| File name: | succed.solve |
| Full analysis: | https://app.any.run/tasks/475e906c-eca7-4dde-9dc5-3b591a93384c |
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2025, 08:33:09 |
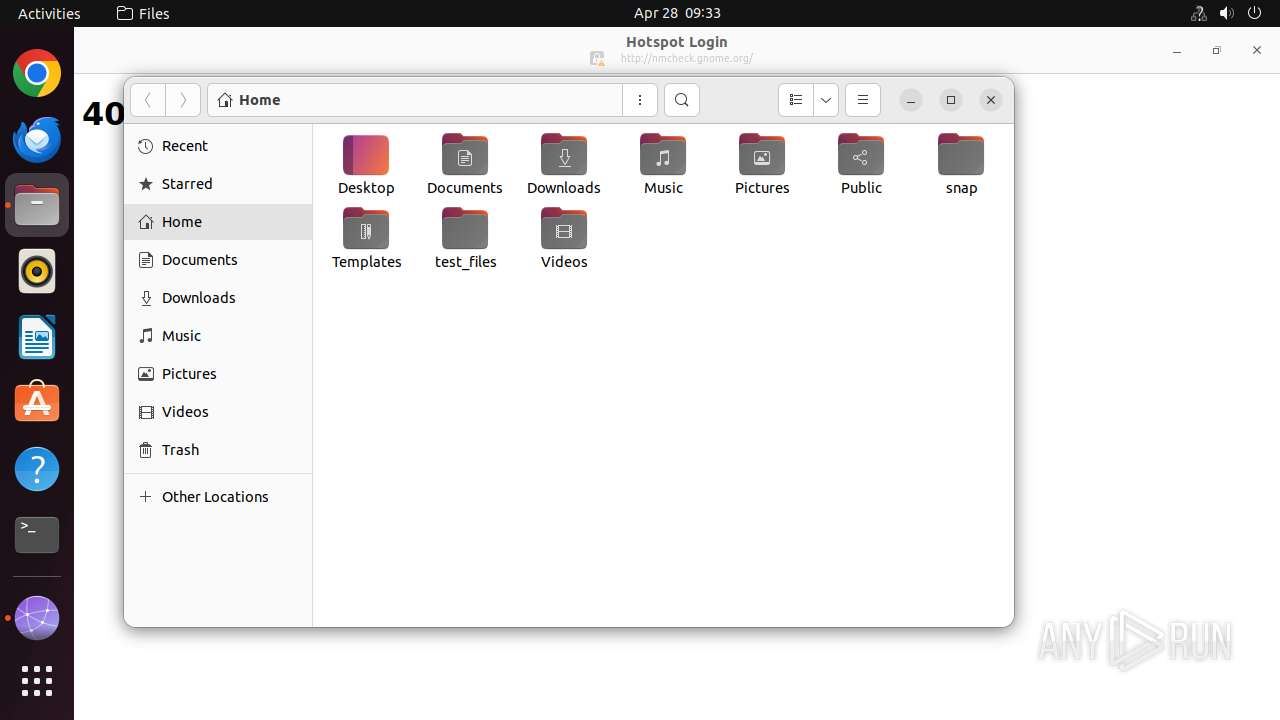
| OS: | Ubuntu 22.04.2 |
| MIME: | application/x-executable |
| File info: | ELF 64-bit LSB executable, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, BuildID[sha1]=a0f2bc1bc15e3770ca2f4b1dfb4d6ecd6863057f, for GNU/Linux 3.2.0, stripped |
| MD5: | 15E6255B0FF428B1410D7459CF5DF2FE |
| SHA1: | B6F5BA0894AF265FC6B0885C48B87EBC76F67C6D |
| SHA256: | 9DE56764CEC9EBC0DF1ADAD83BC0DBA7EE2974EF2E8E8468A93CB6C5BE31F312 |
| SSDEEP: | 768:3Gm1yKi6SqCauuuuuuuuuuuuuuuupBZxJh5RpBZxJh5RHHHHHHHHHHHHHHHXqLti:3H1Lt593 |
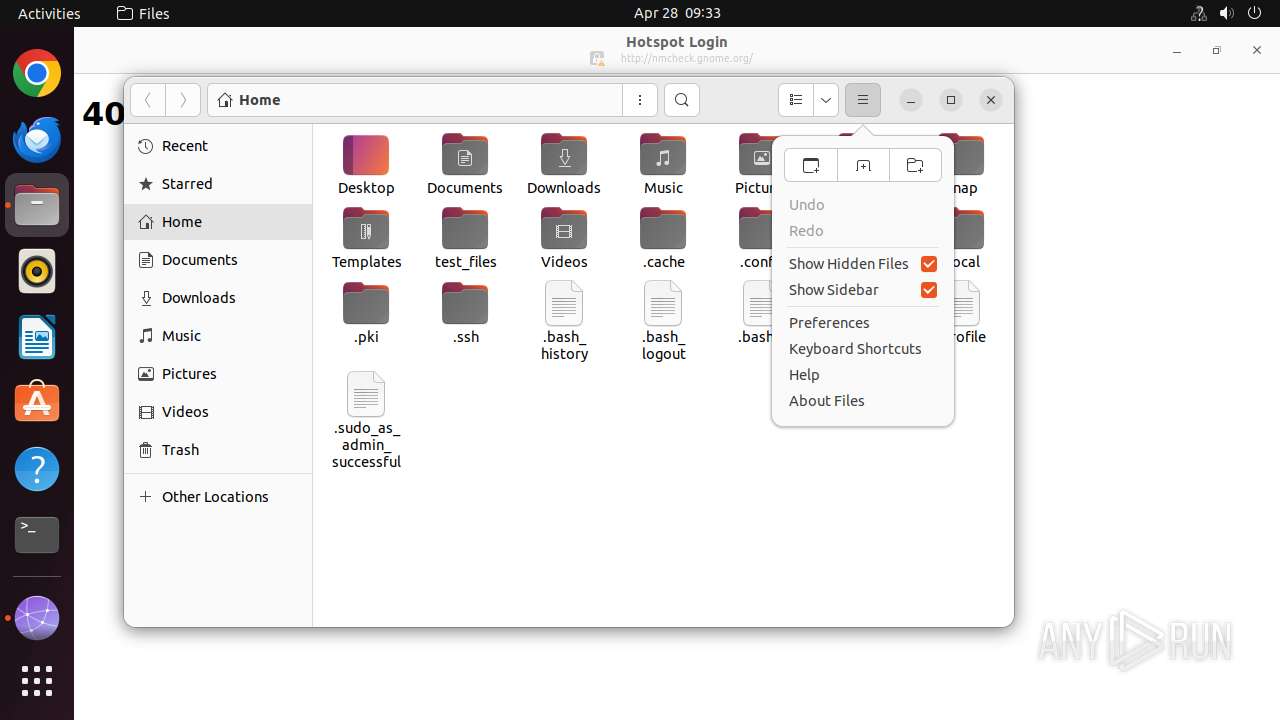
MALICIOUS
No malicious indicators.SUSPICIOUS
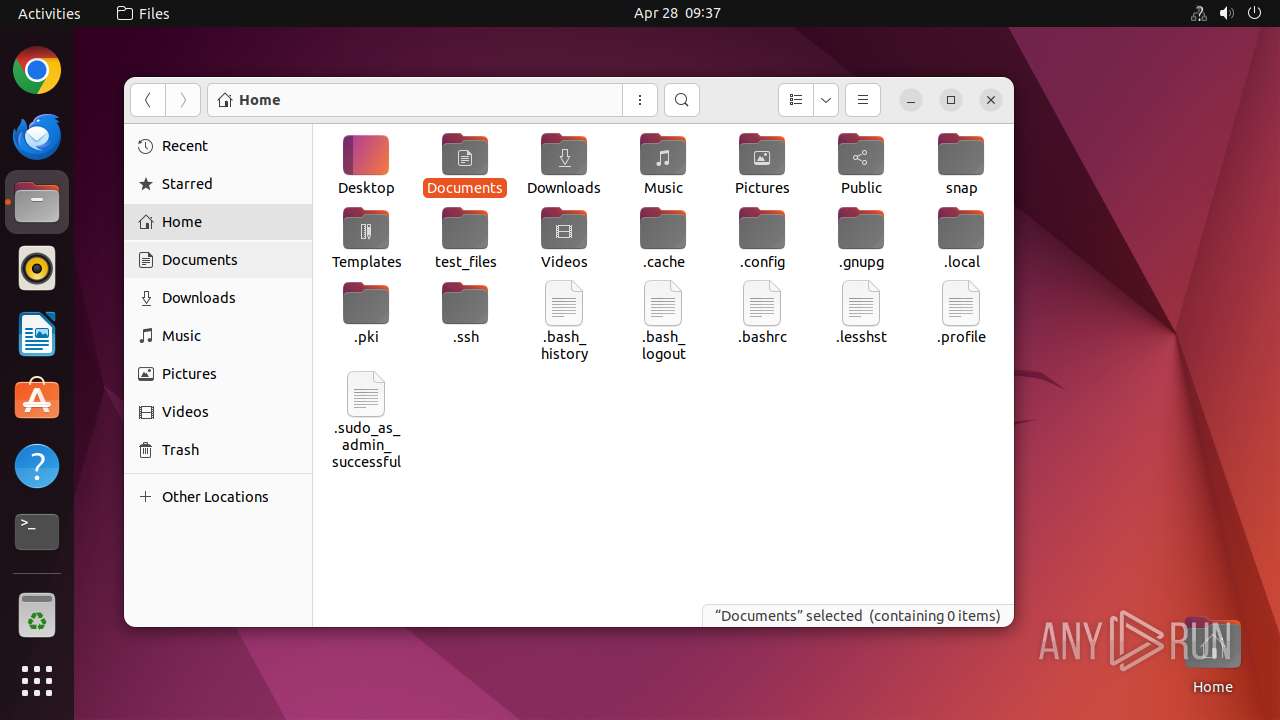
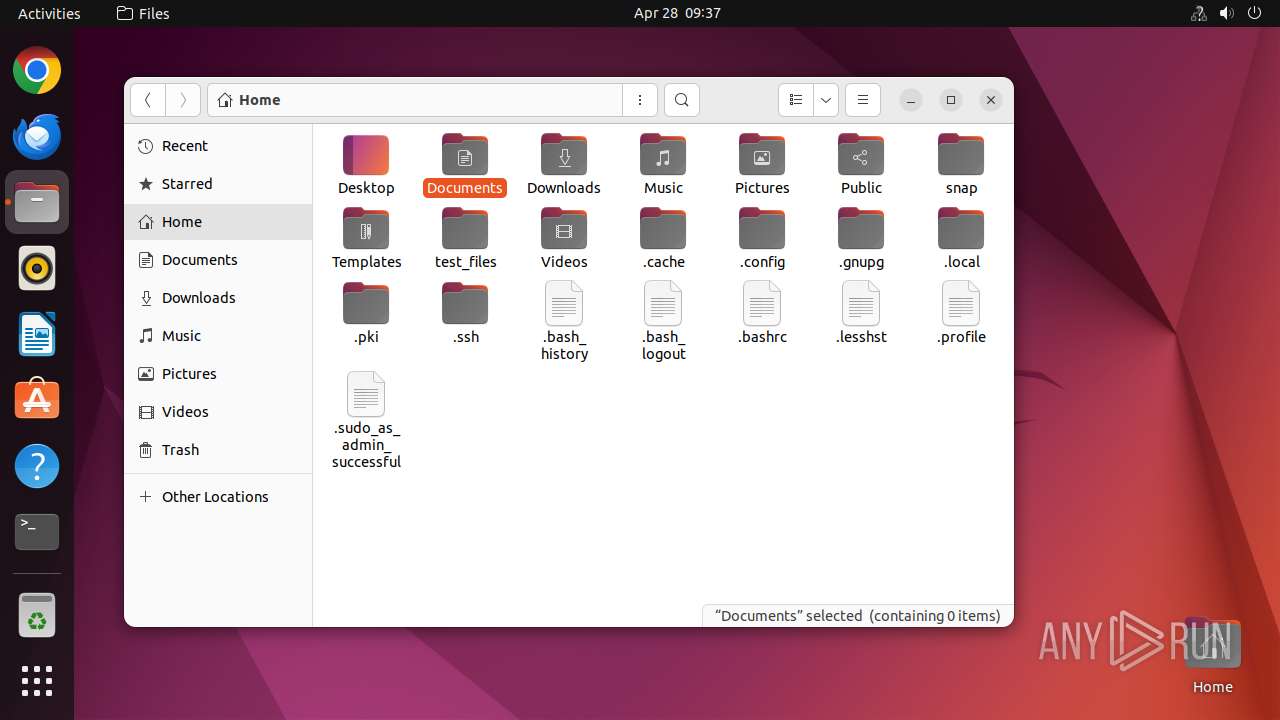
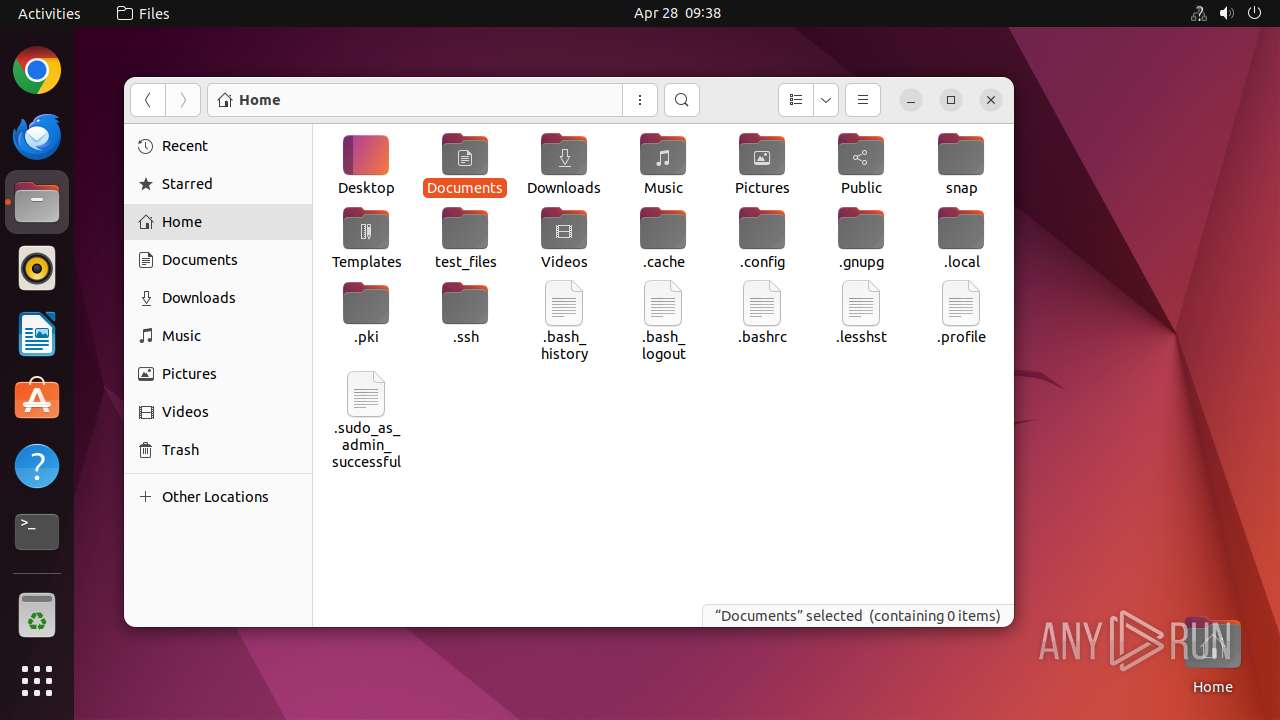
Modifies file or directory owner
- sudo (PID: 40723)
Reads profile file
- succed.solve.elf (PID: 40727)
Executes commands using command-line interpreter
- sudo (PID: 40726)
- succed.solve.elf (PID: 40727)
Reads passwd file
- succed.solve.elf (PID: 40727)
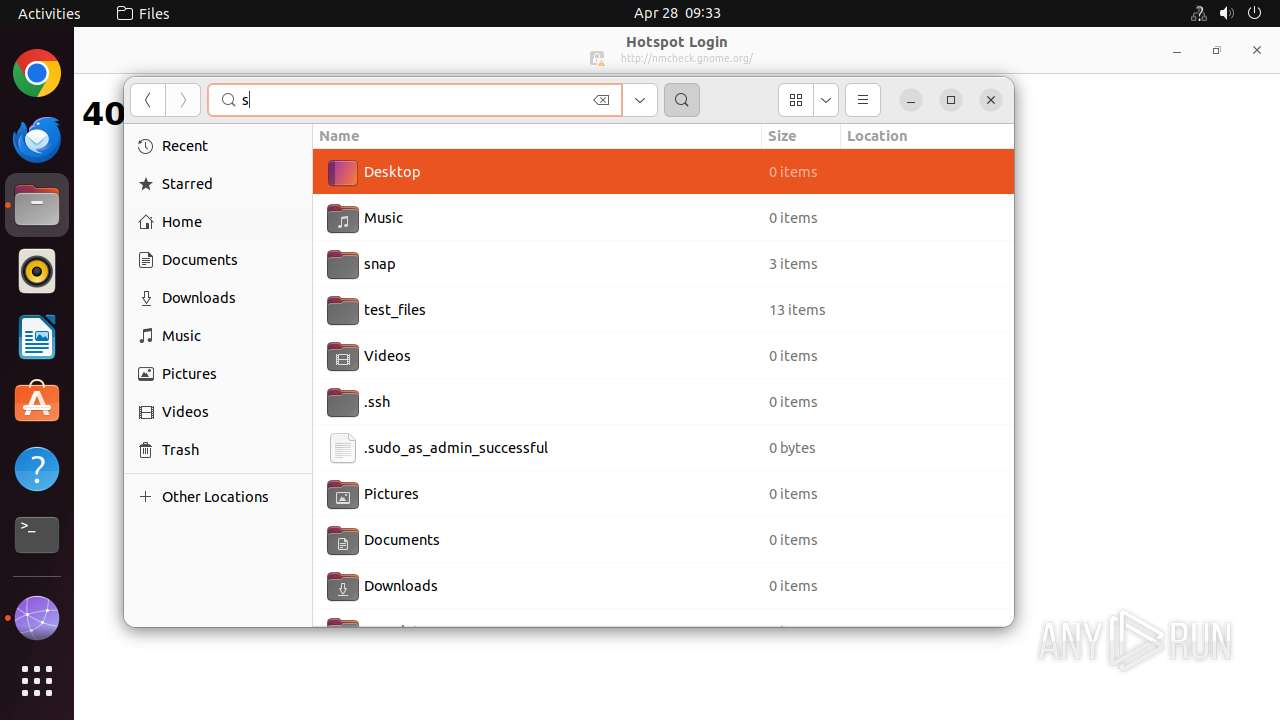
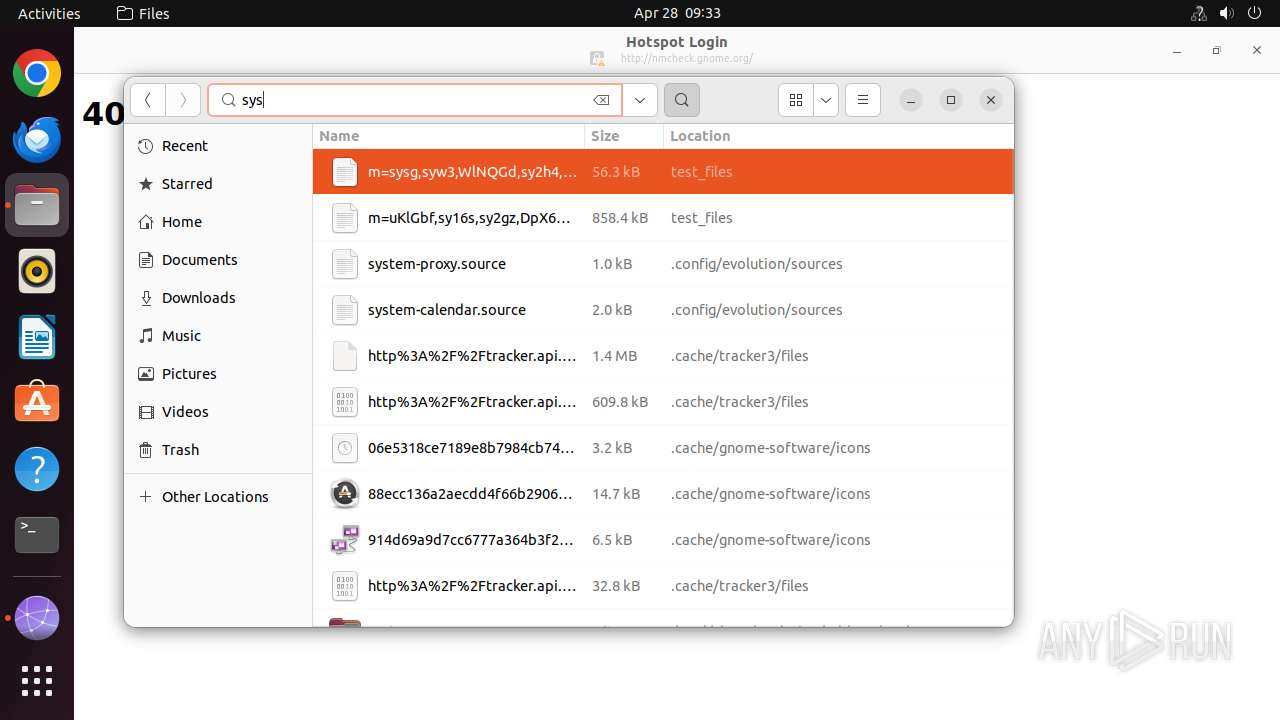
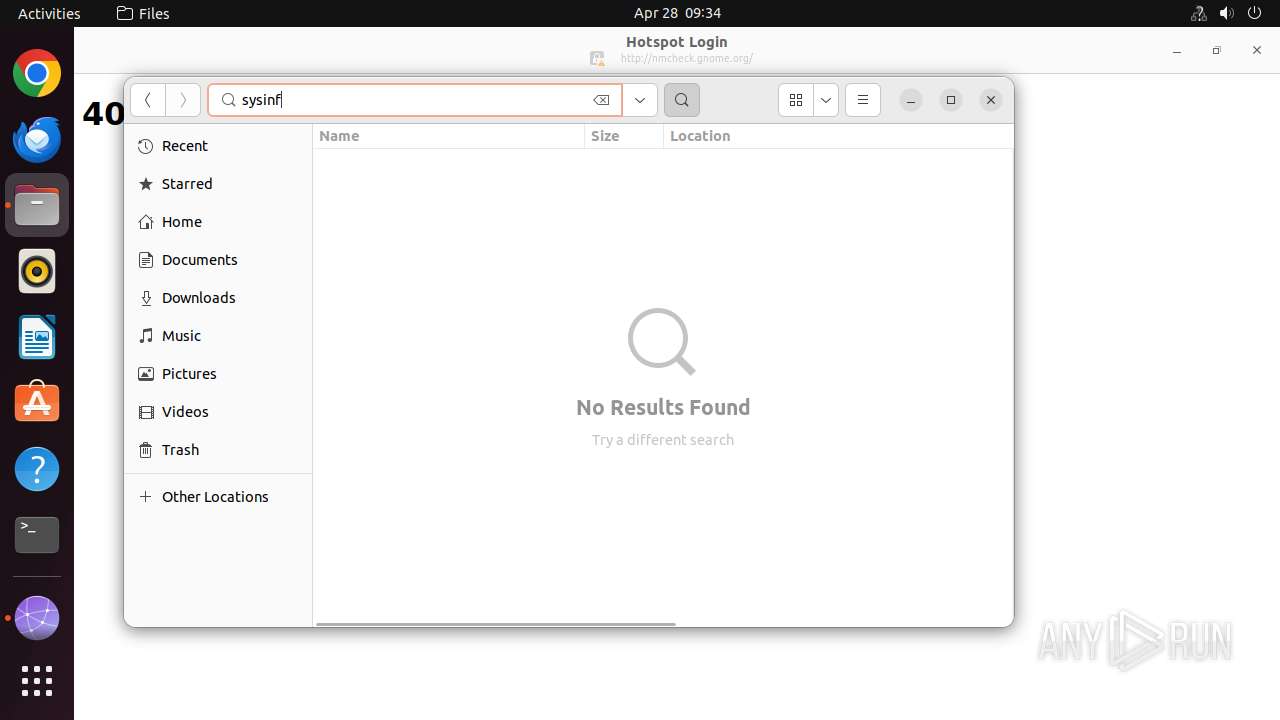
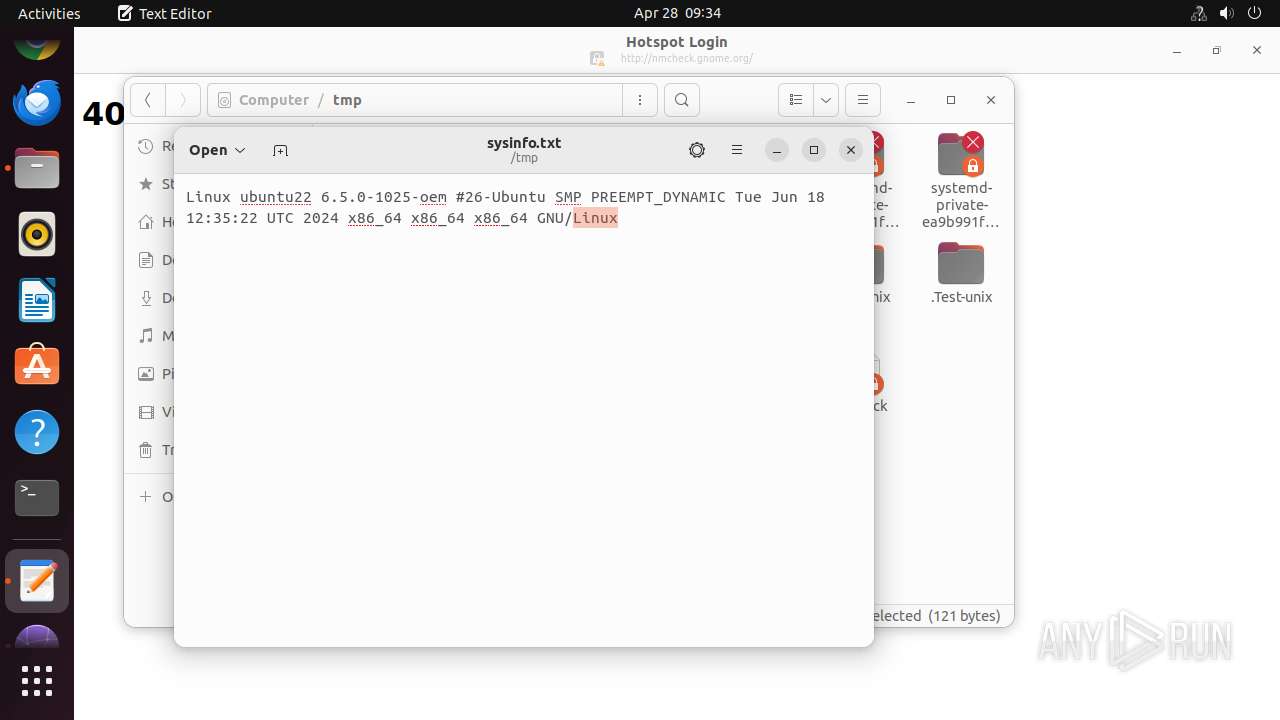
Checks all system information (uname)
- bash (PID: 40734)
INFO
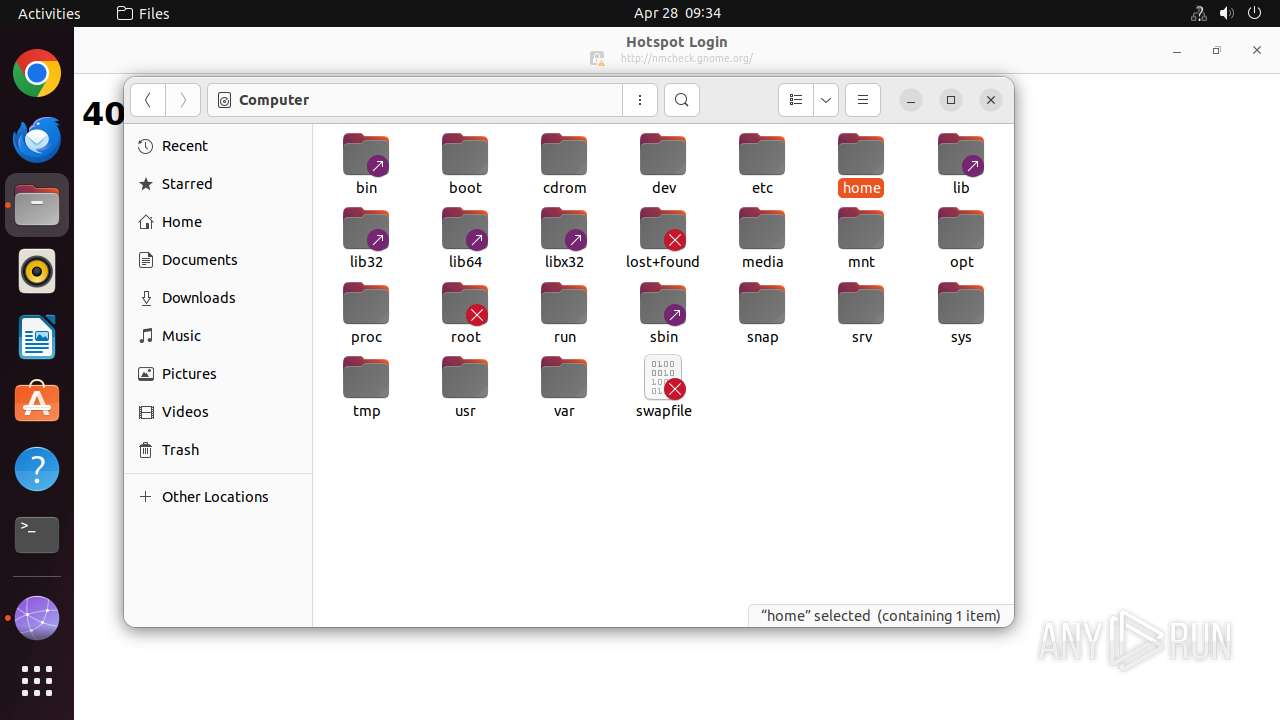
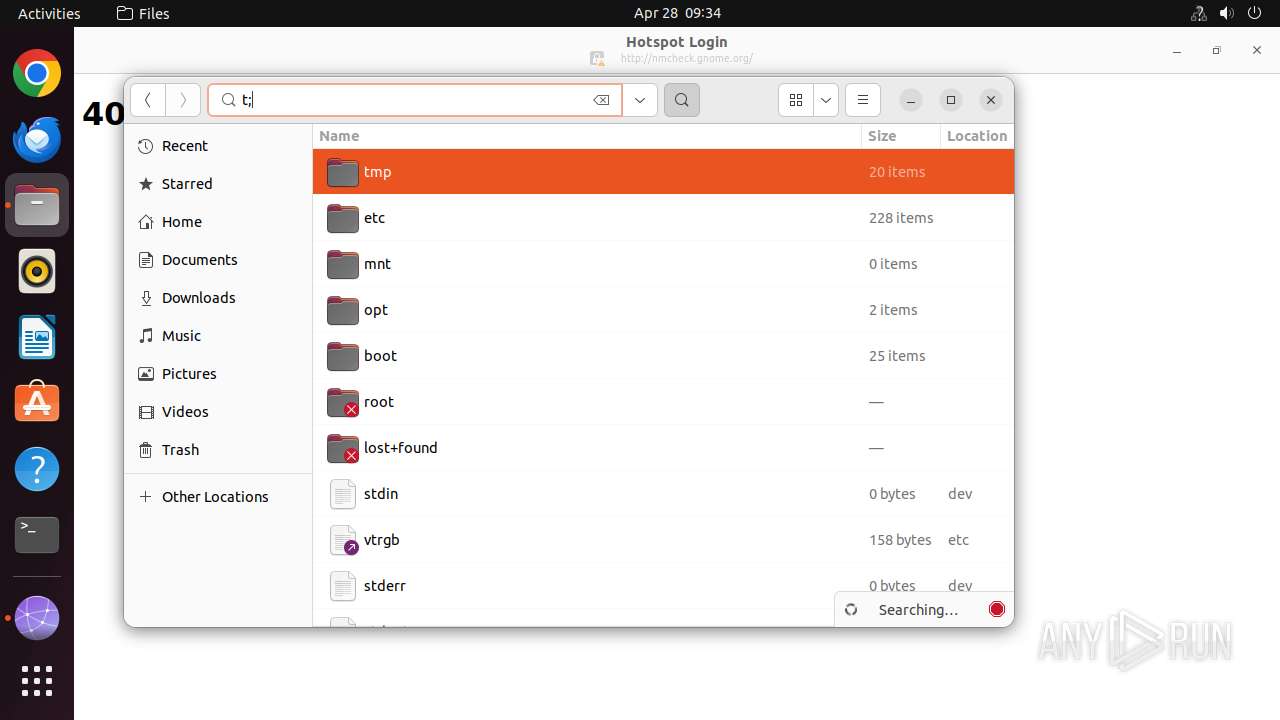
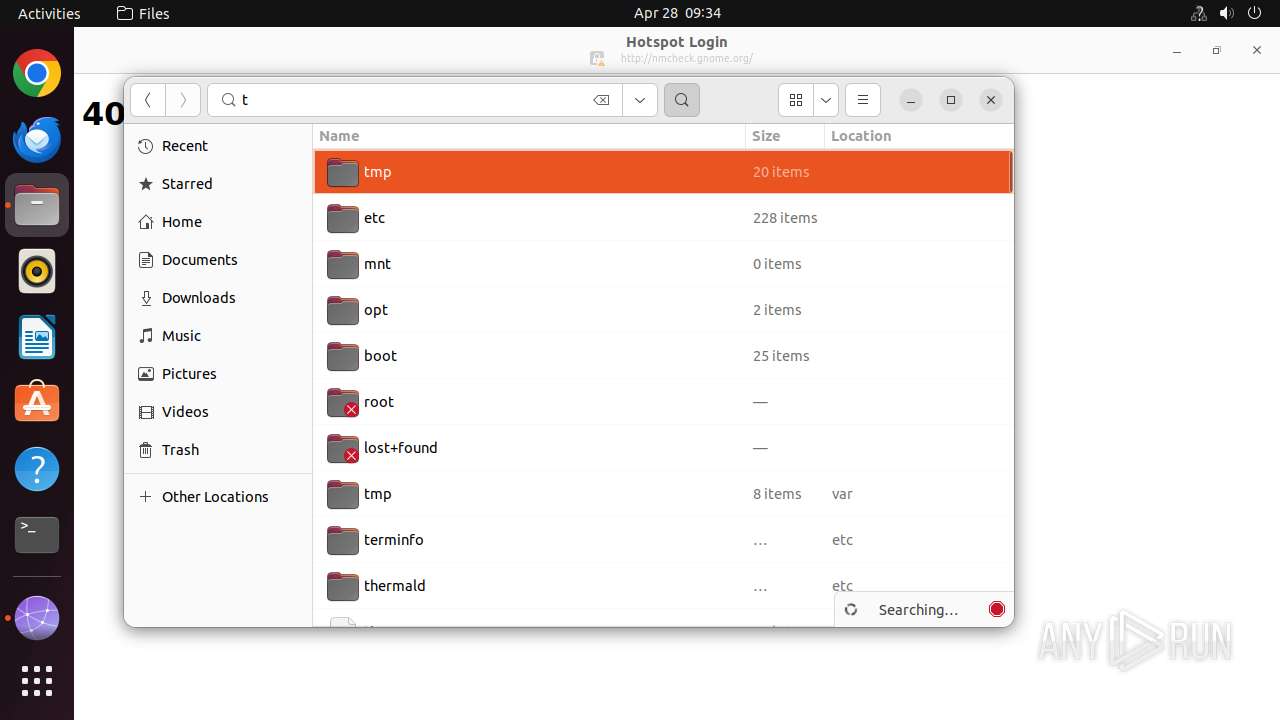
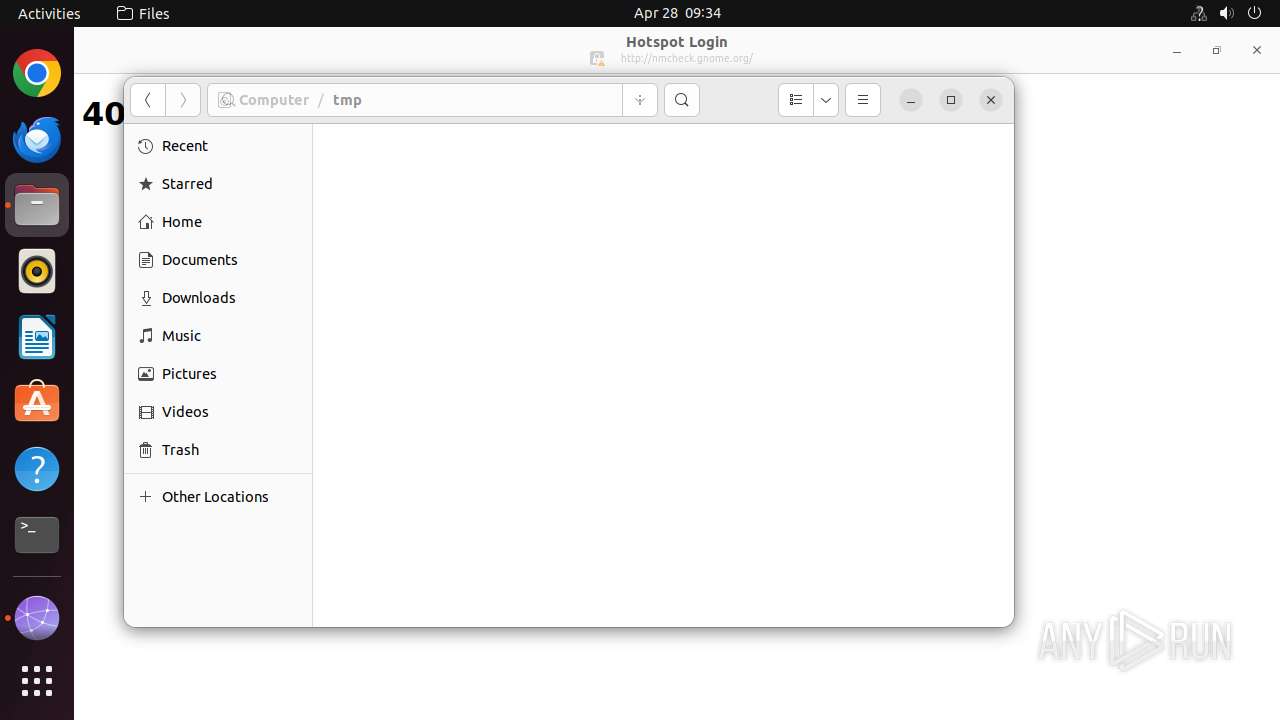
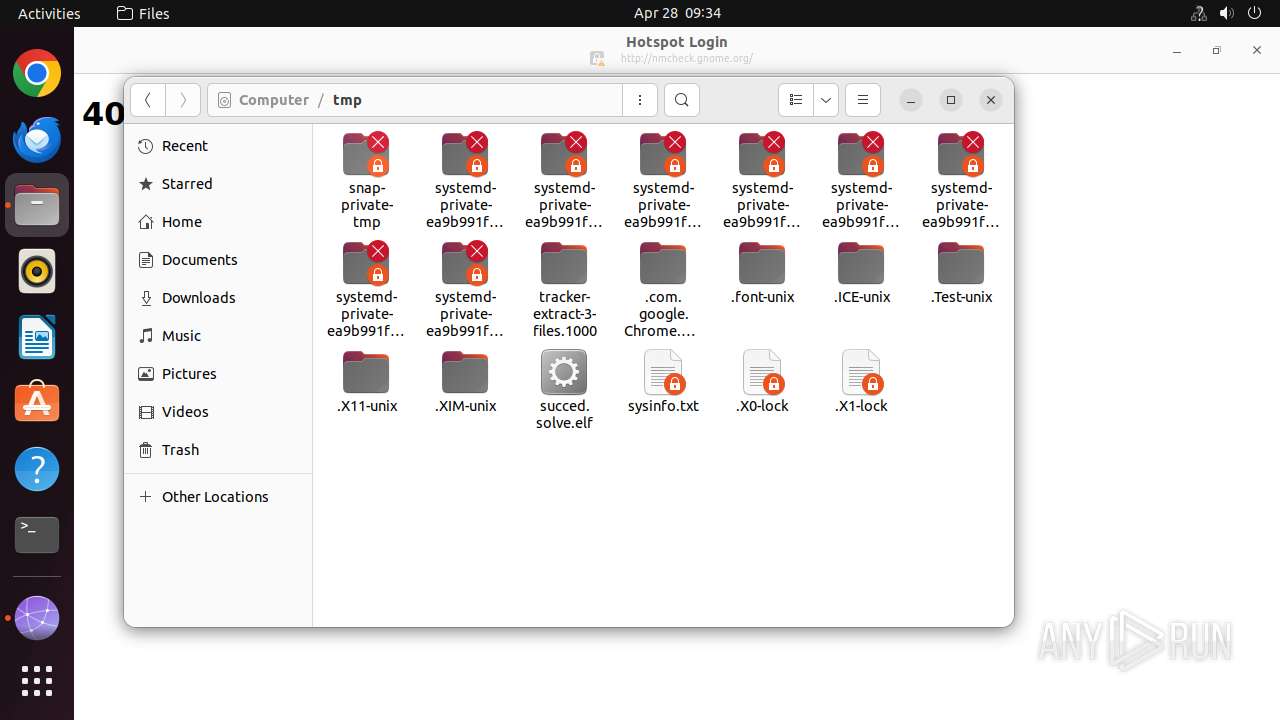
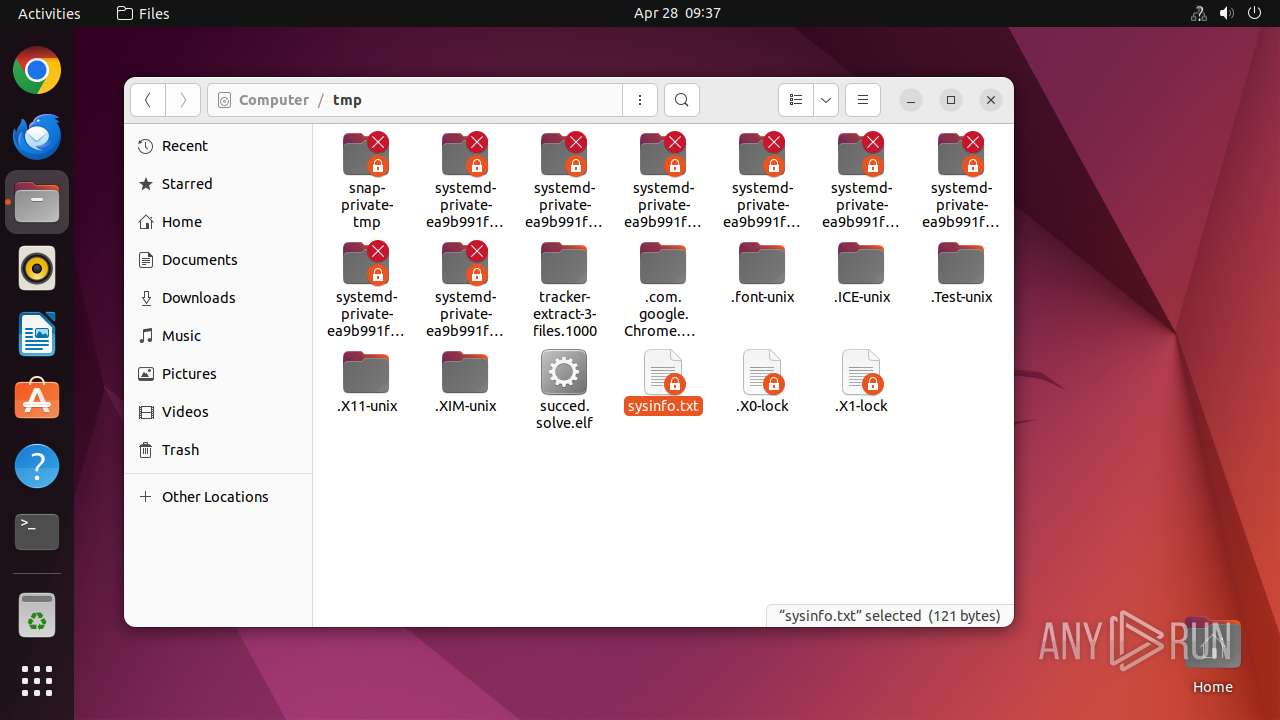
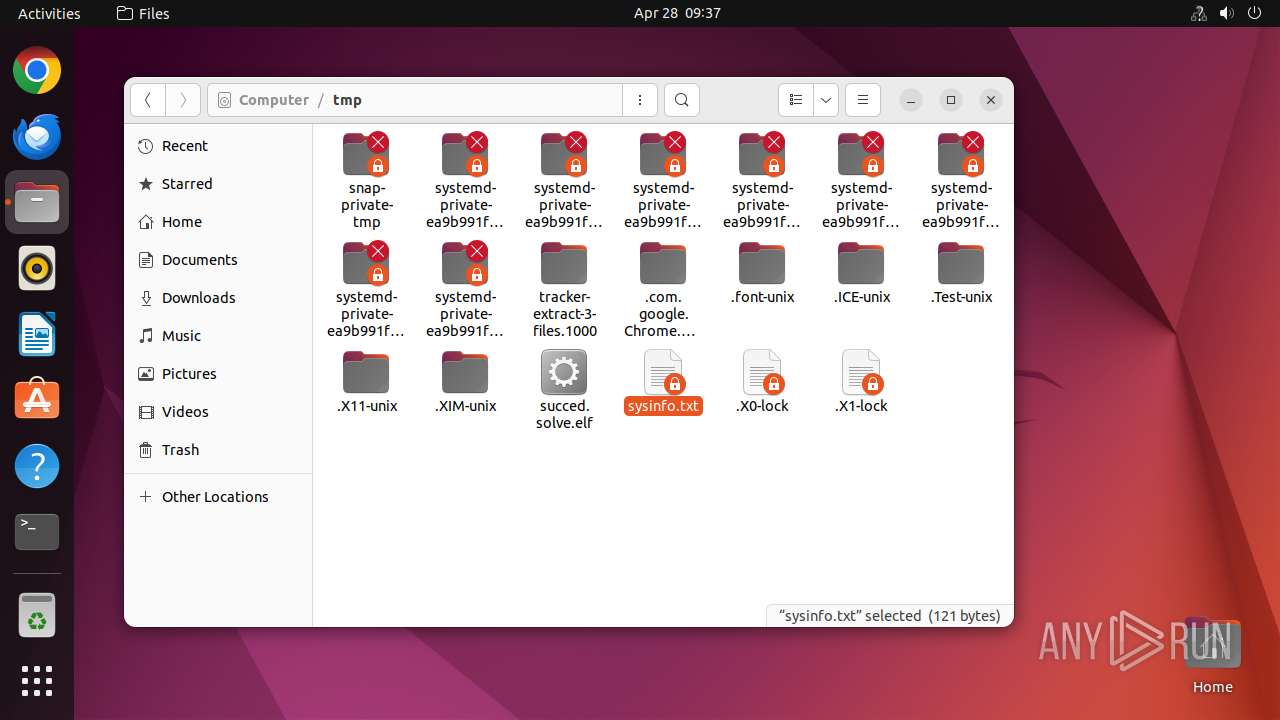
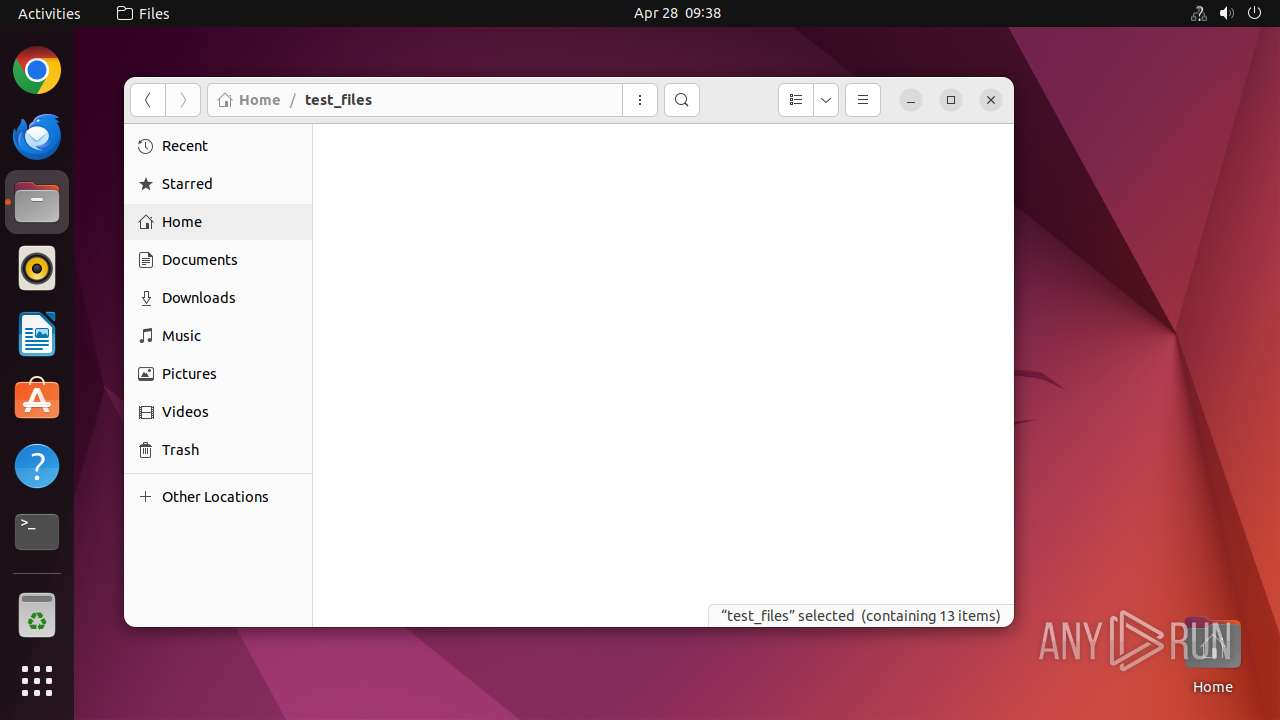
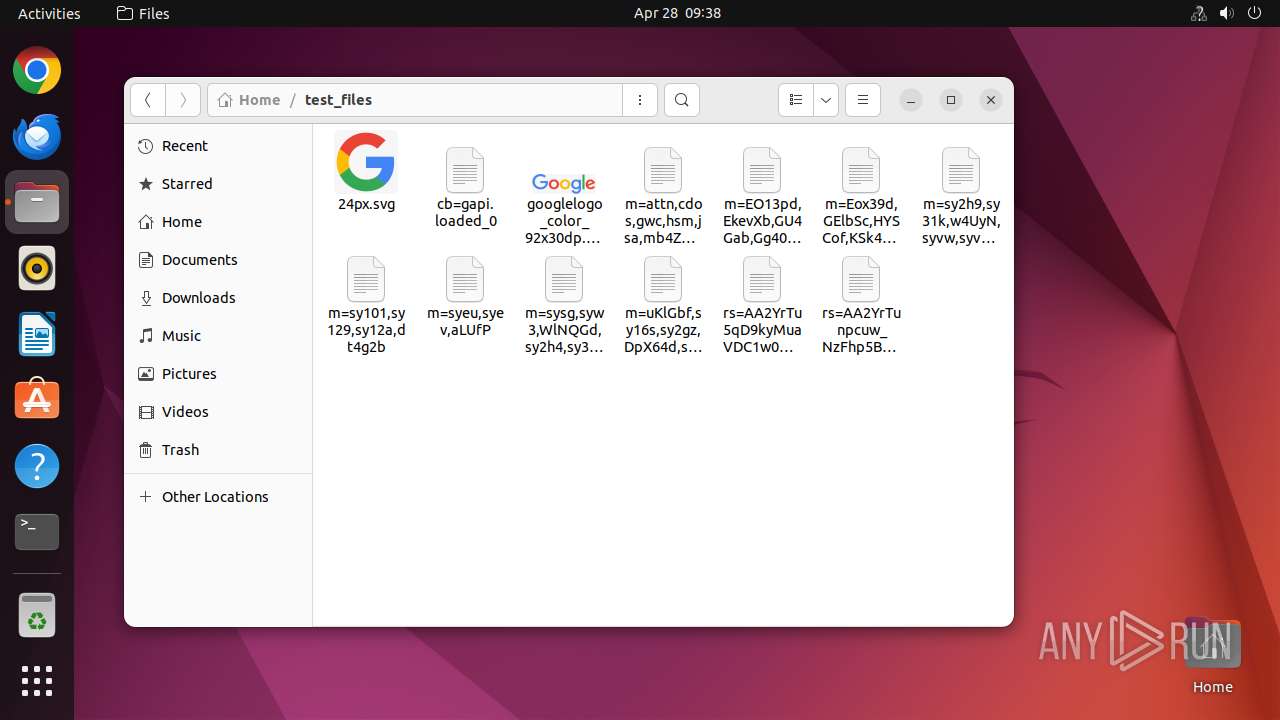
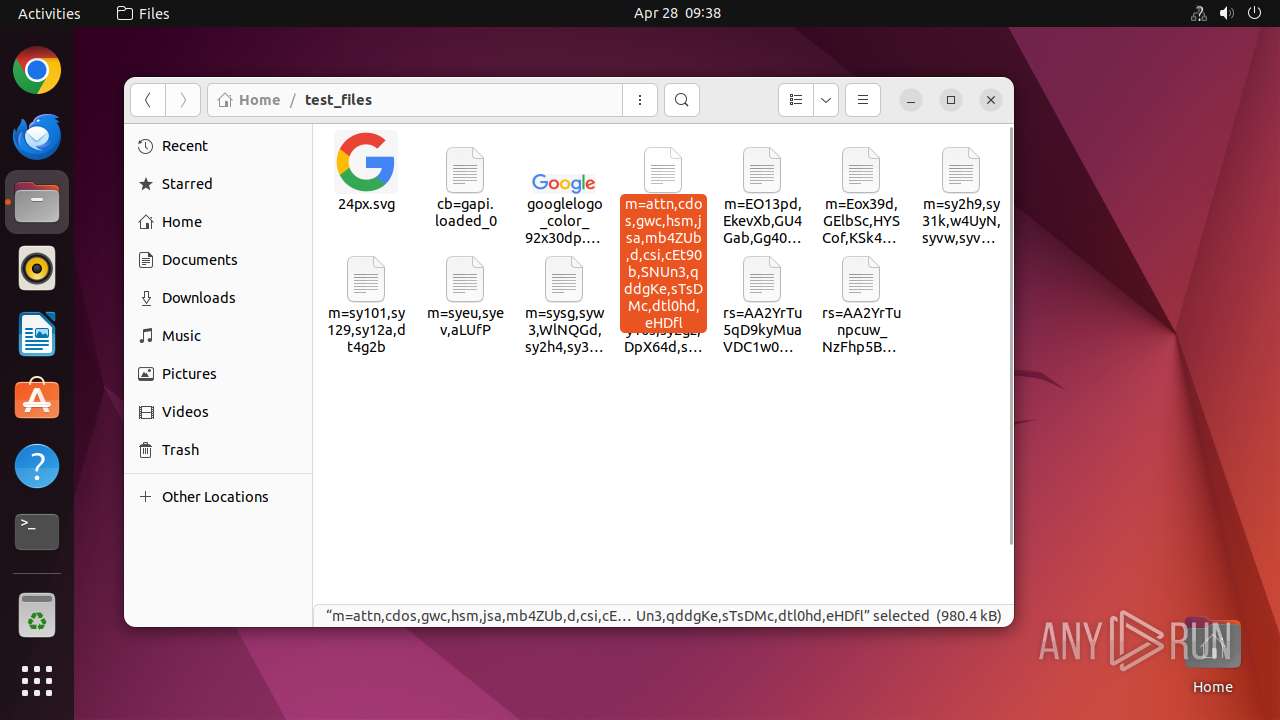
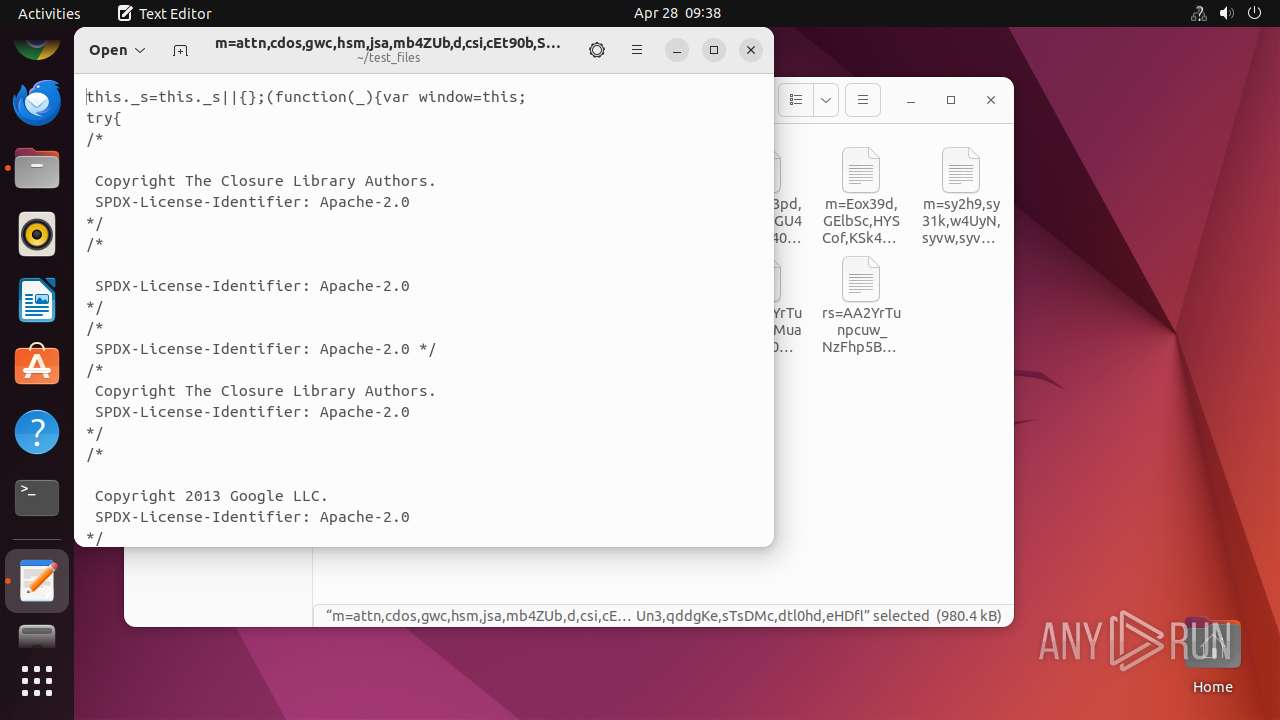
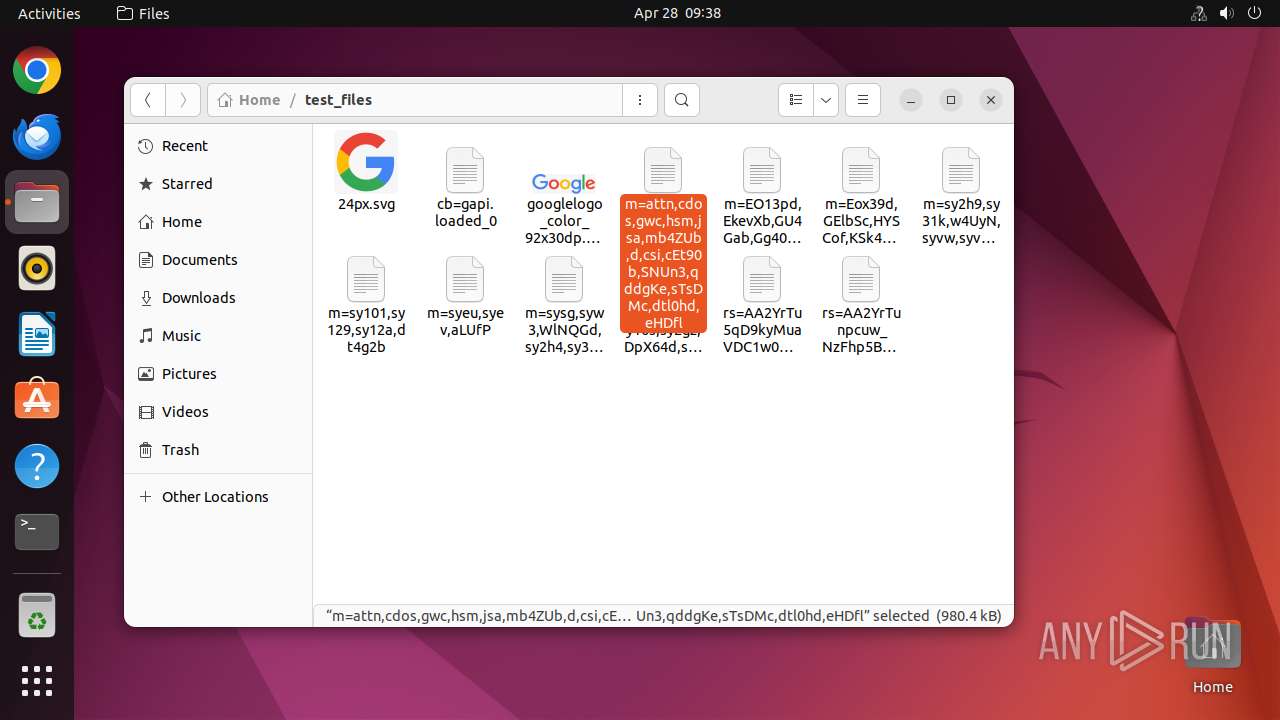
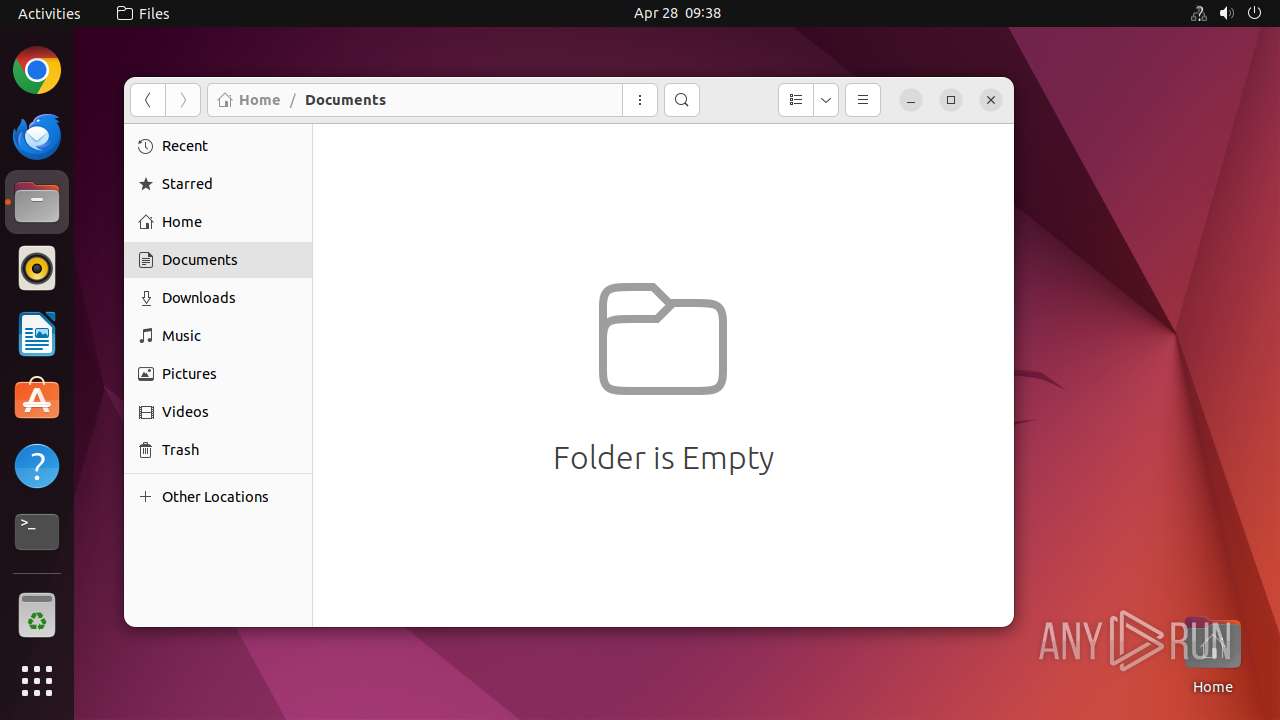
Creates file in the temporary folder
- uname (PID: 40735)
- gdk-pixbuf-thumbnailer (PID: 40789)
- nautilus (PID: 40738)
- gdk-pixbuf-thumbnailer (PID: 40786)
- gdk-pixbuf-thumbnailer (PID: 40792)
- gdk-pixbuf-thumbnailer (PID: 40799)
- gdk-pixbuf-thumbnailer (PID: 40783)
- gdk-pixbuf-thumbnailer (PID: 40796)
- gdk-pixbuf-thumbnailer (PID: 40803)
- gdk-pixbuf-thumbnailer (PID: 40806)
- gdk-pixbuf-thumbnailer (PID: 40812)
- gdk-pixbuf-thumbnailer (PID: 40818)
- gdk-pixbuf-thumbnailer (PID: 40809)
- gdk-pixbuf-thumbnailer (PID: 40815)
- gdk-pixbuf-thumbnailer (PID: 40823)
- gdk-pixbuf-thumbnailer (PID: 40833)
- gdk-pixbuf-thumbnailer (PID: 40839)
- gdk-pixbuf-thumbnailer (PID: 40973)
- gdk-pixbuf-thumbnailer (PID: 40842)
- gdk-pixbuf-thumbnailer (PID: 40846)
- gdk-pixbuf-thumbnailer (PID: 40849)
- gdk-pixbuf-thumbnailer (PID: 40828)
- gdk-pixbuf-thumbnailer (PID: 40836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (49.8) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Executable file |
| CPUType: | AMD x86-64 |
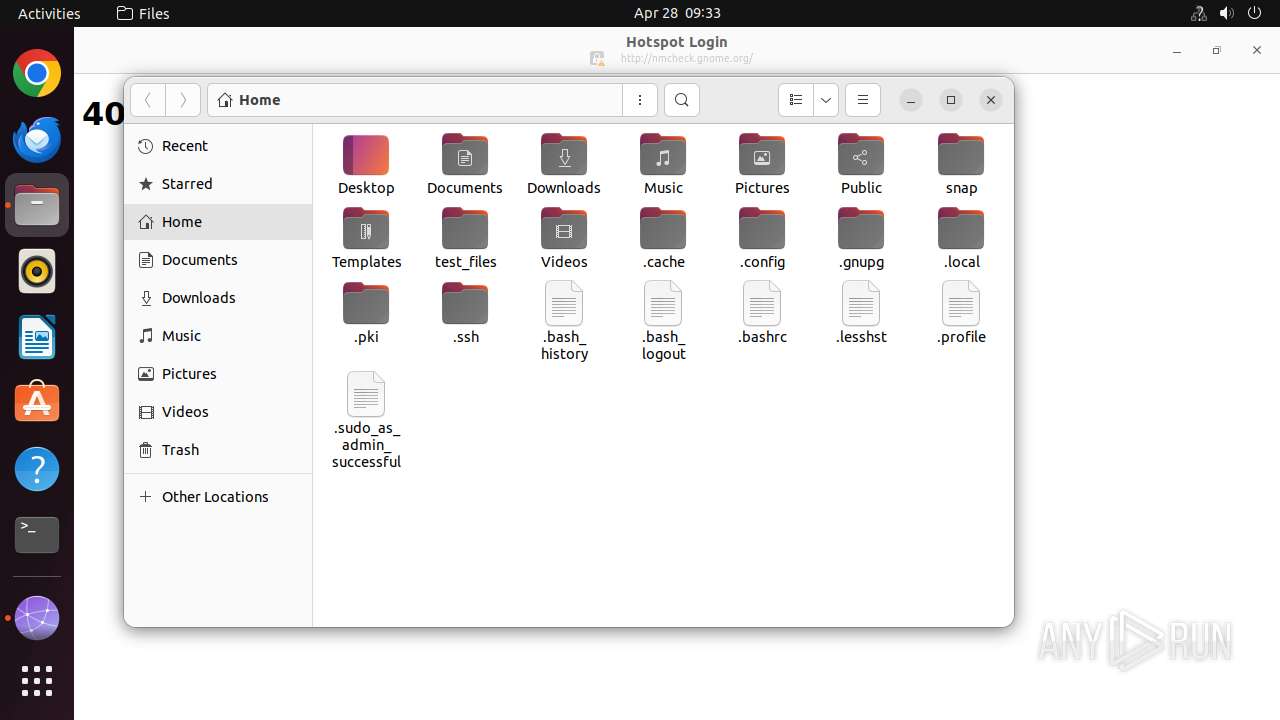
Total processes
312
Monitored processes
84
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 40722 | /bin/sh -c "sudo chown user /tmp/succed\.solve\.elf && chmod +x /tmp/succed\.solve\.elf && DISPLAY=:0 sudo -i /tmp/succed\.solve\.elf " | /usr/bin/dash | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 40723 | sudo chown user /tmp/succed.solve.elf | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40724 | chown user /tmp/succed.solve.elf | /usr/bin/chown | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40725 | chmod +x /tmp/succed.solve.elf | /usr/bin/chmod | — | dash |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40726 | sudo -i /tmp/succed.solve.elf | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 40727 | /tmp/succed.solve.elf | /tmp/succed.solve.elf | — | sudo |
User: root Integrity Level: UNKNOWN | ||||
| 40728 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | succed.solve.elf |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40729 | -bash --login -c \/tmp\/succed\.solve\.elf | /usr/bin/bash | — | succed.solve.elf |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40730 | sh -c "cat /usr/etc/debuginfod/*\.urls 2>/dev/null" | /usr/bin/dash | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 256 | ||||
| 40731 | tr \n " " | /usr/bin/tr | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
55
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40906 | gnome-text-editor | /home/user/.local/share/org.gnome.TextEditor/session.gvariant | binary | |
MD5:— | SHA256:— | |||
| 40735 | uname | /tmp/sysinfo.txt | text | |
MD5:— | SHA256:— | |||
| 40738 | nautilus | /home/user/.config/nautilus/search-metadata.1H2G52 | text | |
MD5:— | SHA256:— | |||
| 40738 | nautilus | /home/user/.config/nautilus/search-metadata.TAKP52 | text | |
MD5:— | SHA256:— | |||
| 40738 | nautilus | /tmp/flatpak-seccomp-ZFCL52 (deleted) | binary | |
MD5:— | SHA256:— | |||
| 40738 | nautilus | /home/user/.cache/thumbnails/large/91f8fe93870de6f6e9adc47aec9ebf49.png | image | |
MD5:— | SHA256:— | |||
| 40738 | nautilus | /tmp/flatpak-seccomp-I8MK52 (deleted) | binary | |
MD5:— | SHA256:— | |||
| 40738 | nautilus | /home/user/.cache/thumbnails/large/9bbba2c351559a67be735744328f79a6.png | binary | |
MD5:— | SHA256:— | |||
| 40738 | nautilus | /tmp/flatpak-seccomp-EU4I52 (deleted) | binary | |
MD5:— | SHA256:— | |||
| 40738 | nautilus | /home/user/.cache/thumbnails/large/727318e07e15e5e42c258c6c8548a01c.png | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
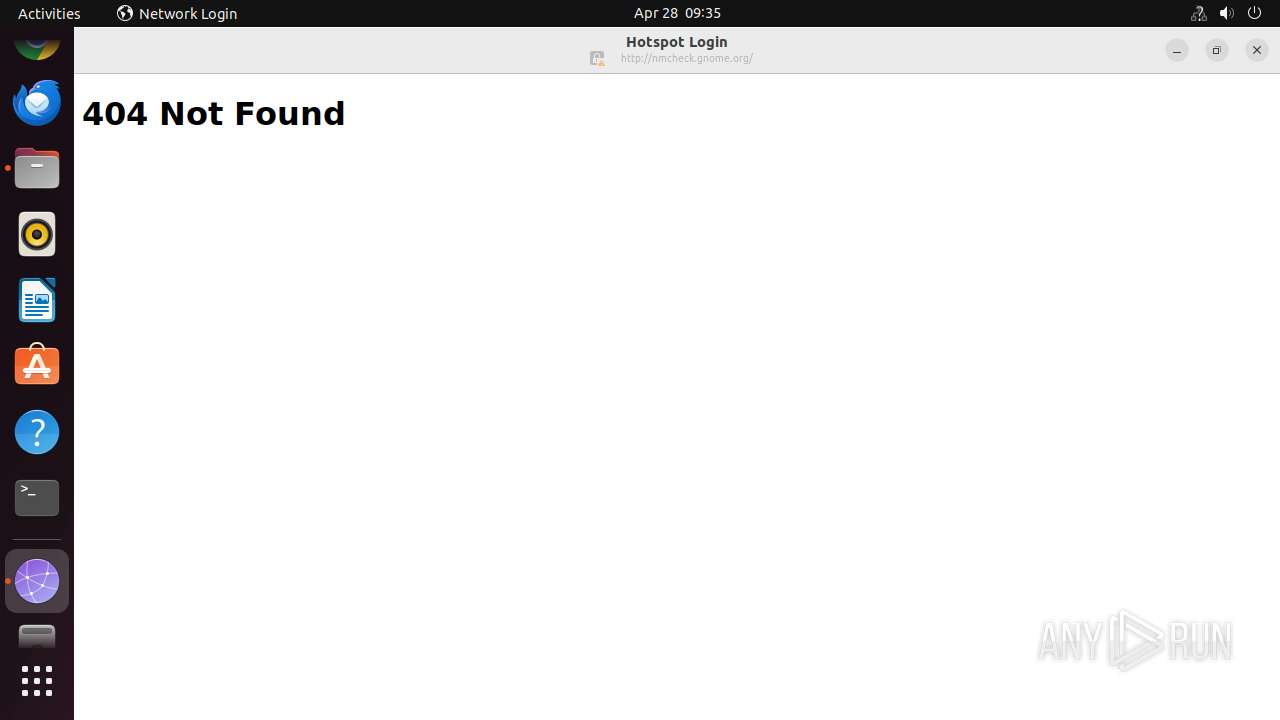
HTTP(S) requests
11
TCP/UDP connections
18
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 404 | 185.125.190.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 404 | 185.125.190.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 404 | 185.125.190.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 404 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 404 | 151.101.193.91:80 | http://nmcheck.gnome.org/ | unknown | — | — | whitelisted |
488 | NetworkManager | GET | 404 | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
488 | NetworkManager | GET | 404 | 91.189.91.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
488 | NetworkManager | GET | 404 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
488 | NetworkManager | GET | 404 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
488 | NetworkManager | GET | 404 | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.190.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.190.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 151.101.193.91:80 | nmcheck.gnome.org | FASTLY | US | whitelisted |
— | — | 195.181.175.40:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
488 | NetworkManager | 91.189.91.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
488 | NetworkManager | 91.189.91.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
488 | NetworkManager | 91.189.91.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
nmcheck.gnome.org |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
14.100.168.192.in-addr.arpa |
| unknown |