| download: | ClickShare-driver-updater |
| Full analysis: | https://app.any.run/tasks/fce27a49-fd06-471c-9675-38e93ddd5d3e |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 19:19:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D9D665B3CFC5DAFFBDB491976EB369A1 |
| SHA1: | FC2186D10B3F942357D03F2B800165C216796A49 |
| SHA256: | 9EA42280C6B6AA8BAF21E7D0A068F1C908B9492A2B30FB20B25E0CFF34E51CB7 |
| SSDEEP: | 196608:hM0lhBOhZp9Tjyn3w7RsR5duq6tMkCobY2GaoMn5kpNA7ph+3J4lHNH:H7OPDTOny0z9bobY2noMn5kpC7/I4lN |
MALICIOUS
Changes settings of System certificates
- ClickShare-driver-updater.tmp (PID: 3296)
SUSPICIOUS
Executable content was dropped or overwritten
- ClickShare-driver-updater.exe (PID: 3240)
- ClickShare-driver-updater.exe (PID: 2428)
- ClickShare-driver-updater.tmp (PID: 3296)
Reads Windows owner or organization settings
- ClickShare-driver-updater.tmp (PID: 3296)
Reads the Windows organization settings
- ClickShare-driver-updater.tmp (PID: 3296)
Reads Windows Product ID
- ClickShare-driver-updater.tmp (PID: 3296)
Reads the machine GUID from the registry
- ClickShare-driver-updater.tmp (PID: 3296)
Adds / modifies Windows certificates
- ClickShare-driver-updater.tmp (PID: 3296)
Reads the cookies of Google Chrome
- ClickShare-driver-updater.tmp (PID: 3296)
Reads the cookies of Mozilla Firefox
- ClickShare-driver-updater.tmp (PID: 3296)
Creates files in the user directory
- ClickShare-driver-updater.tmp (PID: 3296)
Reads the BIOS version
- ClickShare-driver-updater.tmp (PID: 3296)
INFO
Application was dropped or rewritten from another process
- ClickShare-driver-updater.tmp (PID: 2372)
- ClickShare-driver-updater.tmp (PID: 3296)
- reader.exe (PID: 3816)
Loads dropped or rewritten executable
- ClickShare-driver-updater.tmp (PID: 3296)
Creates files in the program directory
- ClickShare-driver-updater.tmp (PID: 3296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 79360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.1.3 |
| ProductVersionNumber: | 2.0.1.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
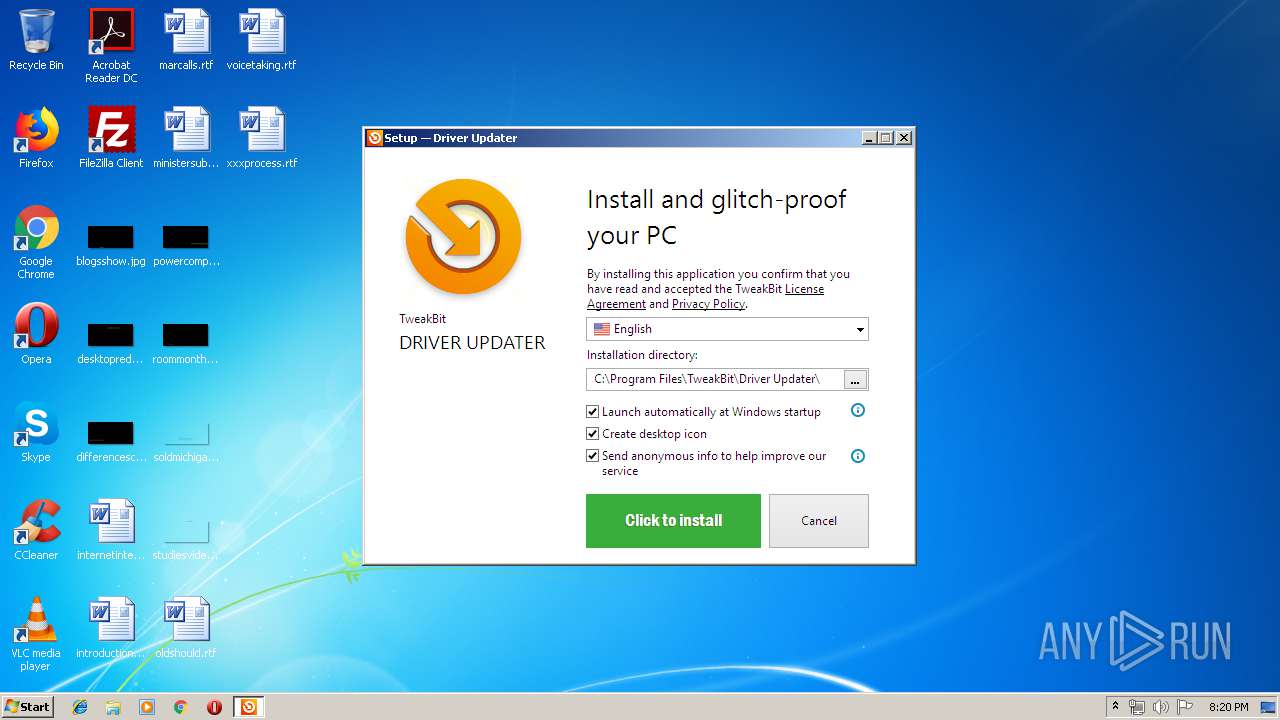
| CompanyName: | TweakBit |
| FileDescription: | TweakBit Driver Updater Installation File |
| FileVersion: | 2.x |
| LegalCopyright: | Copyright © 2013-2019 TweakBit Pty Ltd |
| ProductName: | TweakBit Driver Updater |
| ProductVersion: | 2.0.1.3 |
| OriginalFileName: | |
| InternalName: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | TweakBit |
| FileDescription: | TweakBit Driver Updater Installation File |
| FileVersion: | 2.x |
| LegalCopyright: | Copyright © 2013-2019 TweakBit Pty Ltd |
| ProductName: | TweakBit Driver Updater |
| ProductVersion: | 2.0.1.3 |
| OriginalFilename: | - |
| InternalName: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00011584 | 0x00011600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04035 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.01388 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.07394 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.31982 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.05236 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.5747 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 6.07053 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 6.0658 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.23334 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 3.59032 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2372 | "C:\Users\admin\AppData\Local\Temp\is-M9H2C.tmp\ClickShare-driver-updater.tmp" /SL5="$30112,12147832,146944,C:\Users\admin\AppData\Local\Temp\ClickShare-driver-updater.exe" | C:\Users\admin\AppData\Local\Temp\is-M9H2C.tmp\ClickShare-driver-updater.tmp | — | ClickShare-driver-updater.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2428 | "C:\Users\admin\AppData\Local\Temp\ClickShare-driver-updater.exe" /SPAWNWND=$30134 /NOTIFYWND=$30112 | C:\Users\admin\AppData\Local\Temp\ClickShare-driver-updater.exe | ClickShare-driver-updater.tmp | ||||||||||||
User: admin Company: TweakBit Integrity Level: HIGH Description: TweakBit Driver Updater Installation File Exit code: 0 Version: 2.x Modules
| |||||||||||||||
| 3240 | "C:\Users\admin\AppData\Local\Temp\ClickShare-driver-updater.exe" | C:\Users\admin\AppData\Local\Temp\ClickShare-driver-updater.exe | explorer.exe | ||||||||||||
User: admin Company: TweakBit Integrity Level: MEDIUM Description: TweakBit Driver Updater Installation File Exit code: 0 Version: 2.x Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\AppData\Local\Temp\is-TA41E.tmp\ClickShare-driver-updater.tmp" /SL5="$3011E,12147832,146944,C:\Users\admin\AppData\Local\Temp\ClickShare-driver-updater.exe" /SPAWNWND=$30134 /NOTIFYWND=$30112 | C:\Users\admin\AppData\Local\Temp\is-TA41E.tmp\ClickShare-driver-updater.tmp | ClickShare-driver-updater.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3816 | "C:\Users\admin\AppData\Local\Temp\is-JGDPI.tmp\reader.exe" "C:\Users\admin\AppData\Local\Temp\ClickShare-driver-updater.exe" "(x32)HKEY_LOCAL_MACHINE\Software\\TweakBit\\Driver Updater\\2.x\\Settings" | C:\Users\admin\AppData\Local\Temp\is-JGDPI.tmp\reader.exe | — | ClickShare-driver-updater.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
828
Read events
784
Write events
44
Delete events
0
Modification events
| (PID) Process: | (3296) ClickShare-driver-updater.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: E00C00007A96A08309FAD401 | |||
| (PID) Process: | (3296) ClickShare-driver-updater.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: B260B6374AD11F20D3960D81C8DD9B0F967C4CB7586C8857678477856DF4F7FB | |||
| (PID) Process: | (3296) ClickShare-driver-updater.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3296) ClickShare-driver-updater.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{58F3C249-F0C3-C01F-AA83-D035C692A535}\Version |
| Operation: | write | Name: | Assembly |
Value: 2E97ECB99F84CE2791473584F99FCC232E97ECB99F84CE2791473584F99FCC2388AD8CBB5ED3F66B83A8A2CDF194269C890BB34AEBD806E41A50D3BD9C0B4765894872A600C9A701F40C362CBC4DA7643C23163DDACBB3759A8B6FA21EF3BAC7D2C55D1D3BD8642EE6B6F5AECEBD7182FBD805F7FF1EA178E6BC1E1C9F5C0952 | |||
| (PID) Process: | (3296) ClickShare-driver-updater.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TweakBit\Driver Updater\2.x\Settings |
| Operation: | write | Name: | General.Language |
Value: ENU | |||
| (PID) Process: | (3296) ClickShare-driver-updater.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ClickShare-driver-updater_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3296) ClickShare-driver-updater.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ClickShare-driver-updater_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3296) ClickShare-driver-updater.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ClickShare-driver-updater_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3296) ClickShare-driver-updater.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ClickShare-driver-updater_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3296) ClickShare-driver-updater.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ClickShare-driver-updater_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
15
Suspicious files
6
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3296 | ClickShare-driver-updater.tmp | C:\Users\admin\AppData\Local\Temp\is-JGDPI.tmp\main.ini | text | |
MD5:— | SHA256:— | |||
| 3296 | ClickShare-driver-updater.tmp | C:\Users\admin\AppData\Local\Temp\is-JGDPI.tmp\DriverUpdater.exe | odttf | |
MD5:— | SHA256:— | |||
| 2428 | ClickShare-driver-updater.exe | C:\Users\admin\AppData\Local\Temp\is-TA41E.tmp\ClickShare-driver-updater.tmp | executable | |
MD5:— | SHA256:— | |||
| 3296 | ClickShare-driver-updater.tmp | C:\ProgramData\TweakBit\Driver Updater\2.x\$$Cookies159602495 | — | |
MD5:— | SHA256:— | |||
| 3296 | ClickShare-driver-updater.tmp | C:\ProgramData\TweakBit\Driver Updater\2.x\$$Databases.db159602495 | — | |
MD5:— | SHA256:— | |||
| 3296 | ClickShare-driver-updater.tmp | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3296 | ClickShare-driver-updater.tmp | C:\ProgramData\TweakBit\Driver Updater\2.x\$$History159602526 | — | |
MD5:— | SHA256:— | |||
| 3296 | ClickShare-driver-updater.tmp | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3240 | ClickShare-driver-updater.exe | C:\Users\admin\AppData\Local\Temp\is-M9H2C.tmp\ClickShare-driver-updater.tmp | executable | |
MD5:— | SHA256:— | |||
| 3296 | ClickShare-driver-updater.tmp | C:\Users\admin\AppData\Local\Temp\is-JGDPI.tmp\BrowserHelper.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3296 | ClickShare-driver-updater.tmp | POST | 200 | 172.217.23.174:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3296 | ClickShare-driver-updater.tmp | POST | 200 | 172.217.23.174:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3296 | ClickShare-driver-updater.tmp | POST | 200 | 172.217.23.174:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3296 | ClickShare-driver-updater.tmp | 104.237.131.139:443 | tweakbit.com | Linode, LLC | US | malicious |
3296 | ClickShare-driver-updater.tmp | 172.217.23.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tweakbit.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |