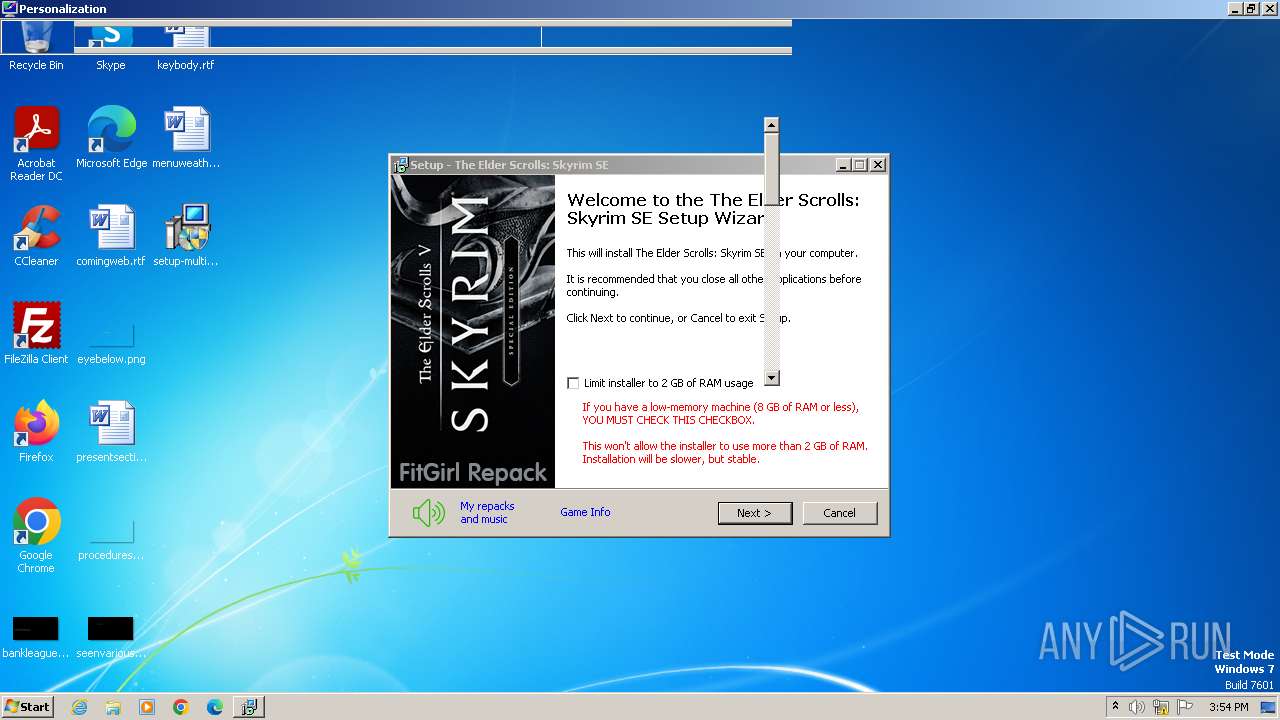
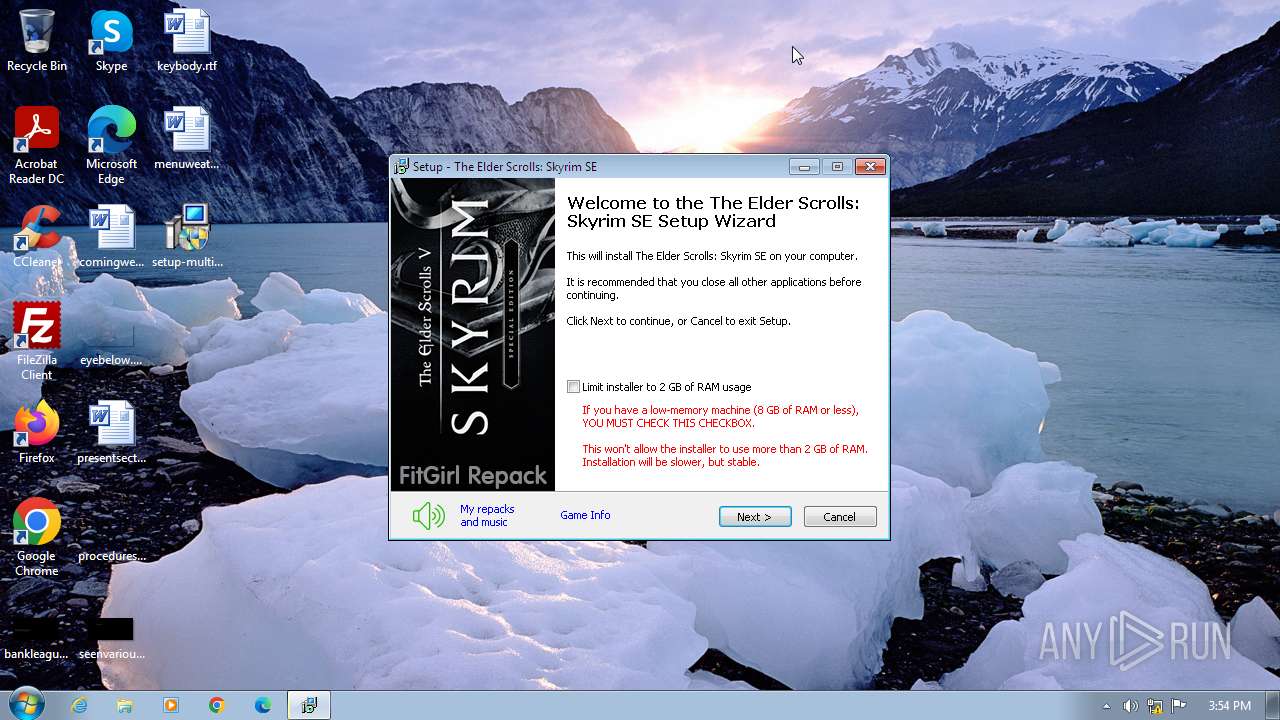
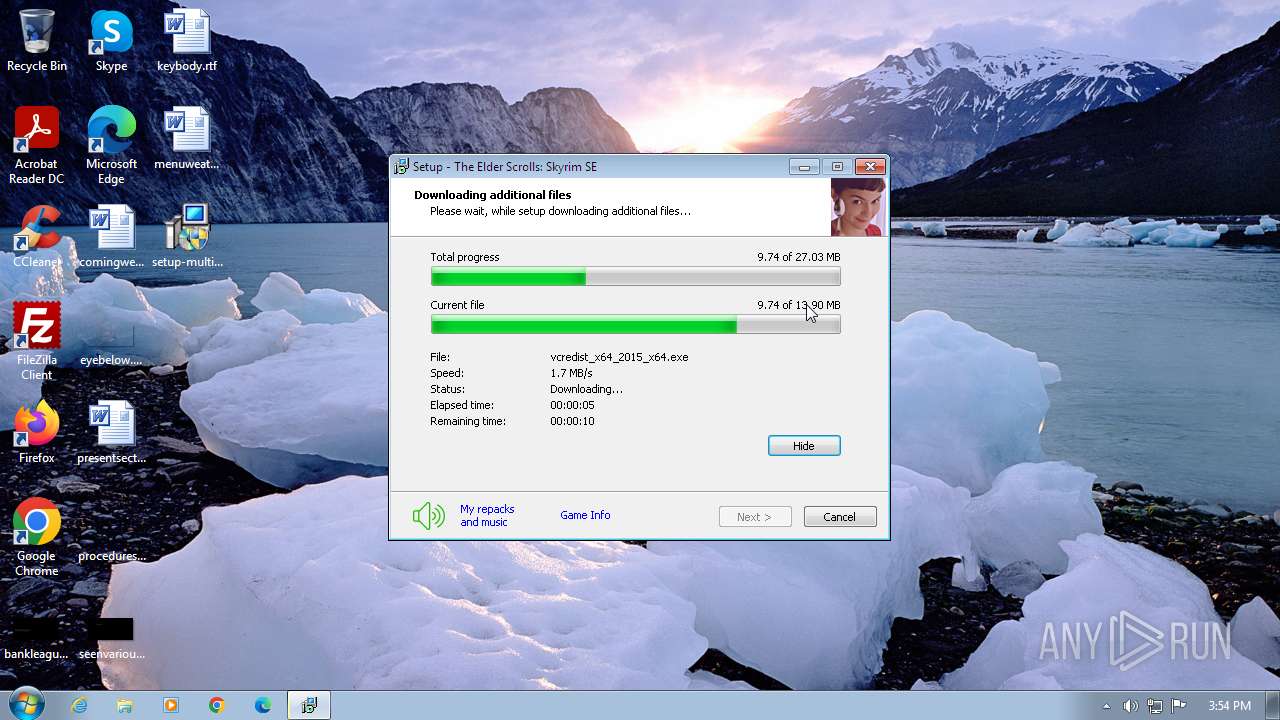
| File name: | setup-multi2.exe |
| Full analysis: | https://app.any.run/tasks/f2138e0d-0df5-4d76-bb84-5e97c470a25b |
| Verdict: | Malicious activity |
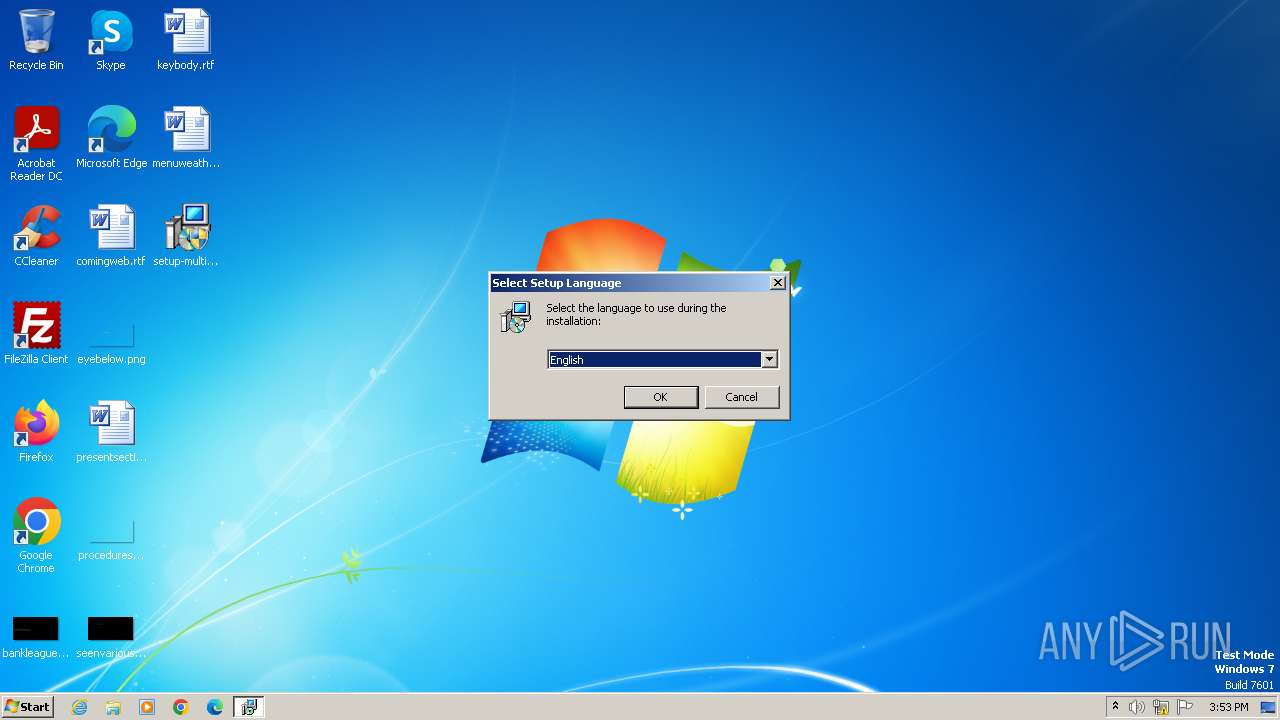
| Analysis date: | November 05, 2023, 15:53:47 |
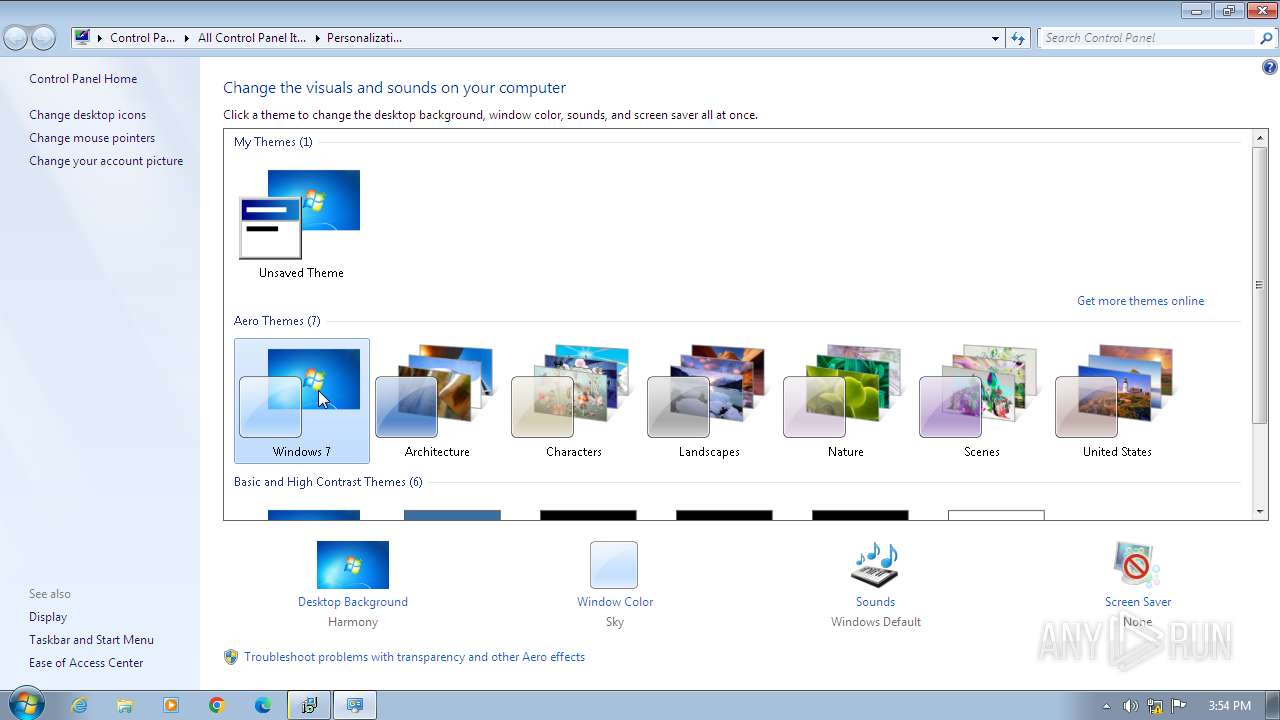
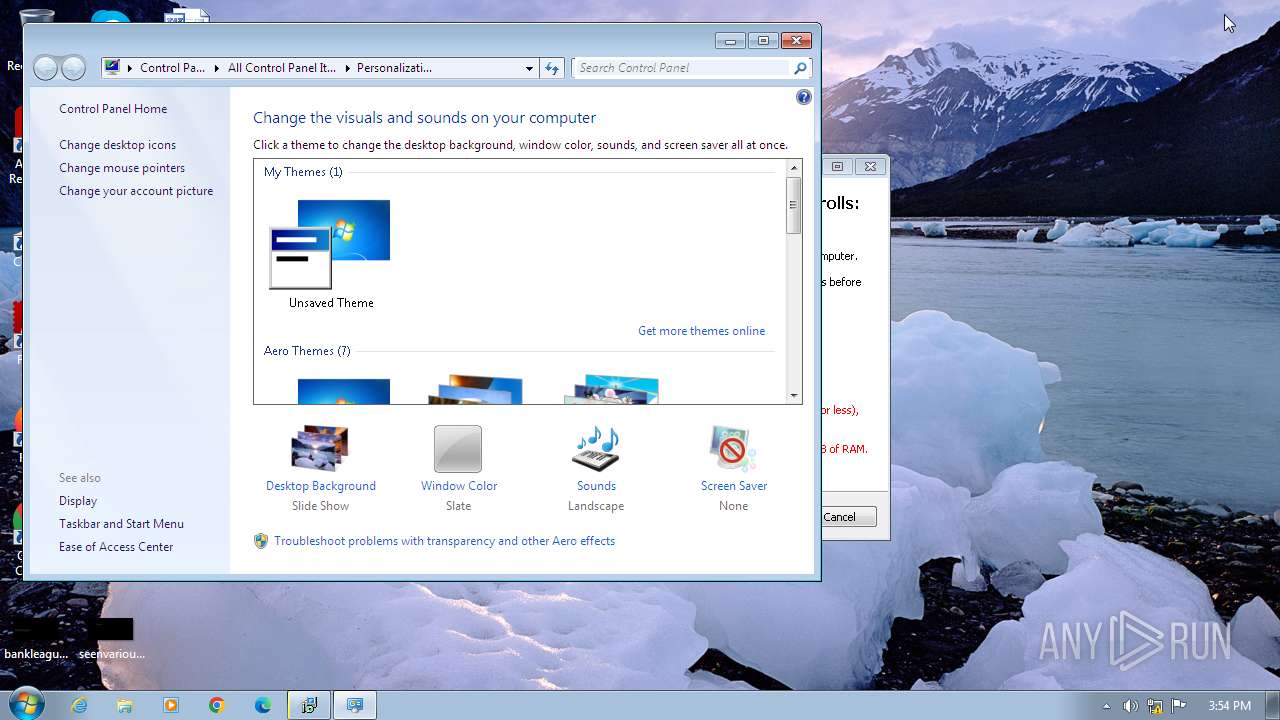
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D8679FE45AA43E0E293A31E411AB6FDC |
| SHA1: | B14B24AA07517E01ED7784F157839DA27B4D3A2A |
| SHA256: | 9DCEC90D39CAB66C8E89290DA0C932A9184009AD4EE7C9DEF4FFFE1CF7D75D01 |
| SSDEEP: | 98304:9Q/SMPUQ+/uMLYOCFpAOLX46e/h//oShmxel+YxjyqcQmJQoUa2X8zJneB+peJNk:YRj4j3Q |
MALICIOUS
Drops the executable file immediately after the start
- setup-multi2.exe (PID: 3164)
- setup-multi2.tmp (PID: 3496)
- csc.exe (PID: 1604)
- csc.exe (PID: 556)
- csc.exe (PID: 1364)
- csc.exe (PID: 2444)
- csc.exe (PID: 2184)
- csc.exe (PID: 2636)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 1608)
- sdiagnhost.exe (PID: 1812)
SUSPICIOUS
Process drops legitimate windows executable
- msdt.exe (PID: 1436)
- setup-multi2.tmp (PID: 3496)
Reads the Windows owner or organization settings
- setup-multi2.tmp (PID: 3496)
Application launched itself
- msdt.exe (PID: 3712)
Reads the Internet Settings
- msdt.exe (PID: 3712)
- sdiagnhost.exe (PID: 1608)
- sdiagnhost.exe (PID: 1812)
- setup-multi2.tmp (PID: 3496)
Uses .NET C# to load dll
- sdiagnhost.exe (PID: 1608)
- sdiagnhost.exe (PID: 1812)
Reads settings of System Certificates
- msdt.exe (PID: 1436)
- setup-multi2.tmp (PID: 3496)
Reads security settings of Internet Explorer
- setup-multi2.tmp (PID: 3496)
Checks Windows Trust Settings
- setup-multi2.tmp (PID: 3496)
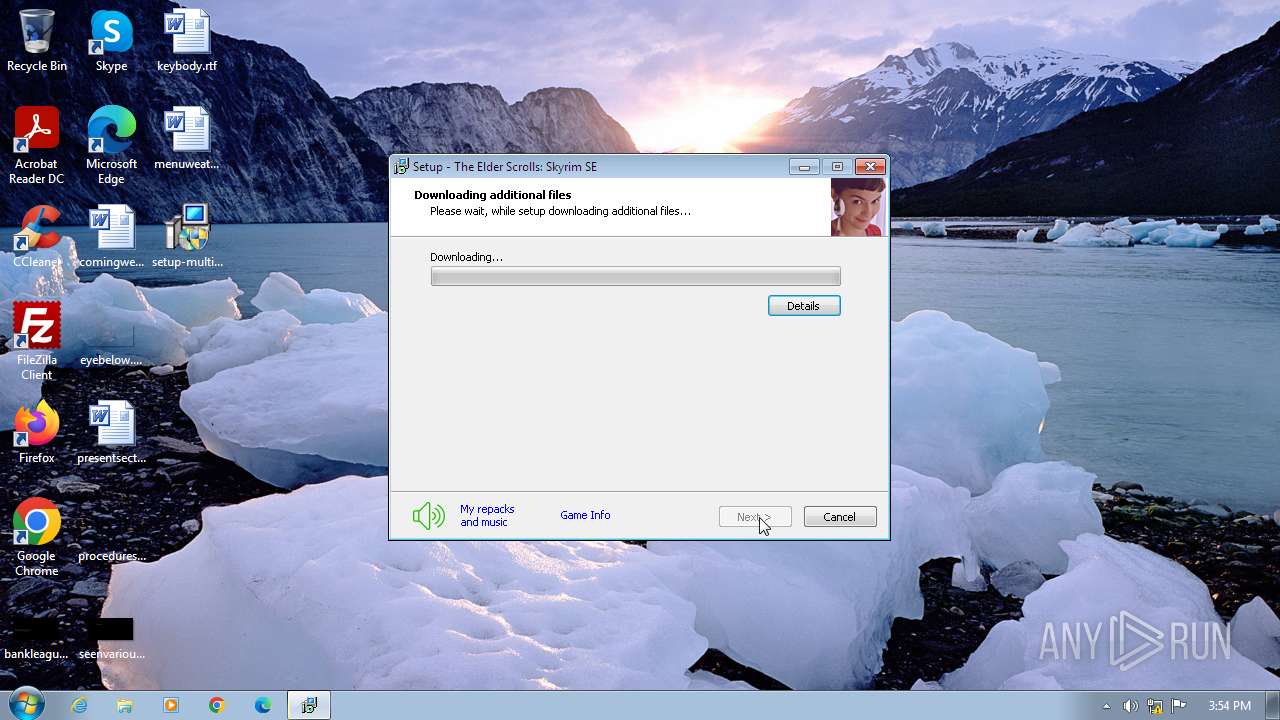
Process requests binary or script from the Internet
- setup-multi2.tmp (PID: 3496)
INFO
Create files in a temporary directory
- setup-multi2.exe (PID: 3164)
- msdt.exe (PID: 1436)
- setup-multi2.tmp (PID: 3496)
- msdt.exe (PID: 3712)
- sdiagnhost.exe (PID: 1608)
- csc.exe (PID: 1604)
- cvtres.exe (PID: 1660)
- csc.exe (PID: 1364)
- csc.exe (PID: 556)
- cvtres.exe (PID: 752)
- sdiagnhost.exe (PID: 1812)
- csc.exe (PID: 2444)
- cvtres.exe (PID: 1348)
- cvtres.exe (PID: 2328)
- csc.exe (PID: 2184)
- cvtres.exe (PID: 3800)
- csc.exe (PID: 2636)
- cvtres.exe (PID: 2392)
Checks supported languages
- setup-multi2.exe (PID: 3164)
- setup-multi2.tmp (PID: 3496)
- cvtres.exe (PID: 1660)
- csc.exe (PID: 1604)
- csc.exe (PID: 1364)
- cvtres.exe (PID: 1348)
- cvtres.exe (PID: 752)
- csc.exe (PID: 2444)
- cvtres.exe (PID: 2328)
- csc.exe (PID: 556)
- csc.exe (PID: 2184)
- cvtres.exe (PID: 3800)
- csc.exe (PID: 2636)
- cvtres.exe (PID: 2392)
- wmpnscfg.exe (PID: 1008)
Drops the executable file immediately after the start
- msdt.exe (PID: 1436)
Reads security settings of Internet Explorer
- sdiagnhost.exe (PID: 1608)
- msdt.exe (PID: 1436)
- sdiagnhost.exe (PID: 1812)
Reads the computer name
- setup-multi2.tmp (PID: 3496)
- wmpnscfg.exe (PID: 1008)
Manual execution by a user
- msdt.exe (PID: 3712)
- wmpnscfg.exe (PID: 1008)
Reads the machine GUID from the registry
- csc.exe (PID: 1604)
- cvtres.exe (PID: 1660)
- csc.exe (PID: 1364)
- cvtres.exe (PID: 1348)
- csc.exe (PID: 556)
- cvtres.exe (PID: 752)
- csc.exe (PID: 2444)
- csc.exe (PID: 2184)
- cvtres.exe (PID: 3800)
- csc.exe (PID: 2636)
- cvtres.exe (PID: 2392)
- cvtres.exe (PID: 2328)
- setup-multi2.tmp (PID: 3496)
- wmpnscfg.exe (PID: 1008)
Creates files or folders in the user directory
- msdt.exe (PID: 1436)
Creates files in the program directory
- msdt.exe (PID: 1436)
Checks proxy server information
- setup-multi2.tmp (PID: 3496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
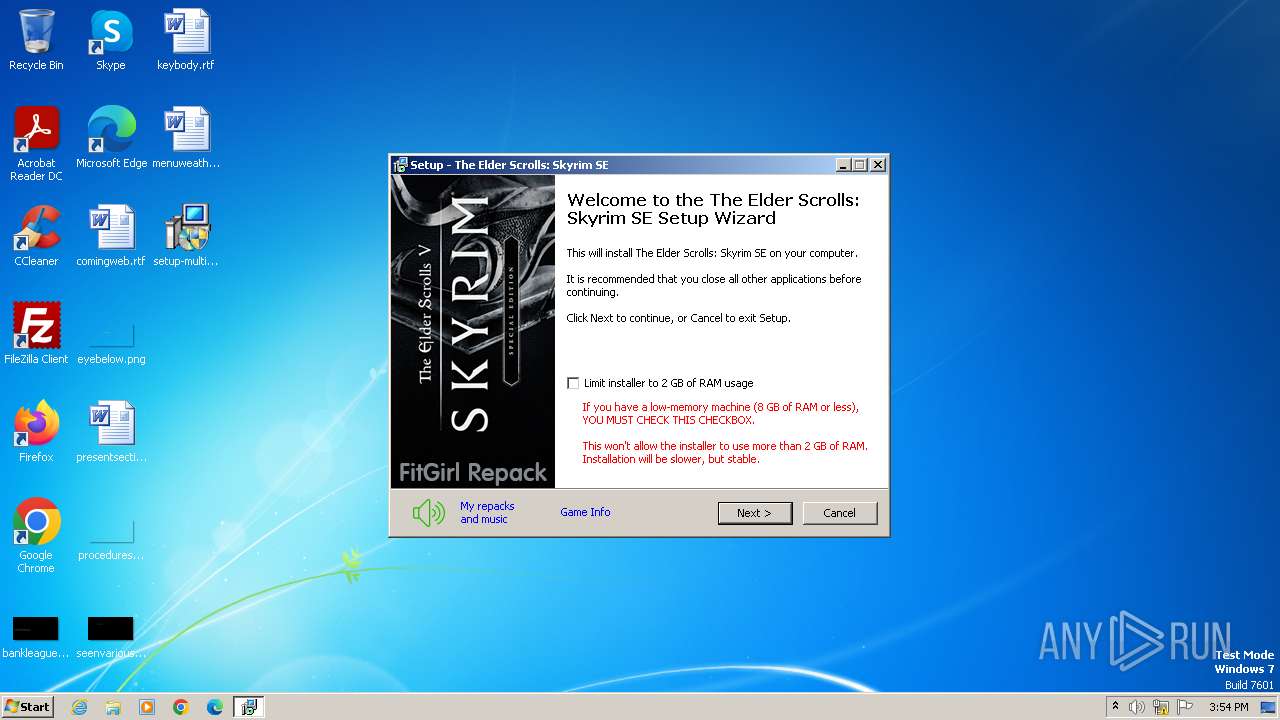
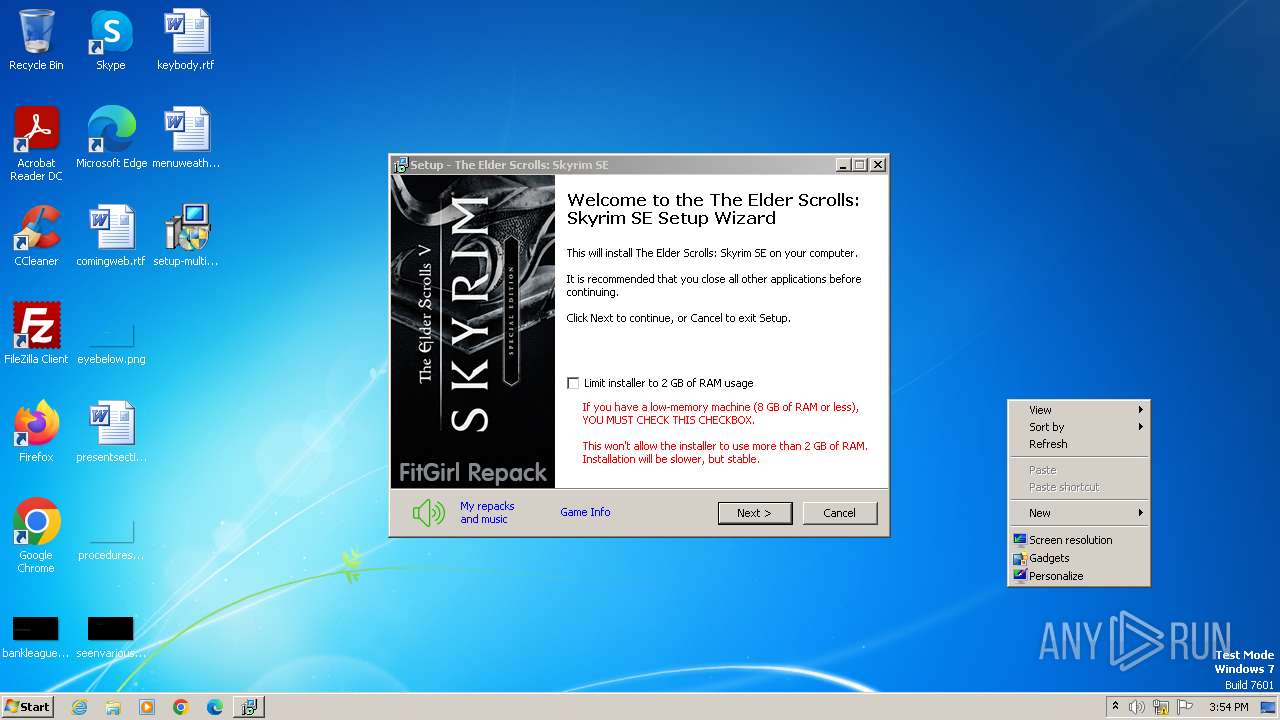
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:02 07:04:04+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86016 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16478 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
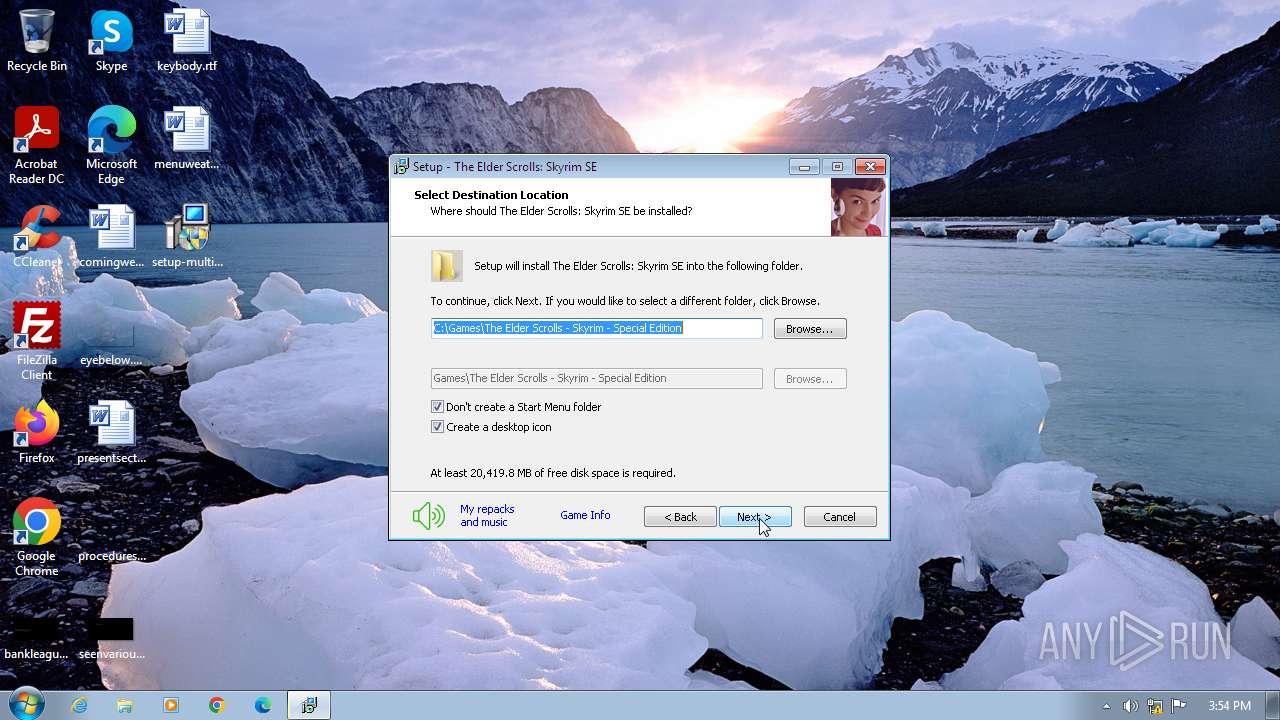
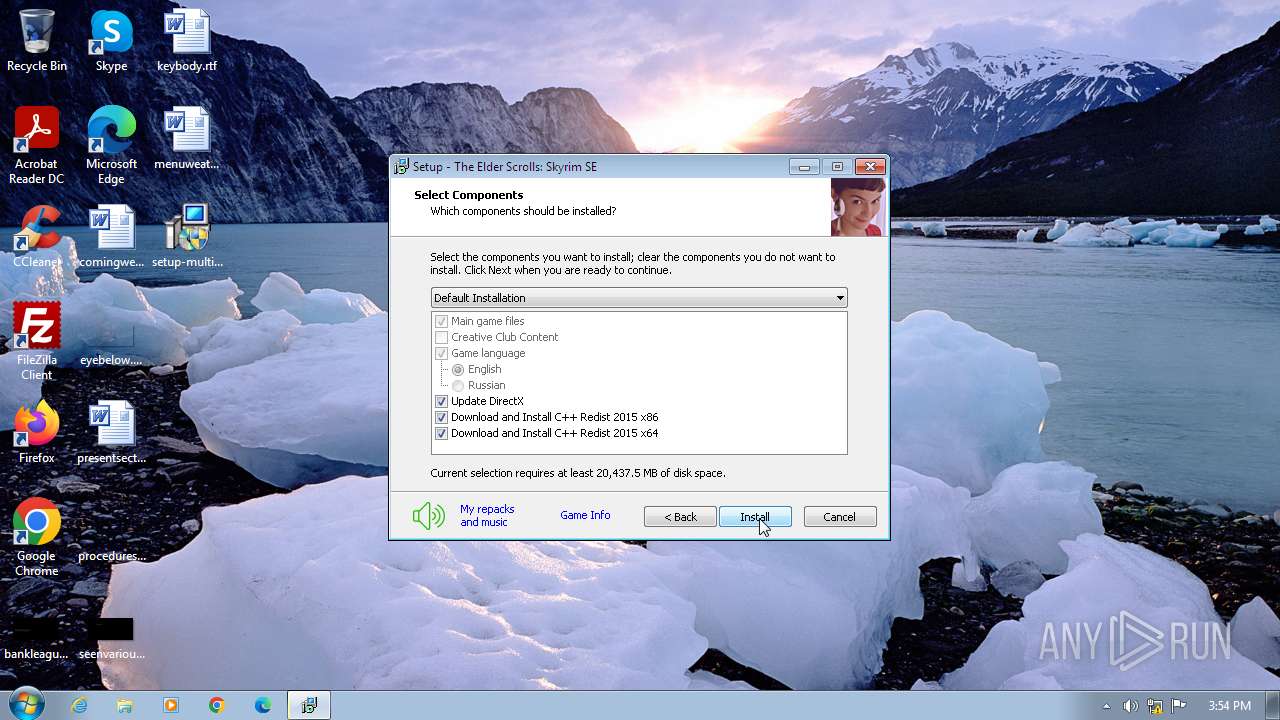
| FileDescription: | The Elder Scrolls: Skyrim SE Setup |
| FileVersion: | |
| LegalCopyright: | FitGirl |
| ProductName: | The Elder Scrolls: Skyrim SE |
| ProductVersion: |
Total processes
69
Monitored processes
23
Malicious processes
6
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\irmcylph.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 752 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESF9E6.tmp" "c:\Users\admin\AppData\Local\Temp\CSCF9E5.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1348 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESF969.tmp" "c:\Users\admin\AppData\Local\Temp\CSCF959.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1364 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\z53y4ut8.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
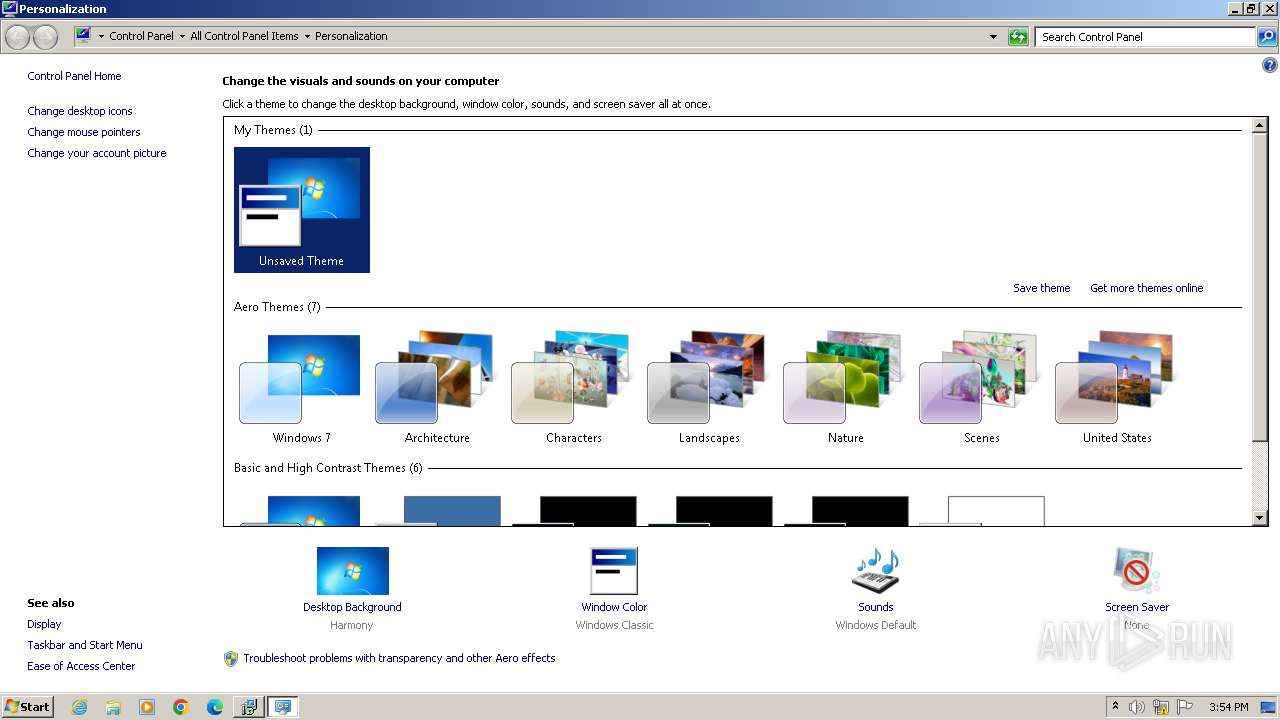
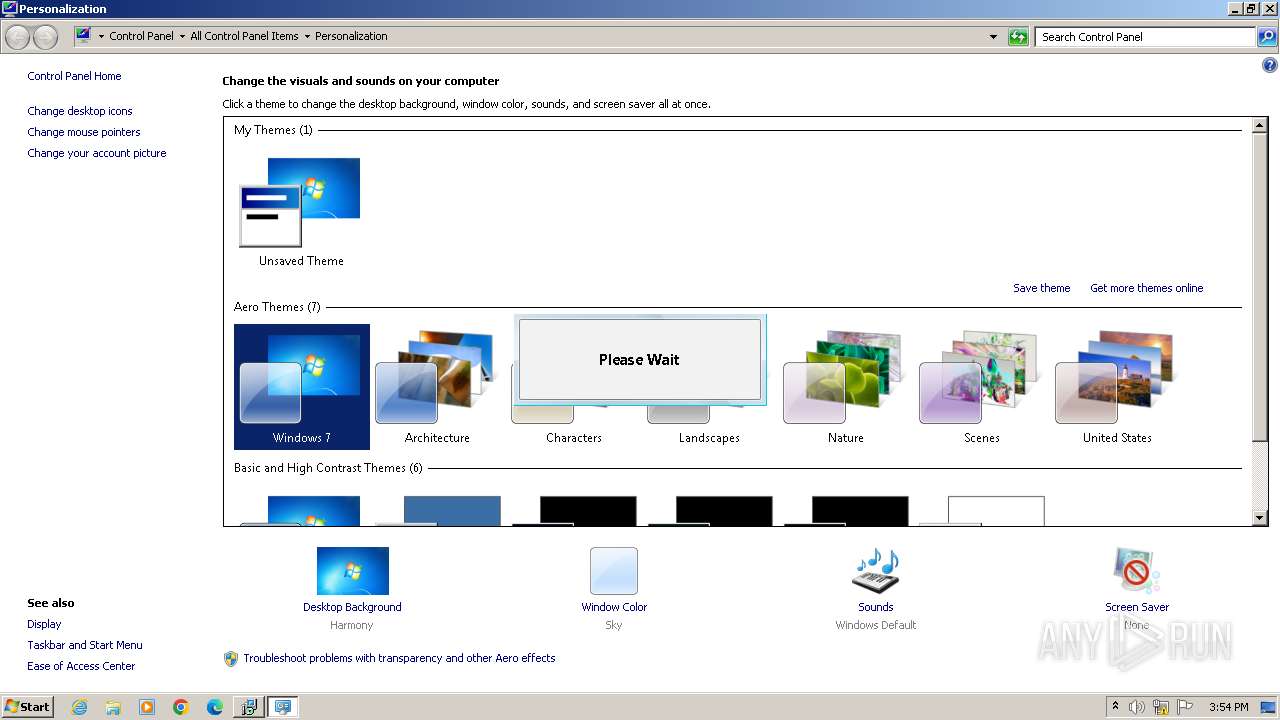
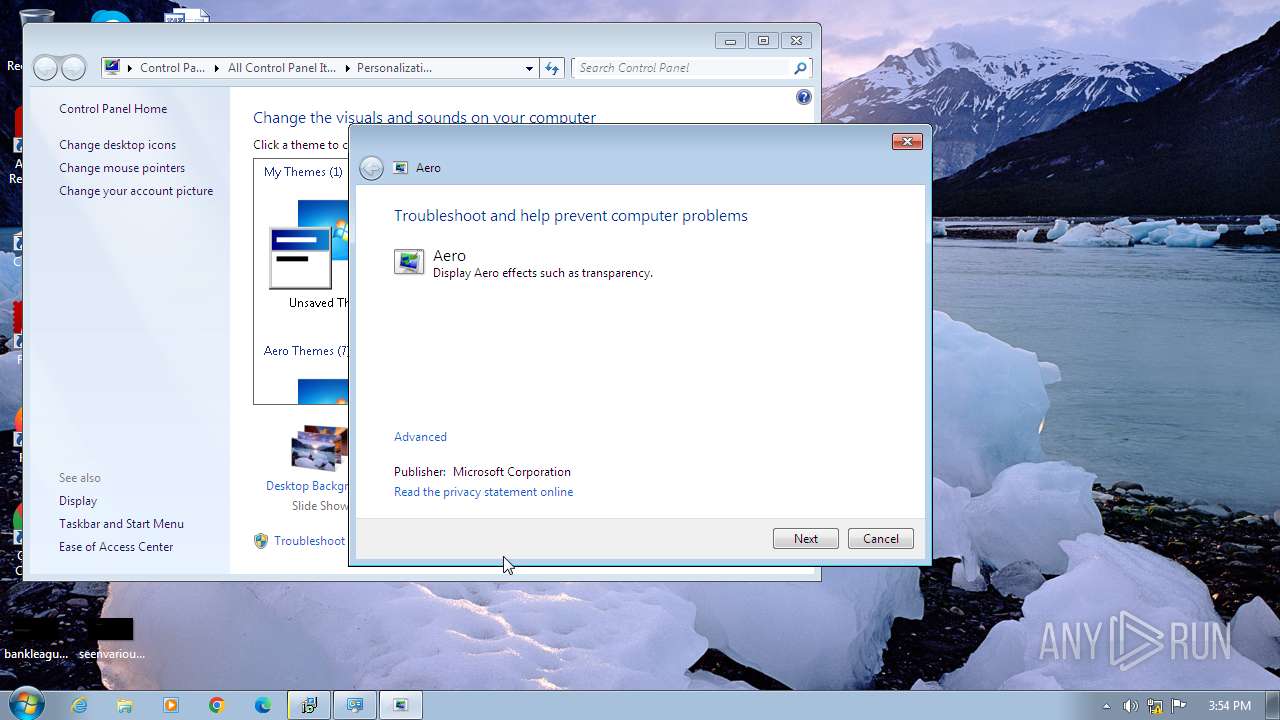
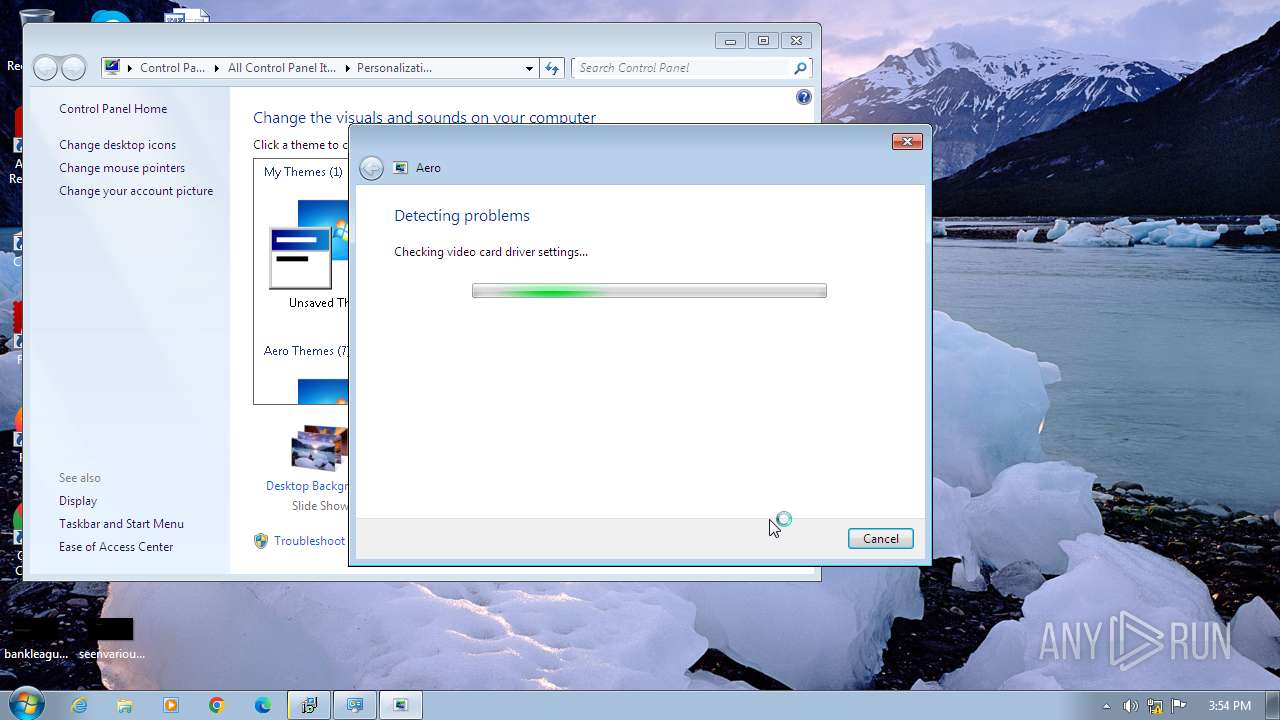
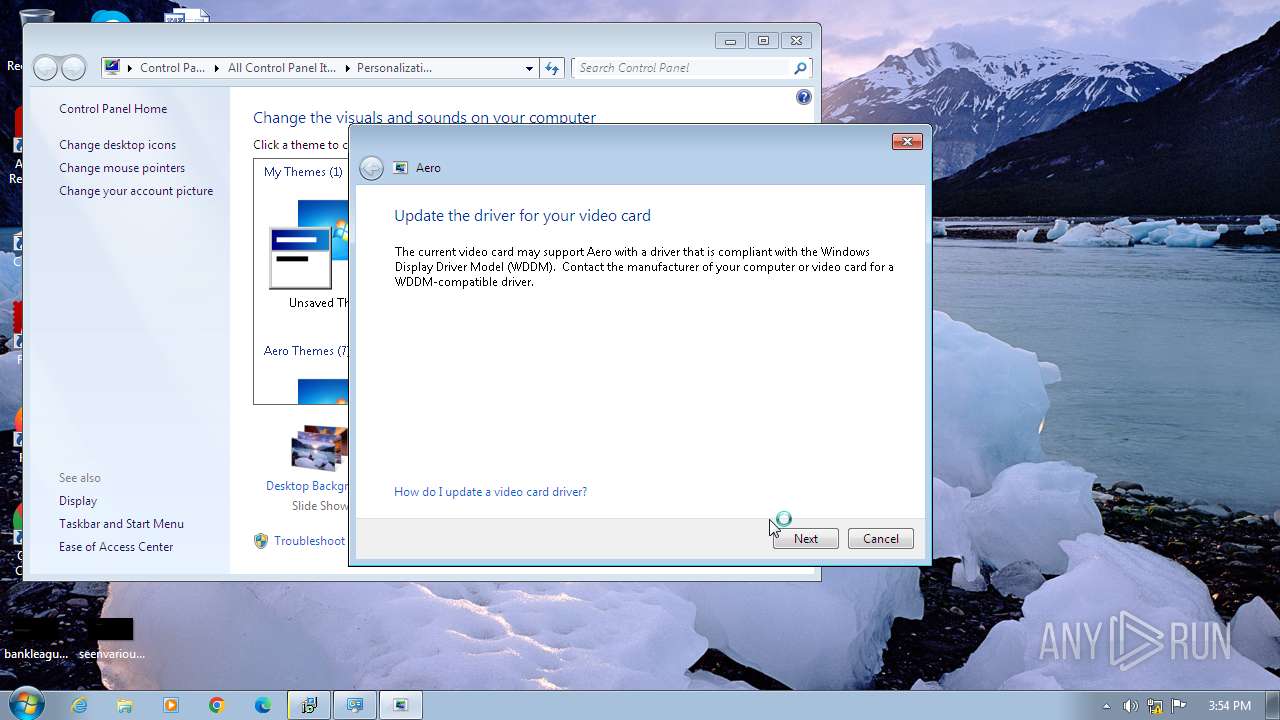
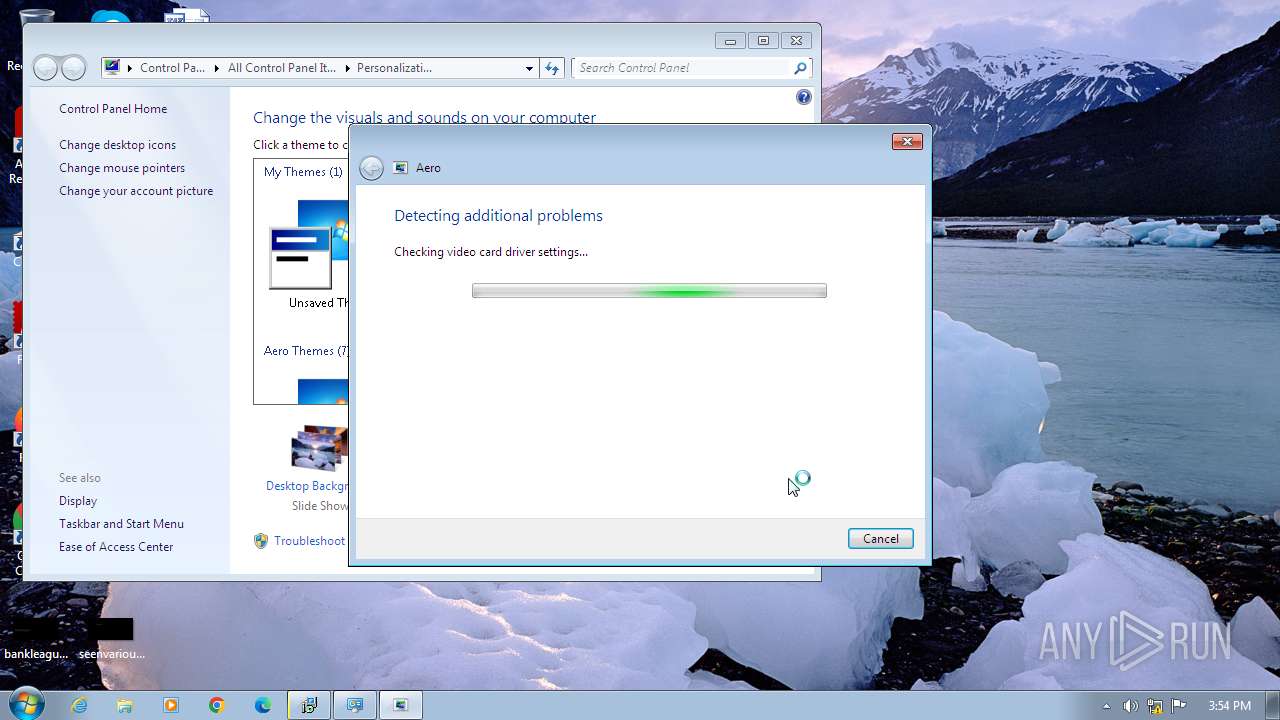
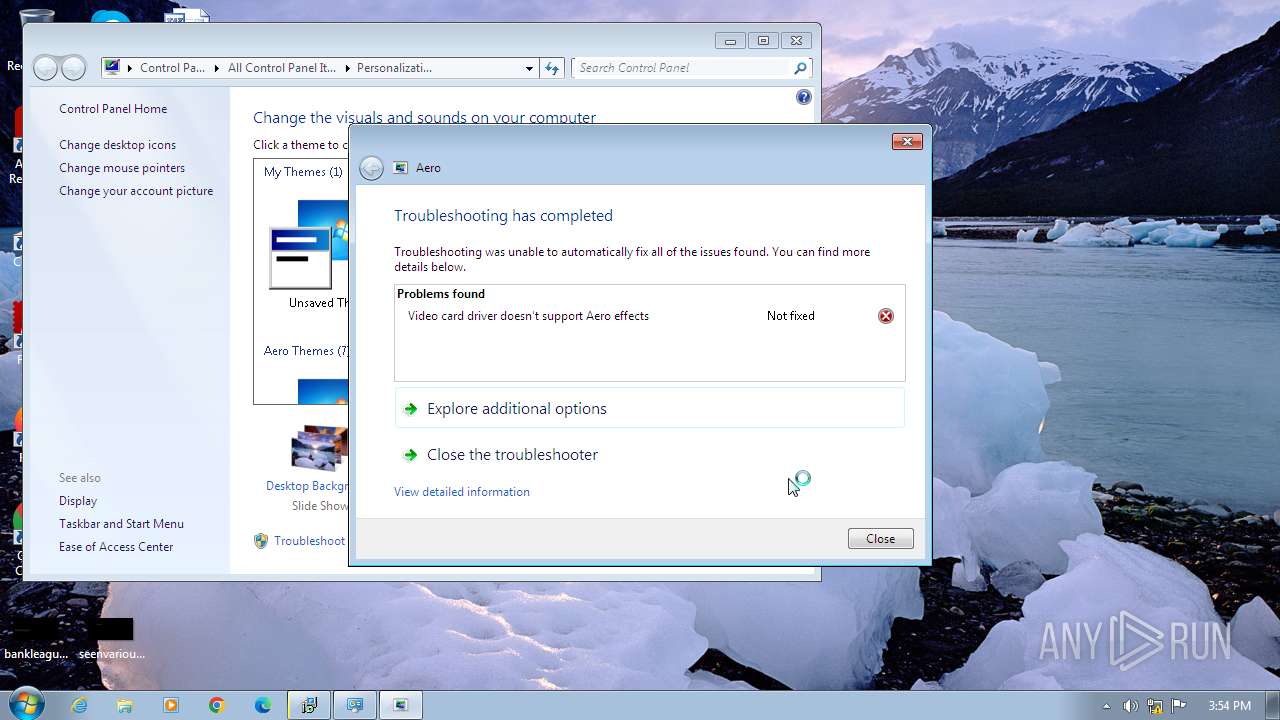
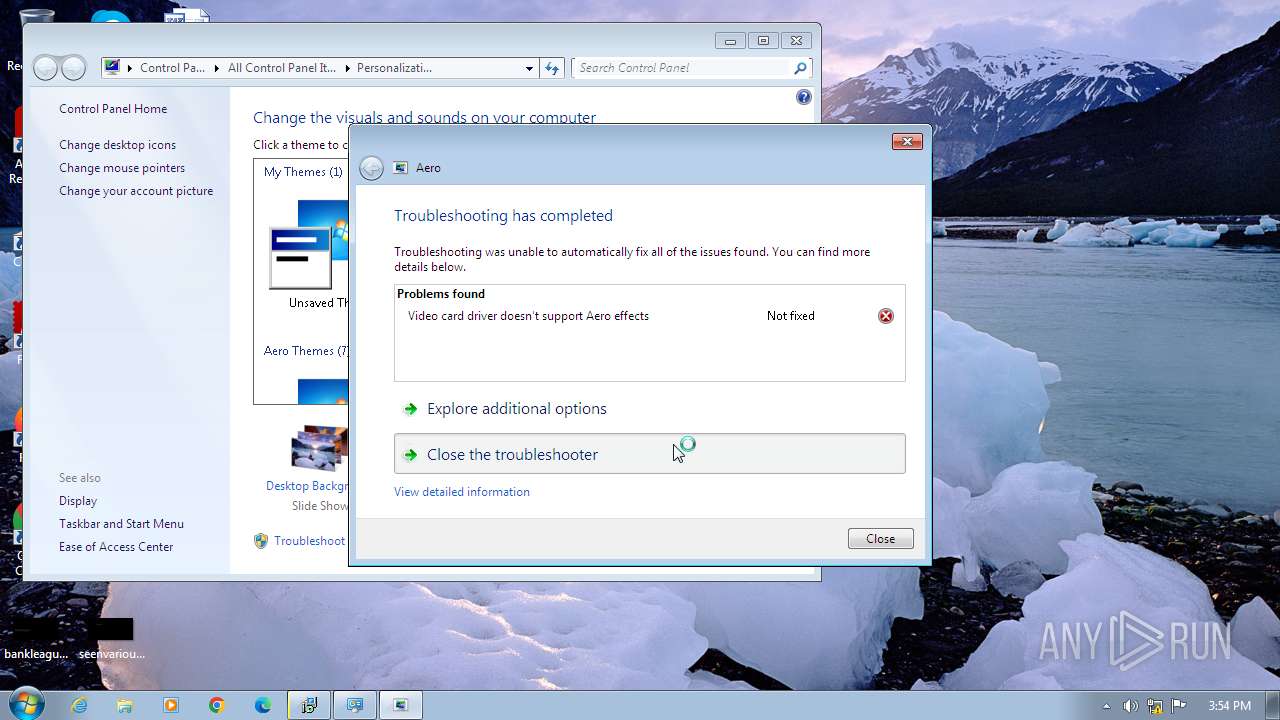
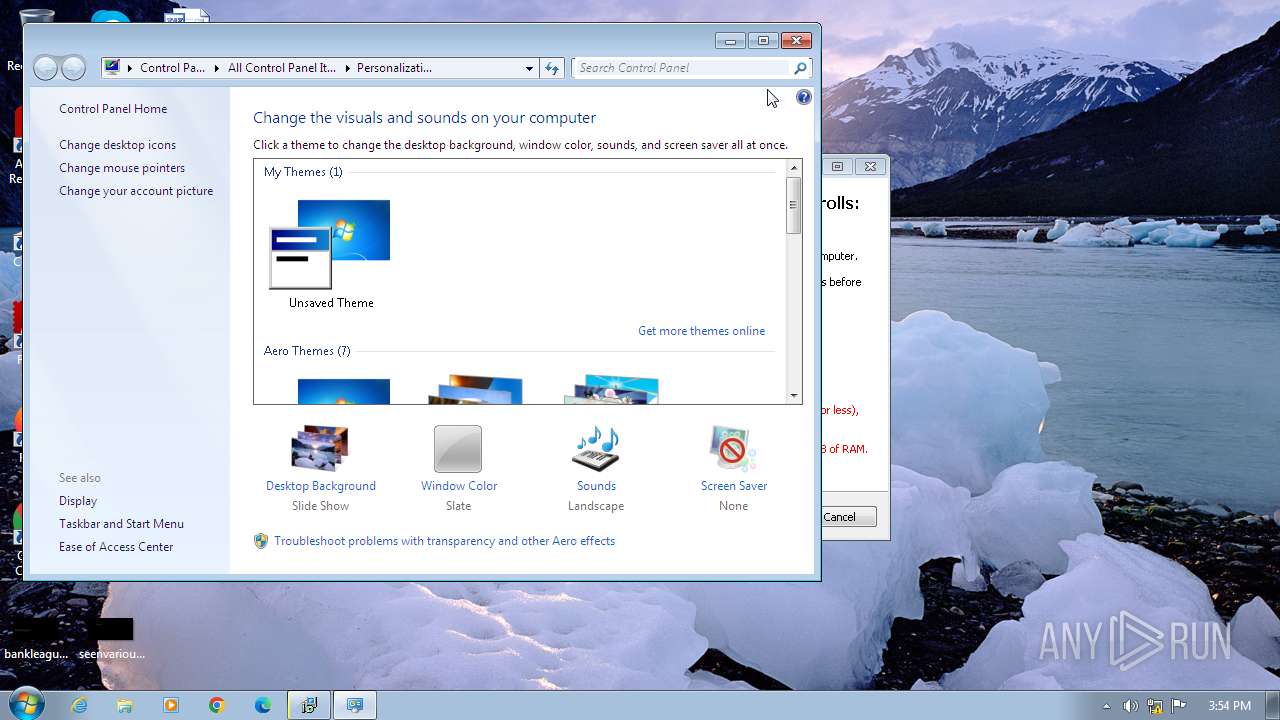
| 1436 | "C:\Windows\system32\msdt.exe" -path "C:\Windows\Diagnostics\Index\AeroDiagnostic.xml" -elevated yes | C:\Windows\System32\msdt.exe | msdt.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Diagnostics Troubleshooting Wizard Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1604 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\m6ldlki_.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1608 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1660 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESF8DD.tmp" "c:\Users\admin\AppData\Local\Temp\CSCF8DC.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1812 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
13 526
Read events
13 427
Write events
93
Delete events
6
Modification events
| (PID) Process: | (3496) setup-multi2.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (3712) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3712) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3712) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3712) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1436) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1608) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1608) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1608) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1608) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
49
Suspicious files
43
Text files
98
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3496 | setup-multi2.tmp | C:\Users\admin\AppData\Local\Temp\is-4TAUU.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 3496 | setup-multi2.tmp | C:\Users\admin\AppData\Local\Temp\is-4TAUU.tmp\idp.dll | executable | |
MD5:AF555AC9C073F88FE5BF0D677F085025 | SHA256:F4FC0187491A9CB89E233197FF72C2405B5EC02E8B8EA640EE68D034DDBC44BB | |||
| 3164 | setup-multi2.exe | C:\Users\admin\AppData\Local\Temp\is-4V28V.tmp\setup-multi2.tmp | executable | |
MD5:AE9890548F2FCAB56A4E9AE446F55B3F | SHA256:09AF8004B85478E1ECA09FA4CB5E3081DDDCB2F68A353F3EF6849D92BE47B449 | |||
| 3496 | setup-multi2.tmp | C:\Users\admin\AppData\Local\Temp\is-4TAUU.tmp\ISDone.dll | executable | |
MD5:4FEAFA8B5E8CDB349125C8AF0AC43974 | SHA256:BB8A0245DCC5C10A1C7181BAD509B65959855009A8105863EF14F2BB5B38AC71 | |||
| 3496 | setup-multi2.tmp | C:\Users\admin\AppData\Local\Temp\is-4TAUU.tmp\wintb.dll | executable | |
MD5:9436DF49E08C83BAD8DDC906478C2041 | SHA256:1910537AA95684142250CA0C7426A0B5F082E39F6FBDBDBA649AECB179541435 | |||
| 3496 | setup-multi2.tmp | C:\Users\admin\AppData\Local\Temp\is-4TAUU.tmp\innocallback.dll | executable | |
MD5:1C55AE5EF9980E3B1028447DA6105C75 | SHA256:6AFA2D104BE6EFE3D9A2AB96DBB75DB31565DAD64DD0B791E402ECC25529809F | |||
| 3496 | setup-multi2.tmp | C:\Users\admin\AppData\Local\Temp\is-4TAUU.tmp\BASS.dll | executable | |
MD5:8005750EC63EB5292884AD6183AE2E77 | SHA256:DF9F56C4DA160101567B0526845228EE481EE7D2F98391696FA27FE41F8ACF15 | |||
| 3496 | setup-multi2.tmp | C:\Users\admin\AppData\Local\Temp\is-4TAUU.tmp\cls-lollypop.dll | executable | |
MD5:0EF04BC15FD1B28975AFF2951B857F03 | SHA256:F84677643D9977AA1E8A4AA8C85A12665D29A4E8292485A0B4DF846DD161F824 | |||
| 3496 | setup-multi2.tmp | C:\Users\admin\AppData\Local\Temp\is-4TAUU.tmp\cls-lollypop2.dll | executable | |
MD5:9E1E200472D66356A4AE5D597B01DABC | SHA256:87DF573AC240E09EA4941E169FB2D15D5316A1B0E053446B8144E04B1154F061 | |||
| 3496 | setup-multi2.tmp | C:\Users\admin\AppData\Local\Temp\is-4TAUU.tmp\cls-lollypop_x86.exe | executable | |
MD5:3527C6739C46F4EE1CFB6B48E1407883 | SHA256:724C6E07180E321298B4EA4405C3F7536C524D9826D24F5D6FC50BCB0EF8F723 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
8
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3496 | setup-multi2.tmp | HEAD | 302 | 2.19.100.212:80 | http://download.microsoft.com/download/9/3/F/93FCF1E7-E6A4-478B-96E7-D4B285925B00/vc_redist.x64.exe | unknown | — | — | unknown |
3496 | setup-multi2.tmp | HEAD | 302 | 2.19.100.212:80 | http://download.microsoft.com/download/9/3/F/93FCF1E7-E6A4-478B-96E7-D4B285925B00/vc_redist.x86.exe | unknown | — | — | unknown |
3496 | setup-multi2.tmp | GET | 302 | 2.19.100.212:80 | http://download.microsoft.com/download/9/3/F/93FCF1E7-E6A4-478B-96E7-D4B285925B00/vc_redist.x64.exe | unknown | — | — | unknown |
3496 | setup-multi2.tmp | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
3496 | setup-multi2.tmp | GET | 200 | 8.253.95.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b54a2c574b0476d0 | unknown | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3496 | setup-multi2.tmp | 2.19.100.212:80 | download.microsoft.com | AKAMAI-AS | DE | unknown |
3496 | setup-multi2.tmp | 2.19.100.212:443 | download.microsoft.com | AKAMAI-AS | DE | unknown |
3496 | setup-multi2.tmp | 8.253.95.121:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
3496 | setup-multi2.tmp | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|