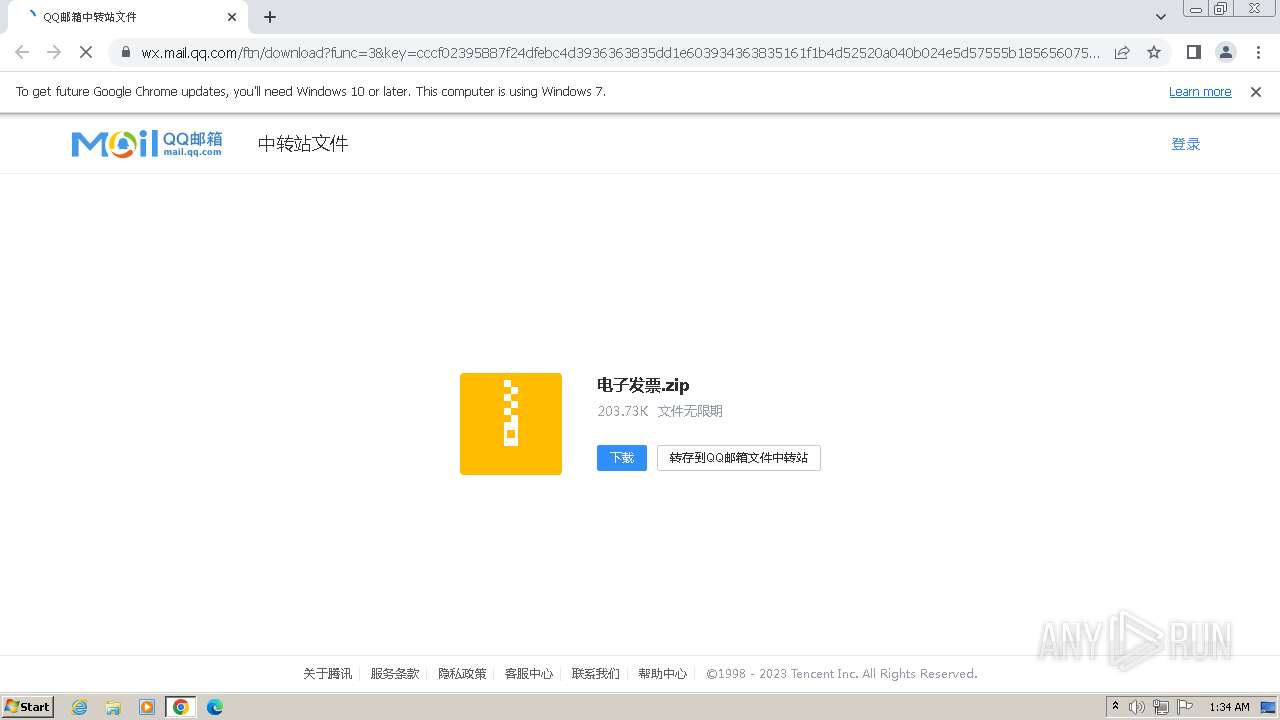
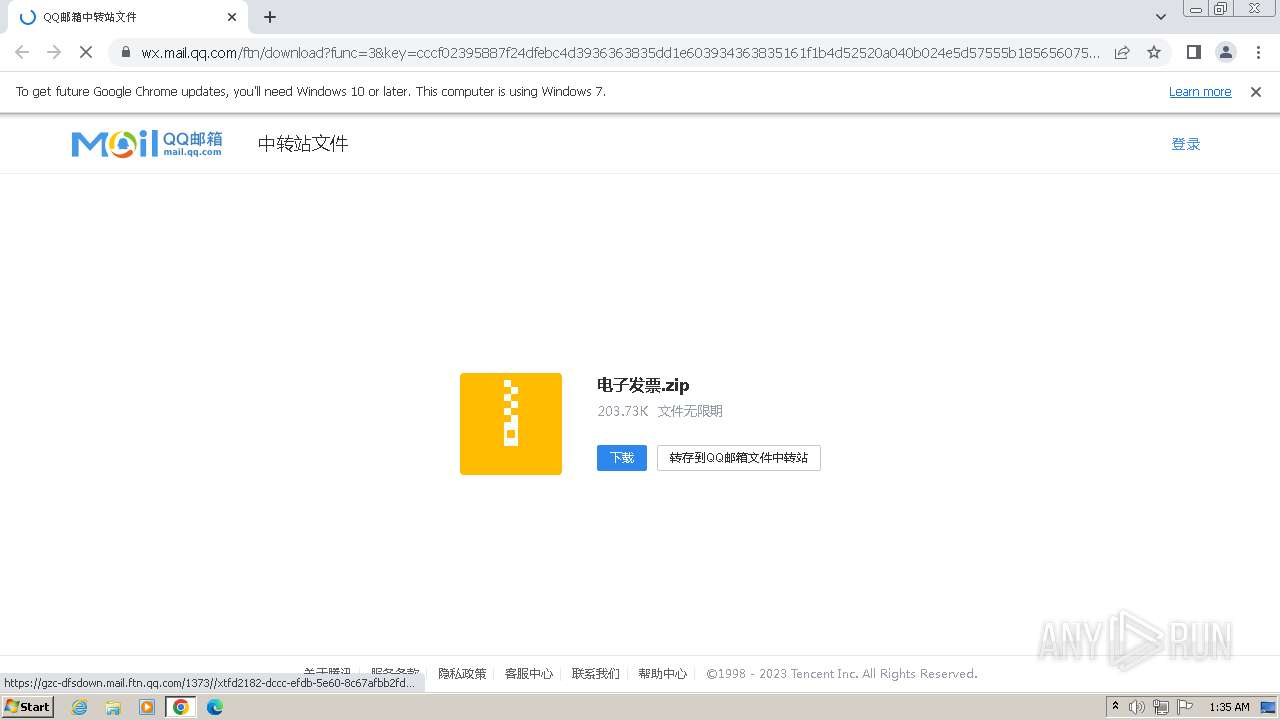
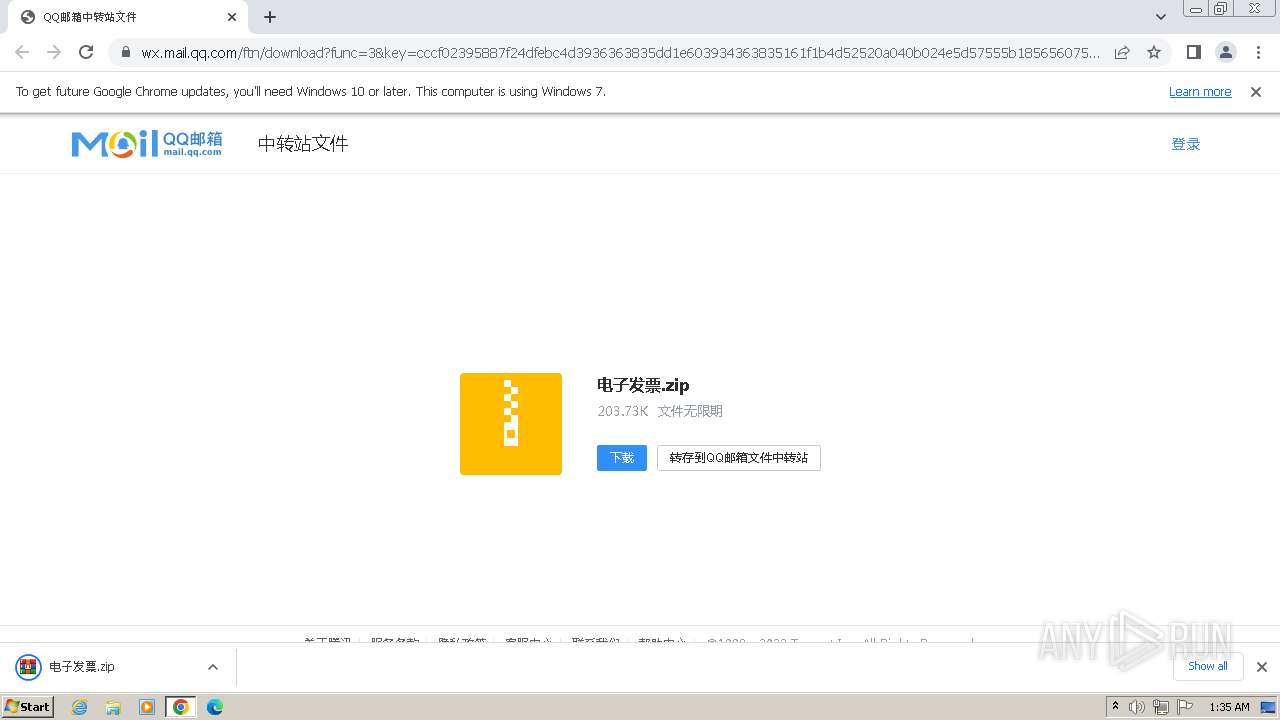
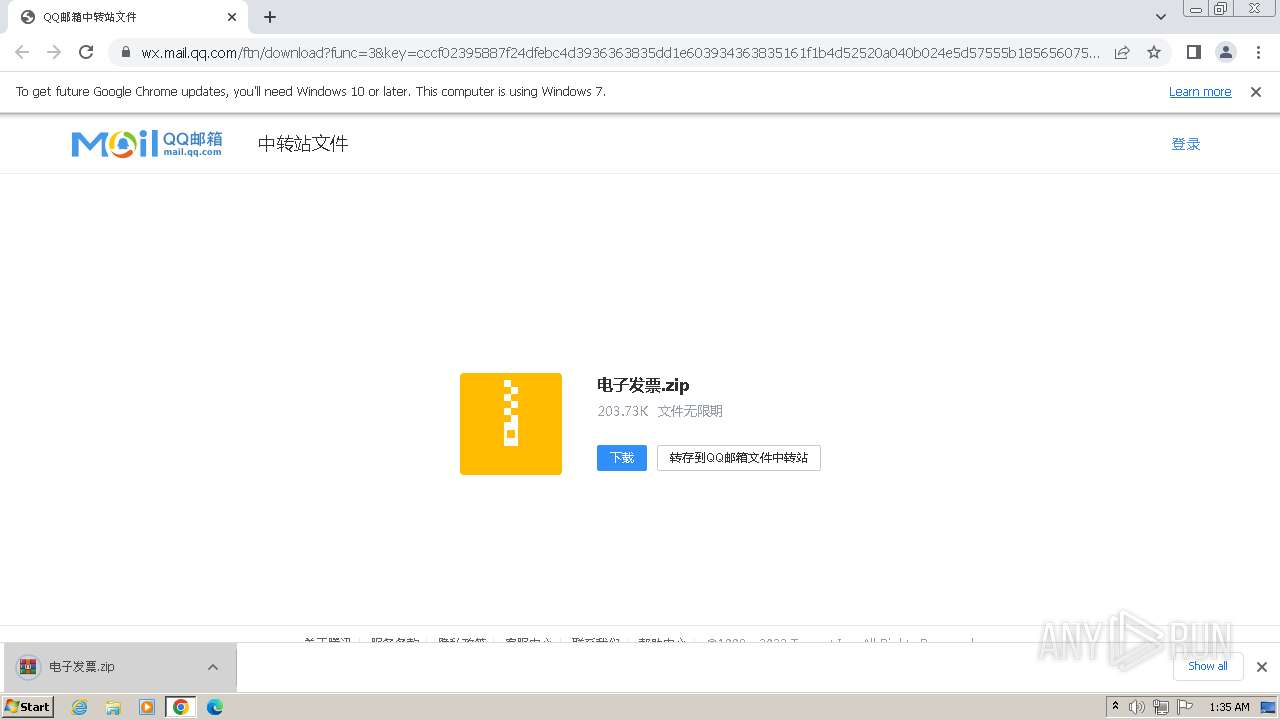
| URL: | https://wx.mail.qq.com/ftn/download?func=3&key=cccf02395887f24dfebc4d3936363835dd1e603934363835161f1b4d52520a040b024e5d57555b185656075b19035d03031d5b5a020159535152515f50552835d4a4d6dc99a6ddbaa2d7c6911a4c514527597bec4baea8bc33304bc424f751d2d9a7780441&code=30c94685&k=cccf02395887f24dfebc4d3936363835dd1e603934363835161f1b4d52520a040b024e5d57555b185656075b19035d03031d5b5a020159535152515f50552835d4a4d6dc99a6ddbaa2d7c6911a4c514527597bec4baea8bc33304bc424f751d2d9a7780441&fweb=1&cl=1 |
| Full analysis: | https://app.any.run/tasks/928b2a93-943d-4a14-b1b6-0c51a8c3c94c |
| Verdict: | Malicious activity |
| Analysis date: | November 21, 2023, 01:34:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 18D0F3C053865DB996D68C4C1902D8A13B17A94A |
| SHA256: | 9E2824E111CC95AD518791961DE77BC6A85D90BAA4167C53B319CA781EB8E605 |
| SSDEEP: | 6:2MLIlbR5dZo2c8NG4fQnvrS0TB8RPi4deVvm5dZo2c8NG4fQnvrS0TB8RPi4sT:2MLIl15w8NRfQnjhX4r5w8NRfQnjhX4u |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks Windows Trust Settings
- pwsh.exe (PID: 2312)
Reads security settings of Internet Explorer
- pwsh.exe (PID: 2312)
Reads settings of System Certificates
- pwsh.exe (PID: 2312)
Process checks Powershell history file
- pwsh.exe (PID: 2312)
Reads the Internet Settings
- pwsh.exe (PID: 2312)
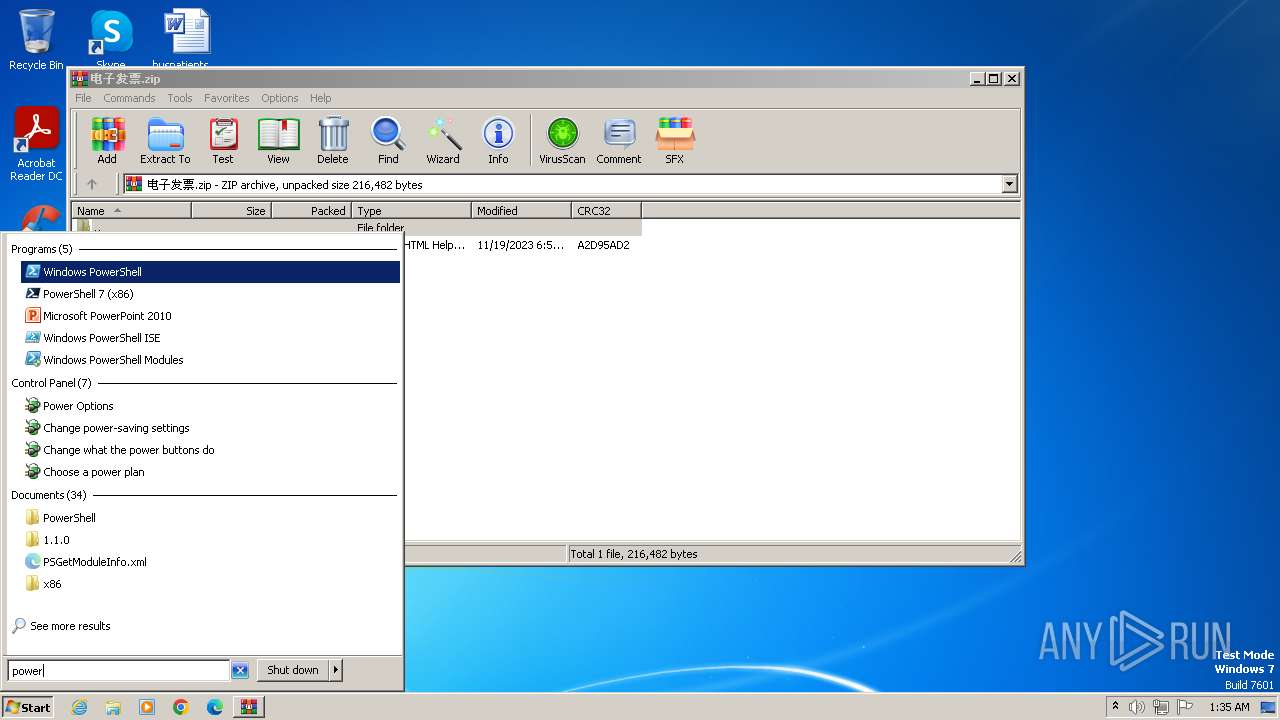
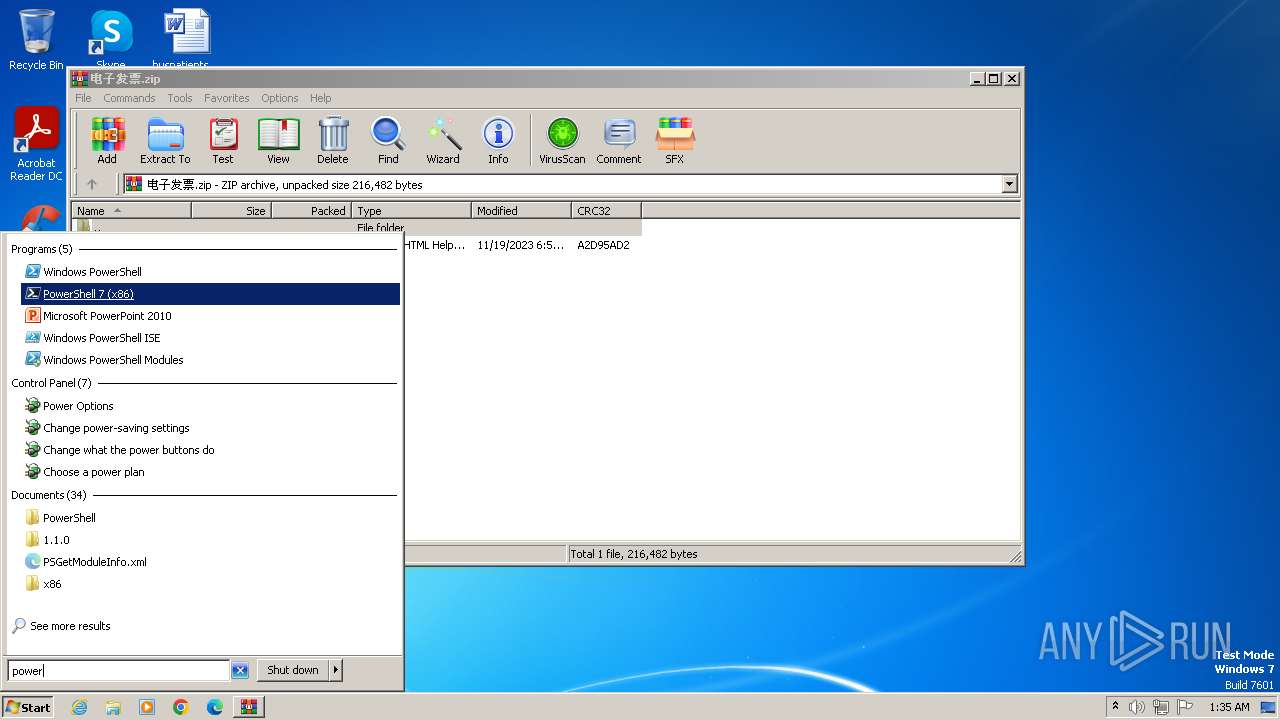
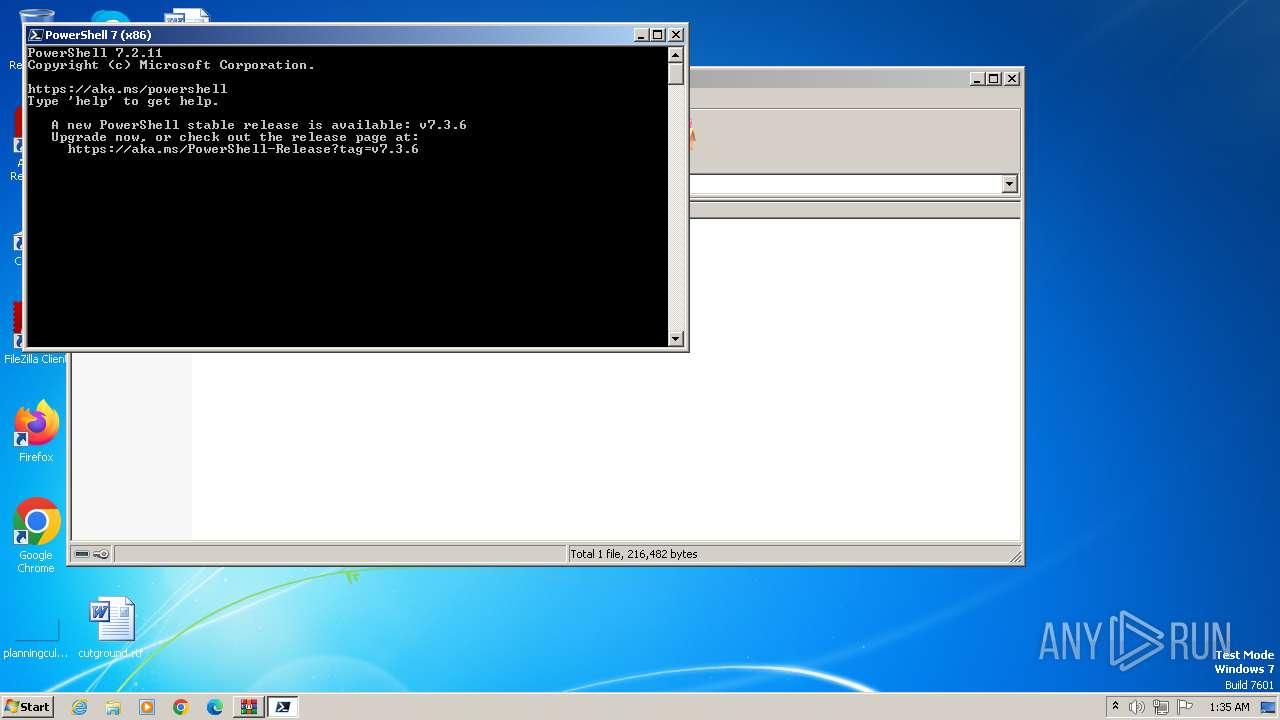
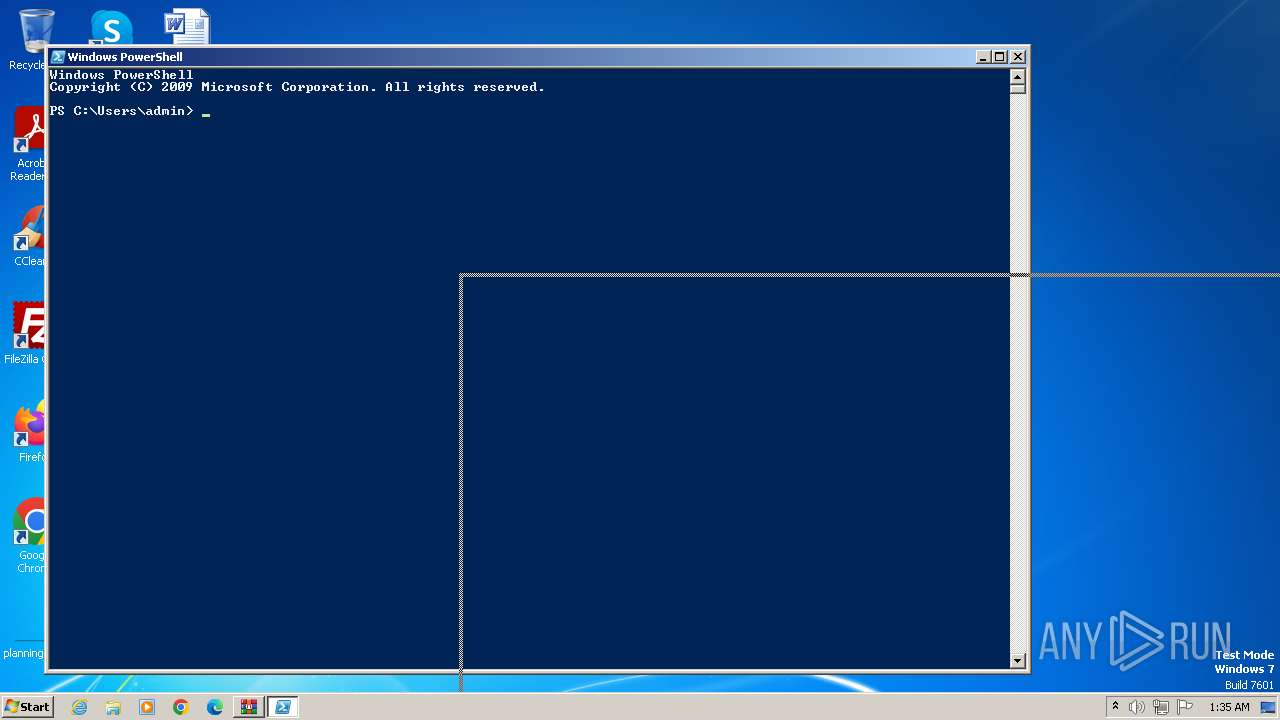
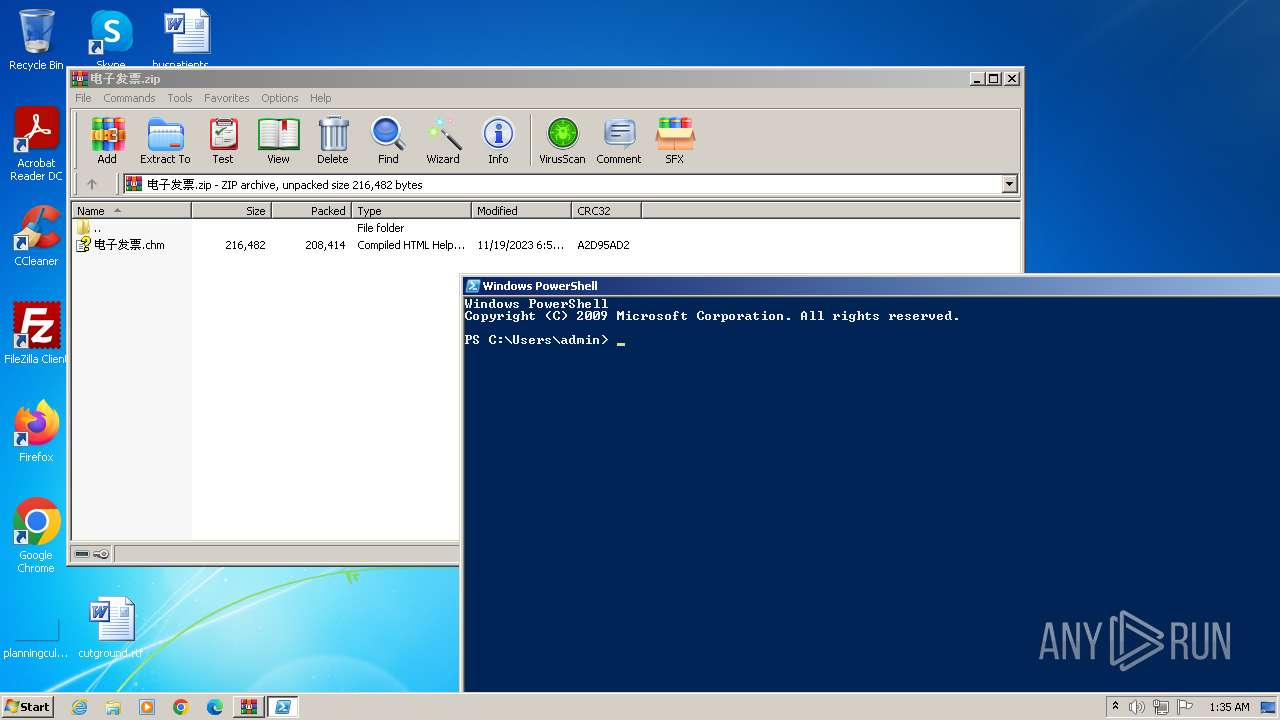
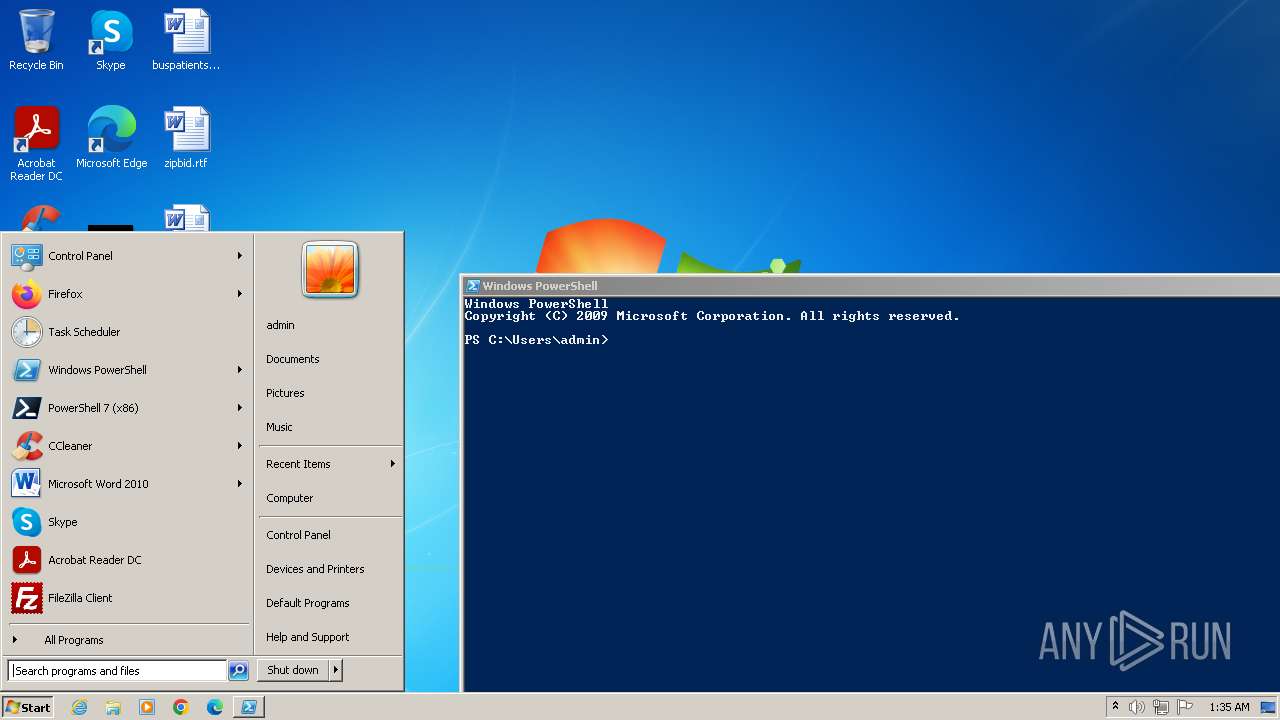
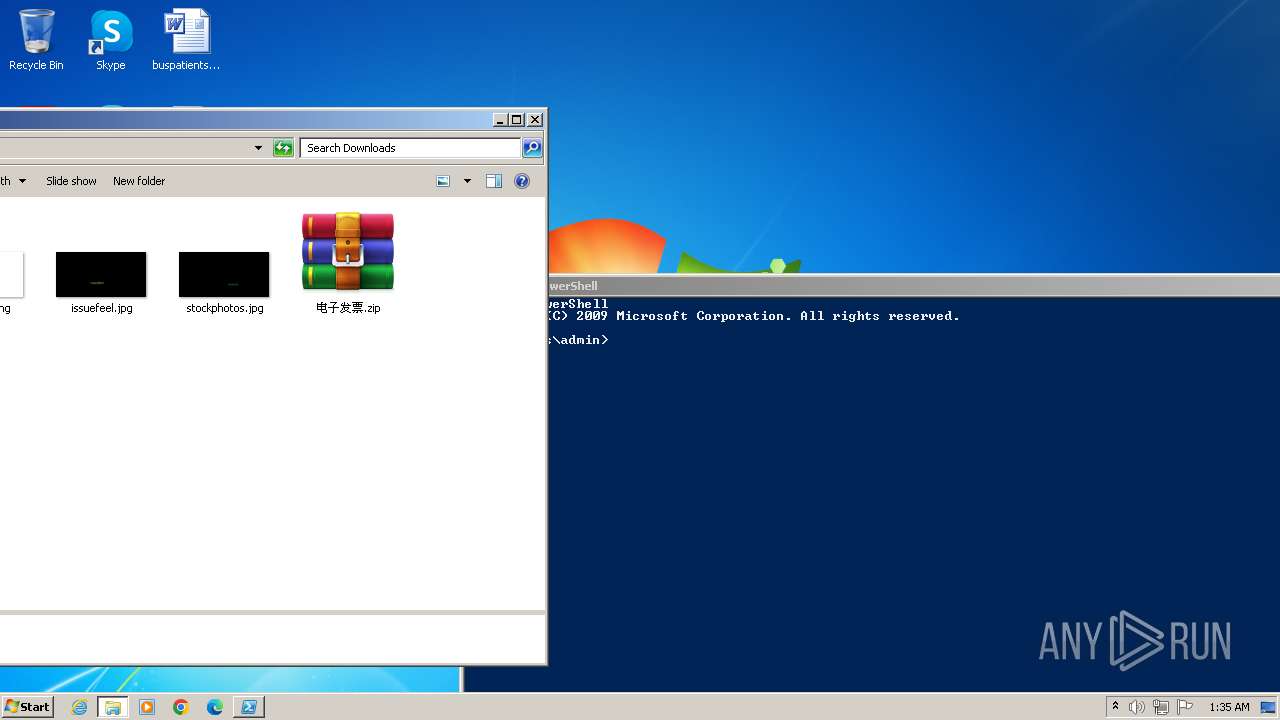
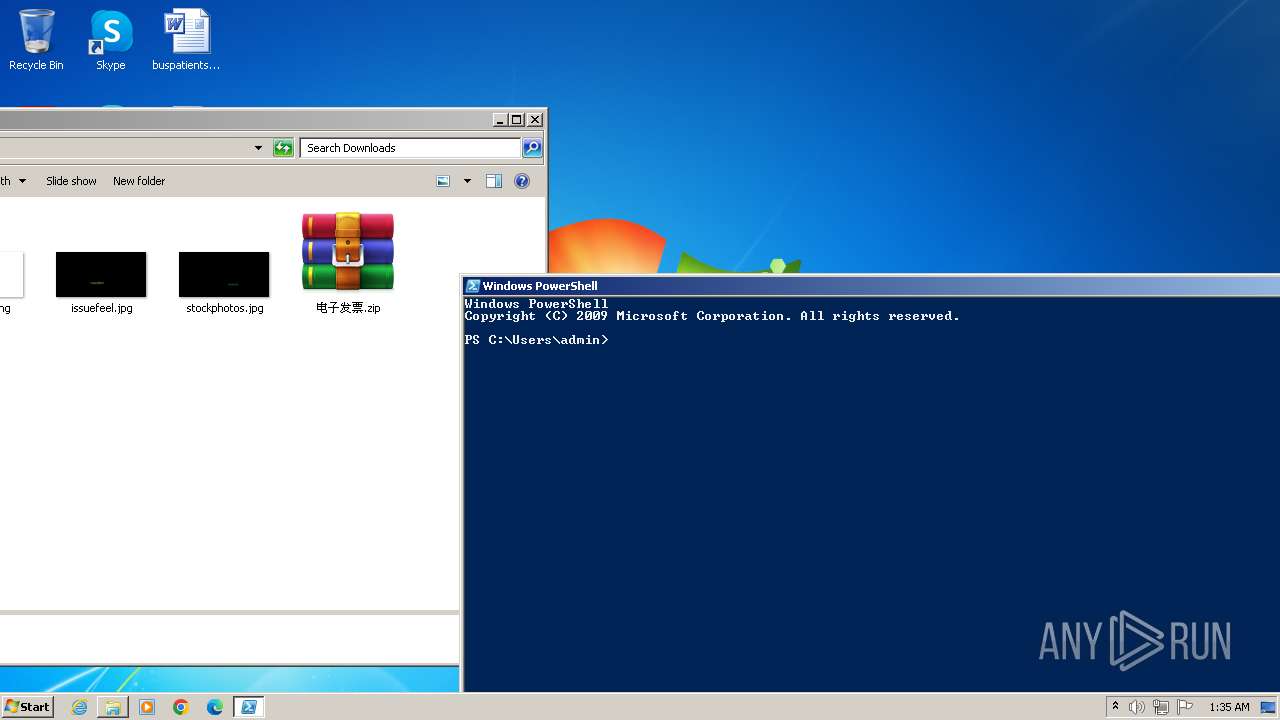
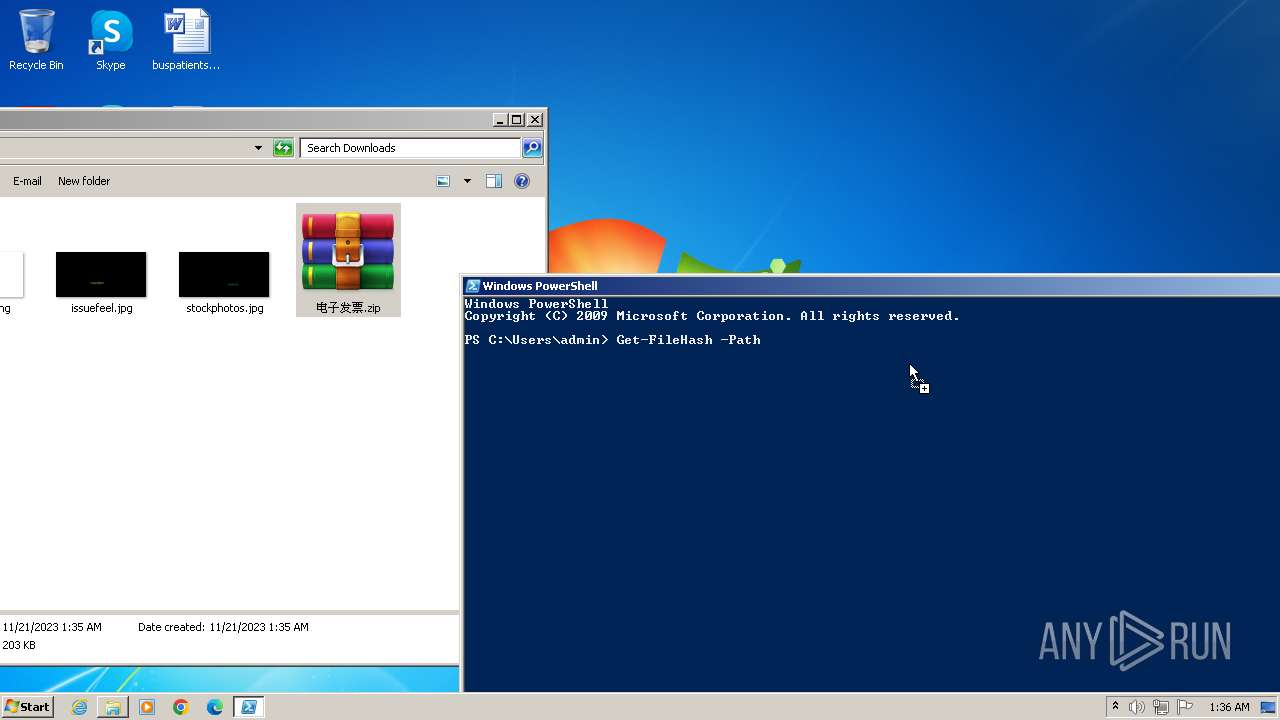
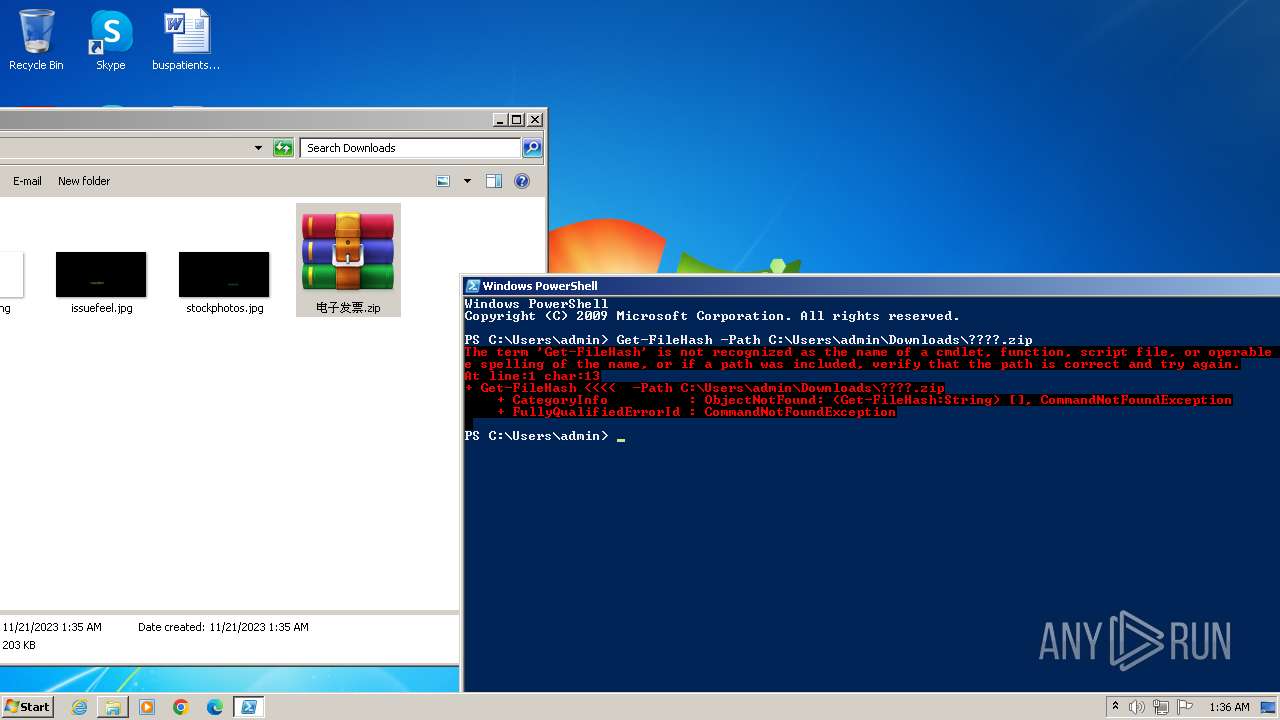
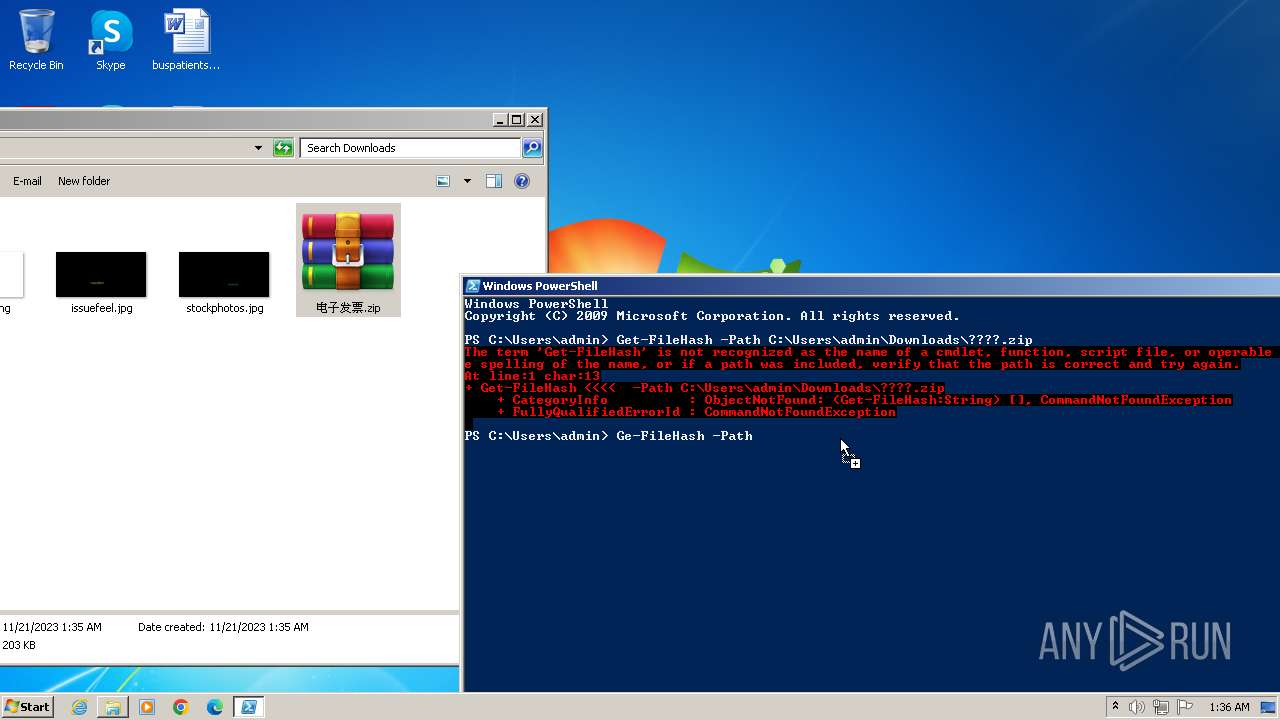
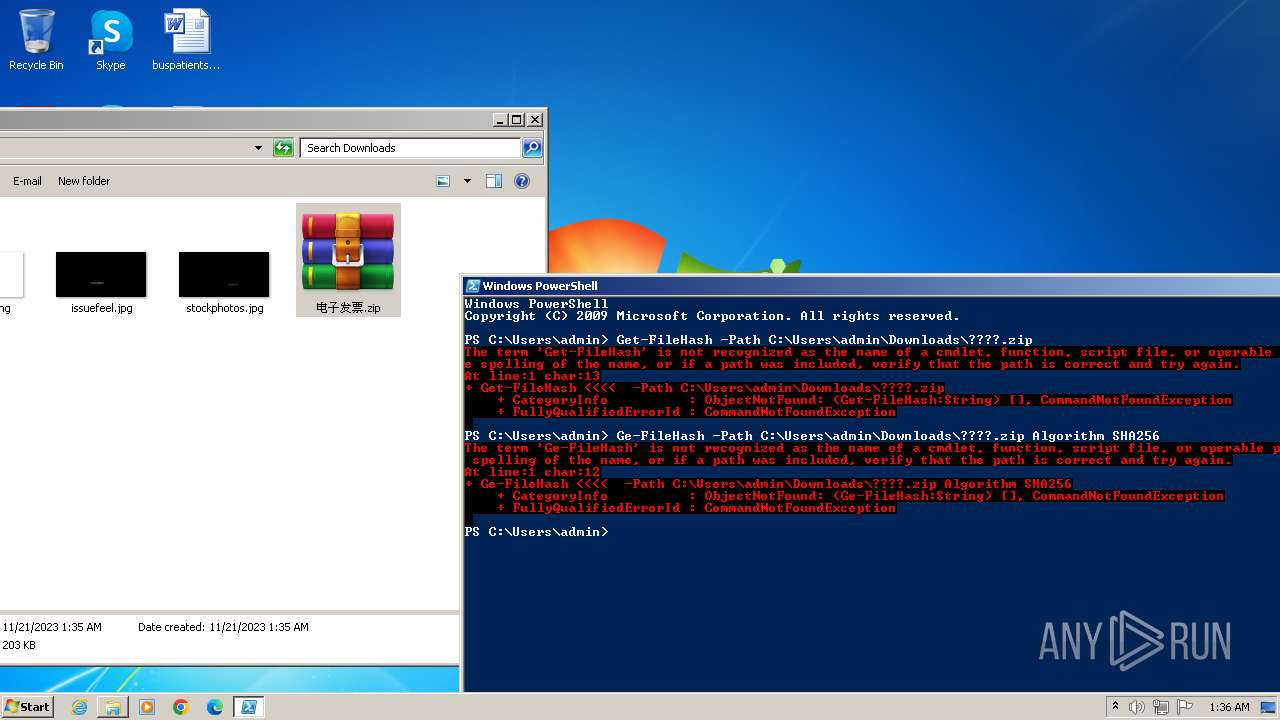
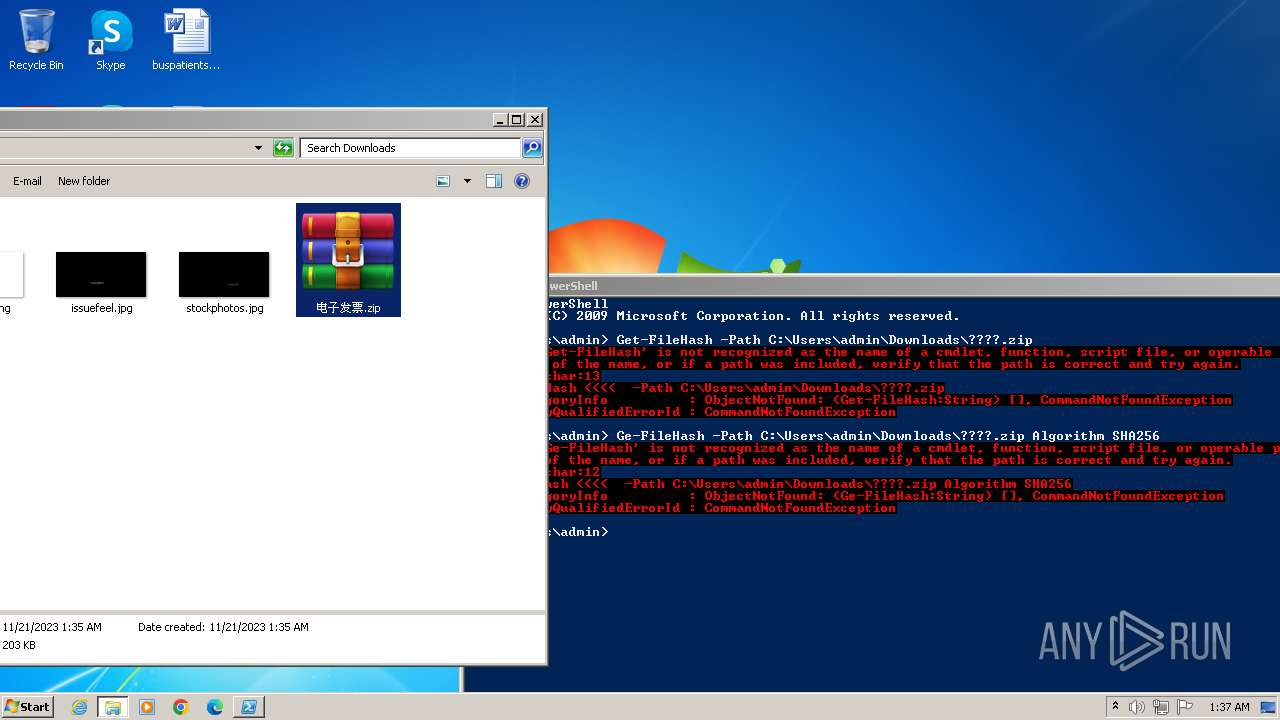
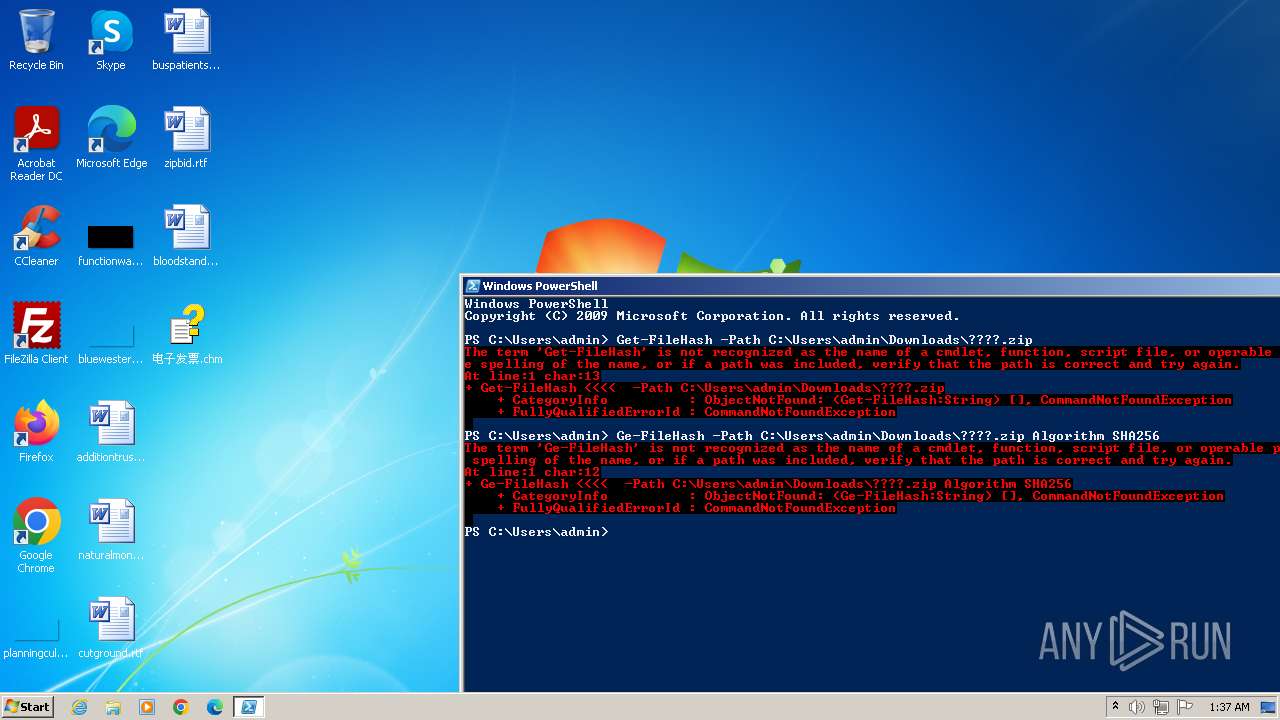
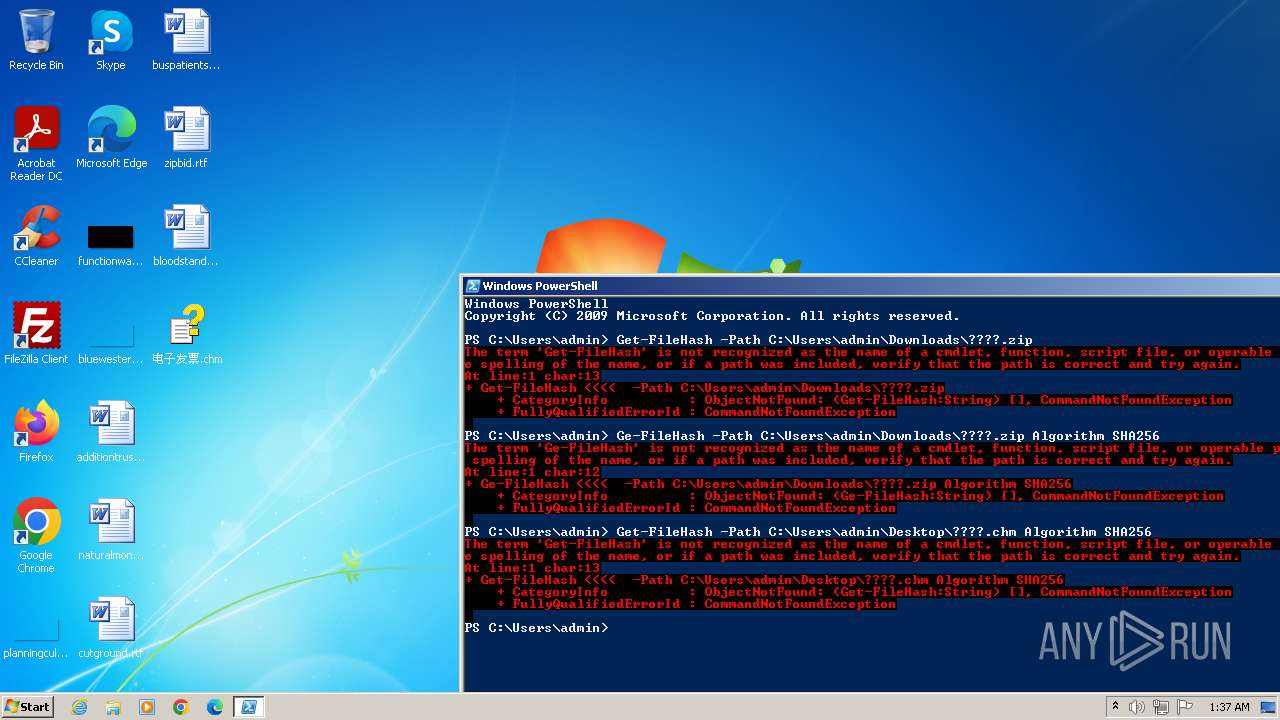
Powershell version downgrade attack
- powershell.exe (PID: 2552)
INFO
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 4036)
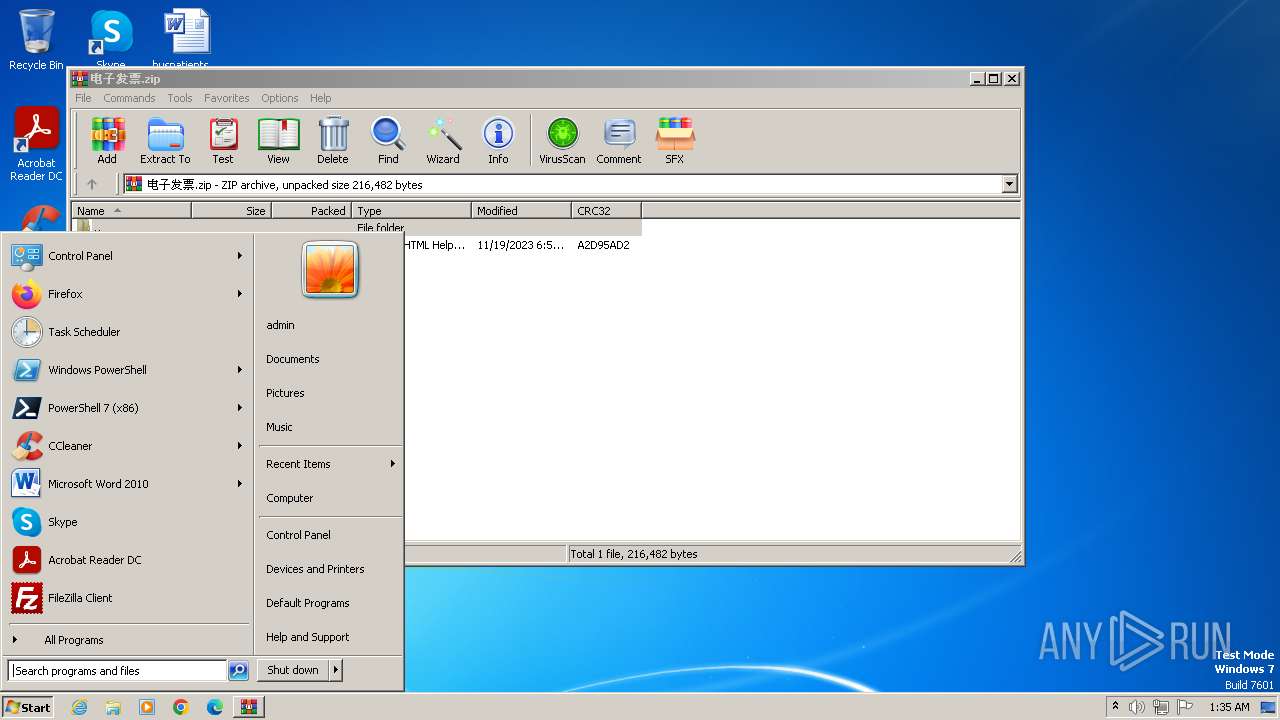
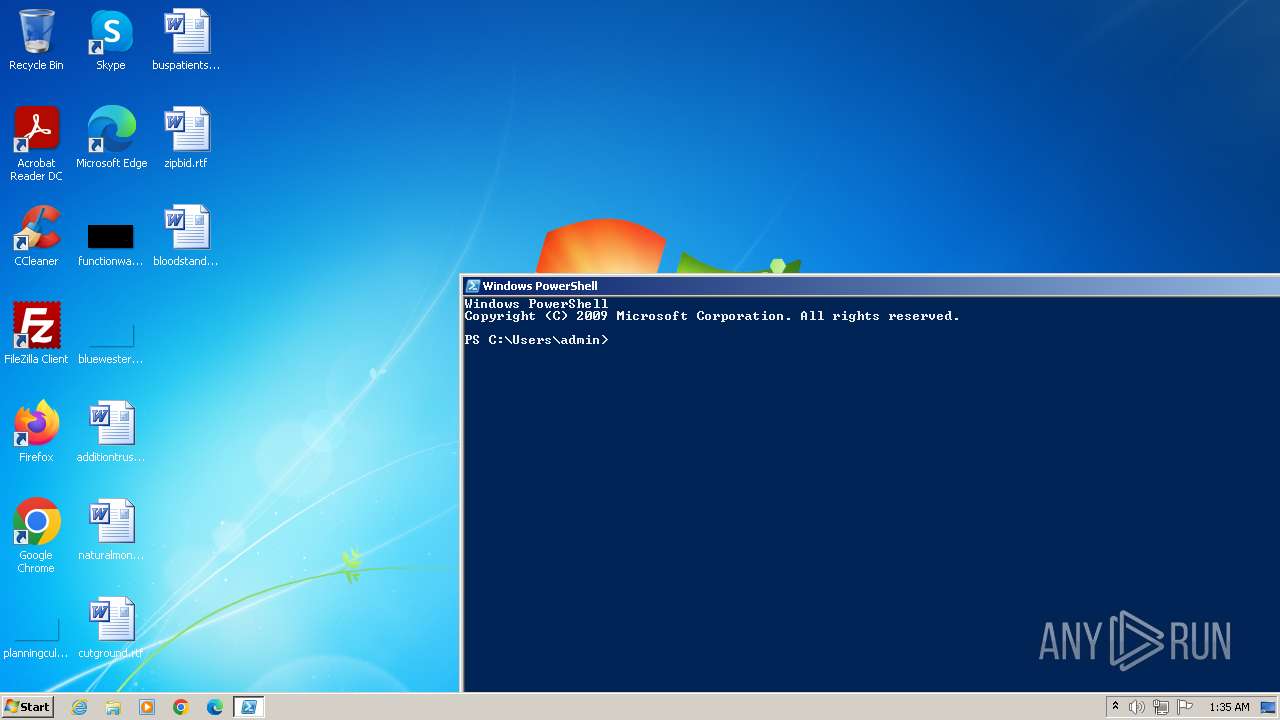
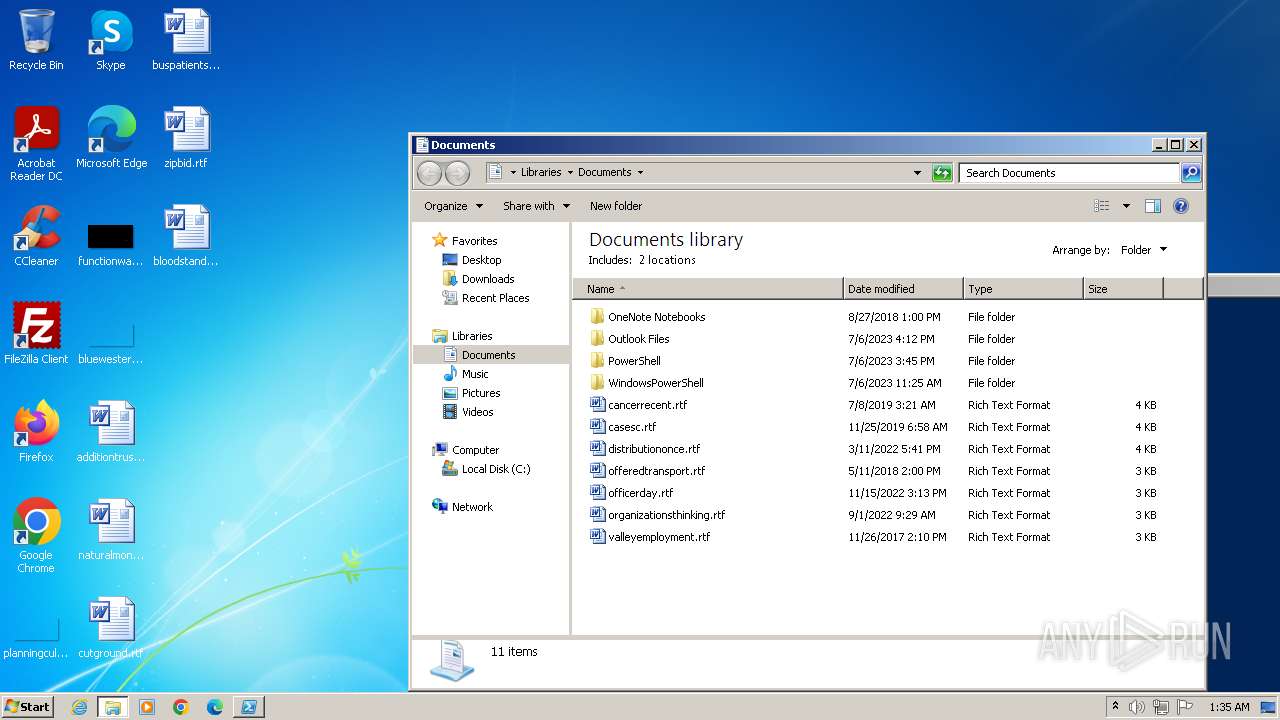
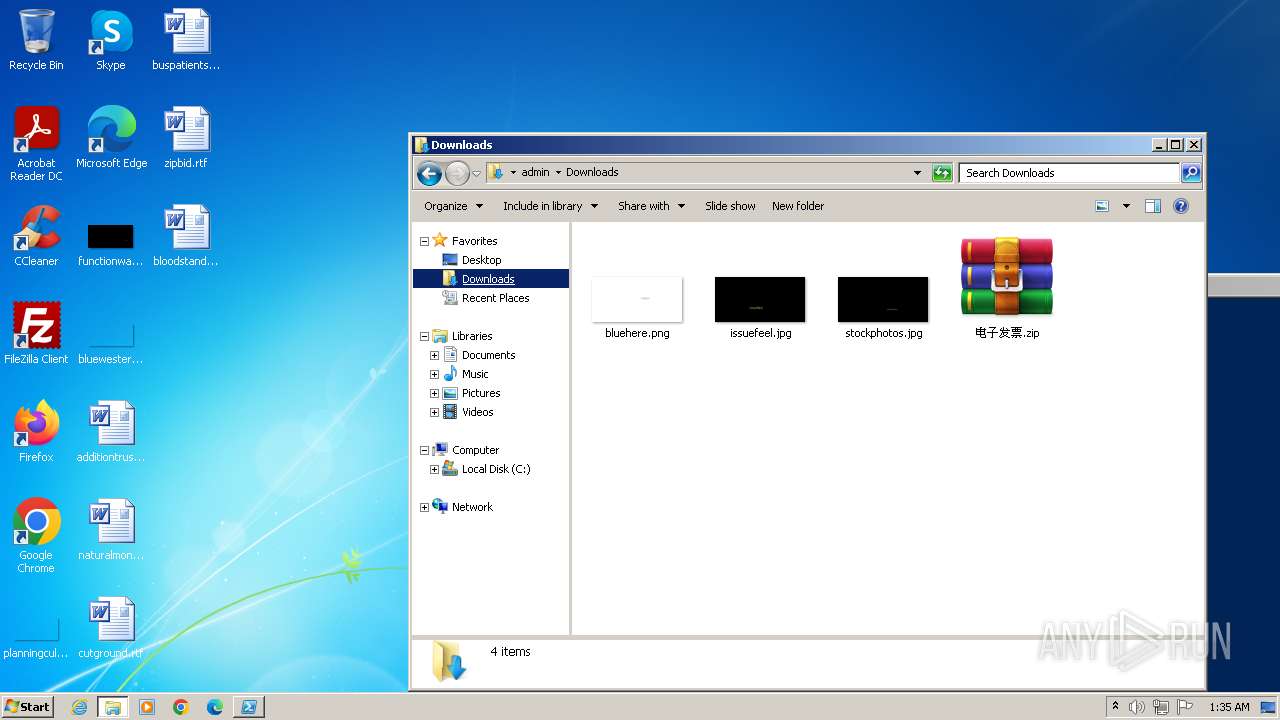
Manual execution by a user
- wmpnscfg.exe (PID: 4036)
- pwsh.exe (PID: 2312)
- powershell.exe (PID: 2552)
- WinRAR.exe (PID: 1028)
Application launched itself
- chrome.exe (PID: 3376)
Checks supported languages
- wmpnscfg.exe (PID: 4036)
- pwsh.exe (PID: 2312)
Reads the computer name
- wmpnscfg.exe (PID: 4036)
- pwsh.exe (PID: 2312)
The process uses the downloaded file
- chrome.exe (PID: 1760)
- WinRAR.exe (PID: 1028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
17
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3096 --field-trial-handle=1152,i,9150392974675919024,10729428685890228018,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
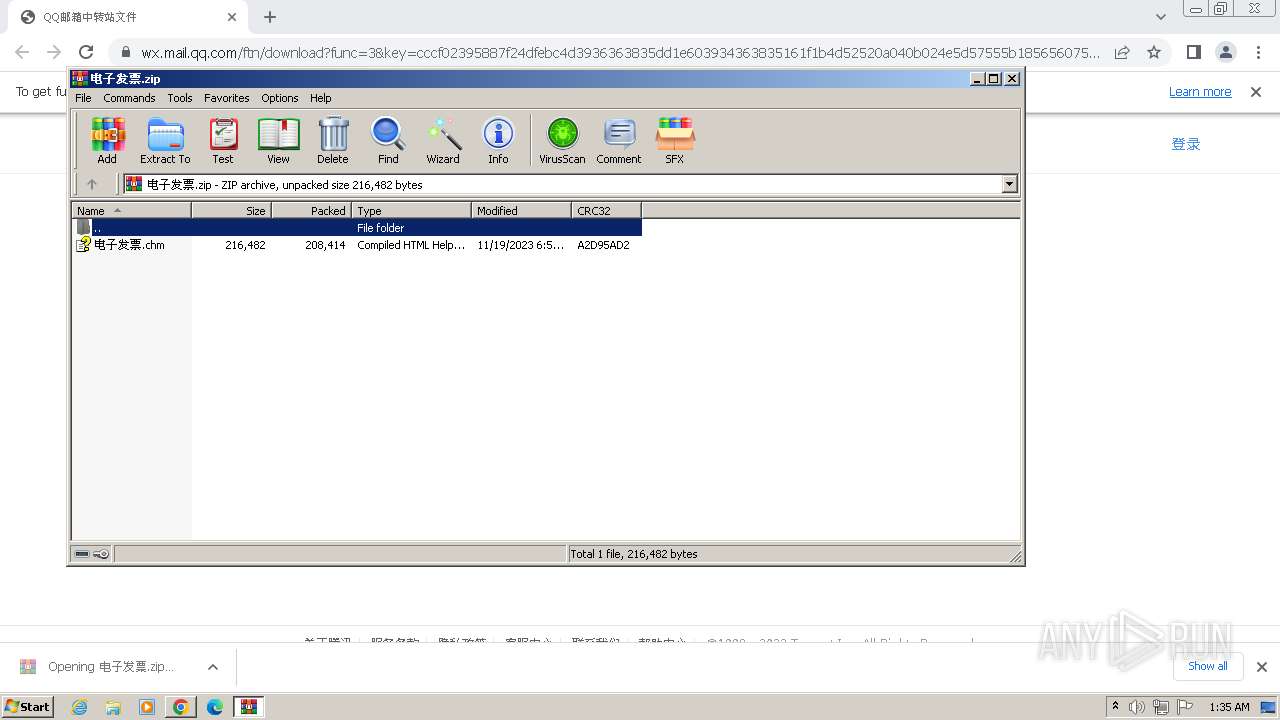
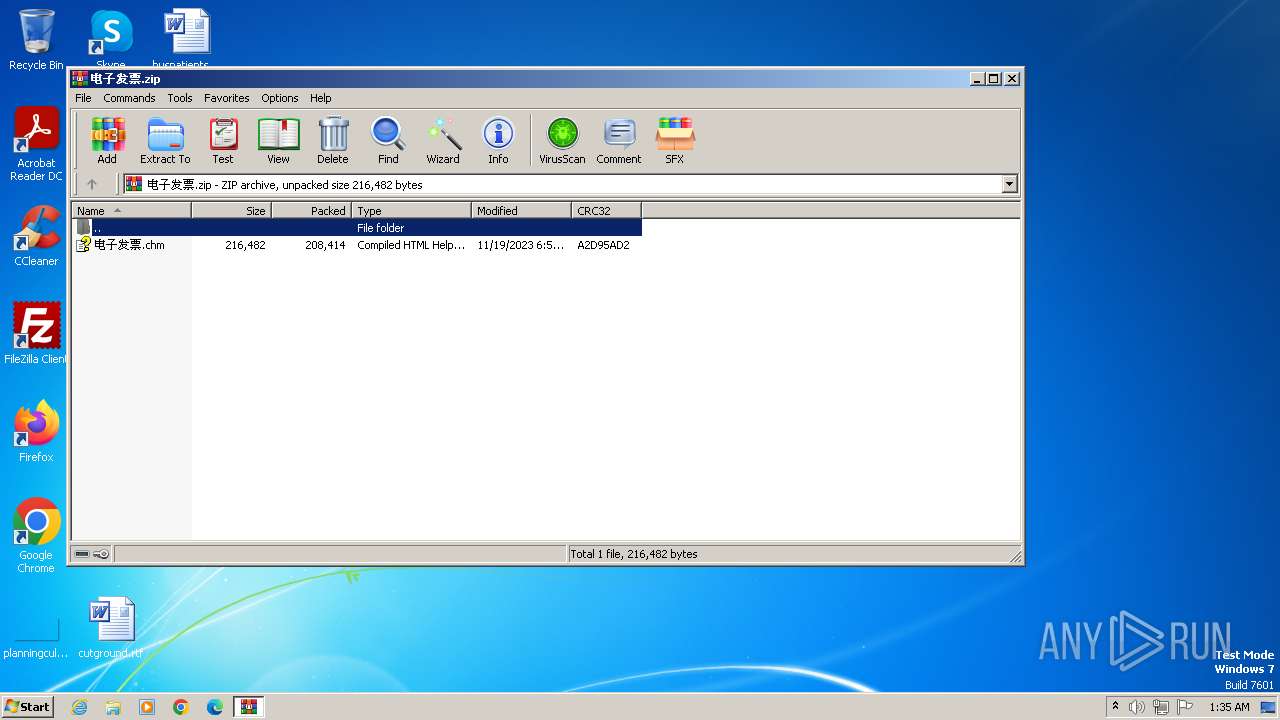
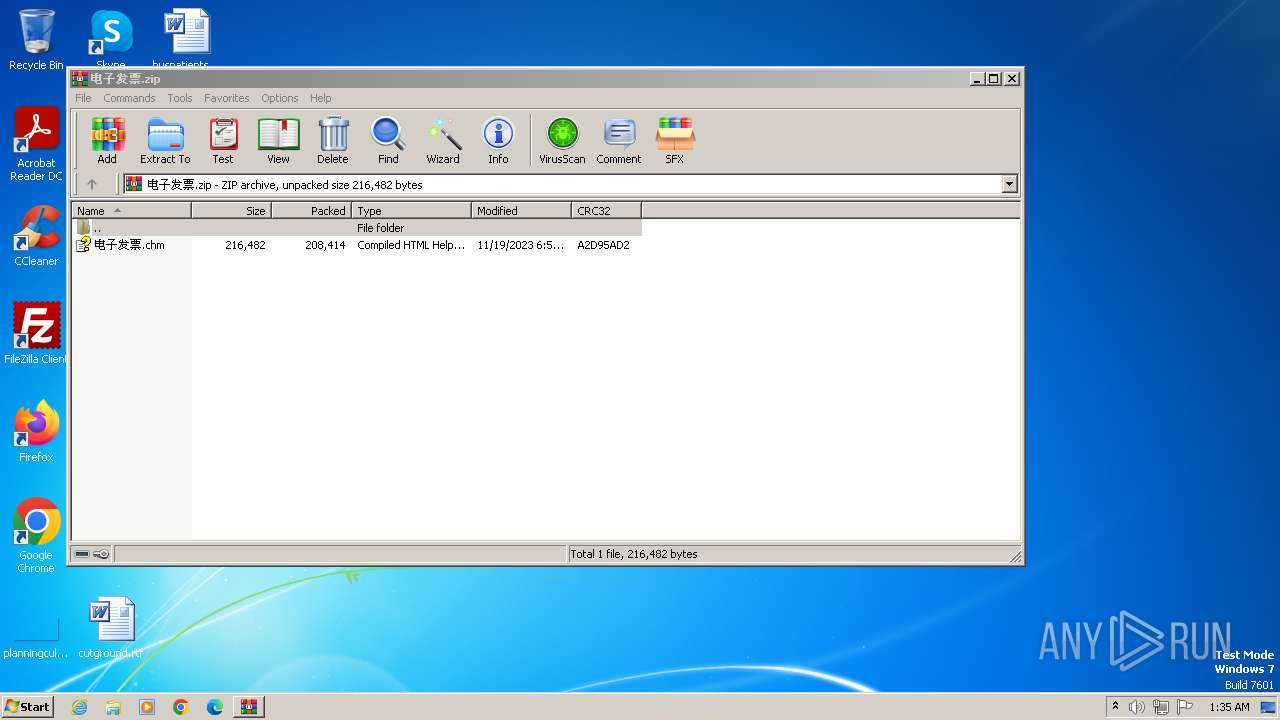
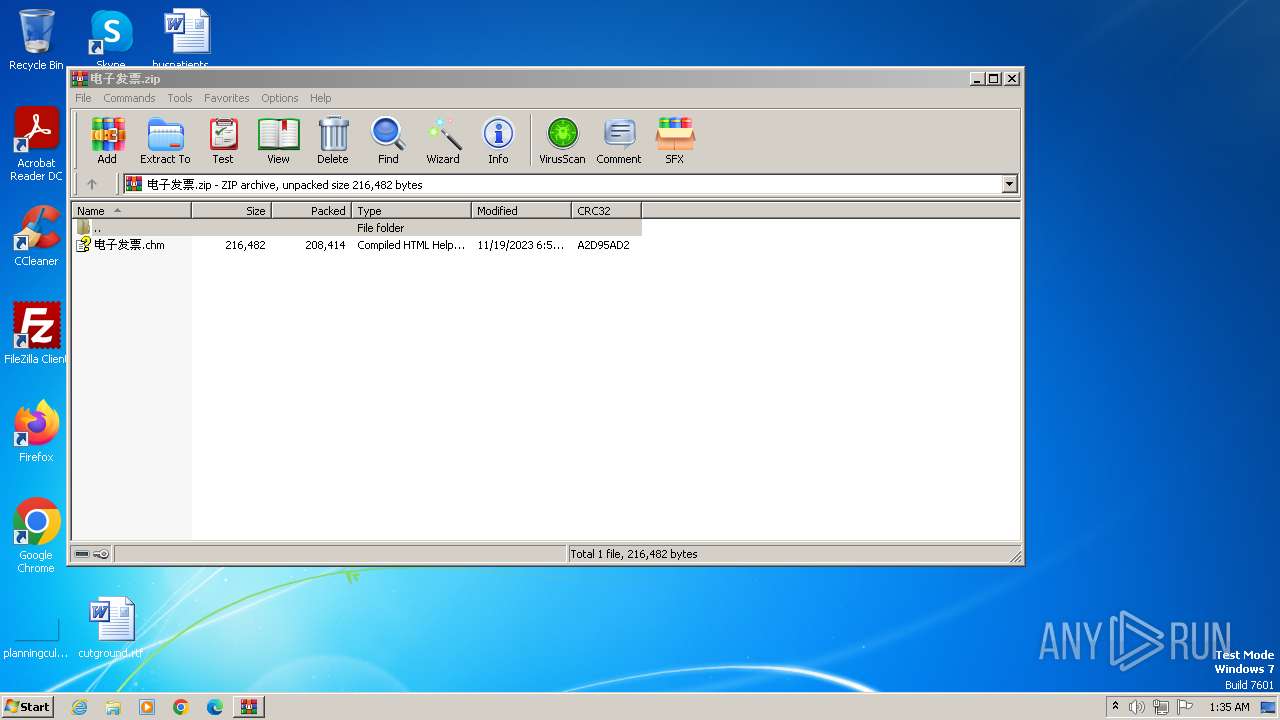
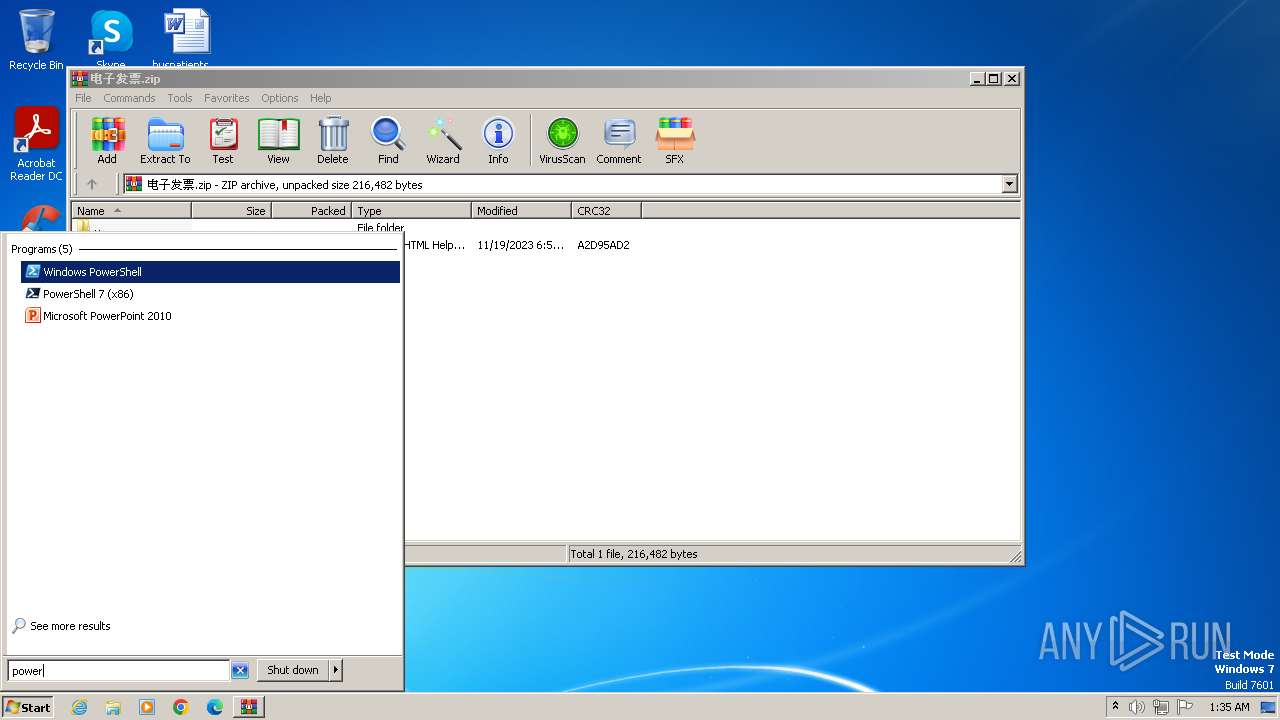
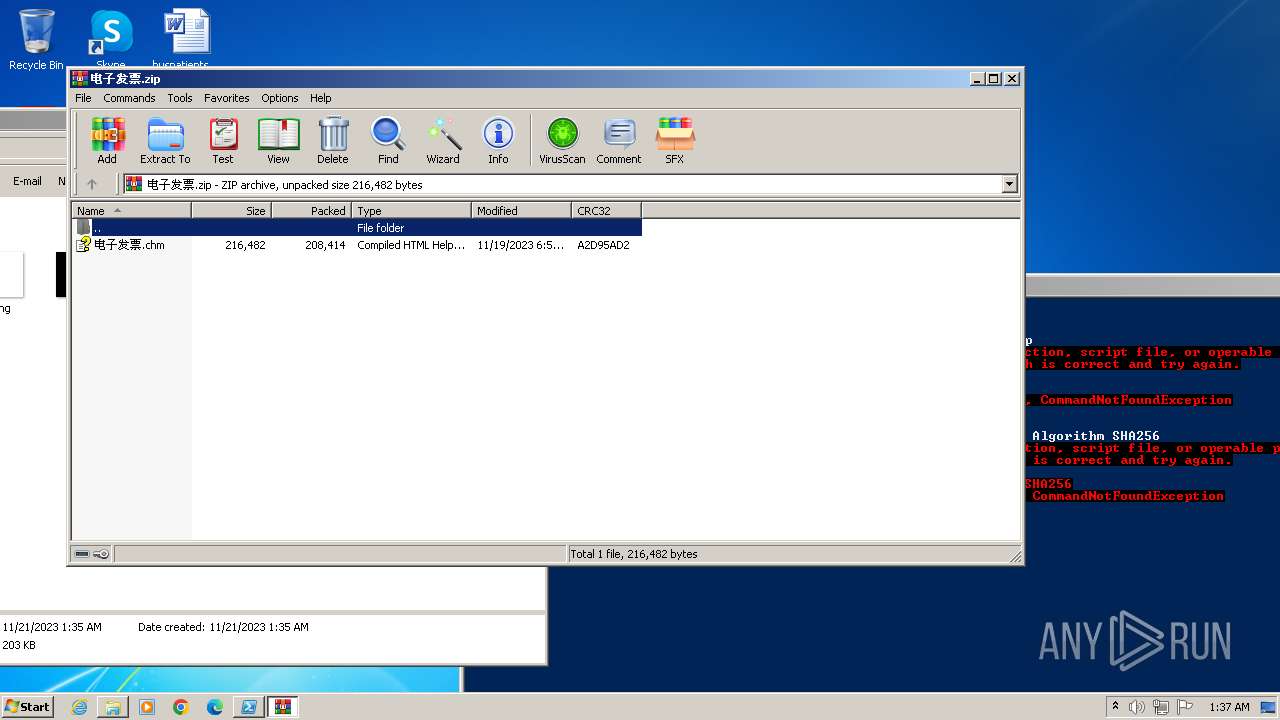
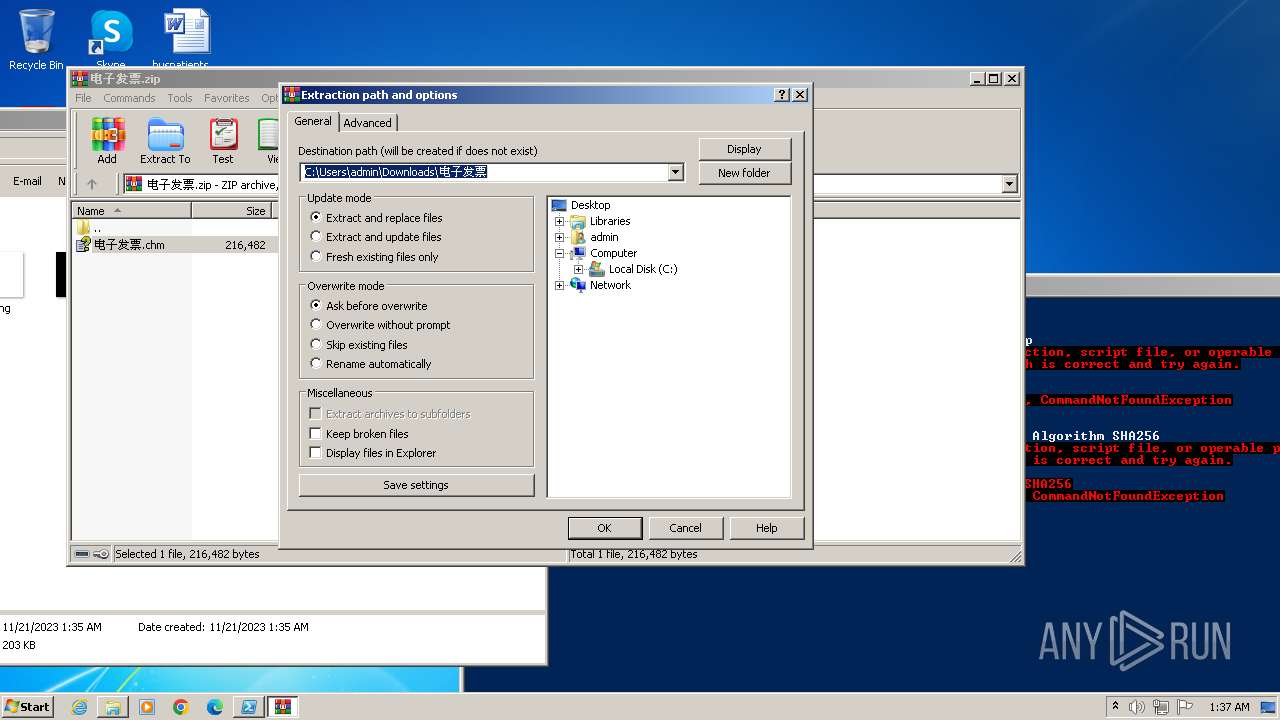
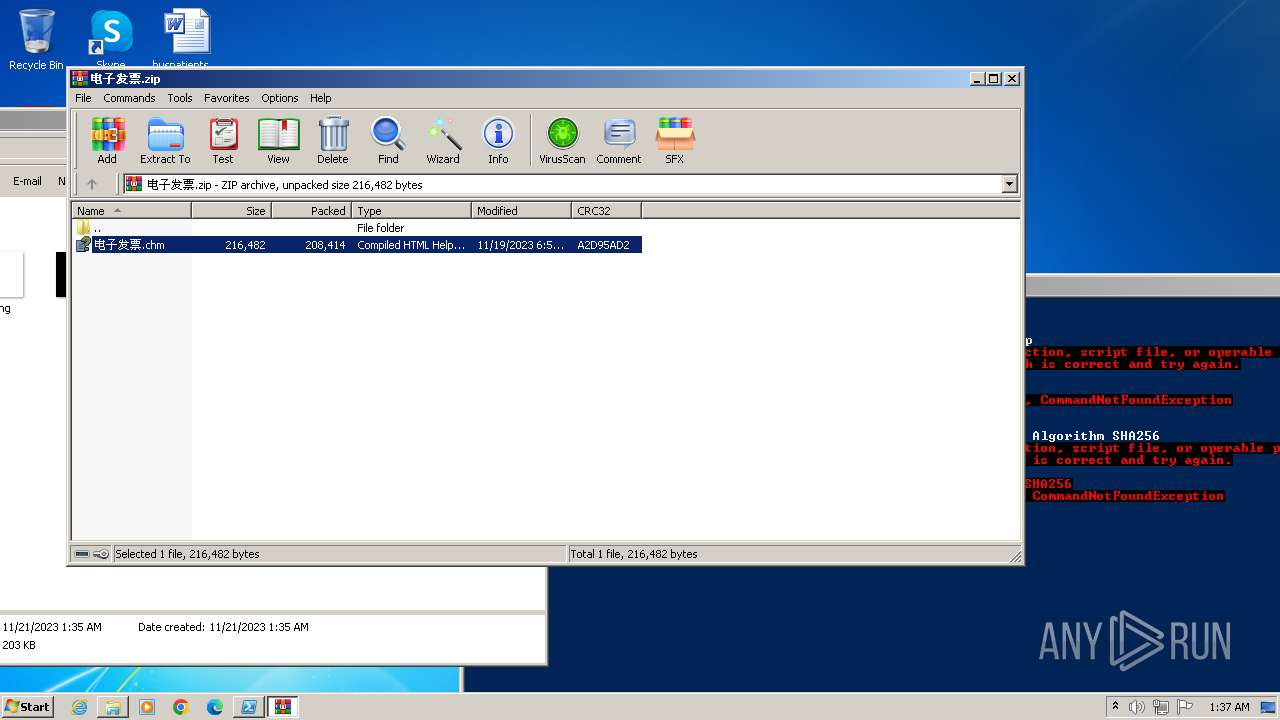
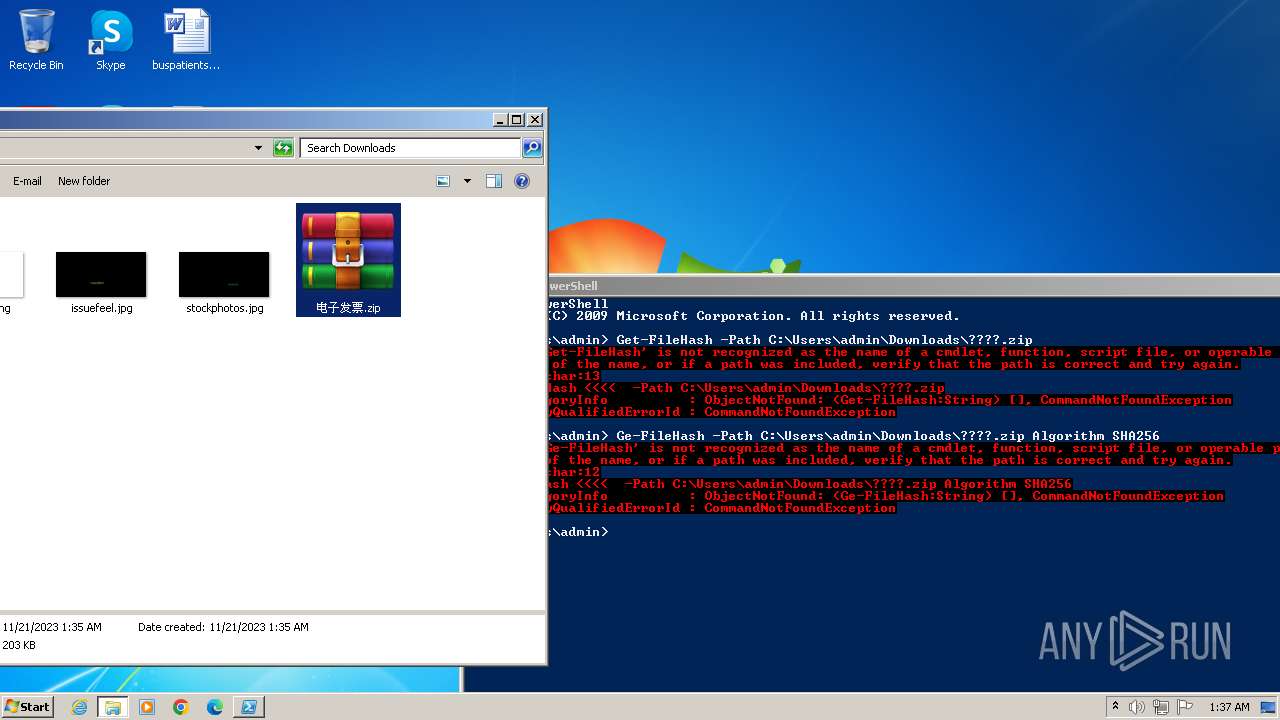
| 1028 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\电子发票.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1364 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\电子发票.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3300 --field-trial-handle=1152,i,9150392974675919024,10729428685890228018,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=3348 --field-trial-handle=1152,i,9150392974675919024,10729428685890228018,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\PowerShell\7\pwsh.exe" -WorkingDirectory ~ | C:\Program Files\powershell\7\pwsh.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: pwsh Exit code: 3221225786 Version: 7.2.11.500 Modules
| |||||||||||||||
| 2552 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://wx.mail.qq.com/ftn/download?func=3&key=cccf02395887f24dfebc4d3936363835dd1e603934363835161f1b4d52520a040b024e5d57555b185656075b19035d03031d5b5a020159535152515f50552835d4a4d6dc99a6ddbaa2d7c6911a4c514527597bec4baea8bc33304bc424f751d2d9a7780441&code=30c94685&k=cccf02395887f24dfebc4d3936363835dd1e603934363835161f1b4d52520a040b024e5d57555b185656075b19035d03031d5b5a020159535152515f50552835d4a4d6dc99a6ddbaa2d7c6911a4c514527597bec4baea8bc33304bc424f751d2d9a7780441&fweb=1&cl=1" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6dcf8b38,0x6dcf8b48,0x6dcf8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 3464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1284 --field-trial-handle=1152,i,9150392974675919024,10729428685890228018,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
9 430
Read events
9 232
Write events
195
Delete events
3
Modification events
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
0
Suspicious files
68
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF16739e.TMP | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:8268A4D53A6A9432A8266584CBD7D624 | SHA256:F785C42945CFE320C52C763837CD41541A8CAAB3E5FD567999EED5343CF0FD7A | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF167544.TMP | text | |
MD5:0917C6BFC618ACD47C1F53C7E7FFFF9C | SHA256:A5CAF56982DA7AE34B201E8609610786B4730371EF0812B7D418A2F9B73547BC | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65635E713D5CFC914717D1CC4CAC6989 | SHA256:4CB3EEB0369758290ABD7868DFD85D663C4AEF6C727FFF43BE693FDDBD0A6C28 | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF167e4d.TMP | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF167554.TMP | text | |
MD5:7C1C23F006788D107F8A01B852CC6701 | SHA256:9FA4E627077EDCBEC8AAA1ED2DD5538E630790893F88F02F1E9CC863E6A27848 | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF167573.TMP | text | |
MD5:56C75810BDDDD686D123E6E36F56E012 | SHA256:3D51A6EF85A51056E1A379D795F55C84A321EC2000DD69F5D70ABA038C61522E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
49
DNS requests
64
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3376 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3464 | chrome.exe | 142.250.185.109:443 | accounts.google.com | GOOGLE | US | unknown |
3464 | chrome.exe | 43.159.233.74:443 | wx.mail.qq.com | Tencent Building, Kejizhongyi Avenue | HK | unknown |
3464 | chrome.exe | 43.152.26.221:443 | res.wx.qq.com | ACE | DE | unknown |
3464 | chrome.exe | 203.205.137.181:443 | rescdn.qqmail.com | Tencent Building, Kejizhongyi Avenue | HK | unknown |
3464 | chrome.exe | 43.135.106.65:443 | open.mobile.qq.com | Tencent Building, Kejizhongyi Avenue | HK | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
wx.mail.qq.com |
| unknown |
rescdn.qqmail.com |
| whitelisted |
res.wx.qq.com |
| whitelisted |
open.mobile.qq.com |
| whitelisted |
open.weixin.qq.com |
| unknown |
graph.qq.com |
| whitelisted |
www.google.com |
| whitelisted |
imgcache.qq.com |
| whitelisted |
xui.ptlogin2.qq.com |
| malicious |
Threats
Process | Message |
|---|---|
pwsh.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 2312. Message ID: [0x2509].
|