| URL: | https://gamefabrique.com |
| Full analysis: | https://app.any.run/tasks/52d5d3e3-1490-4de1-b942-cdf8cf6228f0 |
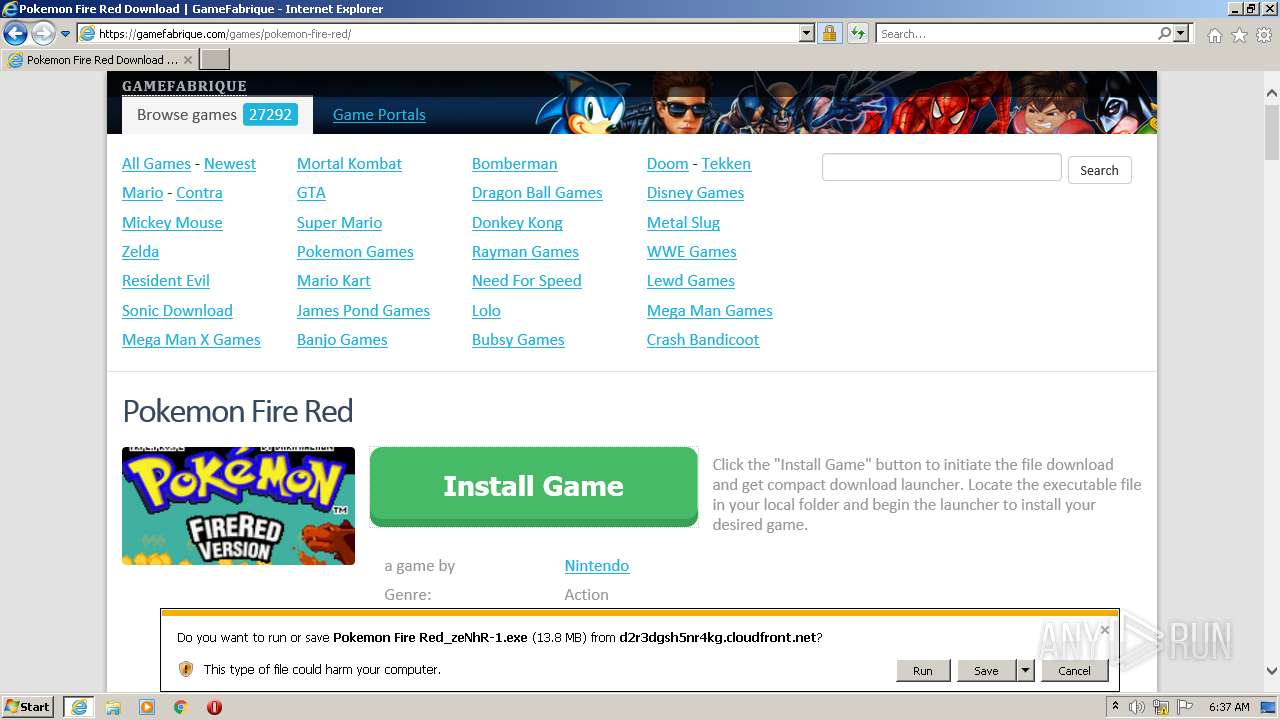
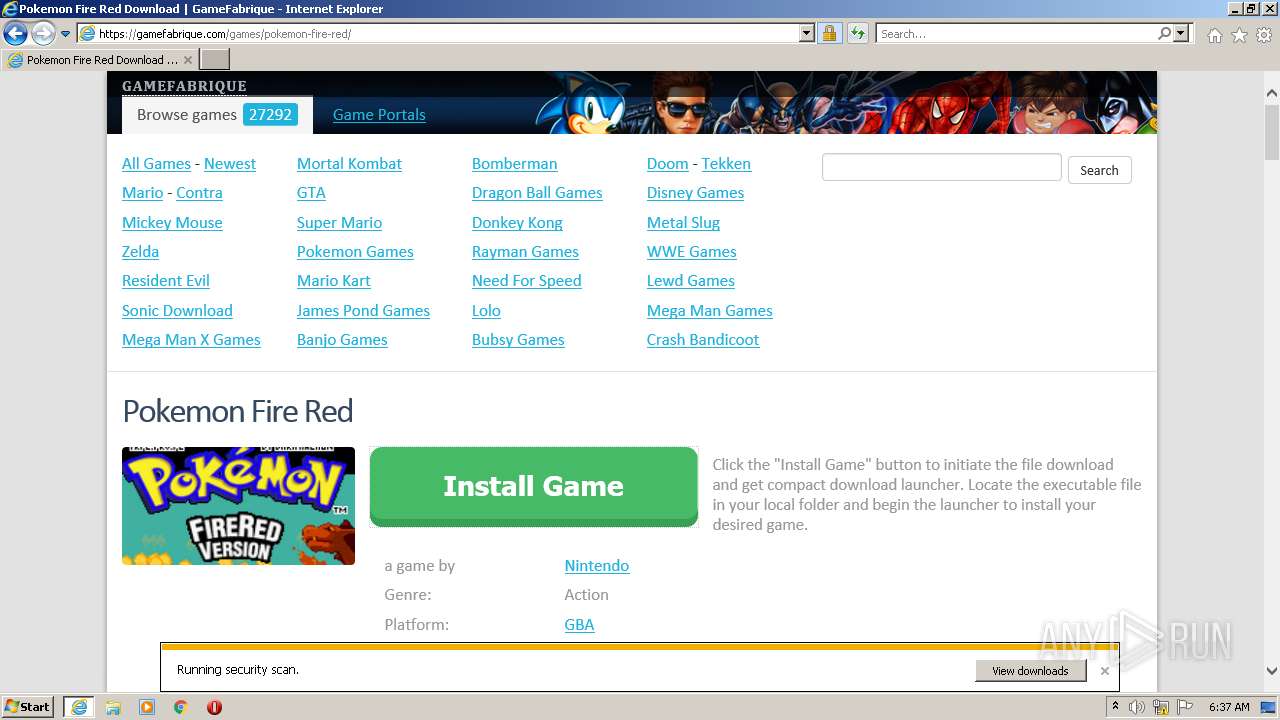
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2022, 05:36:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 776F49F8C74591E829C97D4EF4854895 |
| SHA1: | 4CDD0F02A5C8C2549BA7EA55C6C5078ACD681F00 |
| SHA256: | 9DFEE4B847E05C3E1753E1EB41C1BE7A995BFC82A106807D65EFEB43AA20DF2D |
| SSDEEP: | 3:N8l0XMUhGT:22XMPT |
MALICIOUS
Drops executable file immediately after starts
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 2840)
- Pokemon Fire Red_zeNhR-1.exe (PID: 2036)
Application was dropped or rewritten from another process
- Pokemon Fire Red_zeNhR-1.exe (PID: 2036)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3236)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 2840)
- Pokemon Fire Red_zeNhR-1.exe (PID: 2036)
Drops a file with a compile date too recent
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 2840)
- Pokemon Fire Red_zeNhR-1.exe (PID: 2036)
Checks supported languages
- Pokemon Fire Red_zeNhR-1.exe (PID: 2036)
- Pokemon Fire Red_zeNhR-1.tmp (PID: 2760)
Reads the computer name
- Pokemon Fire Red_zeNhR-1.tmp (PID: 2760)
INFO
Checks supported languages
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3236)
Reads the computer name
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3236)
Changes internet zones settings
- iexplore.exe (PID: 2840)
Application launched itself
- iexplore.exe (PID: 2840)
Checks Windows Trust Settings
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3236)
Reads settings of System Certificates
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3236)
Reads internet explorer settings
- iexplore.exe (PID: 3236)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2840)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2840)
Changes settings of System certificates
- iexplore.exe (PID: 2840)
Creates files in the user directory
- iexplore.exe (PID: 3236)
Application was dropped or rewritten from another process
- Pokemon Fire Red_zeNhR-1.tmp (PID: 2760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2036 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Pokemon Fire Red_zeNhR-1.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Pokemon Fire Red_zeNhR-1.exe | iexplore.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: AKSIUM AUDIT, OOO Download Manager Exit code: 0 Version: 3.334.90 Modules
| |||||||||||||||
| 2760 | "C:\Users\admin\AppData\Local\Temp\is-GJTFL.tmp\Pokemon Fire Red_zeNhR-1.tmp" /SL5="$501E2,13628241,797696,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Pokemon Fire Red_zeNhR-1.exe" | C:\Users\admin\AppData\Local\Temp\is-GJTFL.tmp\Pokemon Fire Red_zeNhR-1.tmp | — | Pokemon Fire Red_zeNhR-1.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://gamefabrique.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2840 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
13 106
Read events
12 960
Write events
138
Delete events
8
Modification events
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30965278 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30965278 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
18
Text files
157
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:5D1DE7BB09F1B36D92D98ED257F9D260 | SHA256:0DF2517AD22D7AF0009EBCD1DF7C74A468AA1C75AE4DC9991BF83BEF2BADDCA5 | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:BF89BE8B029F930414868D4C0E00E5A3 | SHA256:E37657F6E32444FAE752B181357BF37C6FB56AA230B8AB6A89A86A63187CD98F | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:A26978D9F2615325FB2B045C080C9657 | SHA256:F8539E0108A07604E84E1981C07A6DE12589661720624376F0A6DC3A3616535E | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\URPMOZ5U.htm | html | |
MD5:927C5558026F1F3F52723C00C816D254 | SHA256:2BA30296709456EBF8E413C680068DE1742EBB4B2ADFFDD8424A52CD9DAEF907 | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style[1].css | text | |
MD5:C6E3D0C39CC0C23C71DA281721CC0D13 | SHA256:5B223C49C5936FD1F843176295EE183716D195CBC06F3FD8AD5248C2D1578CFF | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:2EAC94298F927B399D52F5180A6B1BB8 | SHA256:D683738C25F5D44D35C2458C7893DC5B6A98861158FC40493CE3621EEB172A27 | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:2E2994B4DA72235815B11DE21A431A92 | SHA256:5E1EB70EEBF0DB9E7B826878BFD0DC5A0E4D55D949B9E848C5D759479D88556F | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1D39E0AFEA82782B1A14DA16A97A132A | binary | |
MD5:07560F0D7067D904571CEE4A0C4A5C2F | SHA256:8949A598D8689EA6EA504F51E6FFAAE6D06D5E1028F1A930470782C51112A387 | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\the-bonfire-2-uncharted-shores[1].png | image | |
MD5:1F940279BE40A9FF2738D7C923E7242E | SHA256:BF5485D011C18FDB5C14EDE253DEBE4F3C97A4C2F04C7D8419EAE8534B6700B1 | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:C0C5FBCCC38C3B047A9922185C40B33B | SHA256:5EEEACA61A509BC2094D661B7813D909682E7B6CF6FF15DA878DE0E66426B5C3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
53
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3236 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDi15VM0BYOewq4TUp6IjEK | US | der | 472 b | whitelisted |
3236 | iexplore.exe | GET | 200 | 18.66.242.62:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3236 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDHeDuP%2BbJl6groO4eS0zlS | US | der | 472 b | whitelisted |
3236 | iexplore.exe | GET | 200 | 108.138.2.195:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3236 | iexplore.exe | GET | 200 | 18.66.137.148:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3236 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3236 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3236 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3236 | iexplore.exe | 89.248.171.137:443 | gamefabrique.com | Quasi Networks LTD. | SC | suspicious |
2840 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2840 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2840 | iexplore.exe | 23.216.77.69:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
3236 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
3236 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3236 | iexplore.exe | 172.217.16.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
— | — | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3236 | iexplore.exe | 104.18.10.207:443 | stackpath.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
— | — | 142.250.186.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gamefabrique.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |