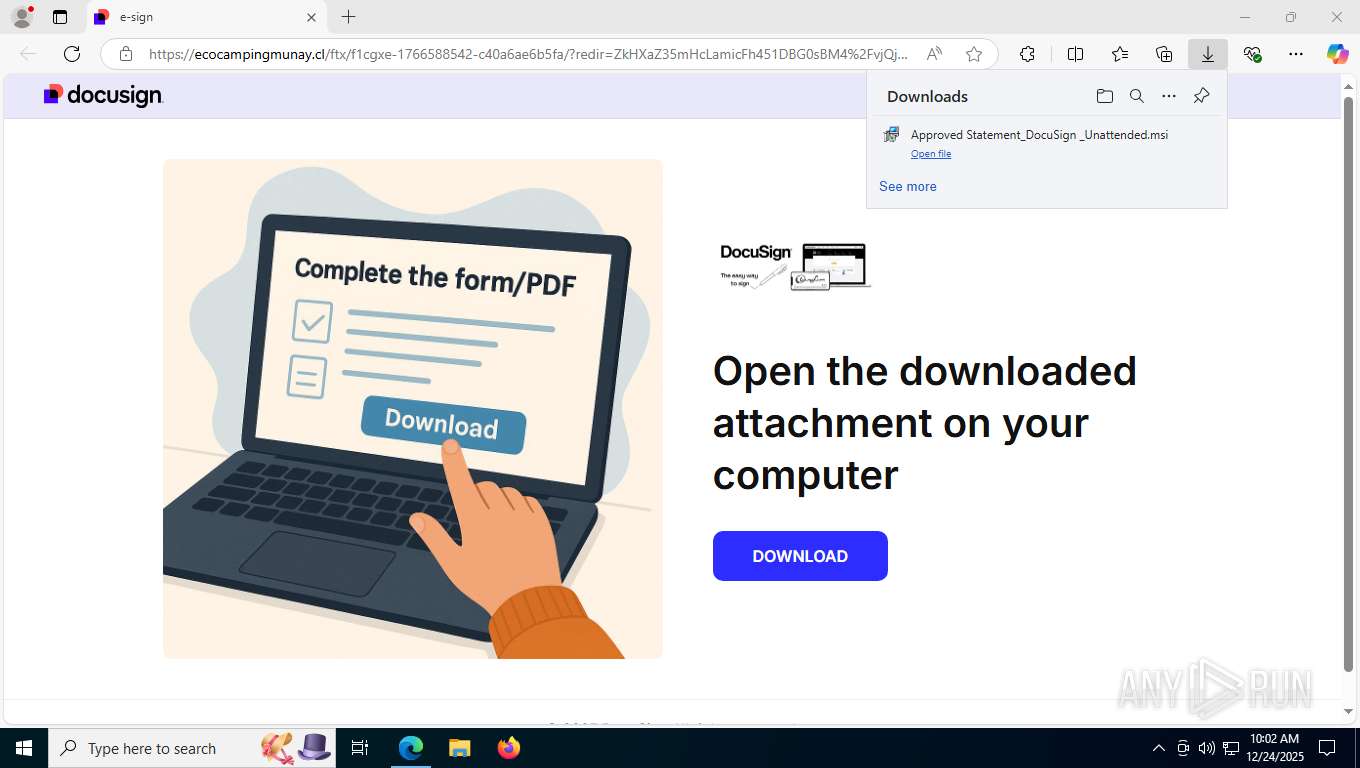
| URL: | https://us.content.exclaimer.net/?url=https%3A%2F%2Fecocampingmunay.cl%2Fftx&tenantid=INKHHXQ6EfC0ggAiSCLEjA&templateid=95cae96132caf0118196000d3a9eb50b&excomponentid=f-8my2-WcjzduShhcaT_oOYyYA_AqxhVW5kENQY21y0&excomponenttype=Link&signature=grQryy8_f8CQ4eerv2uzZnyrbAP9KTVc51AQVs4c1RVBXbJE4e2Wxo0f74DqAEPENAIIDEnMnu1YS0S9-6R7Jfb7D_ezBCMjXc0hB1nw6XnyGE9JprFc8TMfRmY23aBK-9s5Lf1y0i-tAeE7TEQ7GHGn-IPzl441ZzS8FRT7aiAZMKRVMCGuG2mwTUdv7qmqsPfP1fGoqbXCM2zhm4cTFP0ObIluFa4tZs0VWd8c39tFHO7Ey4ITVnZJRQtK_8eqpx14UztFFcFs0Keo-mgZhZurF2vaGxp7CNHcfCP1CZrvOfwgw1ACiWeDe922wb2cRfsuCUX6tWAj__VrWFe3kg&v=1&imprintMessageId=06d53030-aa6f-4d92-a2af-f0d08b6f958a |
| Full analysis: | https://app.any.run/tasks/611239e1-04d2-4975-a1ad-8802393d1126 |
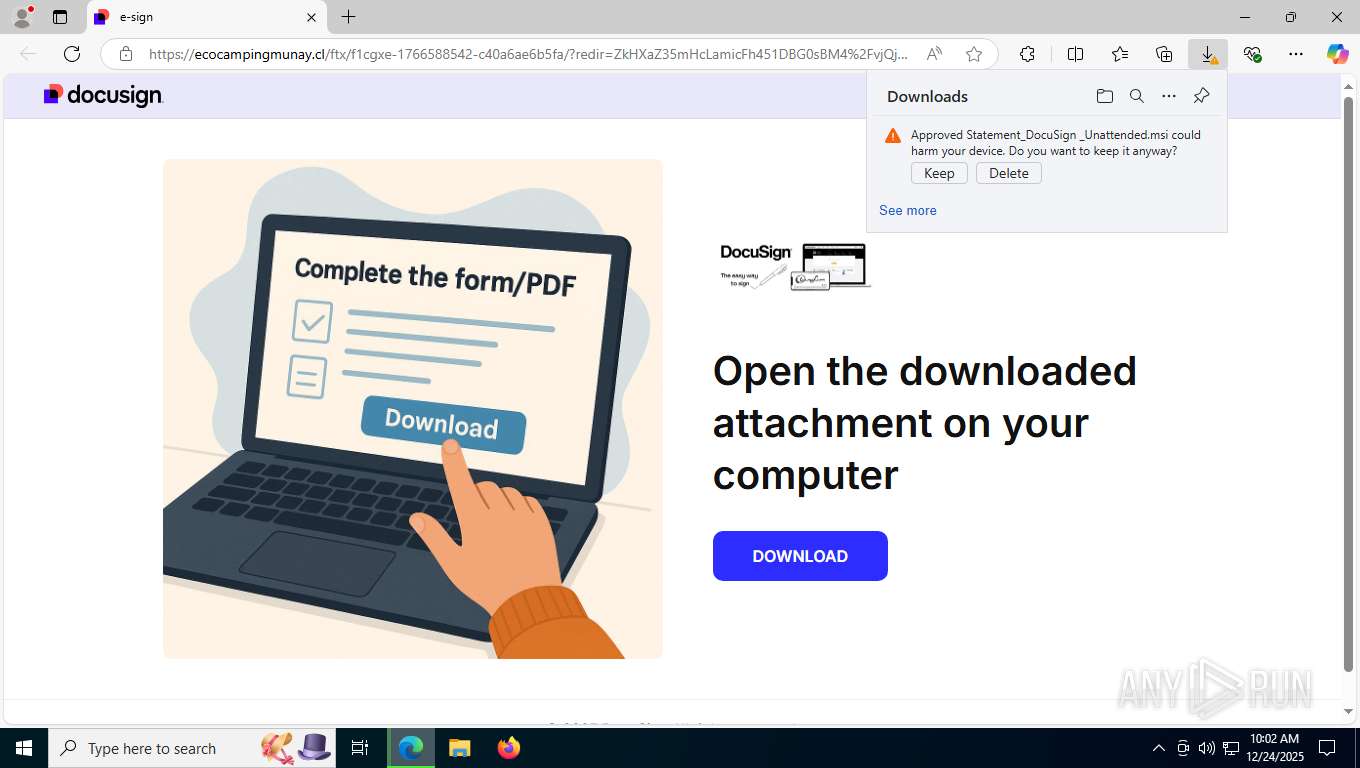
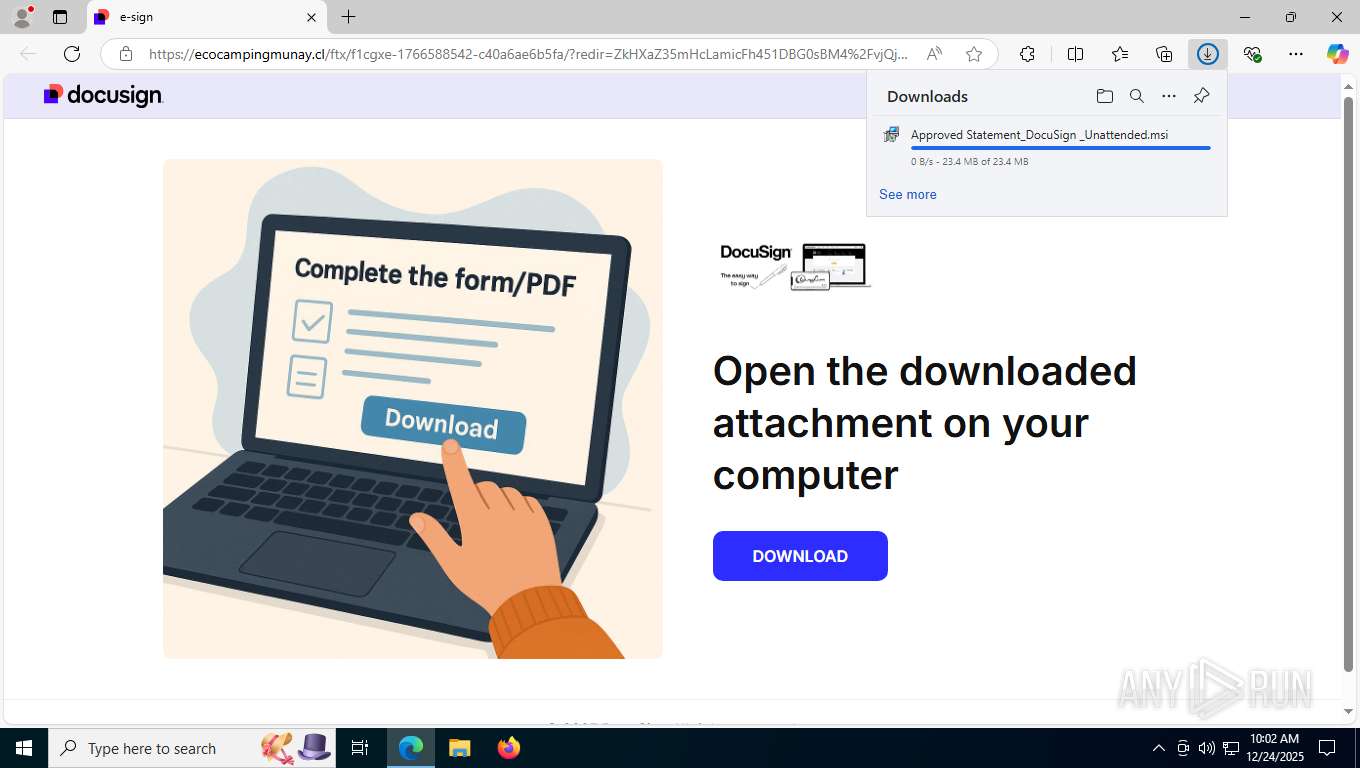
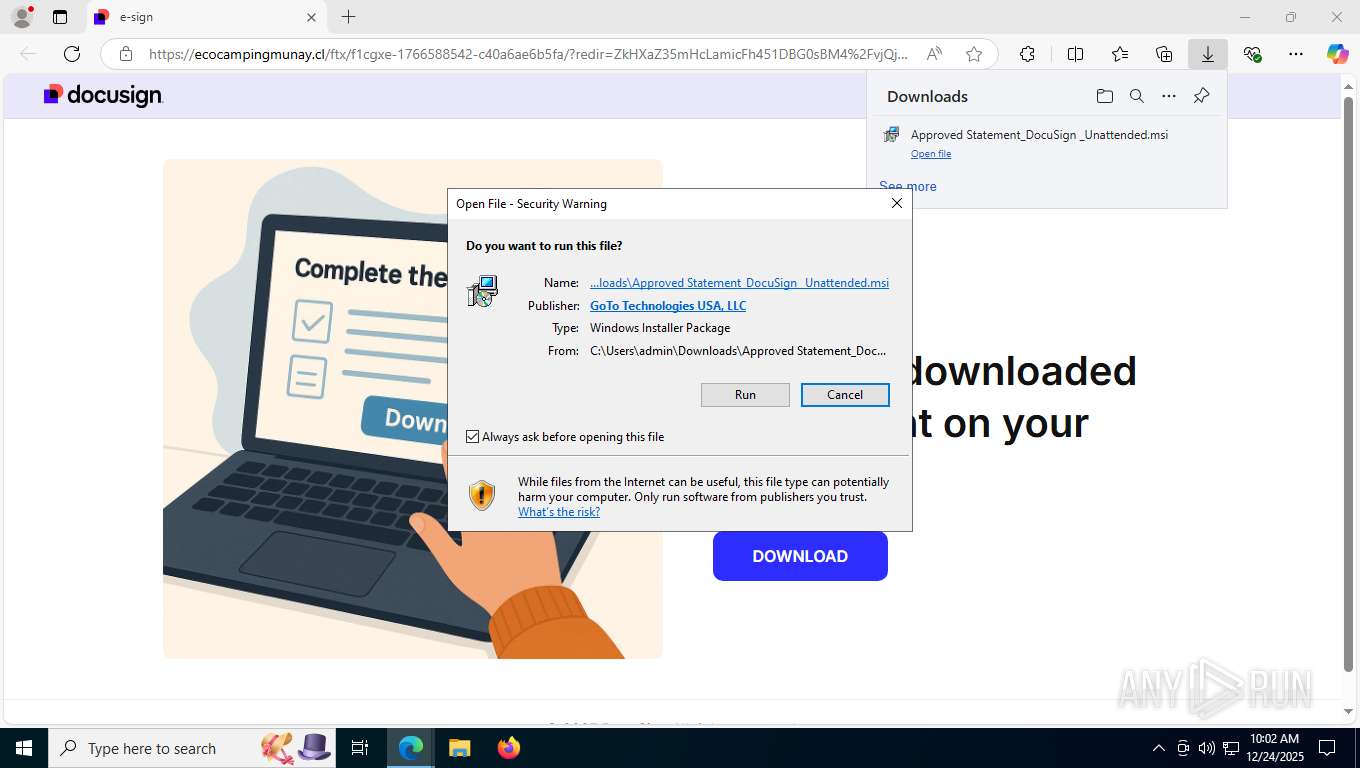
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2025, 15:02:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 738EAC0A725C3728FB51C01AA183D20D |
| SHA1: | E458FAD2905AAEC2C026585C737B1FB4FA1756A5 |
| SHA256: | 9DD44AD3CAC2759AF57E4BC7E0A76CA0E31C53C4EC3D5C02FDE1692F8152F7FF |
| SSDEEP: | 12:2GLo5dQ0hZ+8mybyn8NaWLqOMWKrmYbd0y/ycpelpWQS1M4wIERMJjOrY:2GcDJgybyn8NaW2ZWKrmQftwIERMJjOc |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7844)
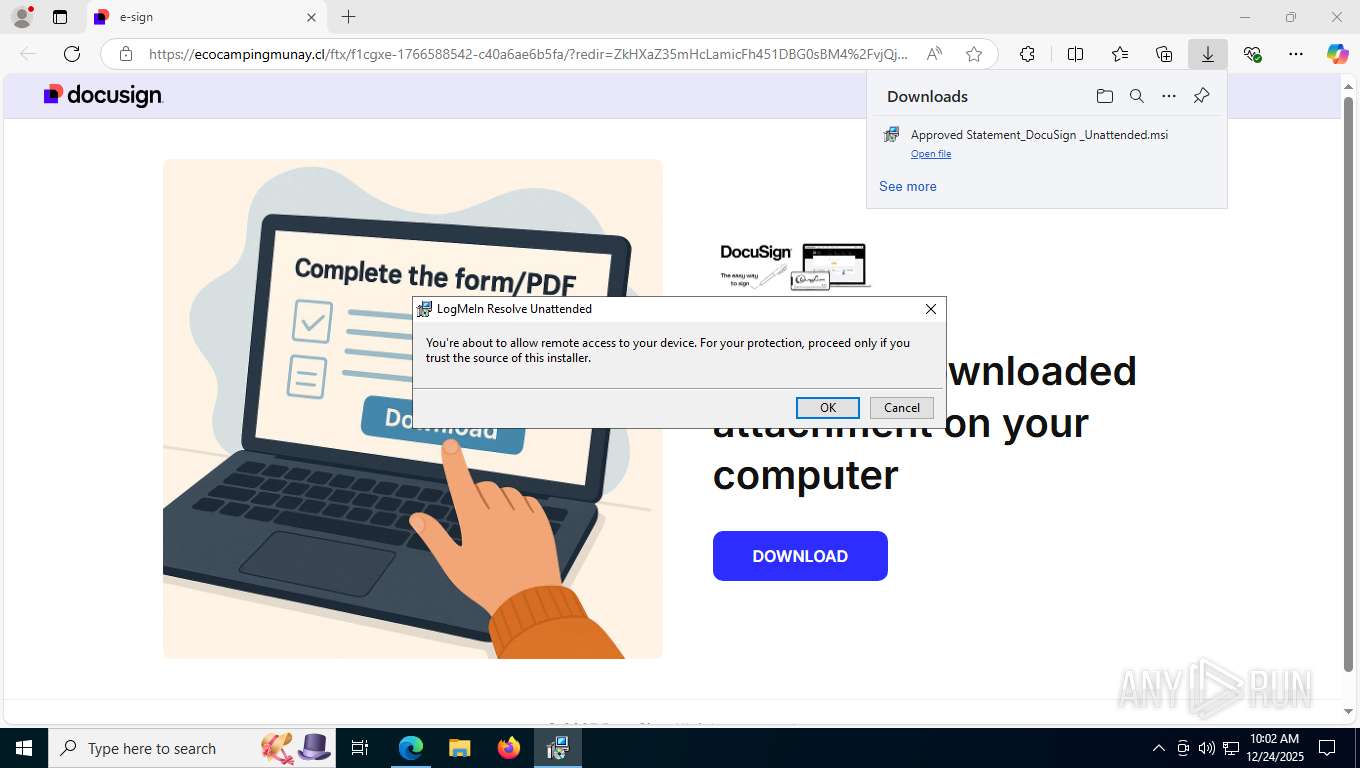
Changes settings of System certificates
- GoToResolveUnattended.exe (PID: 9036)
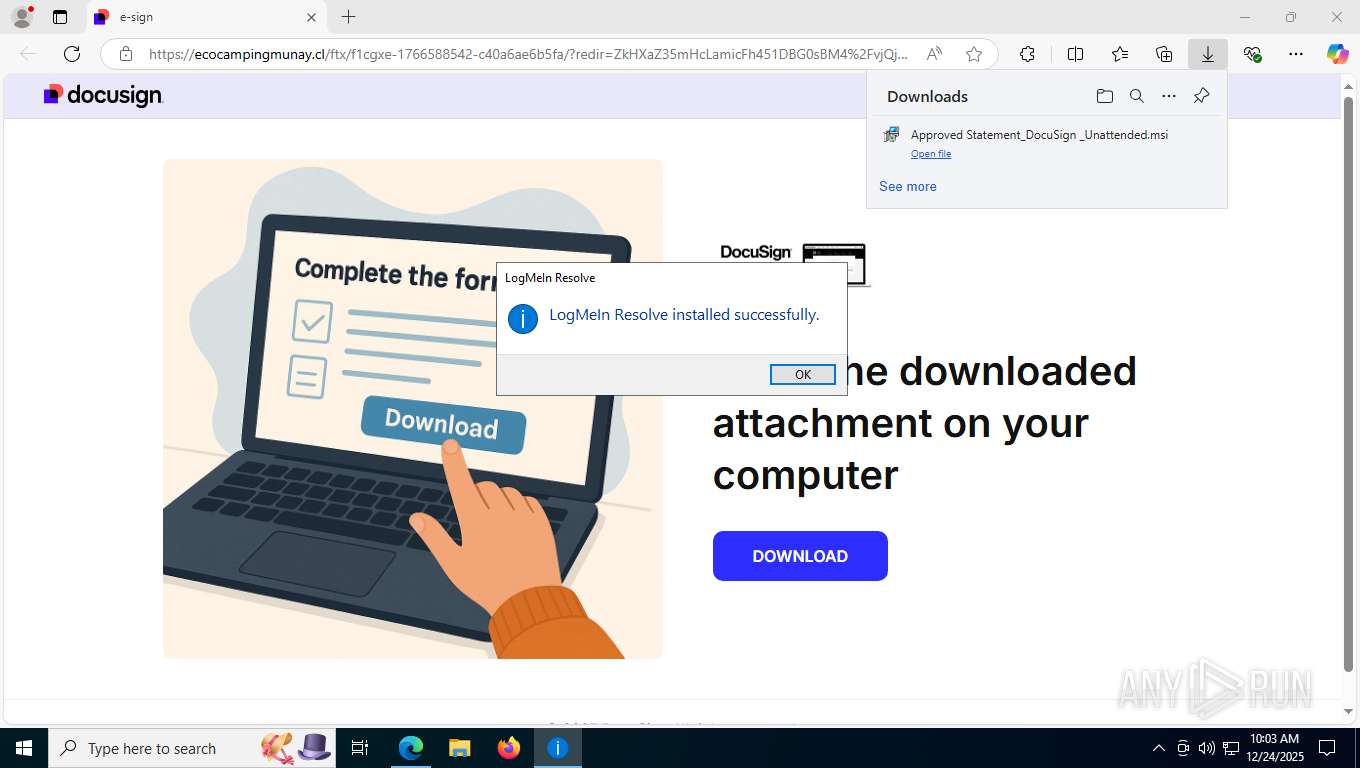
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 9112)
- GoToResolveProcessChecker.exe (PID: 9000)
- GoToResolveProcessChecker.exe (PID: 6976)
- WmiApSrv.exe (PID: 3040)
Starts CMD.EXE for commands execution
- unattended-updater.exe (PID: 6404)
Executable content was dropped or overwritten
- unattended-updater.exe (PID: 6404)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveExternalModuleHandler.exe (PID: 5036)
- GoToResolveExternalModuleHandler.exe (PID: 7344)
Executing commands from ".cmd" file
- unattended-updater.exe (PID: 6404)
Creates files in the driver directory
- GoToResolveTools64.exe (PID: 1772)
- GoToResolveTools64.exe (PID: 8620)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5480)
Reads security settings of Internet Explorer
- GoToResolveUnattended.exe (PID: 6392)
- GoToResolveUnattendedUi.exe (PID: 8268)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveUnattendedUi.exe (PID: 8224)
- GoToResolveUnattended.exe (PID: 8512)
LOGMEINRESCUE mutex has been found
- GoToResolveProcessChecker.exe (PID: 9000)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveProcessChecker.exe (PID: 6976)
- GoToResolveUnattended.exe (PID: 8512)
Named pipe usage
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveExternalModuleHandler.exe (PID: 5036)
- GoToResolveNetworkChecker.exe (PID: 7068)
- GoToResolveLoggerProcess.exe (PID: 9048)
- GoToResolveUnattendedUi.exe (PID: 8268)
- GoToResolveUnattended.exe (PID: 8512)
- GoToResolveLoggerProcess.exe (PID: 8736)
- GoToResolveUnattendedUi.exe (PID: 8224)
- GoToResolveExternalModuleHandler.exe (PID: 7344)
- GoToResolveNetworkChecker.exe (PID: 6664)
Creates/Modifies COM task schedule object
- GoToResolveUnattended.exe (PID: 9036)
Adds/modifies Windows certificates
- GoToResolveUnattended.exe (PID: 9036)
Reads the BIOS version
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveUnattended.exe (PID: 8512)
Process drops legitimate windows executable
- GoToResolveExternalModuleHandler.exe (PID: 7344)
The process creates files with name similar to system file names
- GoToResolveExternalModuleHandler.exe (PID: 7344)
Creates or modifies Windows services
- GoTo.Resolve.DeviceData.App.exe (PID: 8940)
The process verifies whether the antivirus software is installed
- GoTo.Resolve.Antivirus.App.exe (PID: 9044)
Searches for installed software
- GoTo.Resolve.Antivirus.App.exe (PID: 9044)
INFO
Reads the computer name
- identity_helper.exe (PID: 8168)
- msiexec.exe (PID: 8792)
- msiexec.exe (PID: 8836)
- msiexec.exe (PID: 8428)
- unattended-updater.exe (PID: 6404)
- GoToResolveTools64.exe (PID: 1772)
- GoToResolveUnattended.exe (PID: 6392)
- GoToResolveProcessChecker.exe (PID: 8628)
- drvinst.exe (PID: 8724)
- GoToResolveProcessChecker.exe (PID: 9000)
- GoToResolveExternalModuleHandler.exe (PID: 5036)
- GoToResolveNetworkChecker.exe (PID: 7068)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveLoggerProcess.exe (PID: 9048)
- GoToResolveUnattendedUi.exe (PID: 8268)
- GoToResolveTools64.exe (PID: 8620)
- GoToResolveProcessChecker.exe (PID: 6976)
- GoToResolveUnattended.exe (PID: 8512)
- GoToResolveLoggerProcess.exe (PID: 8736)
- GoToResolveExternalModuleHandler.exe (PID: 7344)
- GoToResolveNetworkChecker.exe (PID: 6664)
- GoToResolveUnattendedUi.exe (PID: 8224)
- GoTo.Resolve.DeviceData.App.exe (PID: 8940)
- GoTo.Resolve.Antivirus.App.exe (PID: 9044)
- RemoteExecution.Runner.exe (PID: 8788)
- GoTo.Resolve.Bcdr.App.exe (PID: 9068)
- GoTo.Resolve.Alerts.Monitor.App.exe (PID: 9052)
- GoTo.Resolve.PatchManagement.Client.exe (PID: 8432)
- GoTo.Resolve.Edr.Client.exe (PID: 4120)
- wa_3rd_party_host_32.exe (PID: 9592)
Reads Environment values
- identity_helper.exe (PID: 8168)
- GoToResolveTools64.exe (PID: 1772)
- GoToResolveUnattended.exe (PID: 6392)
- GoToResolveProcessChecker.exe (PID: 9000)
- GoToResolveProcessChecker.exe (PID: 8628)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveExternalModuleHandler.exe (PID: 5036)
- GoToResolveTools64.exe (PID: 8620)
- GoToResolveUnattended.exe (PID: 8512)
- GoToResolveExternalModuleHandler.exe (PID: 7344)
- GoToResolveProcessChecker.exe (PID: 6976)
Checks supported languages
- identity_helper.exe (PID: 8168)
- msiexec.exe (PID: 8792)
- msiexec.exe (PID: 8836)
- msiexec.exe (PID: 8428)
- unattended-updater.exe (PID: 6404)
- GoToResolveUnattended.exe (PID: 6392)
- GoToResolveCrashHandler.exe (PID: 8508)
- GoToResolveTools64.exe (PID: 1772)
- drvinst.exe (PID: 8724)
- GoToResolveProcessChecker.exe (PID: 8628)
- GoToResolveProcessChecker.exe (PID: 9000)
- GoToResolveCrashHandler.exe (PID: 9028)
- GoToResolveExternalModuleHandler.exe (PID: 5036)
- GoToResolveNetworkChecker.exe (PID: 7068)
- GoToResolveLoggerProcess.exe (PID: 9048)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveUnattendedUi.exe (PID: 8268)
- GoToResolveTools64.exe (PID: 8620)
- GoToResolveCrashHandler.exe (PID: 6648)
- GoToResolveProcessChecker.exe (PID: 6976)
- GoToResolveCrashHandler.exe (PID: 8848)
- GoToResolveUnattended.exe (PID: 8512)
- GoToResolveLoggerProcess.exe (PID: 8736)
- GoToResolveNetworkChecker.exe (PID: 6664)
- GoToResolveUnattendedUi.exe (PID: 8224)
- GoToResolveCrashHandler.exe (PID: 2624)
- GoToResolveExternalModuleHandler.exe (PID: 7344)
- GoTo.Resolve.Bcdr.App.exe (PID: 9068)
- GoTo.Resolve.Iata.App.exe (PID: 4704)
- GoTo.Resolve.DeviceData.App.exe (PID: 8940)
- RemoteExecution.Runner.exe (PID: 8788)
- GoTo.Resolve.Edr.Client.exe (PID: 4120)
- GoTo.Resolve.Antivirus.App.exe (PID: 9044)
- GoTo.Resolve.Alerts.Monitor.App.exe (PID: 9052)
- wa_3rd_party_host_32.exe (PID: 9592)
- GoToResolveCrashHandler.exe (PID: 4468)
- GoTo.Resolve.PatchManagement.Client.exe (PID: 8432)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8744)
- msiexec.exe (PID: 8792)
Manages system restore points
- SrTasks.exe (PID: 1976)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 8744)
Creates files or folders in the user directory
- unattended-updater.exe (PID: 6404)
- GoToResolveUnattendedUi.exe (PID: 8268)
Creates files in the program directory
- unattended-updater.exe (PID: 6404)
- GoToResolveTools64.exe (PID: 1772)
- GoToResolveCrashHandler.exe (PID: 8508)
- GoToResolveProcessChecker.exe (PID: 8628)
- GoToResolveUnattended.exe (PID: 6392)
- GoToResolveProcessChecker.exe (PID: 9000)
- GoToResolveCrashHandler.exe (PID: 9028)
- GoToResolveLoggerProcess.exe (PID: 9048)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveExternalModuleHandler.exe (PID: 5036)
- GoToResolveNetworkChecker.exe (PID: 7068)
- GoToResolveCrashHandler.exe (PID: 4468)
- GoToResolveUnattendedUi.exe (PID: 8268)
- GoToResolveProcessChecker.exe (PID: 6976)
- GoToResolveUnattended.exe (PID: 8512)
- GoToResolveLoggerProcess.exe (PID: 8736)
- GoToResolveExternalModuleHandler.exe (PID: 7344)
- GoTo.Resolve.Iata.App.exe (PID: 4704)
- GoTo.Resolve.Alerts.Monitor.App.exe (PID: 9052)
- GoTo.Resolve.DeviceData.App.exe (PID: 8940)
- GoTo.Resolve.Antivirus.App.exe (PID: 9044)
- GoTo.Resolve.Bcdr.App.exe (PID: 9068)
- RemoteExecution.Runner.exe (PID: 8788)
- GoTo.Resolve.PatchManagement.Client.exe (PID: 8432)
- GoTo.Resolve.Edr.Client.exe (PID: 4120)
Reads the machine GUID from the registry
- GoToResolveUnattended.exe (PID: 6392)
- GoToResolveProcessChecker.exe (PID: 8628)
- drvinst.exe (PID: 8724)
- GoToResolveProcessChecker.exe (PID: 9000)
- GoToResolveExternalModuleHandler.exe (PID: 5036)
- GoToResolveNetworkChecker.exe (PID: 7068)
- GoToResolveUnattendedUi.exe (PID: 8268)
- GoToResolveLoggerProcess.exe (PID: 9048)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveProcessChecker.exe (PID: 6976)
- GoToResolveUnattended.exe (PID: 8512)
- GoToResolveLoggerProcess.exe (PID: 8736)
- GoToResolveExternalModuleHandler.exe (PID: 7344)
- GoToResolveNetworkChecker.exe (PID: 6664)
- GoToResolveUnattendedUi.exe (PID: 8224)
- GoTo.Resolve.DeviceData.App.exe (PID: 8940)
- GoTo.Resolve.Antivirus.App.exe (PID: 9044)
- wa_3rd_party_host_32.exe (PID: 9592)
Reads CPU info
- GoToResolveTools64.exe (PID: 1772)
- GoToResolveUnattended.exe (PID: 6392)
- GoToResolveProcessChecker.exe (PID: 8628)
- GoToResolveProcessChecker.exe (PID: 9000)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveTools64.exe (PID: 8620)
- GoToResolveProcessChecker.exe (PID: 6976)
- GoToResolveUnattended.exe (PID: 8512)
- GoTo.Resolve.Alerts.Monitor.App.exe (PID: 9052)
The sample compiled with english language support
- unattended-updater.exe (PID: 6404)
- drvinst.exe (PID: 8724)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveExternalModuleHandler.exe (PID: 7344)
Process checks computer location settings
- GoToResolveUnattended.exe (PID: 6392)
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveUnattended.exe (PID: 8512)
- GoTo.Resolve.Alerts.Monitor.App.exe (PID: 9052)
- RemoteExecution.Runner.exe (PID: 8788)
- GoTo.Resolve.PatchManagement.Client.exe (PID: 8432)
- GoTo.Resolve.Edr.Client.exe (PID: 4120)
- GoTo.Resolve.Antivirus.App.exe (PID: 9044)
- GoTo.Resolve.Bcdr.App.exe (PID: 9068)
Checks proxy server information
- GoToResolveUnattendedUi.exe (PID: 8268)
- slui.exe (PID: 6456)
Creates a software uninstall entry
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveUnattended.exe (PID: 8512)
Reads the time zone
- GoToResolveUnattended.exe (PID: 9036)
- GoToResolveUnattended.exe (PID: 8512)
- GoTo.Resolve.Alerts.Monitor.App.exe (PID: 9052)
Application launched itself
- msedge.exe (PID: 7508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
247
Monitored processes
95
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5748,i,418116343751629642,4075789671346179634,262144 --variations-seed-version --mojo-platform-channel-handle=5740 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=18 --always-read-main-dll --field-trial-handle=6652,i,418116343751629642,4075789671346179634,262144 --variations-seed-version --mojo-platform-channel-handle=5272 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6148,i,418116343751629642,4075789671346179634,262144 --variations-seed-version --mojo-platform-channel-handle=6512 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1296 | timeout /T 3 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1772 | "C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\GoToResolveTools64.exe" -InstallVDD | C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\GoToResolveTools64.exe | unattended-updater.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1976 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:15 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2164 | timeout /T 3 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6676,i,418116343751629642,4075789671346179634,262144 --variations-seed-version --mojo-platform-channel-handle=6976 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2624 | "C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\GoToResolveCrashHandler.exe" "--database=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\UnattendedUiCrashReportDB" "--metrics-dir=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\UnattendedUiCrashReportDB" --url=https://dumpster.console.gotoresolve.com/api/dump --annotation=companyid=5569630477930893341 --annotation=component=Unattended --annotation=format=minidump --annotation=hostname=DESKTOP-JGLLJLD --annotation=installationid=GuDCFgWdgl --annotation=platform=win --annotation=version=1.30.1.670 "--attachment=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\params.json" "--attachment=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\unattended.json" "--attachment=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\mandatory.json" "--attachment=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\pc.json" "--attachment=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\ui.json" "--attachment=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\logger.json" "--attachment=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\leavebehind.json" "--attachment=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\rc.json" "--attachment=C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\appdata\externalmodulehandler.json" --initial-client-data=0x594,0x5a0,0x5b0,0x7d4,0x598,0x70bb2b50,0x70bb2b60,0x70bb2b70 | C:\Program Files (x86)\GoTo Resolve Unattended\5569630477930893341\GoToResolveCrashHandler.exe | — | GoToResolveUnattendedUi.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
117 228
Read events
116 979
Write events
220
Delete events
29
Modification events
| (PID) Process: | (8792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000005827755FE674DC015822000088230000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000005827755FE674DC015822000088230000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000D4ADBC5FE674DC015822000088230000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000D4ADBC5FE674DC015822000088230000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000D4ADBC5FE674DC015822000088230000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 15 | |||
| (PID) Process: | (8792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000CF0EDE5FE674DC015822000088230000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000CF0EDE5FE674DC015822000034200000E80300000100000000000000000000000DCC6FEC2B0FBC4981A5F015D39BE44400000000000000000000000000000000 | |||
| (PID) Process: | (9112) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (9112) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 48000000000000005E83F35FE674DC019823000030200000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
951
Suspicious files
115
Text files
577
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfdd66.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfdd76.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfdd86.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfdd86.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFfdd95.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfdd86.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
133
TCP/UDP connections
173
DNS requests
119
Threats
103
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7844 | msedge.exe | GET | 302 | 104.18.35.178:443 | https://us.content.exclaimer.net/?url=https%3A%2F%2Fecocampingmunay.cl%2Fftx&tenantid=INKHHXQ6EfC0ggAiSCLEjA&templateid=95cae96132caf0118196000d3a9eb50b&excomponentid=f-8my2-WcjzduShhcaT_oOYyYA_AqxhVW5kENQY21y0&excomponenttype=Link&signature=grQryy8_f8CQ4eerv2uzZnyrbAP9KTVc51AQVs4c1RVBXbJE4e2Wxo0f74DqAEPENAIIDEnMnu1YS0S9-6R7Jfb7D_ezBCMjXc0hB1nw6XnyGE9JprFc8TMfRmY23aBK-9s5Lf1y0i-tAeE7TEQ7GHGn-IPzl441ZzS8FRT7aiAZMKRVMCGuG2mwTUdv7qmqsPfP1fGoqbXCM2zhm4cTFP0ObIluFa4tZs0VWd8c39tFHO7Ey4ITVnZJRQtK_8eqpx14UztFFcFs0Keo-mgZhZurF2vaGxp7CNHcfCP1CZrvOfwgw1ACiWeDe922wb2cRfsuCUX6tWAj__VrWFe3kg&v=1&imprintMessageId=06d53030-aa6f-4d92-a2af-f0d08b6f958a | US | — | — | unknown |
7844 | msedge.exe | GET | 302 | 104.21.31.33:443 | https://ecocampingmunay.cl/ftx/ | US | — | — | unknown |
7844 | msedge.exe | OPTIONS | 204 | 149.154.167.220:443 | https://api.telegram.org/bot8204916548:AAFI6_OMDTi9spHwZtR_BZFEBLTaNpKO3qQ/sendMessage | VG | — | — | unknown |
7844 | msedge.exe | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=XalSMpjIusR7sedMMDp3%2FgvEvsIuGP1OPs7gKcBd1%2BSgcmU%2Bk2ga4n%2B%2Fj3Oc8ndsNkXGikHOUs9b6R8K0FKj6jKNik3IaNJ4W6Aucq2HR%2FU%3D | US | — | — | unknown |
7844 | msedge.exe | GET | 200 | 45.43.142.3:443 | https://i.ibb.co/yF35Jv2Q/docu-ico.png | FR | image | 1.43 Kb | unknown |
7844 | msedge.exe | GET | 200 | 45.43.142.3:443 | https://i.ibb.co/sJFnm0RH/Icon-pdf-file-svg.png | FR | image | 19.1 Kb | unknown |
7844 | msedge.exe | GET | 200 | 13.107.246.45:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v1/GetGlobalConfig?EdgeChannel=stable&EdgeVersion=133.0.3065.92&ConfigVersion=0 | US | — | 128 Kb | whitelisted |
7844 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | US | text | 768 b | whitelisted |
7844 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:dvT9OE4A1SHBvCs2G_Blj7Ssa0Vw8G5Nh7msgbgHzF8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
7844 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 311 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4292 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4964 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7844 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7844 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7844 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7844 | msedge.exe | 104.18.35.178:443 | us.content.exclaimer.net | CLOUDFLARENET | US | whitelisted |
7844 | msedge.exe | 104.18.22.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
us.content.exclaimer.net |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
ecocampingmunay.cl |
| unknown |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7844 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7844 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7844 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
7844 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ipapi .co in DNS lookup) |
7844 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ipapi .co in DNS lookup) |
7844 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (ipibb) |
7844 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (cdnjstlg) |
7844 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Possible sending an external IP address to Telegram |
7844 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7844 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Possible sending an external IP address to Telegram |
Process | Message |
|---|---|
GoToResolveUnattended.exe | DllMain: DLL_PROCESS_ATTACH: lpReserved=0
|
GoToResolveUnattended.exe | DllMain: DLL_THREAD_ATTACH
|
GoToResolveUnattended.exe | DllMain: DLL_THREAD_ATTACH
|
GoToResolveUnattended.exe | DllMain: DLL_THREAD_ATTACH
|
GoToResolveUnattended.exe | DllMain: DLL_THREAD_ATTACH
|
GoToResolveUnattended.exe | DllMain: DLL_THREAD_ATTACH
|
GoToResolveUnattended.exe | DllMain: DLL_THREAD_DETACH
|
GoToResolveProcessChecker.exe | DllMain: DLL_PROCESS_ATTACH: lpReserved=0
|
GoToResolveProcessChecker.exe | DllMain: DLL_PROCESS_ATTACH: lpReserved=0
|
GoToResolveProcessChecker.exe | DllMain: DLL_THREAD_ATTACH
|