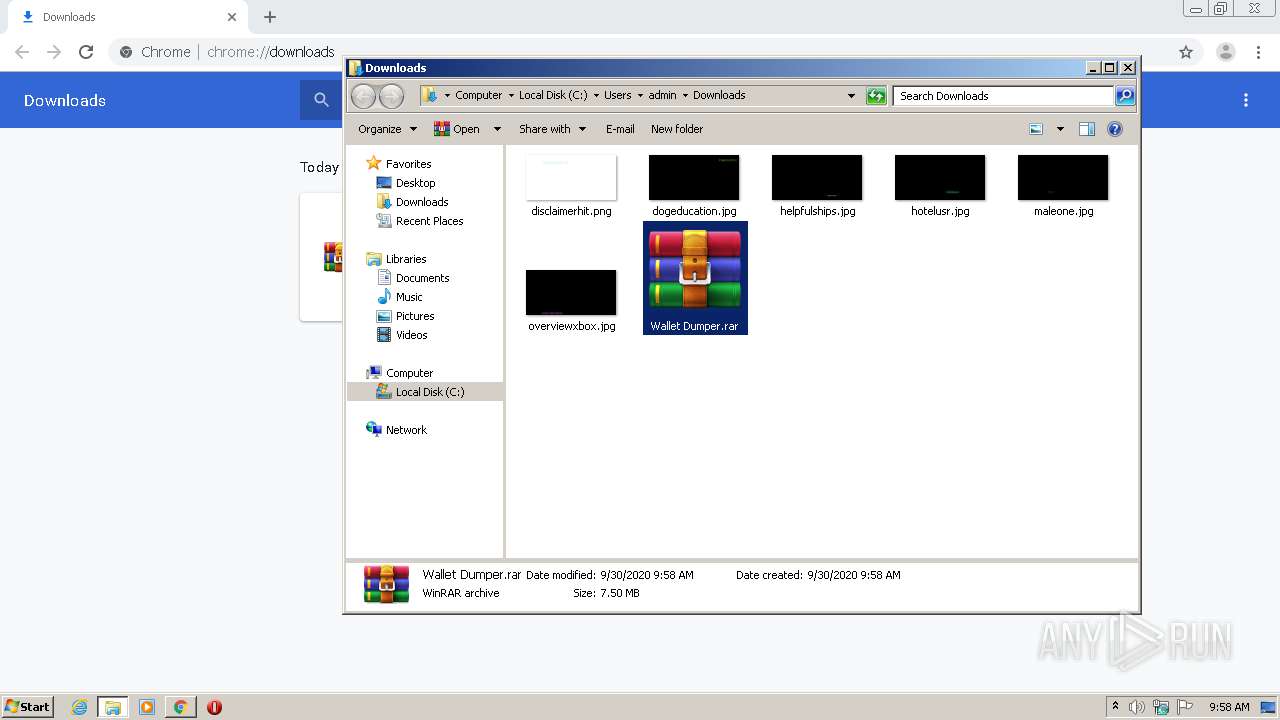
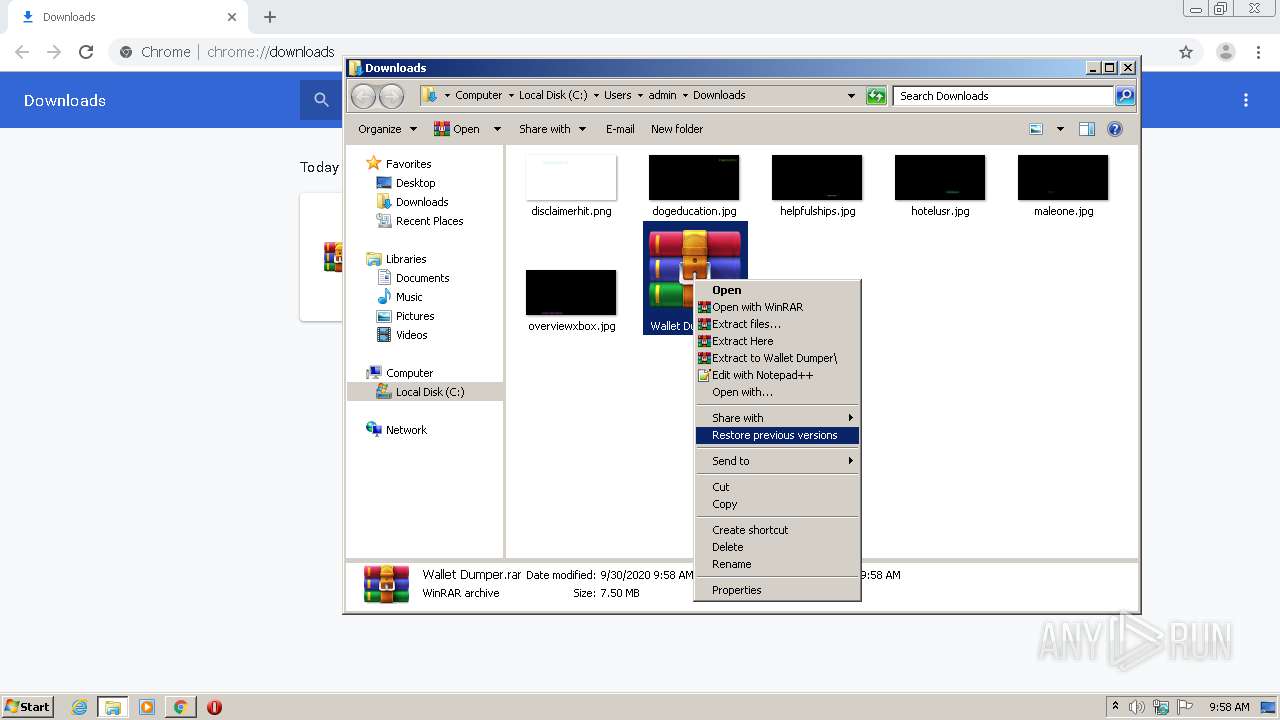
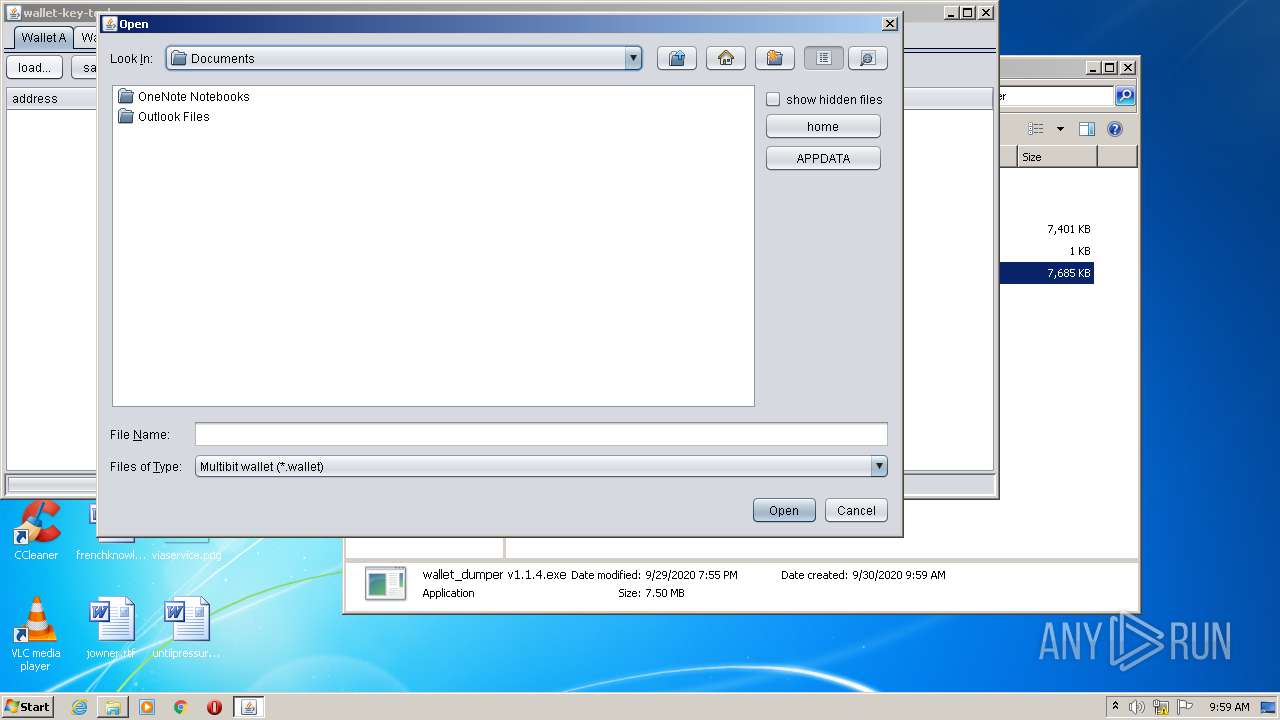
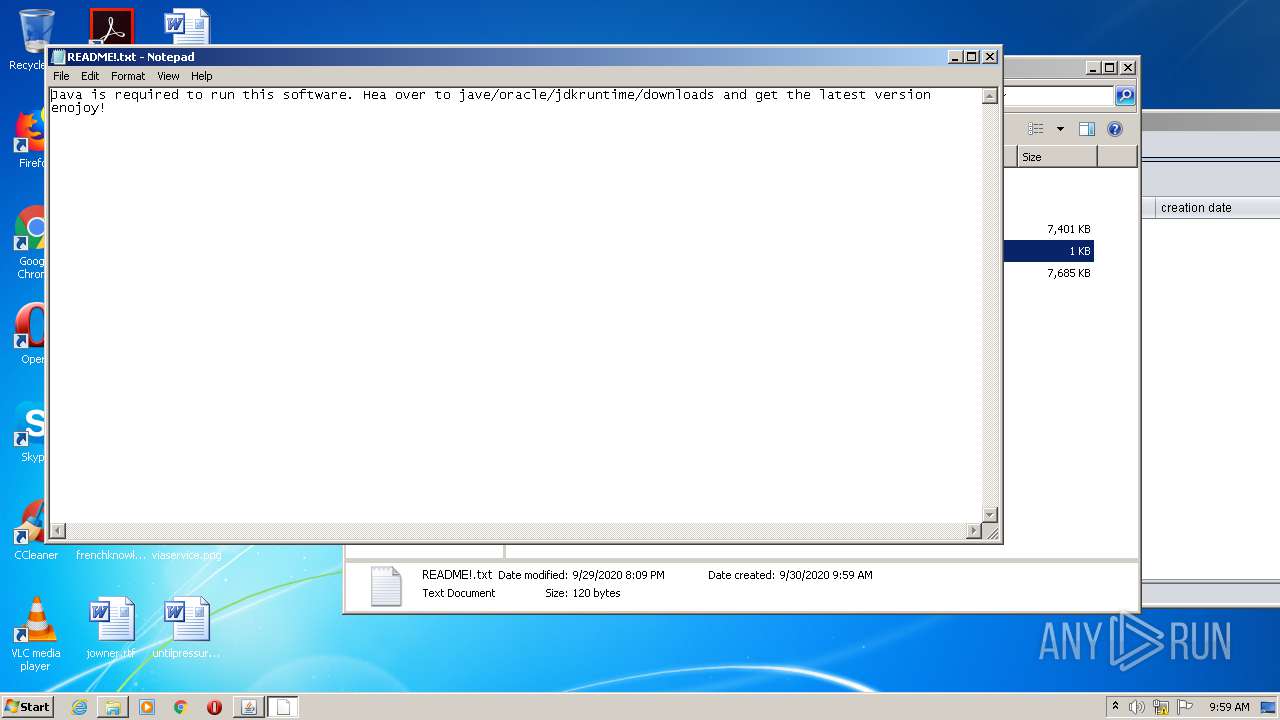
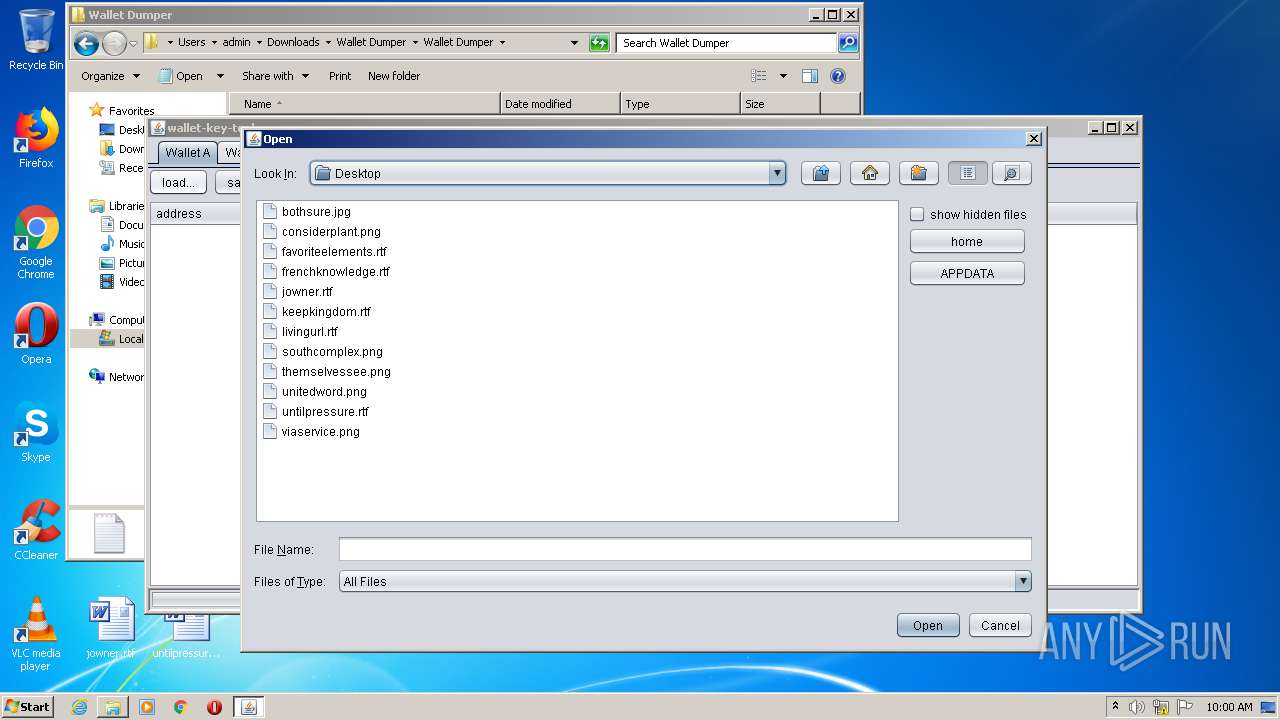
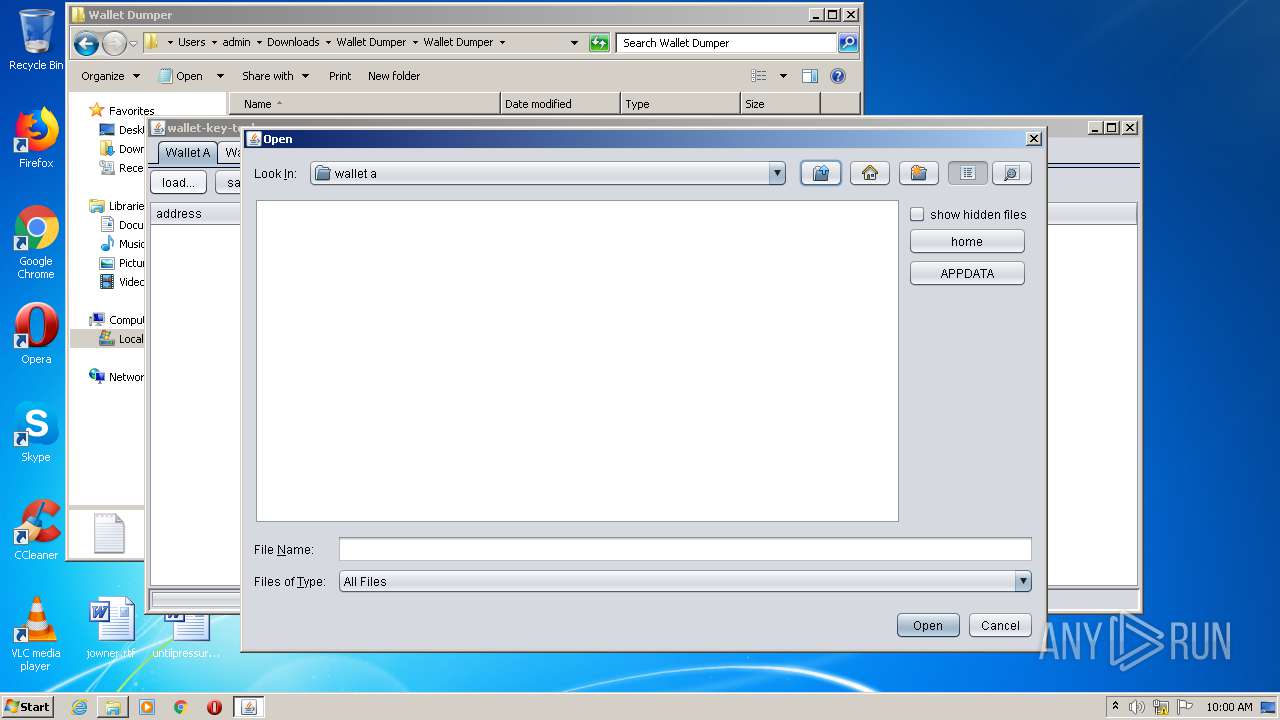
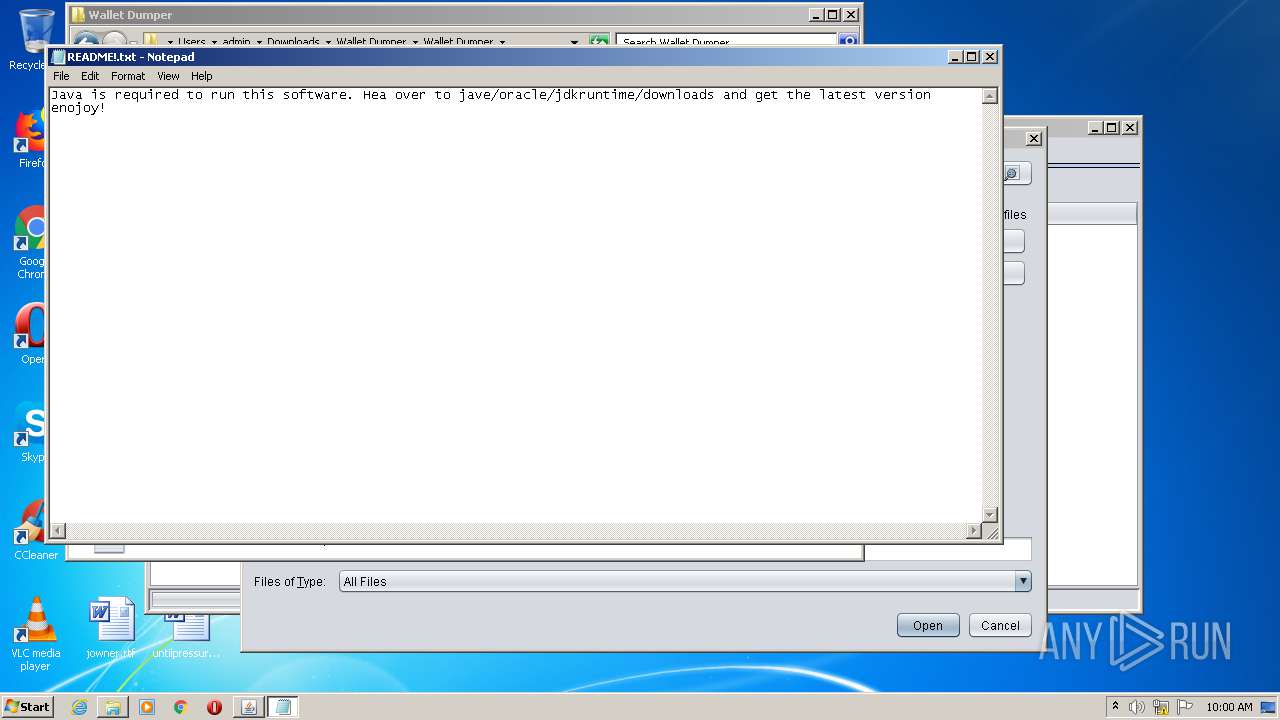
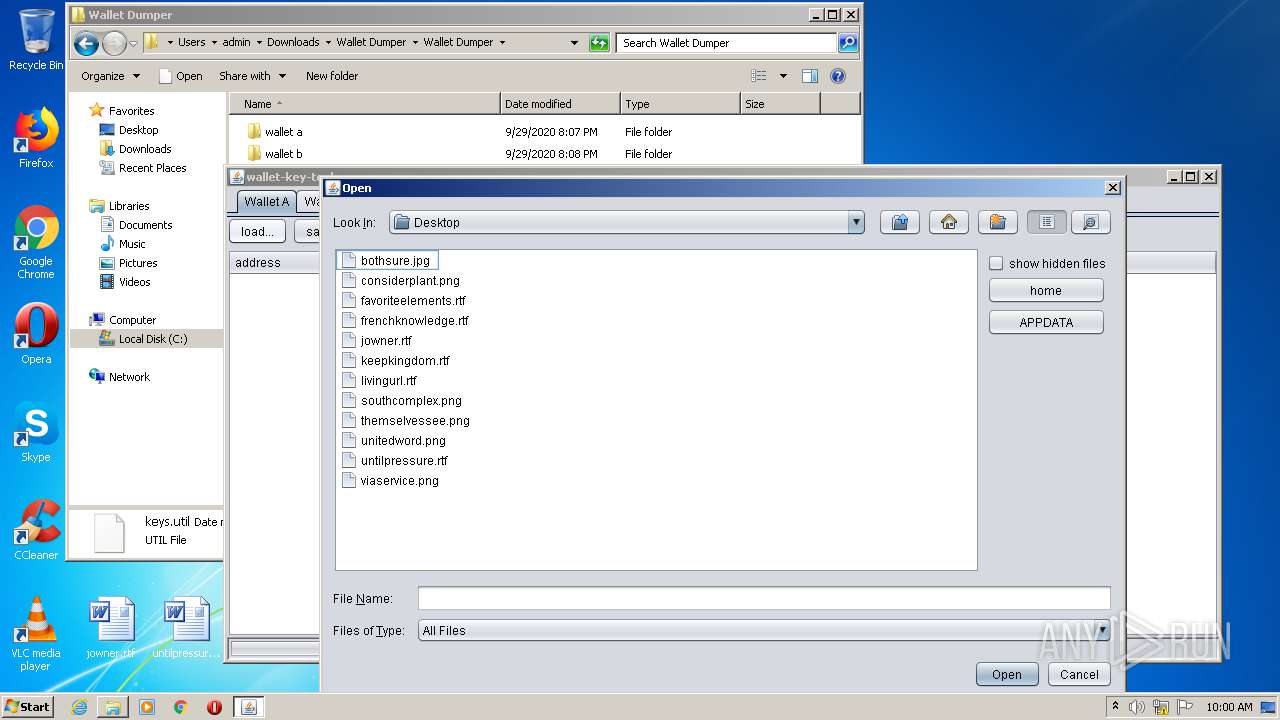
Manual execution by user
- WinRAR.exe (PID: 3232)
- NOTEPAD.EXE (PID: 860)
- NOTEPAD.EXE (PID: 2636)
- wallet_dumper v1.1.4.exe (PID: 2384)
Reads Internet Cache Settings
- chrome.exe (PID: 2492)
Application launched itself
- chrome.exe (PID: 2492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
28
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
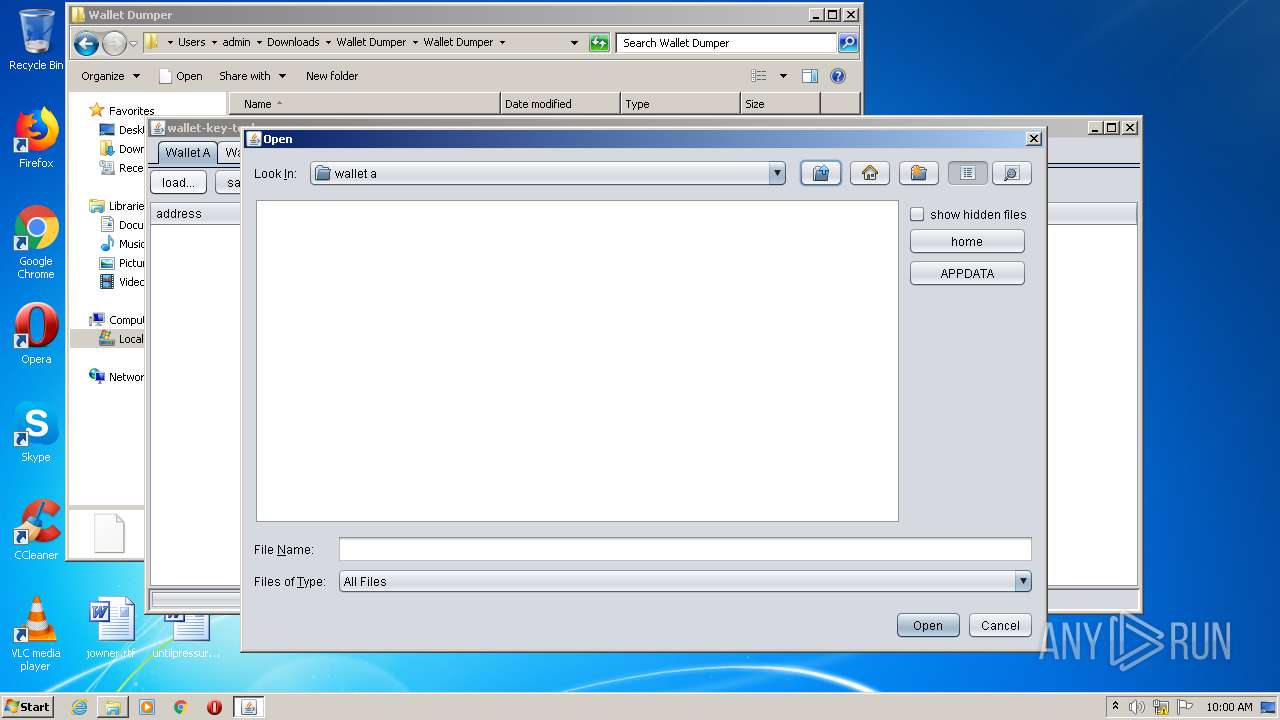
| 824 | "C:\Windows\System32\cmd.exe" /c keys.util | C:\Windows\System32\cmd.exe | — | wallet_dumper v1.1.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
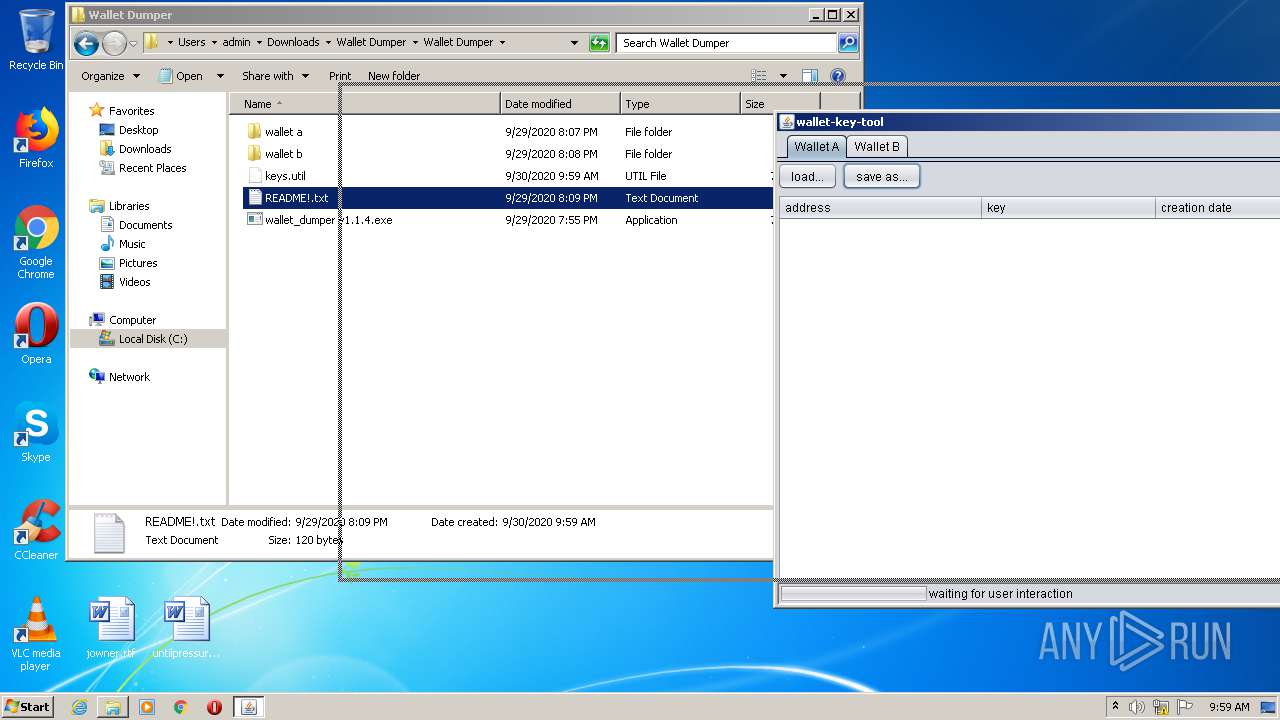
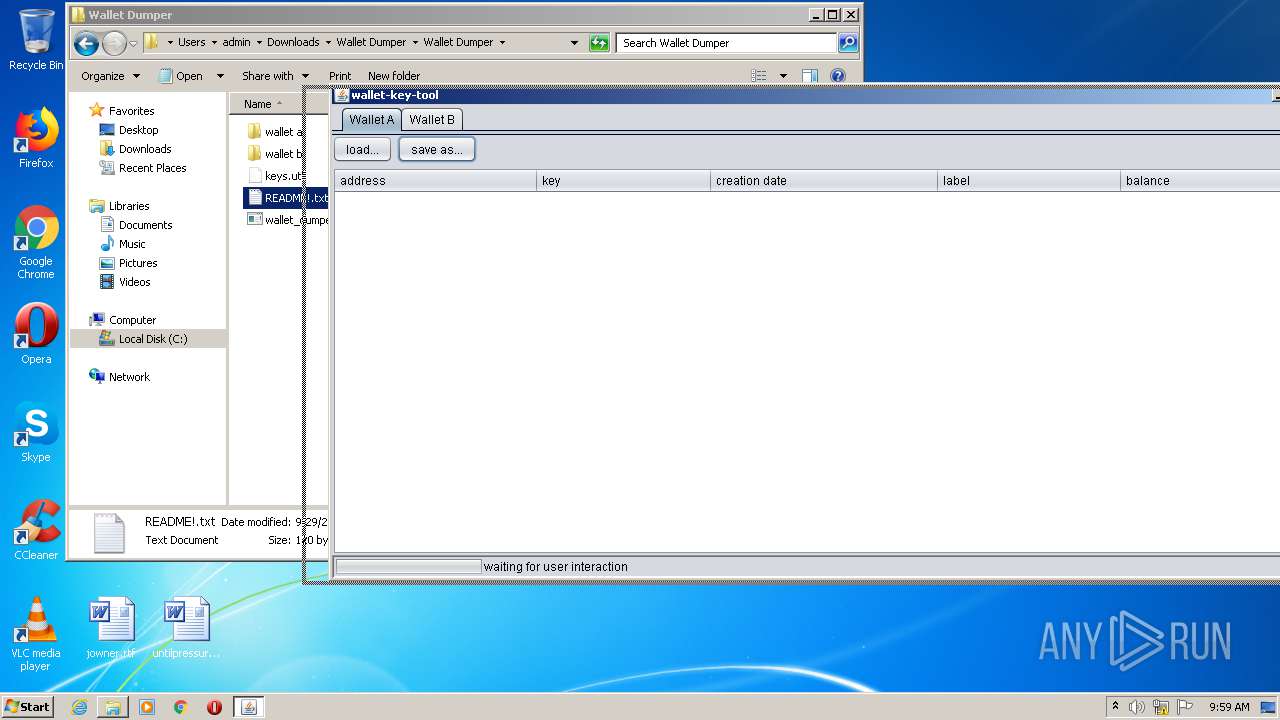
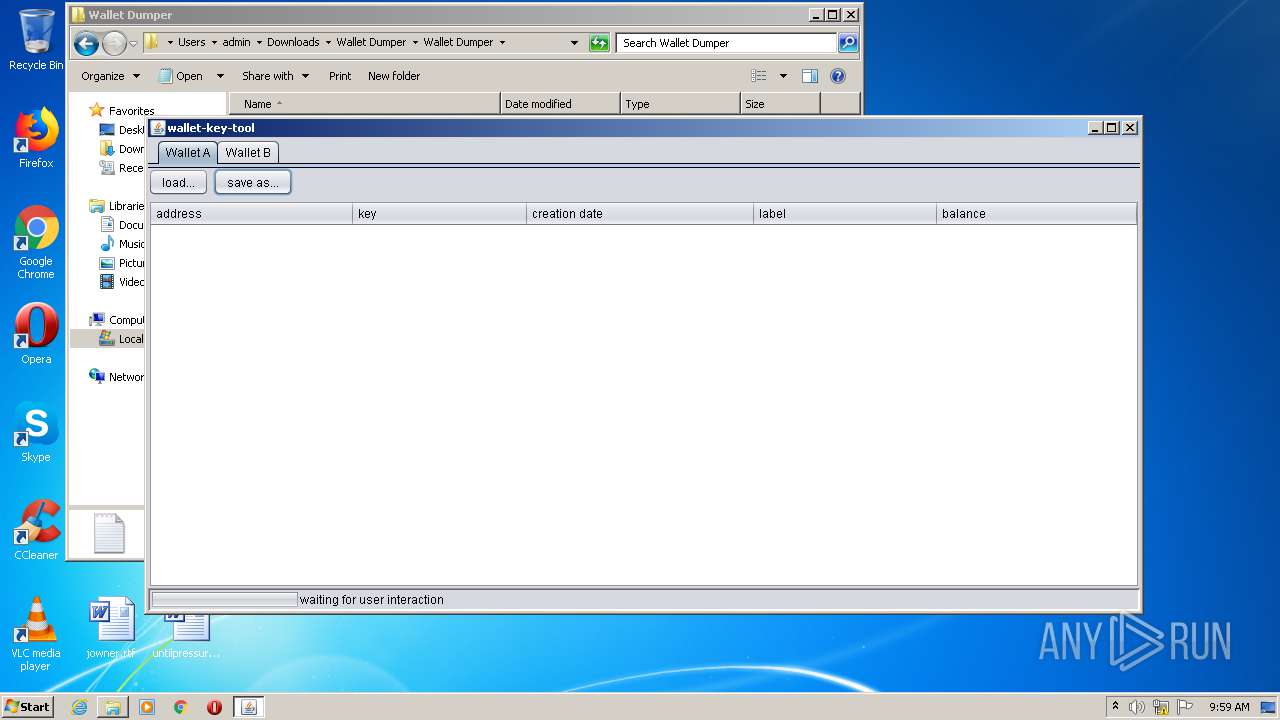
| 852 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -classpath "C:\Users\admin\Downloads\Wallet Dumper\Wallet Dumper\keys.util;lib\org.eclipse.xtend.lib-2.6.0.jar;lib\bitcoinj-0.11.2-MB-ALICE.jar;lib\slf4j-simple-1.7.7.jar;lib\miglayout-3.7.4.jar;lib\commons-cli-1.2.jar;lib\json-20140107.jar;lib\org.eclipse.xtext.xbase.lib-2.6.0.jar;lib\guava-14.0.1.jar;lib\sc-light-jdk15on-1.47.0.2.jar;lib\protobuf-java-2.5.0.jar;lib\jsr305-1.3.9.jar;lib\jcip-annotations-1.0.jar;lib\scrypt-1.3.3.jar;lib\netty-3.6.3.Final.jar;lib\slf4j-api-1.7.7.jar" prof7bit.bitcoin.wallettool.core.Main | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | keys.util | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 860 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\Wallet Dumper\Wallet Dumper\README!.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2628 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,11296904630636750683,845351218816549247,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8630759722001460845 --mojo-platform-channel-handle=2544 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,11296904630636750683,845351218816549247,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11737436355661995306 --mojo-platform-channel-handle=2588 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,11296904630636750683,845351218816549247,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12866358696676909858 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11296904630636750683,845351218816549247,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2789877939567100612 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,11296904630636750683,845351218816549247,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15340647528144710510 --mojo-platform-channel-handle=3364 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,11296904630636750683,845351218816549247,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2240682310859865913 --mojo-platform-channel-handle=3608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 321
Read events
1 166
Write events
151
Delete events
4
Modification events
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2492-13245929890343875 |
Value: 259 | |||
Executable files
2
Suspicious files
49
Text files
105
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F7448A2-9BC.pma | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8cd6b806-714b-4a49-8852-af5b4a039af2.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1aac6e.TMP | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF1aaceb.TMP | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF1aad39.TMP | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1aac9d.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
32
DNS requests
17
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1888 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
1888 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1888 | chrome.exe | 13.225.84.11:443 | djv99sxoqpv11.cloudfront.net | — | US | suspicious |
1888 | chrome.exe | 13.226.155.14:443 | counterry.club | — | US | unknown |
1888 | chrome.exe | 143.204.94.118:443 | providentsopport.site | — | US | suspicious |
1888 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1888 | chrome.exe | 52.86.219.129:443 | baconaces.pro | Amazon.com, Inc. | US | malicious |
1888 | chrome.exe | 13.226.155.123:443 | leneshedhous.club | — | US | unknown |
1888 | chrome.exe | 52.28.220.7:443 | smtwv.voluumtrk3.com | Amazon.com, Inc. | DE | unknown |
1888 | chrome.exe | 54.237.125.12:443 | baconaces.pro | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
baconaces.pro |
| shared |
counterry.club |
| whitelisted |
addressen.club |
| shared |
providentsopport.site |
| whitelisted |
leneshedhous.club |
| suspicious |