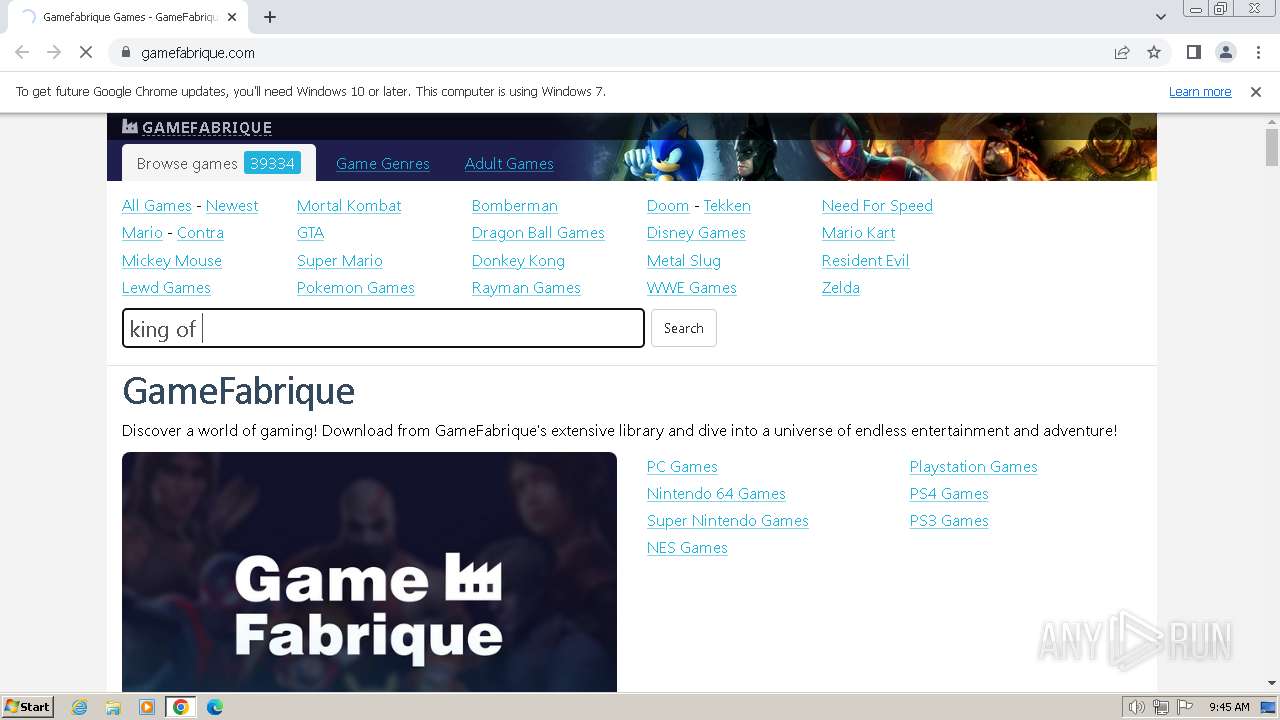
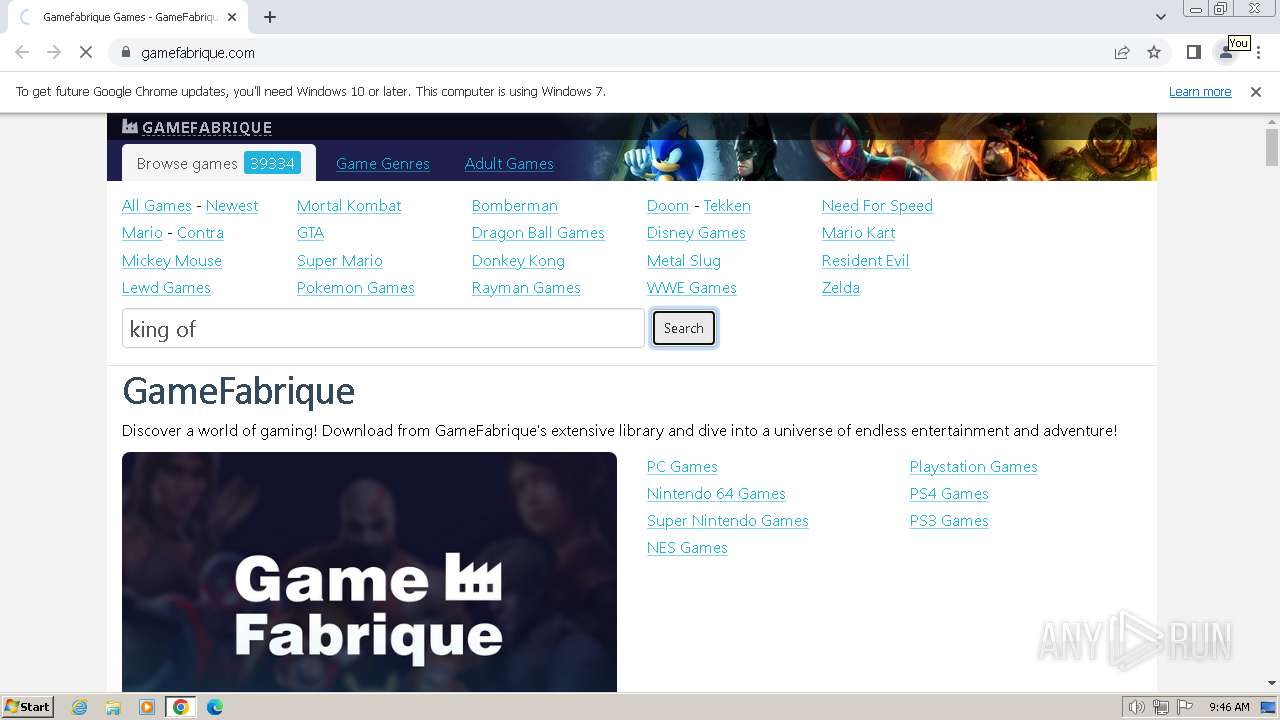
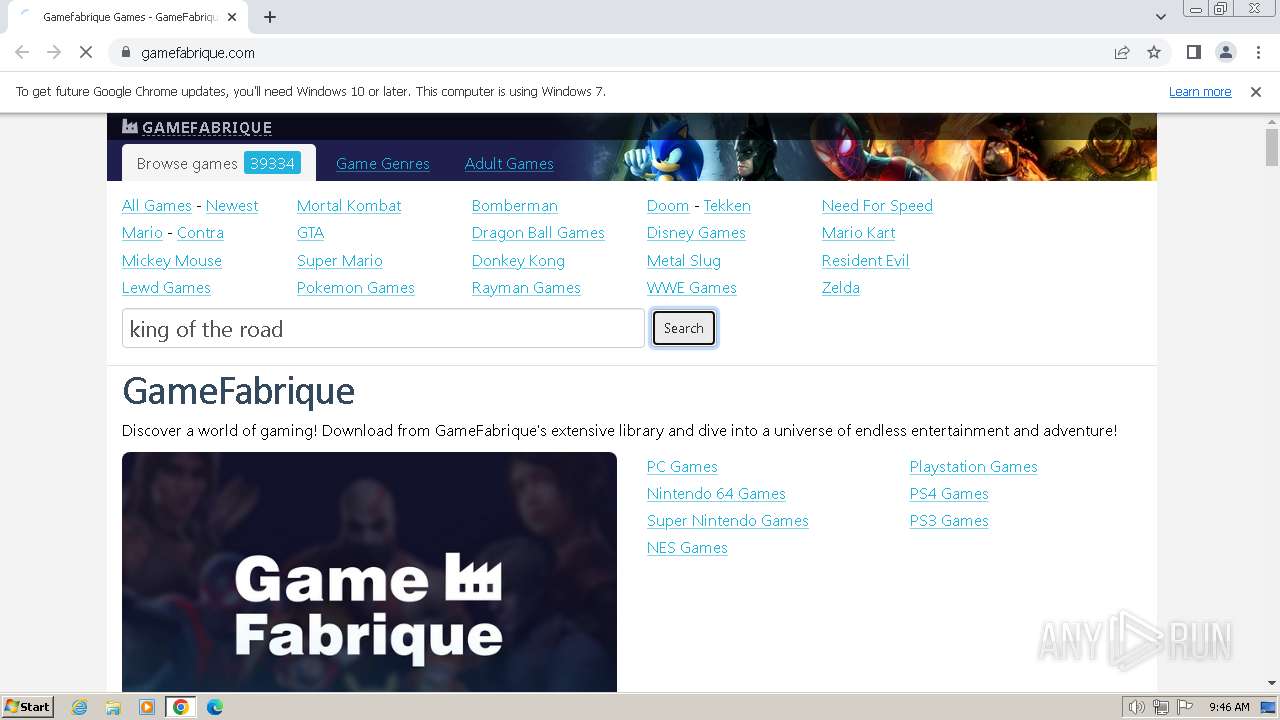
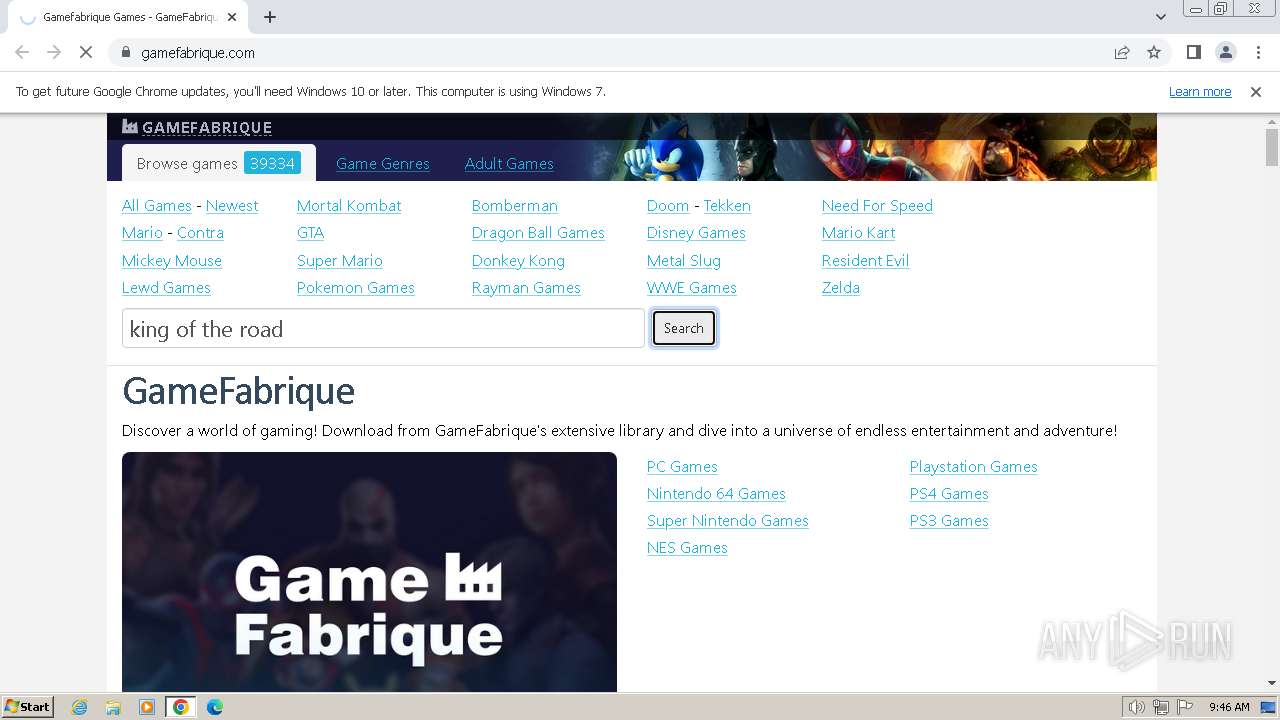
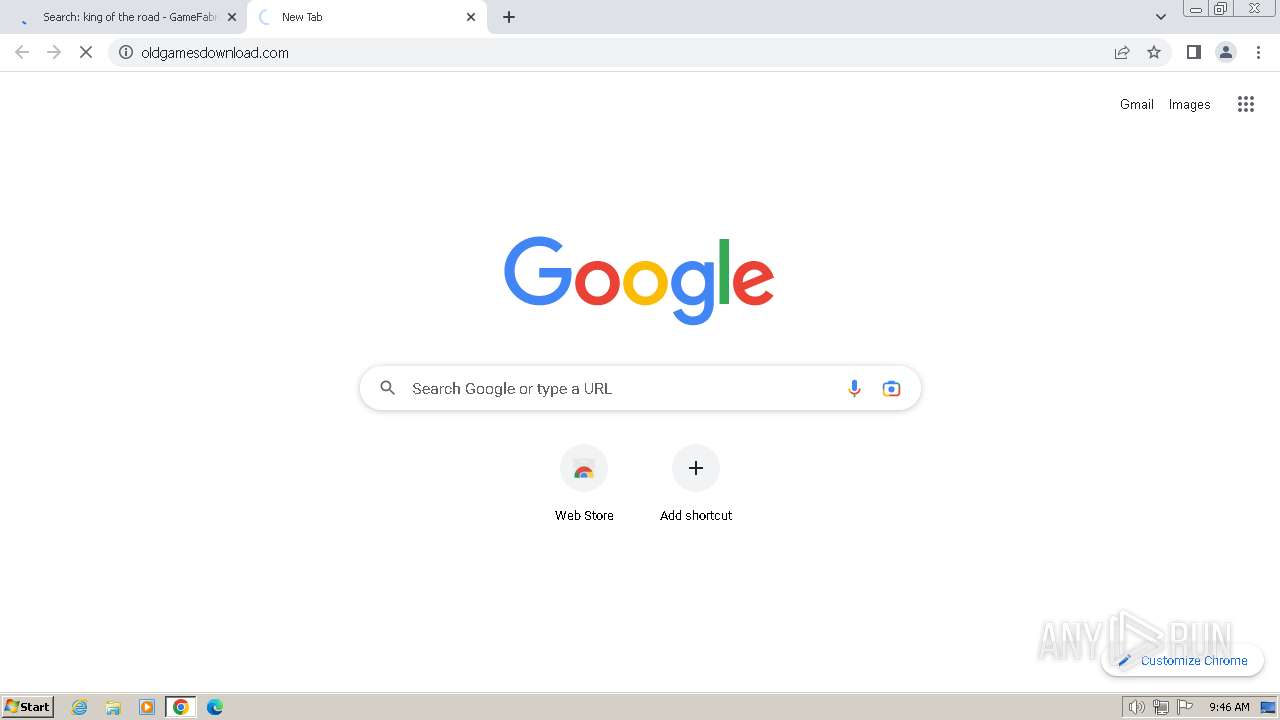
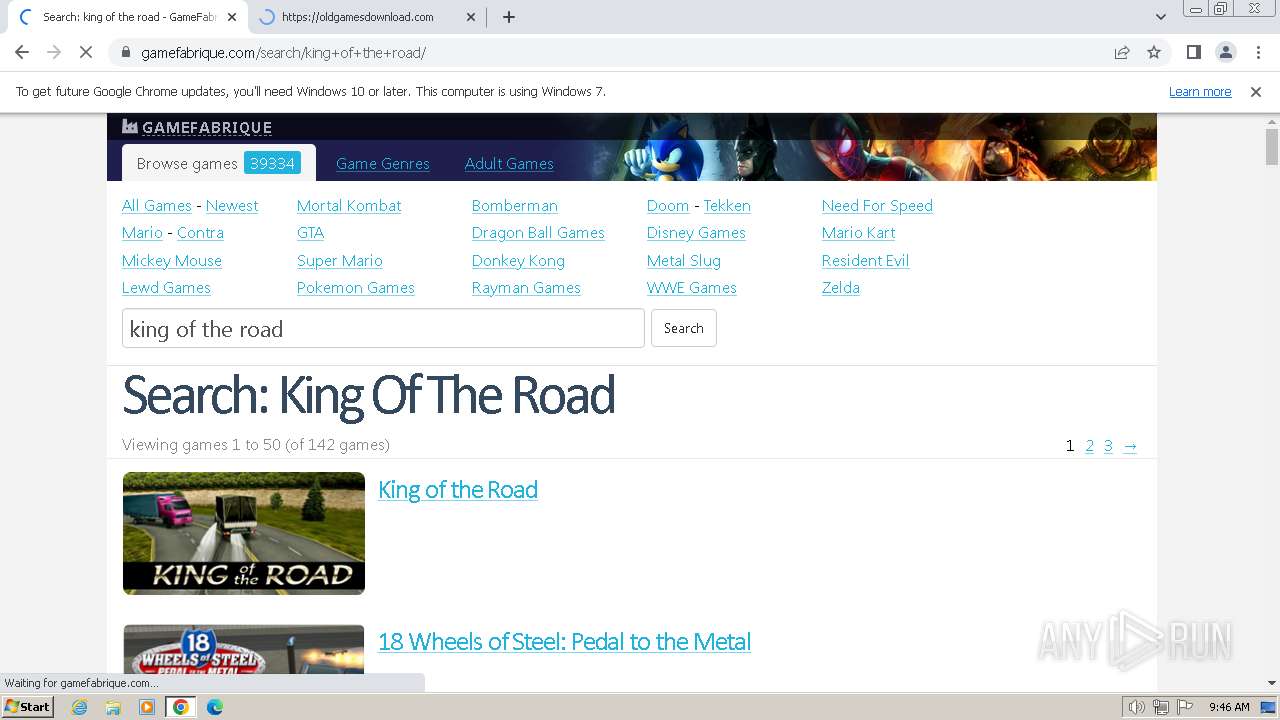
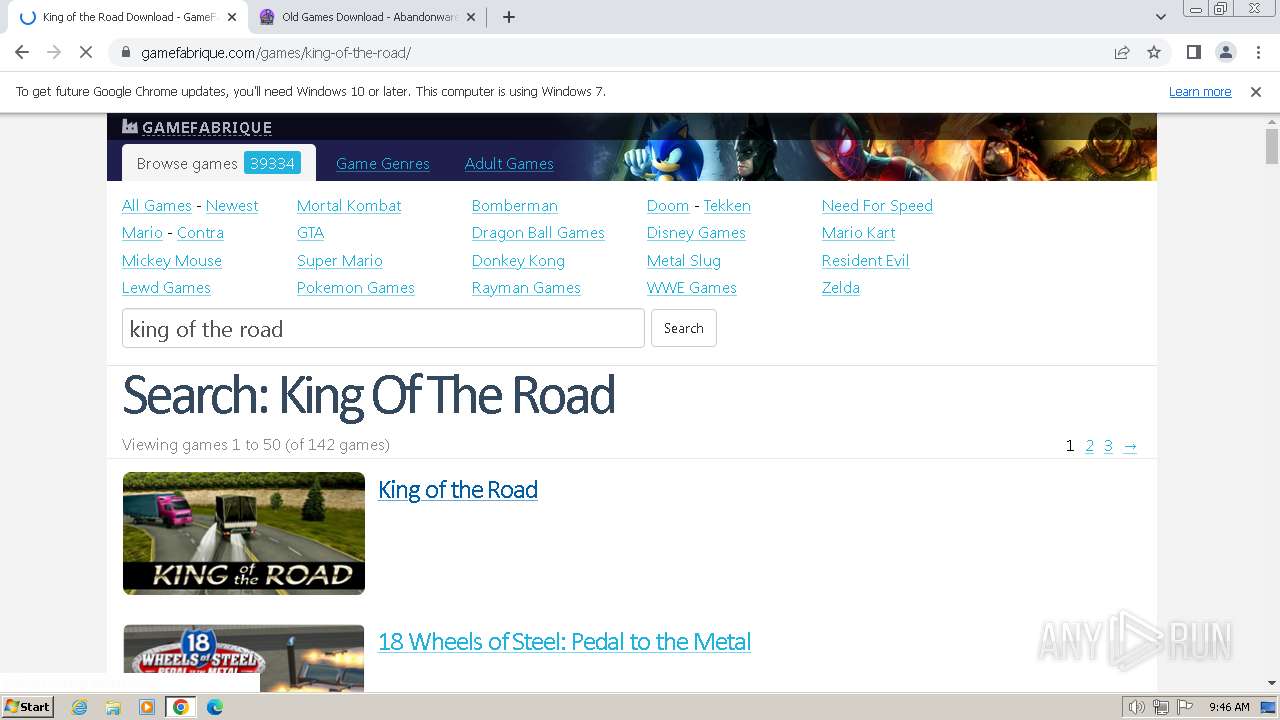
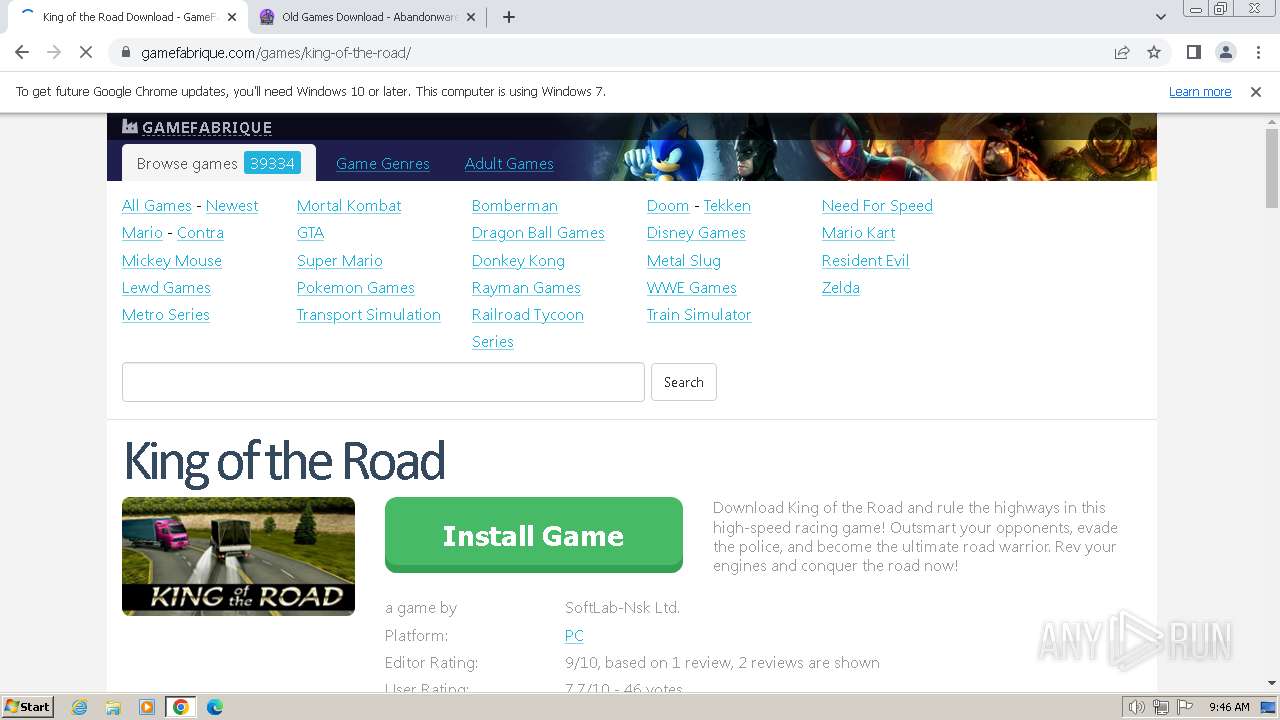
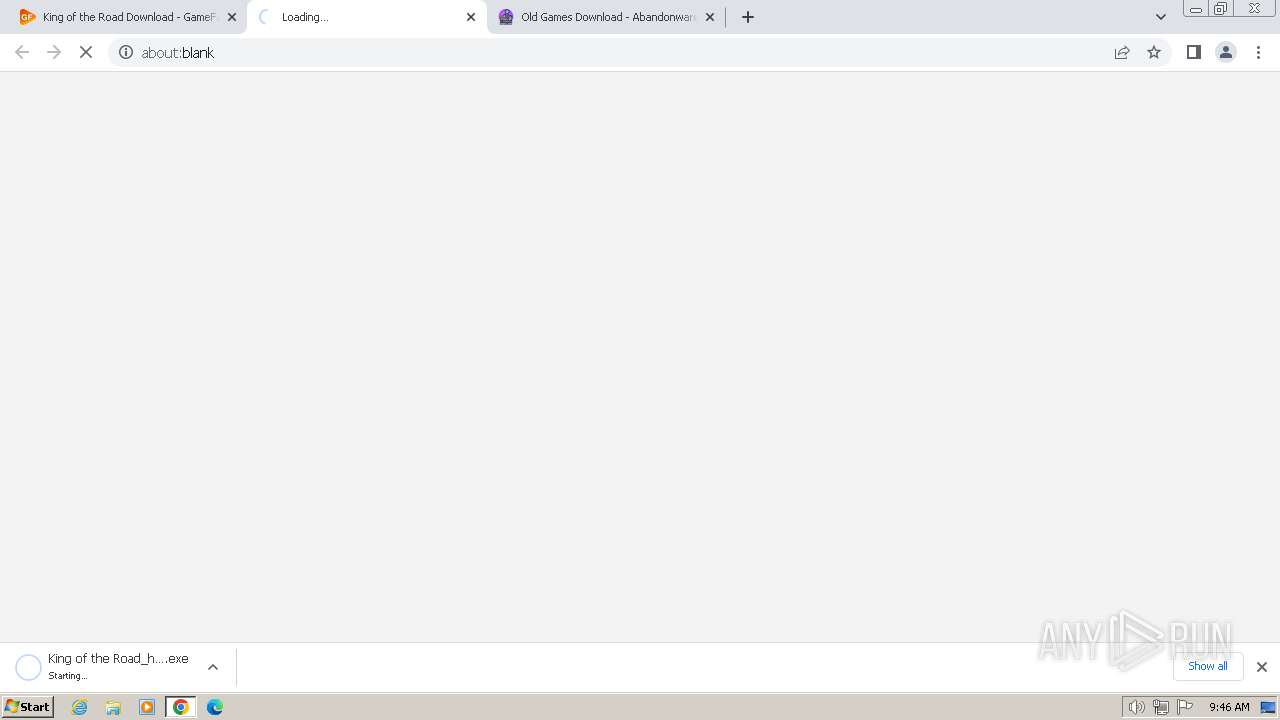
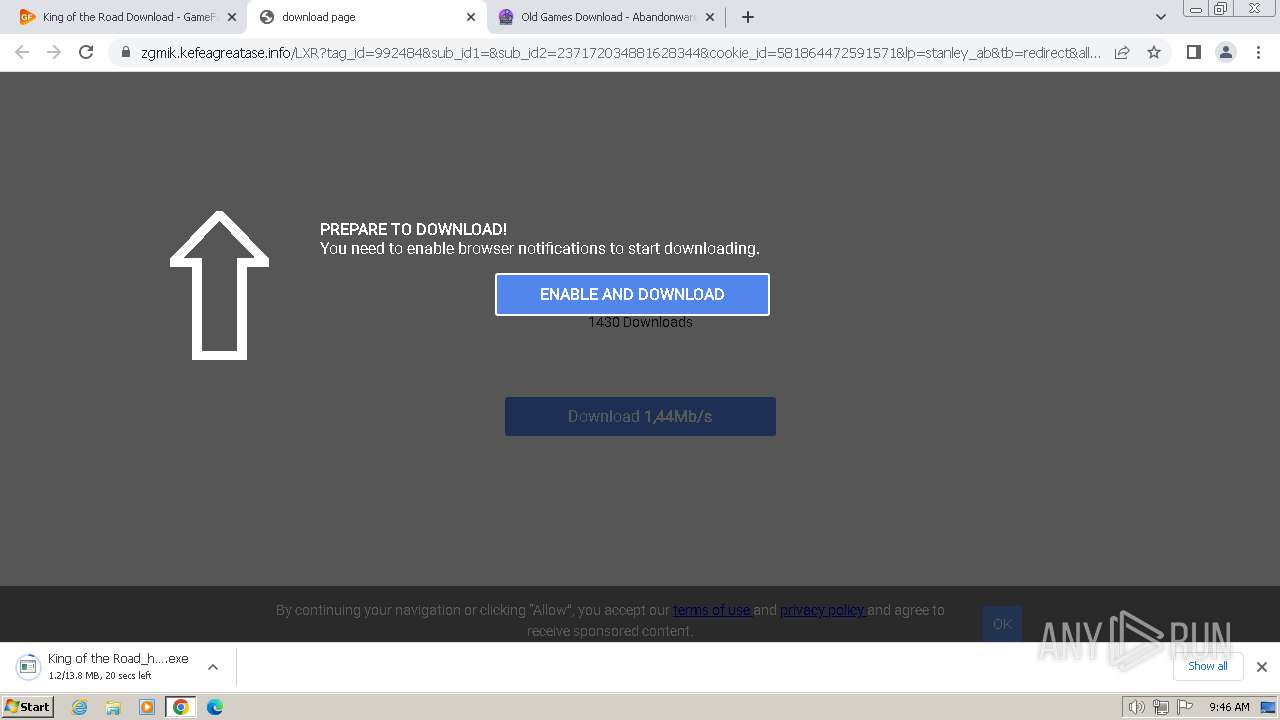
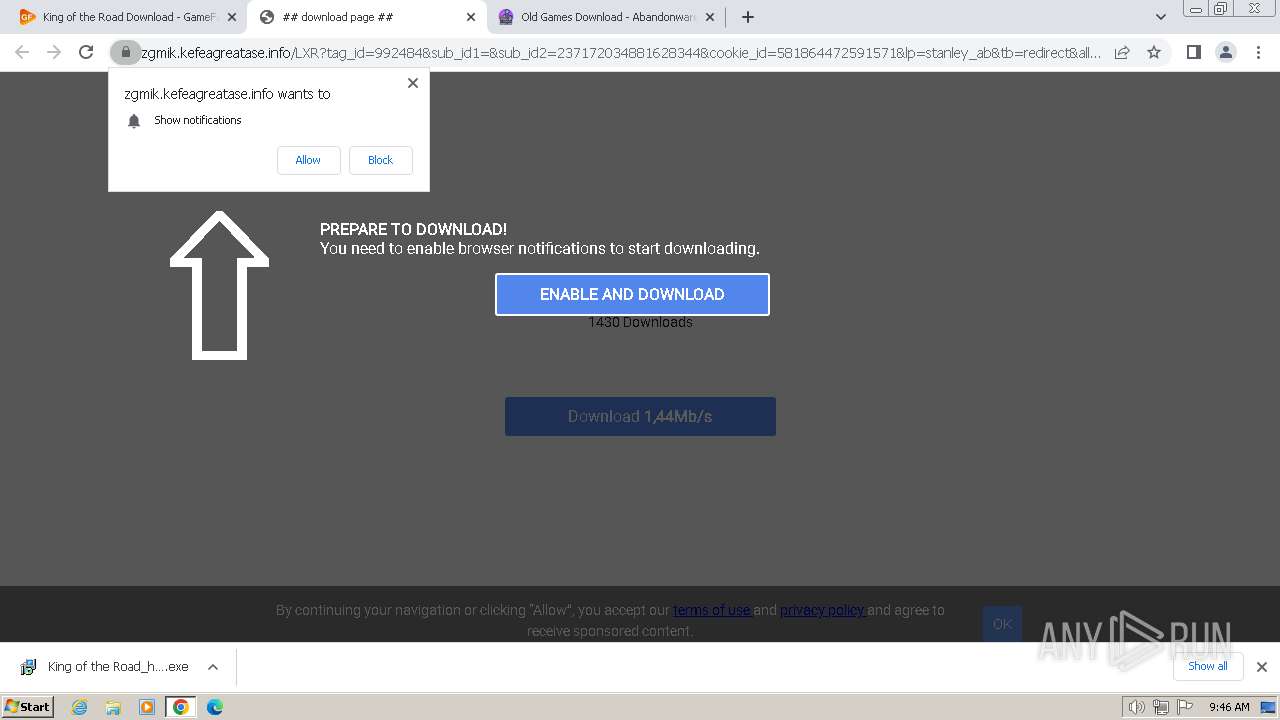
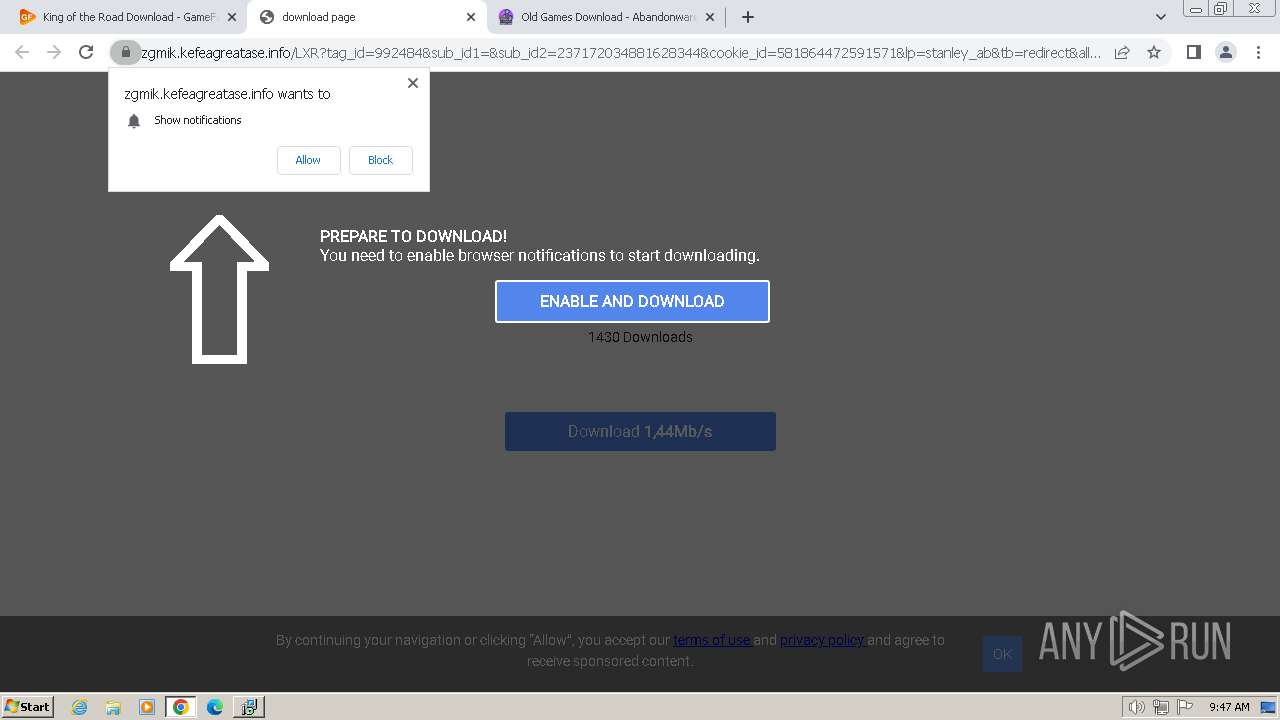
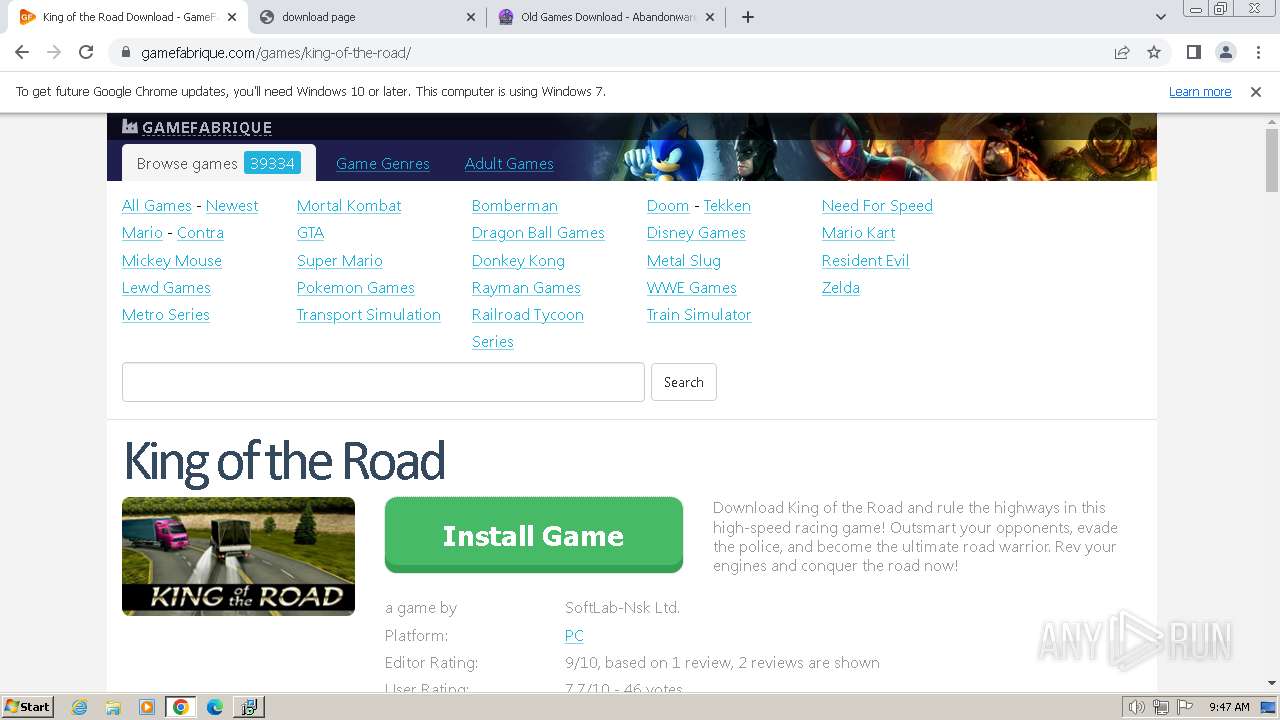
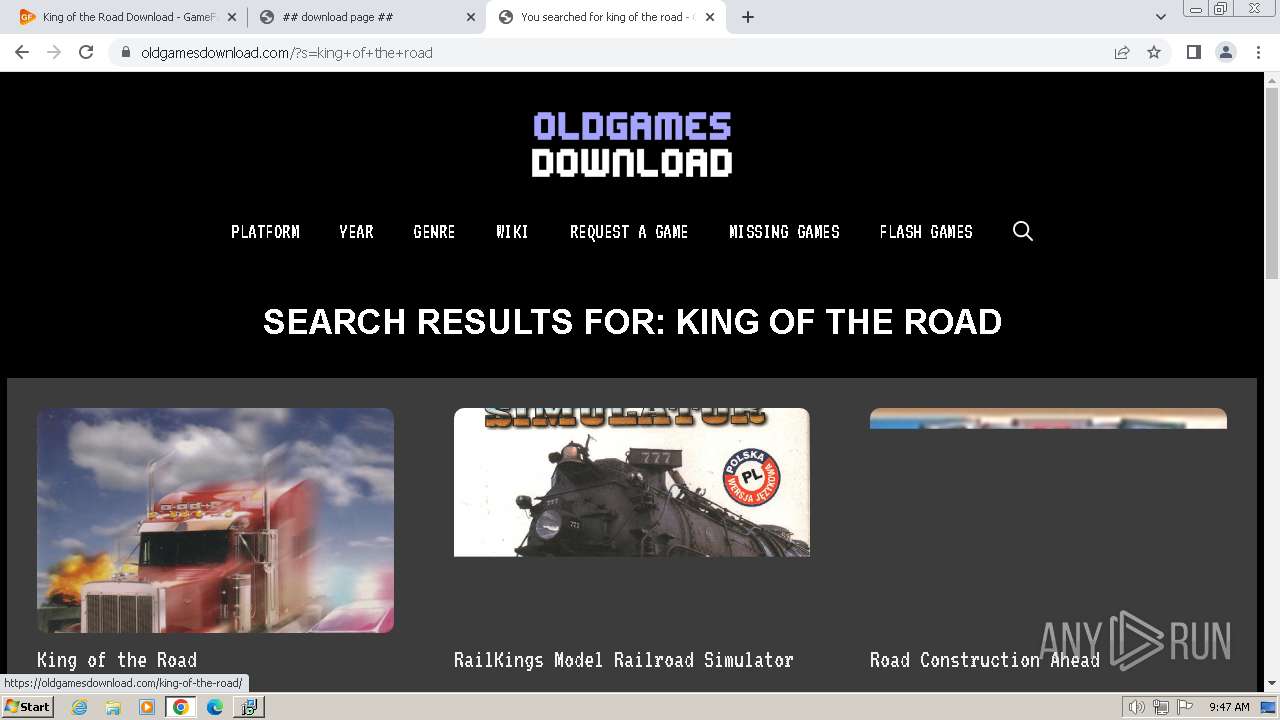
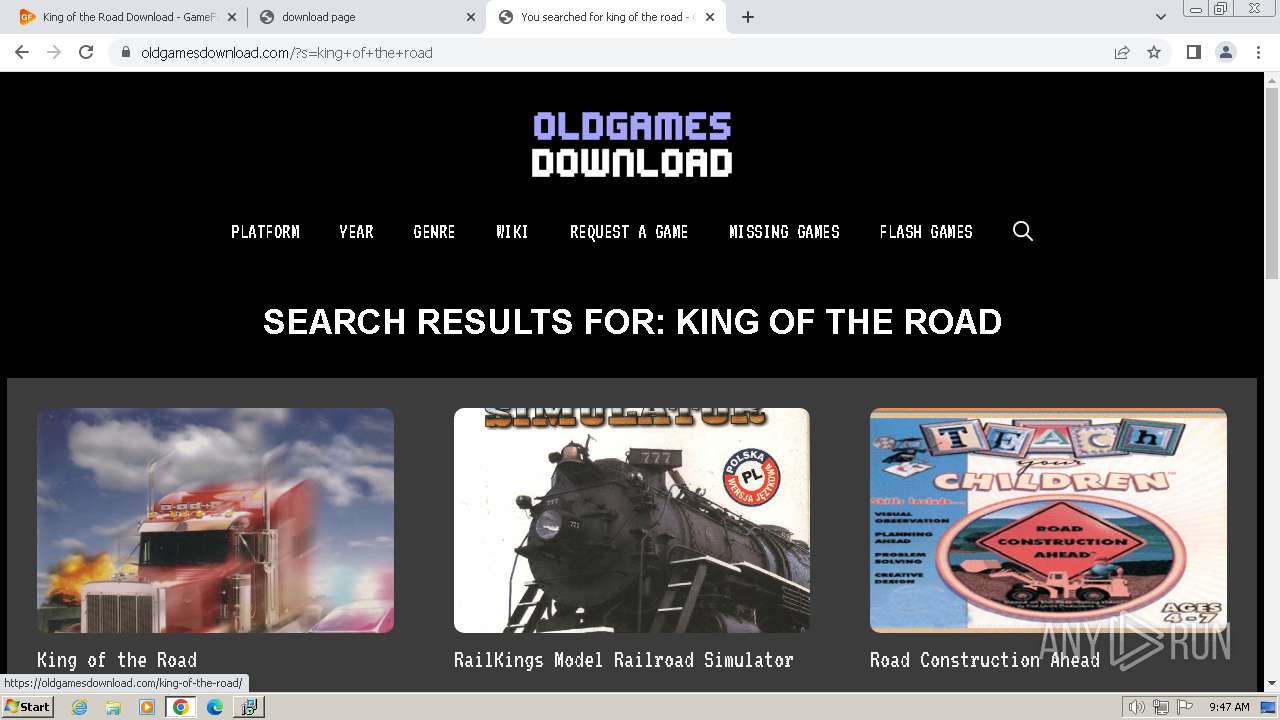
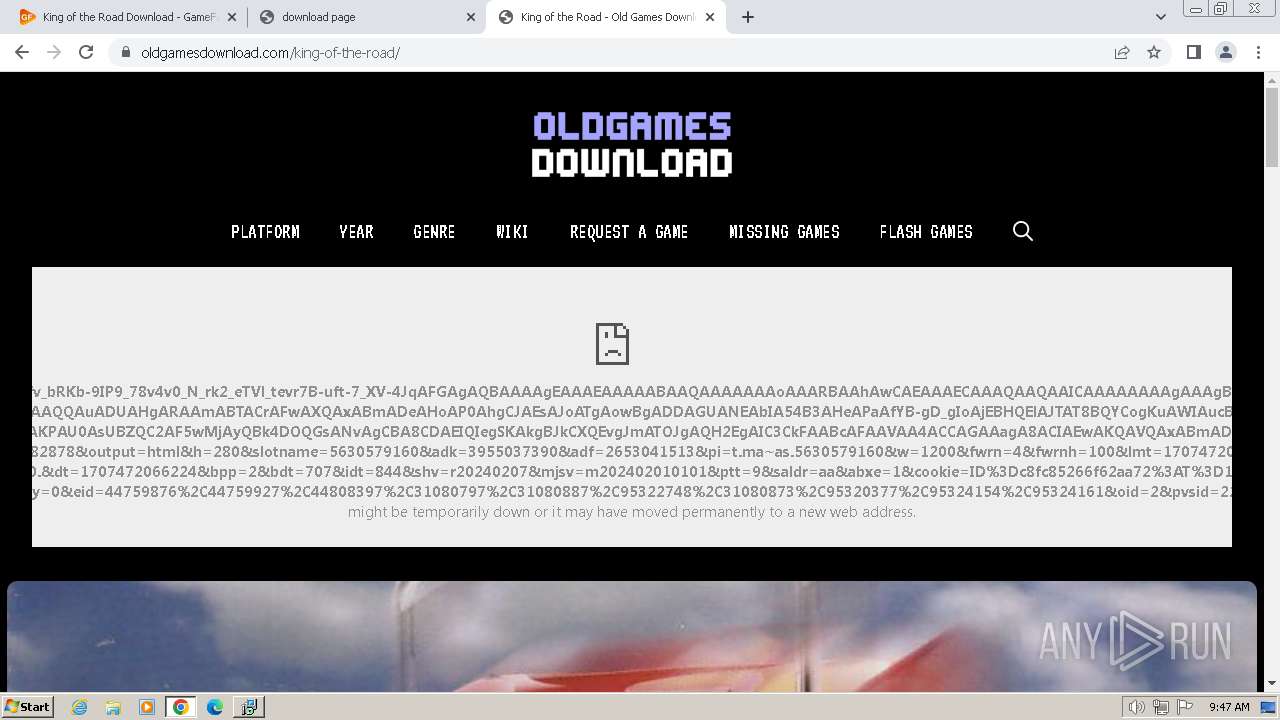
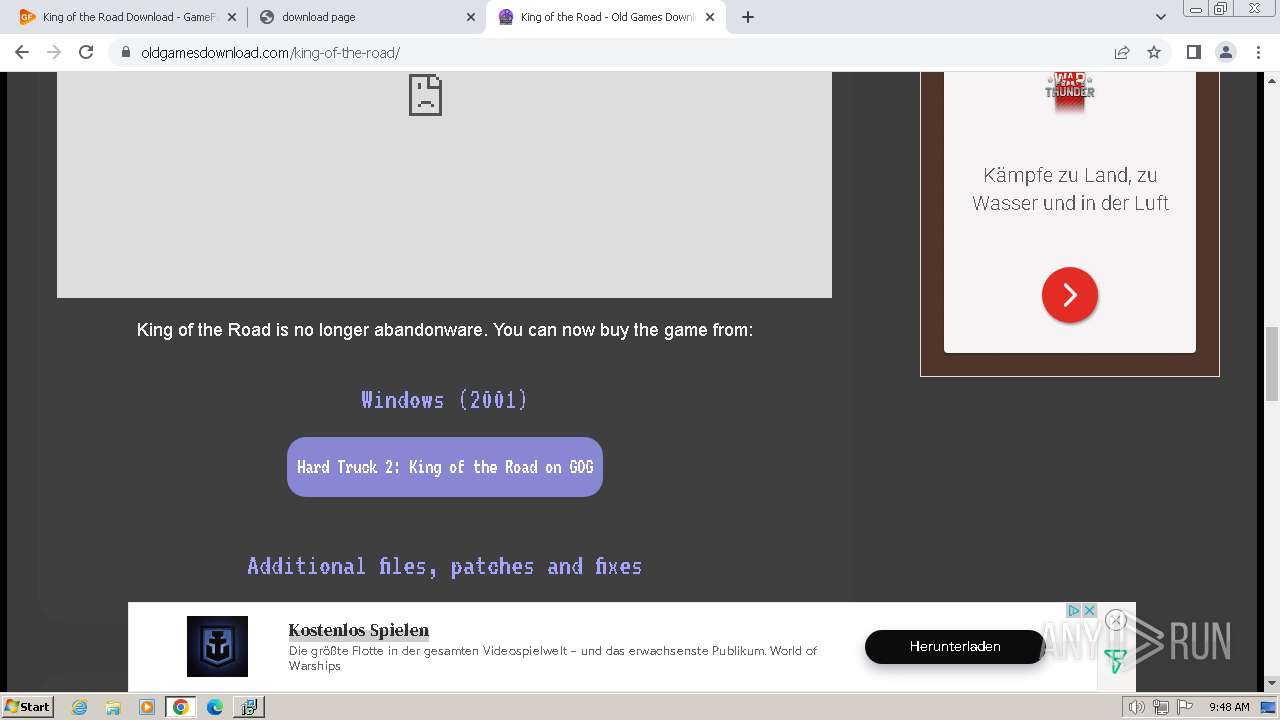
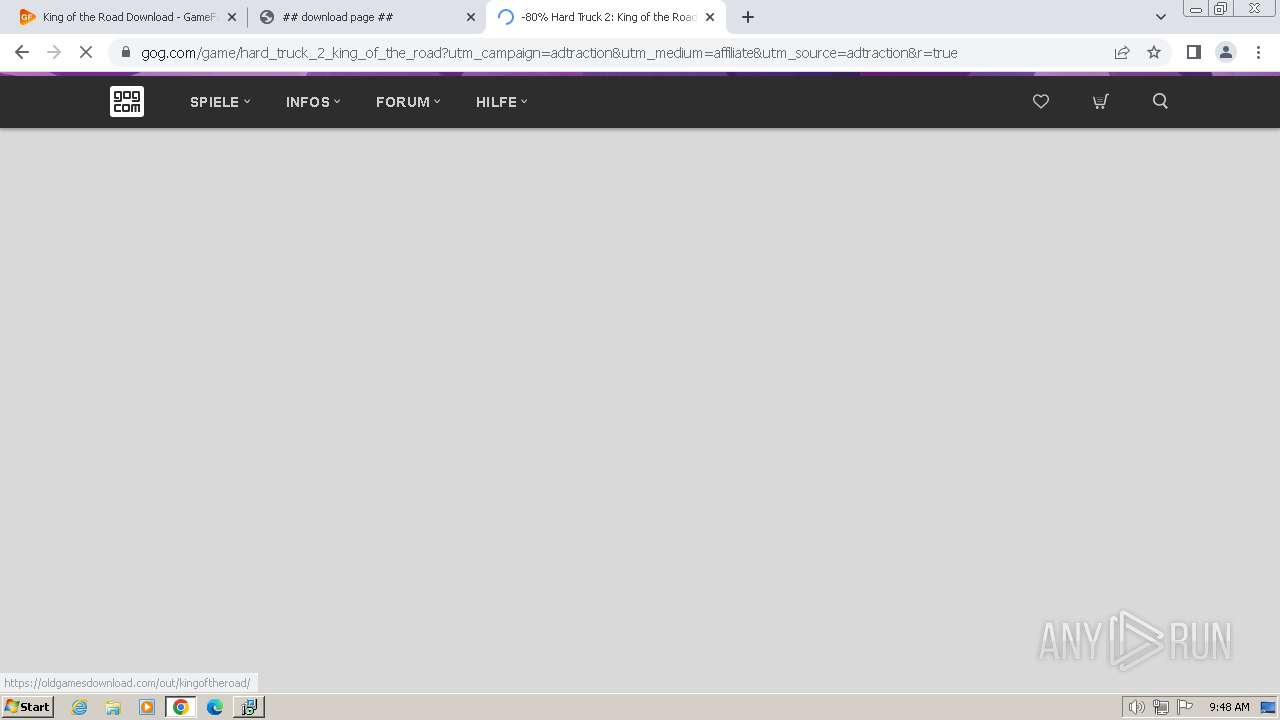
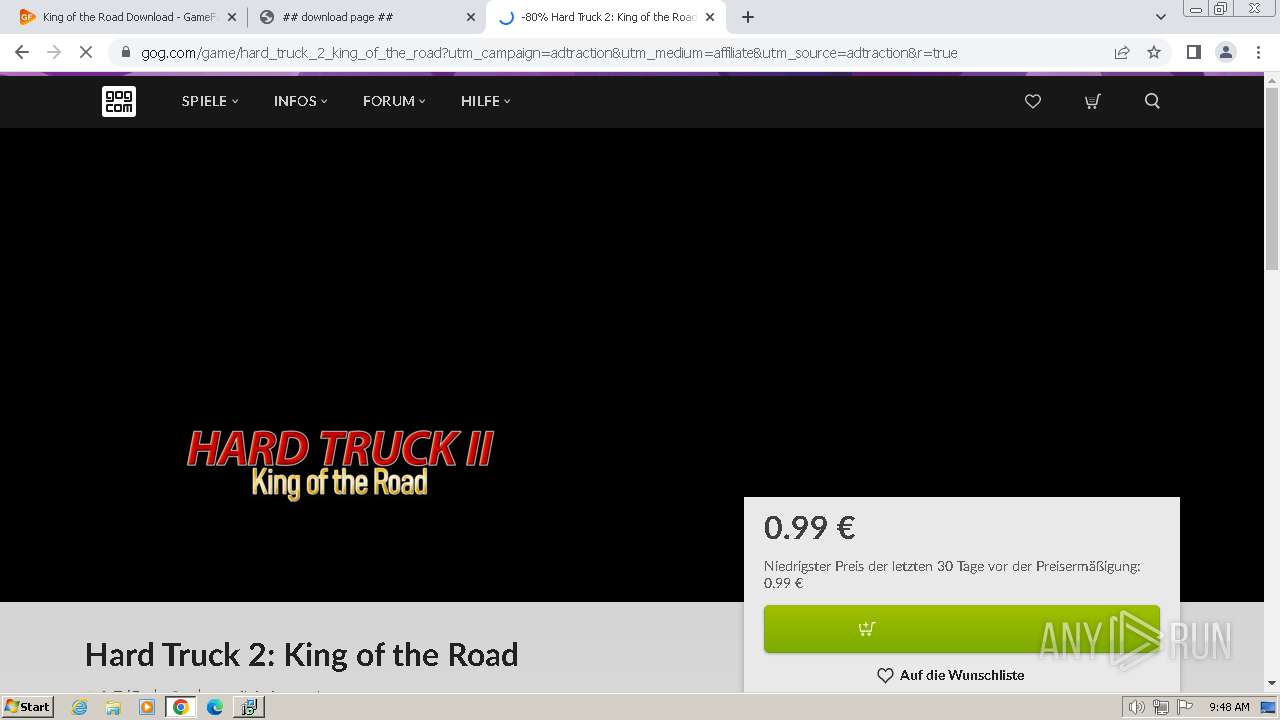
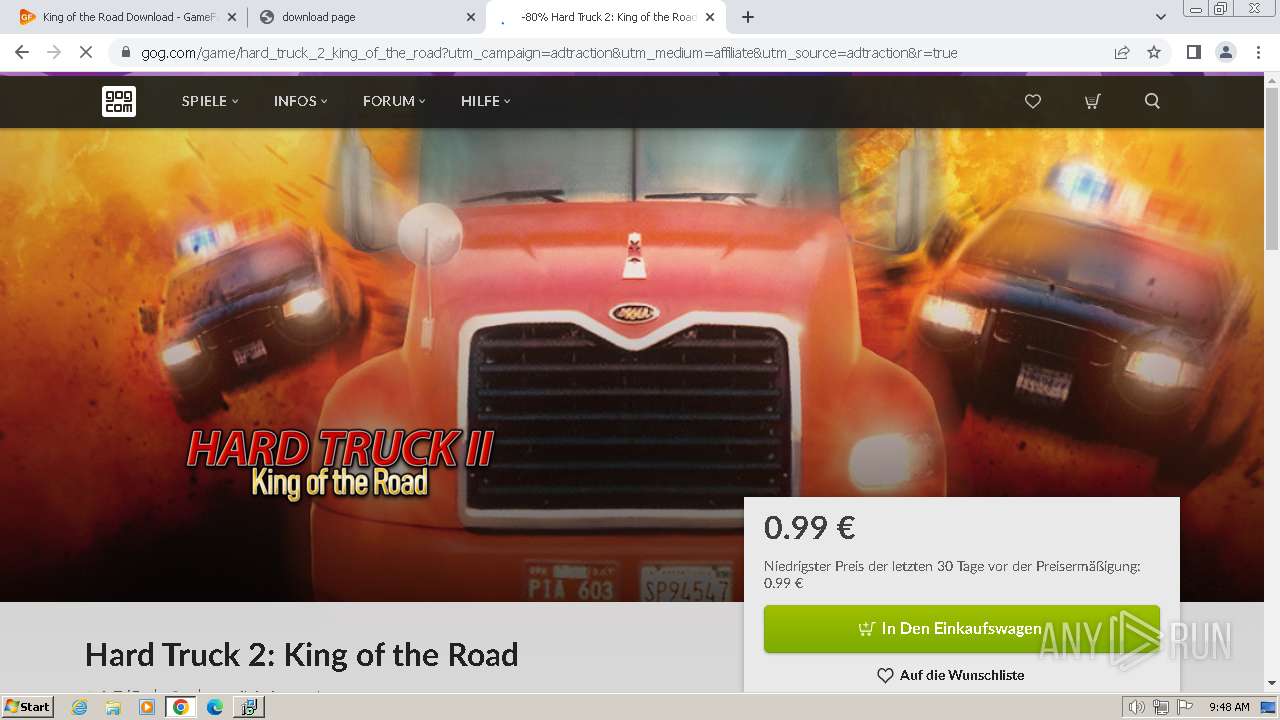
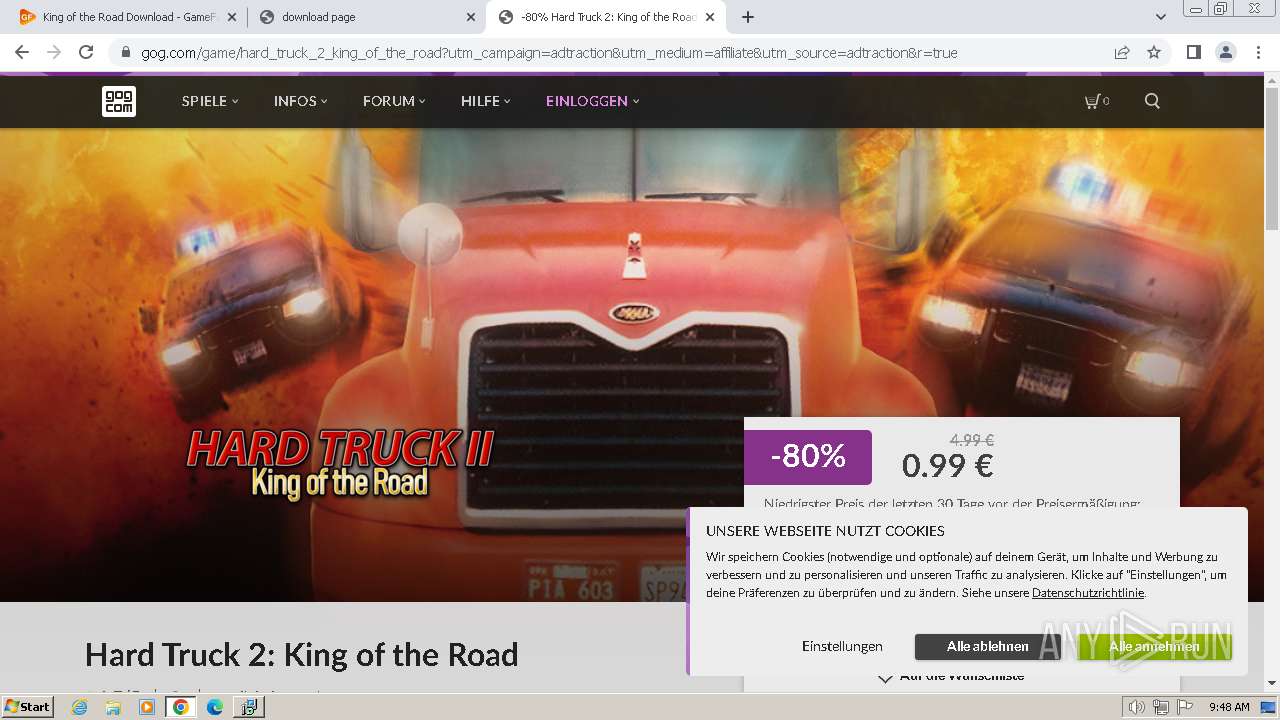
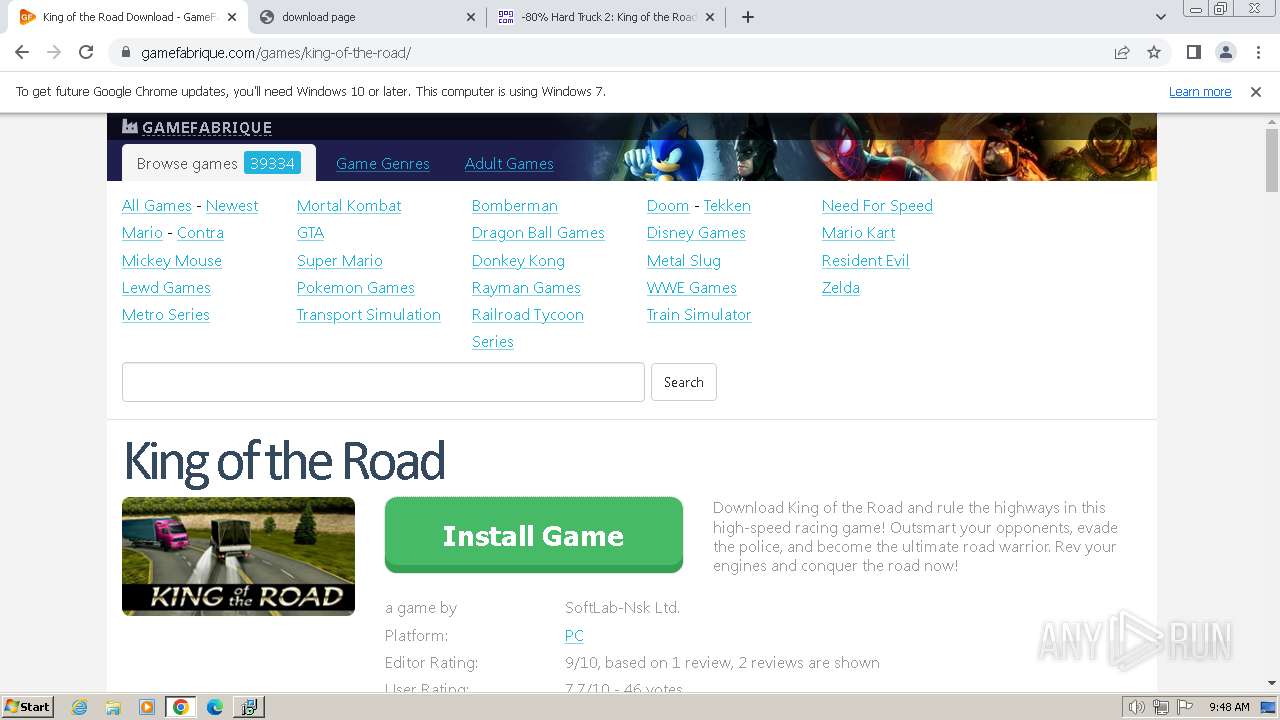
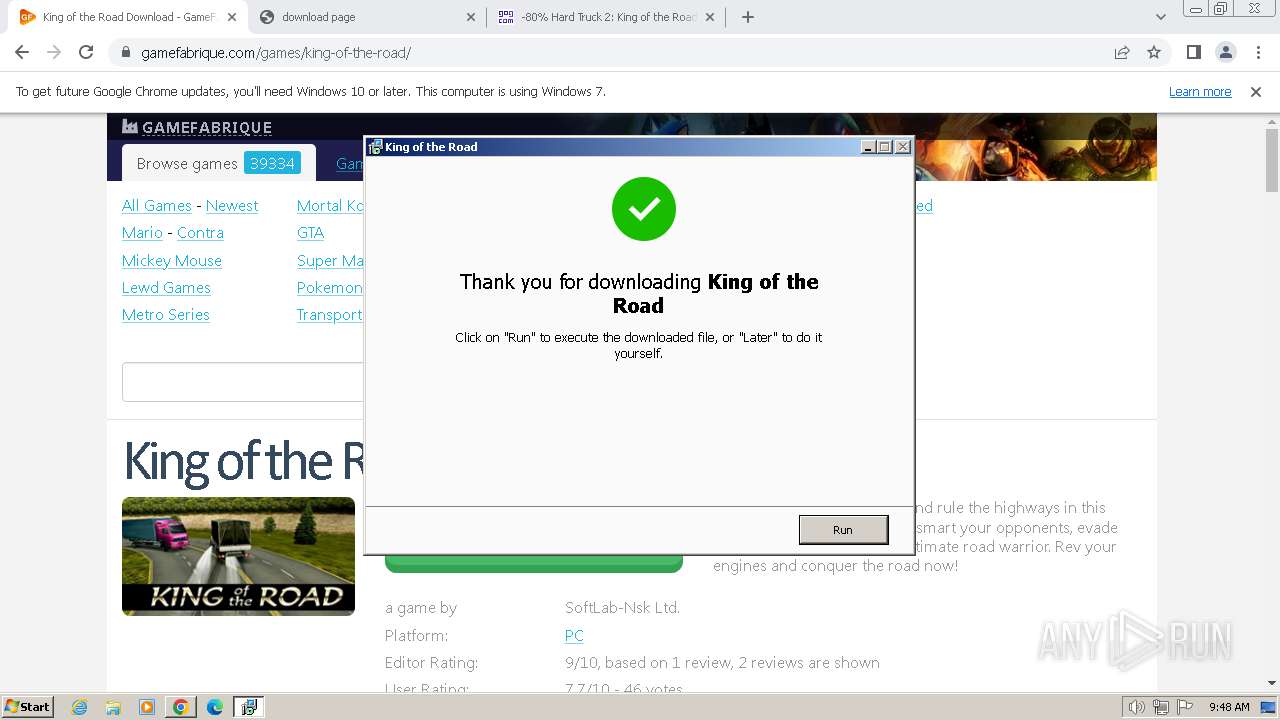
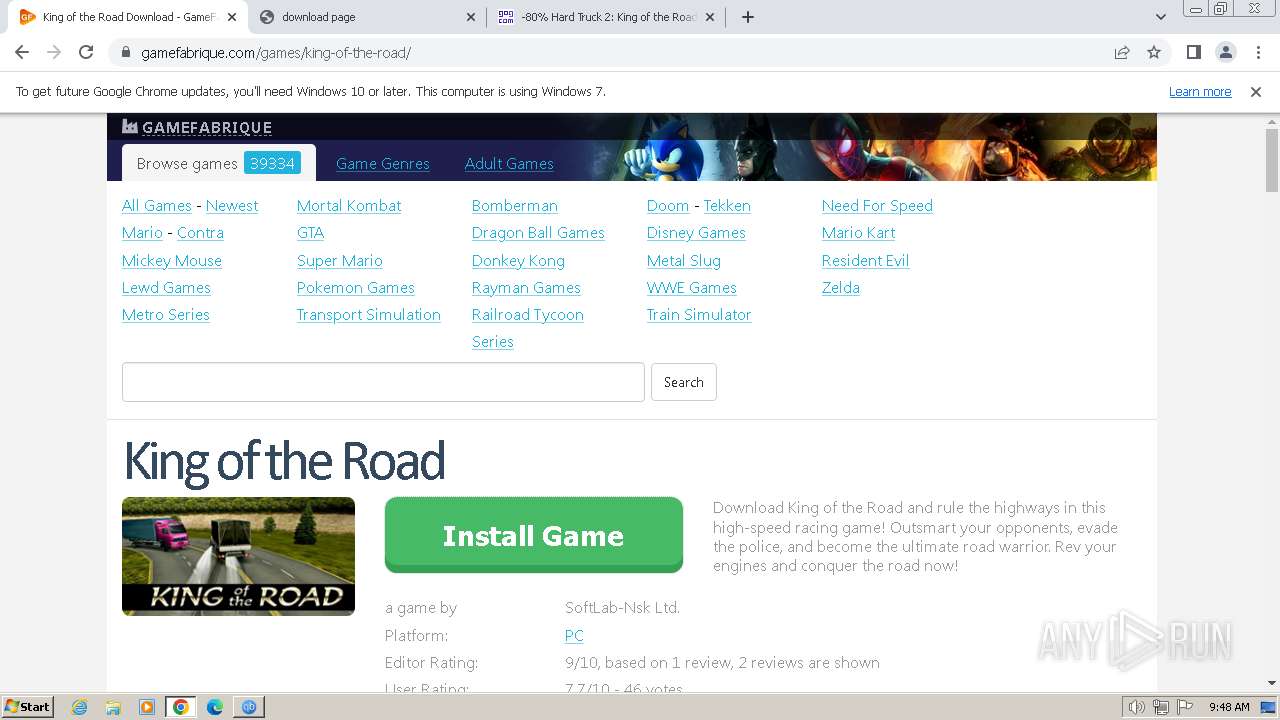
| URL: | https://gamefabrique.com |
| Full analysis: | https://app.any.run/tasks/a92bda4a-80c6-42e3-9233-bd6f923995c3 |
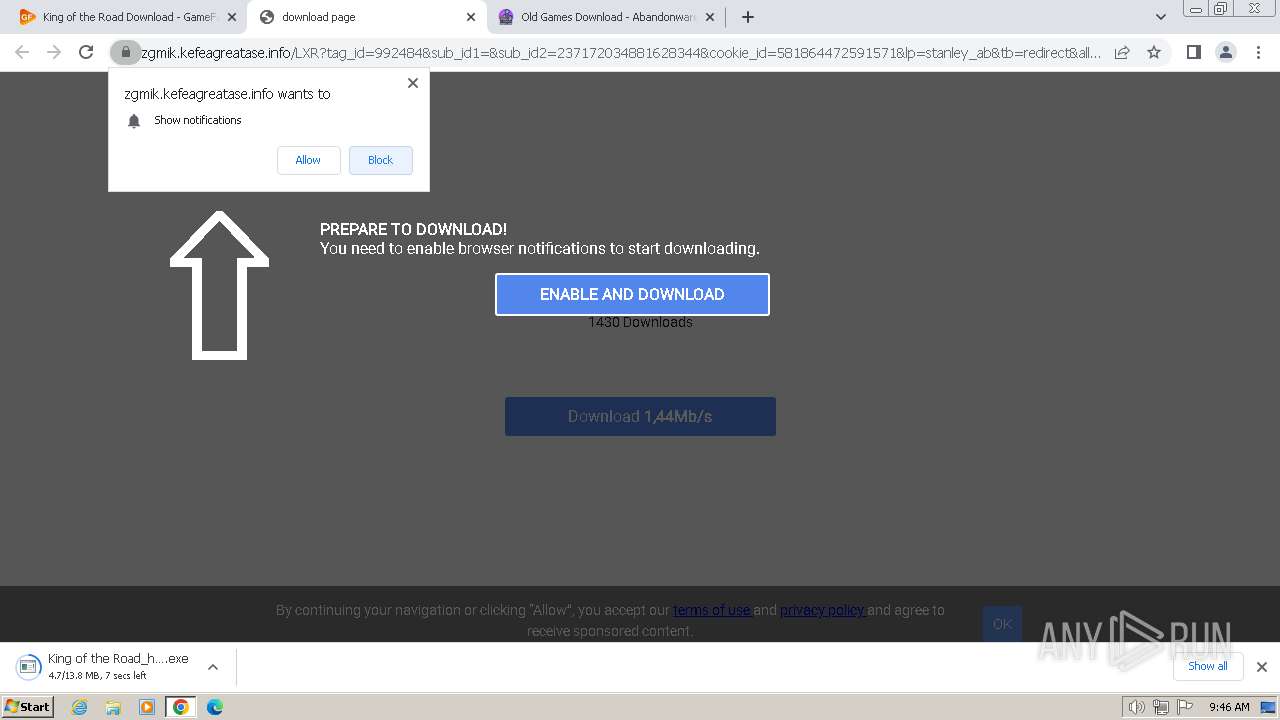
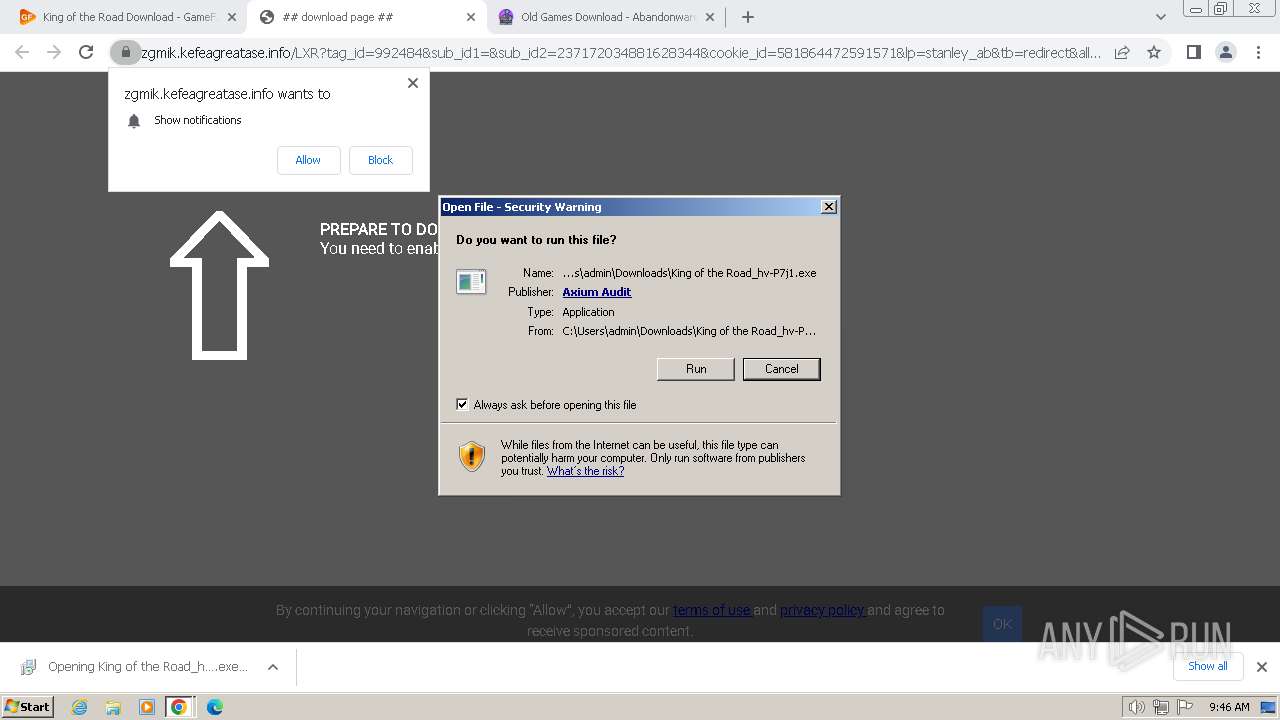
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2024, 09:45:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 776F49F8C74591E829C97D4EF4854895 |
| SHA1: | 4CDD0F02A5C8C2549BA7EA55C6C5078ACD681F00 |
| SHA256: | 9DFEE4B847E05C3E1753E1EB41C1BE7A995BFC82A106807D65EFEB43AA20DF2D |
| SSDEEP: | 3:N8l0XMUhGT:22XMPT |
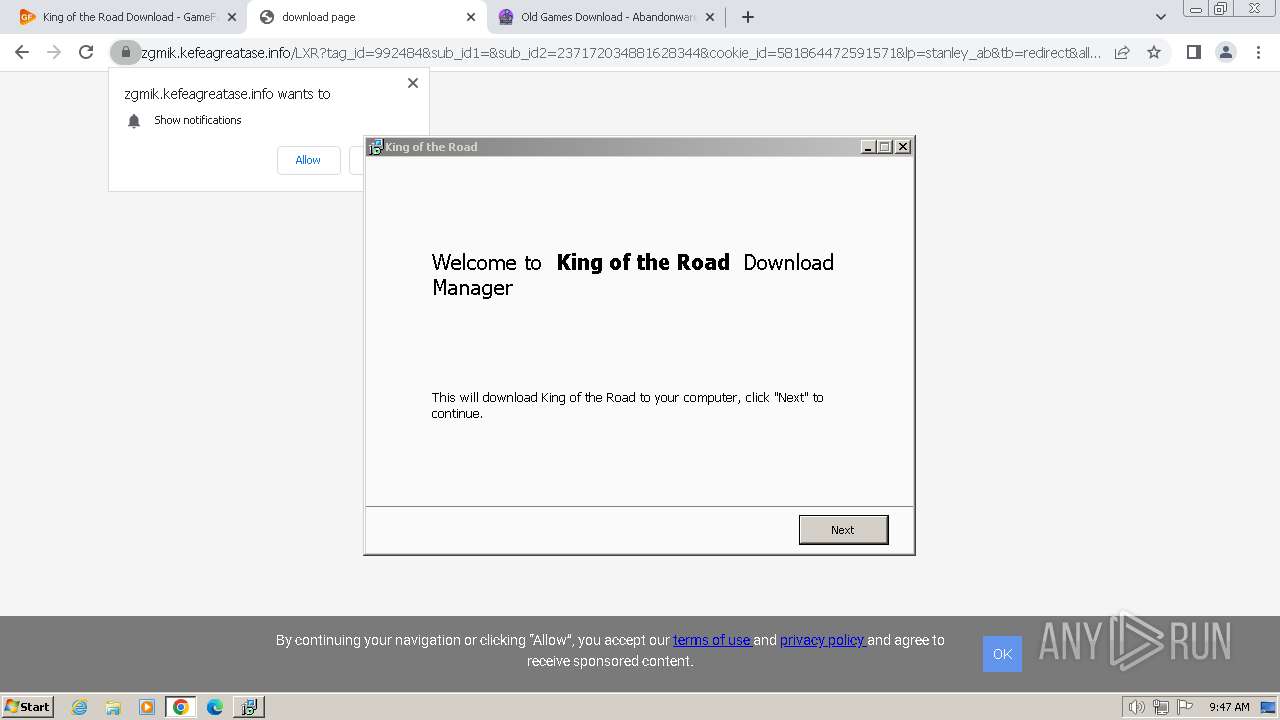
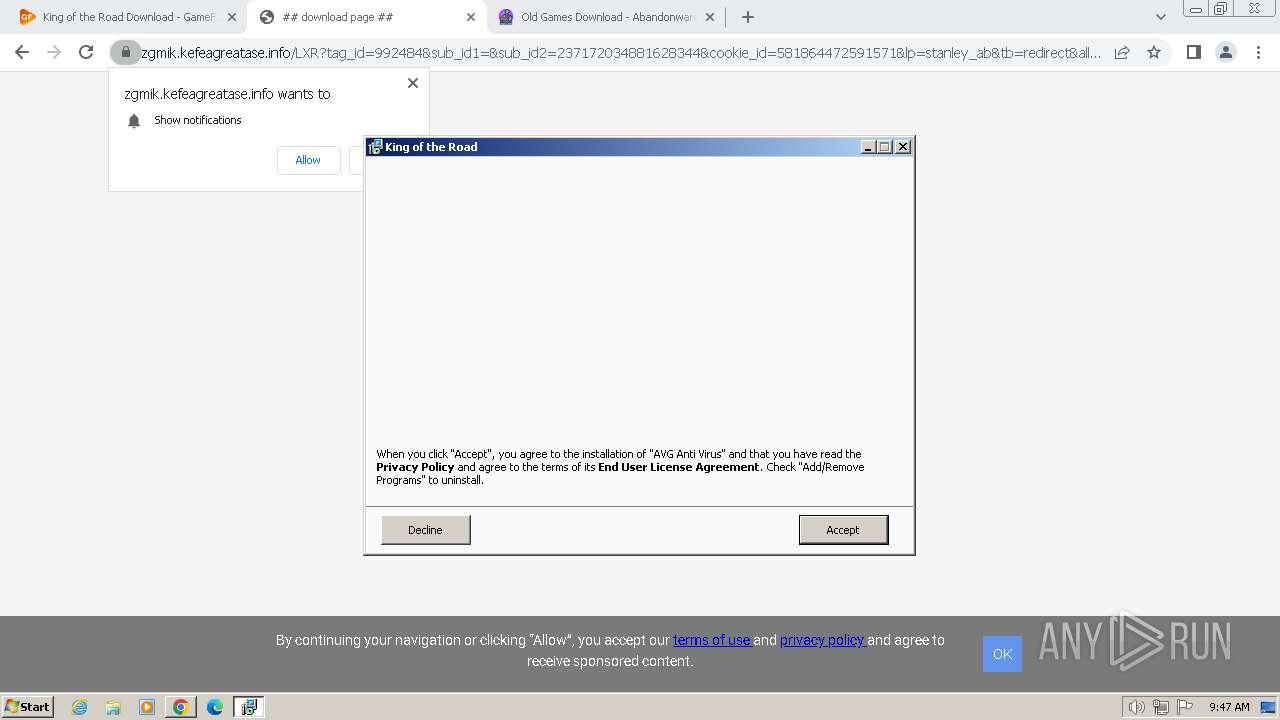
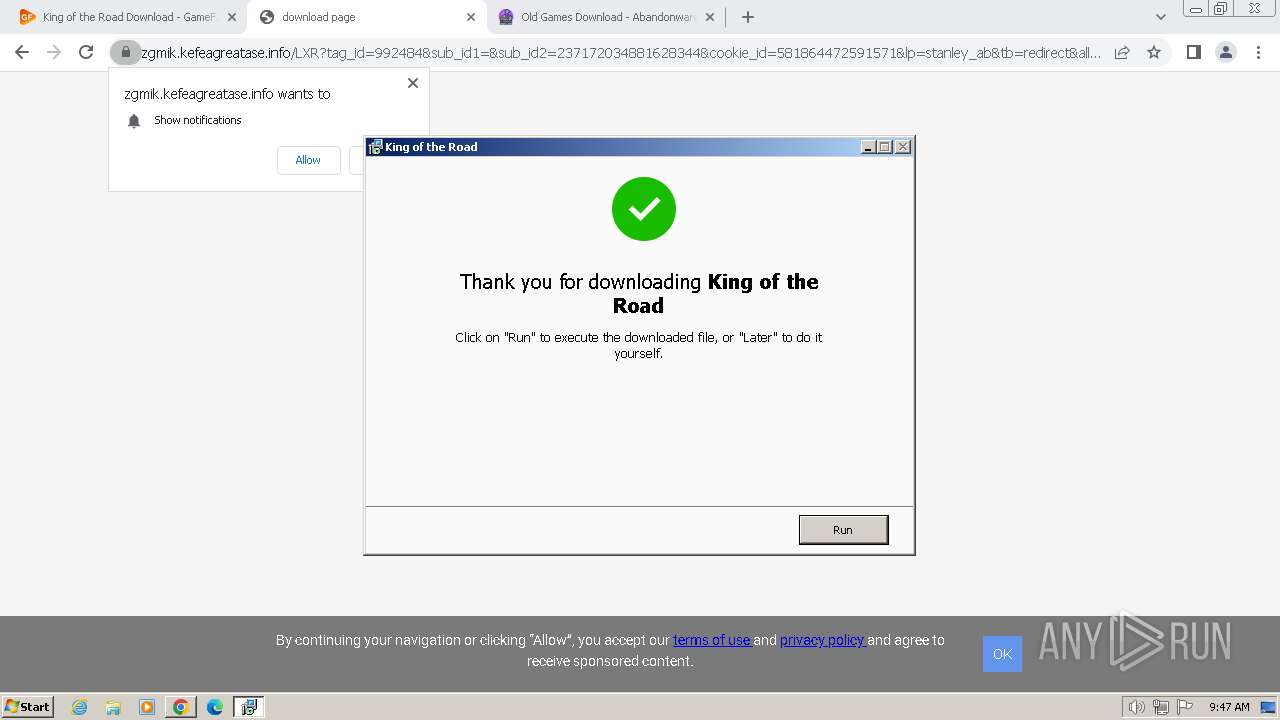
MALICIOUS
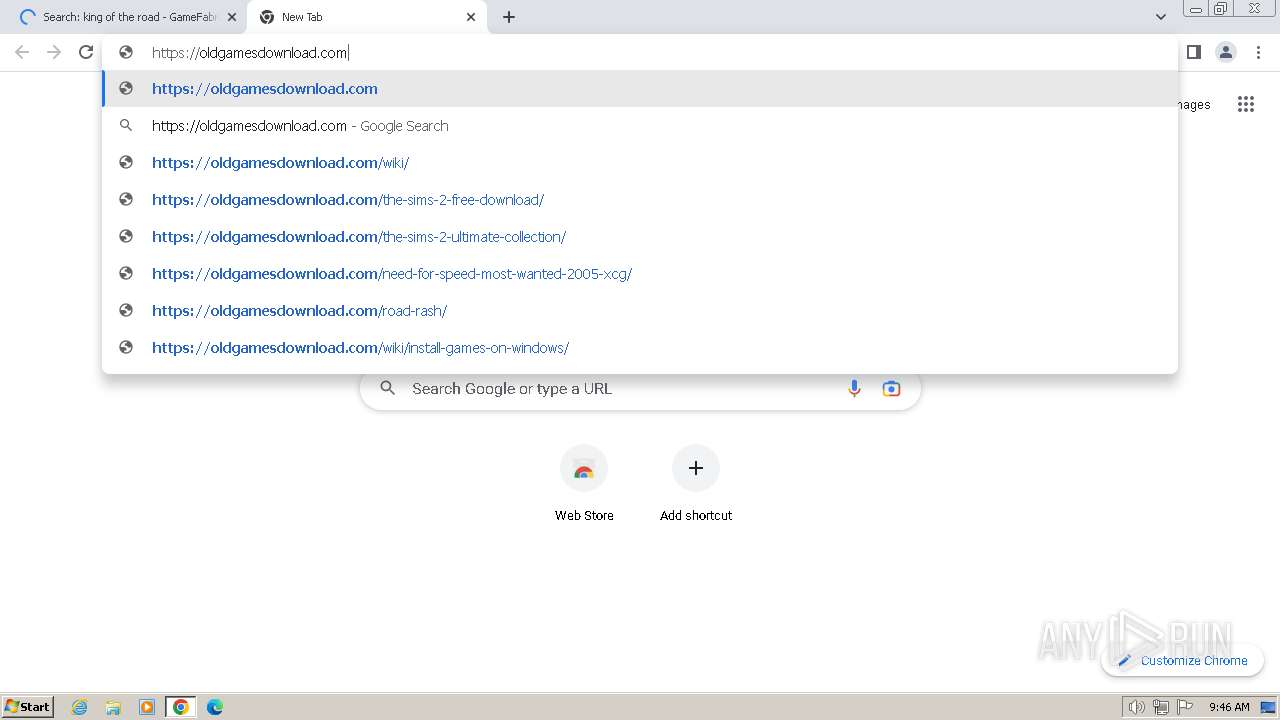
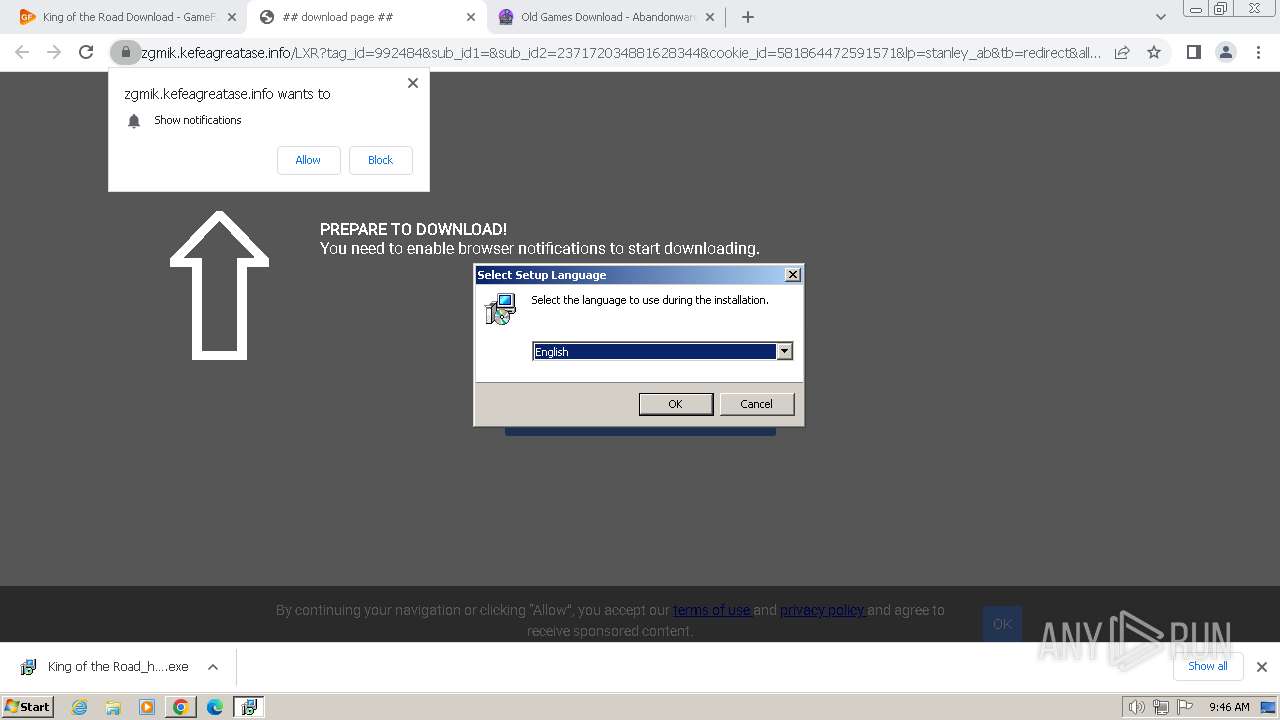
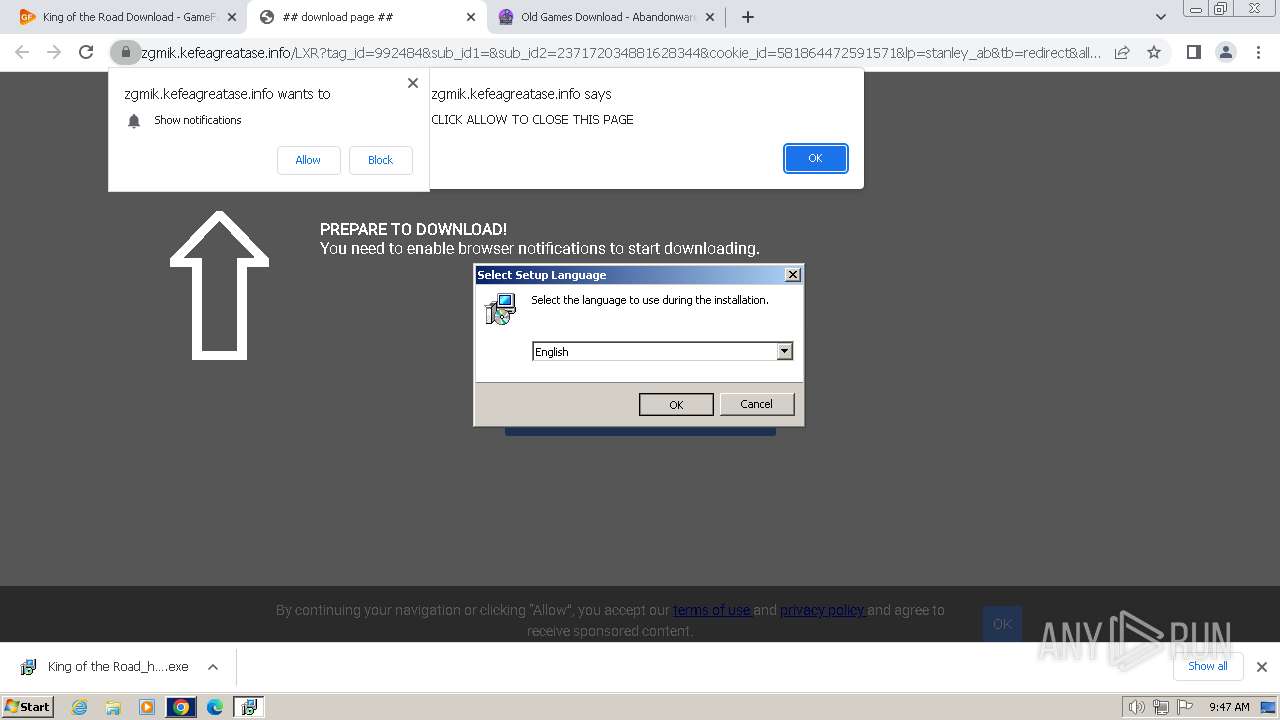
Drops the executable file immediately after the start
- King of the Road_hv-P7j1.exe (PID: 3704)
- King of the Road_hv-P7j1.exe (PID: 2668)
- King of the Road_hv-P7j1.tmp (PID: 844)
- avg_antivirus_free_setup.exe (PID: 2508)
- avg_antivirus_free_online_setup.exe (PID: 1504)
- icarus.exe (PID: 1576)
- icarus.exe (PID: 3216)
Creates a writable file in the system directory
- icarus.exe (PID: 3216)
SUSPICIOUS
Executable content was dropped or overwritten
- King of the Road_hv-P7j1.exe (PID: 3704)
- King of the Road_hv-P7j1.exe (PID: 2668)
- King of the Road_hv-P7j1.tmp (PID: 844)
- avg_antivirus_free_setup.exe (PID: 2508)
- avg_antivirus_free_online_setup.exe (PID: 1504)
- icarus.exe (PID: 1576)
- icarus.exe (PID: 3216)
Reads the Windows owner or organization settings
- King of the Road_hv-P7j1.tmp (PID: 844)
Reads the Internet Settings
- King of the Road_hv-P7j1.tmp (PID: 844)
Reads settings of System Certificates
- King of the Road_hv-P7j1.tmp (PID: 844)
- avg_antivirus_free_setup.exe (PID: 2508)
- avg_antivirus_free_online_setup.exe (PID: 1504)
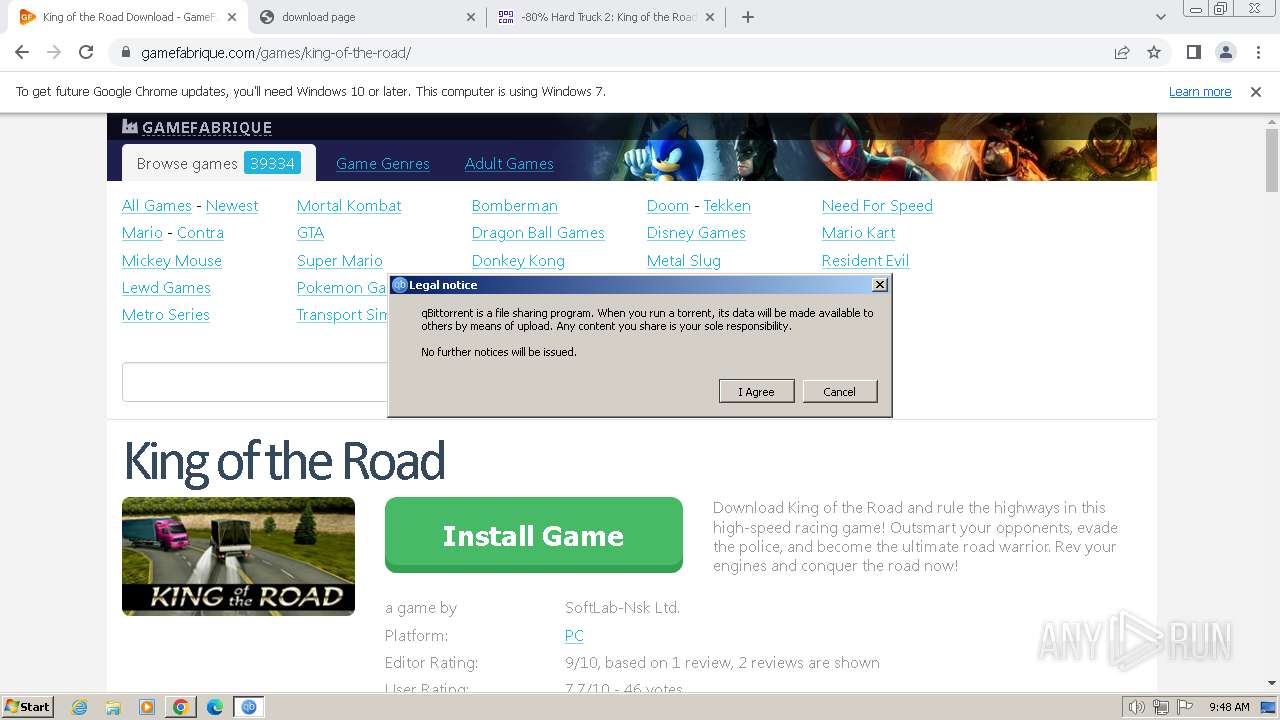
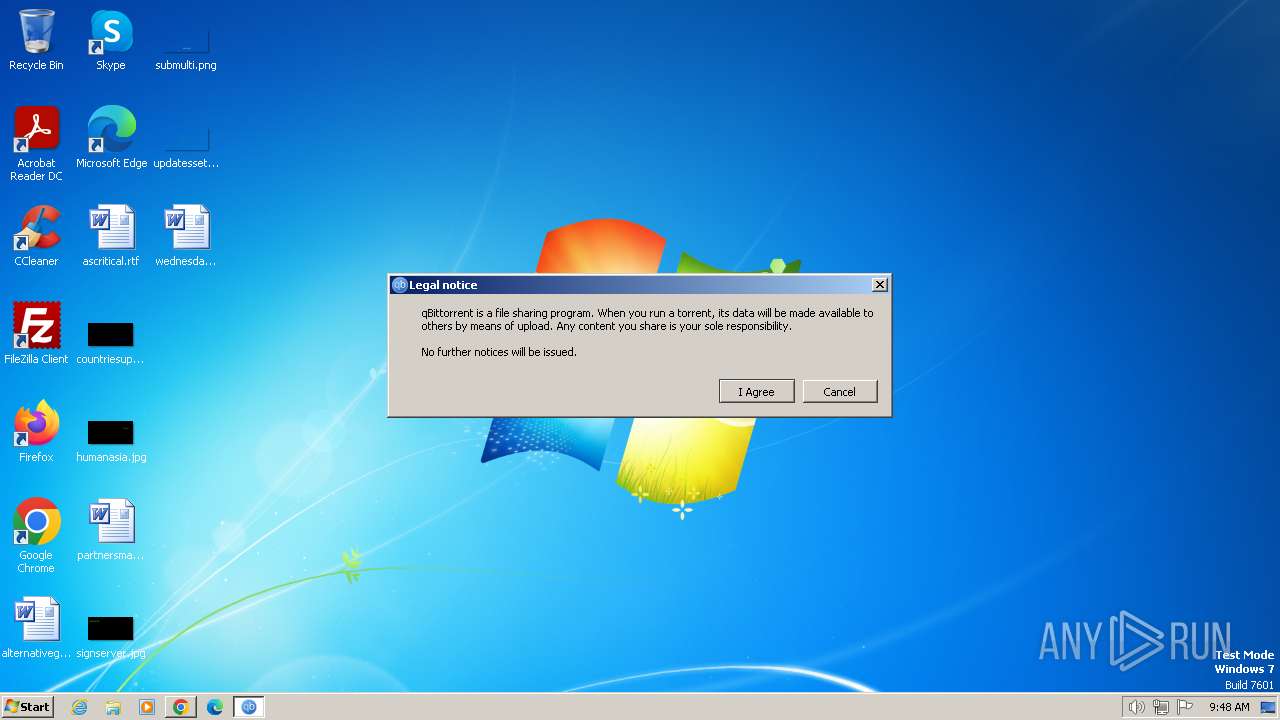
- qbittorrent.exe (PID: 5792)
Reads security settings of Internet Explorer
- King of the Road_hv-P7j1.tmp (PID: 844)
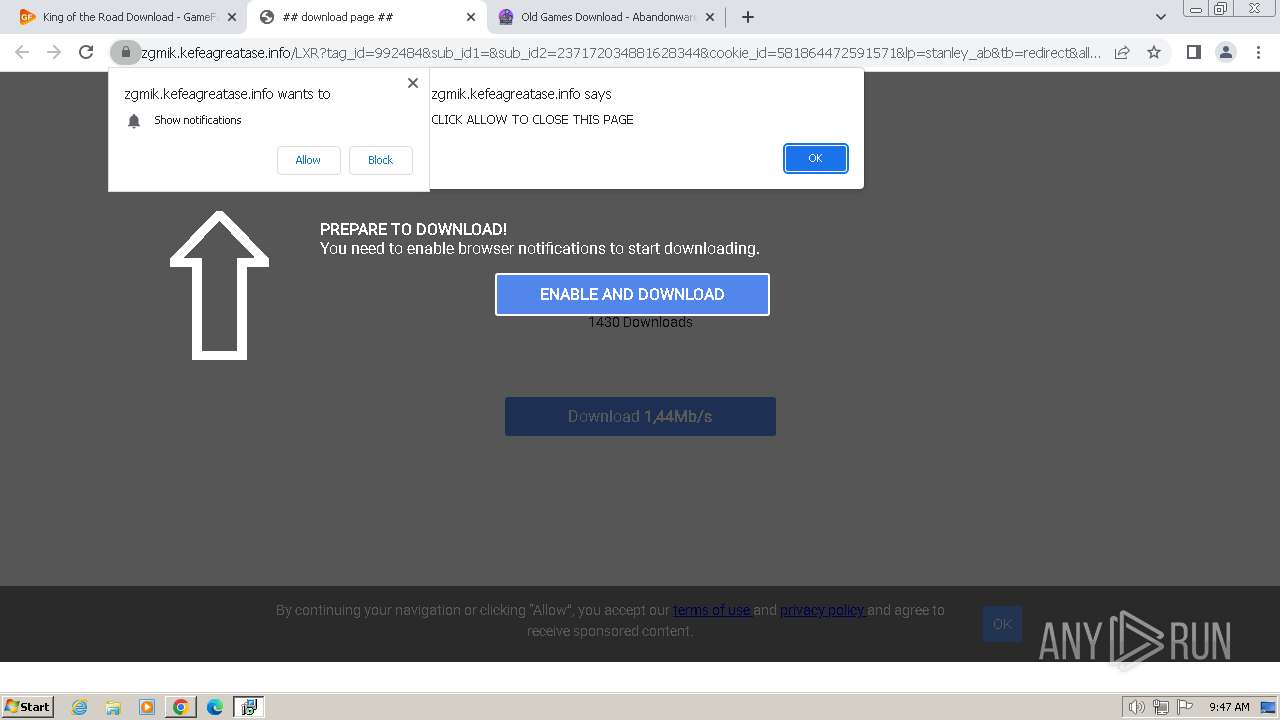
Starts itself from another location
- icarus.exe (PID: 1576)
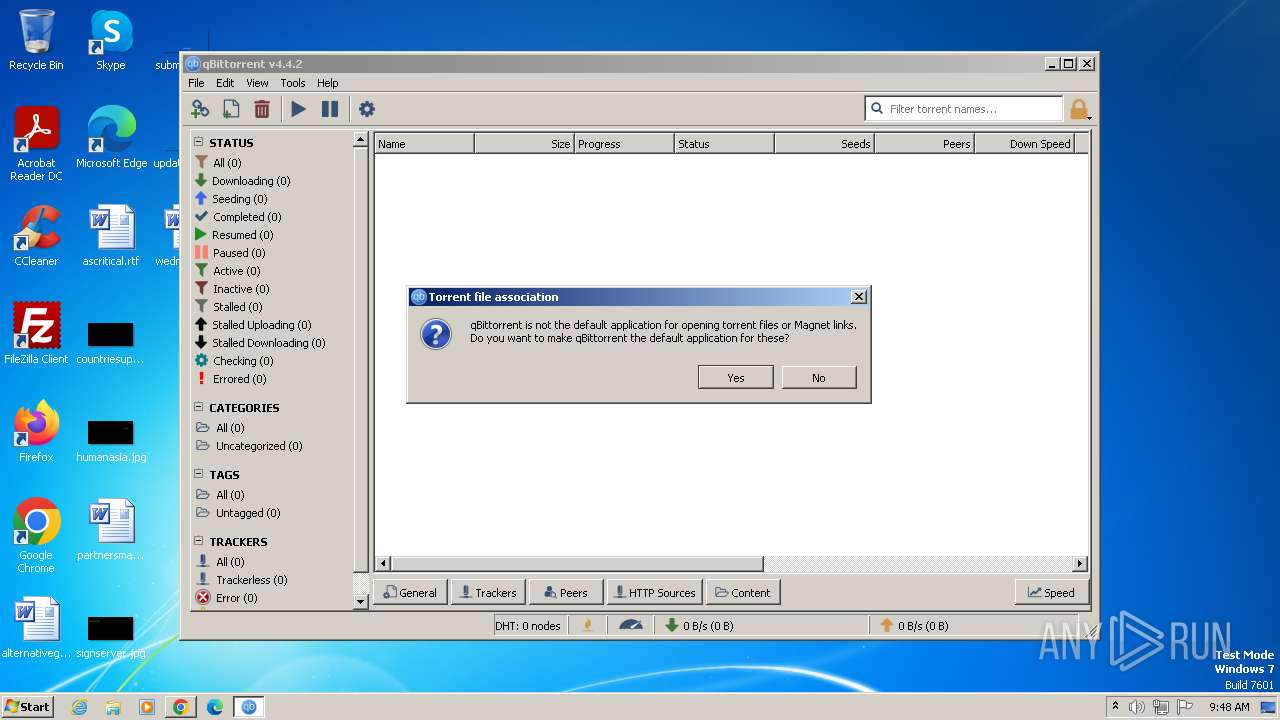
Uses NETSH.EXE to add a firewall rule or allowed programs
- King of the Road_hv-P7j1.tmp (PID: 844)
Process drops legitimate windows executable
- icarus.exe (PID: 3216)
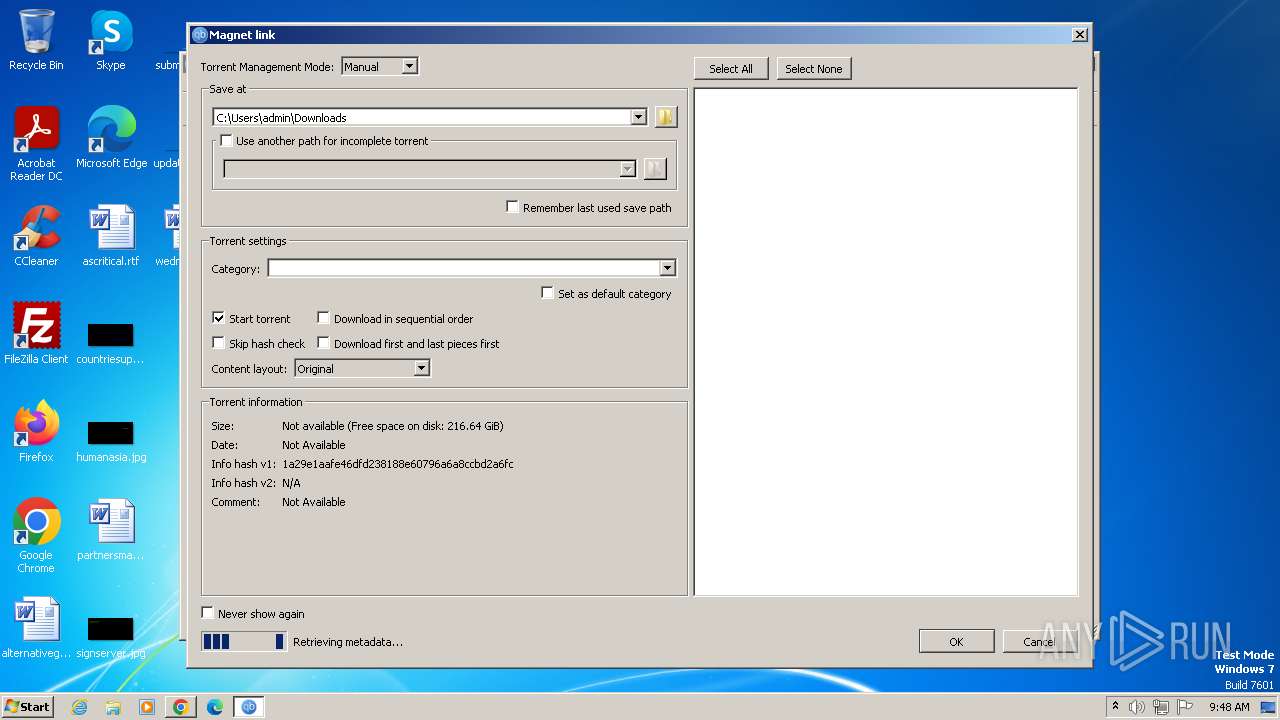
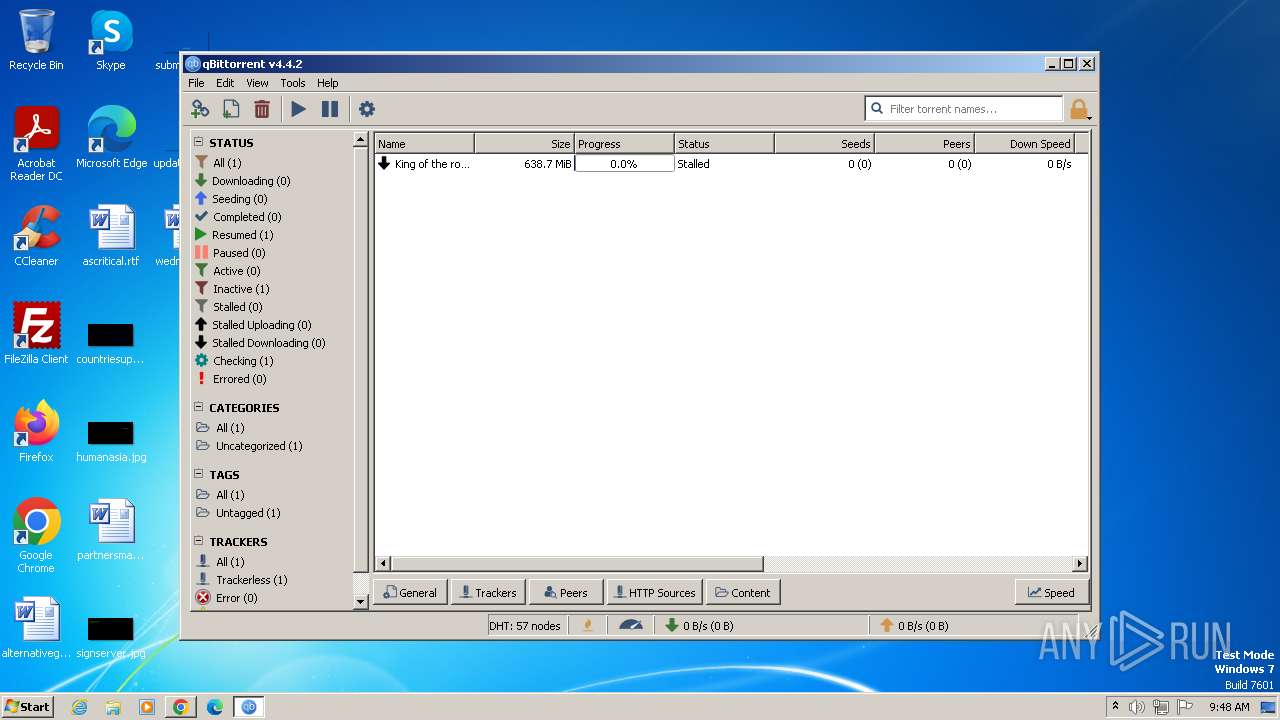
Connects to unusual port
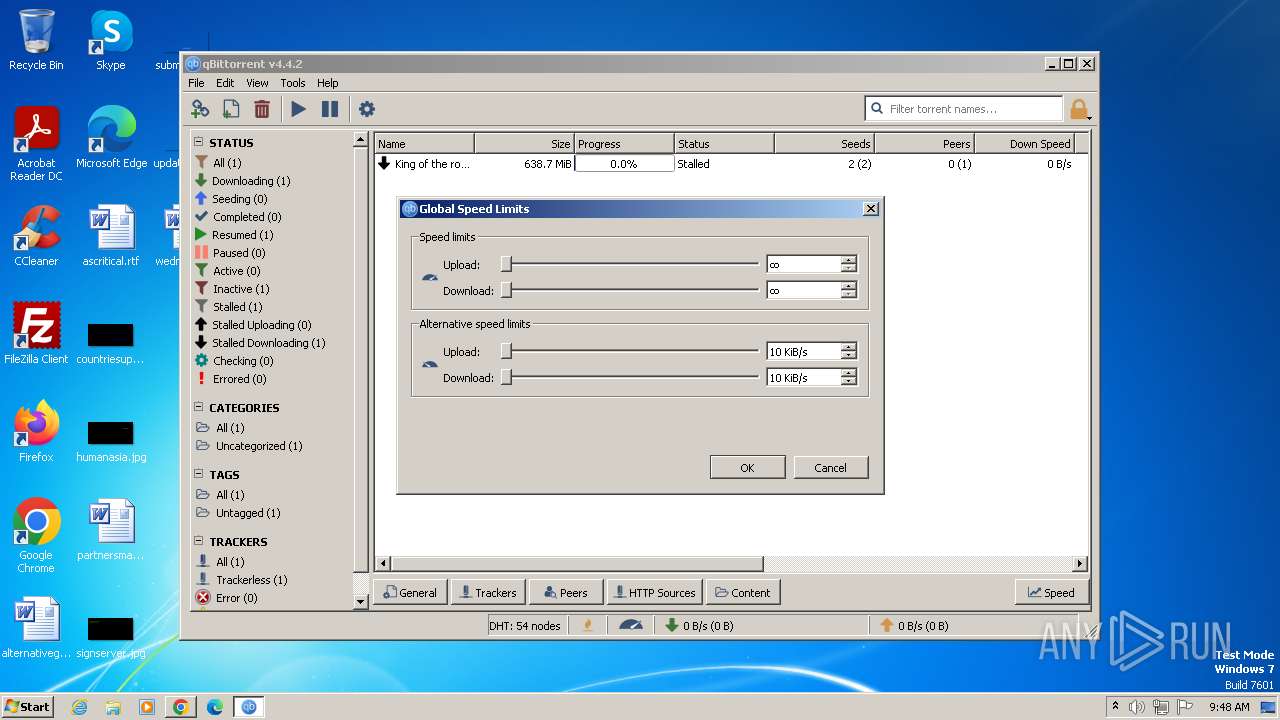
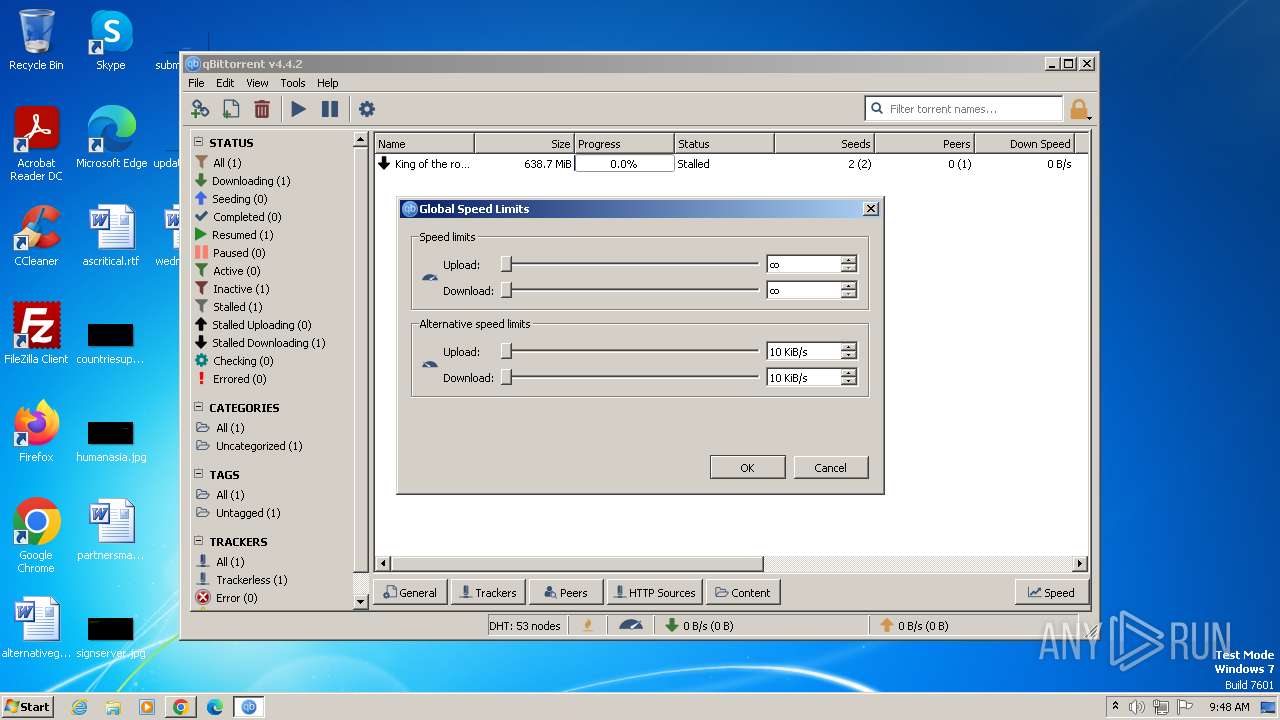
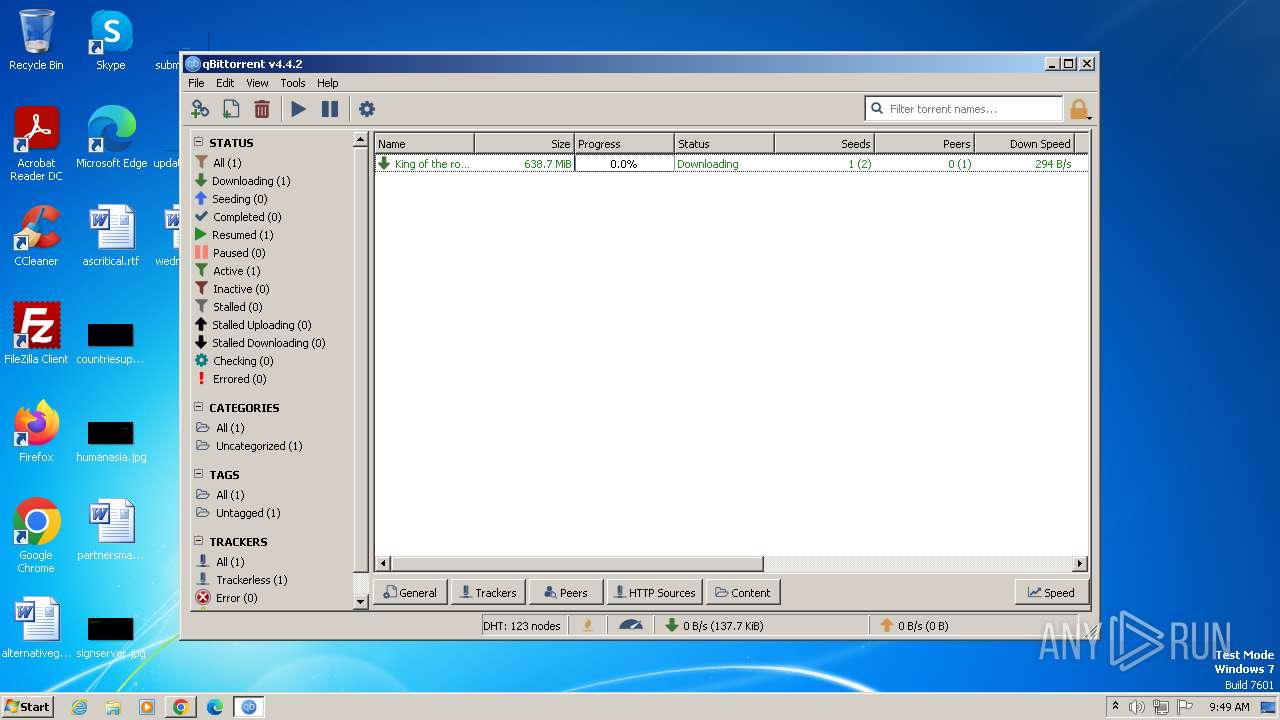
- qbittorrent.exe (PID: 5792)
The process creates files with name similar to system file names
- icarus.exe (PID: 3216)
The process drops C-runtime libraries
- icarus.exe (PID: 3216)
The process verifies whether the antivirus software is installed
- icarus.exe (PID: 3216)
INFO
Drops the executable file immediately after the start
- chrome.exe (PID: 3864)
- chrome.exe (PID: 1492)
Checks supported languages
- King of the Road_hv-P7j1.exe (PID: 3704)
- King of the Road_hv-P7j1.tmp (PID: 752)
- King of the Road_hv-P7j1.exe (PID: 2668)
- King of the Road_hv-P7j1.tmp (PID: 844)
- avg_antivirus_free_setup.exe (PID: 2508)
- avg_antivirus_free_online_setup.exe (PID: 1504)
- icarus.exe (PID: 1576)
- icarus.exe (PID: 3216)
- icarus.exe (PID: 1040)
- qbittorrent.exe (PID: 5792)
The process uses the downloaded file
- chrome.exe (PID: 3864)
- chrome.exe (PID: 3040)
Create files in a temporary directory
- King of the Road_hv-P7j1.exe (PID: 3704)
- King of the Road_hv-P7j1.exe (PID: 2668)
- King of the Road_hv-P7j1.tmp (PID: 844)
- avg_antivirus_free_online_setup.exe (PID: 1504)
- icarus.exe (PID: 1576)
- icarus.exe (PID: 1040)
- icarus.exe (PID: 3216)
Executable content was dropped or overwritten
- chrome.exe (PID: 3864)
Reads the computer name
- King of the Road_hv-P7j1.tmp (PID: 752)
- King of the Road_hv-P7j1.tmp (PID: 844)
- avg_antivirus_free_setup.exe (PID: 2508)
- avg_antivirus_free_online_setup.exe (PID: 1504)
- icarus.exe (PID: 1576)
- icarus.exe (PID: 1040)
- icarus.exe (PID: 3216)
- qbittorrent.exe (PID: 5792)
Application launched itself
- chrome.exe (PID: 3864)
Reads the software policy settings
- King of the Road_hv-P7j1.tmp (PID: 844)
- avg_antivirus_free_setup.exe (PID: 2508)
- avg_antivirus_free_online_setup.exe (PID: 1504)
Reads the machine GUID from the registry
- King of the Road_hv-P7j1.tmp (PID: 844)
- avg_antivirus_free_setup.exe (PID: 2508)
- avg_antivirus_free_online_setup.exe (PID: 1504)
- icarus.exe (PID: 1576)
- icarus.exe (PID: 1040)
- icarus.exe (PID: 3216)
- qbittorrent.exe (PID: 5792)
Creates files in the program directory
- avg_antivirus_free_online_setup.exe (PID: 1504)
- icarus.exe (PID: 1576)
- icarus.exe (PID: 3216)
Dropped object may contain TOR URL's
- icarus.exe (PID: 1576)
- icarus.exe (PID: 3216)
Reads CPU info
- icarus.exe (PID: 1576)
- icarus.exe (PID: 1040)
- icarus.exe (PID: 3216)
Reads Environment values
- icarus.exe (PID: 3216)
Creates files or folders in the user directory
- qbittorrent.exe (PID: 5792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
147
Monitored processes
101
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=44 --mojo-platform-channel-handle=5408 --field-trial-handle=1144,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=45 --mojo-platform-channel-handle=5704 --field-trial-handle=1144,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3512 --field-trial-handle=1144,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 712 | "netsh" firewall add allowedprogramC:\Users\admin\AppData\Local\Temp\is-PKO0D.tmp\qbittorrent.exe "qBittorrent" ENABLE | C:\Windows\System32\netsh.exe | — | King of the Road_hv-P7j1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3320 --field-trial-handle=1144,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 752 | "C:\Users\admin\AppData\Local\Temp\is-VAN97.tmp\King of the Road_hv-P7j1.tmp" /SL5="$220186,13603942,780800,C:\Users\admin\Downloads\King of the Road_hv-P7j1.exe" | C:\Users\admin\AppData\Local\Temp\is-VAN97.tmp\King of the Road_hv-P7j1.tmp | — | King of the Road_hv-P7j1.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --mojo-platform-channel-handle=756 --field-trial-handle=1144,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=54 --mojo-platform-channel-handle=6404 --field-trial-handle=1144,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 844 | "C:\Users\admin\AppData\Local\Temp\is-V1BE4.tmp\King of the Road_hv-P7j1.tmp" /SL5="$2701A6,13603942,780800,C:\Users\admin\Downloads\King of the Road_hv-P7j1.exe" /SPAWNWND=$D0148 /NOTIFYWND=$220186 | C:\Users\admin\AppData\Local\Temp\is-V1BE4.tmp\King of the Road_hv-P7j1.tmp | King of the Road_hv-P7j1.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --mojo-platform-channel-handle=5492 --field-trial-handle=1144,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
38 717
Read events
38 343
Write events
359
Delete events
15
Modification events
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
225
Suspicious files
206
Text files
178
Unknown types
71
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f0e8.TMP | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17f107.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17faea.TMP | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dc0a351b-3634-41ea-ba06-a1ec294c9eba.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF180ff9.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
567
DNS requests
607
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3228 | chrome.exe | GET | 200 | 104.18.38.233:80 | http://crt.sectigo.com/SectigoRSADomainValidationSecureServerCA.crt | unknown | binary | 1.52 Kb | unknown |
2508 | avg_antivirus_free_setup.exe | POST | 204 | 34.117.223.223:80 | http://v7event.stats.avast.com/cgi-bin/iavsevents.cgi | unknown | — | — | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/owvudhl2grtijokmm2wvjksj5y_857/efniojlnjndmcbiieegkicadnoecjjef_857_all_acylmrkcyywkykqsgg5pzah5u7ja.crx3 | unknown | binary | 8.72 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 8.72 Kb | unknown |
2508 | avg_antivirus_free_setup.exe | POST | 200 | 142.250.186.142:80 | http://www.google-analytics.com/collect | unknown | image | 35 b | unknown |
3228 | chrome.exe | GET | 200 | 192.124.249.41:80 | http://certificates.godaddy.com/repository/gdig2.crt | unknown | binary | 1.21 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 6.66 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/owvudhl2grtijokmm2wvjksj5y_857/efniojlnjndmcbiieegkicadnoecjjef_857_all_acylmrkcyywkykqsgg5pzah5u7ja.crx3 | unknown | binary | 15.8 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 173 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 259 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3864 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3228 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3228 | chrome.exe | 104.26.3.131:443 | gamefabrique.com | CLOUDFLARENET | US | shared |
3228 | chrome.exe | 142.250.185.232:443 | www.googletagmanager.com | GOOGLE | US | unknown |
3228 | chrome.exe | 104.18.11.207:443 | stackpath.bootstrapcdn.com | CLOUDFLARENET | — | unknown |
3228 | chrome.exe | 216.58.212.170:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 108.156.61.146:443 | d1pdf4c3hchi80.cloudfront.net | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gamefabrique.com |
| whitelisted |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
d1pdf4c3hchi80.cloudfront.net |
| unknown |
www.google-analytics.com |
| whitelisted |
pogothere.xyz |
| unknown |
beitandfalloni.com |
| unknown |
herlittleboywhow.info |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3228 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5792 | qbittorrent.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
5792 | qbittorrent.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT announce_peers request |
Process | Message |
|---|---|
qbittorrent.exe | QObject::startTimer: Timers cannot have negative intervals
|