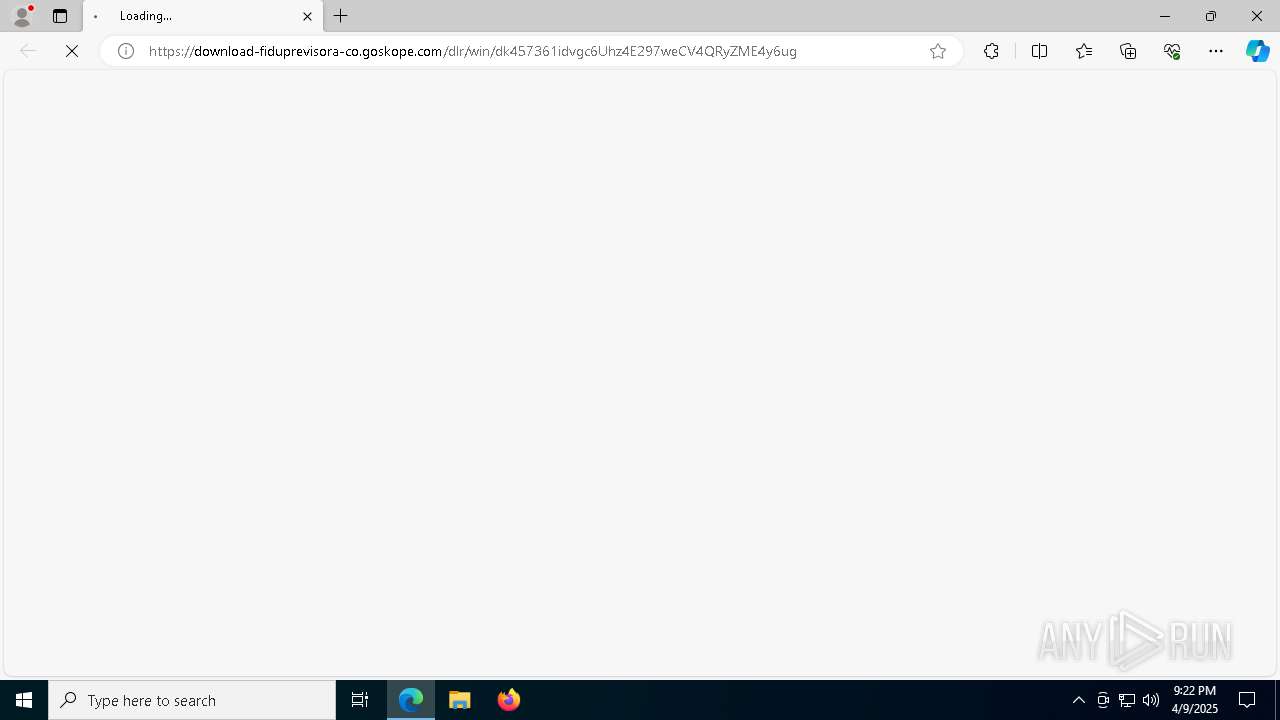
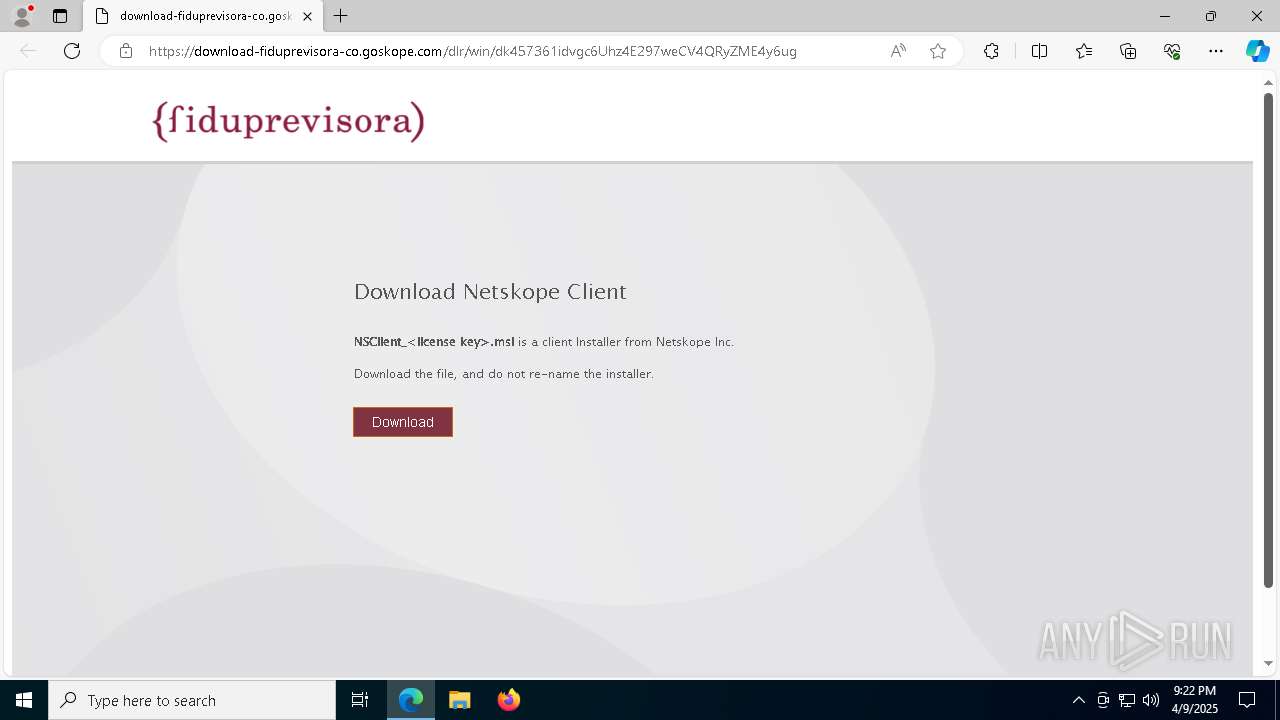
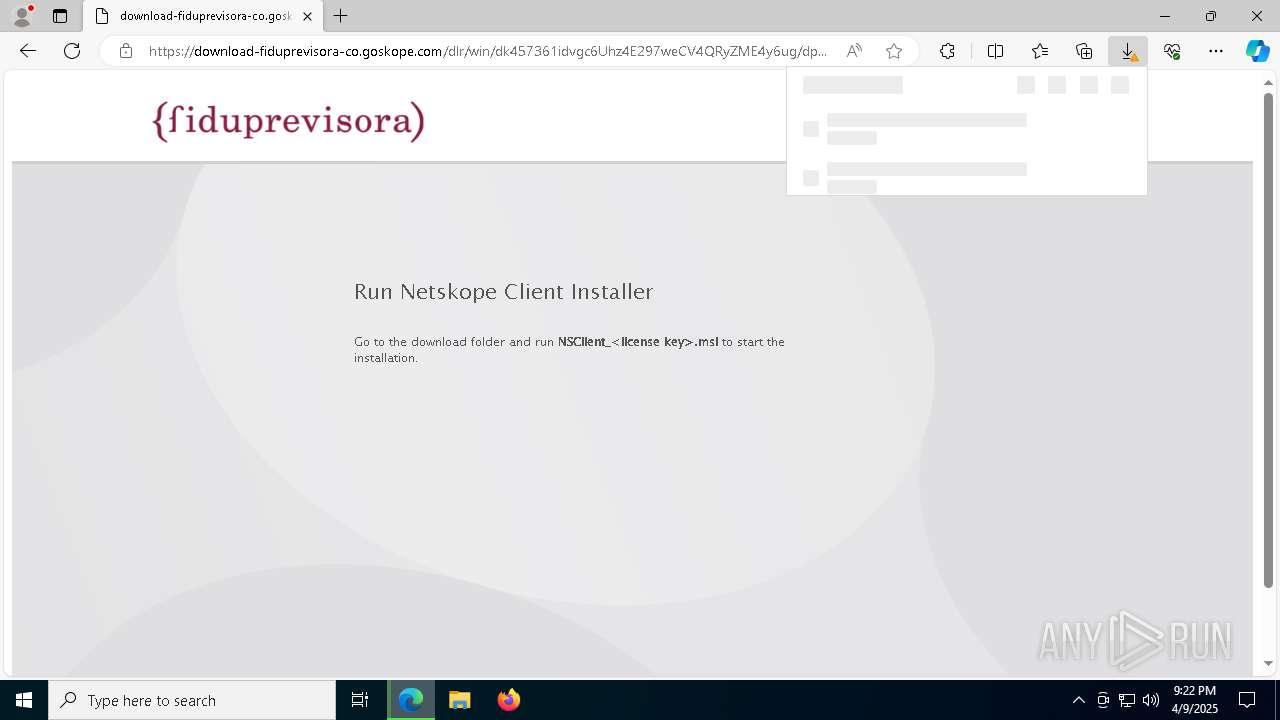
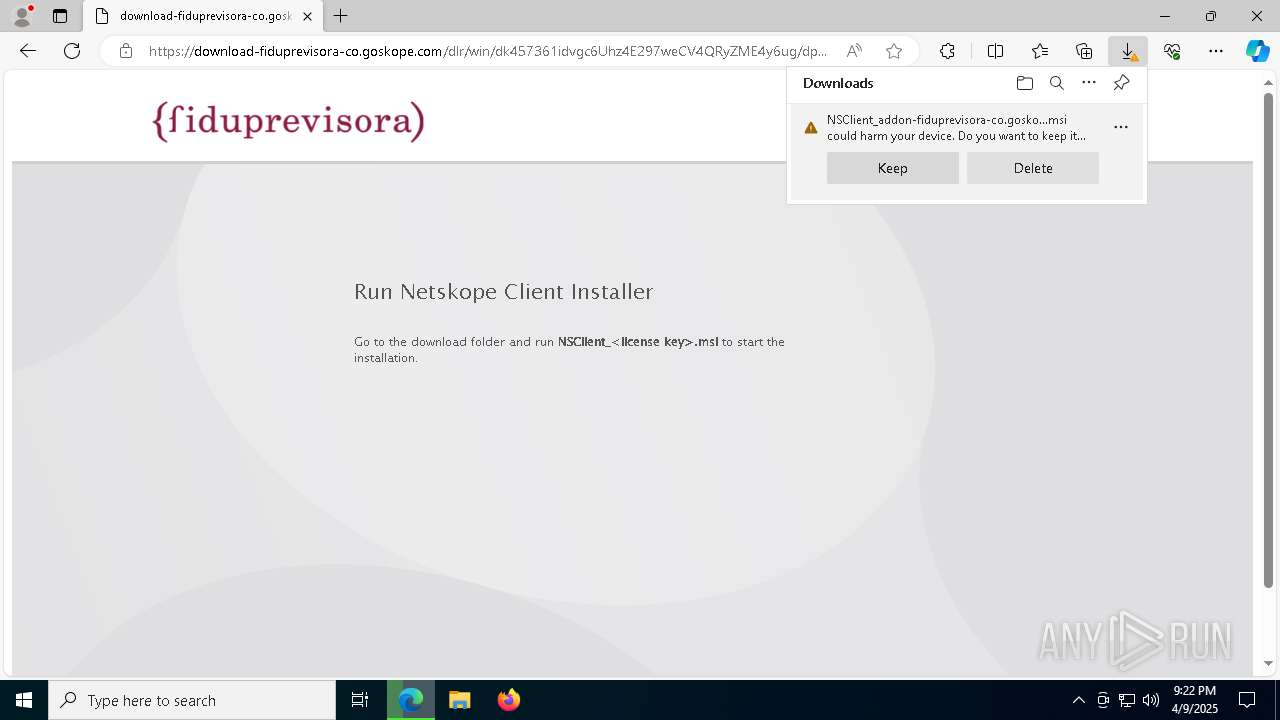
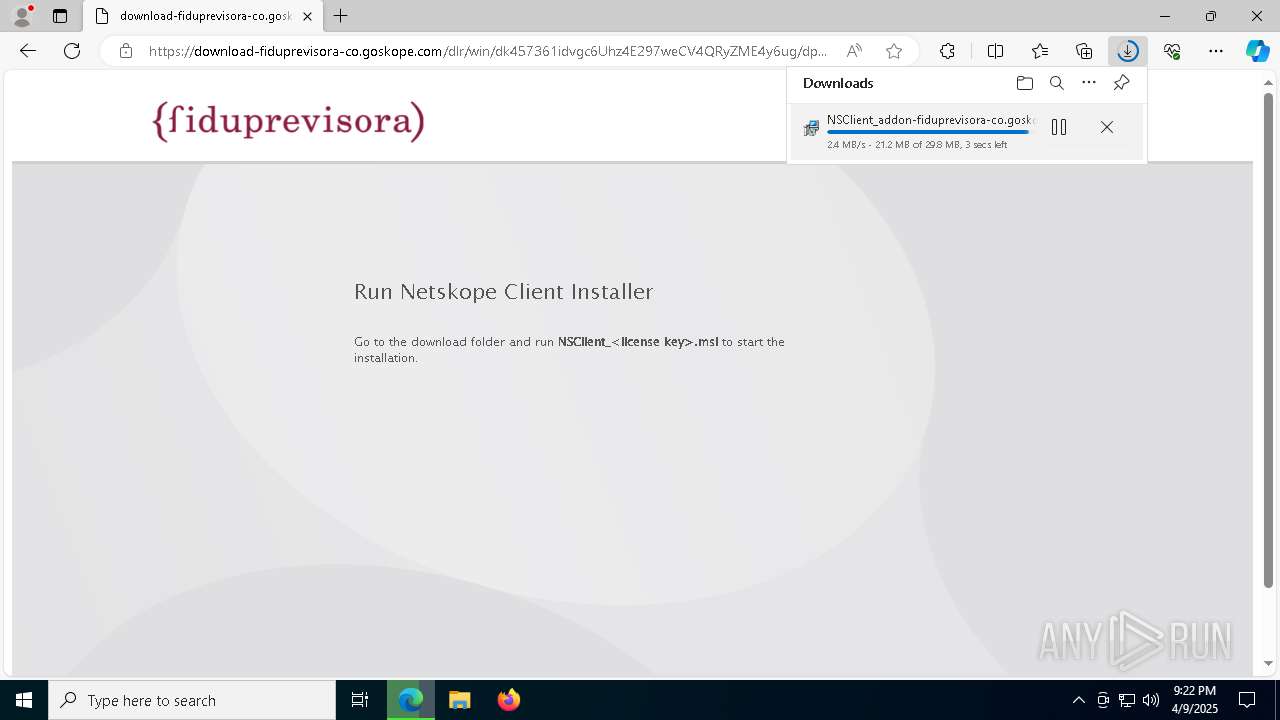
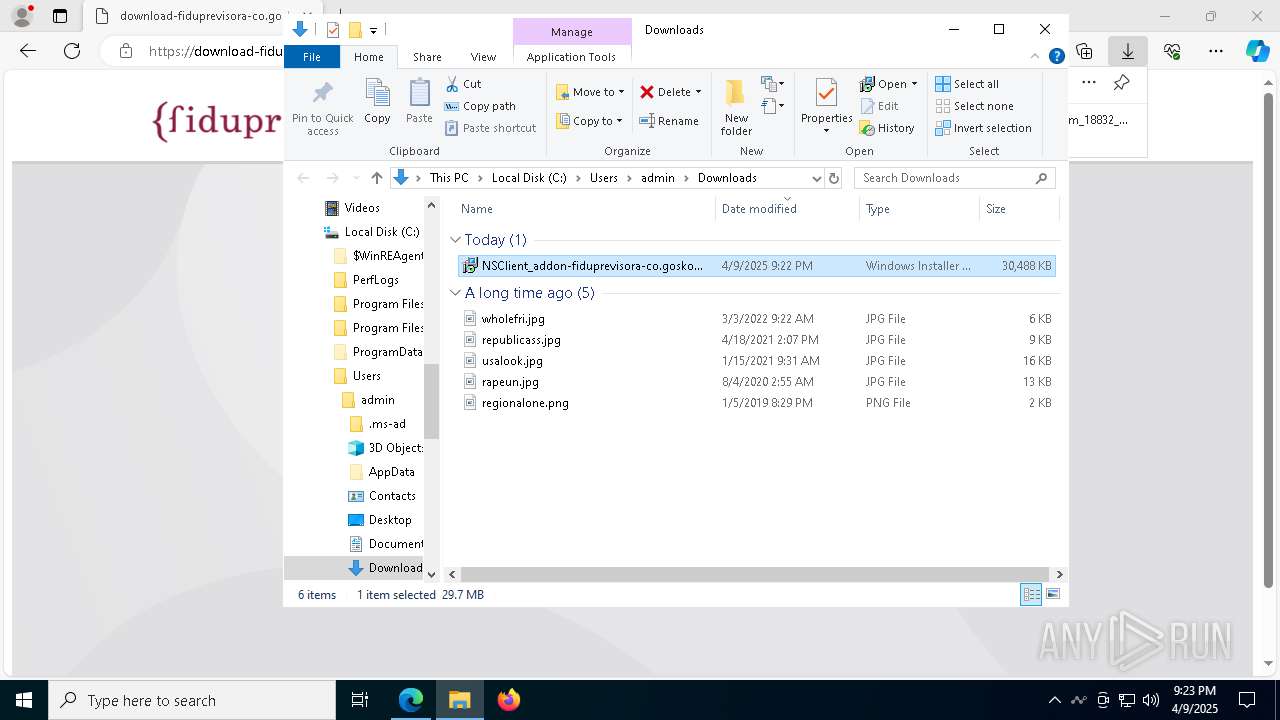
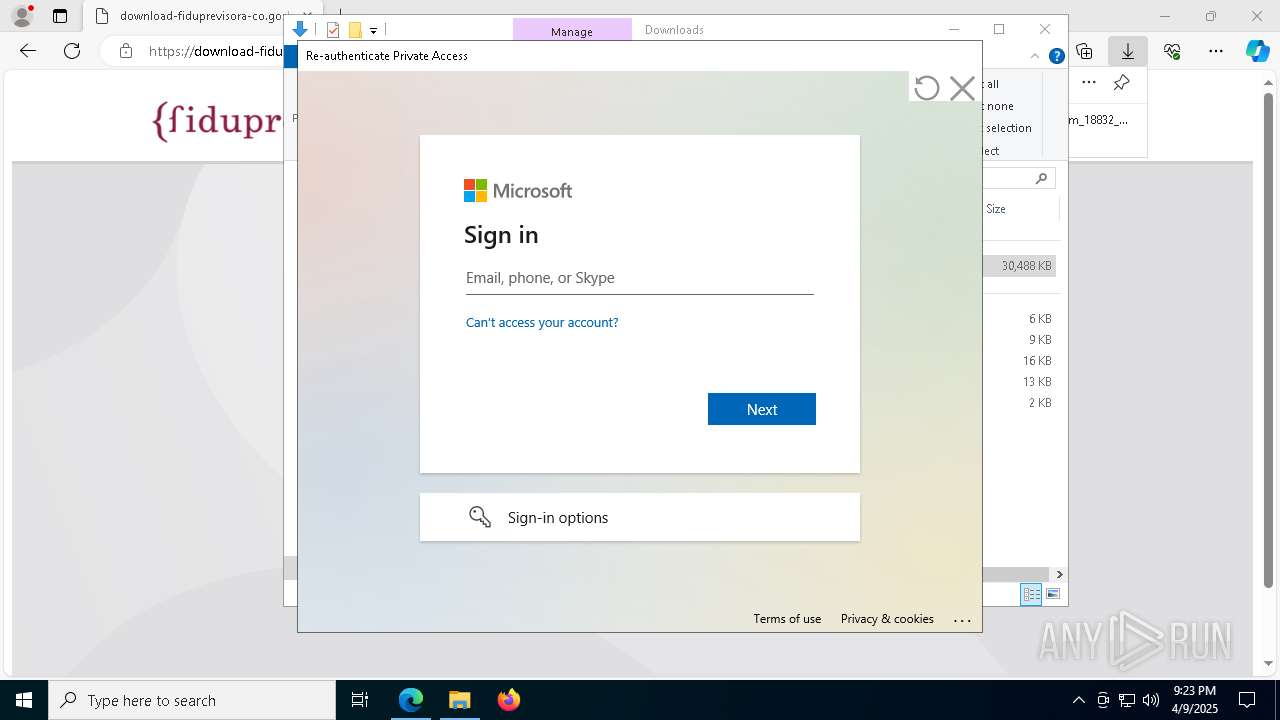
| URL: | https://download-fiduprevisora-co.goskope.com/dlr/win/dk457361idvgc6Uhz4E297weCV4QRyZME4y6ug |
| Full analysis: | https://app.any.run/tasks/e05bdd43-a6fd-46db-ac69-2fc0c8c55a9a |
| Verdict: | Malicious activity |
| Analysis date: | April 09, 2025, 21:22:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2FBA78DD7A0F63551F09981BF0236C9A |
| SHA1: | 19BBB7E14034135769922843A8AAC0086DFB35DD |
| SHA256: | 9E0874A9F6CD22261C14F8D473A491F5063BA302362D6BC3C03E6DEAC4083132 |
| SSDEEP: | 3:N8SEmDfbNXhdLCK8JGBJyLavleG8DScW5sLu:2Stp+RkvL0AEu |
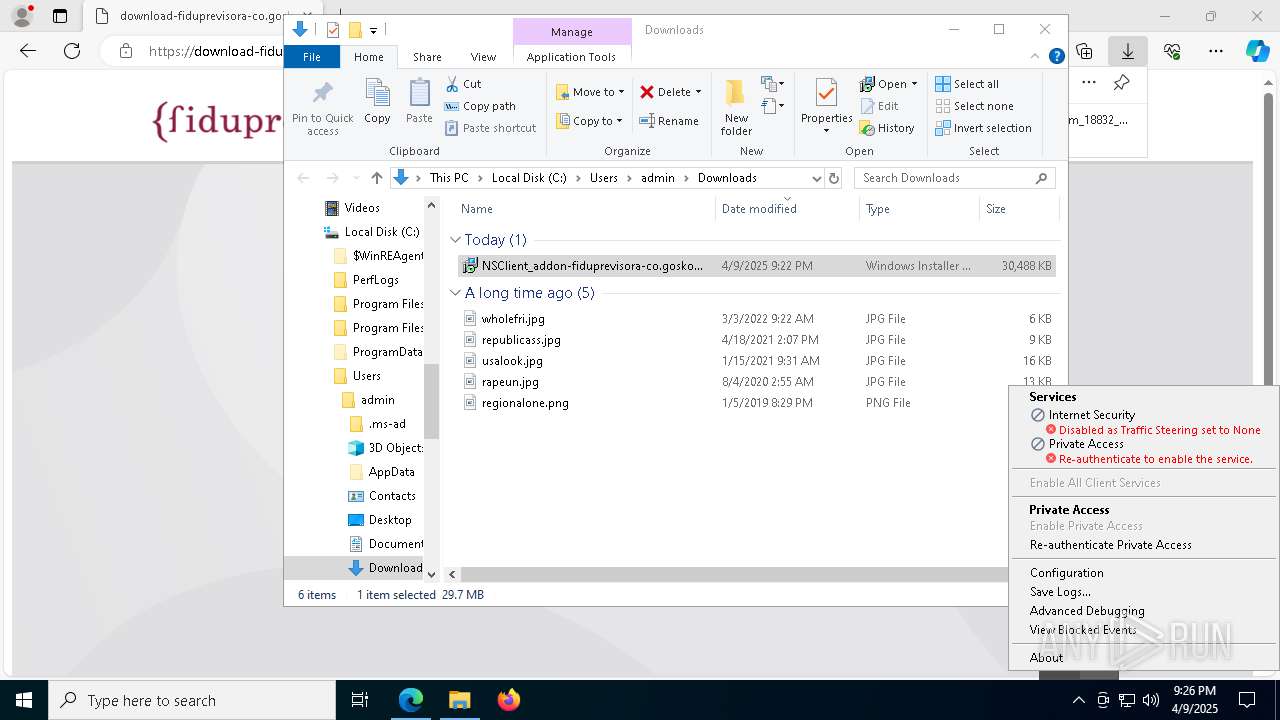
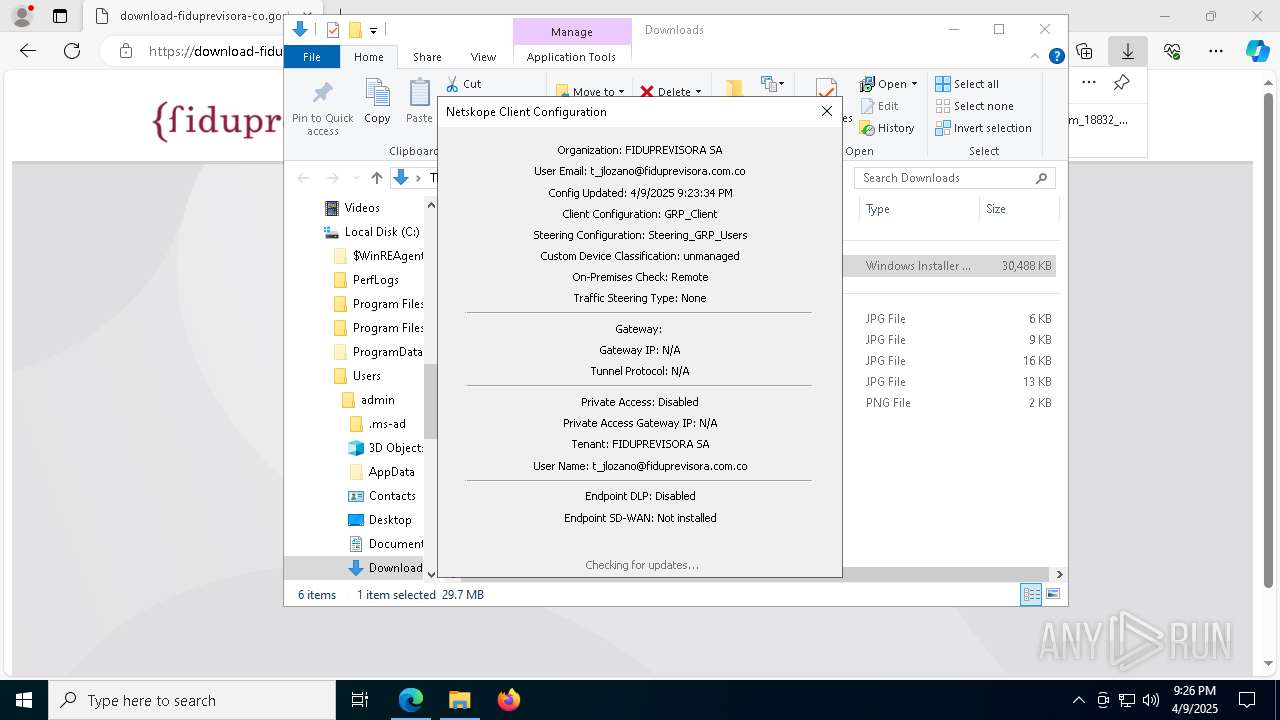
MALICIOUS
Changes the autorun value in the registry
- msiexec.exe (PID: 5608)
SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 5492)
Executes as Windows Service
- VSSVC.exe (PID: 208)
- stAgentSvc.exe (PID: 3032)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5608)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 5608)
- msiexec.exe (PID: 7824)
The process creates files with name similar to system file names
- msiexec.exe (PID: 5608)
- msiexec.exe (PID: 7824)
The process drops C-runtime libraries
- msiexec.exe (PID: 5608)
- msiexec.exe (PID: 7824)
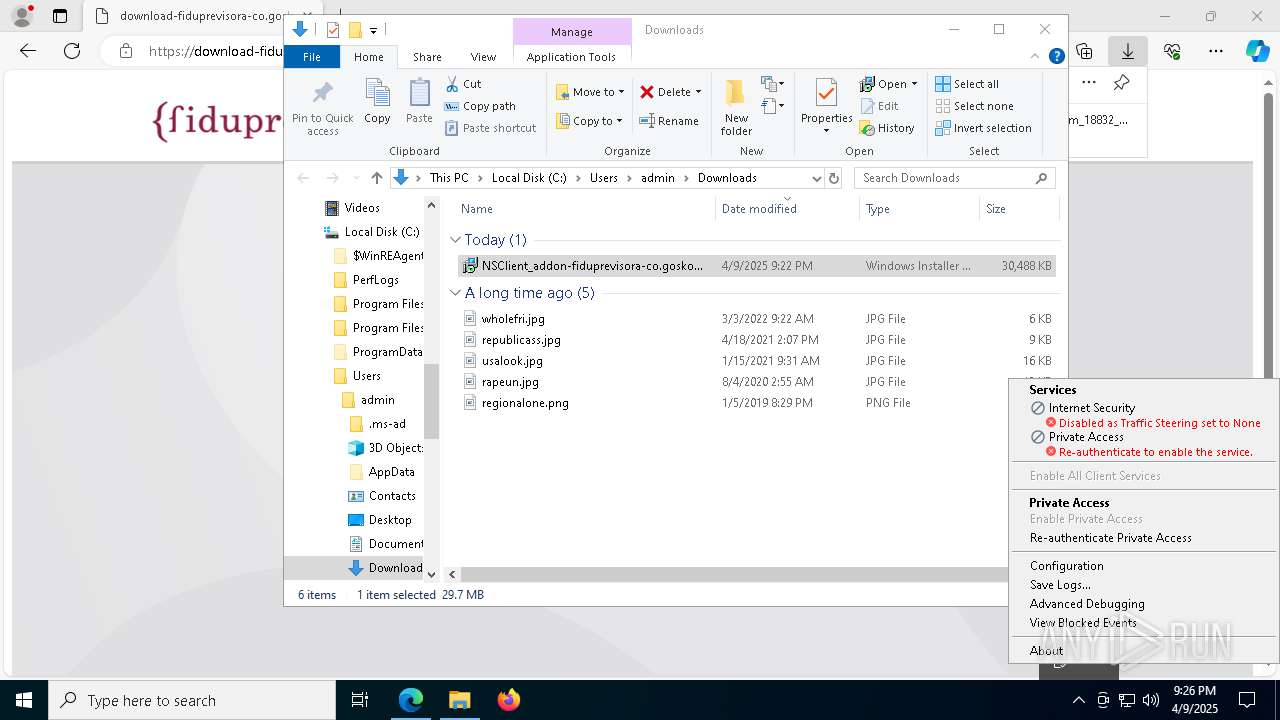
Uses NETSH.EXE to trace traffic
- stAgentSvc.exe (PID: 3032)
Process drops legitimate windows executable
- msiexec.exe (PID: 5608)
- msiexec.exe (PID: 7824)
The process verifies whether the antivirus software is installed
- stAgentSvc.exe (PID: 3032)
Reads Microsoft Outlook installation path
- stAgentUI.exe (PID: 7820)
Reads Internet Explorer settings
- stAgentUI.exe (PID: 7820)
Connects to unusual port
- stAgentSvc.exe (PID: 3032)
Process uses IPCONFIG to clear DNS cache
- stAgentSvc.exe (PID: 3032)
Reads security settings of Internet Explorer
- stAgentUI.exe (PID: 7820)
Adds/modifies Windows certificates
- stAgentSvc.exe (PID: 3032)
INFO
Checks supported languages
- identity_helper.exe (PID: 4688)
- msiexec.exe (PID: 5608)
- msiexec.exe (PID: 660)
- msiexec.exe (PID: 4608)
- msiexec.exe (PID: 6132)
- msiexec.exe (PID: 7824)
- msiexec.exe (PID: 4572)
- stAgentSvc.exe (PID: 3032)
- stAgentUI.exe (PID: 7820)
- stAgentUI.exe (PID: 7892)
- keytool.exe (PID: 7808)
- keytool.exe (PID: 2284)
- keytool.exe (PID: 6004)
- keytool.exe (PID: 4016)
- keytool.exe (PID: 5416)
- keytool.exe (PID: 3180)
Creates files or folders in the user directory
- explorer.exe (PID: 5492)
- msiexec.exe (PID: 660)
- stAgentUI.exe (PID: 7820)
Reads Environment values
- identity_helper.exe (PID: 4688)
- msiexec.exe (PID: 4608)
- stAgentSvc.exe (PID: 3032)
- stAgentUI.exe (PID: 7820)
- msiexec.exe (PID: 4572)
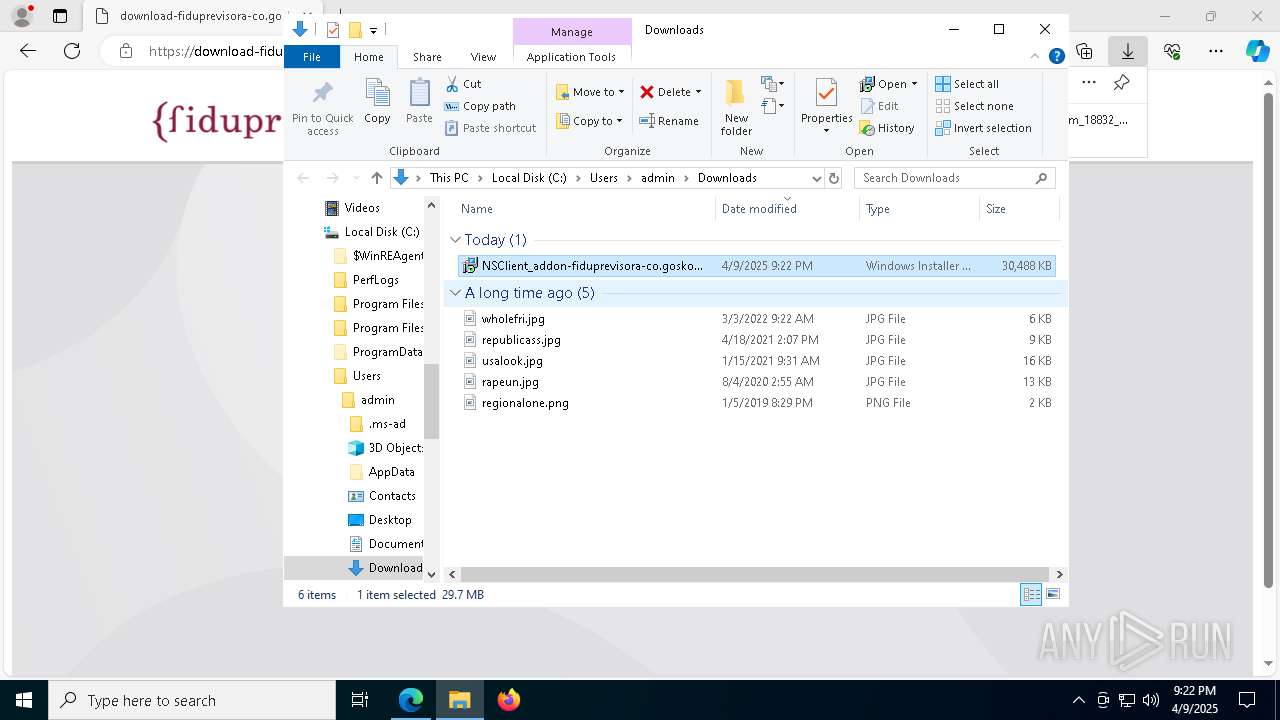
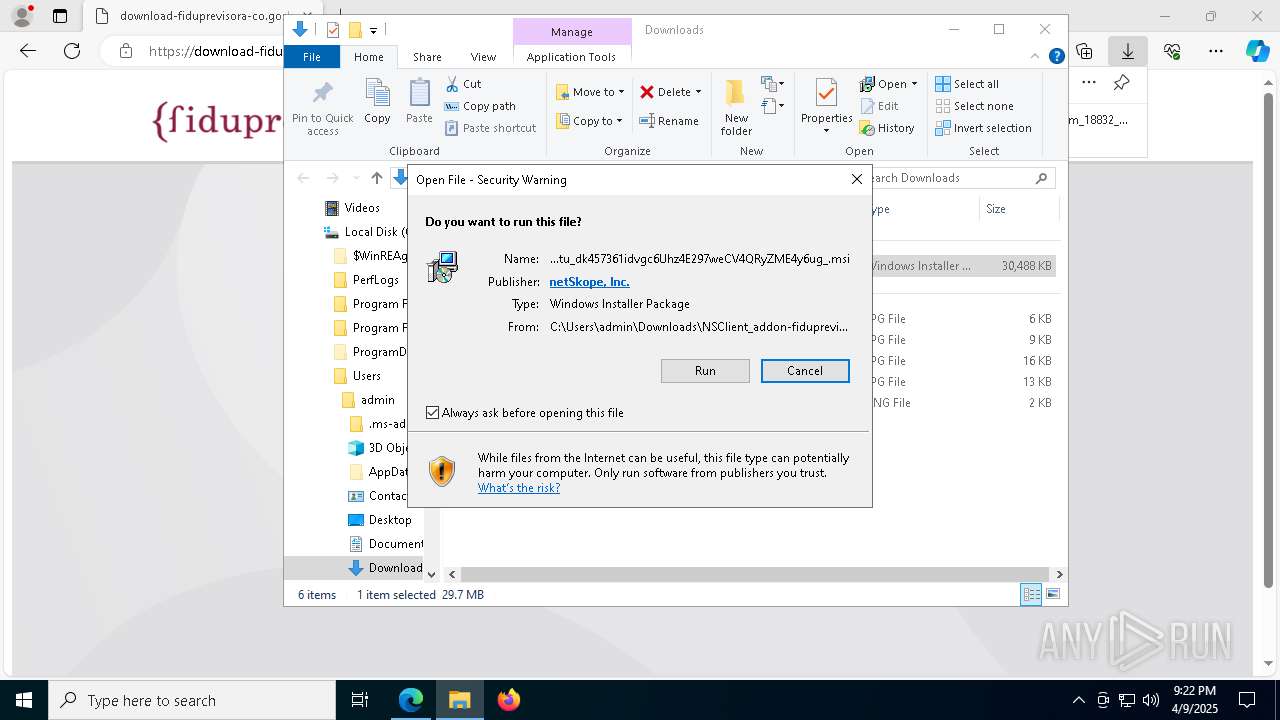
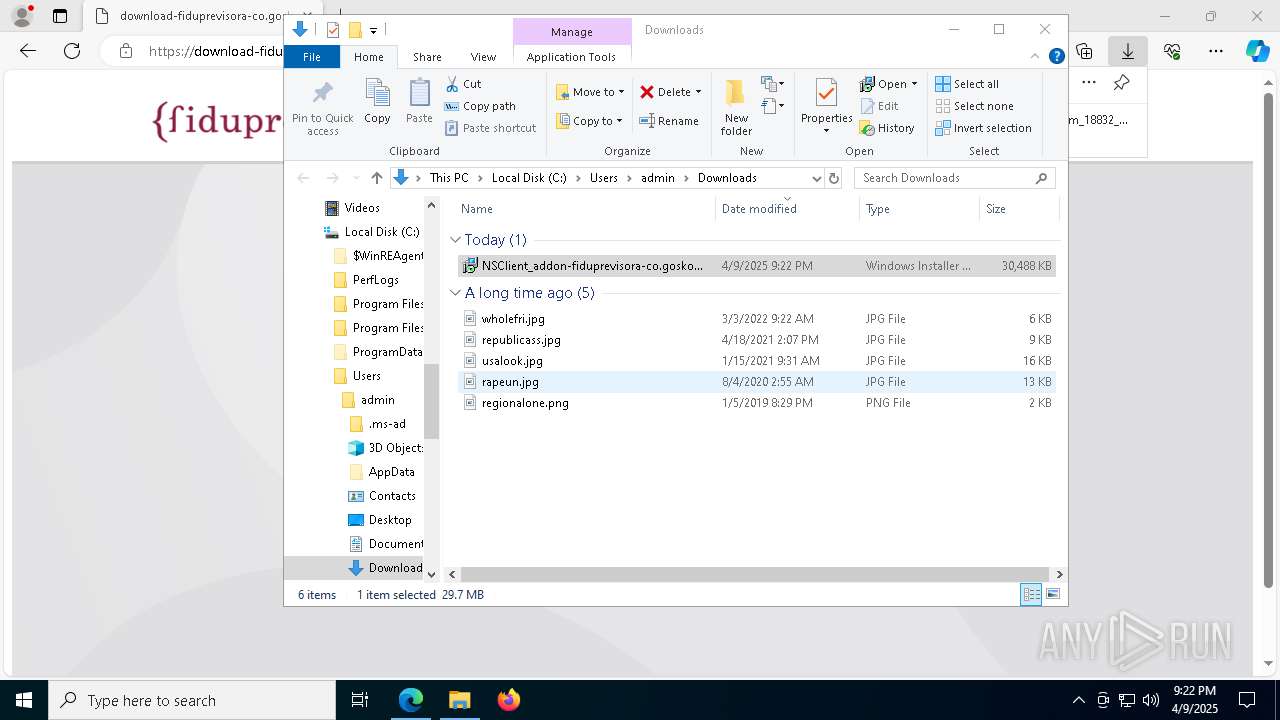
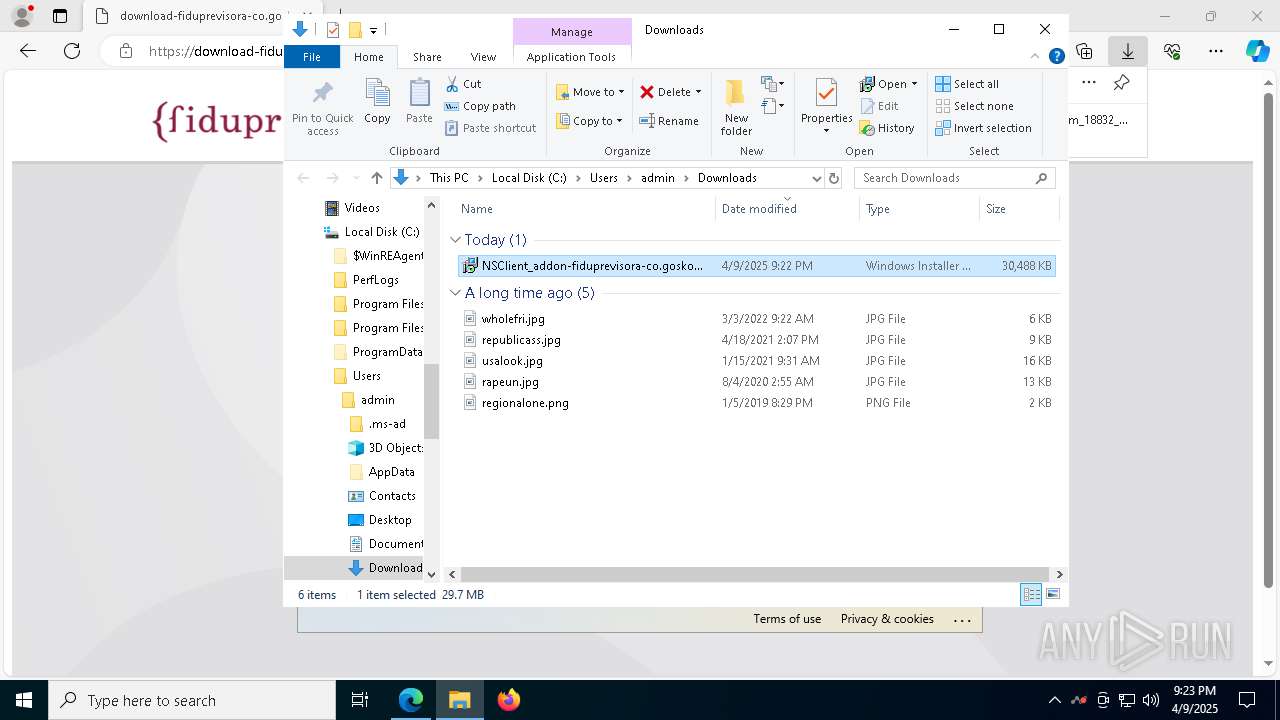
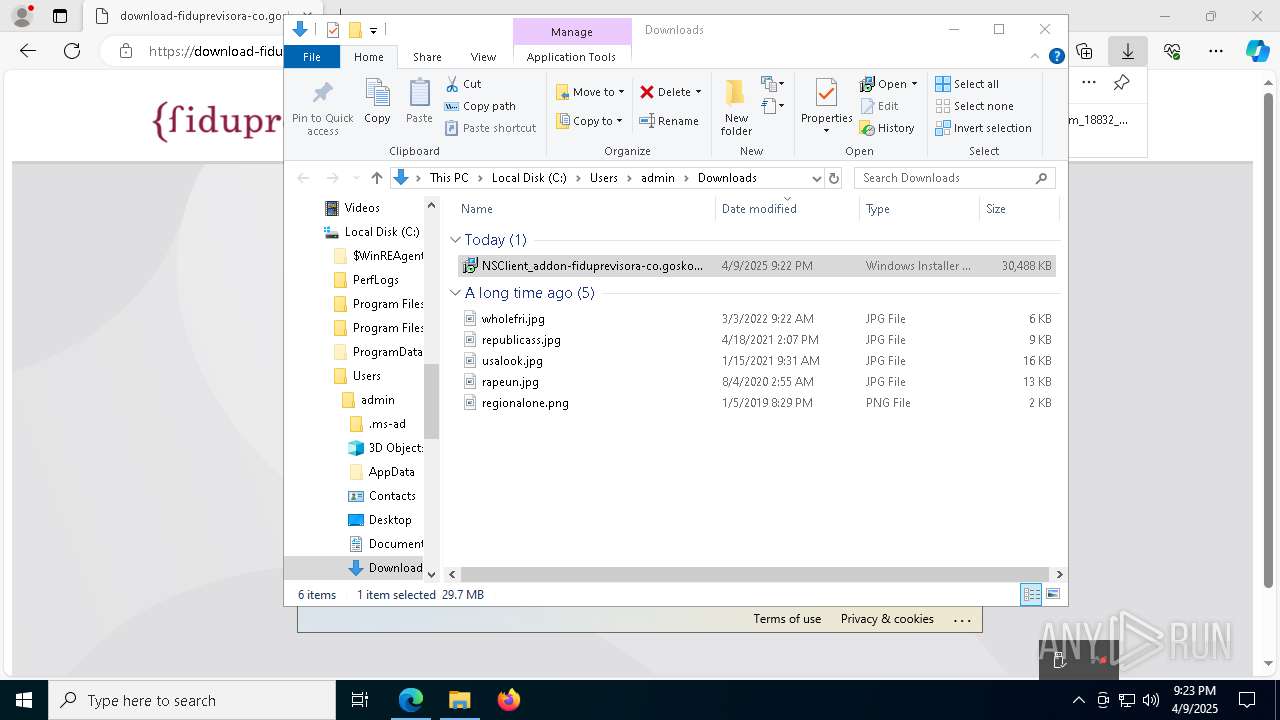
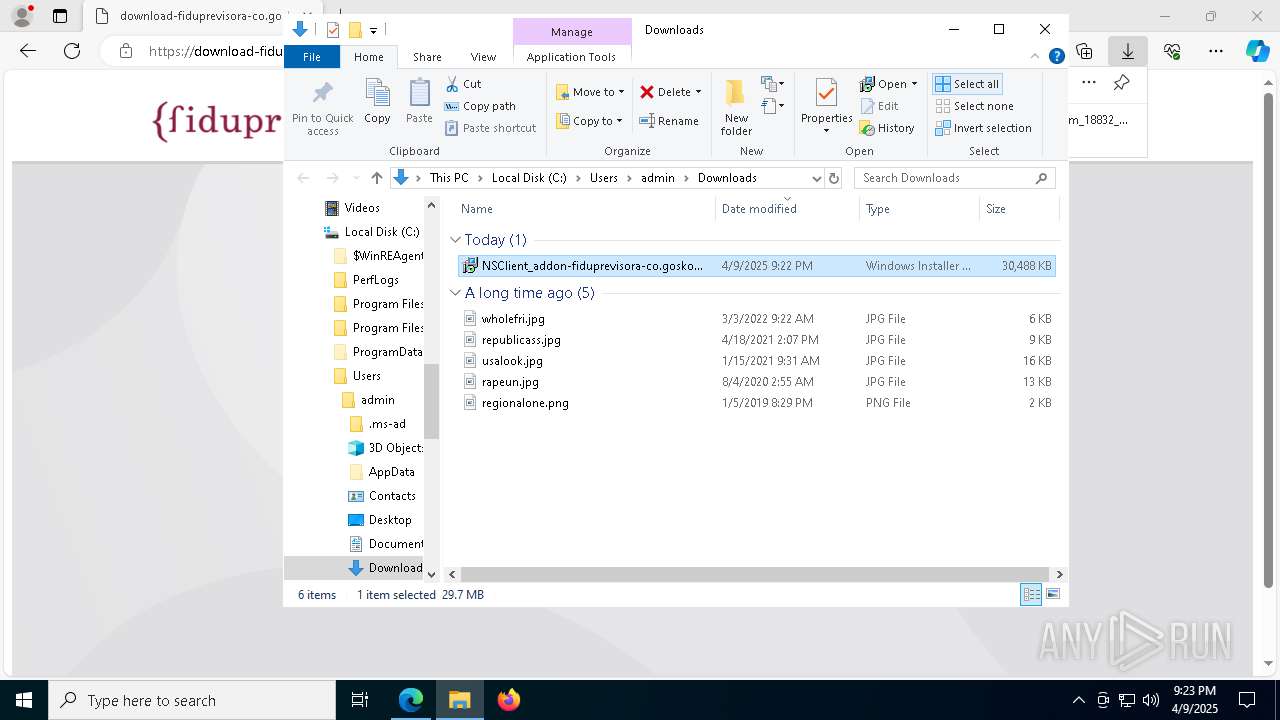
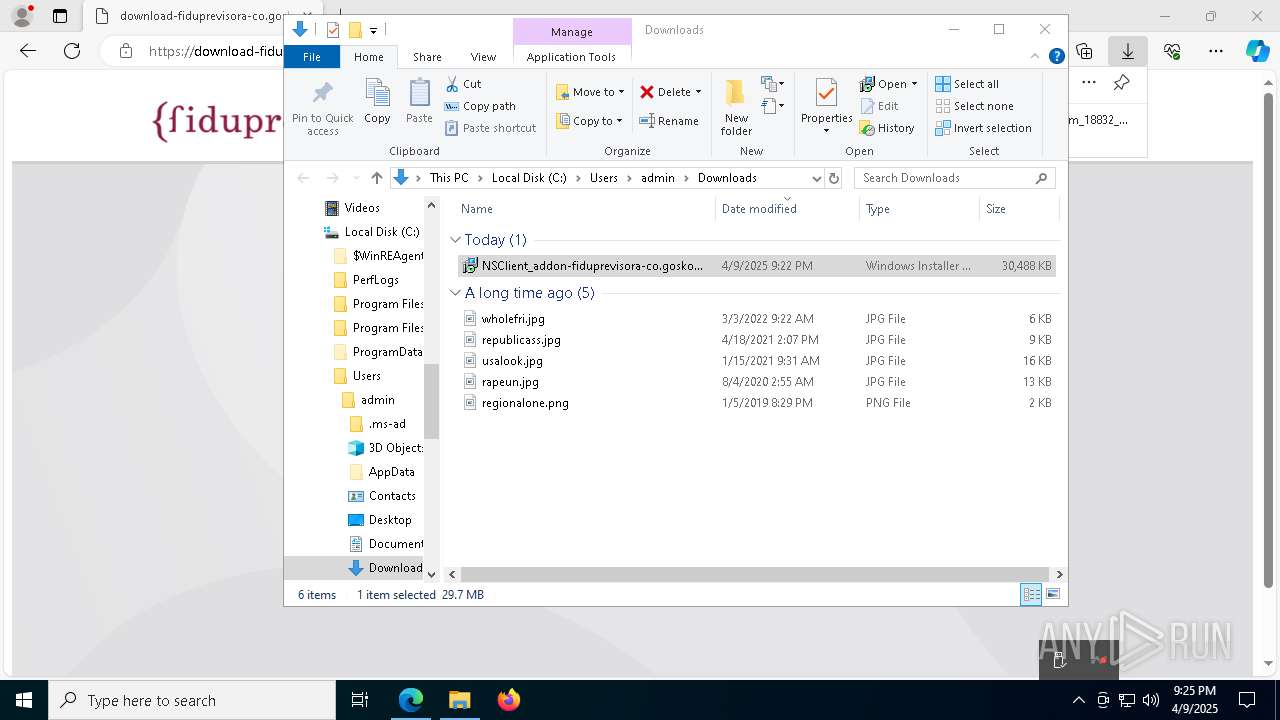
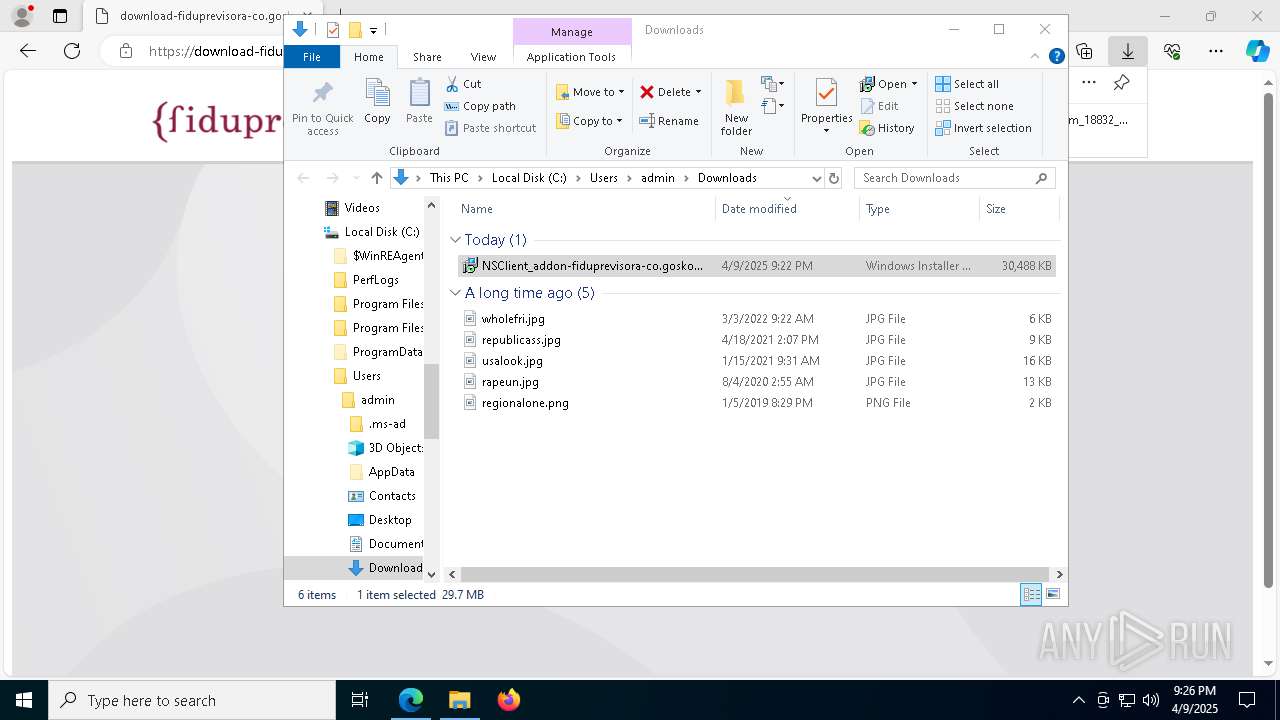
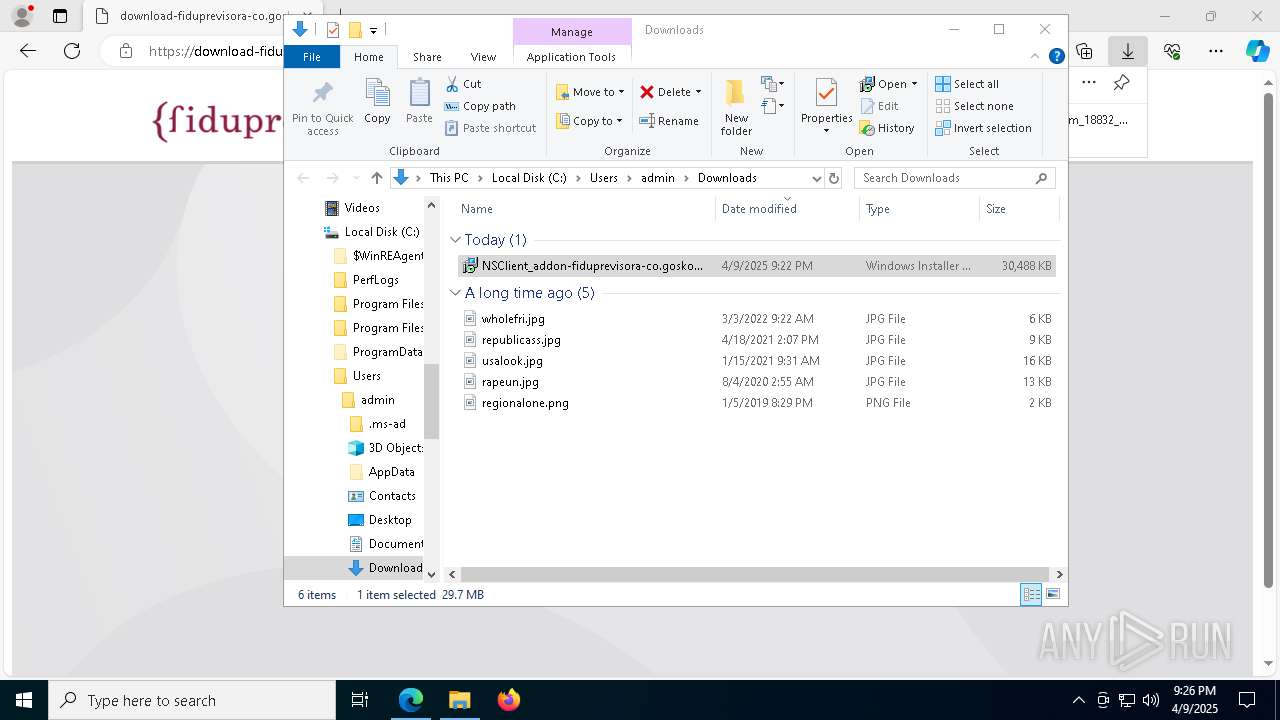
Autorun file from Downloads
- msedge.exe (PID: 5728)
Reads the software policy settings
- explorer.exe (PID: 5492)
- msiexec.exe (PID: 3180)
- msiexec.exe (PID: 5608)
- msiexec.exe (PID: 4608)
- stAgentSvc.exe (PID: 3032)
- slui.exe (PID: 8088)
- msiexec.exe (PID: 4572)
- stAgentUI.exe (PID: 7820)
- slui.exe (PID: 872)
Reads Microsoft Office registry keys
- explorer.exe (PID: 5492)
Checks proxy server information
- explorer.exe (PID: 5492)
- msiexec.exe (PID: 4608)
- stAgentUI.exe (PID: 7820)
- slui.exe (PID: 872)
Reads the computer name
- identity_helper.exe (PID: 4688)
- msiexec.exe (PID: 5608)
- msiexec.exe (PID: 660)
- msiexec.exe (PID: 4608)
- msiexec.exe (PID: 6132)
- msiexec.exe (PID: 7824)
- msiexec.exe (PID: 4572)
- stAgentUI.exe (PID: 7820)
- stAgentSvc.exe (PID: 3032)
- stAgentUI.exe (PID: 7892)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3180)
- explorer.exe (PID: 5492)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3180)
- msiexec.exe (PID: 5608)
- msiexec.exe (PID: 7824)
- msedge.exe (PID: 1748)
Manages system restore points
- SrTasks.exe (PID: 2268)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4608)
- msiexec.exe (PID: 5608)
- stAgentSvc.exe (PID: 3032)
- stAgentUI.exe (PID: 7820)
- msiexec.exe (PID: 4572)
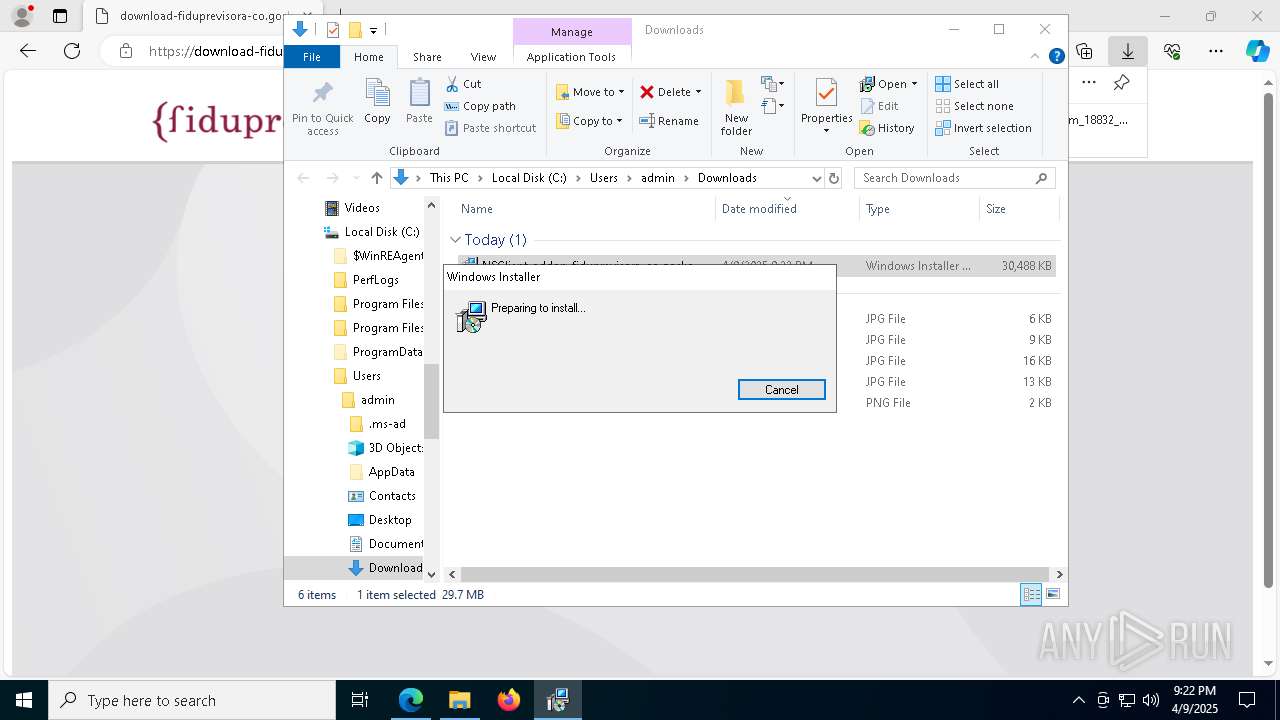
Application launched itself
- msiexec.exe (PID: 5608)
- msedge.exe (PID: 2616)
The sample compiled with english language support
- msiexec.exe (PID: 5608)
- msiexec.exe (PID: 7824)
- msedge.exe (PID: 1748)
Creates files in the program directory
- stAgentSvc.exe (PID: 3032)
- keytool.exe (PID: 7808)
Creates a software uninstall entry
- msiexec.exe (PID: 5608)
Found Base64 encoded access to processes via PowerShell (YARA)
- stAgentSvc.exe (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
90
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | C:\Windows\syswow64\MsiExec.exe -Embedding E6D780BBD9EE8149E70FF2F2A0A422E7 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5608 --field-trial-handle=1420,i,15385618616068760995,17818899383798482721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4840 --field-trial-handle=1420,i,15385618616068760995,17818899383798482721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | keytool.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6544 --field-trial-handle=1420,i,15385618616068760995,17818899383798482721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4428 --field-trial-handle=1420,i,15385618616068760995,17818899383798482721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
49 499
Read events
48 992
Write events
480
Delete events
27
Modification events
| (PID) Process: | (2616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:00000000000602CC |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (2616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2616) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 94396B58F5902F00 | |||
| (PID) Process: | (2616) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 17267758F5902F00 | |||
| (PID) Process: | (2616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393932 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4AA68082-8876-40E2-895A-5077EAE3BF29} | |||
| (PID) Process: | (2616) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393932 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3FE3B28A-0042-468D-9ED1-68563A15C109} | |||
| (PID) Process: | (2616) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F6FFB558F5902F00 | |||
Executable files
156
Suspicious files
397
Text files
131
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ba78.TMP | — | |
MD5:— | SHA256:— | |||
| 2616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ba88.TMP | — | |
MD5:— | SHA256:— | |||
| 2616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bab7.TMP | — | |
MD5:— | SHA256:— | |||
| 2616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bab7.TMP | — | |
MD5:— | SHA256:— | |||
| 2616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bac6.TMP | — | |
MD5:— | SHA256:— | |||
| 2616 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
116
DNS requests
99
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3396 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1744639756&P2=404&P3=2&P4=TW7S%2fGVy%2bRcxUFkI0C%2bjWz%2bNe9tIoqlPwD8Tl1DQW80aeZYMlUy2iPR4UTq9Bs%2fqp%2fwFvn2RqbcrPXB0nQLfiw%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGEJFcIpBz28BuO60qVQ%3D | unknown | — | — | whitelisted |
1328 | SIHClient.exe | GET | 200 | 23.38.81.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1328 | SIHClient.exe | GET | 200 | 23.38.81.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
3396 | svchost.exe | HEAD | 200 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1744639756&P2=404&P3=2&P4=TW7S%2fGVy%2bRcxUFkI0C%2bjWz%2bNe9tIoqlPwD8Tl1DQW80aeZYMlUy2iPR4UTq9Bs%2fqp%2fwFvn2RqbcrPXB0nQLfiw%3d%3d | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDAfAcTao81JOF%2Fv0qw%3D%3D | unknown | — | — | whitelisted |
3396 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1744639756&P2=404&P3=2&P4=TW7S%2fGVy%2bRcxUFkI0C%2bjWz%2bNe9tIoqlPwD8Tl1DQW80aeZYMlUy2iPR4UTq9Bs%2fqp%2fwFvn2RqbcrPXB0nQLfiw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2616 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7360 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 2.22.242.11:443 | bzib.nelreports.net | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
download-fiduprevisora-co.goskope.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
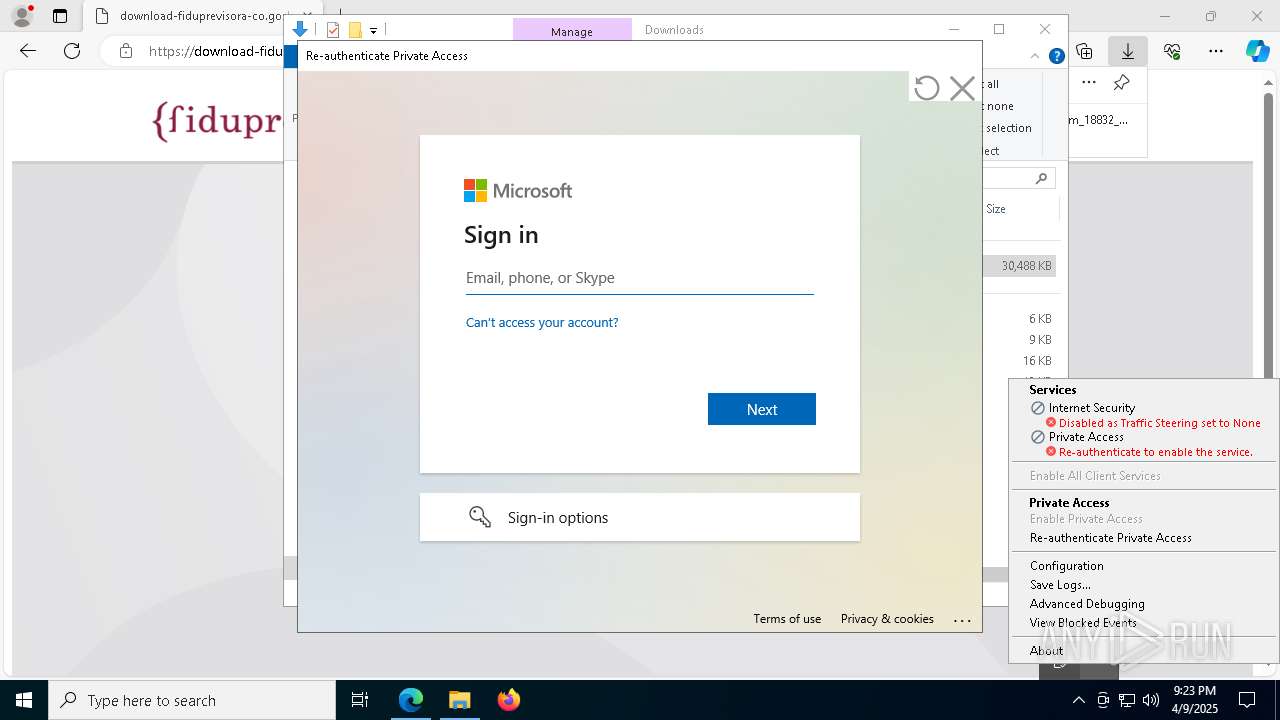
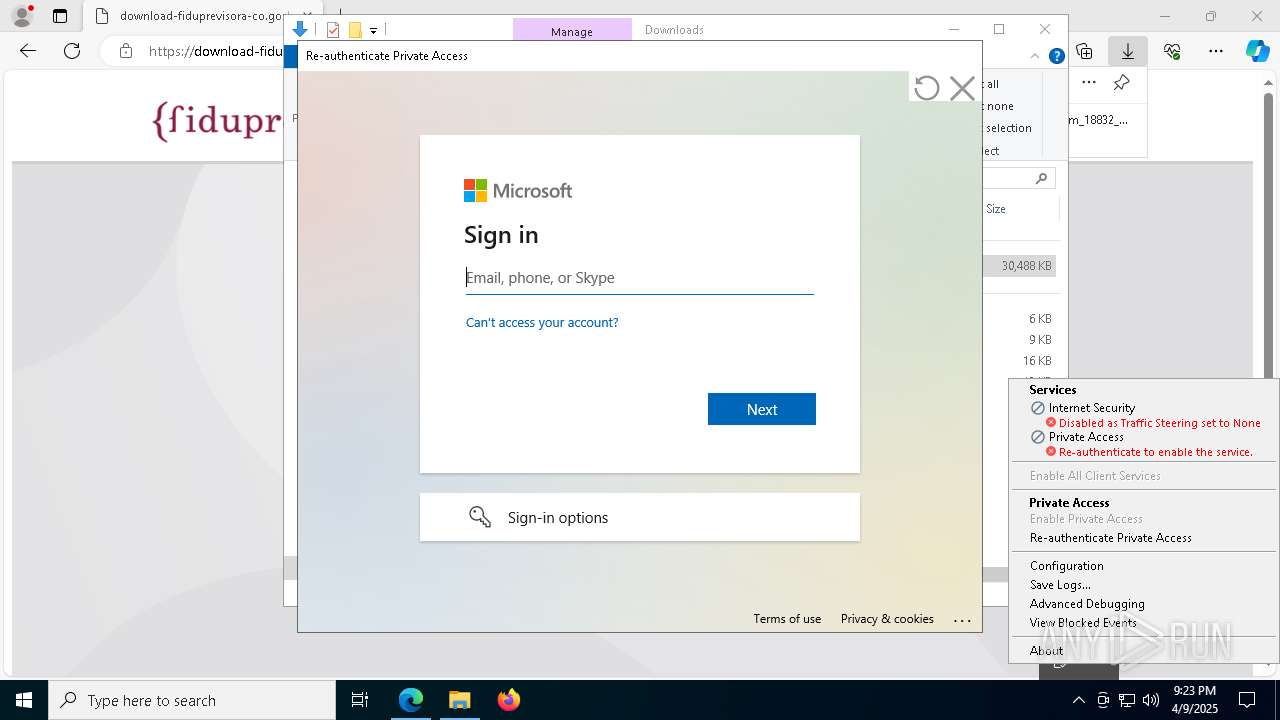
3032 | stAgentSvc.exe | Misc activity | ET INFO Observed Google DNS over HTTPS Domain (dns .google in TLS SNI) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Microsoft Entra seamless single sign-on (autologon .microsoftazuread-sso .com) |
Process | Message |
|---|---|
stAgentSvc.exe | [stAgentSvc]: All NPA IP rules are added into kernel.
|