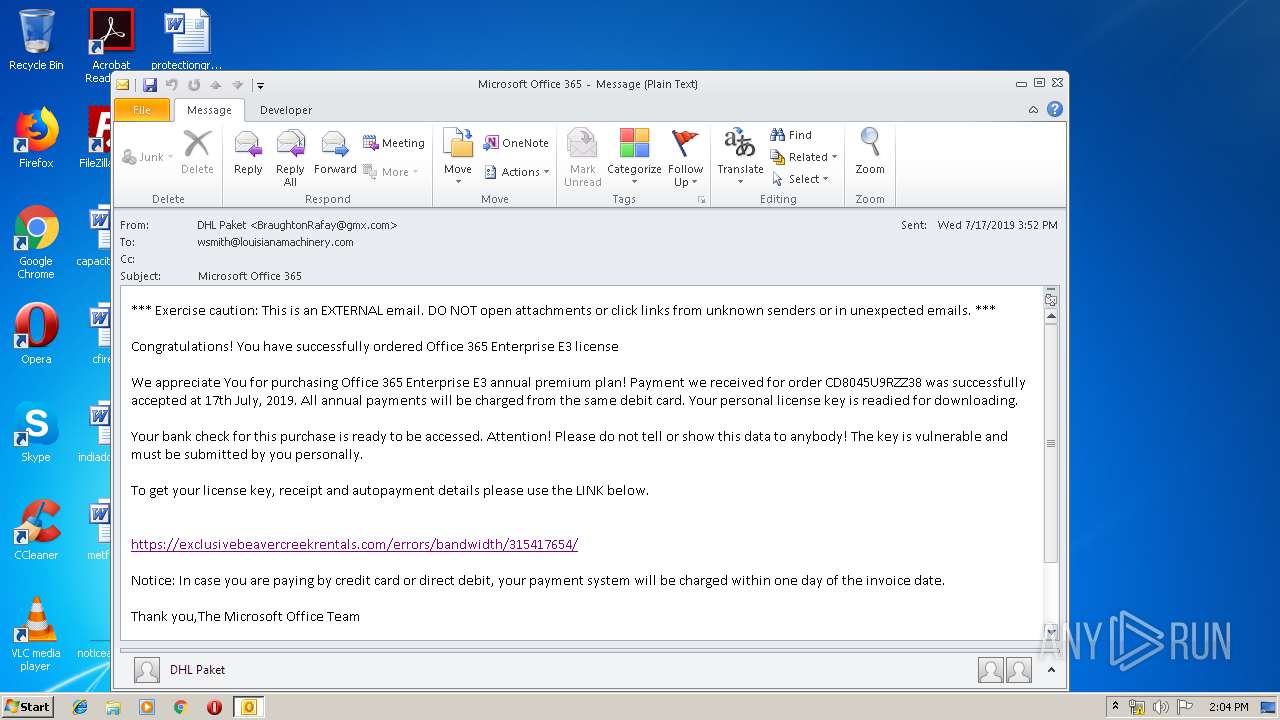
| File name: | 365.msg |
| Full analysis: | https://app.any.run/tasks/526cfb7d-7510-4765-84fc-0c670a045d32 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 13:03:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
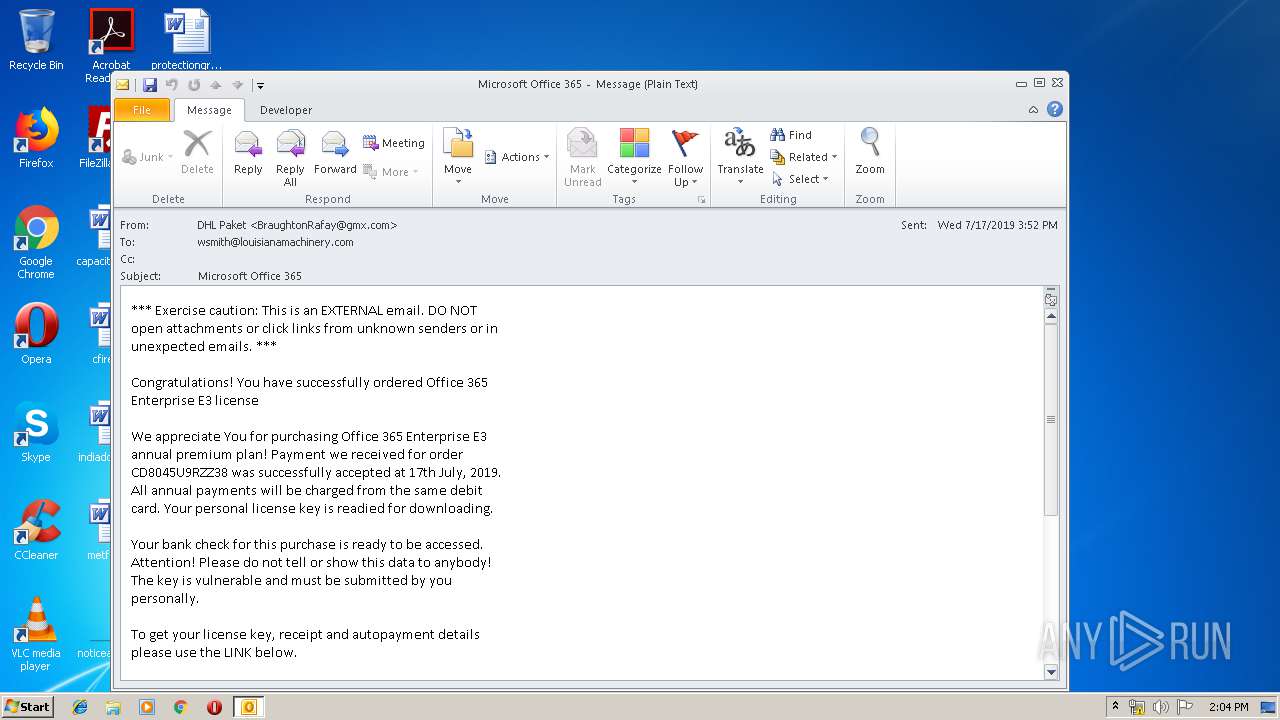
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | EFB2048DA1657C148C4B53117798F156 |
| SHA1: | A991806CBCE86450663EDC34C9F86B0D0E8842CF |
| SHA256: | 9E4CAB3F560C6A6B4AD13C99AB341C8CD35AB44282CDF9B63E2313F53430F58B |
| SSDEEP: | 768:Pj/TouGwgDzusKgaGik0bnG9yGrNfcKO8hX6lACa:pIdG |
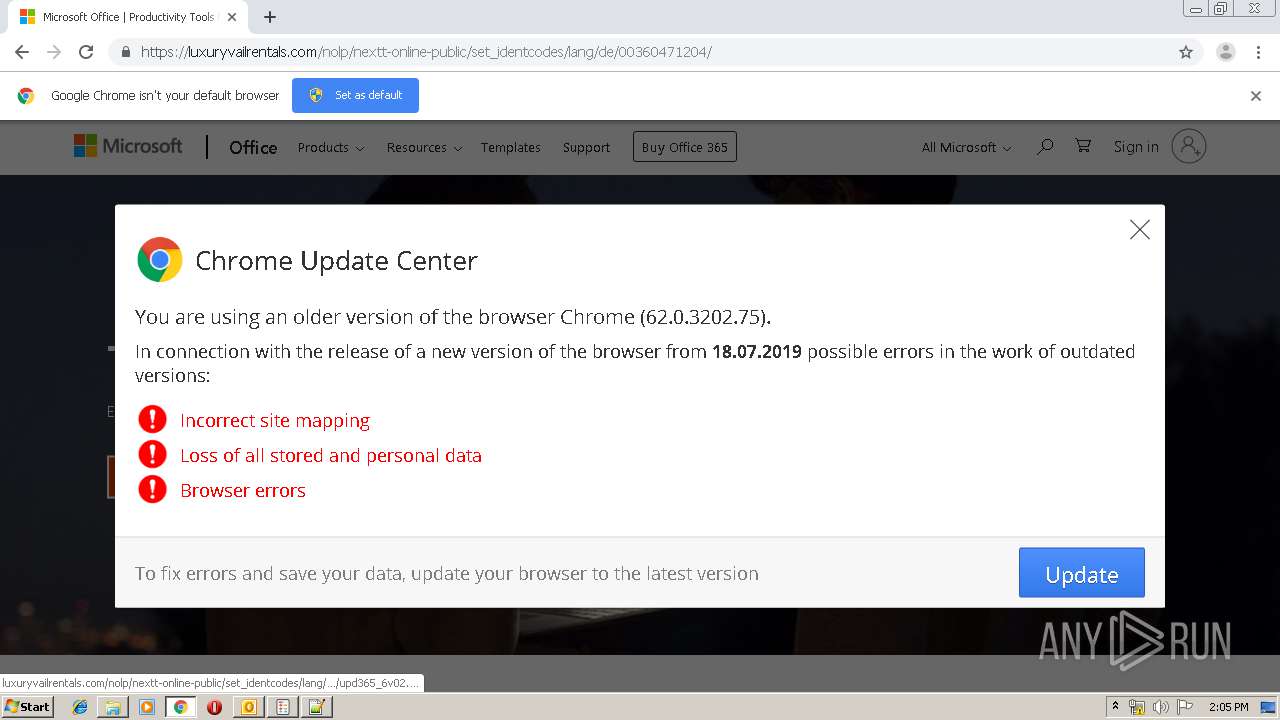
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3512)
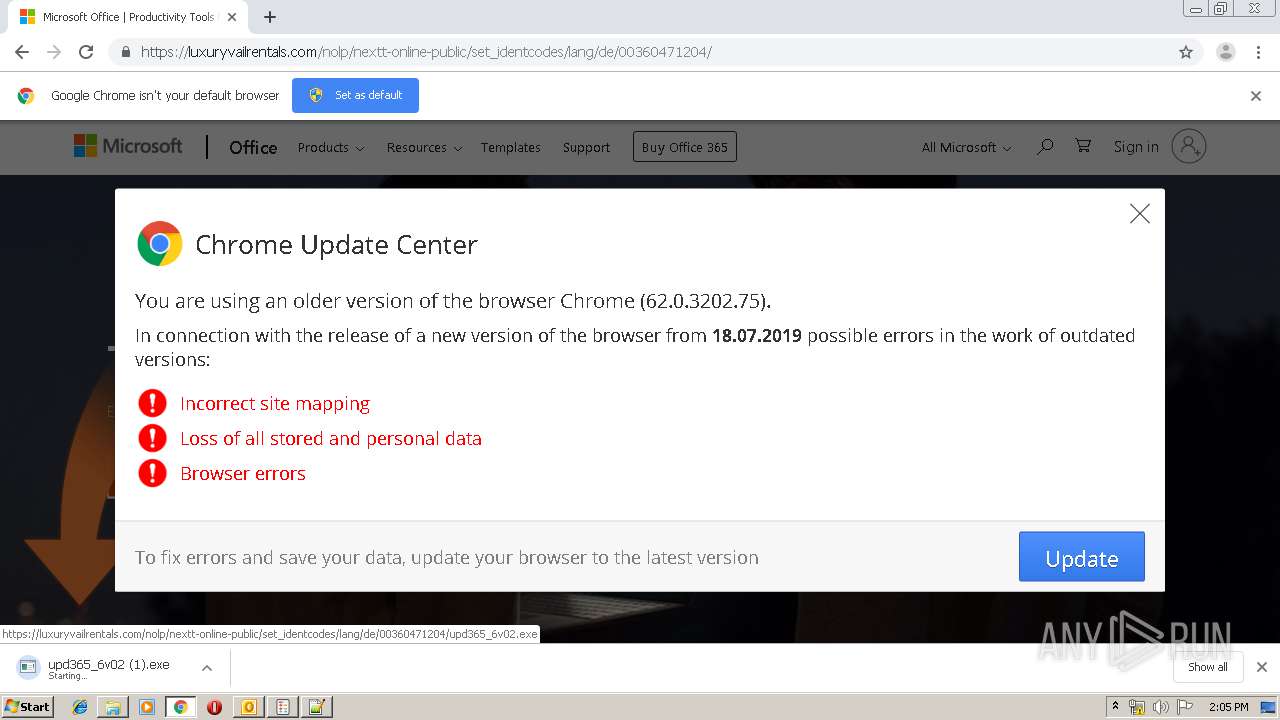
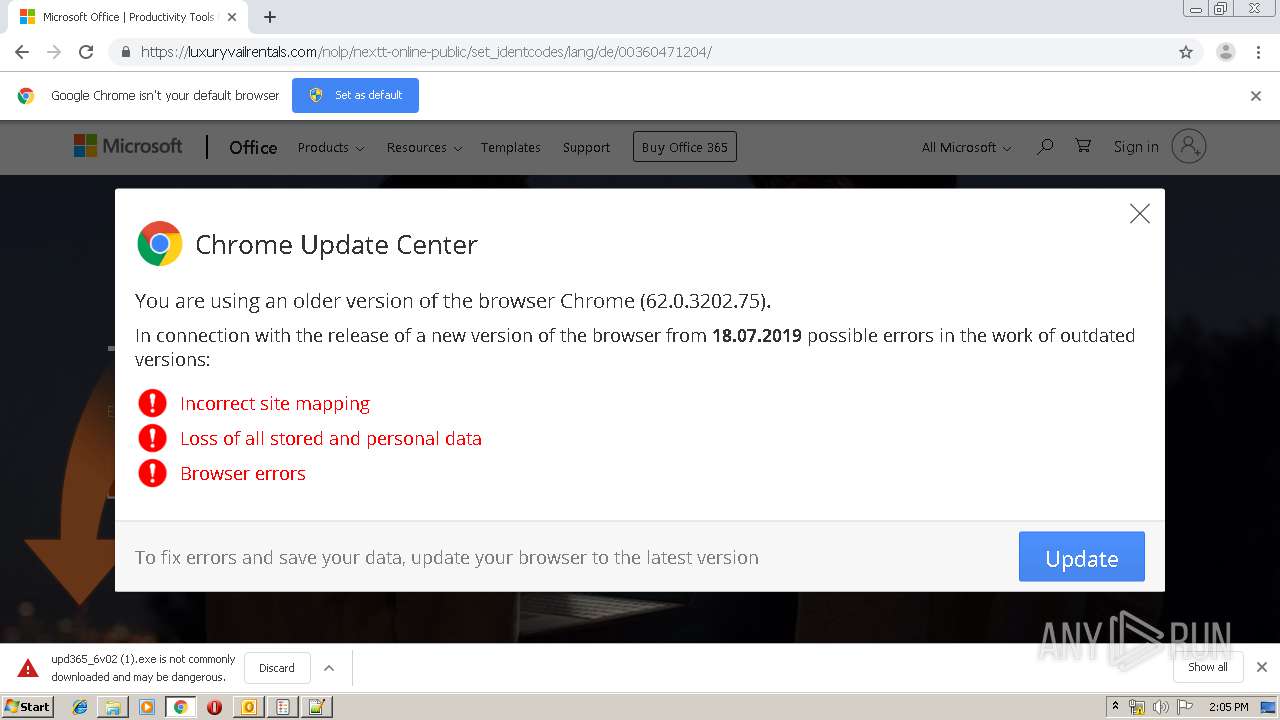
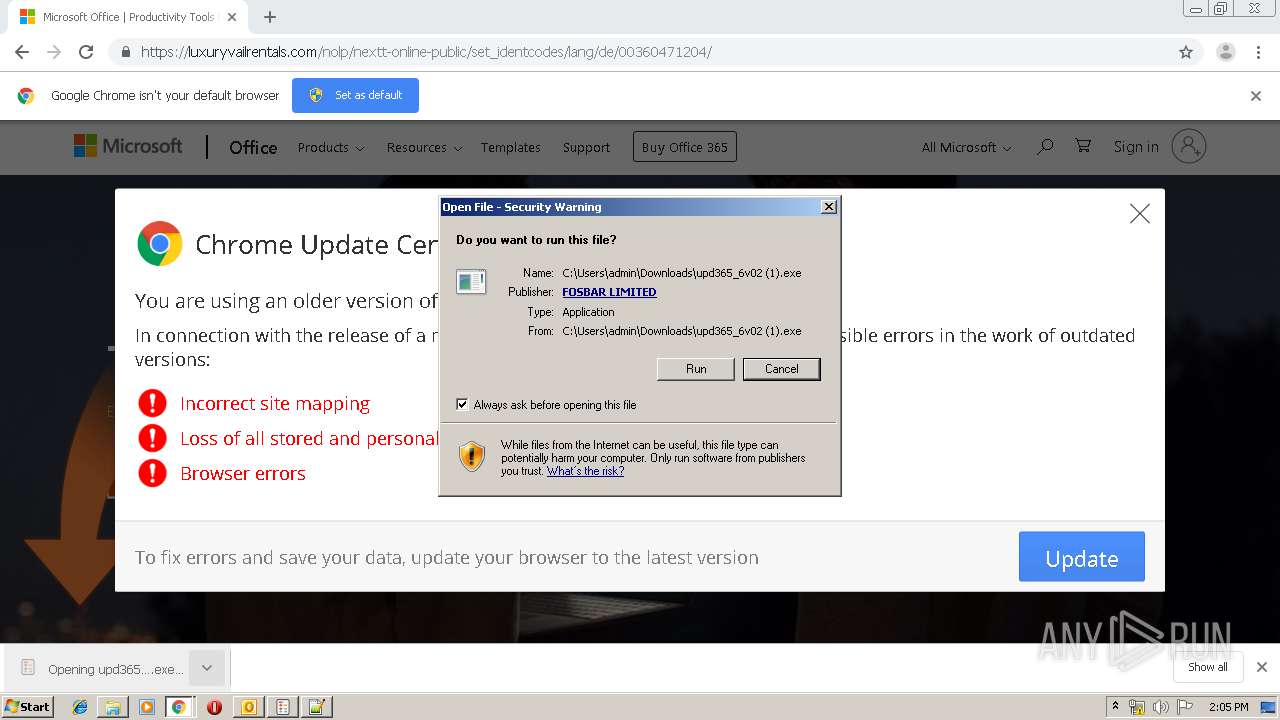
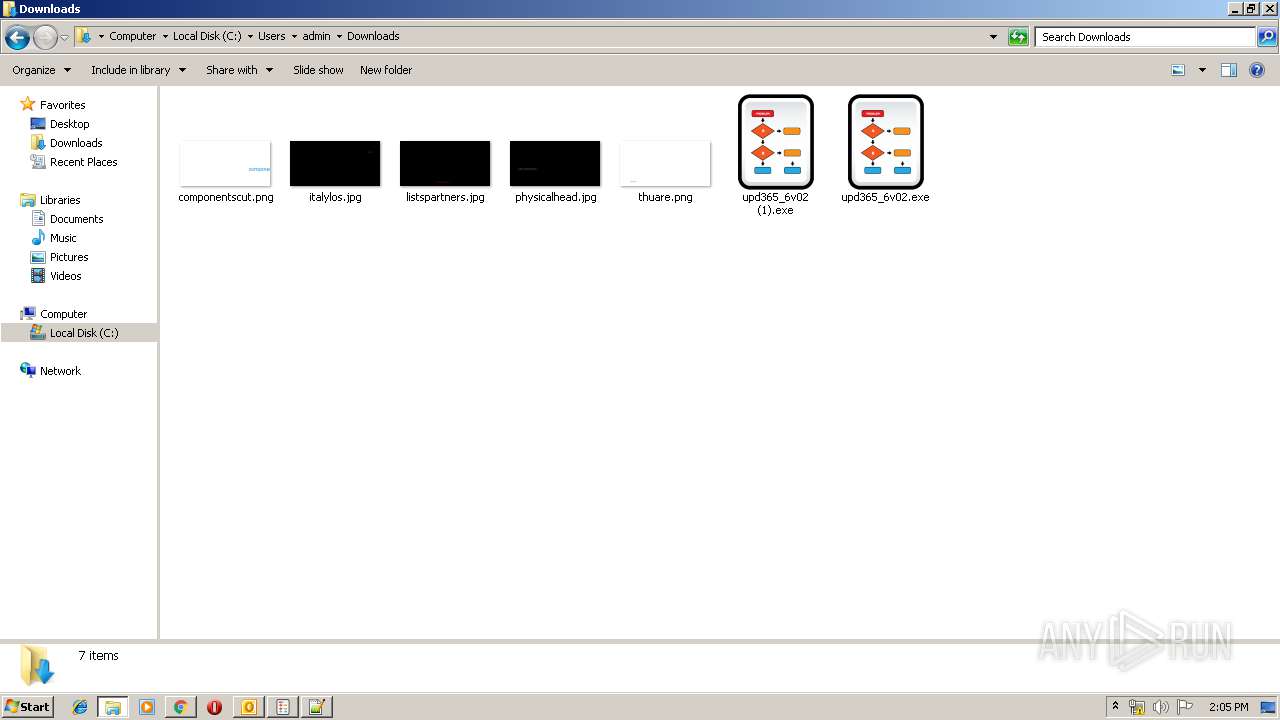
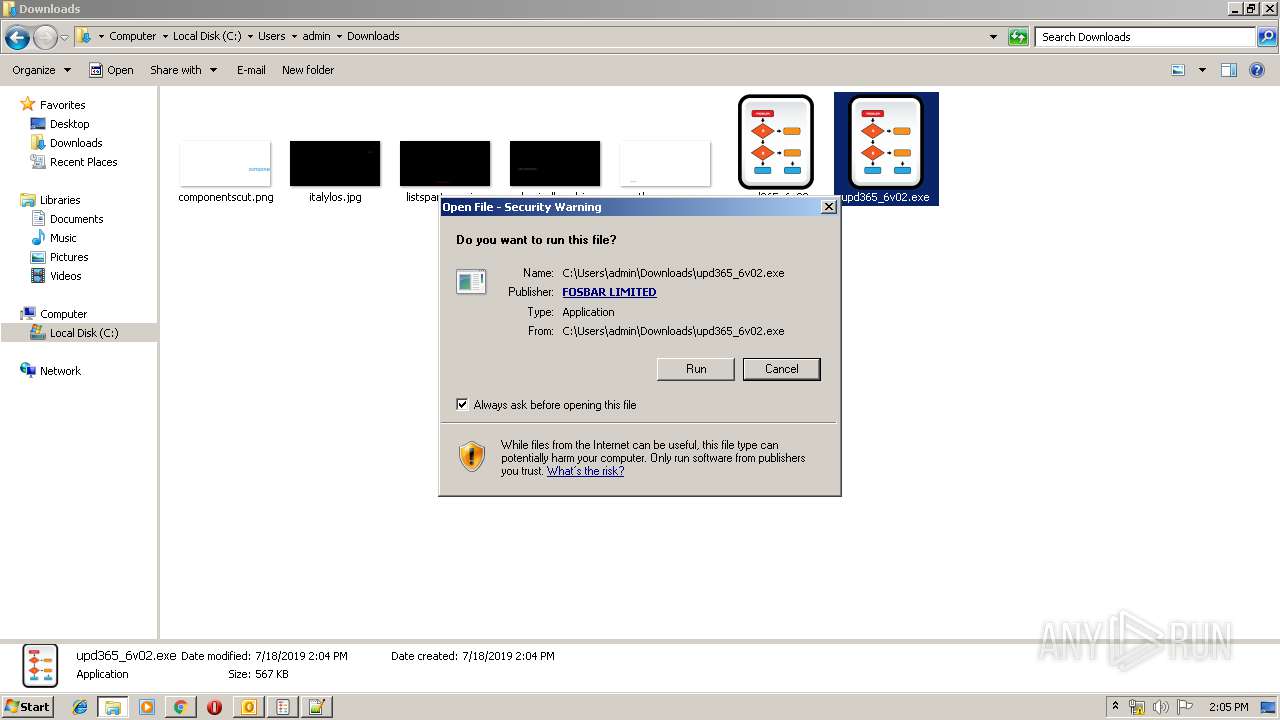
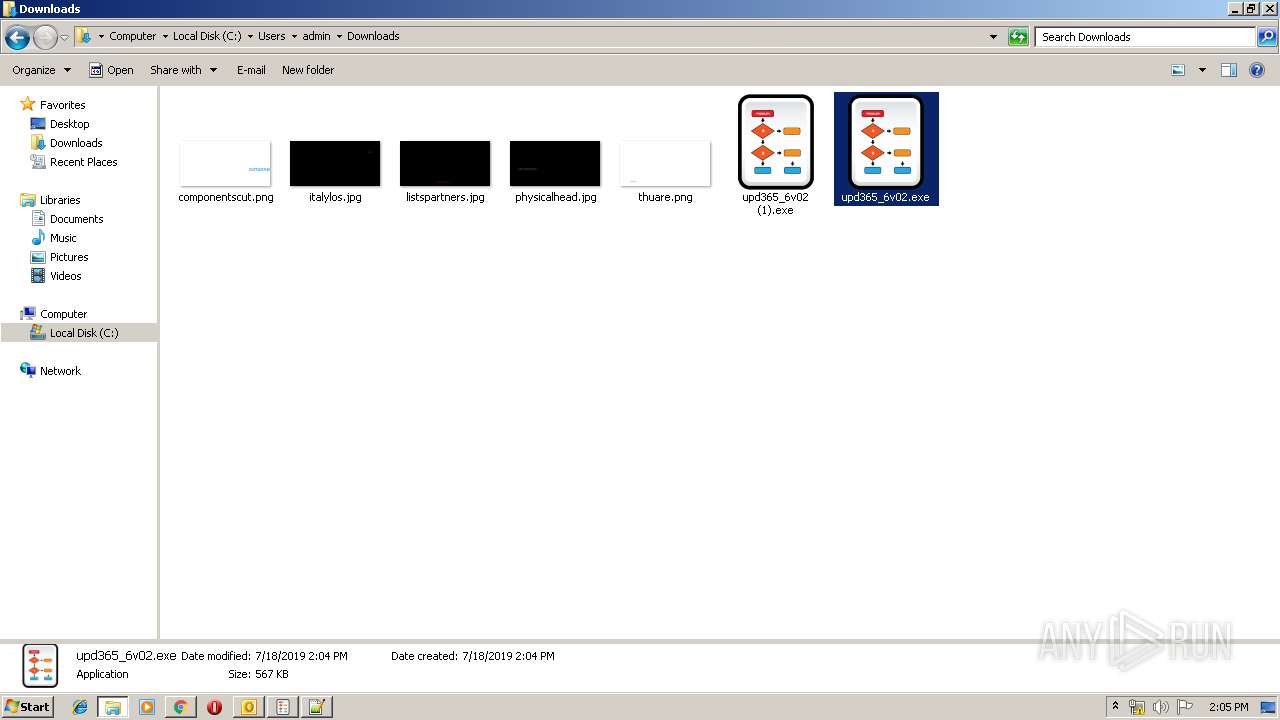
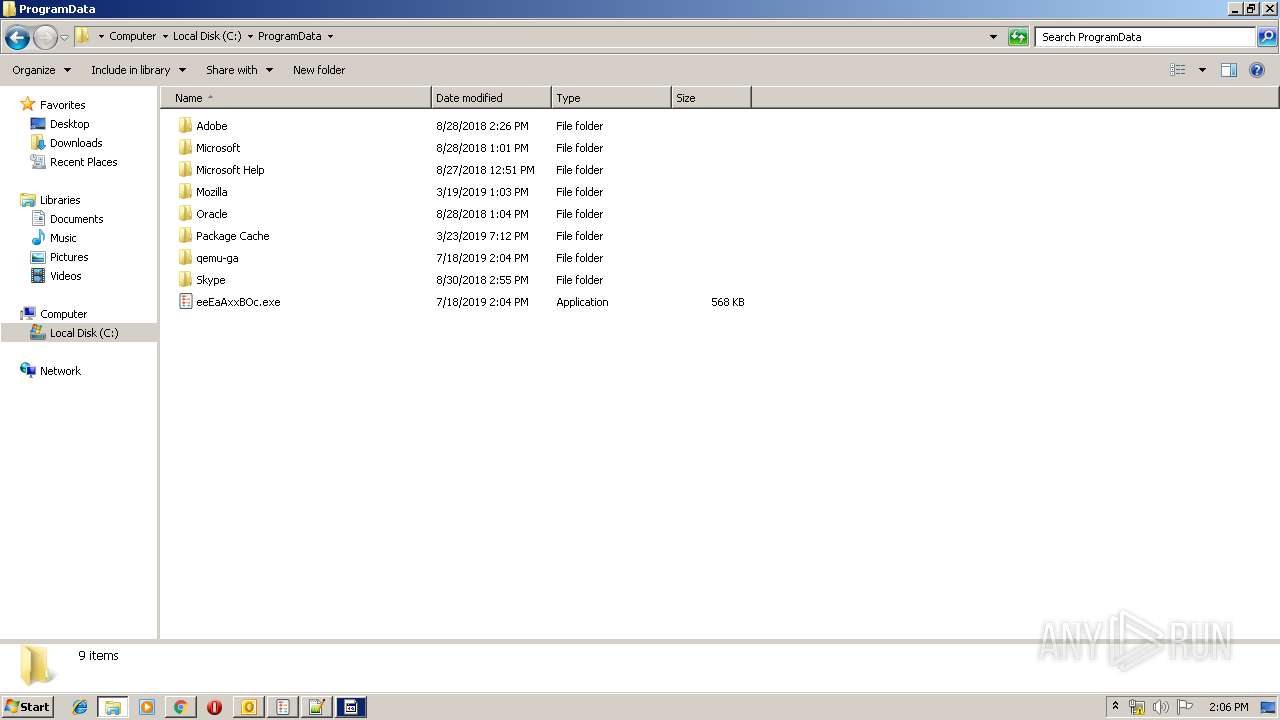
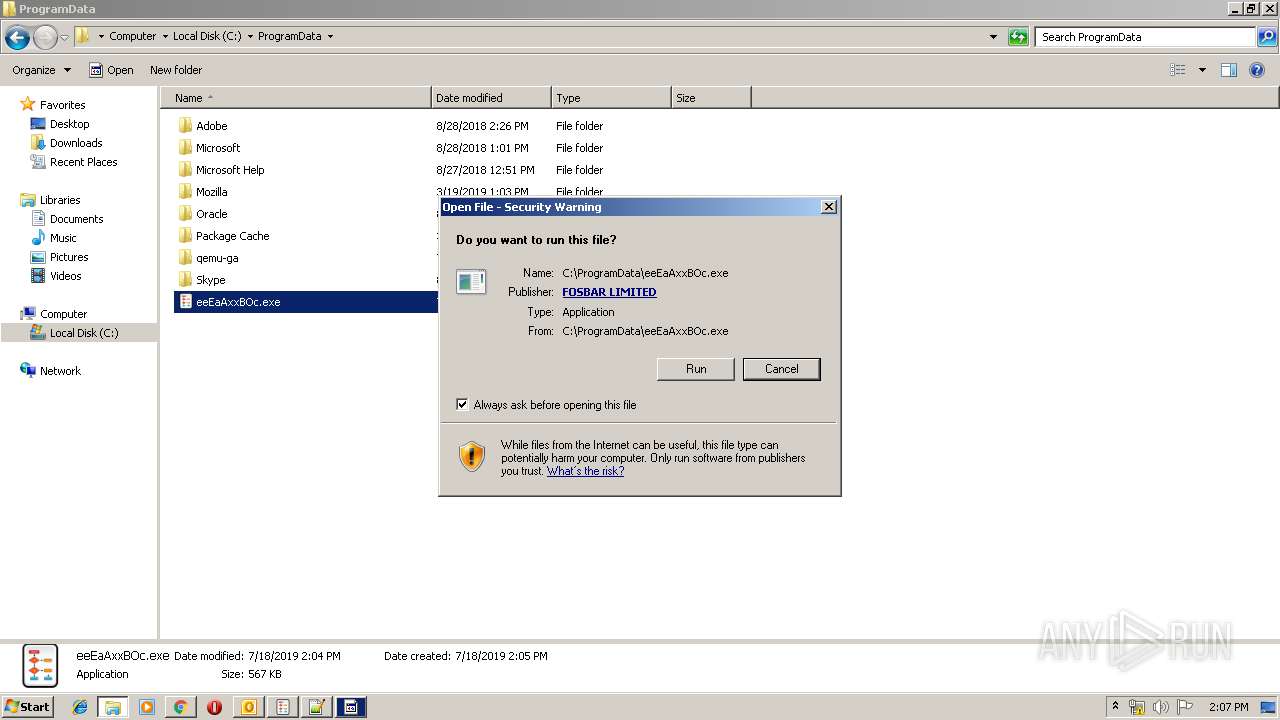
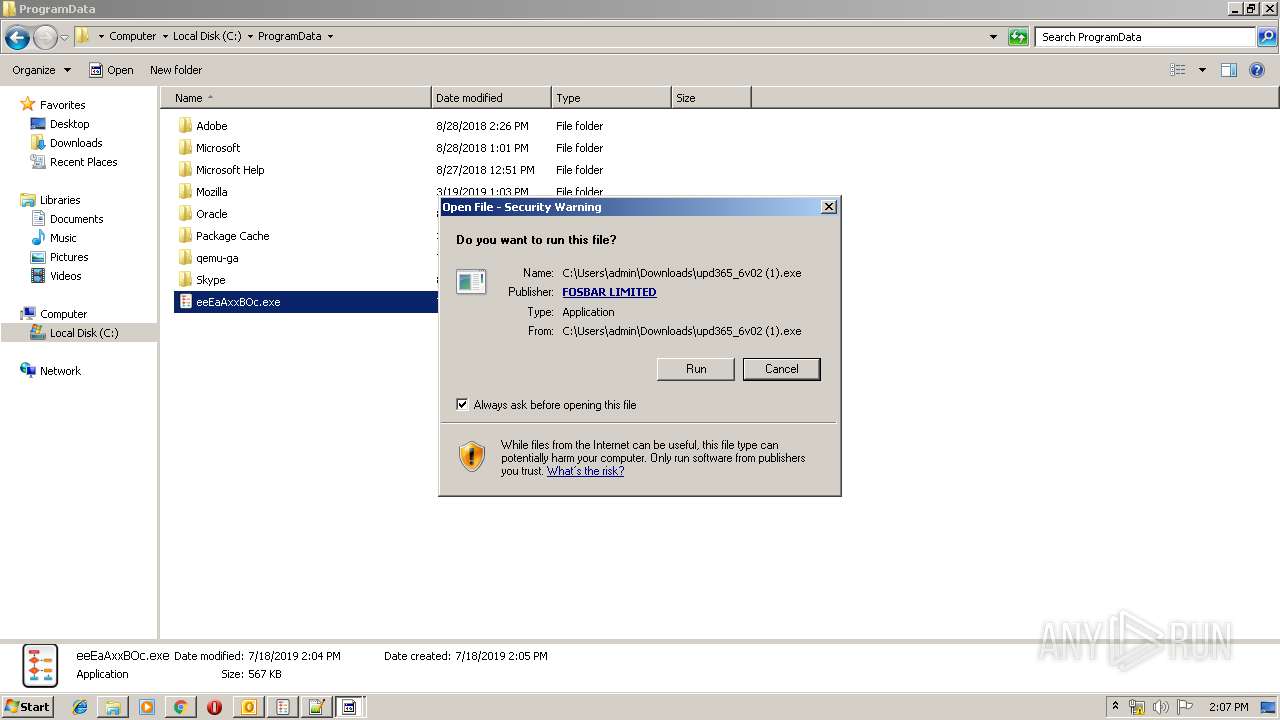
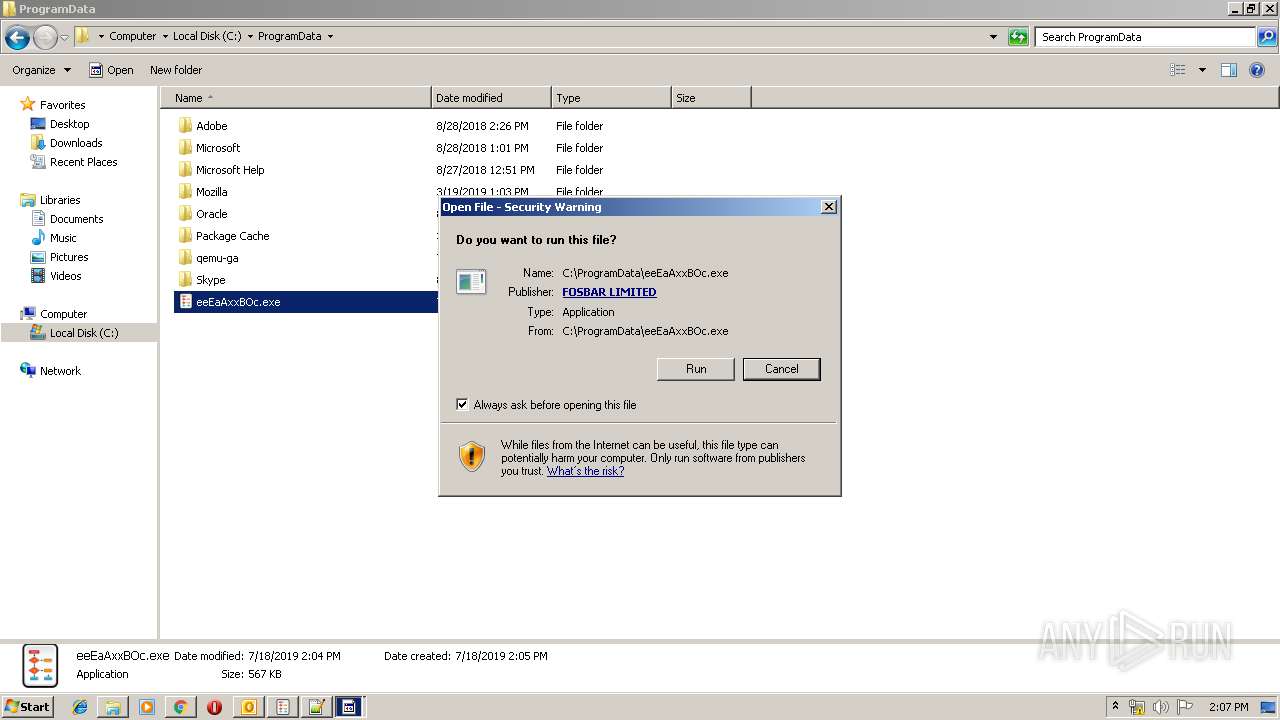
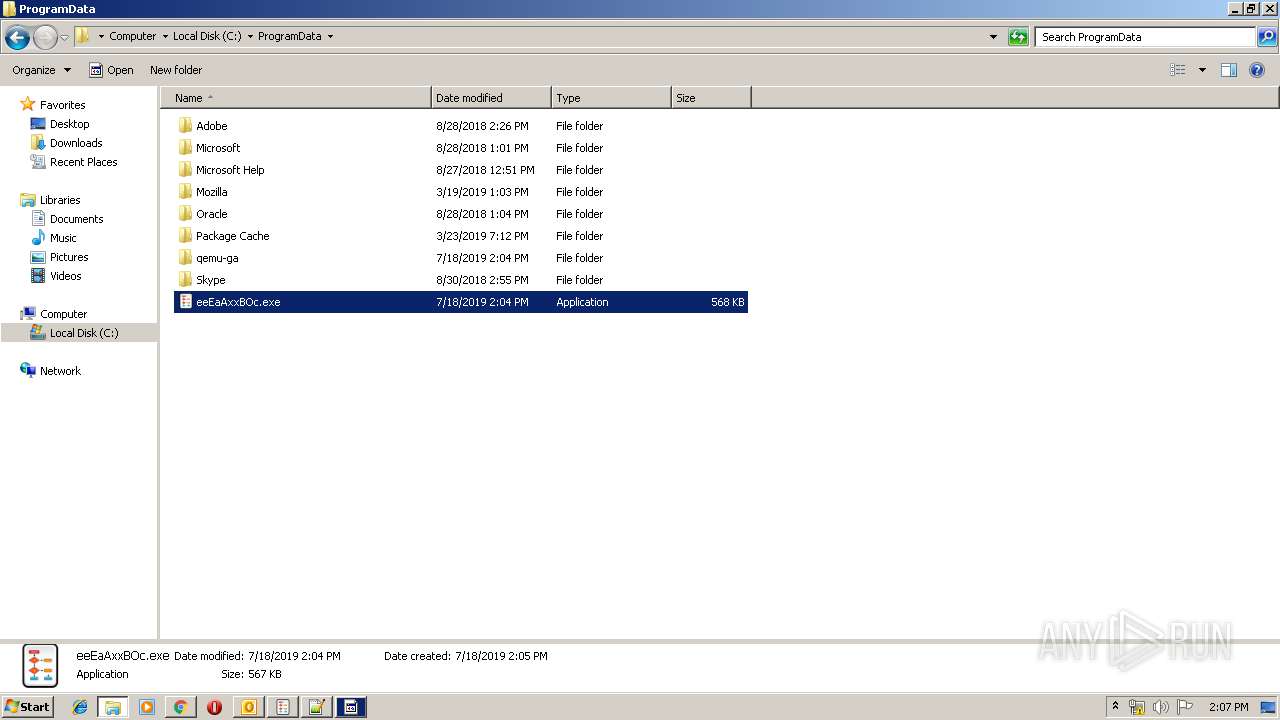
Application was dropped or rewritten from another process
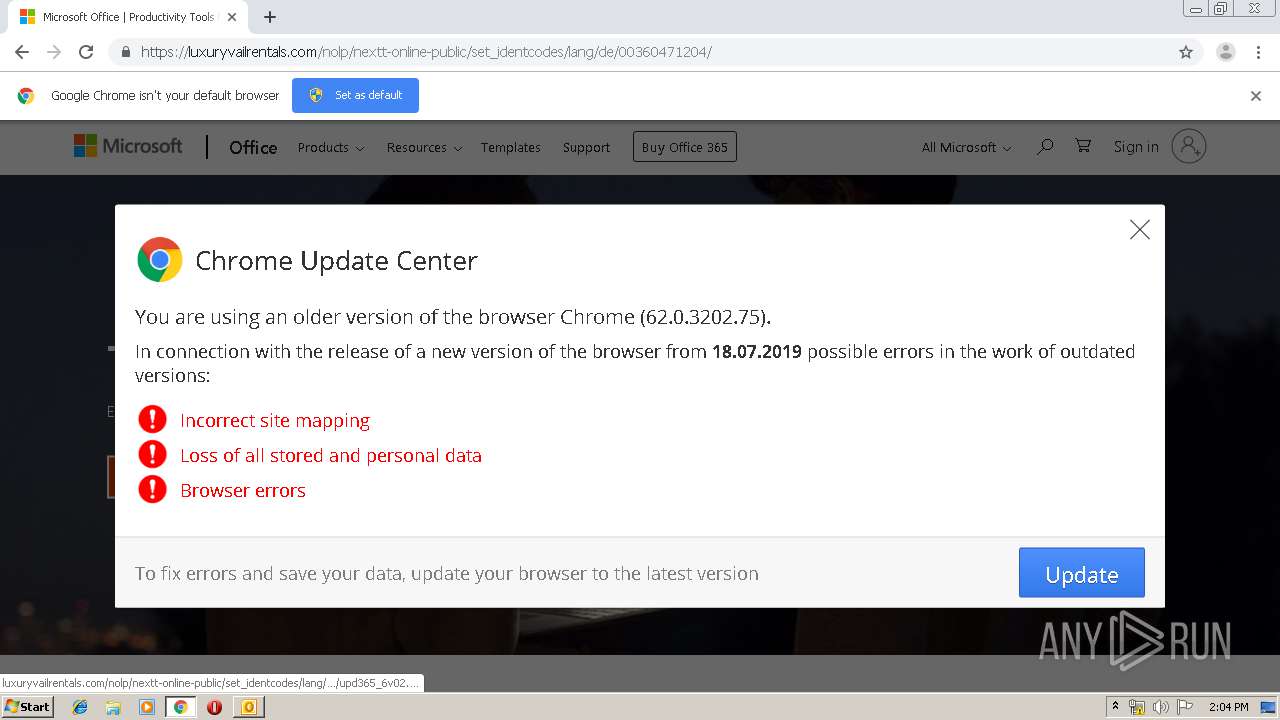
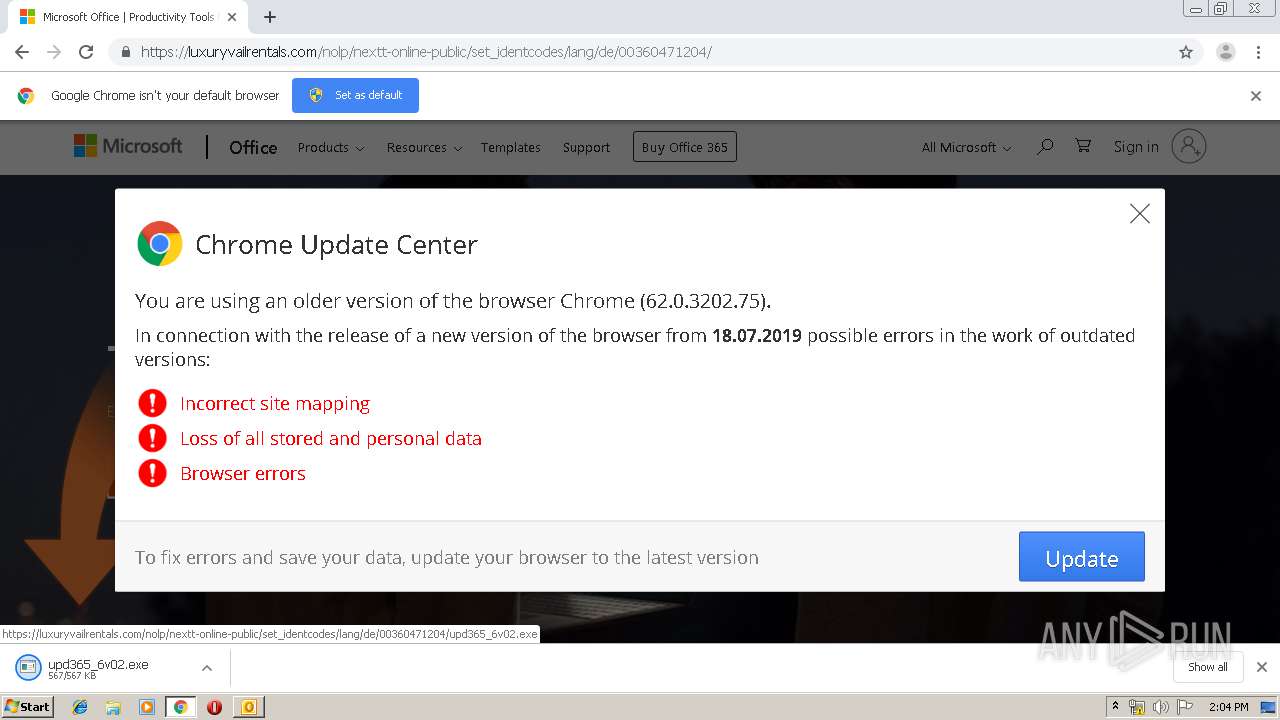
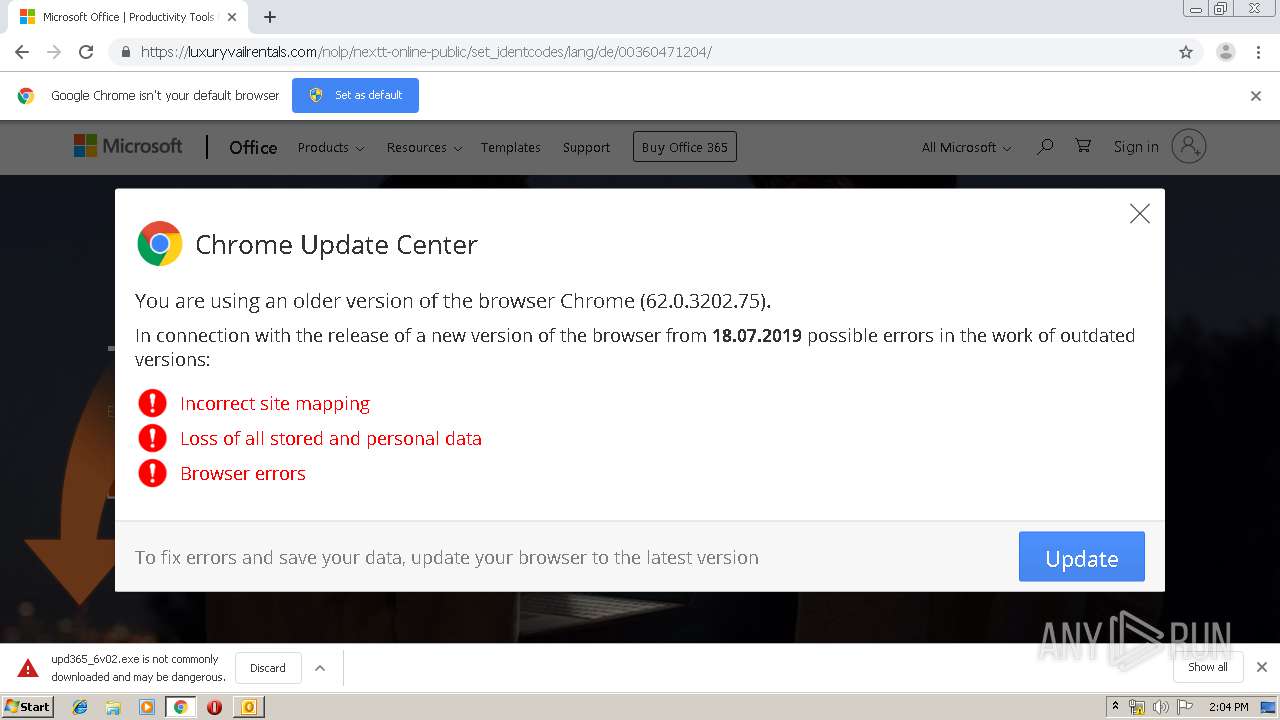
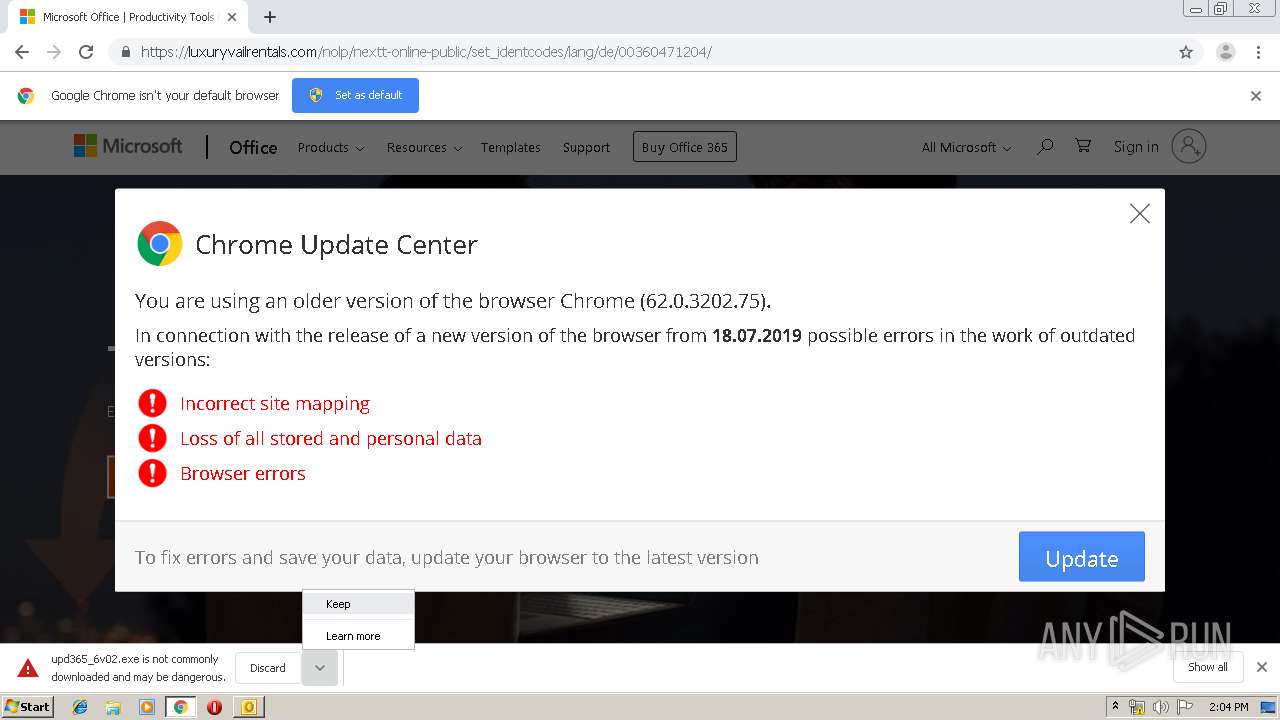
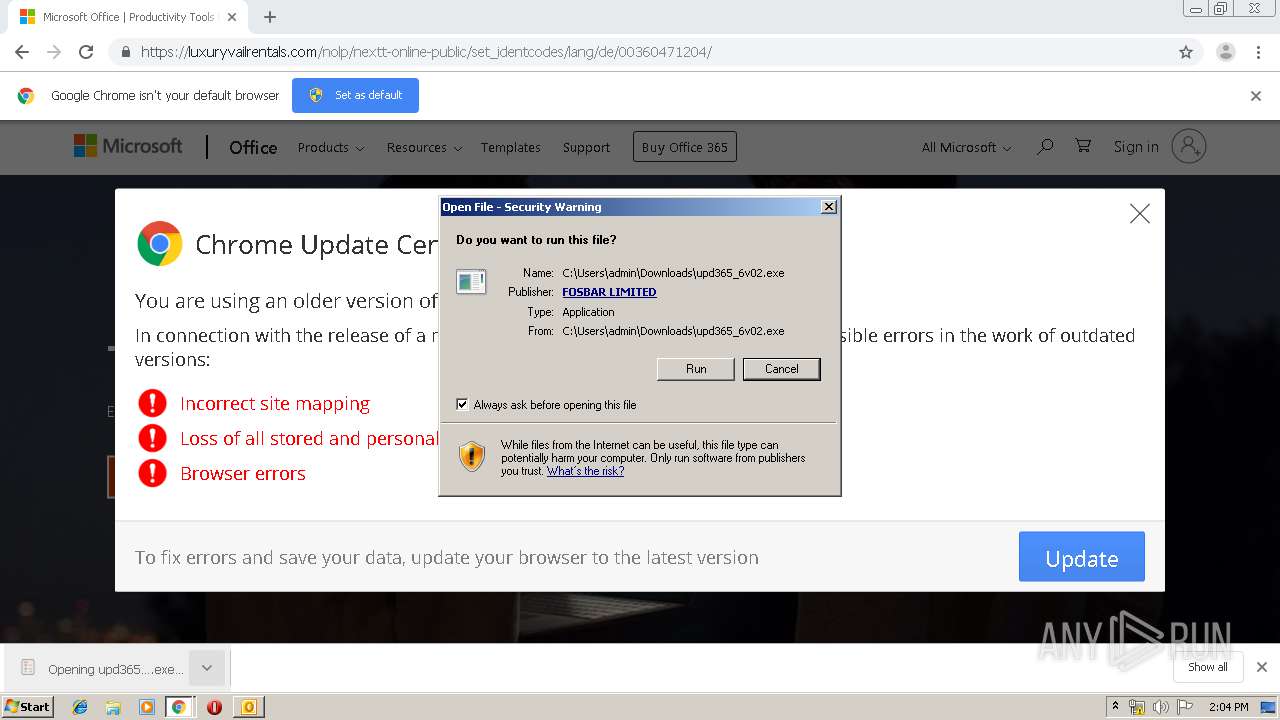
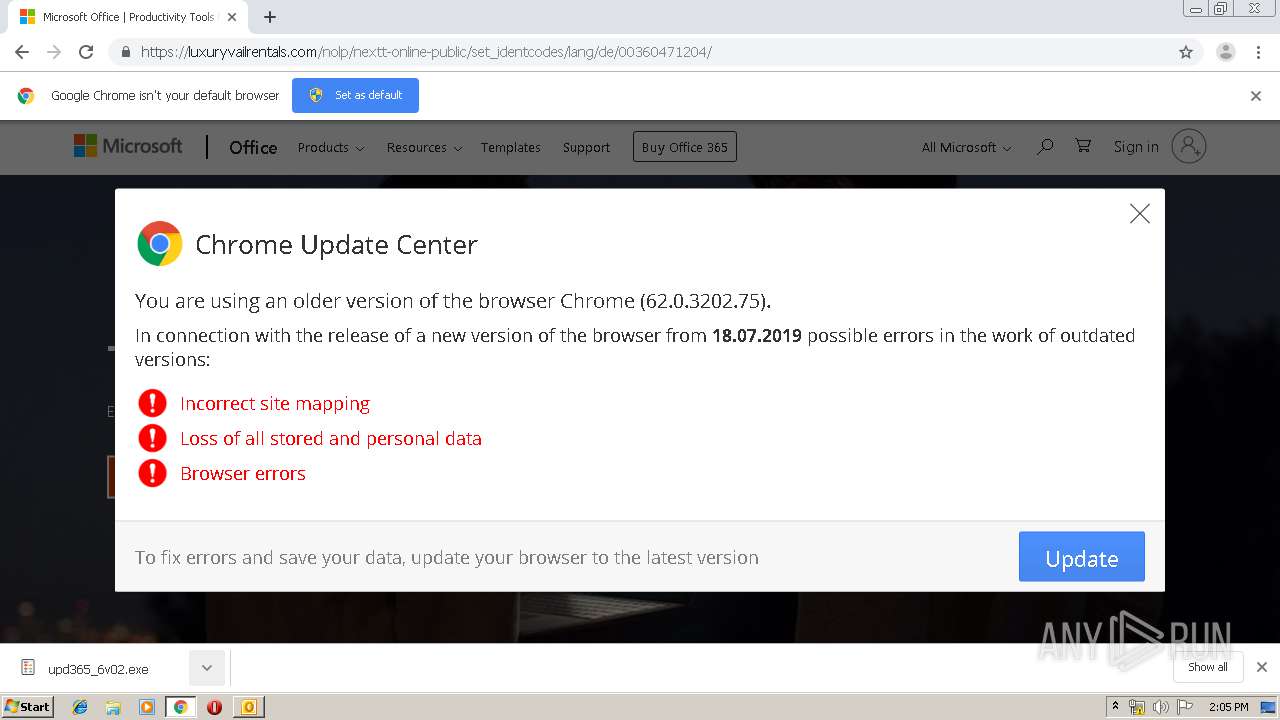
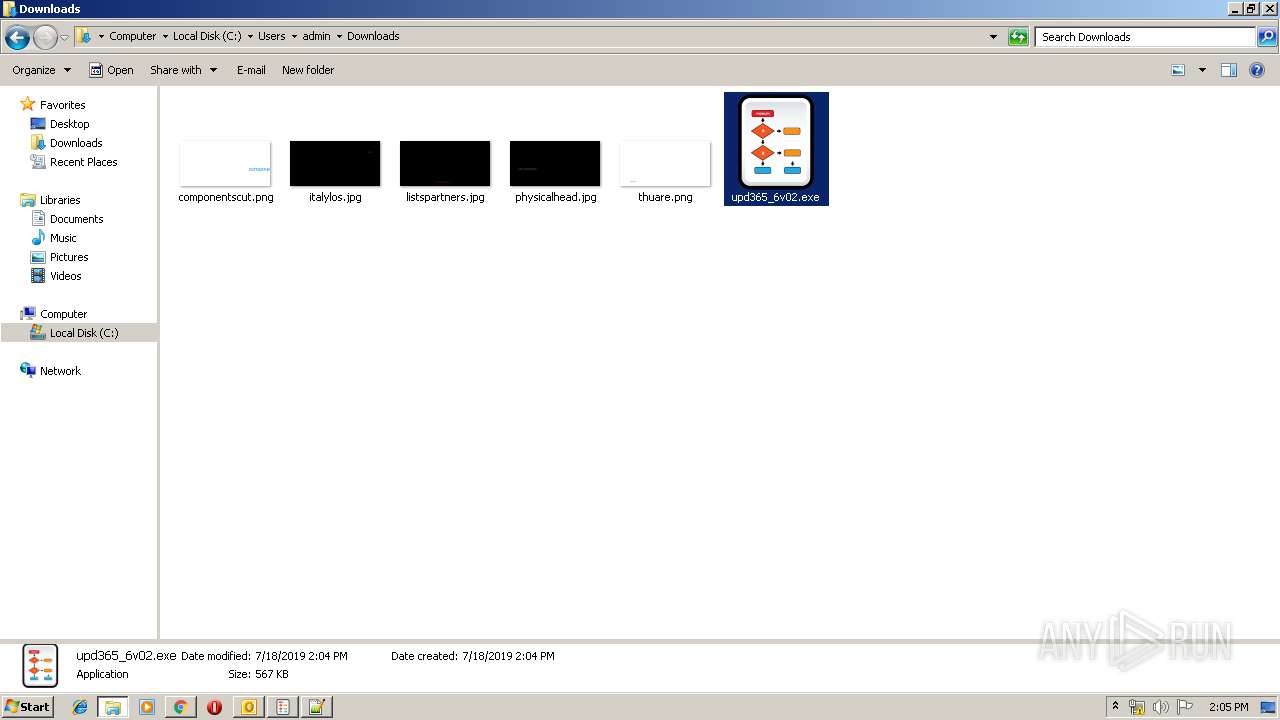
- upd365_6v02 (1).exe (PID: 3372)
- upd365_6v02.exe (PID: 804)
- urd387_8v02.exe (PID: 1376)
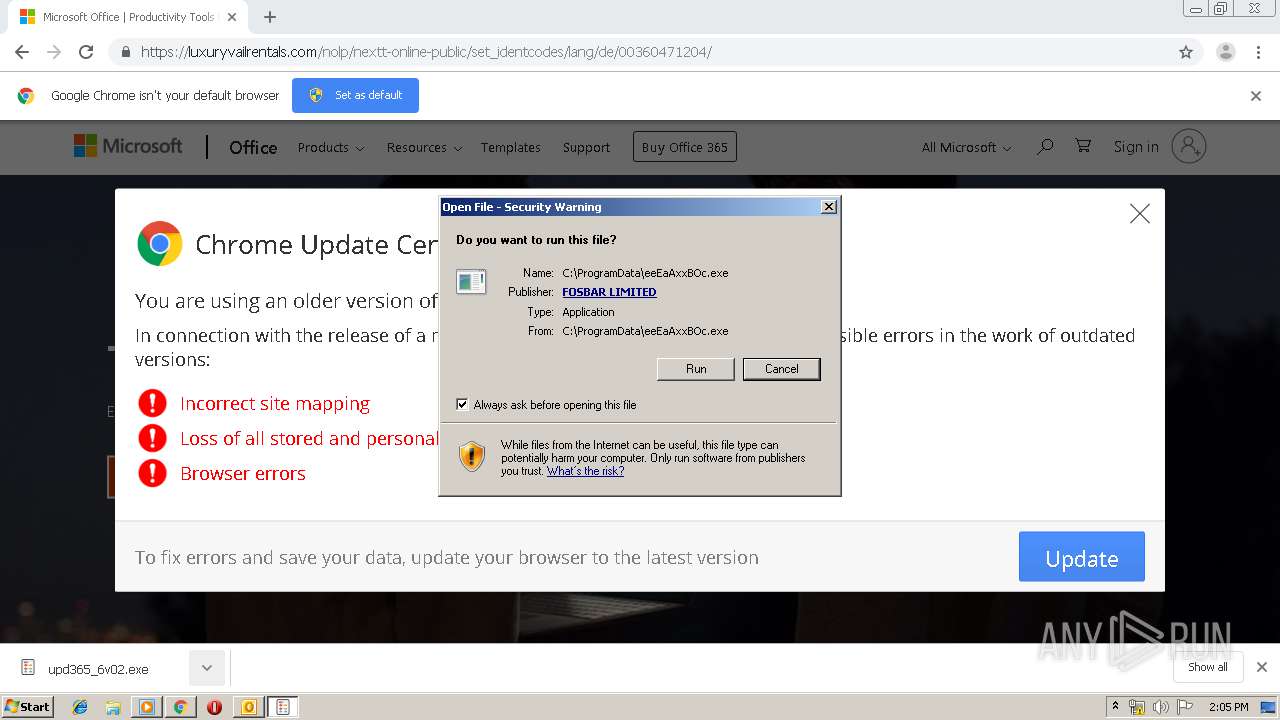
- ееЕаАххВОс.exe (PID: 880)
- upd365_6v02 (1).exe (PID: 2396)
- explorer.exe (PID: 3220)
- upd365_6v02.exe (PID: 3464)
Connects to CnC server
- upd365_6v02.exe (PID: 804)
Loads the Task Scheduler COM API
- upd365_6v02.exe (PID: 804)
Known privilege escalation attack
- DllHost.exe (PID: 696)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 3444)
- cmd.exe (PID: 3332)
Disables Windows Defender
- upd365_6v02 (1).exe (PID: 2396)
Executes PowerShell scripts
- cmd.exe (PID: 2176)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 3088)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 4060)
- cmd.exe (PID: 2256)
- cmd.exe (PID: 3048)
- cmd.exe (PID: 2060)
- cmd.exe (PID: 2972)
- cmd.exe (PID: 3164)
SUSPICIOUS
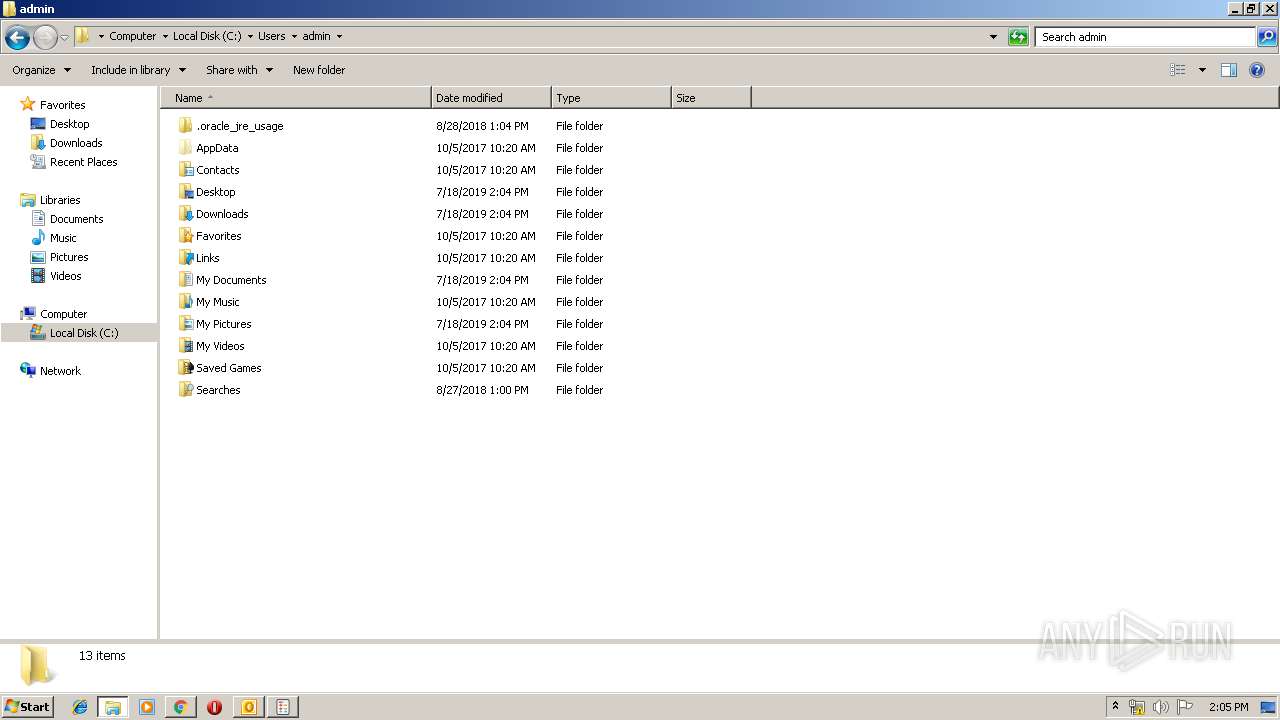
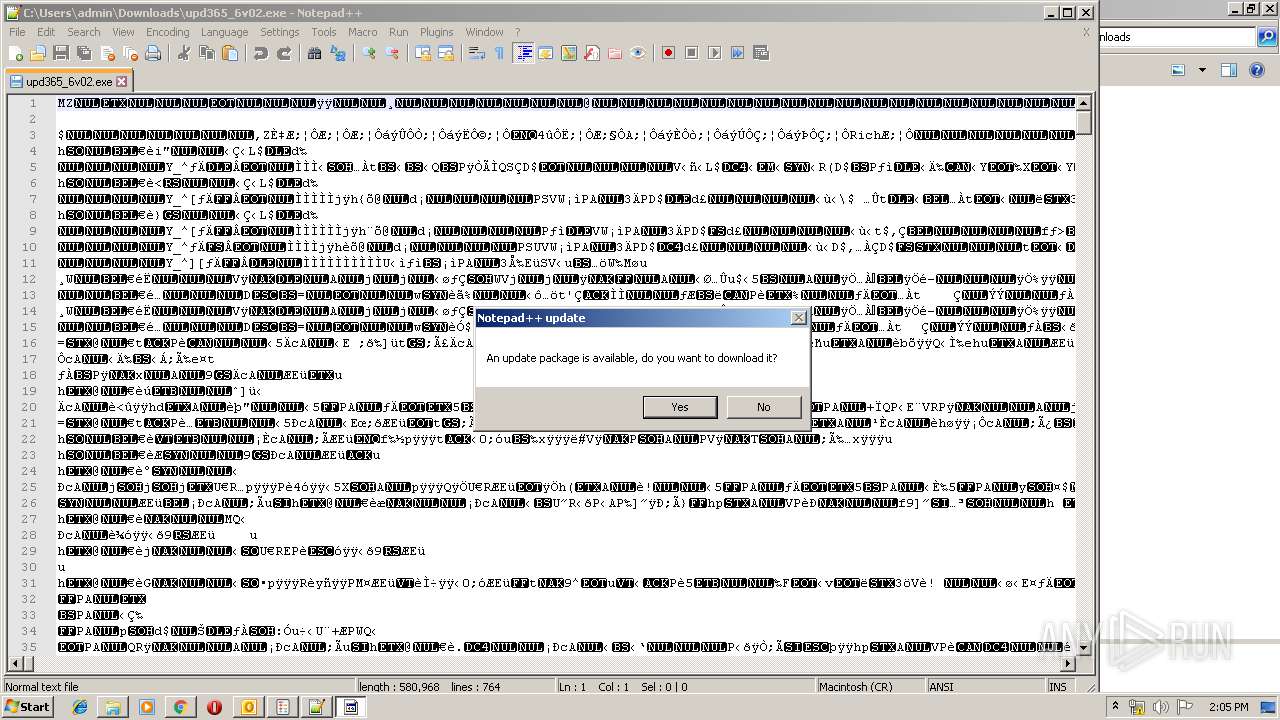
Creates files in the user directory
- OUTLOOK.EXE (PID: 3512)
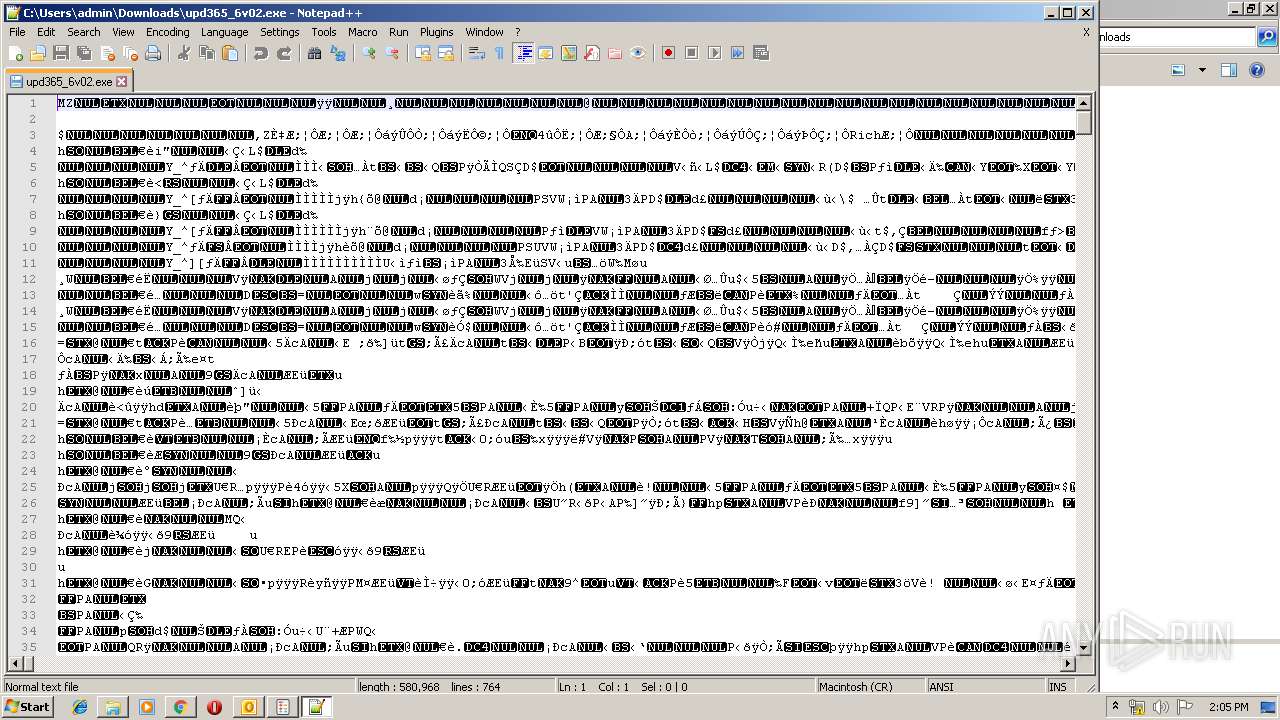
- notepad++.exe (PID: 3700)
- upd365_6v02.exe (PID: 804)
- powershell.exe (PID: 2772)
- powershell.exe (PID: 1752)
- powershell.exe (PID: 3284)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 2468)
- powershell.exe (PID: 3228)
- powershell.exe (PID: 2216)
- ееЕаАххВОс.exe (PID: 880)
- powershell.exe (PID: 1896)
- upd365_6v02 (1).exe (PID: 2396)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3512)
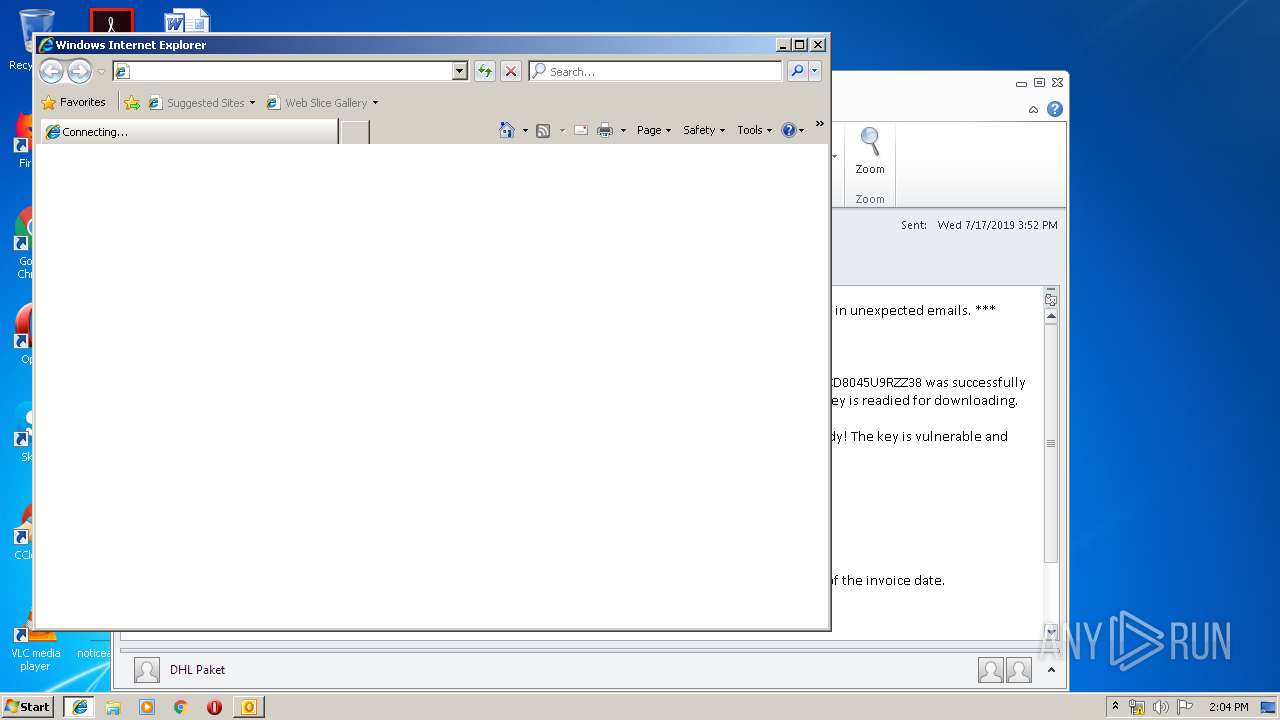
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3512)
Executable content was dropped or overwritten
- chrome.exe (PID: 2840)
- upd365_6v02.exe (PID: 804)
- upd365_6v02 (1).exe (PID: 2396)
- ееЕаАххВОс.exe (PID: 880)
- upd365_6v02.exe (PID: 3464)
Executed via COM
- DllHost.exe (PID: 696)
Executed via Task Scheduler
- urd387_8v02.exe (PID: 1376)
Starts CMD.EXE for commands execution
- upd365_6v02 (1).exe (PID: 2396)
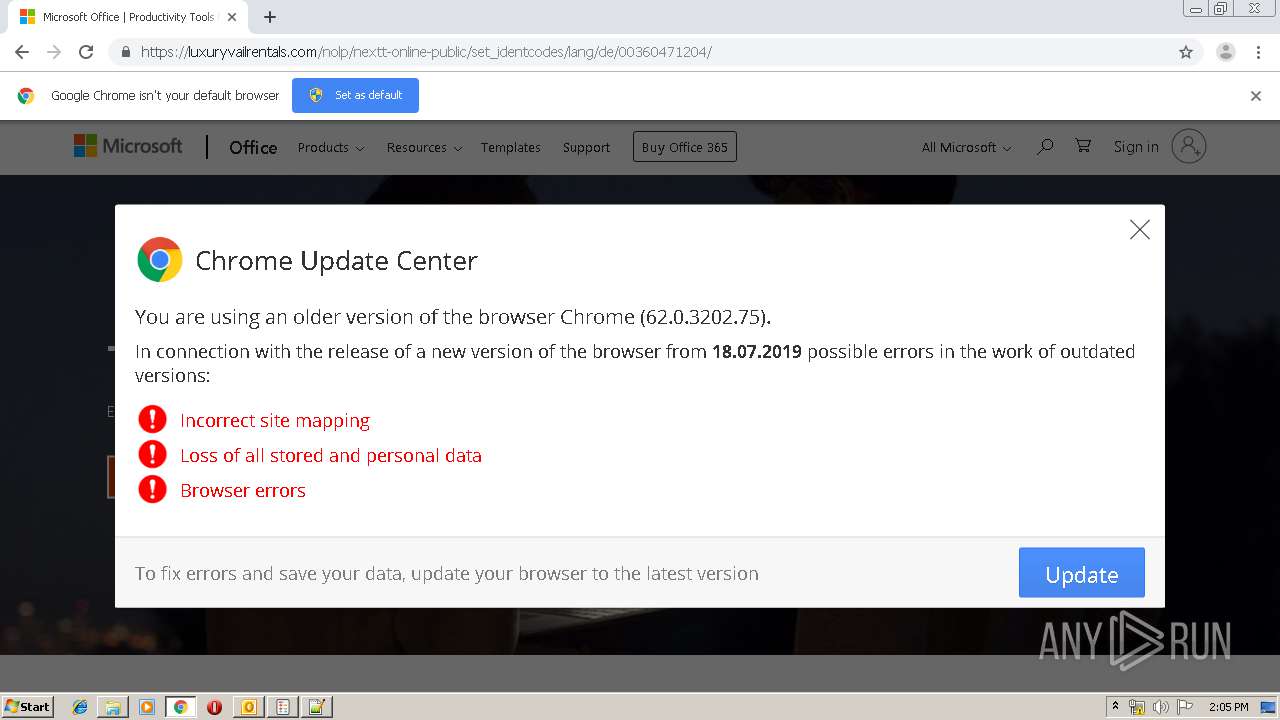
Modifies files in Chrome extension folder
- chrome.exe (PID: 2840)
Creates files in the program directory
- upd365_6v02.exe (PID: 3464)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3792)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3512)
Reads settings of System Certificates
- chrome.exe (PID: 1812)
Application launched itself
- iexplore.exe (PID: 3792)
- chrome.exe (PID: 2840)
Reads Internet Cache Settings
- iexplore.exe (PID: 616)
- chrome.exe (PID: 2840)
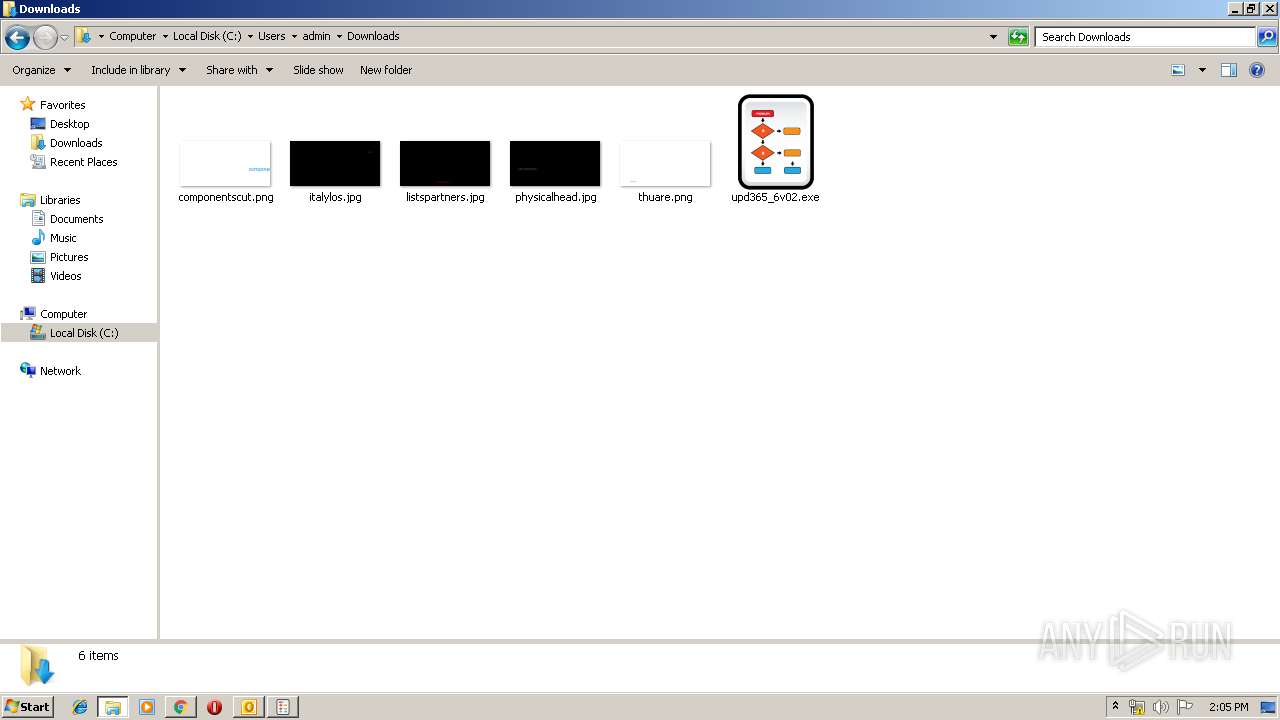
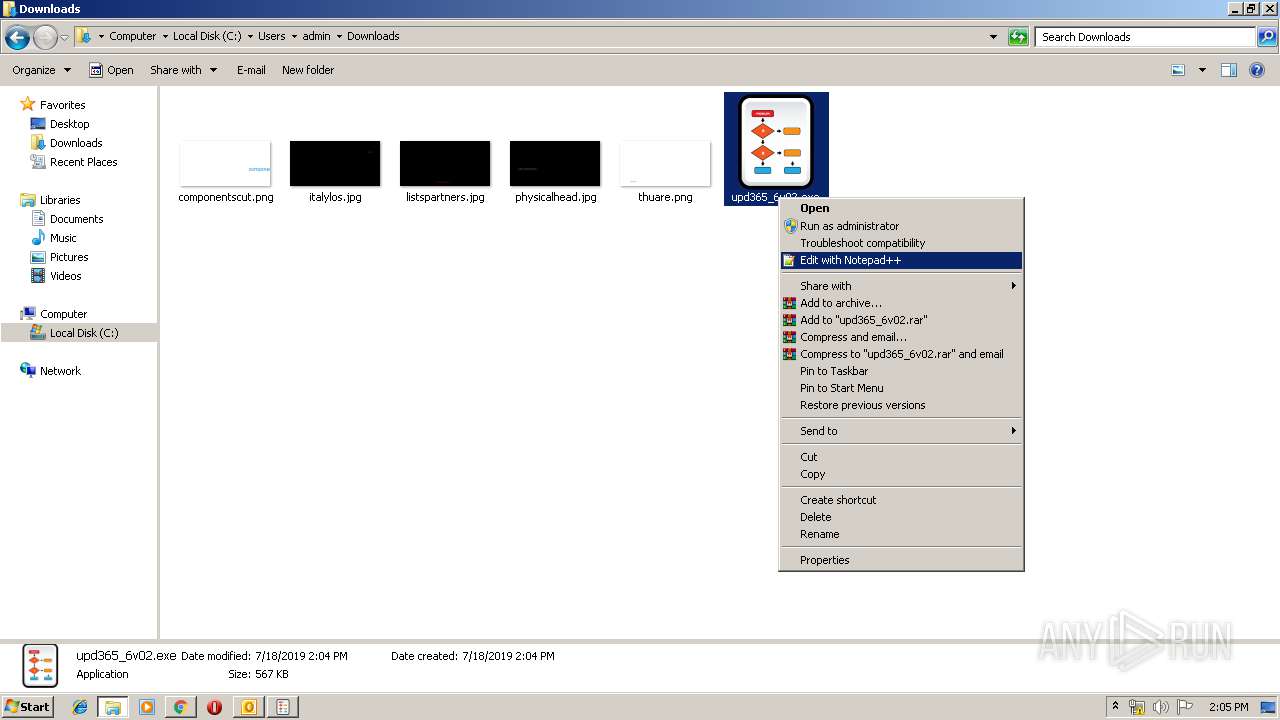
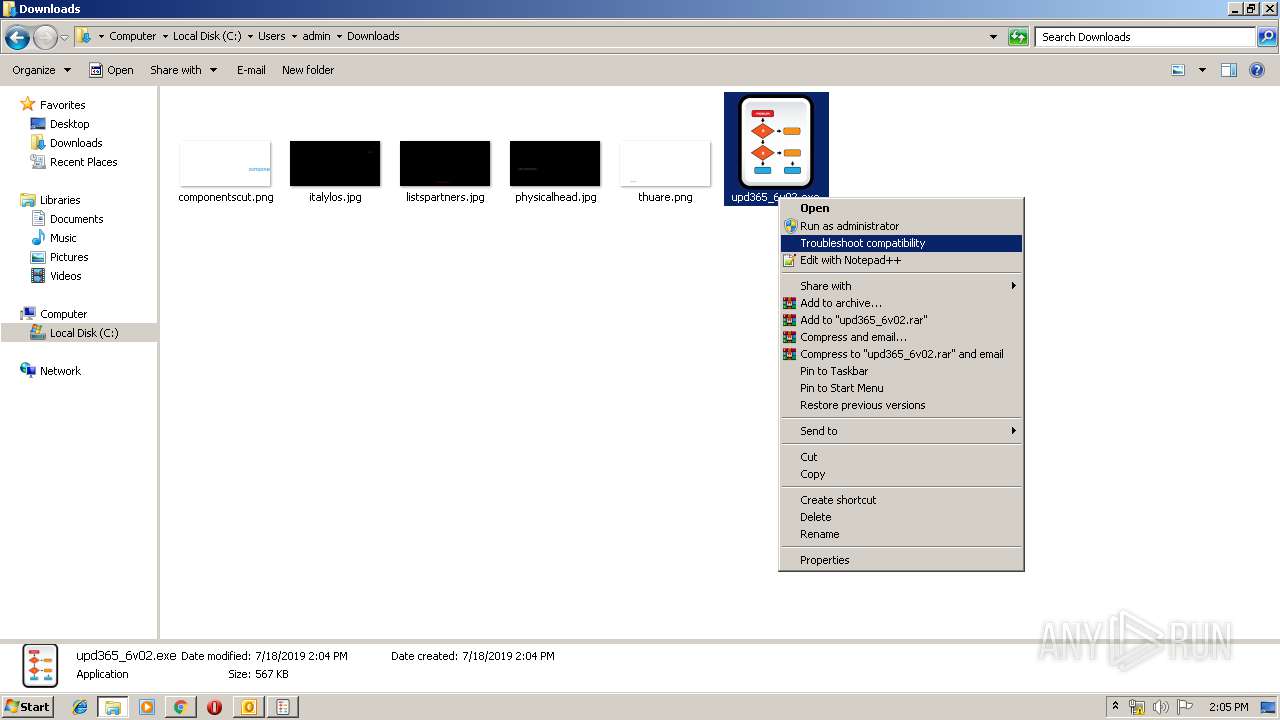
Manual execution by user
- chrome.exe (PID: 2840)
- upd365_6v02.exe (PID: 804)
- ееЕаАххВОс.exe (PID: 880)
- notepad++.exe (PID: 3700)
- explorer.exe (PID: 3220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
117
Monitored processes
62
Malicious processes
17
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,11141668318645806746,4071653740513525189,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4945412476059759320 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11141668318645806746,4071653740513525189,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=922675374387147821 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11141668318645806746,4071653740513525189,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=39413959884010295 --mojo-platform-channel-handle=4636 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11141668318645806746,4071653740513525189,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5324087069139919742 --mojo-platform-channel-handle=3348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 616 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3792 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 696 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 804 | "C:\Users\admin\Downloads\upd365_6v02.exe" | C:\Users\admin\Downloads\upd365_6v02.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Arabic_English_101 Keyboard Layout Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
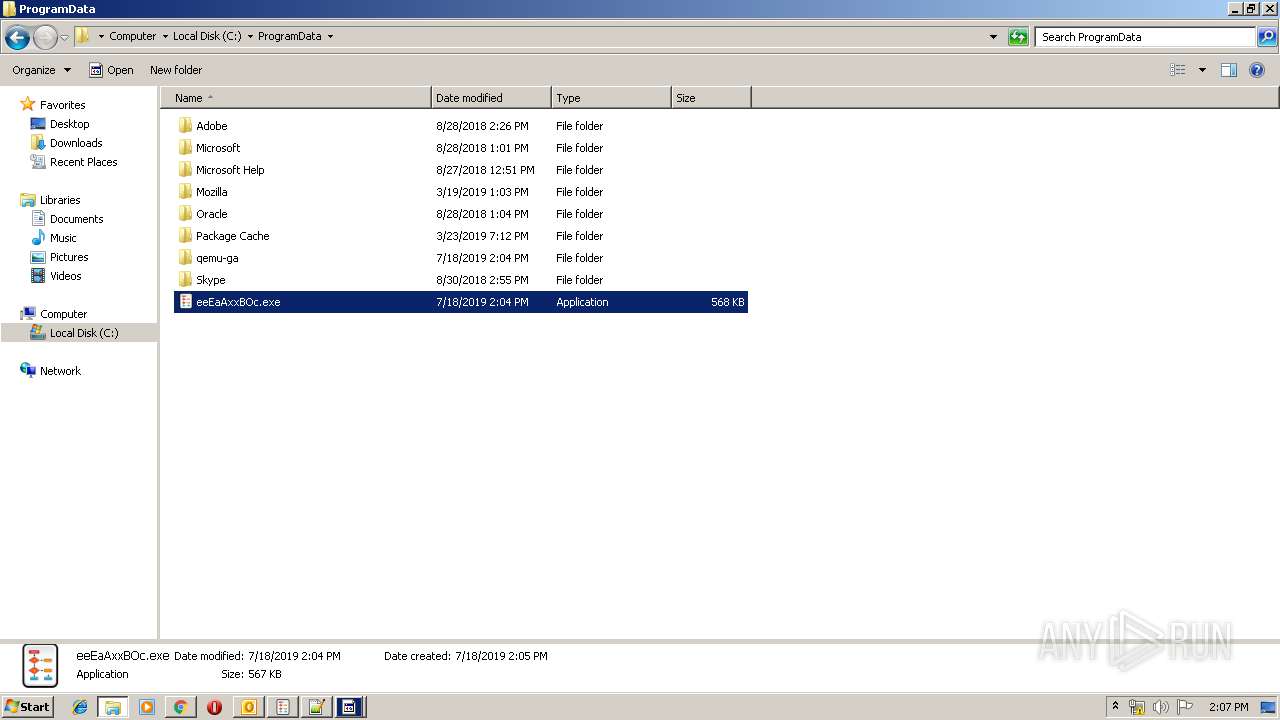
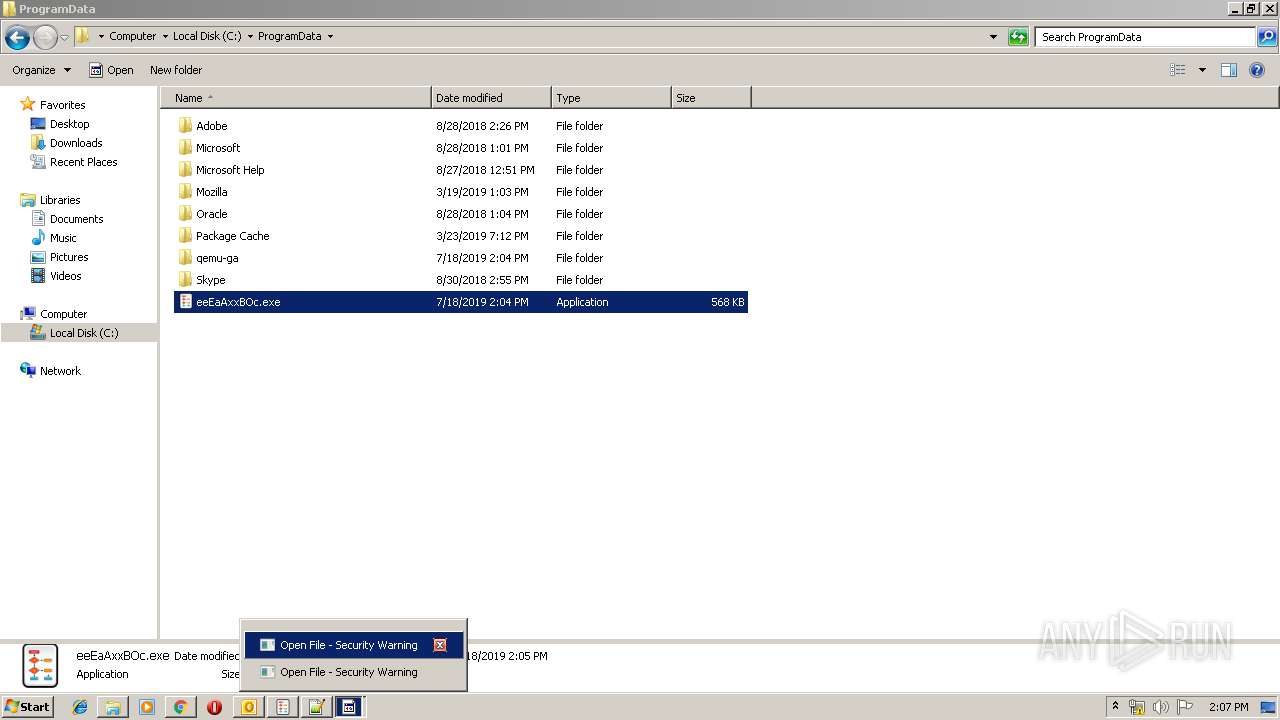
| 880 | "C:\ProgramData\ееЕаАххВОс.exe" | C:\ProgramData\ееЕаАххВОс.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Arabic_English_101 Keyboard Layout Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11141668318645806746,4071653740513525189,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=773792605559359546 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11141668318645806746,4071653740513525189,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1279624900657106897 --mojo-platform-channel-handle=3292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
5 288
Read events
4 140
Write events
1 123
Delete events
25
Modification events
| (PID) Process: | (3512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | zw: |
Value: 7A773A00B80D0000010000000000000000000000 | |||
| (PID) Process: | (3512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: B80D00002098DE4A693DD50100000000 | |||
| (PID) Process: | (3512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220131360 | |||
| (PID) Process: | (3512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3512) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1324482581 | |||
Executable files
10
Suspicious files
58
Text files
239
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3512 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVREB6A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF274B3F98D1C9B162.TMP | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9C3606FD9EAB47A5.TMP | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8074C398DC1C40B5.TMP | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{8DE3A9CA-A95C-11E9-95C0-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFBFF962AA3281D59A.TMP | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{8DE3A9C9-A95C-11E9-95C0-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3512 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
46
DNS requests
32
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3512 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
— | — | GET | 200 | 72.247.178.16:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.36 Kb | whitelisted |
1812 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
1812 | chrome.exe | GET | 200 | 173.194.187.41:80 | http://r4---sn-4g5e6nsd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.119.34&mm=28&mn=sn-4g5e6nsd&ms=nvh&mt=1563455008&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3512 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
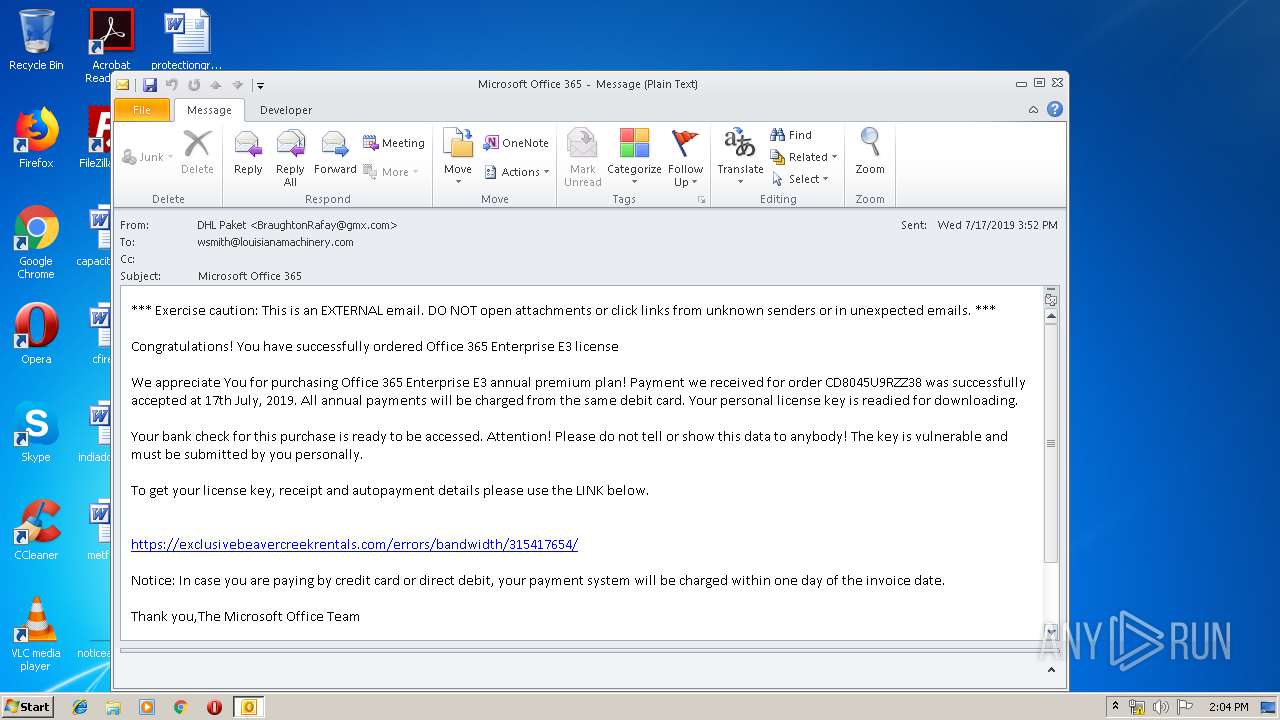
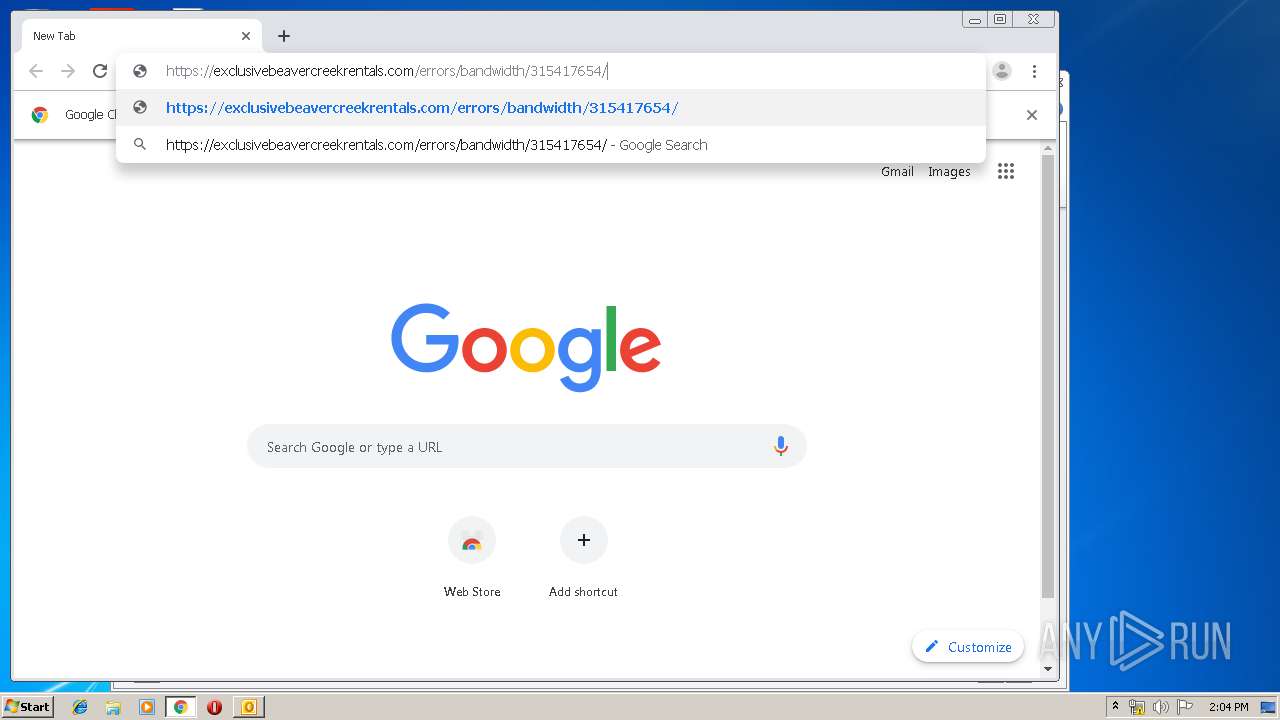
616 | iexplore.exe | 134.209.156.190:443 | exclusivebeavercreekrentals.com | — | US | unknown |
3792 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1812 | chrome.exe | 172.217.18.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1812 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1812 | chrome.exe | 134.209.156.190:443 | exclusivebeavercreekrentals.com | — | US | unknown |
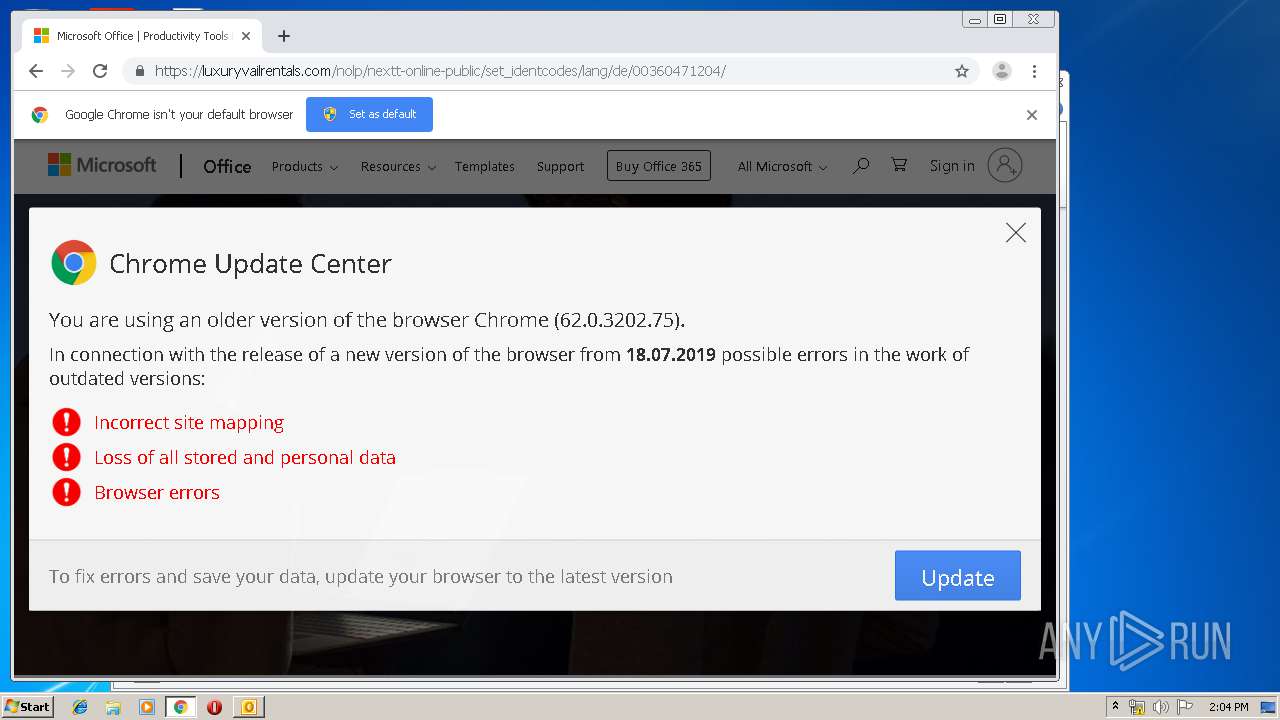
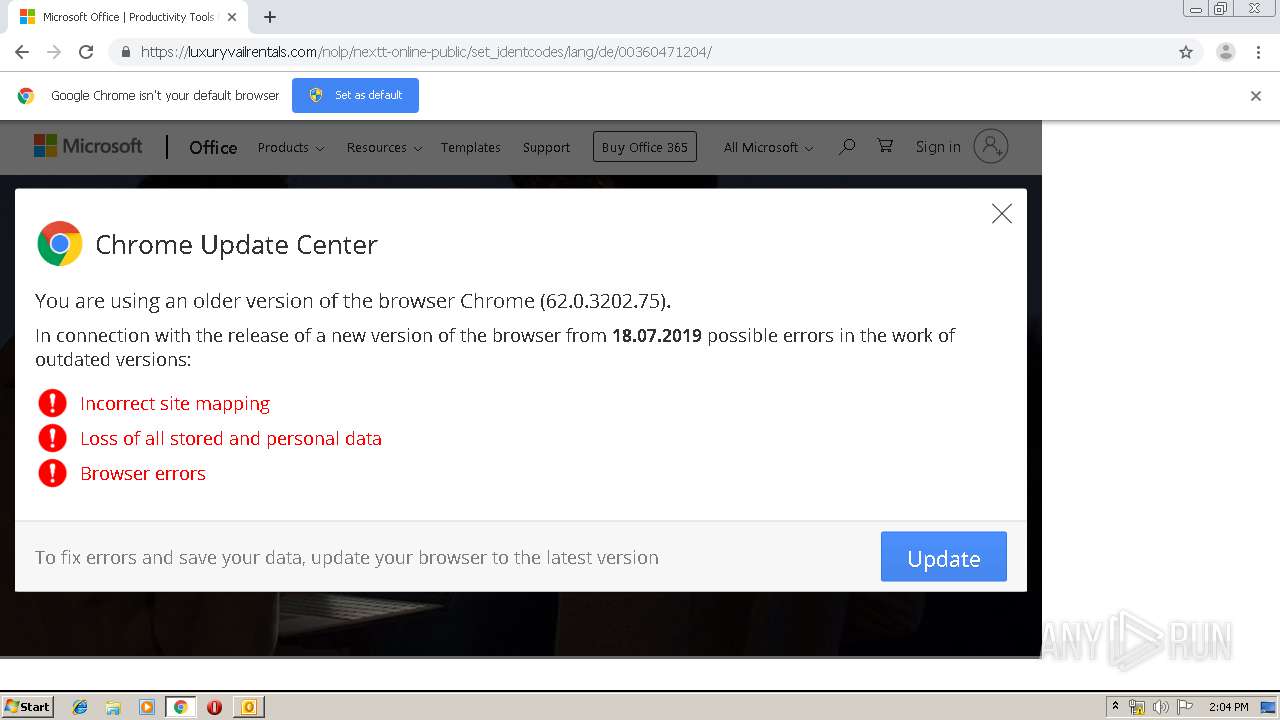
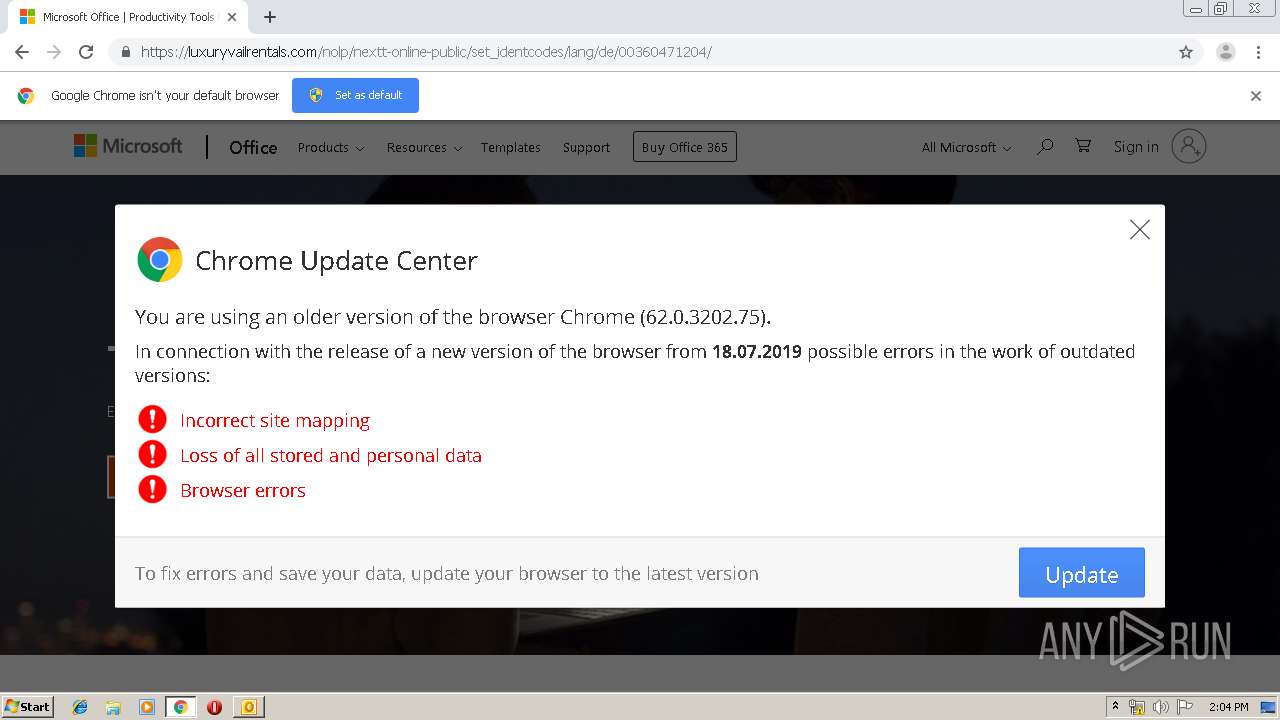
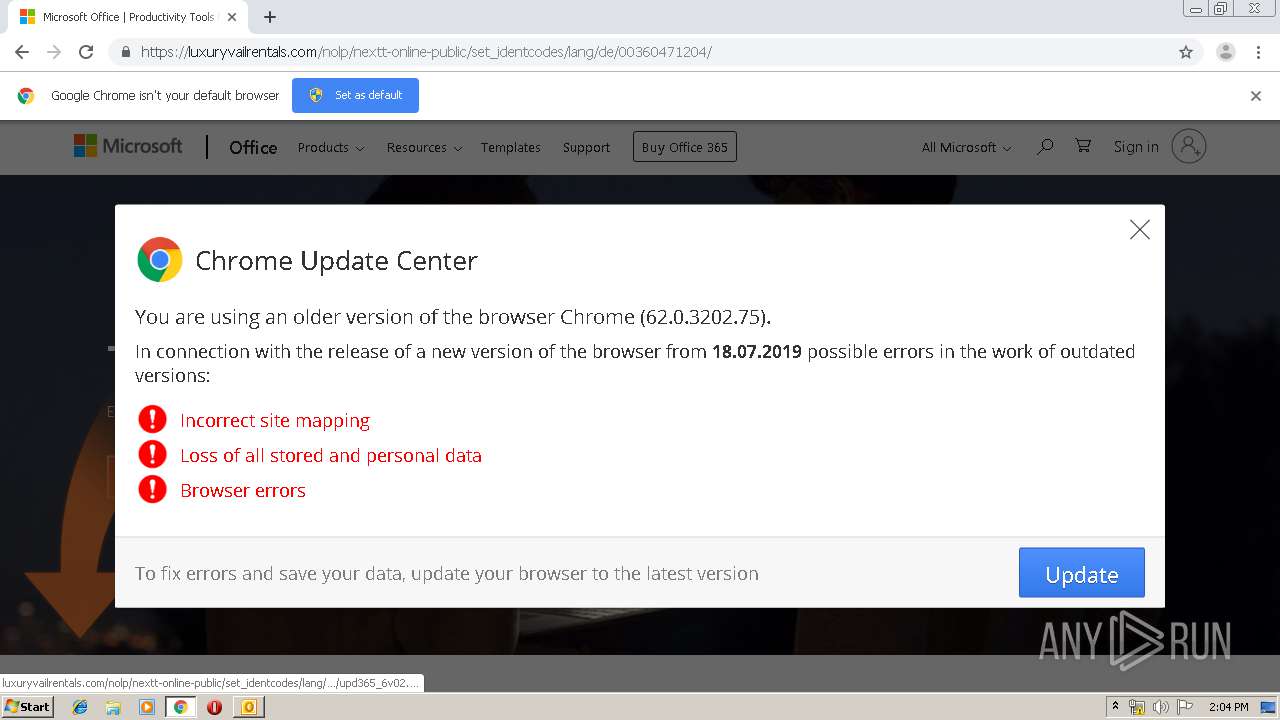
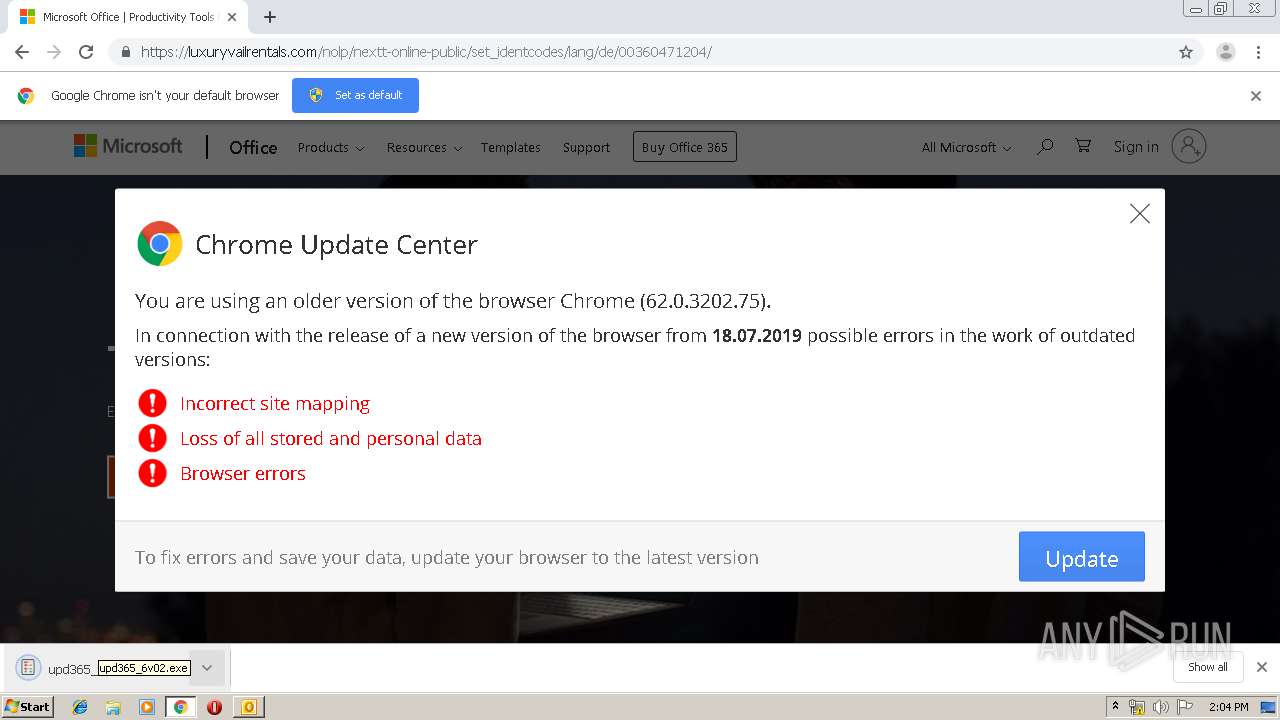
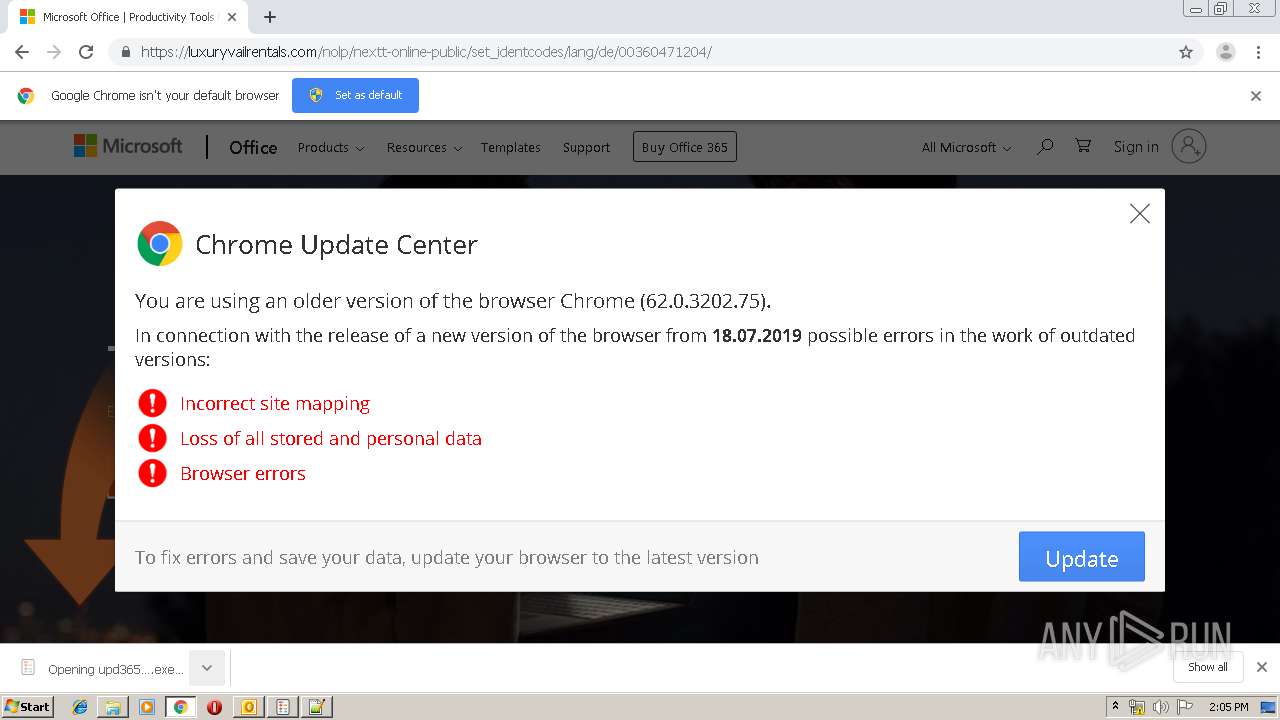
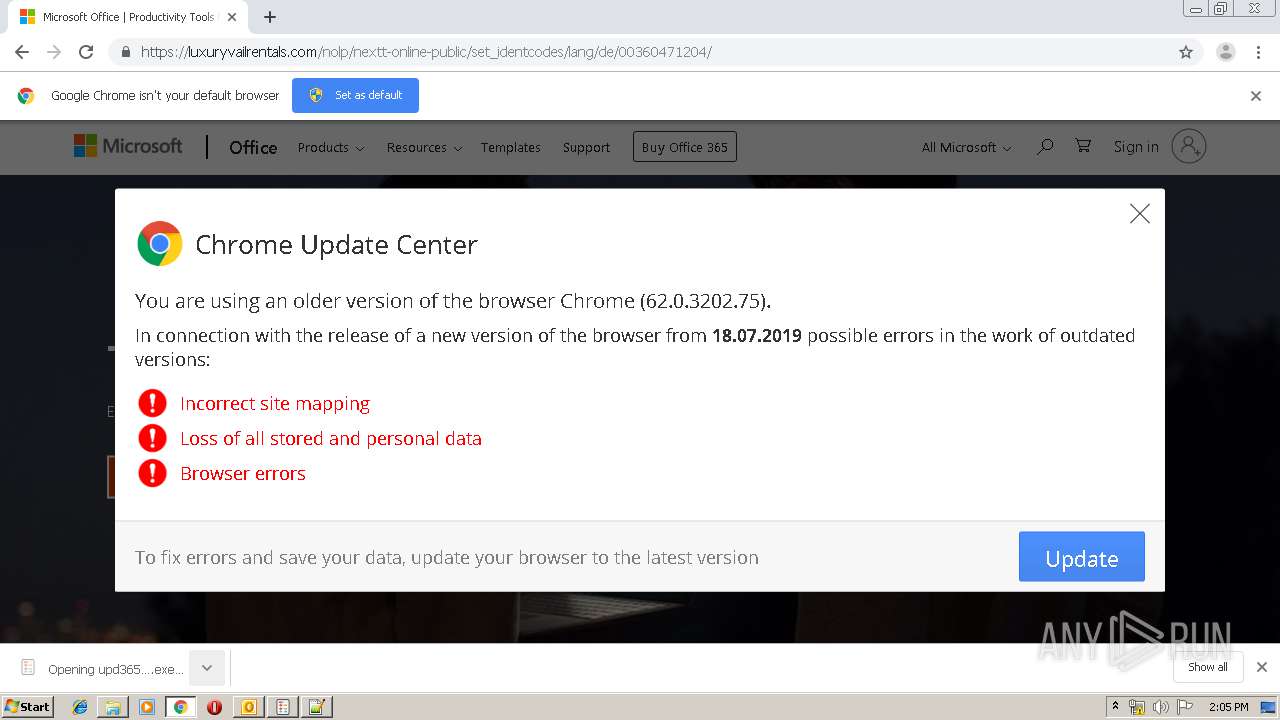
1812 | chrome.exe | 212.42.121.51:443 | luxuryvailrentals.com | ElCat Ltd. | KG | suspicious |
1812 | chrome.exe | 95.100.39.58:443 | img-prod-cms-rt-microsoft-com.akamaized.net | Akamai International B.V. | DE | whitelisted |
1812 | chrome.exe | 104.99.234.13:443 | www.microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
exclusivebeavercreekrentals.com |
| unknown |
www.bing.com |
| whitelisted |
luxuryvailrentals.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
804 | upd365_6v02.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 12 |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|