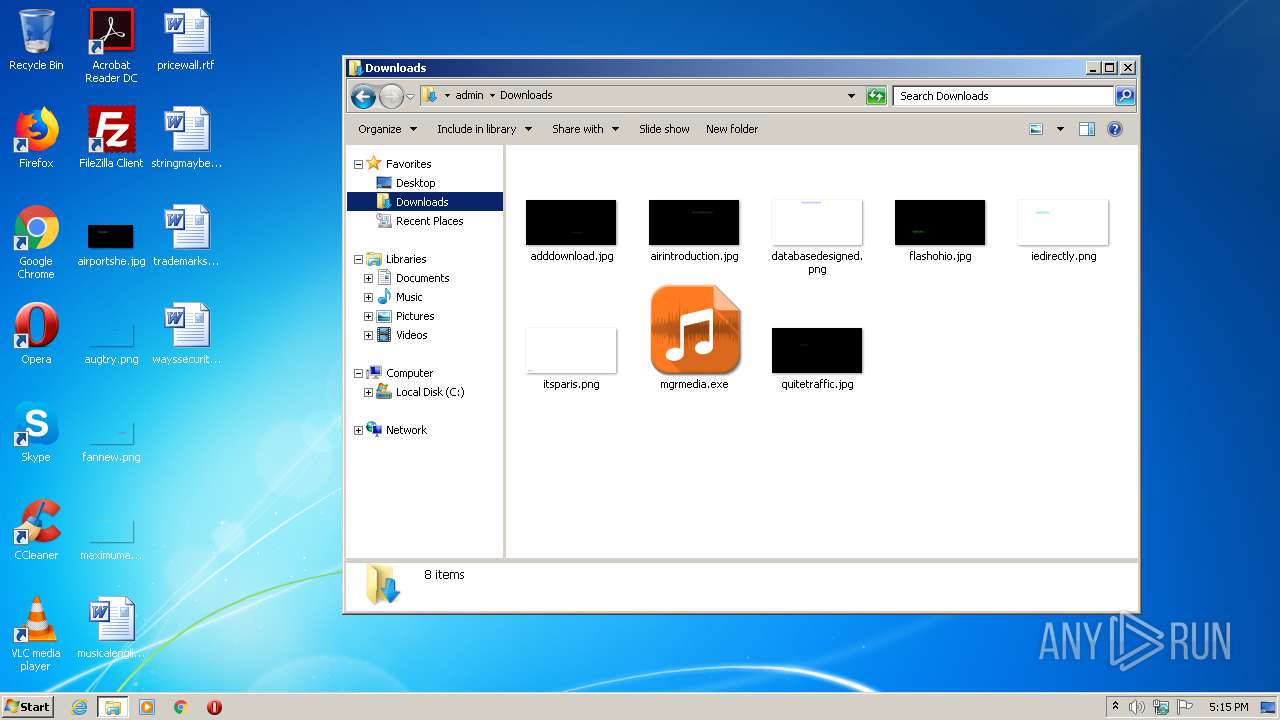
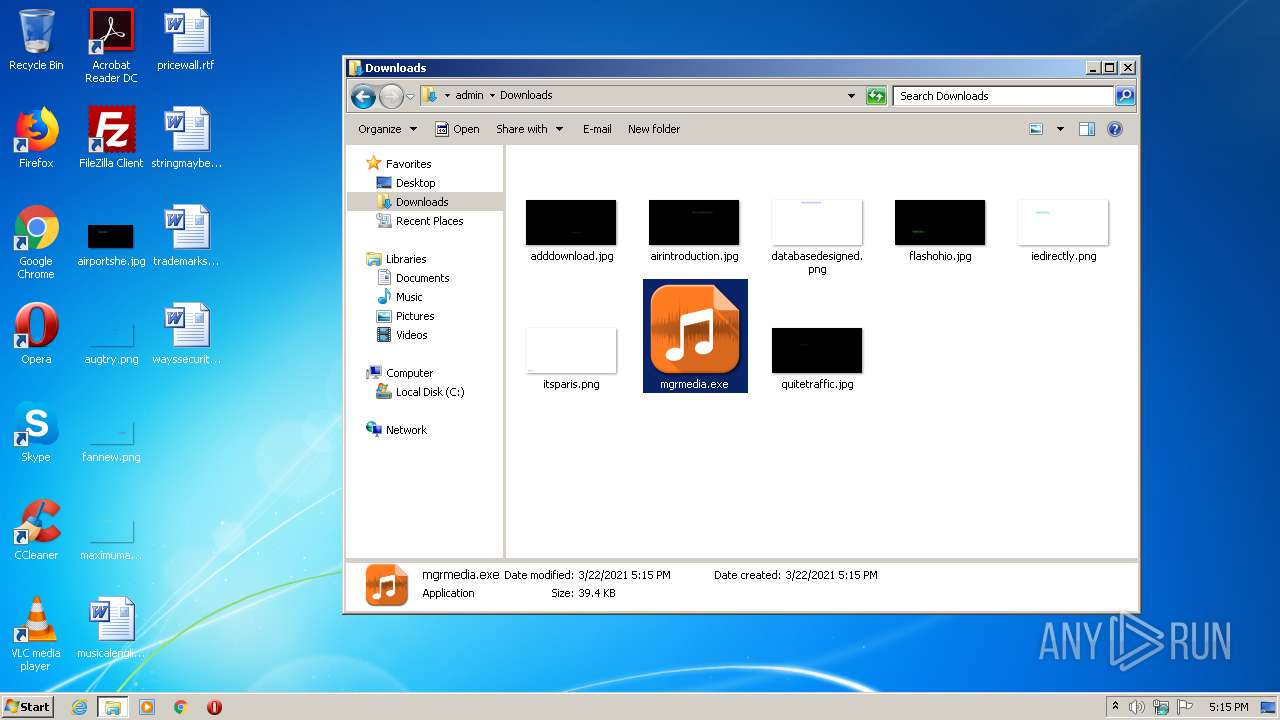
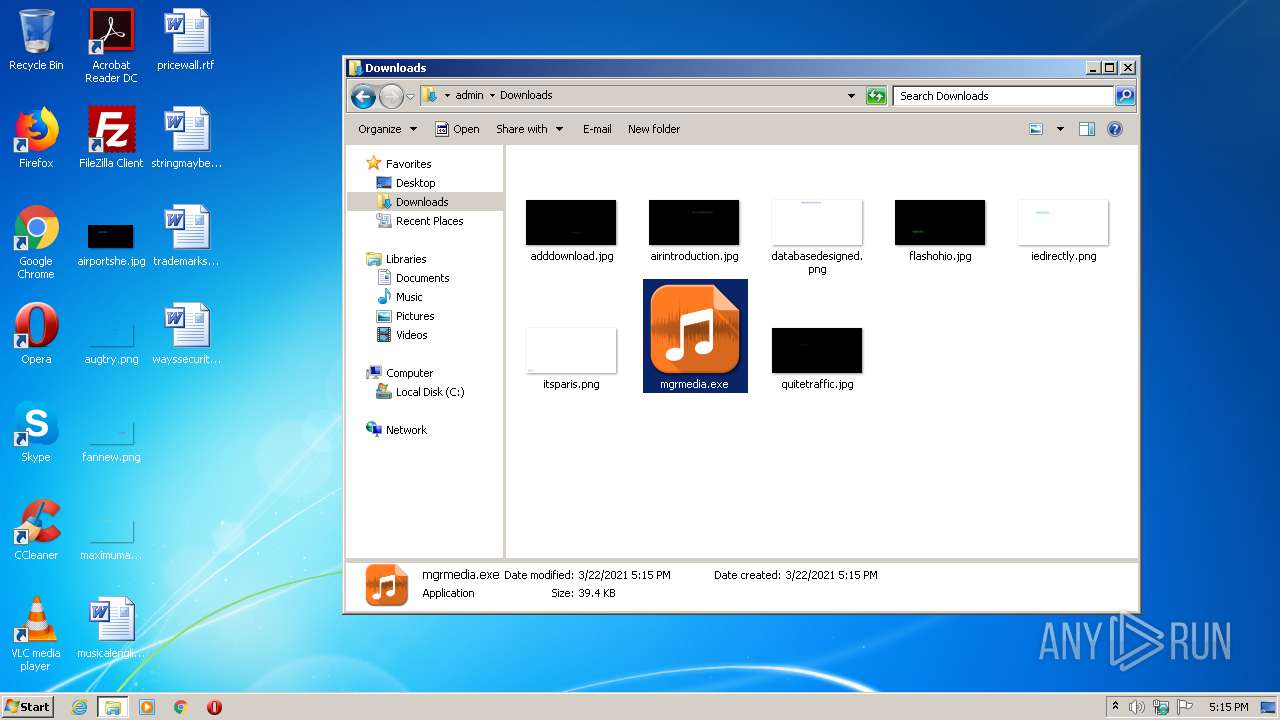
| File name: | mgrmedia.exe |
| Full analysis: | https://app.any.run/tasks/e030e72f-ea84-4d88-8349-0de4eda3803a |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2021, 17:14:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0A3F02191D65ECC0CB979EF07E8EF08E |
| SHA1: | 5C5092AEAD7989AFE64D05BDD75DA51E970DC3C6 |
| SHA256: | 9DCCF5416B67CFF495EEFA5357C151840407D6F94F87E9D295B3F7574CA59CF8 |
| SSDEEP: | 768:uxV4/V/pghFbvKW/NWDhHi571KTX3AGlc7uPKg:AVM9YKHDxmBKTXZ6g |
MALICIOUS
Starts Visual C# compiler
- sdiagnhost.exe (PID: 2064)
SUSPICIOUS
Reads internet explorer settings
- mgrmedia.exe (PID: 2328)
- mgrmedia.exe (PID: 3444)
Executed via COM
- sdiagnhost.exe (PID: 2064)
Drops a file with too old compile date
- msdt.exe (PID: 4032)
Executable content was dropped or overwritten
- msdt.exe (PID: 4032)
INFO
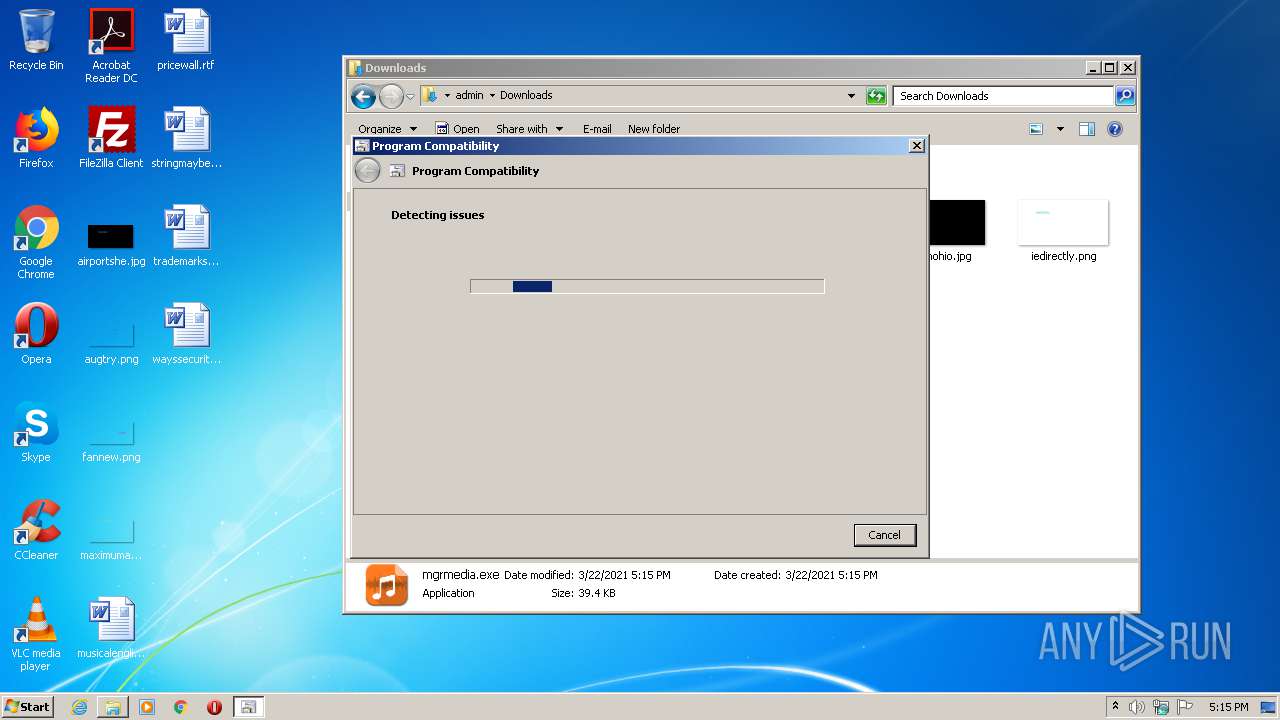
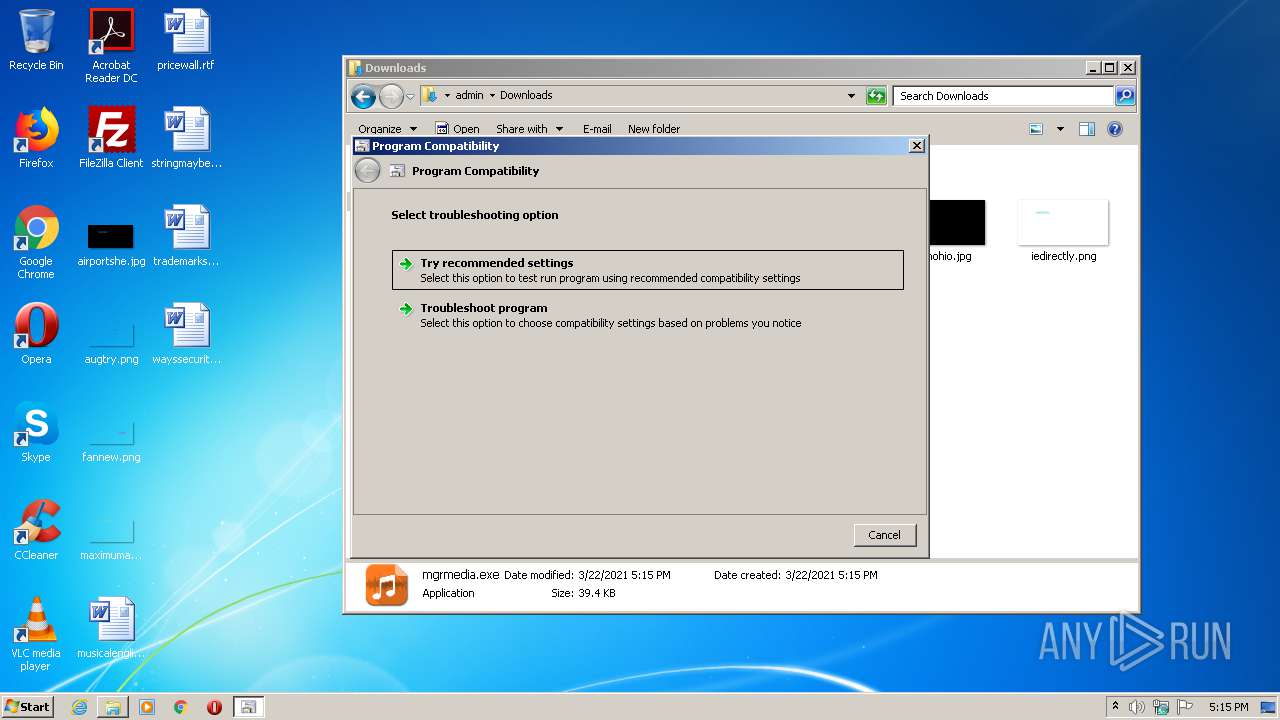
Manual execution by user
- explorer.exe (PID: 1784)
- pcwrun.exe (PID: 928)
- mgrmedia.exe (PID: 3444)
Reads settings of System Certificates
- mgrmedia.exe (PID: 3444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:12:28 14:29:15+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 5632 |
| InitializedDataSize: | 25600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3422 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Web Manager online |
| CompanyName: | - |
| FileDescription: | Web Manager |
| FileVersion: | 1.0.0.0 |
| InternalName: | WebMed.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | WebMed.exe |
| ProductName: | Web Med online |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Dec-2020 13:29:15 |
| Debug artifacts: |
|
| Comments: | Web Manager online |
| CompanyName: | - |
| FileDescription: | Web Manager |
| FileVersion: | 1.0.0.0 |
| InternalName: | WebMed.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | WebMed.exe |
| ProductName: | Web Med online |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 28-Dec-2020 13:29:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00001428 | 0x00001600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.10373 |
.rsrc | 0x00004000 | 0x0000612C | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.85418 |
.reloc | 0x0000C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.51664 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
51
Monitored processes
12
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | C:\Windows\system32\pcwrun.exe "C:\Users\admin\Downloads\mgrmedia.exe" | C:\Windows\system32\pcwrun.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1784 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES28D.tmp" "c:\Users\admin\AppData\Local\Temp\CSC27C.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2208 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES339.tmp" "c:\Users\admin\AppData\Local\Temp\CSC338.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2328 | "C:\Users\admin\Downloads\mgrmedia.exe" | C:\Users\admin\Downloads\mgrmedia.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Web Manager Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2336 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES442.tmp" "c:\Users\admin\AppData\Local\Temp\CSC441.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3364 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\epg_vqdo.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3376 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ujj3onw5.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3444 | "C:\Users\admin\Downloads\mgrmedia.exe" | C:\Users\admin\Downloads\mgrmedia.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Web Manager Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
445
Read events
398
Write events
47
Delete events
0
Modification events
| (PID) Process: | (2328) mgrmedia.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2328) mgrmedia.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2328) mgrmedia.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2328) mgrmedia.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2328) mgrmedia.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2328) mgrmedia.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2328) mgrmedia.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4032) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4032) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (4032) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
Executable files
2
Suspicious files
7
Text files
24
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2328 | mgrmedia.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\errorPageStrings[2] | text | |
MD5:— | SHA256:— | |||
| 2064 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\epg_vqdo.0.cs | — | |
MD5:— | SHA256:— | |||
| 2064 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\epg_vqdo.cmdline | — | |
MD5:— | SHA256:— | |||
| 3364 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC27C.tmp | — | |
MD5:— | SHA256:— | |||
| 3364 | csc.exe | C:\Users\admin\AppData\Local\Temp\epg_vqdo.pdb | — | |
MD5:— | SHA256:— | |||
| 2136 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES28D.tmp | — | |
MD5:— | SHA256:— | |||
| 3364 | csc.exe | C:\Users\admin\AppData\Local\Temp\epg_vqdo.dll | — | |
MD5:— | SHA256:— | |||
| 3364 | csc.exe | C:\Users\admin\AppData\Local\Temp\epg_vqdo.out | — | |
MD5:— | SHA256:— | |||
| 2064 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\ujj3onw5.0.cs | — | |
MD5:— | SHA256:— | |||
| 2064 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\ujj3onw5.cmdline | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3444 | mgrmedia.exe | GET | 200 | 23.55.163.57:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 1.16 Kb | whitelisted |
3444 | mgrmedia.exe | GET | 200 | 23.32.238.67:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMqD1Cetk7lQsrz6q%2Ffj5R%2BJg%3D%3D | US | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2328 | mgrmedia.exe | 5.2.72.179:443 | linkto.freeforalldownload.net | Liteserver VOF | NL | unknown |
— | — | 5.2.72.179:443 | linkto.freeforalldownload.net | Liteserver VOF | NL | unknown |
3444 | mgrmedia.exe | 5.2.72.179:443 | linkto.freeforalldownload.net | Liteserver VOF | NL | unknown |
3444 | mgrmedia.exe | 23.55.163.57:80 | crl.identrust.com | Akamai International B.V. | US | unknown |
3444 | mgrmedia.exe | 23.32.238.67:80 | r3.o.lencr.org | XO Communications | US | unknown |
3444 | mgrmedia.exe | 23.32.238.75:80 | crl.identrust.com | XO Communications | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
linkto.freeforalldownload.net |
| unknown |
crl.identrust.com |
| whitelisted |
r3.o.lencr.org |
| shared |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|