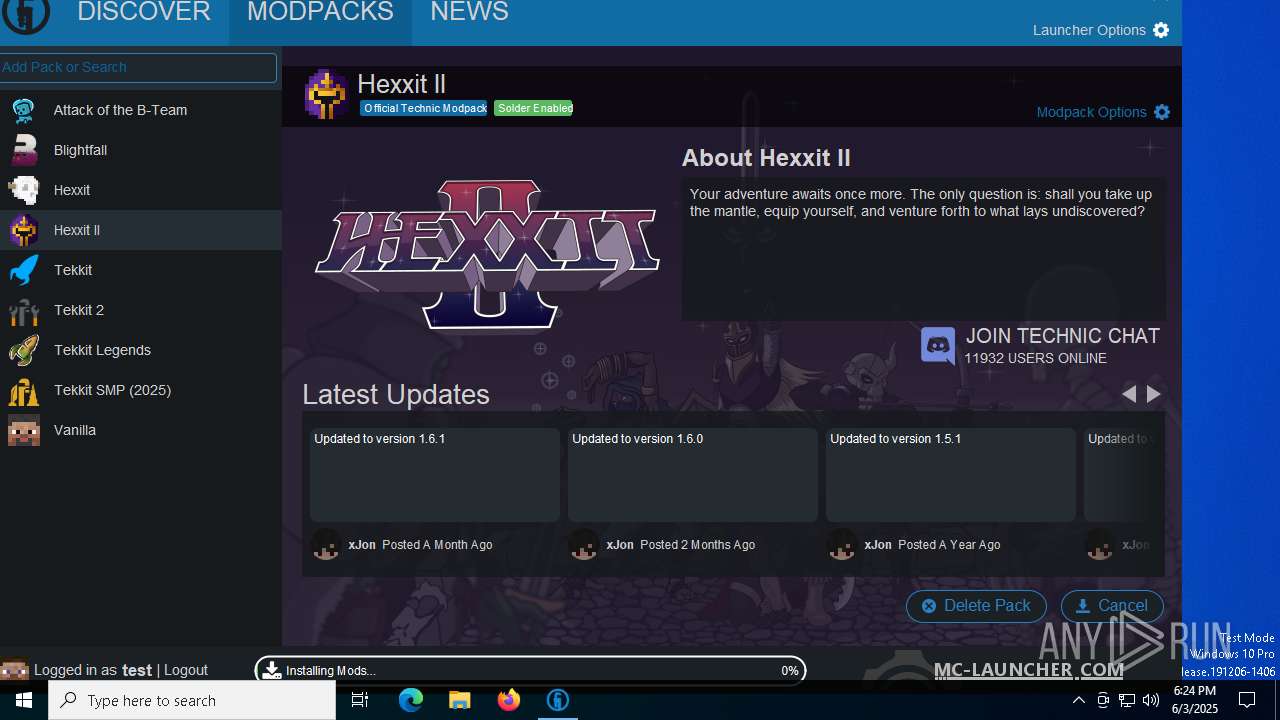
| File name: | Technic Z1.1.exe |
| Full analysis: | https://app.any.run/tasks/237d0bd1-f2d1-4f59-8fe2-49dbb3b5249d |
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2025, 18:23:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive, with extra data prepended |
| MD5: | 8814E2C11C6D0ED36430C00C0DBDBD9B |
| SHA1: | 062BD5999C0BDA1A717A65DB9C1345C401B9F238 |
| SHA256: | 9E3D23722F74AA253F651CD59C10F6DB19779DB4F5B8B6CBCEEE77F0ECCDC8E7 |
| SSDEEP: | 98304:ddIiA8SYLKmkWSQw+NOBXSGMisREThr6i4NZVvG2w2lor3H3gqUrbTZm4FOvi/xf:nYpz1JaZh |
MALICIOUS
No malicious indicators.SUSPICIOUS
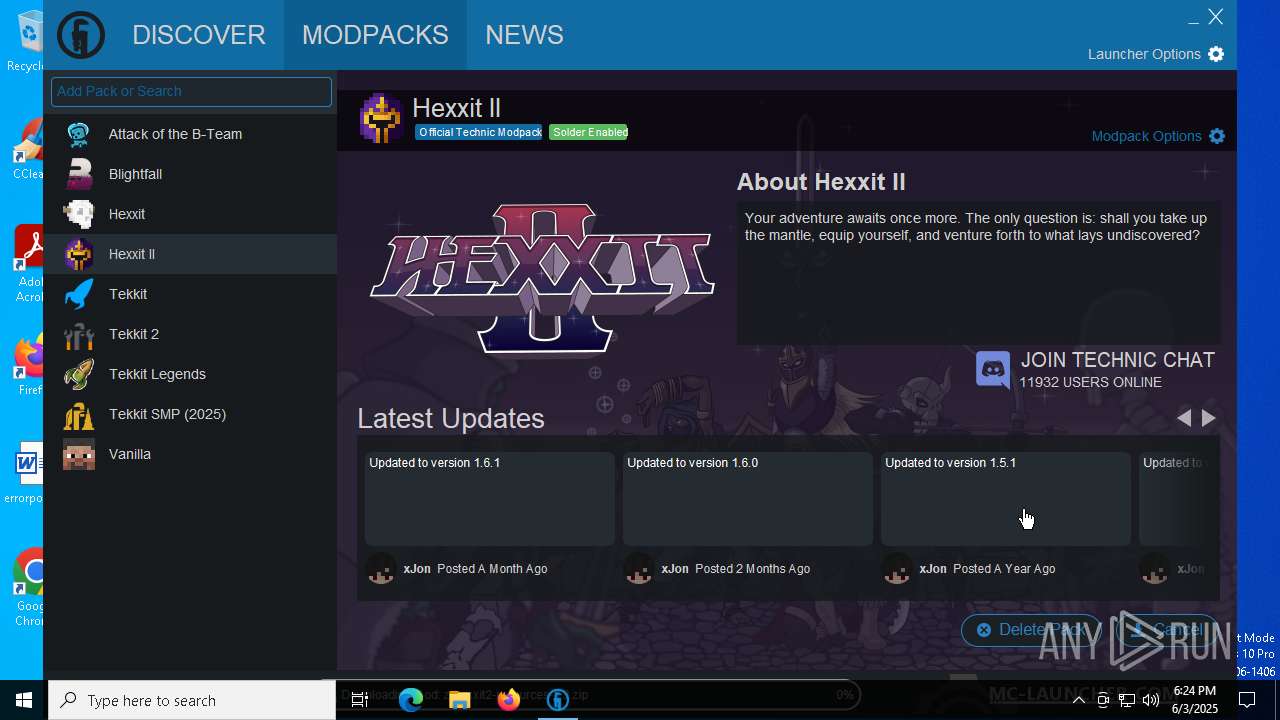
Checks for Java to be installed
- Technic Z1.1.exe (PID: 5960)
- Technic Z1.1.exe (PID: 6068)
Uses REG/REGEDIT.EXE to modify registry
- javaw.exe (PID: 7380)
There is functionality for taking screenshot (YARA)
- javaw.exe (PID: 7380)
INFO
Creates files in the program directory
- javaw.exe (PID: 5968)
The sample compiled with english language support
- Technic Z1.1.exe (PID: 5960)
Reads the computer name
- javaw.exe (PID: 5968)
- javaw.exe (PID: 7380)
Create files in a temporary directory
- javaw.exe (PID: 5968)
- javaw.exe (PID: 7380)
- java.exe (PID: 8116)
- java.exe (PID: 7224)
- java.exe (PID: 7676)
Checks supported languages
- javaw.exe (PID: 5968)
- Technic Z1.1.exe (PID: 5960)
- Technic Z1.1.exe (PID: 6068)
- javaw.exe (PID: 7380)
- java.exe (PID: 8116)
- java.exe (PID: 7224)
- java.exe (PID: 7676)
Reads the machine GUID from the registry
- javaw.exe (PID: 5968)
- javaw.exe (PID: 7380)
Creates files or folders in the user directory
- javaw.exe (PID: 5968)
- javaw.exe (PID: 7380)
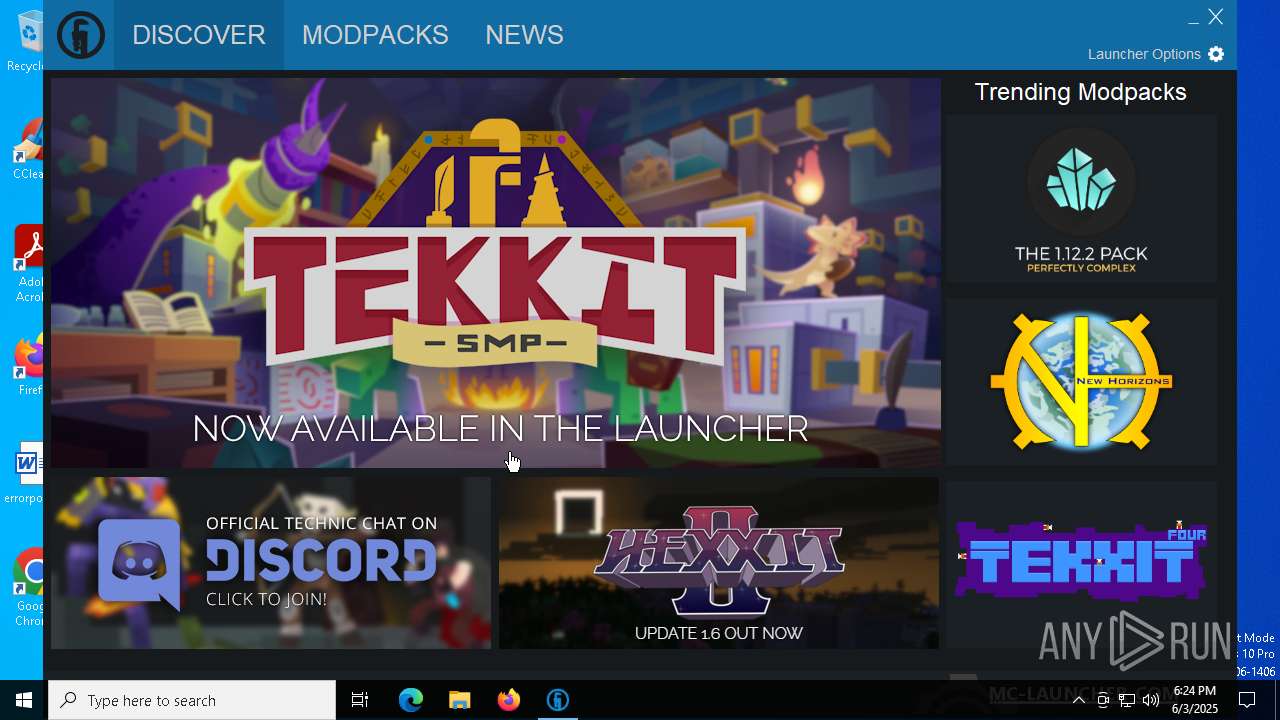
Attempting to use instant messaging service
- javaw.exe (PID: 7380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:07:10 16:24:03+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 23040 |
| InitializedDataSize: | 31744 |
| UninitializedDataSize: | 36352 |
| EntryPoint: | 0x1590 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.757 |
| ProductVersionNumber: | 4.0.0.757 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
| FileDescription: | Technic Launcher |
| FileVersion: | 4.0.0.757 |
| InternalName: | launcher |
| LegalCopyright: | Syndicate, LLC, https://www.technicpack.net |
| LegalTrademarks: | - |
| OriginalFileName: | launcher.exe |
| ProductName: | Technic Launcher |
| ProductVersion: | 4.0.0.757 |
Total processes
140
Monitored processes
17
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | C:\WINDOWS\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4008 | reg query HKEY_LOCAL_MACHINE\Software\JavaSoft\ /f Home /t REG_SZ /s /reg:64 | C:\Windows\System32\reg.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4272 | reg query HKEY_LOCAL_MACHINE\Software\JavaSoft\ /f Home /t REG_SZ /s /reg:32 | C:\Windows\System32\reg.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
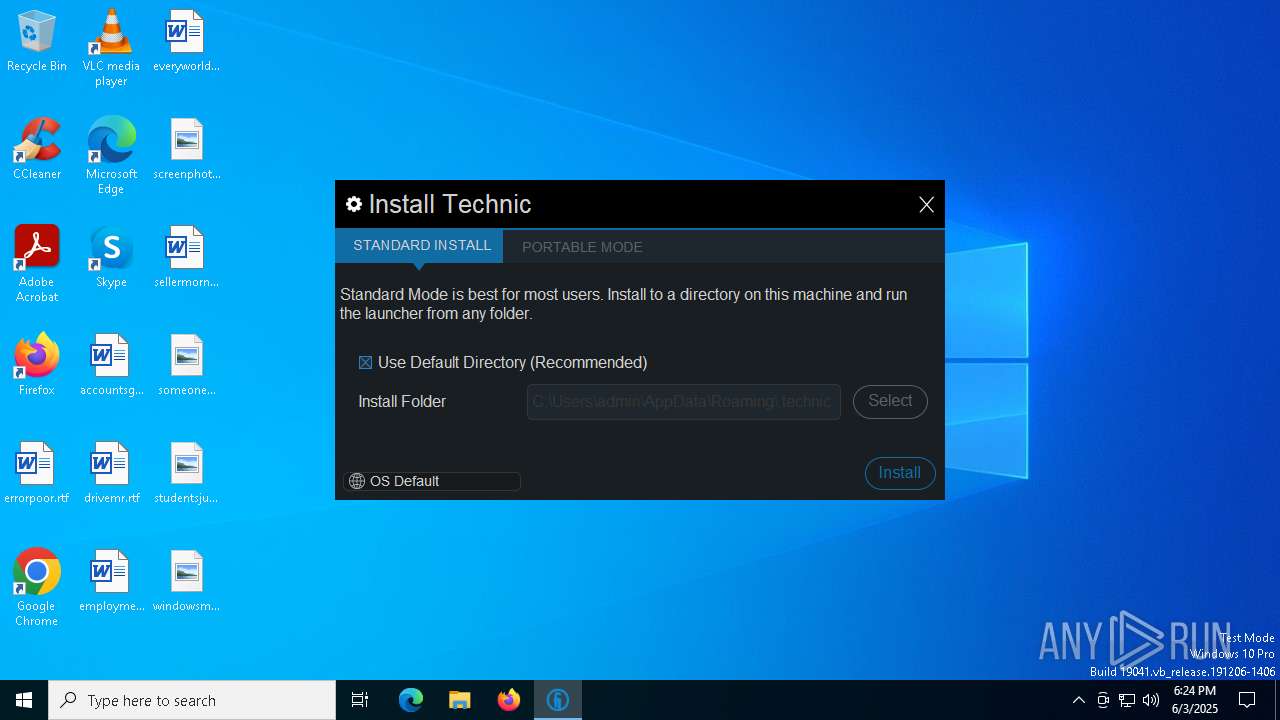
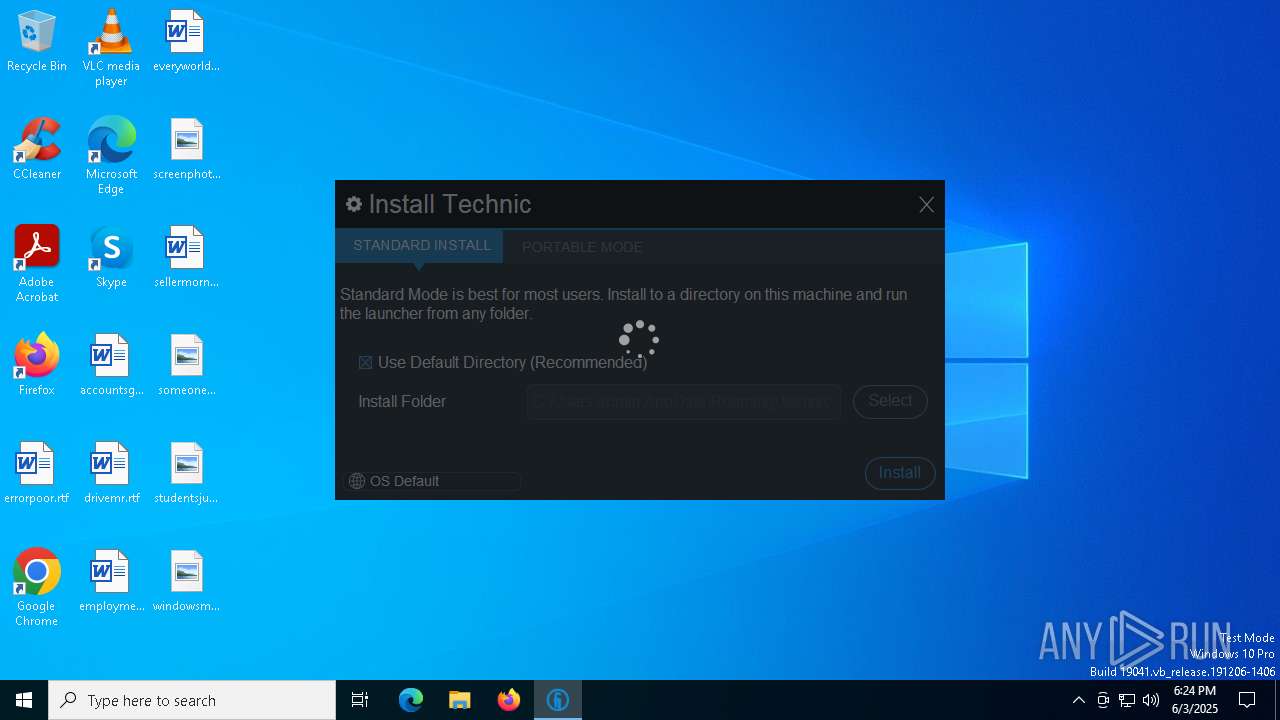
| 5960 | "C:\Users\admin\AppData\Local\Temp\Technic Z1.1.exe" | C:\Users\admin\AppData\Local\Temp\Technic Z1.1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Technic Launcher Exit code: 0 Version: 4.0.0.757 Modules
| |||||||||||||||
| 5968 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -Djava.net.preferIPv4Stack=true -Dawt.useSystemAAFontSettings=lcd -Dswing.aatext=true -classpath "C:\Users\admin\AppData\Local\Temp\Technic Z1.1.exe;anything" net.technicpack.launcher.LauncherMain | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | Technic Z1.1.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
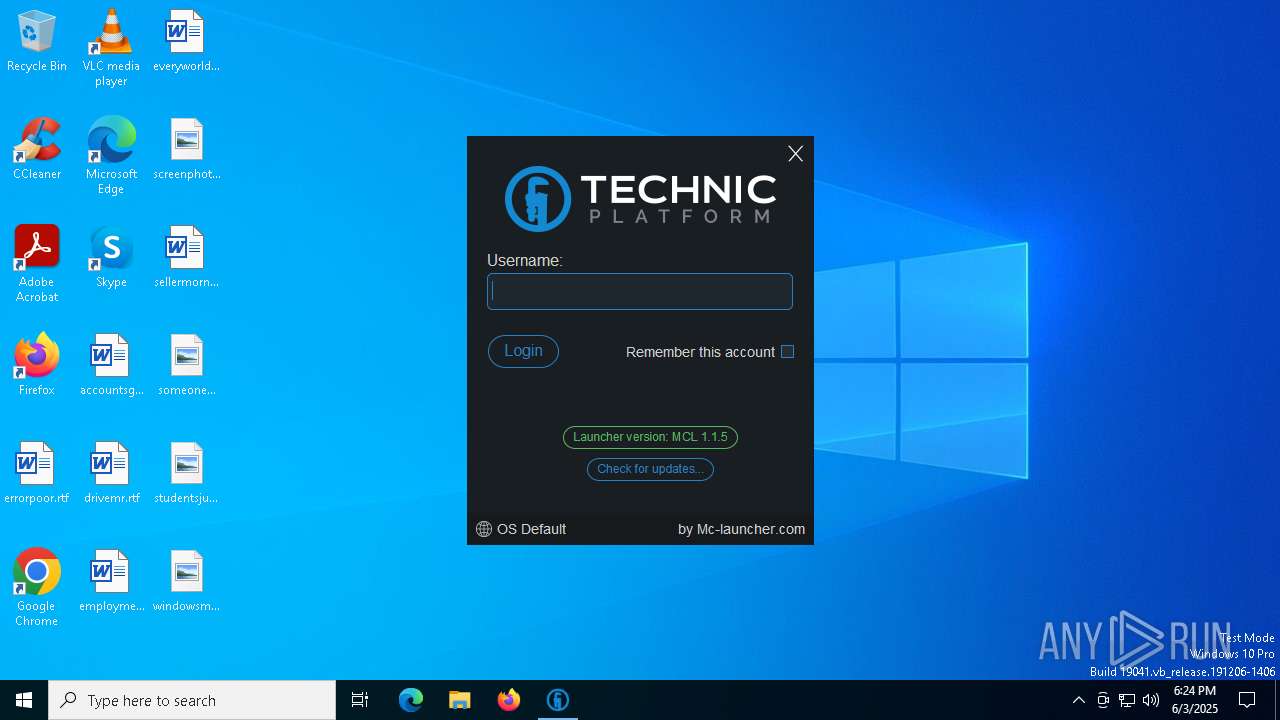
| 6068 | "C:\Users\admin\AppData\Local\Temp\Technic Z1.1.exe" | C:\Users\admin\AppData\Local\Temp\Technic Z1.1.exe | — | javaw.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Technic Launcher Exit code: 0 Version: 4.0.0.757 Modules
| |||||||||||||||
Total events
1 893
Read events
1 893
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
443
Text files
954
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5968 | javaw.exe | C:\Users\admin\AppData\Roaming\.technic\settings.json | binary | |
MD5:B0293C01C9EF805A80E7FB9DF361C102 | SHA256:B79F48EC48F33FD6890D7A3E27B4B7C0544CFF4FADA6DDCDE79FFDACE4DEC88D | |||
| 7380 | javaw.exe | C:\Users\admin\AppData\Roaming\.technic\logs\techniclauncher_2025-06-03.log | text | |
MD5:5E51288E996DEECDC43AA53FB566E658 | SHA256:C6E121090F3EA8B4D6B3410FE5D38DCB2DCD5893A44F019E34C2D17F3C399931 | |||
| 7380 | javaw.exe | C:\Users\admin\AppData\Roaming\.technic\assets\avatars\gravitar\Pyker.png | — | |
MD5:— | SHA256:— | |||
| 7380 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio3761594829993350411.tmp | image | |
MD5:C525BBB493AA27FBDC70C8B1316F7720 | SHA256:E3C3454EE06979CAC0516984A7291558D7E52F43C6E60367F9797287E2390C97 | |||
| 7380 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio28842161798625251.tmp | image | |
MD5:C525BBB493AA27FBDC70C8B1316F7720 | SHA256:E3C3454EE06979CAC0516984A7291558D7E52F43C6E60367F9797287E2390C97 | |||
| 7380 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio1104081089140555926.tmp | image | |
MD5:C525BBB493AA27FBDC70C8B1316F7720 | SHA256:E3C3454EE06979CAC0516984A7291558D7E52F43C6E60367F9797287E2390C97 | |||
| 7380 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio6515045937468142364.tmp | image | |
MD5:0BBA5ABB1DC6C530B7AC07013D2AF13C | SHA256:CD42745BCD36ABC298E9C1E591E6F2770279AE9BE55768DDD0B467B5802DE0A1 | |||
| 5968 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio5028298480294986553.tmp | image | |
MD5:C525BBB493AA27FBDC70C8B1316F7720 | SHA256:E3C3454EE06979CAC0516984A7291558D7E52F43C6E60367F9797287E2390C97 | |||
| 5968 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:C63FC3407496501A9D7FECF39CDE6CE2 | SHA256:20414038BA3E125B00041ECADAC7EFCC7C87EF337001927992C855E1AA2386CF | |||
| 5968 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\83aa4cc77f591dfc2374580bbd95f6ba_bb926e54-e3ca-40fd-ae90-2764341e7792 | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
77
DNS requests
33
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7344 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7344 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
8044 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.209.214.100:80 | www.microsoft.com | PT. Telekomunikasi Selular | ID | whitelisted |
5404 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5968 | javaw.exe | 172.217.16.142:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
7380 | javaw.exe | 104.26.7.125:443 | technicpack.net | CLOUDFLARENET | US | whitelisted |
7380 | javaw.exe | 192.0.80.240:443 | gravatar.com | AUTOMATTIC | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
minecraft.net |
| whitelisted |
session.minecraft.net |
| whitelisted |
textures.minecraft.net |
| whitelisted |
libraries.minecraft.net |
| shared |
authserver.mojang.com |
| whitelisted |
account.mojang.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
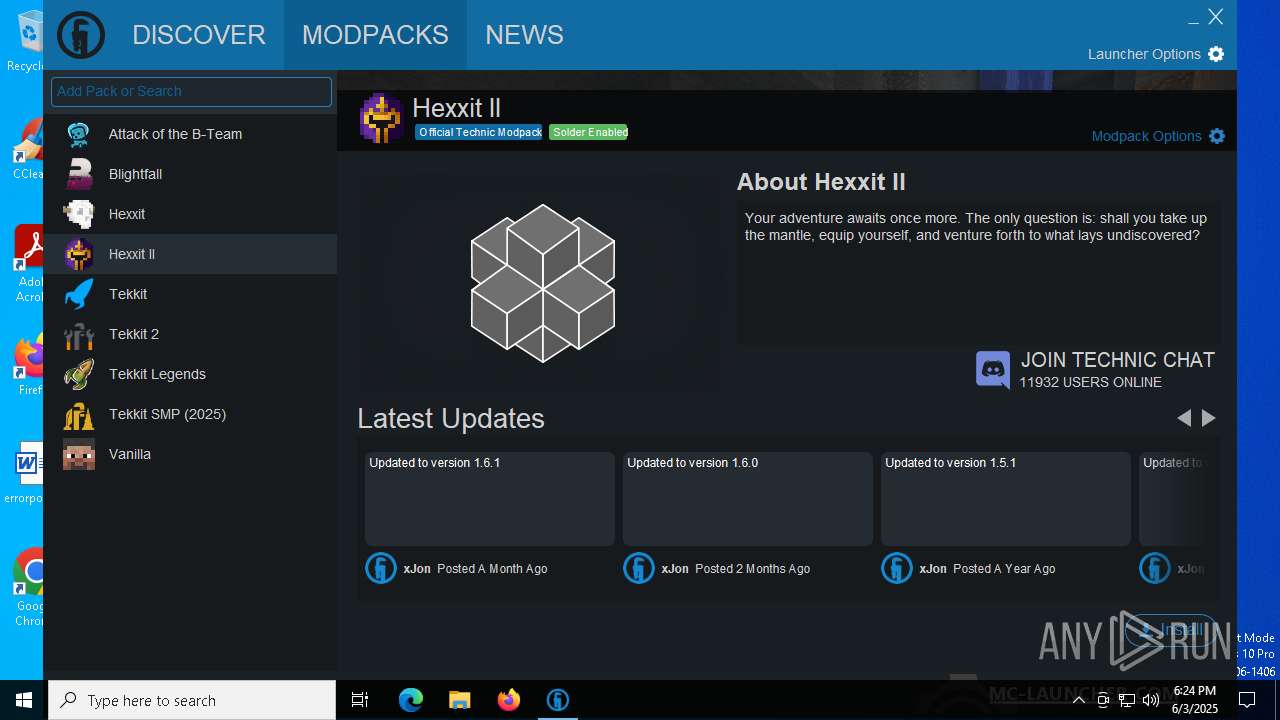
2196 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
7380 | javaw.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2196 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
7380 | javaw.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |