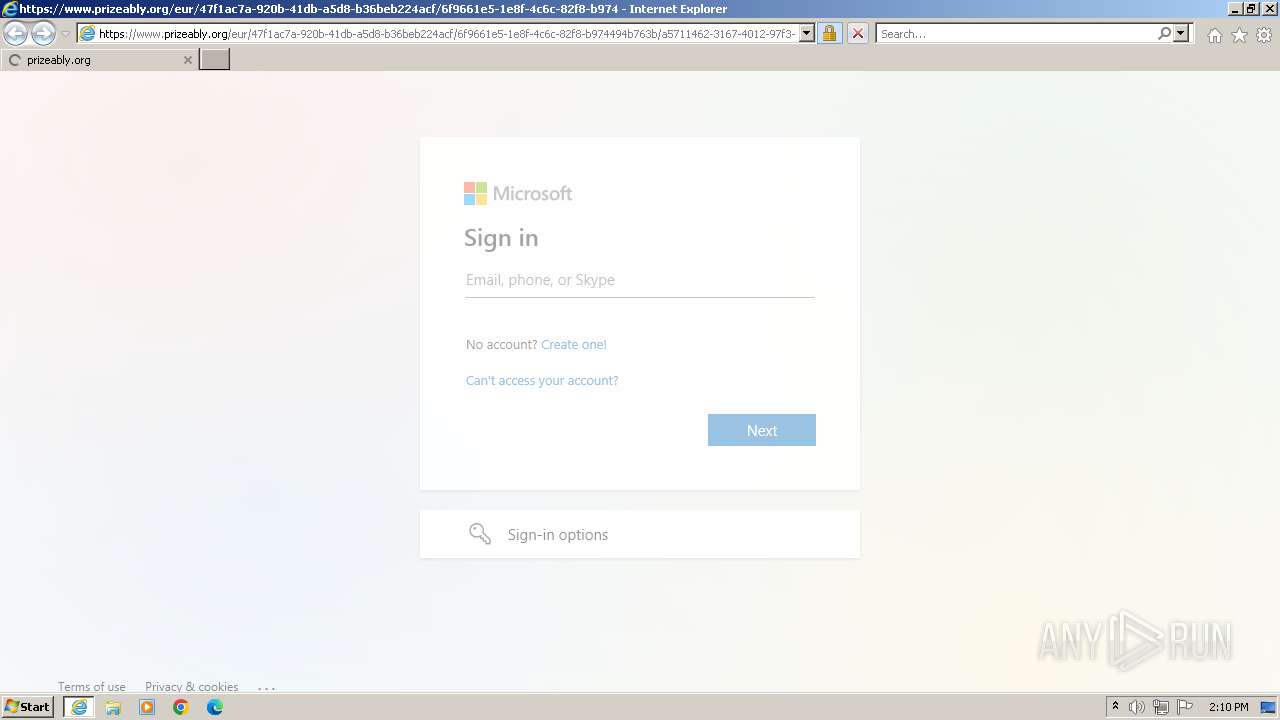
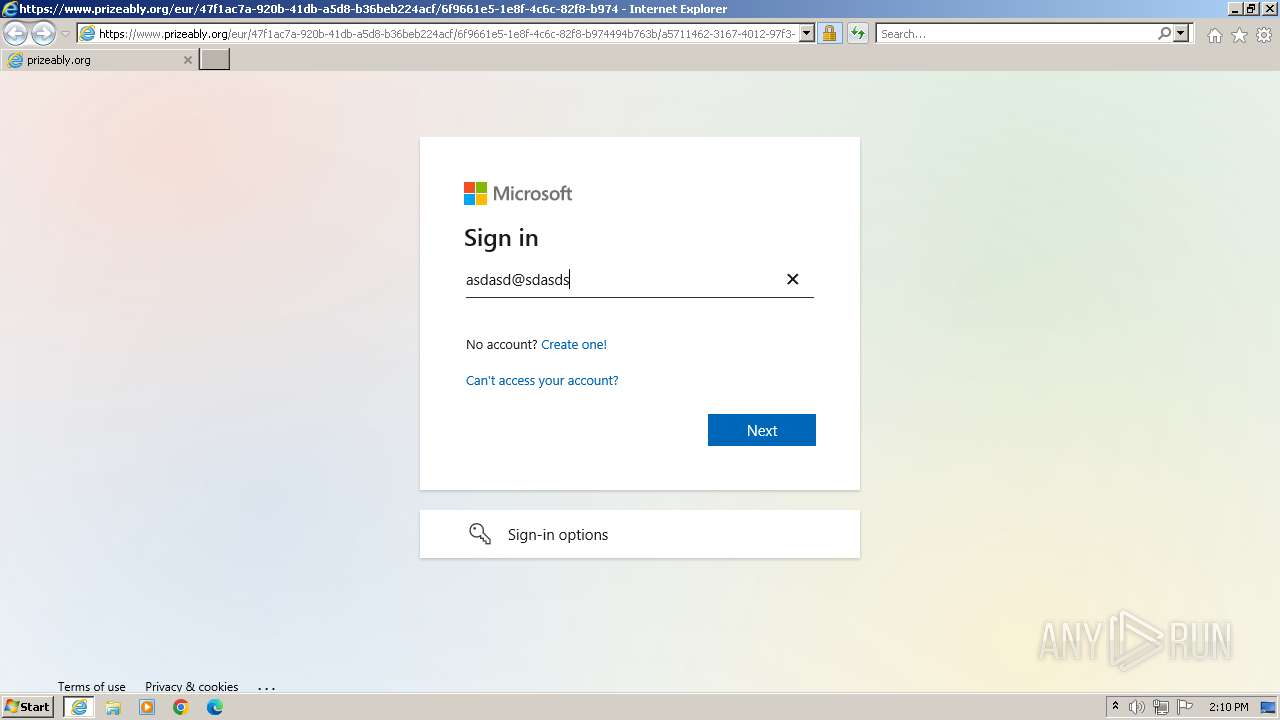
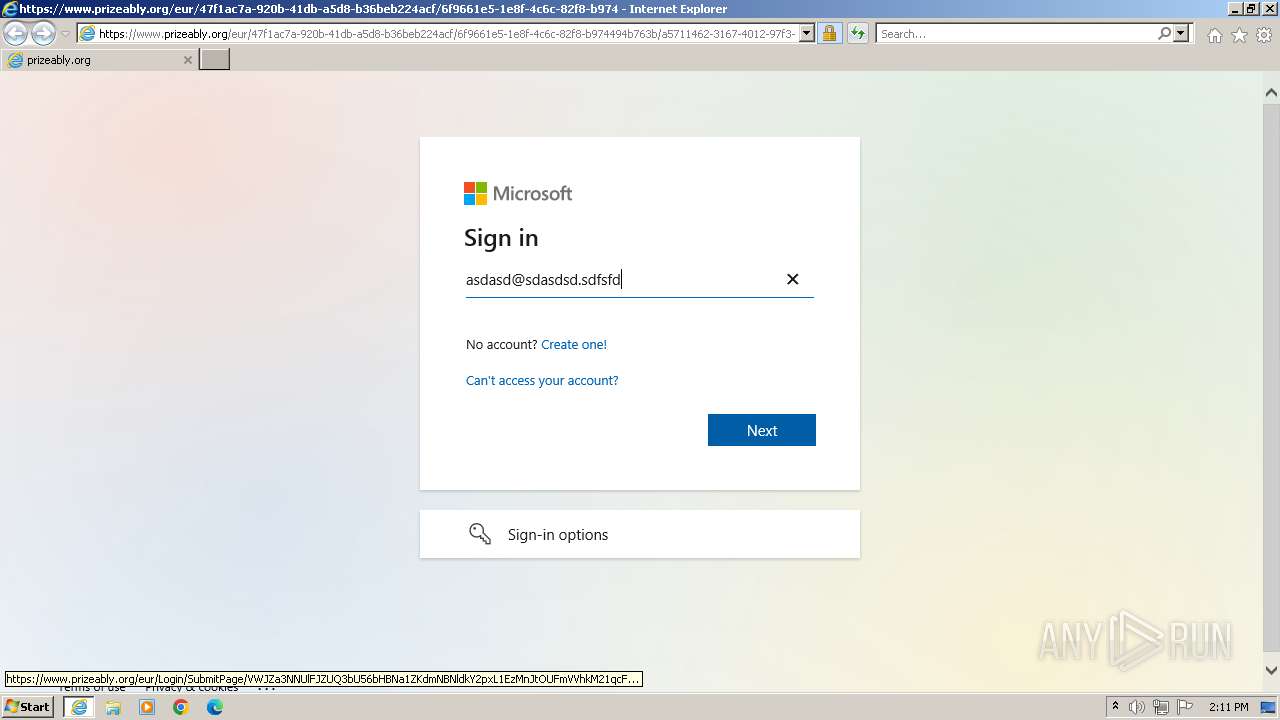
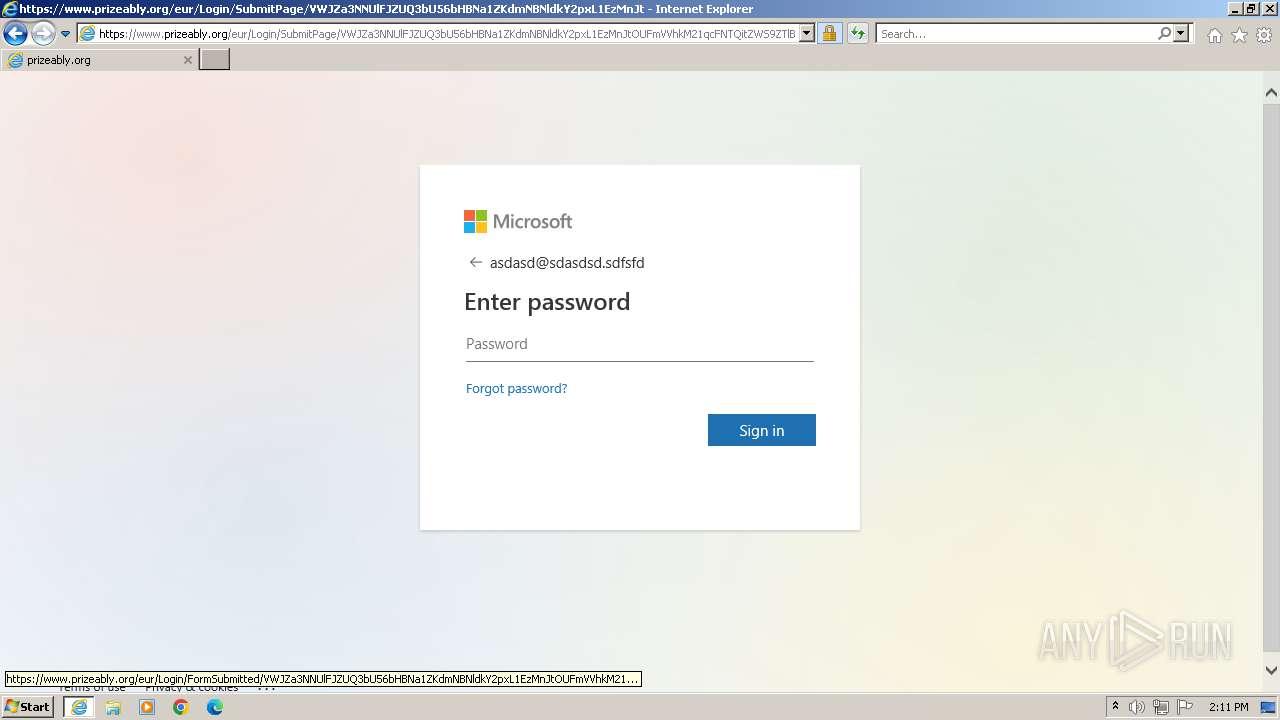
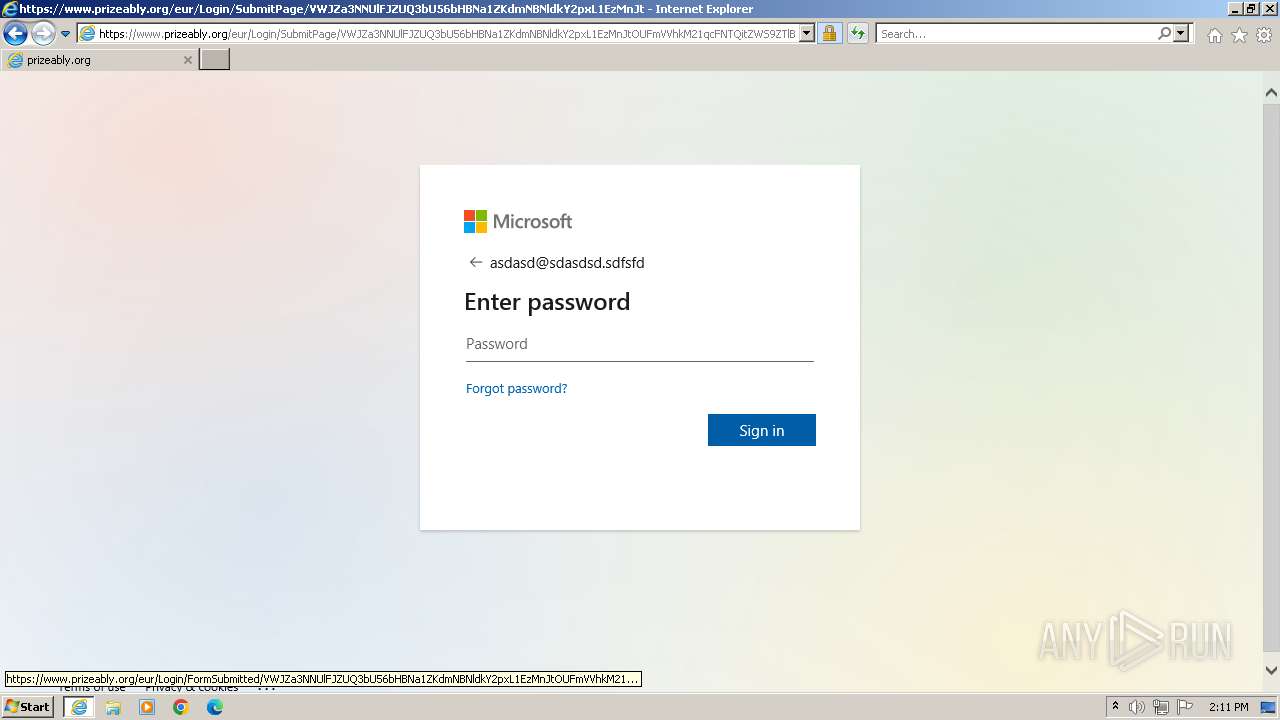
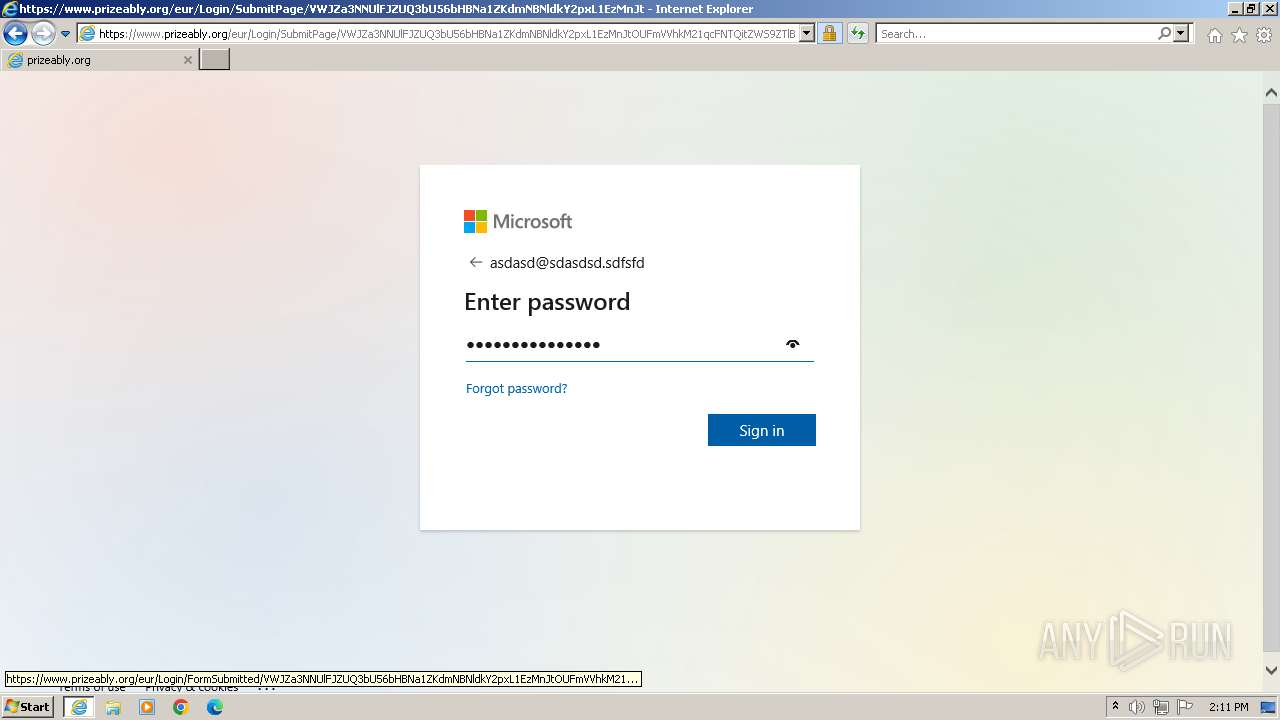
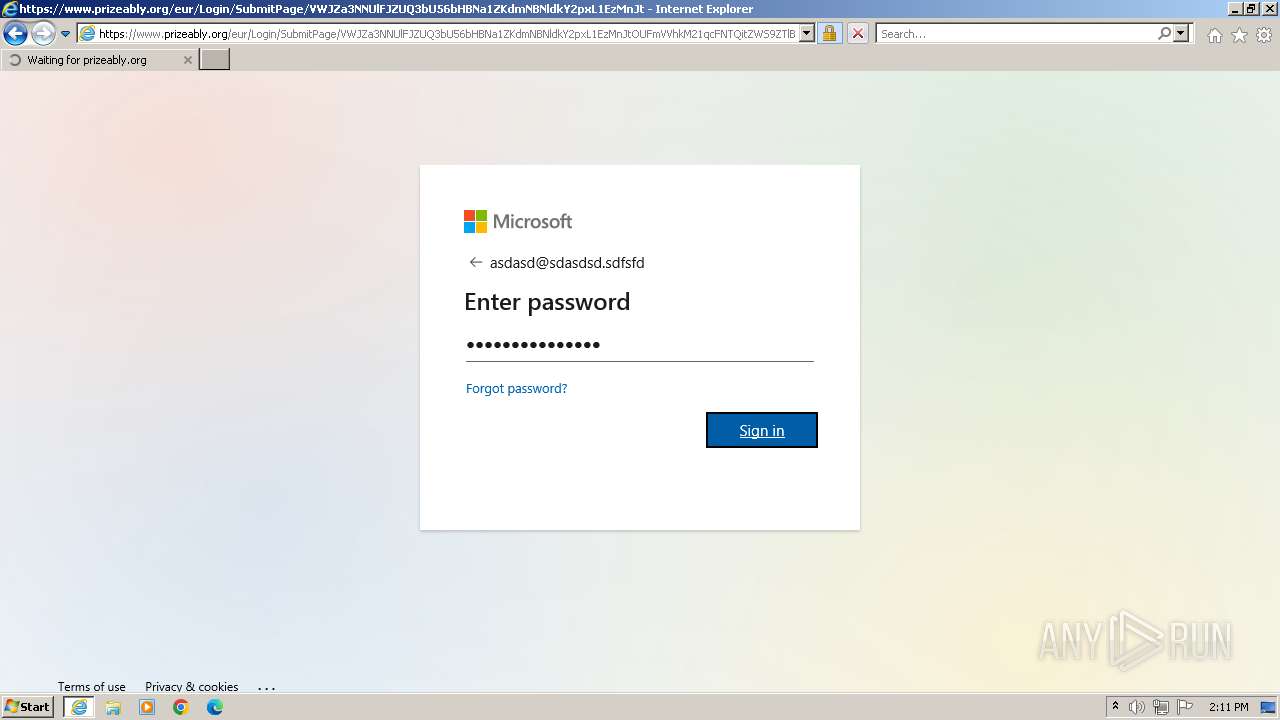
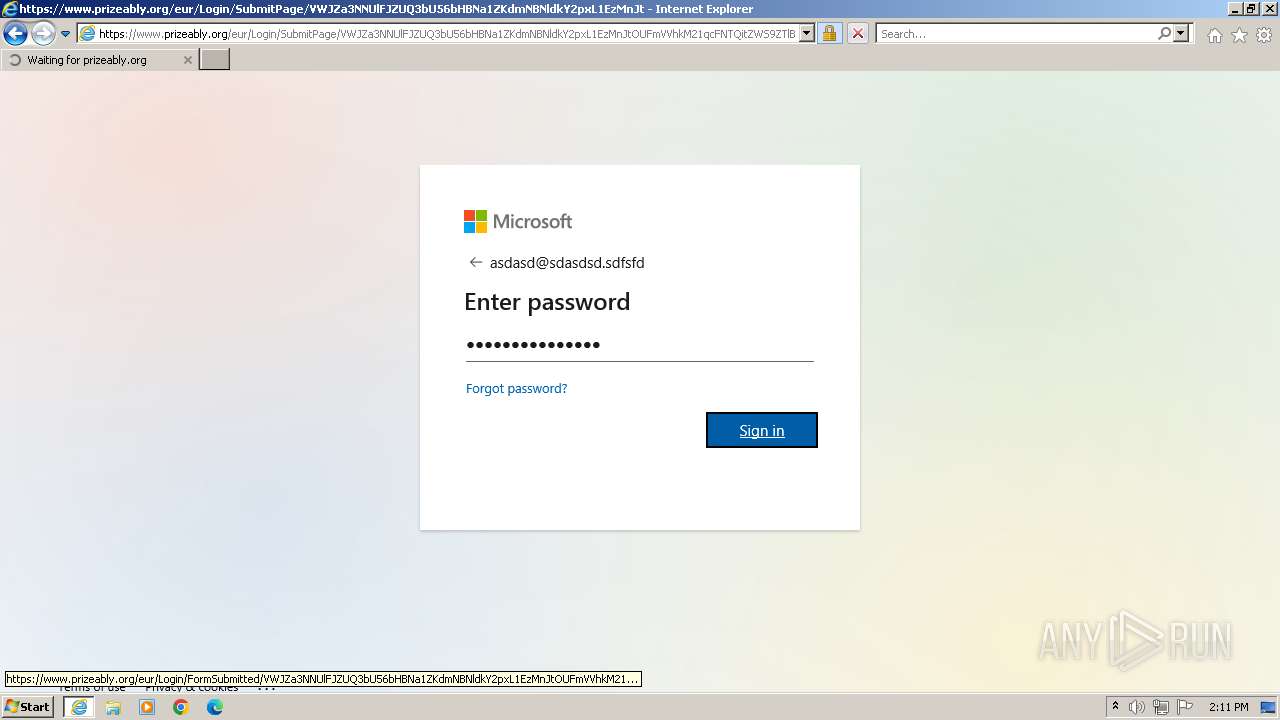
| URL: | https://www.prizeably.org/eur/47f1ac7a-920b-41db-a5d8-b36beb224acf/6f9661e5-1e8f-4c6c-82f8-b974494b763b/a5711462-3167-4012-97f3-0dfb6b80c9cb/login?id=VWJZa3NNUlFJZUQ3bU56bHBNa1ZKdmNBNldkY2pxL1EzMnJtOUFmVVhkM21qcFNTQitZWS9ZTlBTY2k4TjdodUl3Y3JQa0x5R0hjQ2hIQ09Bd3gzM0gxYkFZMGxja1NDTjUwd3JWQnBQdWxsV1RUTC94KysvVEEzZjJ4NXlCQ0s1K011SzJybm9Cd3N2bFBIL3pNZjVMVHVUajhPdUR2eGNXMjhFT1hMUVFUT3M0UksyVTdIMS93YTE4N2luRkZKMlg5RHNxUEdsVjJDT2ZJSmFnTzBGRTBoRzVTVFZaMklPWnd3d2hTd3RLT0wwMXlzQTBPTHVkdXlXQU82VjJkUDRadlZiV05qdUJ4ZW1Hdnl6VDFxNWd0RWk0RDZGR3ZVemhuaklkbVV1N0FqR0dNdHg3K3BRZis1T3QyRTVINldBaDhHVDJBTEhTd2IyRWRuNVQwUEJlT0hEUmlSWkM1Ky83a3BRQ1pPQ2NFVjdMdVFBTjJDblVQWGk0TGQzUnU1ck1TL1JIckMzTldTVDgwWWc1OGxoZz09 |
| Full analysis: | https://app.any.run/tasks/881ebcb6-e10a-44a5-b8a5-ae327c8327f0 |
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2023, 13:10:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 95E499FD02C4ED845205D1E25AE25D84 |
| SHA1: | 91EF3C8FB410E1414B5ED51C7F5BF7A6DD007ADF |
| SHA256: | 9E3DBD2612D91DF60A62C305763409EB5002752F51613462476D42AB2BEAEE58 |
| SSDEEP: | 12:2YGW5visGiXkMkjr/0us/rljIiYDLVSzyRUV5pMHI/uF50qsFm:2iSiyMlzl8iY/ZeVHrg50Bm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- msdt.exe (PID: 3548)
Reads settings of System Certificates
- msdt.exe (PID: 3548)
Reads the Internet Settings
- sdiagnhost.exe (PID: 2440)
Process uses IPCONFIG to discover network configuration
- sdiagnhost.exe (PID: 2440)
Uses ROUTE.EXE to obtain the routing table information
- sdiagnhost.exe (PID: 2440)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 2312)
Reads the computer name
- wmpnscfg.exe (PID: 2312)
Manual execution by a user
- wmpnscfg.exe (PID: 2312)
Create files in a temporary directory
- msdt.exe (PID: 3548)
- sdiagnhost.exe (PID: 2440)
- makecab.exe (PID: 2600)
Application launched itself
- iexplore.exe (PID: 2472)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 2312)
Reads security settings of Internet Explorer
- msdt.exe (PID: 3548)
- sdiagnhost.exe (PID: 2440)
Drops the executable file immediately after the start
- msdt.exe (PID: 3548)
Creates files or folders in the user directory
- msdt.exe (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\System32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\System32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2440 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
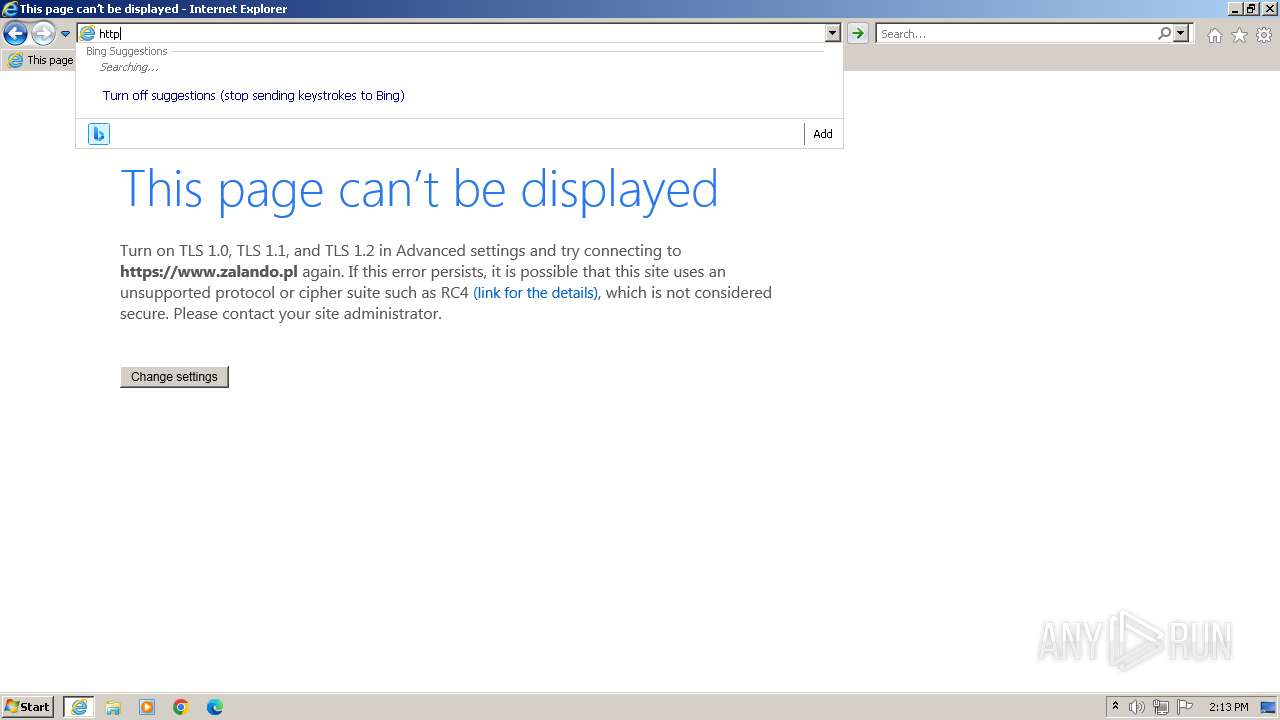
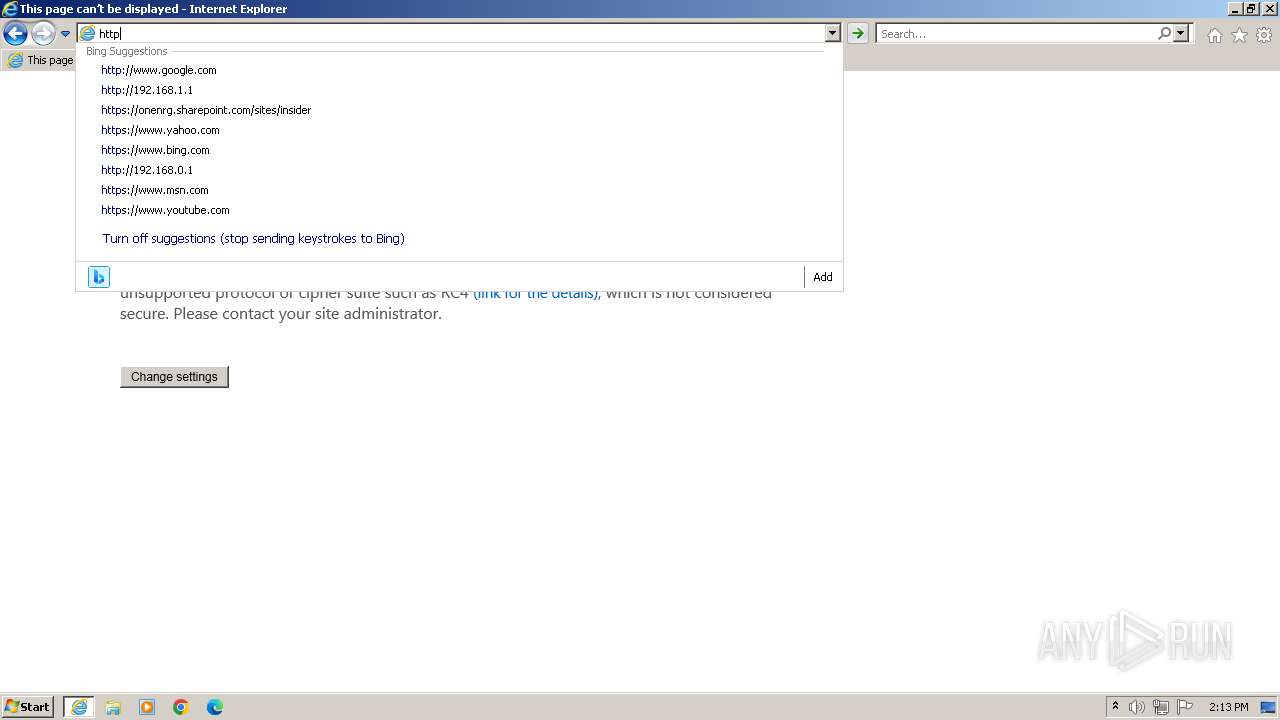
| 2472 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.prizeably.org/eur/47f1ac7a-920b-41db-a5d8-b36beb224acf/6f9661e5-1e8f-4c6c-82f8-b974494b763b/a5711462-3167-4012-97f3-0dfb6b80c9cb/login?id=VWJZa3NNUlFJZUQ3bU56bHBNa1ZKdmNBNldkY2pxL1EzMnJtOUFmVVhkM21qcFNTQitZWS9ZTlBTY2k4TjdodUl3Y3JQa0x5R0hjQ2hIQ09Bd3gzM0gxYkFZMGxja1NDTjUwd3JWQnBQdWxsV1RUTC94KysvVEEzZjJ4NXlCQ0s1K011SzJybm9Cd3N2bFBIL3pNZjVMVHVUajhPdUR2eGNXMjhFT1hMUVFUT3M0UksyVTdIMS93YTE4N2luRkZKMlg5RHNxUEdsVjJDT2ZJSmFnTzBGRTBoRzVTVFZaMklPWnd3d2hTd3RLT0wwMXlzQTBPTHVkdXlXQU82VjJkUDRadlZiV05qdUJ4ZW1Hdnl6VDFxNWd0RWk0RDZGR3ZVemhuaklkbVV1N0FqR0dNdHg3K3BRZis1T3QyRTVINldBaDhHVDJBTEhTd2IyRWRuNVQwUEJlT0hEUmlSWkM1Ky83a3BRQ1pPQ2NFVjdMdVFBTjJDblVQWGk0TGQzUnU1ck1TL1JIckMzTldTVDgwWWc1OGxoZz09" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2600 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\System32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | -modal 1180074 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF8B0.tmp -ep NetworkDiagnosticsWeb | C:\Windows\System32\msdt.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4068 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2472 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
20 234
Read events
20 145
Write events
86
Delete events
3
Modification events
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
59
Text files
65
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_C0427F5F77D9B3A439FC620EDAAB6177 | binary | |
MD5:492F2A57DCE58DDA9877738C64E4230F | SHA256:F2FFAF8186A895CB6B07537621D4B3E5DFC7396A4A516026D285702ABEE8485B | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:BDB61B66990D71673BDDAEE6F820A4ED | SHA256:F84CF83BD076BD2C9481C283AD87EA2F4AC2D3A25DF14D429E76EF61F1CAEE2C | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\DE0D974FB4DC3536B9035FD604565AB7_9B8158FC18CBC2124A1E631BD623205F | binary | |
MD5:9C02A4AD3DB086147813C2DCD6E09967 | SHA256:653F9430AC22653ABBF644BE7184C1EF496629CB2867EC9B6EEC9B8C41FD1C22 | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | binary | |
MD5:8DB7EF2748AA34DBAA3888D1269B70EE | SHA256:792AC18EB25E3F6E16F523D4017FE440A7399B10DCF13C3C8B26A956EF356605 | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:C2B93AC8145DA4E54217E27324A2DB63 | SHA256:80B349978AEB987E4882F331B02EA7283717F00AD342F04341EE7F6F7588795D | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\DE0D974FB4DC3536B9035FD604565AB7_9B8158FC18CBC2124A1E631BD623205F | binary | |
MD5:E6E5018F555E165687BAFBD301F40907 | SHA256:7314ABCCB78DCE2040C6D0581D457A501B1A5470038F5550A65D6C00B8CEF053 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | binary | |
MD5:B67FB3C8C3B53B826560005DC920405B | SHA256:BB6330A39055F72454427E1CEF9D4AB134AD358C3E645C4DFA73886D4032EC7C | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
52
DNS requests
34
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4068 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | unknown | binary | 471 b | unknown |
4068 | iexplore.exe | GET | 200 | 67.27.235.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?060020e49c501eb3 | unknown | compressed | 4.66 Kb | unknown |
4068 | iexplore.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRS%2FsoQjbTlq1Jokw0nyC%2FyFeJLtQQUAKuR%2FCFiJpeaqHkbYUGQYKliZ%2F0CEzMAwVKFmb8%2Fl9hOfmgAAADBUoU%3D | unknown | binary | 1.74 Kb | unknown |
4068 | iexplore.exe | GET | 200 | 67.27.235.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b40315f06fd1d4d8 | unknown | compressed | 4.66 Kb | unknown |
2472 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | der | 471 b | unknown |
4068 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
2472 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
2472 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
4068 | iexplore.exe | GET | 200 | 108.138.2.10:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
4068 | iexplore.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.51 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4068 | iexplore.exe | 13.107.246.45:443 | aadcdn.msauth.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4068 | iexplore.exe | 67.27.235.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
4068 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4068 | iexplore.exe | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2472 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2472 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2472 | iexplore.exe | 13.107.246.45:443 | aadcdn.msauth.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
aadcdn.msauth.net |
| whitelisted |
aadcdn.msftauth.net |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4068 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
4068 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
4068 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
4068 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
4068 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
4068 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
2472 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
2472 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
4068 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |