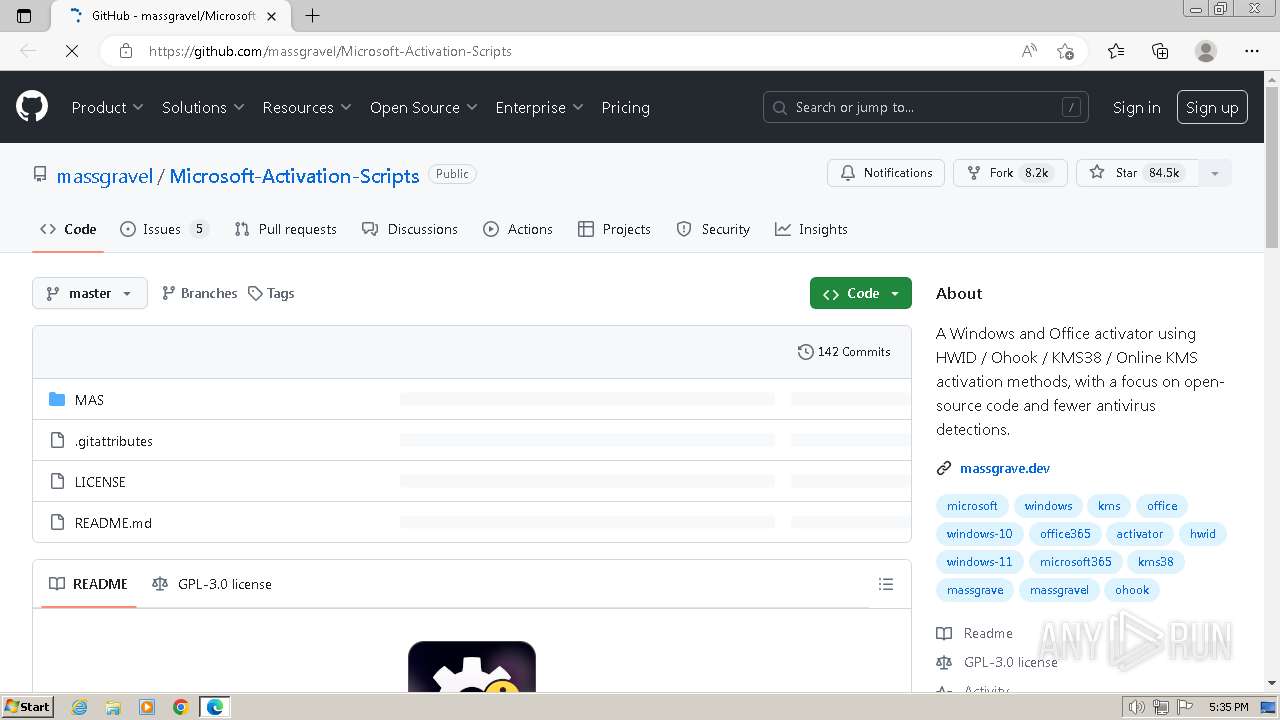
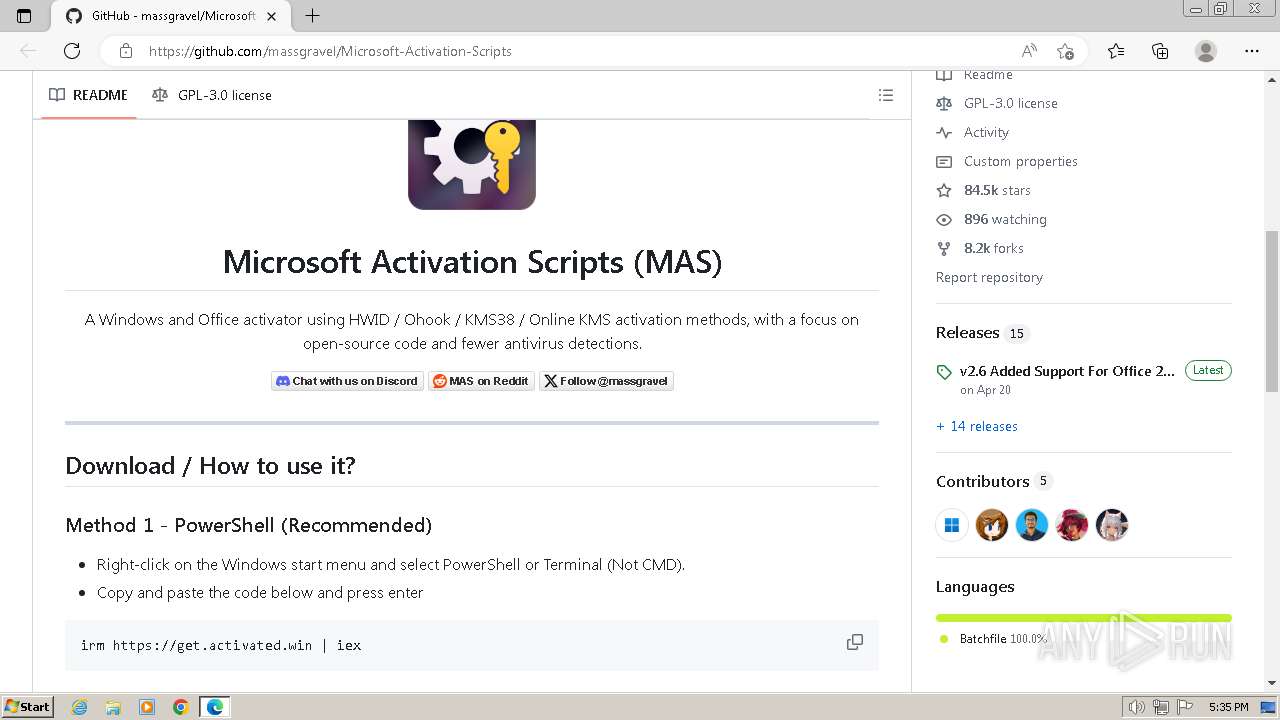
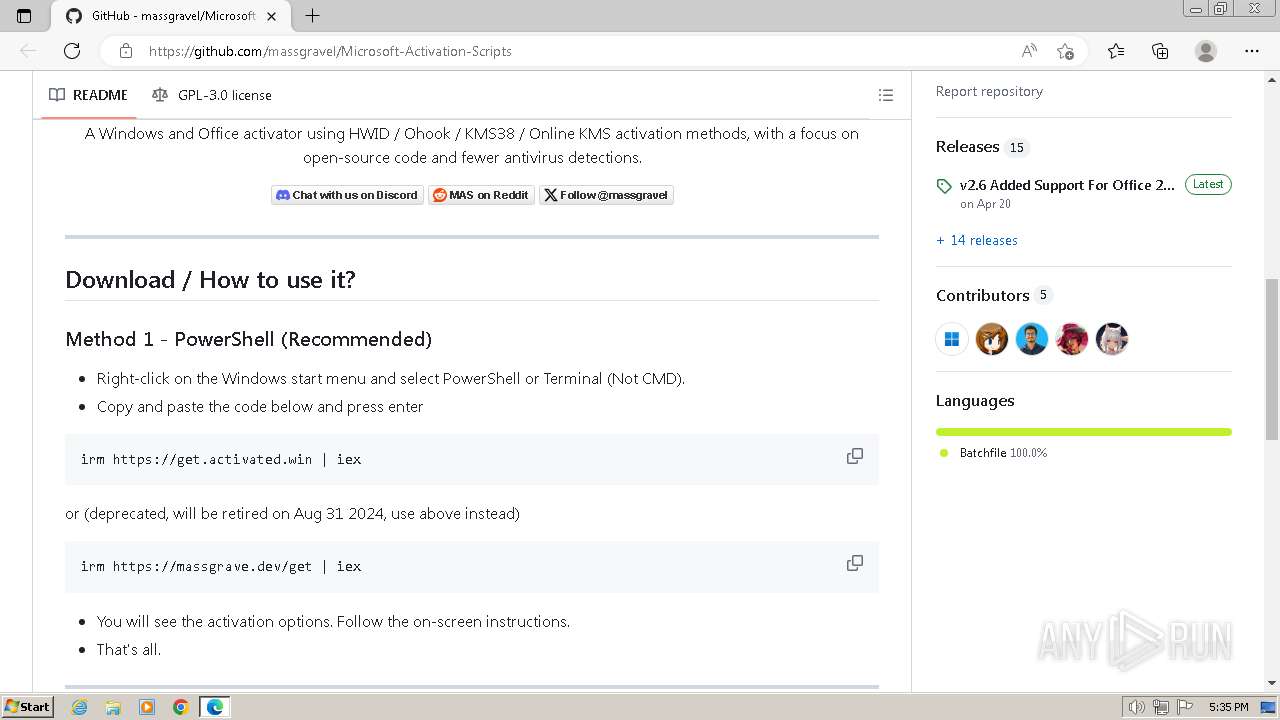
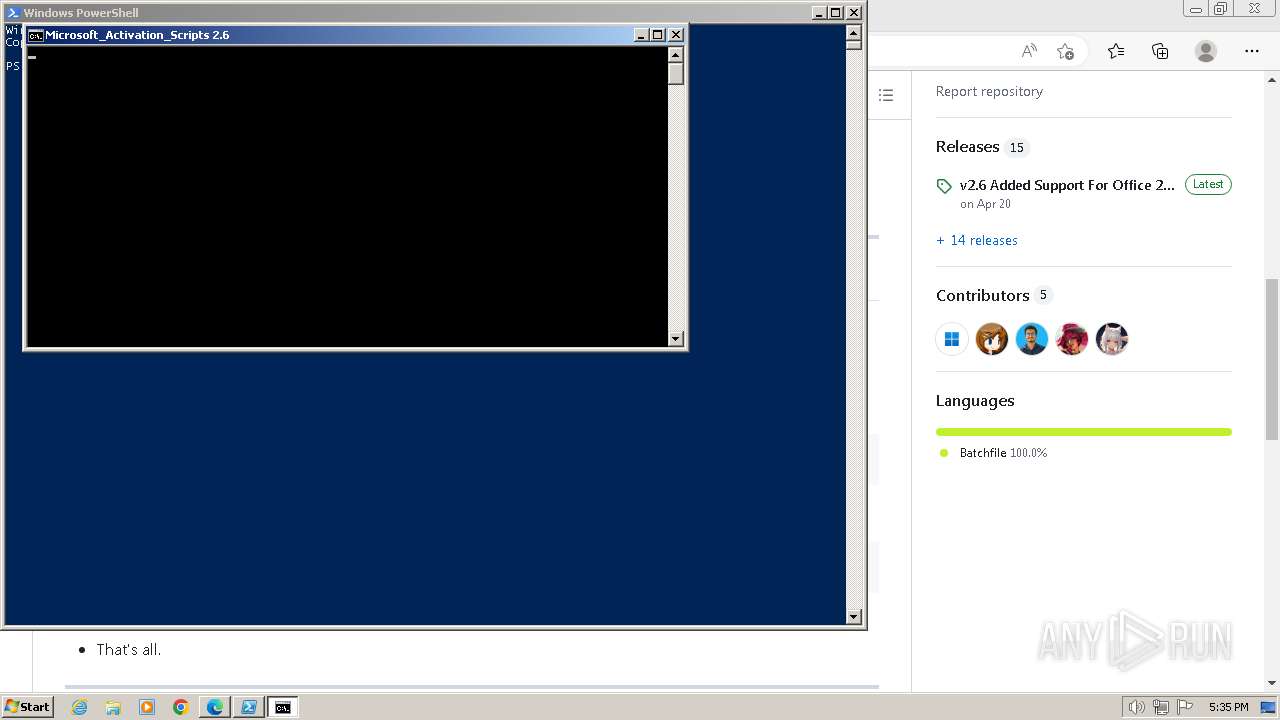
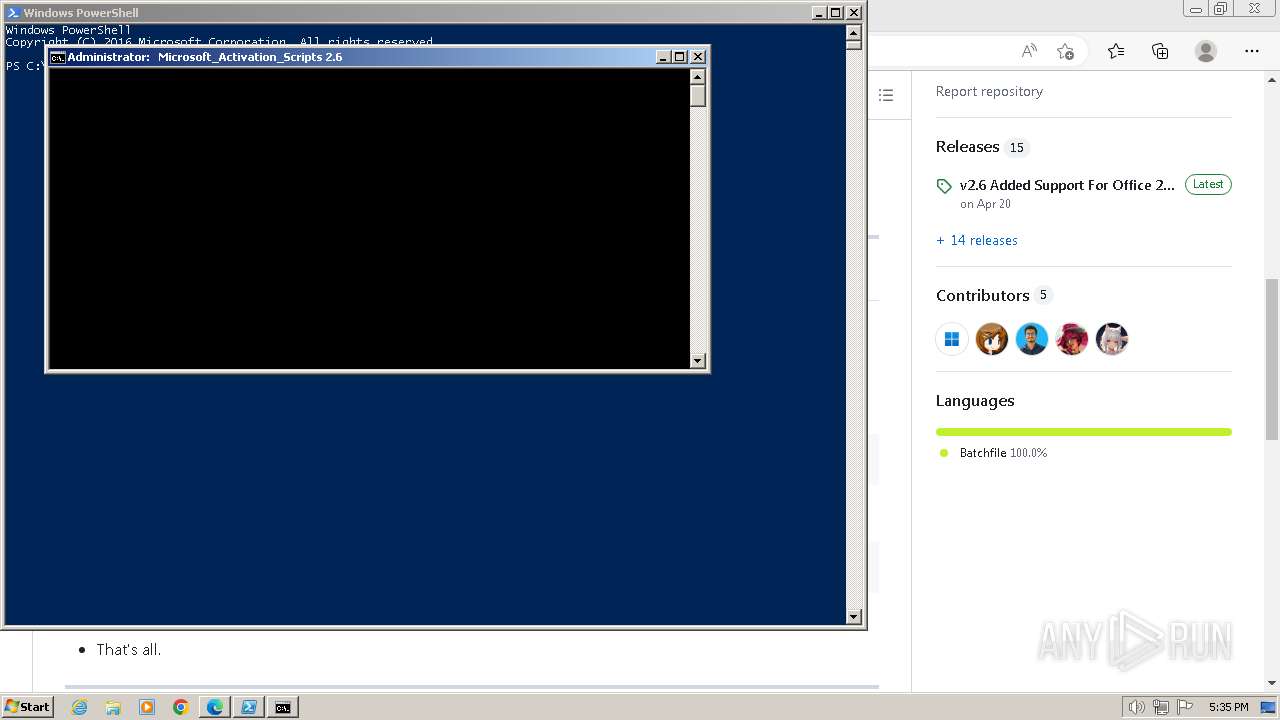
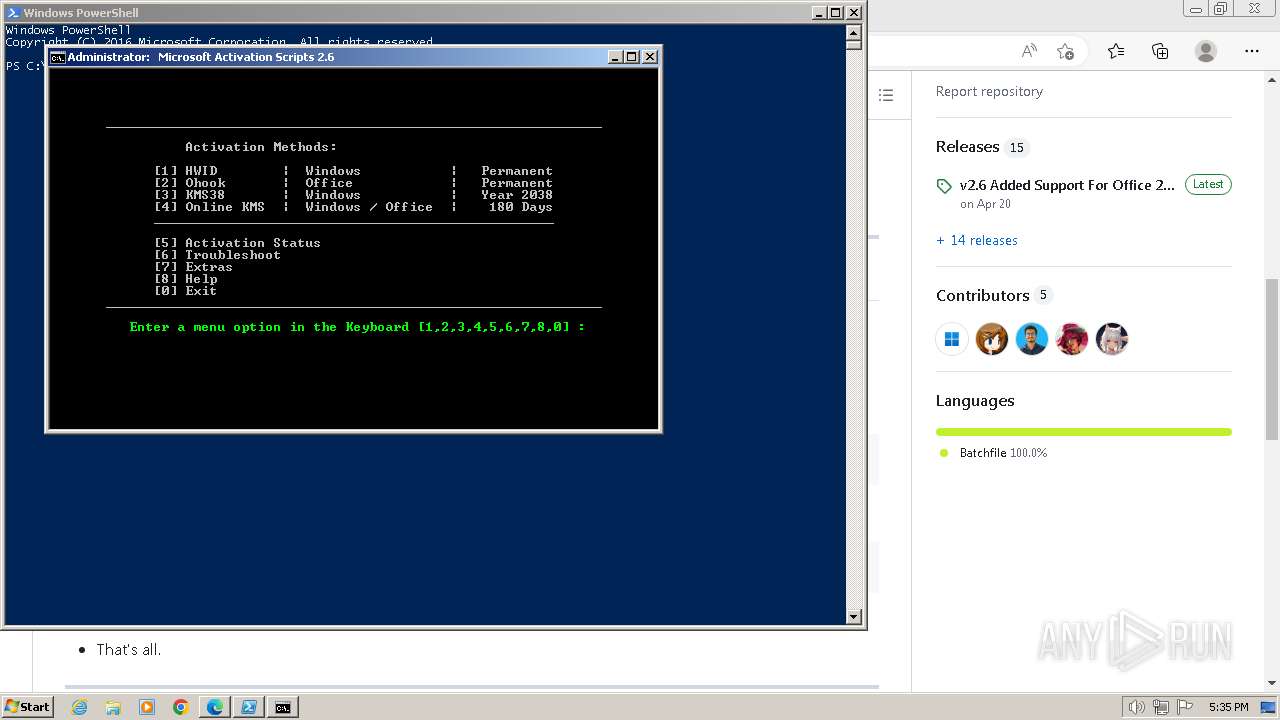
| URL: | https://github.com/massgravel/Microsoft-Activation-Scripts |
| Full analysis: | https://app.any.run/tasks/fb73ed88-7995-4cdf-98eb-3892c633869e |
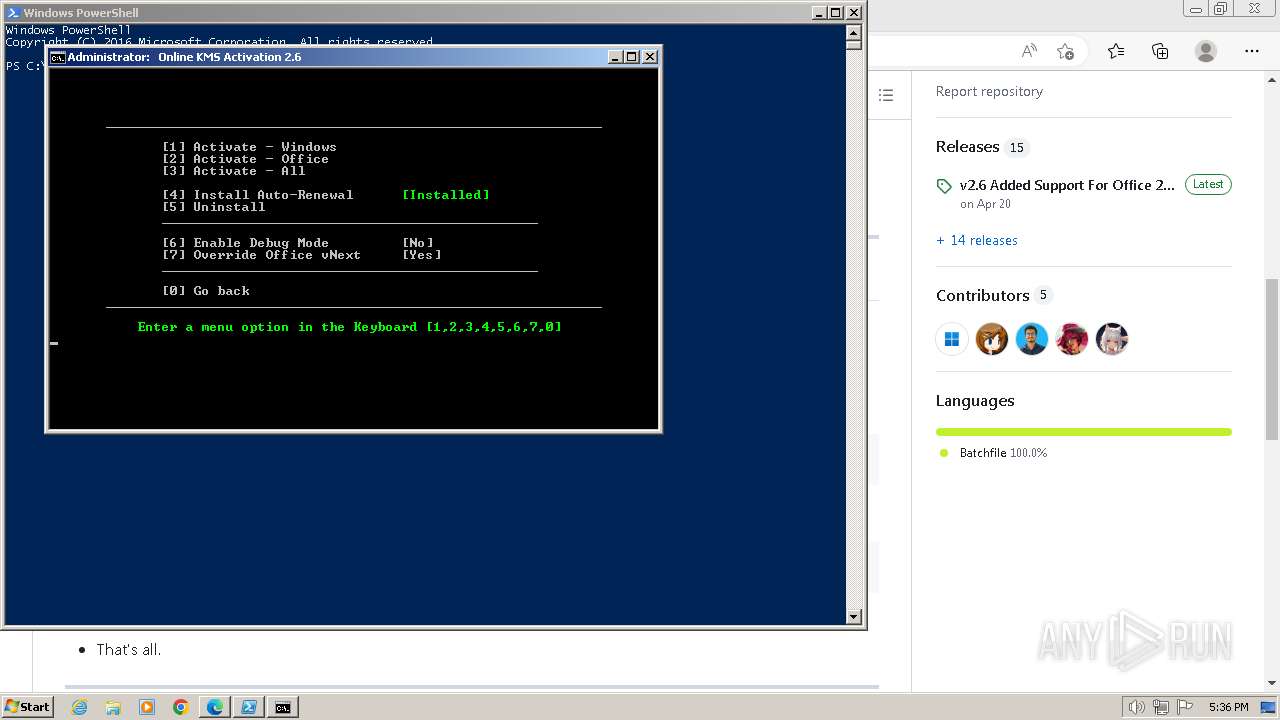
| Verdict: | Malicious activity |
| Analysis date: | June 29, 2024, 16:35:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AFD6FF84DA2D0BA12E52C775DF44B55B |
| SHA1: | 01C9074D7E2703A728921432F53128804DA08B5E |
| SHA256: | 9E176C48748F3D4D4303D5D603F477906CE34A381ACACC46ADB8DC346A2F00D9 |
| SSDEEP: | 3:N8tEd4PKoHXuukGR3RLLLGXUw:2uuPKzukGv/LGXUw |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 3784)
- net.exe (PID: 3704)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3784)
SUSPICIOUS
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1516)
Reads the Internet Settings
- powershell.exe (PID: 1516)
- powershell.exe (PID: 1156)
- WMIC.exe (PID: 328)
- WMIC.exe (PID: 2704)
- WMIC.exe (PID: 1832)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 1516)
- cmd.exe (PID: 3408)
- powershell.exe (PID: 1156)
- cmd.exe (PID: 3784)
Executing commands from ".cmd" file
- powershell.exe (PID: 1516)
- cmd.exe (PID: 3408)
- powershell.exe (PID: 1156)
- cmd.exe (PID: 3784)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3408)
- cmd.exe (PID: 3784)
Starts SC.EXE for service management
- cmd.exe (PID: 3408)
- cmd.exe (PID: 3784)
Application launched itself
- cmd.exe (PID: 3408)
- cmd.exe (PID: 3784)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3408)
- cmd.exe (PID: 3784)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3784)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 3784)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 3784)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 660)
- powershell.exe (PID: 3980)
Starts NET.EXE to map network drives
- cmd.exe (PID: 3784)
Hides command output
- cmd.exe (PID: 3644)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 3844)
- cmd.exe (PID: 1620)
- cmd.exe (PID: 3868)
- cmd.exe (PID: 240)
- cmd.exe (PID: 1800)
- cmd.exe (PID: 4004)
- cmd.exe (PID: 748)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 3980)
- powershell.exe (PID: 660)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3980)
- powershell.exe (PID: 660)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 3784)
INFO
Application launched itself
- msedge.exe (PID: 3384)
Disables trace logs
- powershell.exe (PID: 1516)
Checks current location (POWERSHELL)
- powershell.exe (PID: 1516)
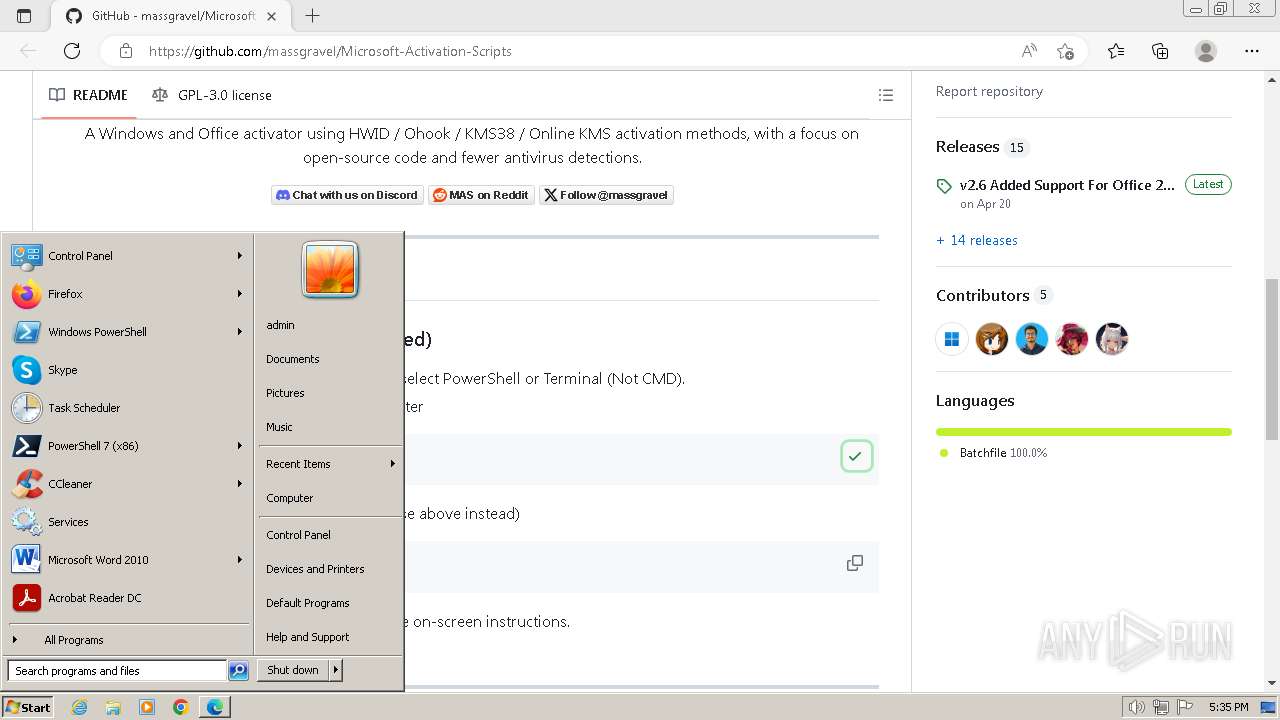
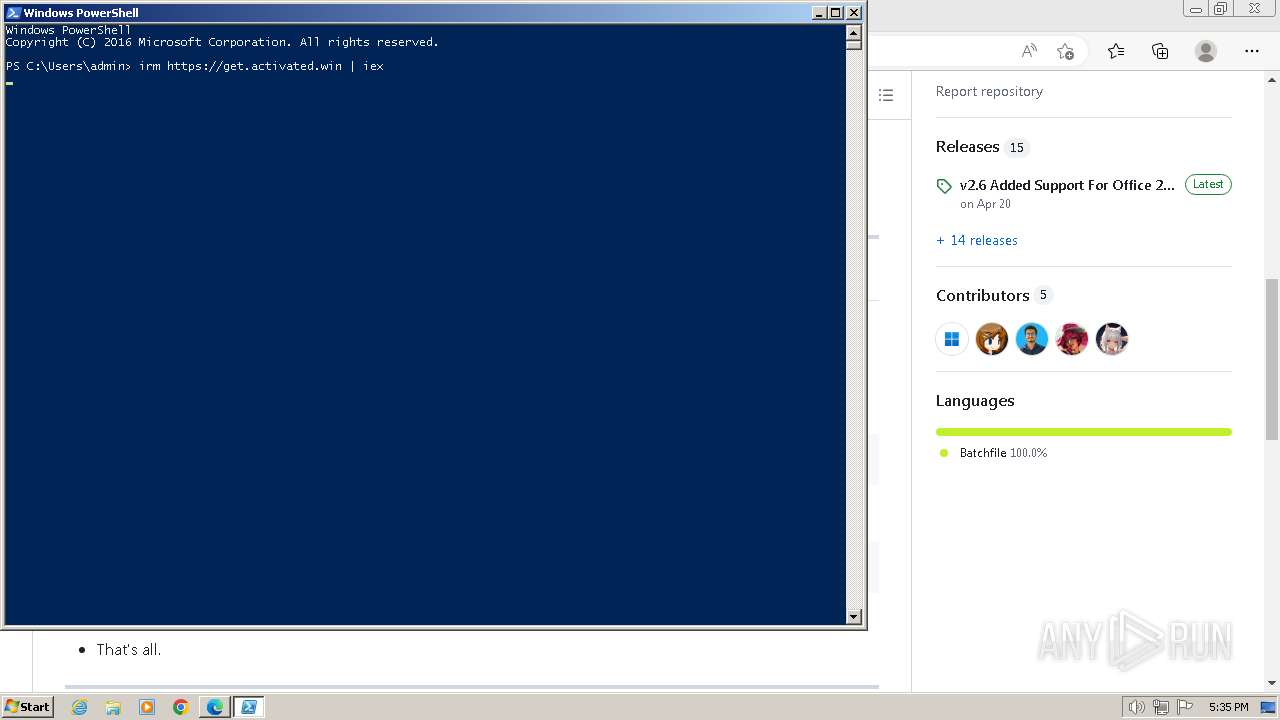
Manual execution by a user
- powershell.exe (PID: 1516)
Checks operating system version
- cmd.exe (PID: 3408)
- cmd.exe (PID: 3784)
Checks supported languages
- mode.com (PID: 2272)
- mode.com (PID: 3496)
- mode.com (PID: 1756)
- mode.com (PID: 1000)
- mode.com (PID: 3184)
- mode.com (PID: 3808)
- mode.com (PID: 3624)
Creates files in the program directory
- cmd.exe (PID: 3784)
- powershell.exe (PID: 660)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 660)
- powershell.exe (PID: 3980)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 660)
- powershell.exe (PID: 3980)
Reads Microsoft Office registry keys
- reg.exe (PID: 3084)
- reg.exe (PID: 2432)
- reg.exe (PID: 764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
232
Monitored processes
188
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | C:\Windows\system32\cmd.exe /c "reg query HKLM\SOFTWARE\Microsoft\Office\15.0\Common\InstallRoot /v Path" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 328 | wmic path Win32_ComputerSystem get CreationClassName /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 348 | find /i "0x1" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 400 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1640 --field-trial-handle=1352,i,18173783076569010564,12989508338452668802,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 444 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 444 | C:\Windows\system32\cmd.exe /c reg query "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /v Desktop | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 448 | findstr /a:07 /f:`.txt "." | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v DisableDnsPublishing | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 540 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1560 --field-trial-handle=1352,i,18173783076569010564,12989508338452668802,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 660 | powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_62835071.cmd') -split \":_extracttask\:.*`r`n\"; [io.file]::WriteAllText('C:\Program Files\Activation-Renewal\Activation_task.cmd', '@REM Dummy ' + '12252' + [Environment]::NewLine + $f[1].Trim(), [System.Text.Encoding]::ASCII);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
43 227
Read events
43 084
Write events
129
Delete events
14
Modification events
| (PID) Process: | (3384) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3384) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3384) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3384) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3384) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3384) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3384) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3384) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 9454D73BA07A2F00 | |||
| (PID) Process: | (3384) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3384) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
0
Suspicious files
169
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF4e1b1.TMP | — | |
MD5:— | SHA256:— | |||
| 3384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4e1f0.TMP | — | |
MD5:— | SHA256:— | |||
| 3384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF4e22e.TMP | — | |
MD5:— | SHA256:— | |||
| 3384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF4e2fa.TMP | text | |
MD5:00AA7B4B4257D481C40A58482D5D6B24 | SHA256:65A7BF11BD80C6FE73C58A20E4BB0F8FA653EEB70B707DA7D16DD9E7F954CA21 | |||
| 3384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:4B74C392839DDD59792975091A30DB00 | SHA256:7A5A3B8CC4D5BB579FA5E6C6A831964FB245A5CFF9AD3B80F5E9DC34DA4A7D53 | |||
| 3384 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF4e1b1.TMP | text | |
MD5:4BDB64FCF217848BCEEF4FF1723E32A0 | SHA256:6DB71689542AA54221535B9135FD82321DFE987612818B1D3BBA1629C4DC2F63 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
40
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | US | — | — | unknown |
1060 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?11acddbe1ebd82b3 | US | — | — | unknown |
1372 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | unknown |
1372 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | unknown |
1516 | powershell.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0cba2a1b29c00512 | US | compressed | 70.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
540 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3384 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
540 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
540 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
540 | msedge.exe | 185.199.110.154:443 | github.githubassets.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
camo.githubusercontent.com |
| shared |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
www.bing.com |
| whitelisted |
collector.github.com |
| whitelisted |