| File name: | Loader.exe |
| Full analysis: | https://app.any.run/tasks/b476ca7e-0bf5-48f4-b84f-5bfd576f1c66 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 01:36:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 7A0515CDDE60F1B13F804CDA14BBEE87 |
| SHA1: | 14AF0897C25B222768B52E86022062E0C194B61B |
| SHA256: | 9DCC53EC0E94170656AD2E5FC6D77C9828F2F90E66D12793A706E50B359B0849 |
| SSDEEP: | 24576:+/QA4lEgzCemhmuuwx6kHgsS8VsfnJpaQ:+/QNDexhmuuwx6kHgsS8VsfnJpaQ |
MALICIOUS
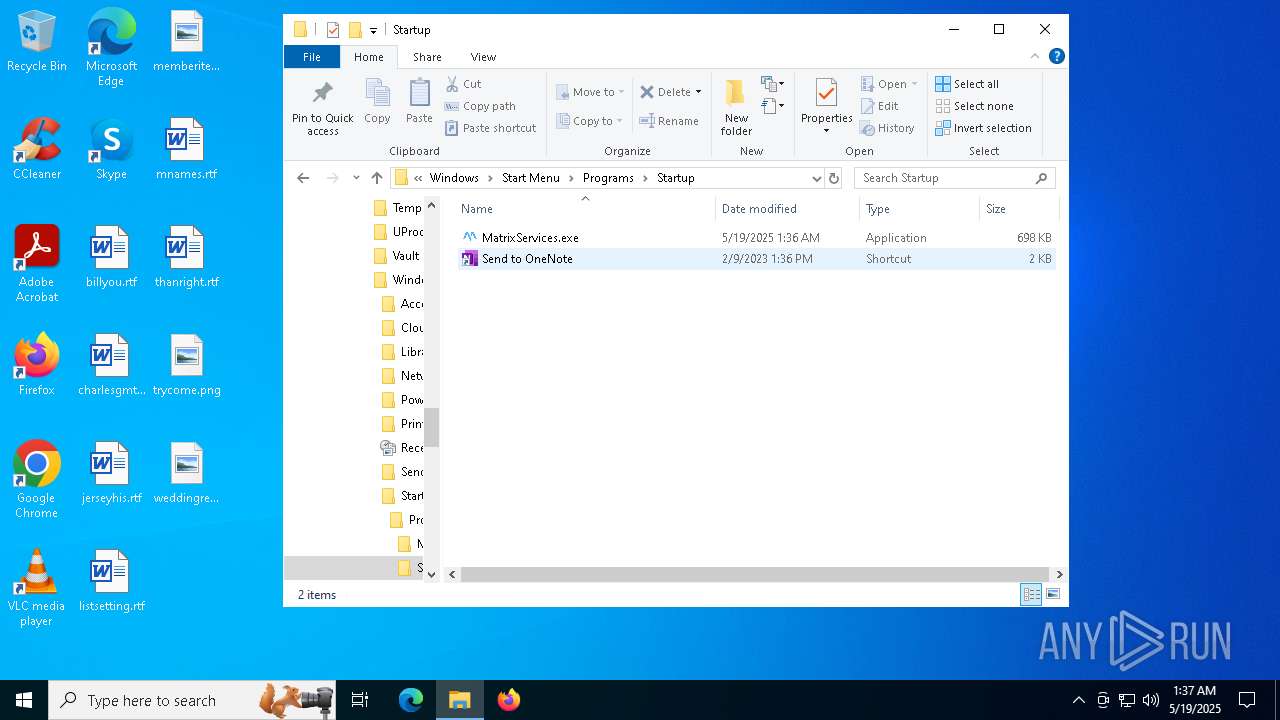
Executing a file with an untrusted certificate
- Loader.exe (PID: 6640)
- MatrixServices.exe (PID: 736)
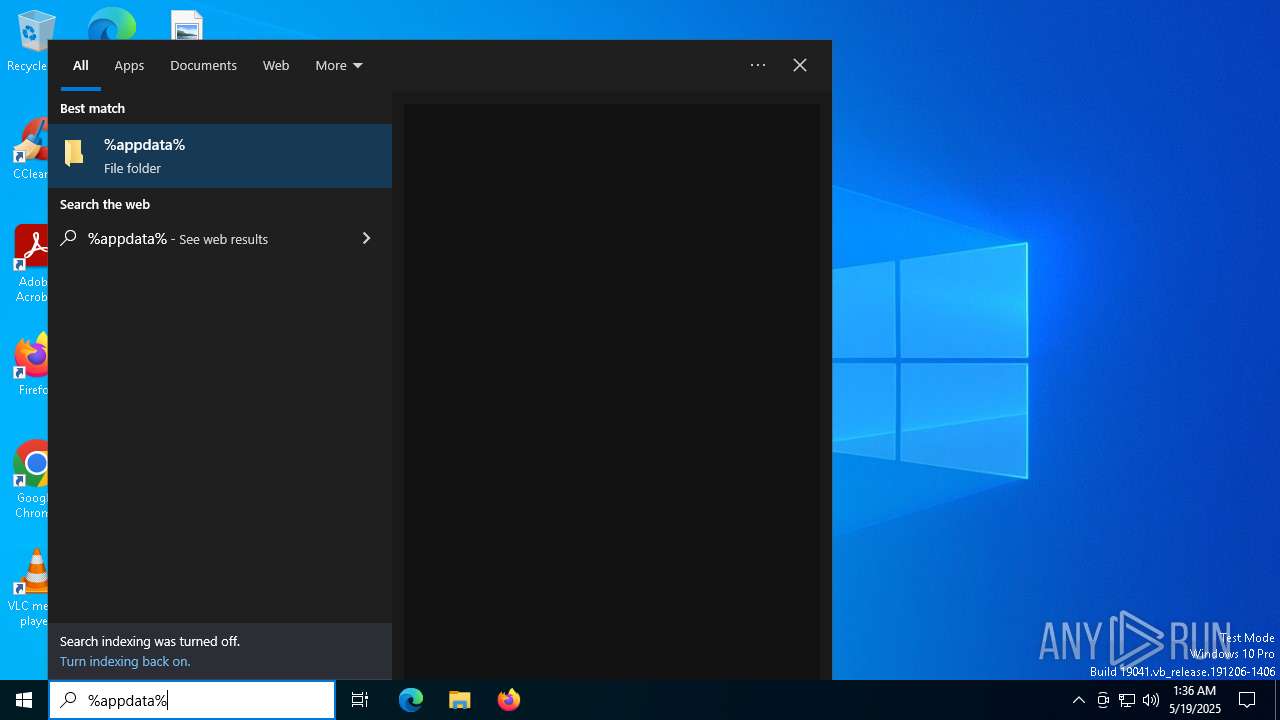
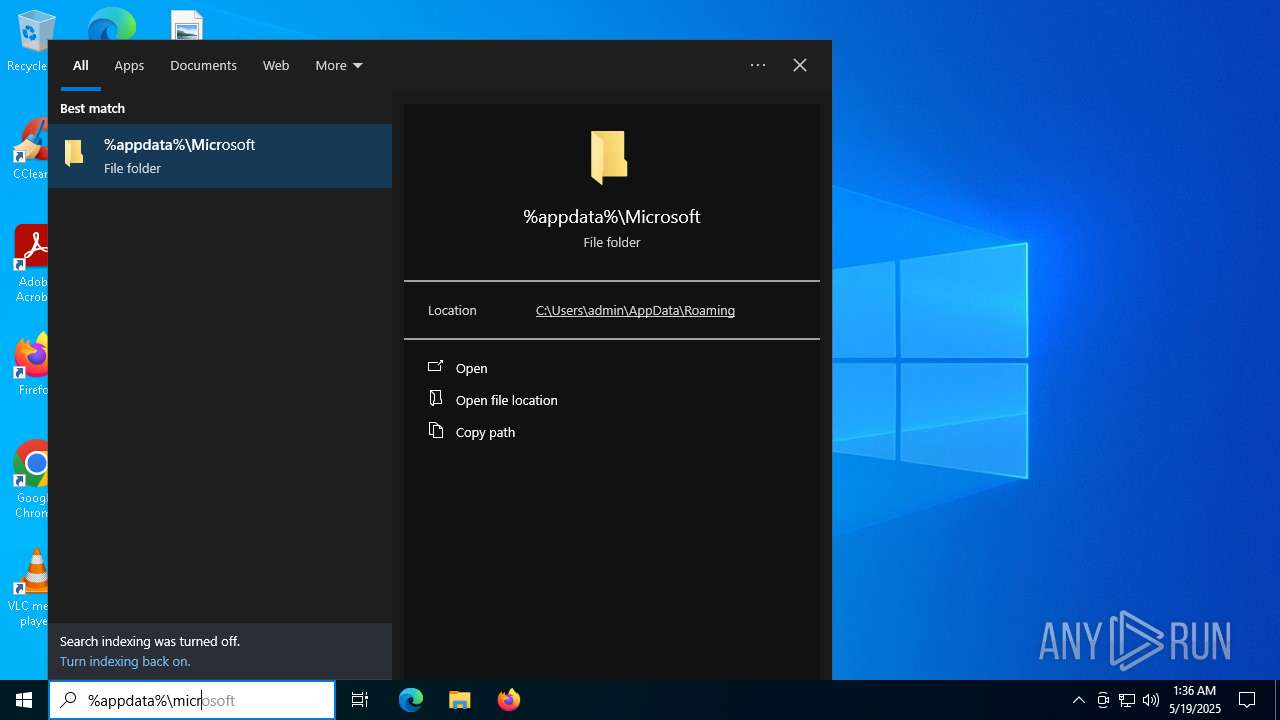
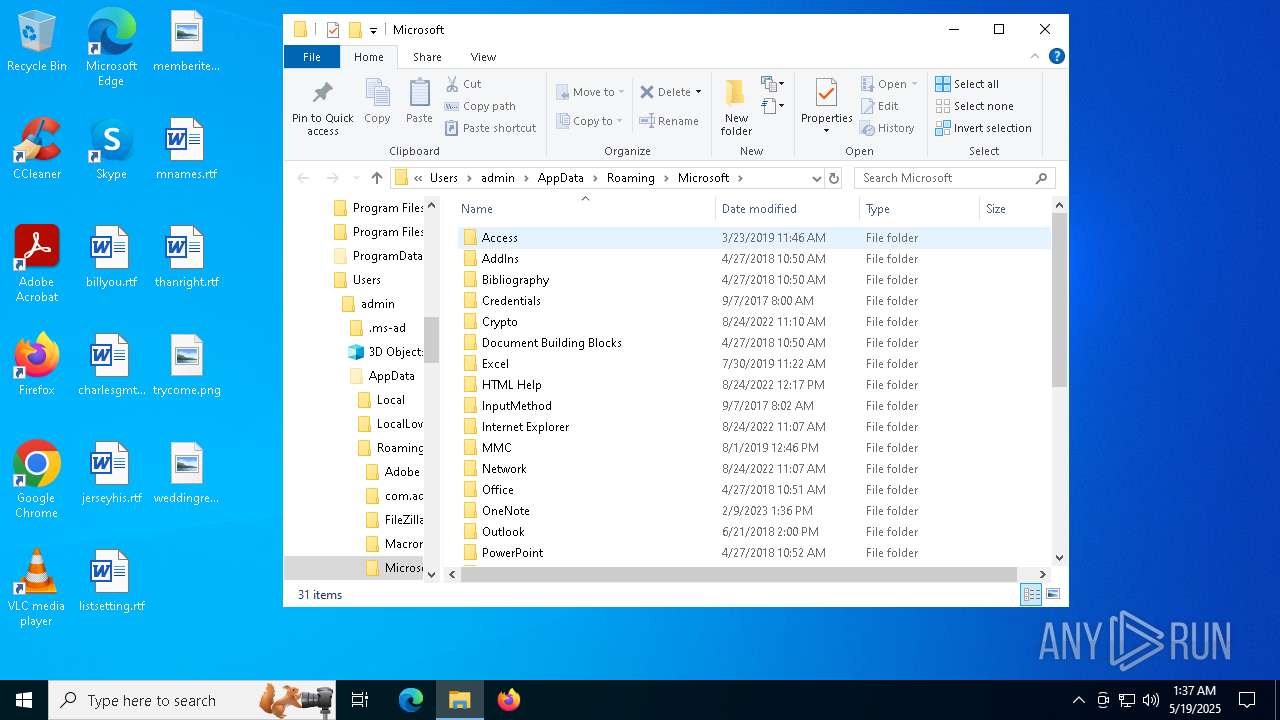
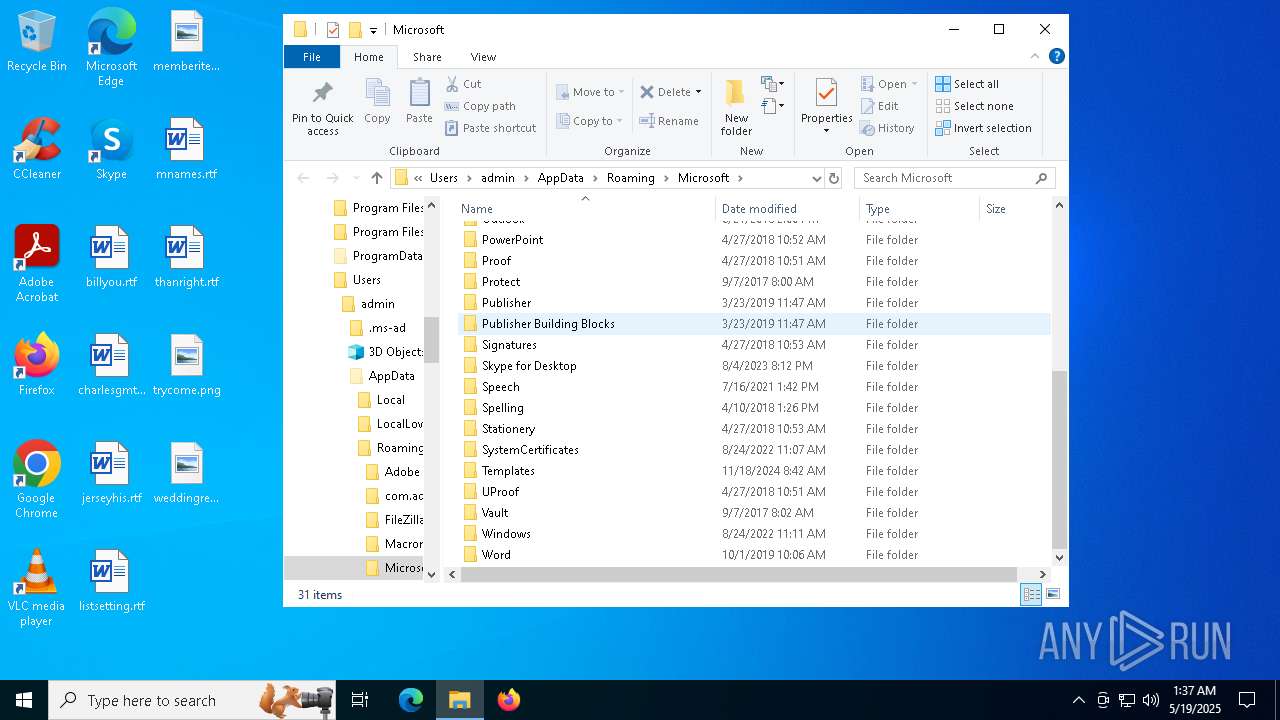
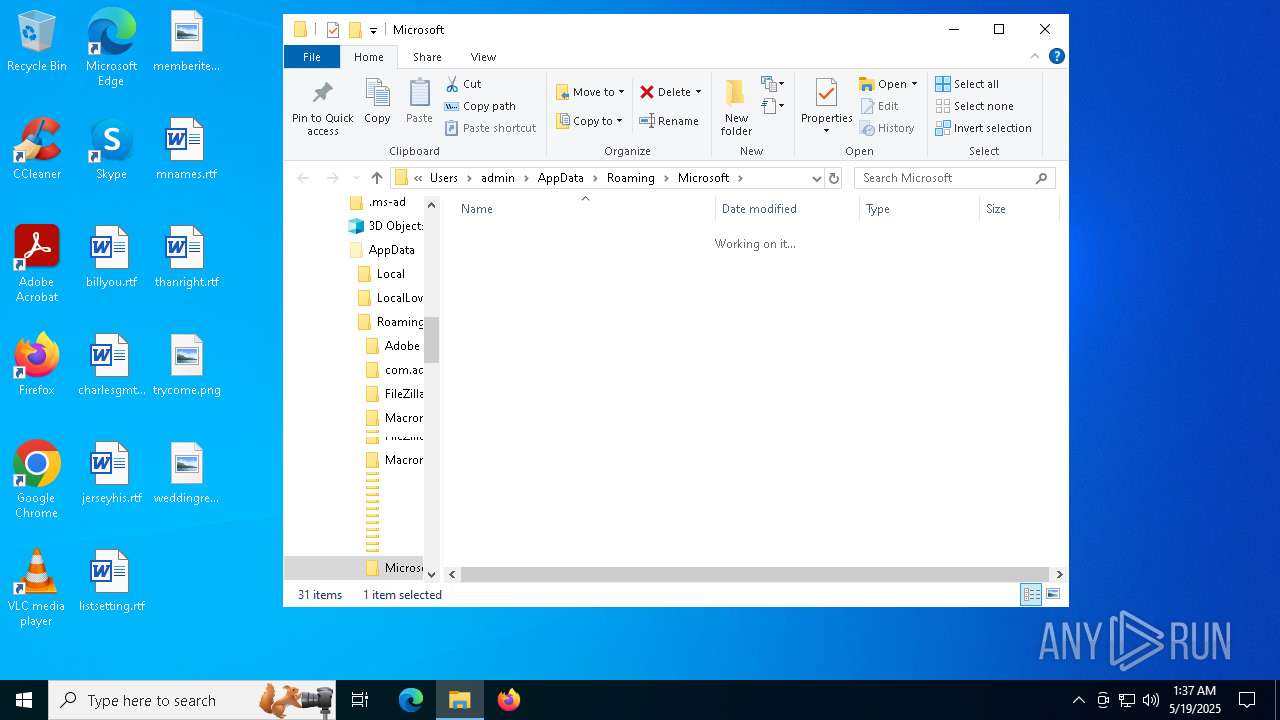
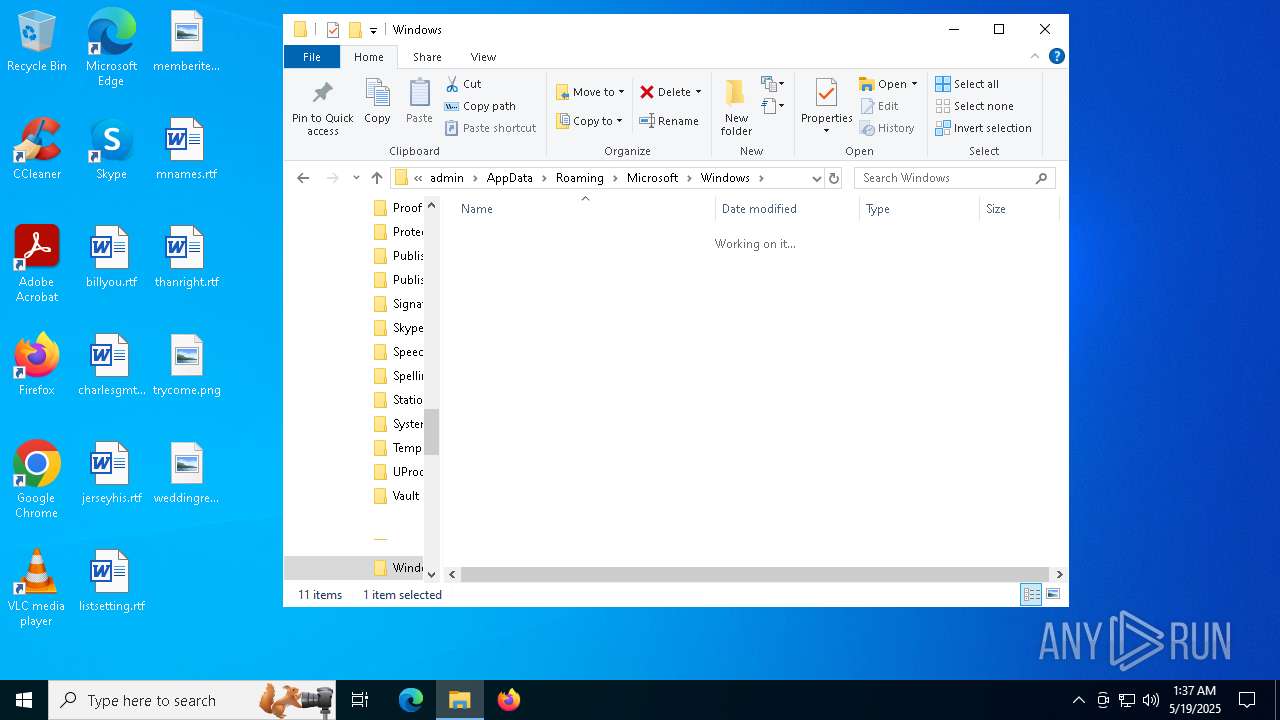
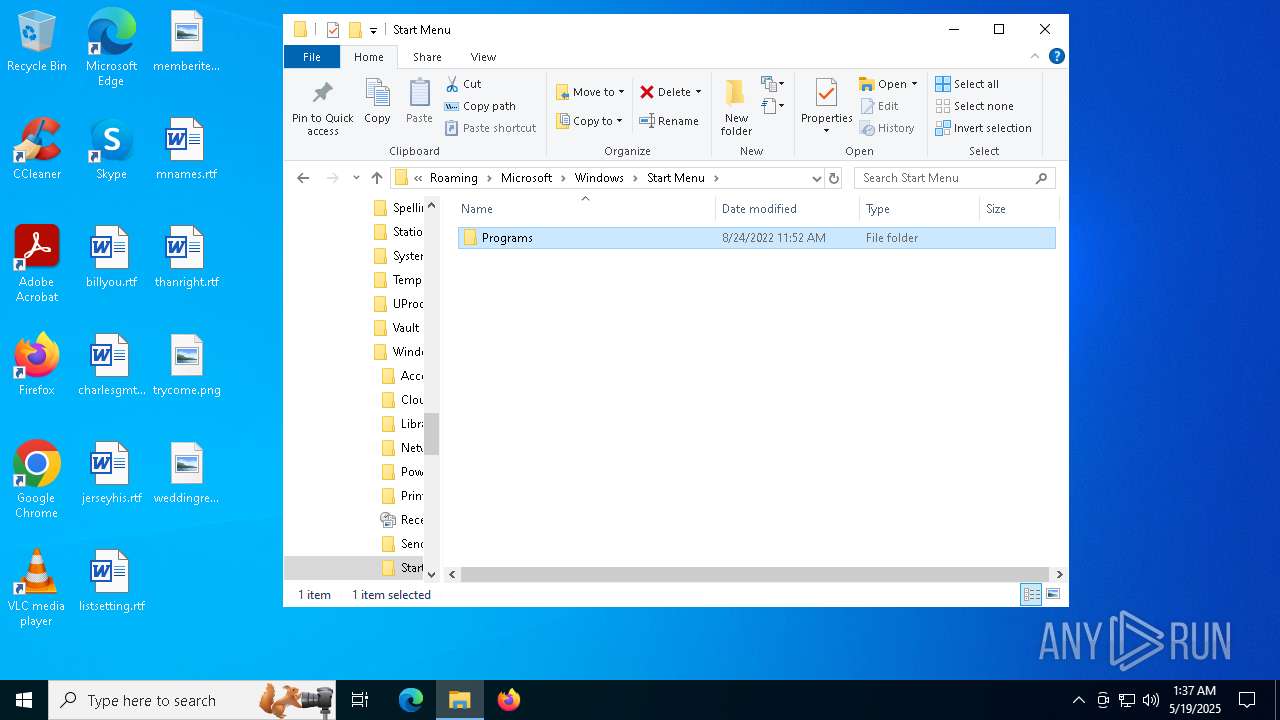
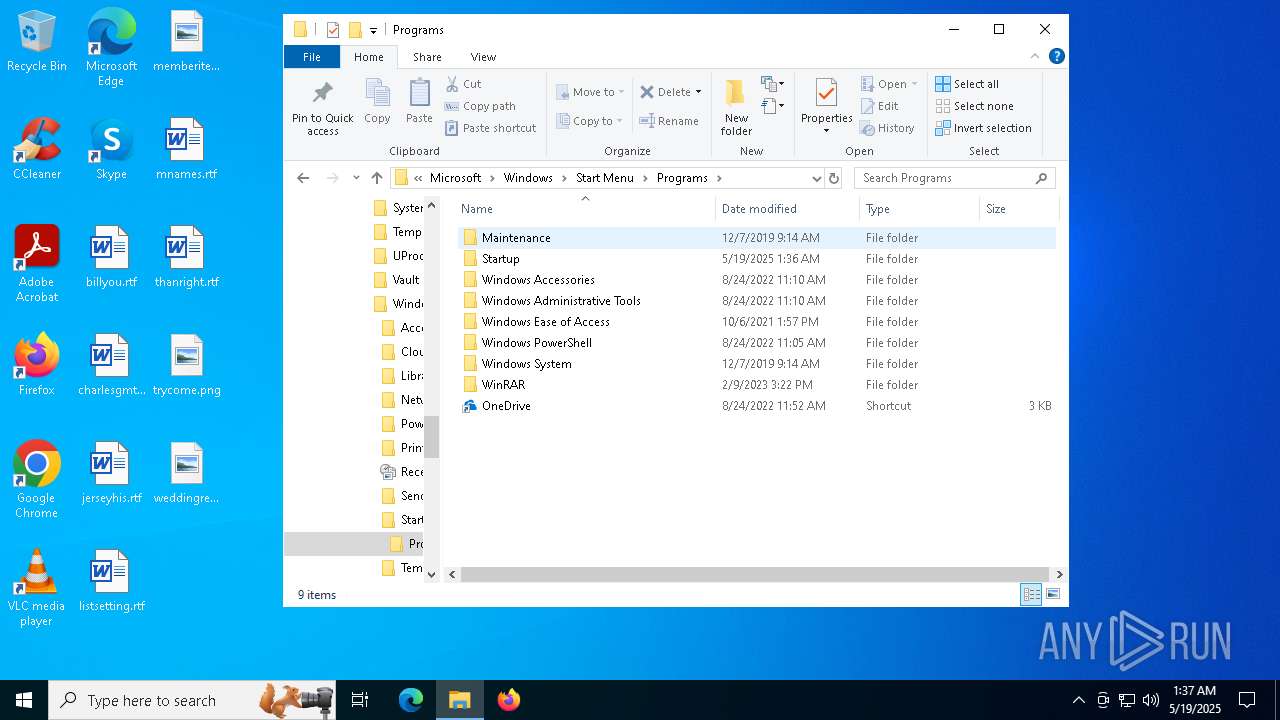
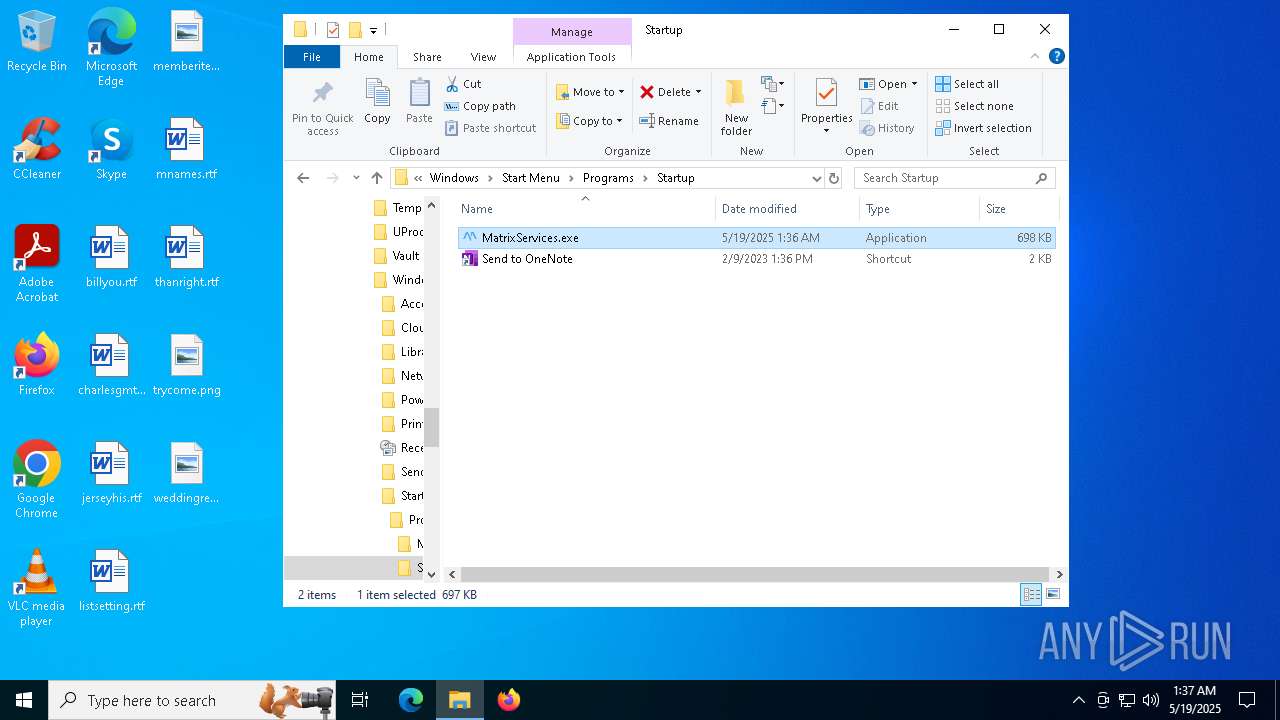
Create files in the Startup directory
- Loader.exe (PID: 6640)
SUSPICIOUS
Executable content was dropped or overwritten
- Loader.exe (PID: 6640)
The process creates files with name similar to system file names
- Loader.exe (PID: 6640)
- WerFault.exe (PID: 5964)
Executes application which crashes
- Loader.exe (PID: 6640)
- MatrixServices.exe (PID: 736)
INFO
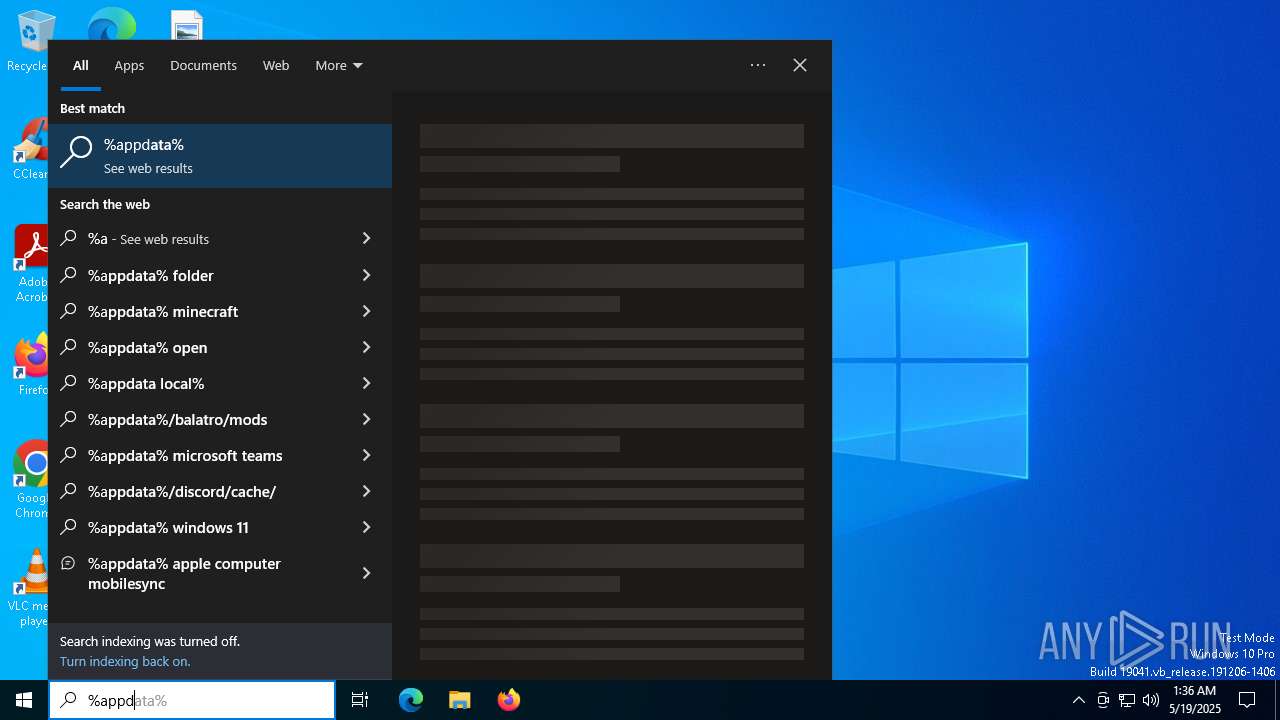
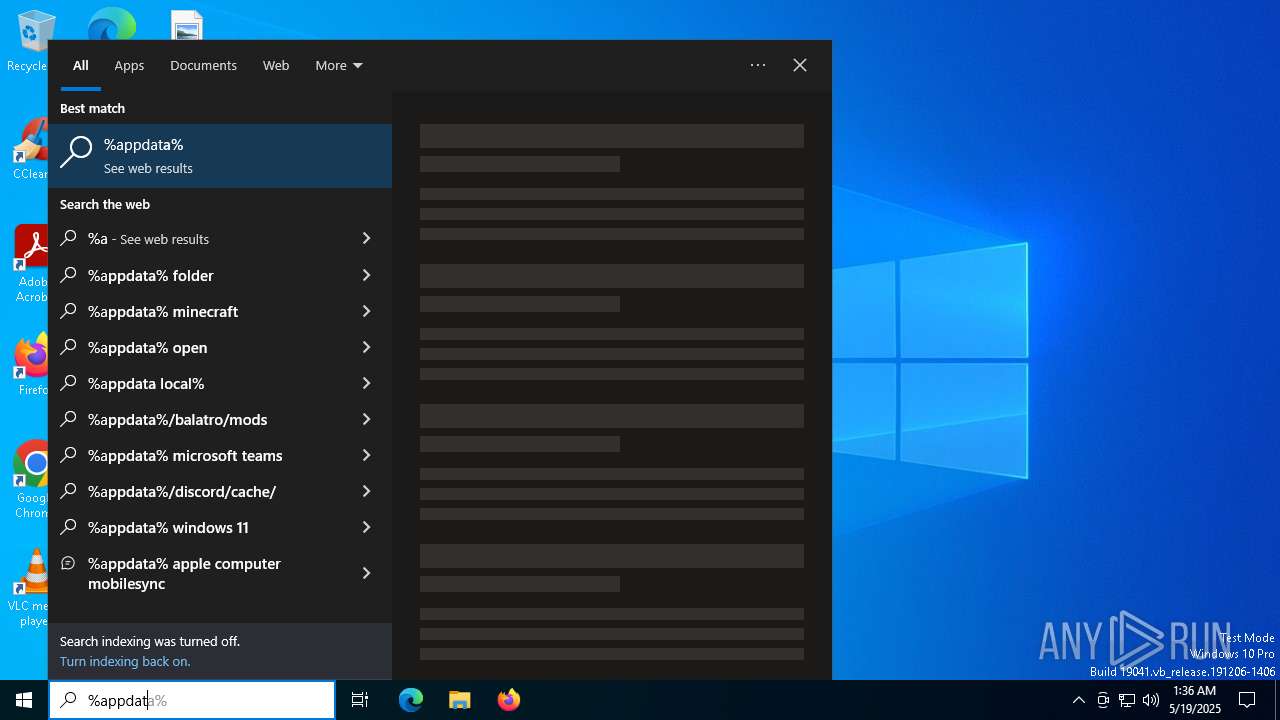
Creates files or folders in the user directory
- Loader.exe (PID: 6640)
- WerFault.exe (PID: 4812)
- WerFault.exe (PID: 5964)
Checks supported languages
- Loader.exe (PID: 6640)
- MatrixServices.exe (PID: 736)
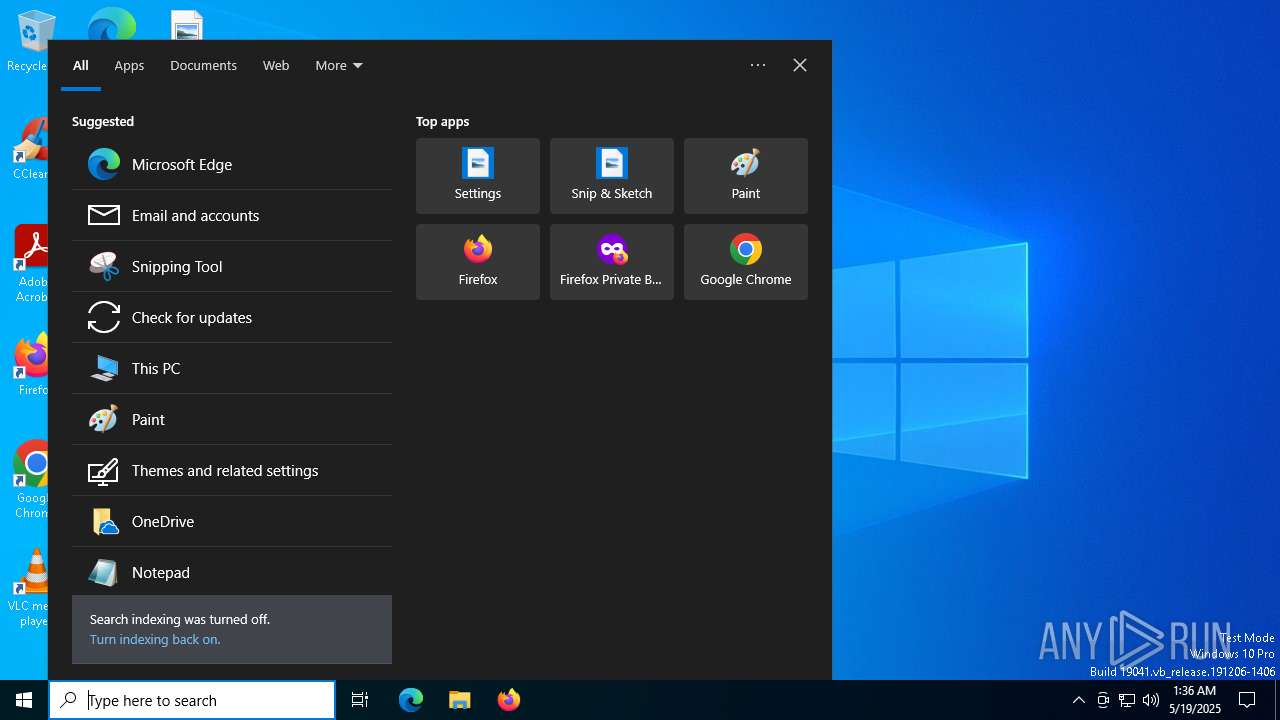
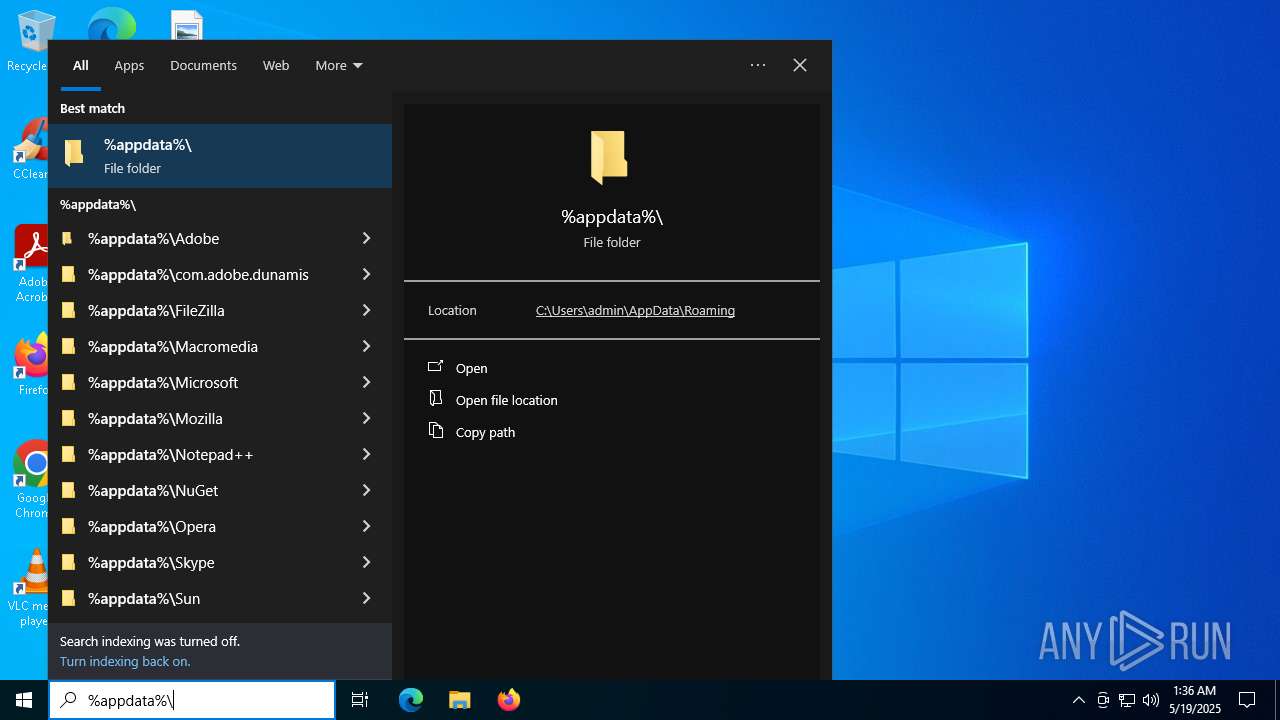
Manual execution by a user
- MatrixServices.exe (PID: 736)
Reads the software policy settings
- slui.exe (PID: 2236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:13 18:52:21+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 480256 |
| InitializedDataSize: | 235008 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x43dd8 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
142
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
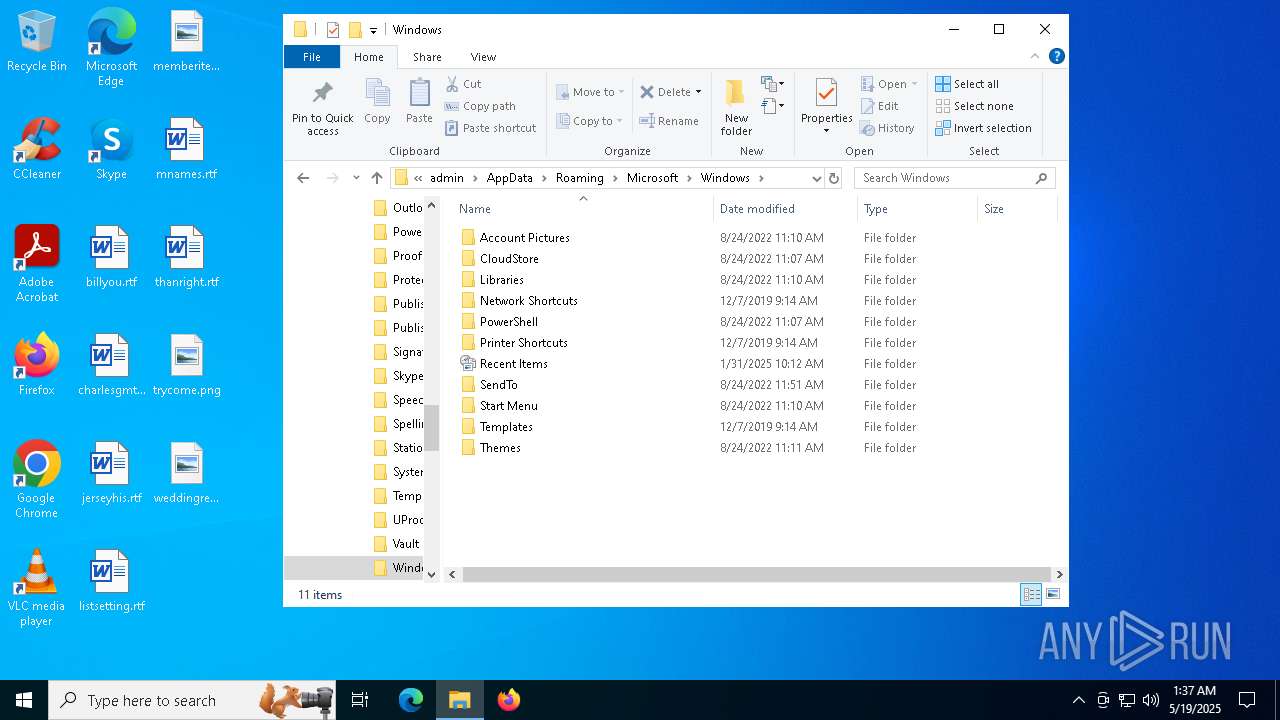
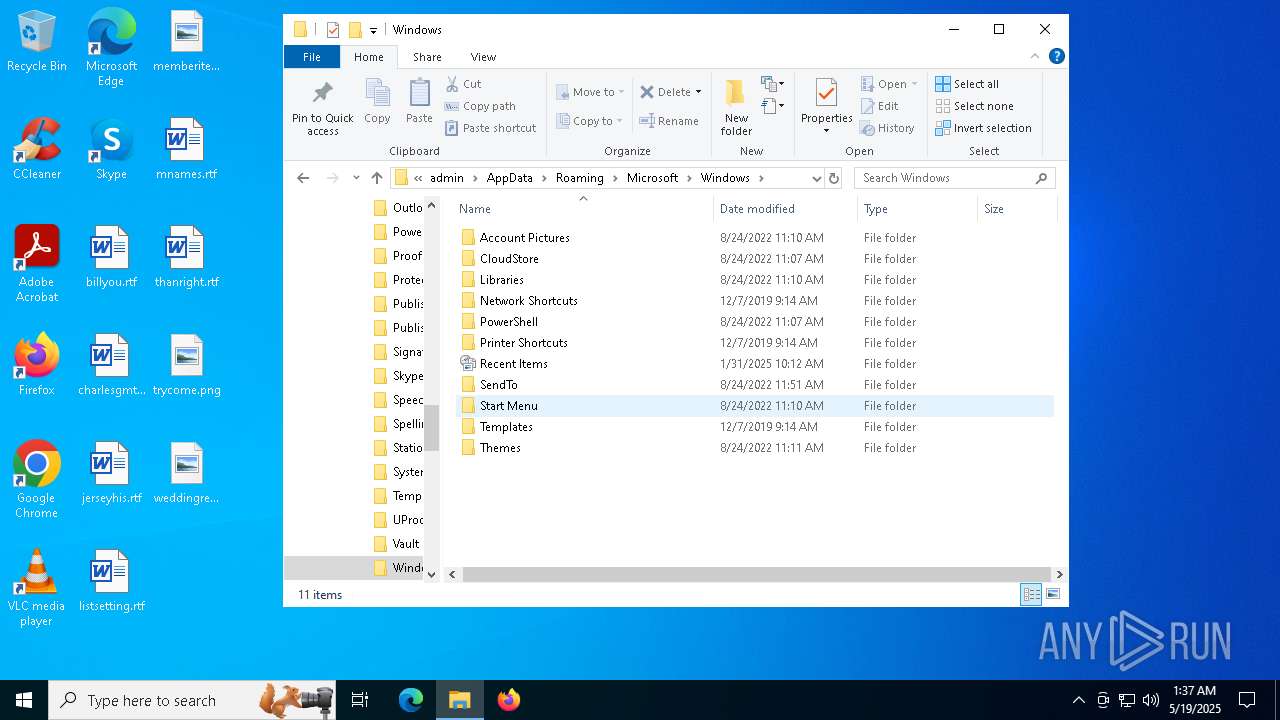
| 736 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\MatrixServices.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\MatrixServices.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 2236 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2564 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4200 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4812 | C:\WINDOWS\system32\WerFault.exe -u -p 6640 -s 572 | C:\Windows\System32\WerFault.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5964 | C:\WINDOWS\system32\WerFault.exe -u -p 736 -s 520 | C:\Windows\System32\WerFault.exe | — | MatrixServices.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | "C:\Users\admin\AppData\Local\Temp\Loader.exe" | C:\Users\admin\AppData\Local\Temp\Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
Total events
4 119
Read events
4 119
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
6
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4812 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_Loader.exe_c92c8ed3801780fdb94dec3ef69cd668dec77241_a535a5a0_eec2306a-228a-42c3-a7eb-79333babb5e8\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5964 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_MatrixServices.e_f29214c04c9222ccd6d5b76689fe2caf21658da_d85f93f7_74a70ec3-d6b3-4cf5-91cc-7ca95fbe3871\Report.wer | — | |
MD5:— | SHA256:— | |||
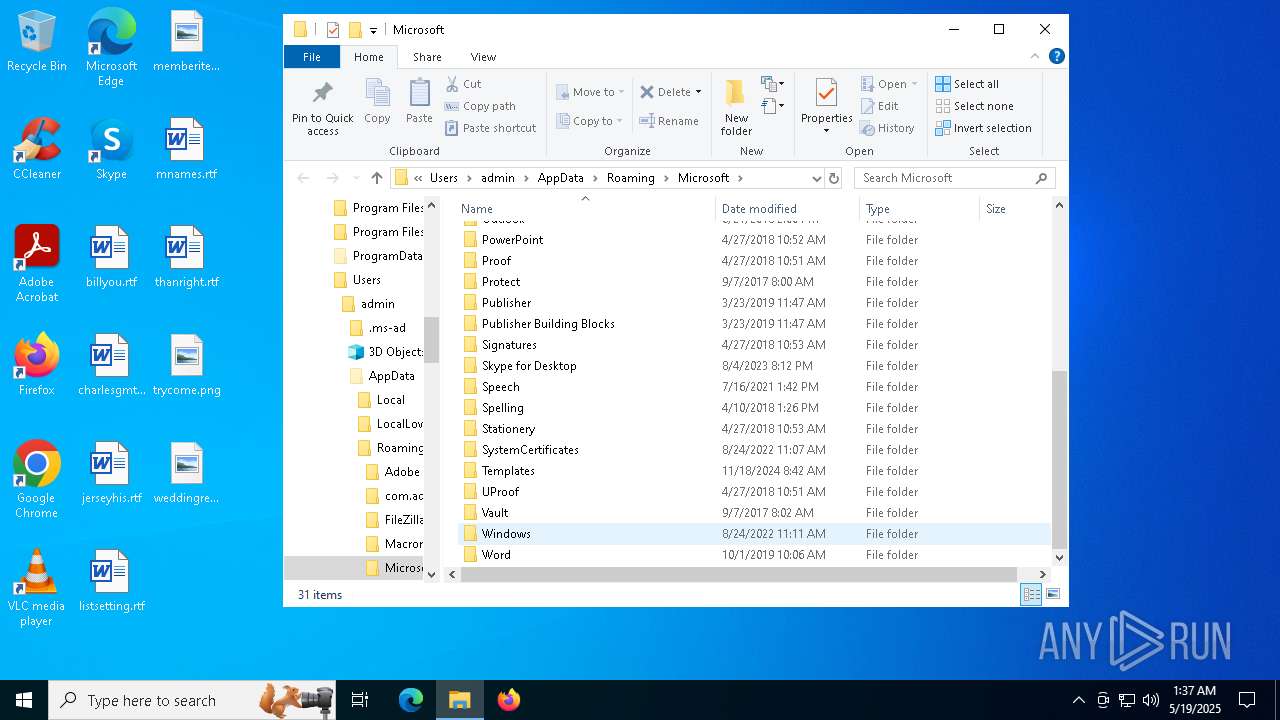
| 6640 | Loader.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\MatrixServices.exe | executable | |
MD5:7A0515CDDE60F1B13F804CDA14BBEE87 | SHA256:9DCC53EC0E94170656AD2E5FC6D77C9828F2F90E66D12793A706E50B359B0849 | |||
| 4812 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERBF6B.tmp.WERInternalMetadata.xml | binary | |
MD5:0F2F415A318463116346AB4BF37C1C24 | SHA256:37DE4946690A7BBC939846AD5DA7E010F2C56A99293387550ADBADCAE7D2A423 | |||
| 5964 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\MatrixServices.exe.736.dmp | binary | |
MD5:5BCB81559379185D3610D098C0D4218A | SHA256:6E7633F3D095B2BA20972B0554F69992EAA58B93700F9147DFF2D7012E32D71F | |||
| 5964 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER96B0.tmp.WERInternalMetadata.xml | binary | |
MD5:DE9CBF619C810E76B032FA0820A8920D | SHA256:2DF25526D10AAA9CC3D542A9DDCE307DFF65D76C1BAD453805F280EFA418864E | |||
| 5964 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER9661.tmp.dmp | binary | |
MD5:44B272E22BE89B779649315D515FED87 | SHA256:D41416CAED9634F2321ED7F270C044592EE1ACA7711163AE9919AB98C3535985 | |||
| 5964 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER96E0.tmp.xml | xml | |
MD5:BBA864D748BC56FF7E1487E6022ACE56 | SHA256:0763798886196495E685C8CB5B2406A507933F9293DE9C15741CC8A48C3DD756 | |||
| 4812 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERBE41.tmp.dmp | binary | |
MD5:DCA1DF2F3C8535A7CEAEF262CF4ECFA5 | SHA256:B1769266F225A042EF52750EF362A7E3A291B898AE68A3B1581D0191C78087B2 | |||
| 4812 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERBFAA.tmp.xml | xml | |
MD5:194C2CCCAFDA1116B89C64FDA706345D | SHA256:BE6E2AC39EDD627BC8D7D76EB23CFEE7E5A48B65EB8405A913130CFB89A830B6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
33
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
672 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
672 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
672 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |