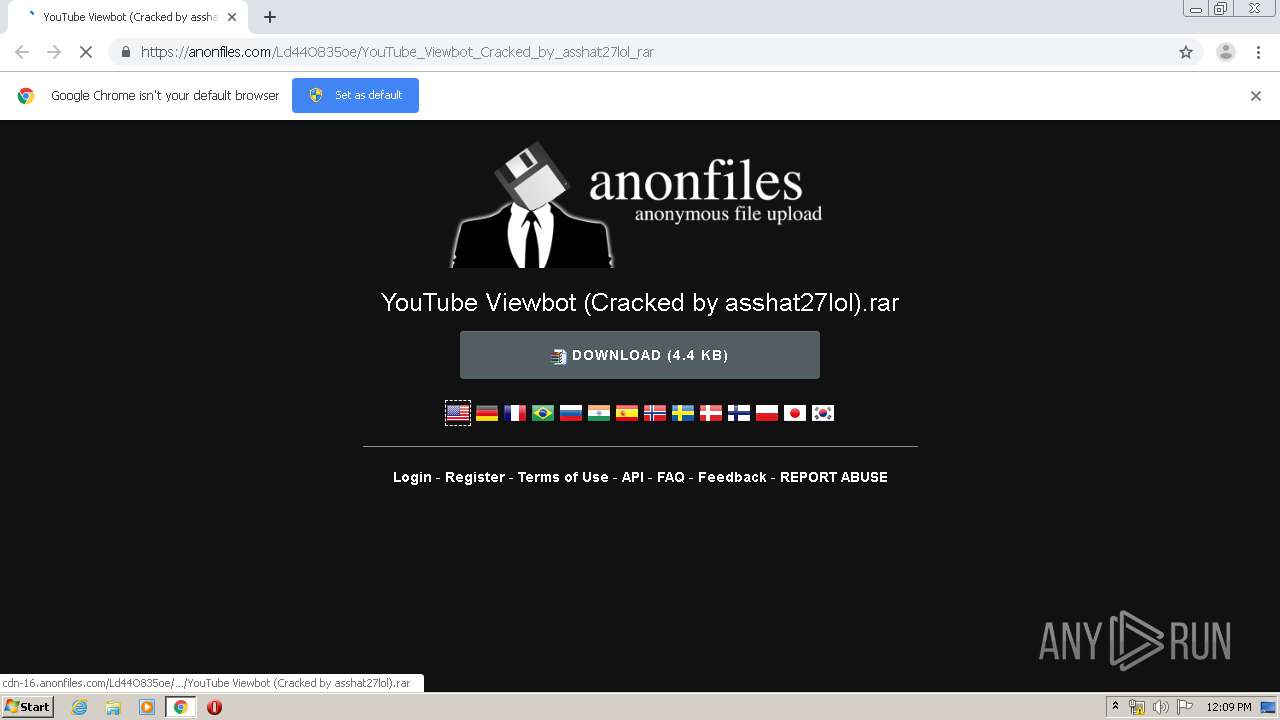
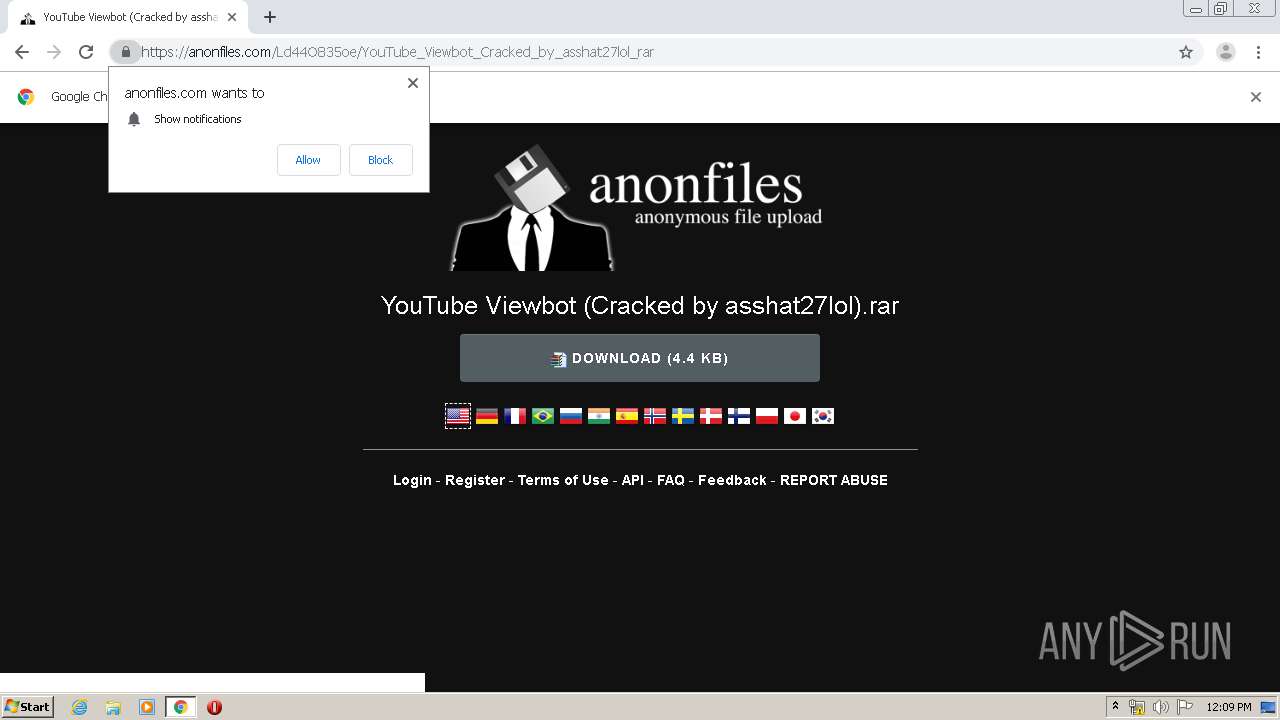
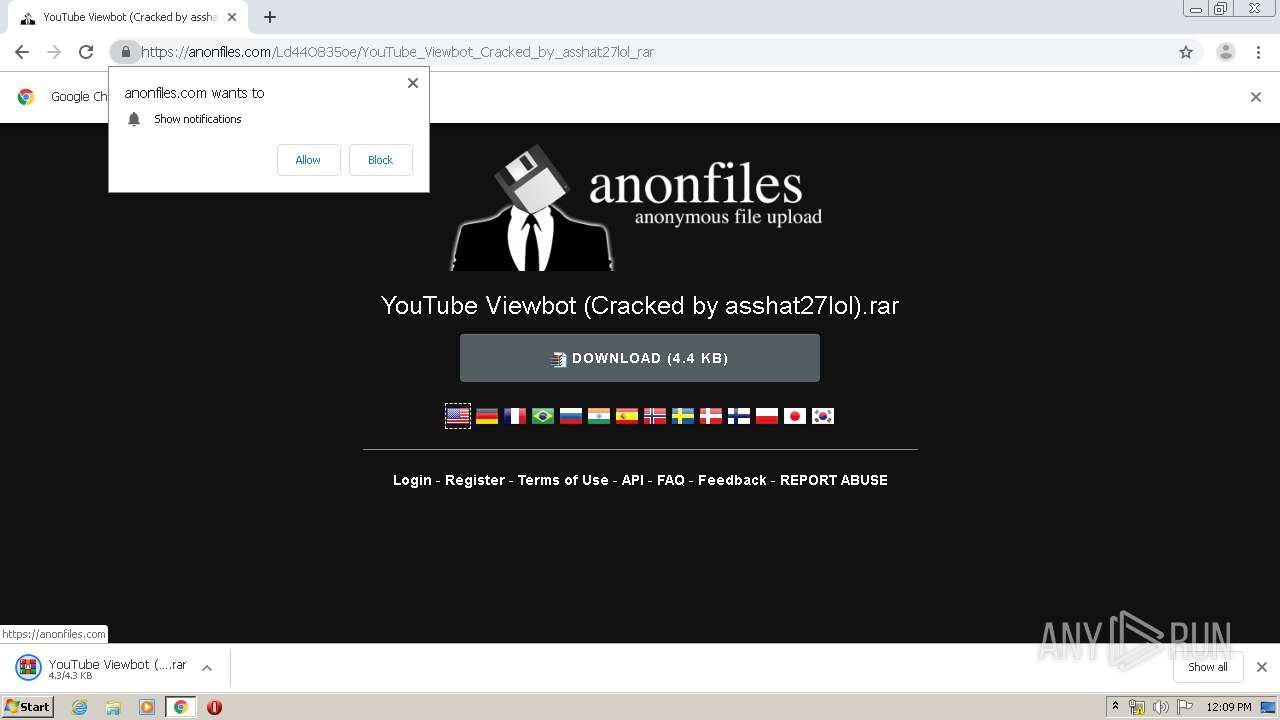
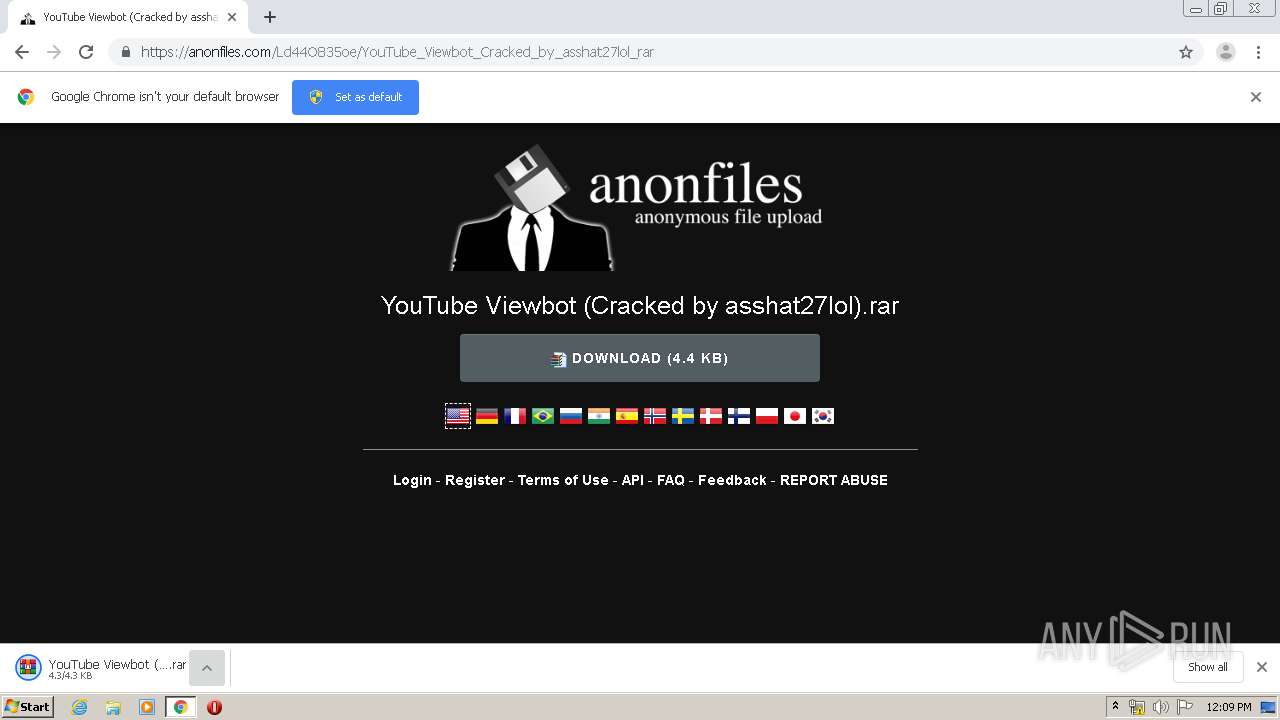
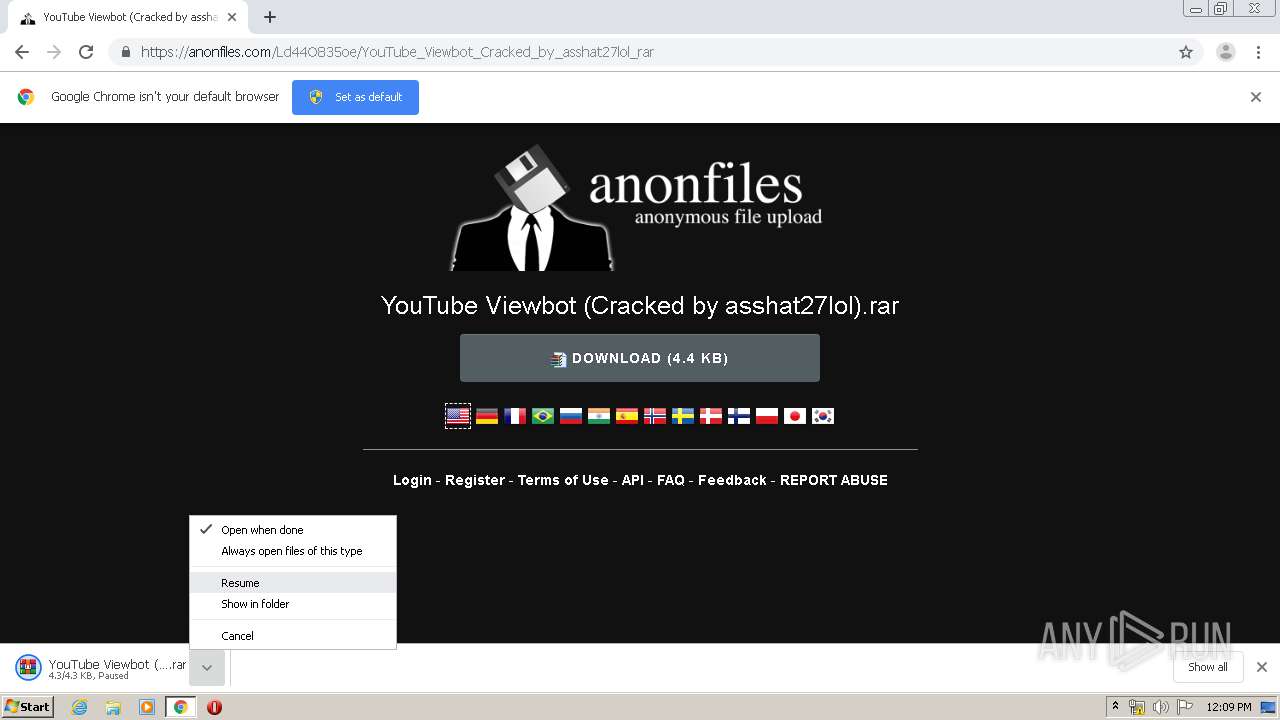
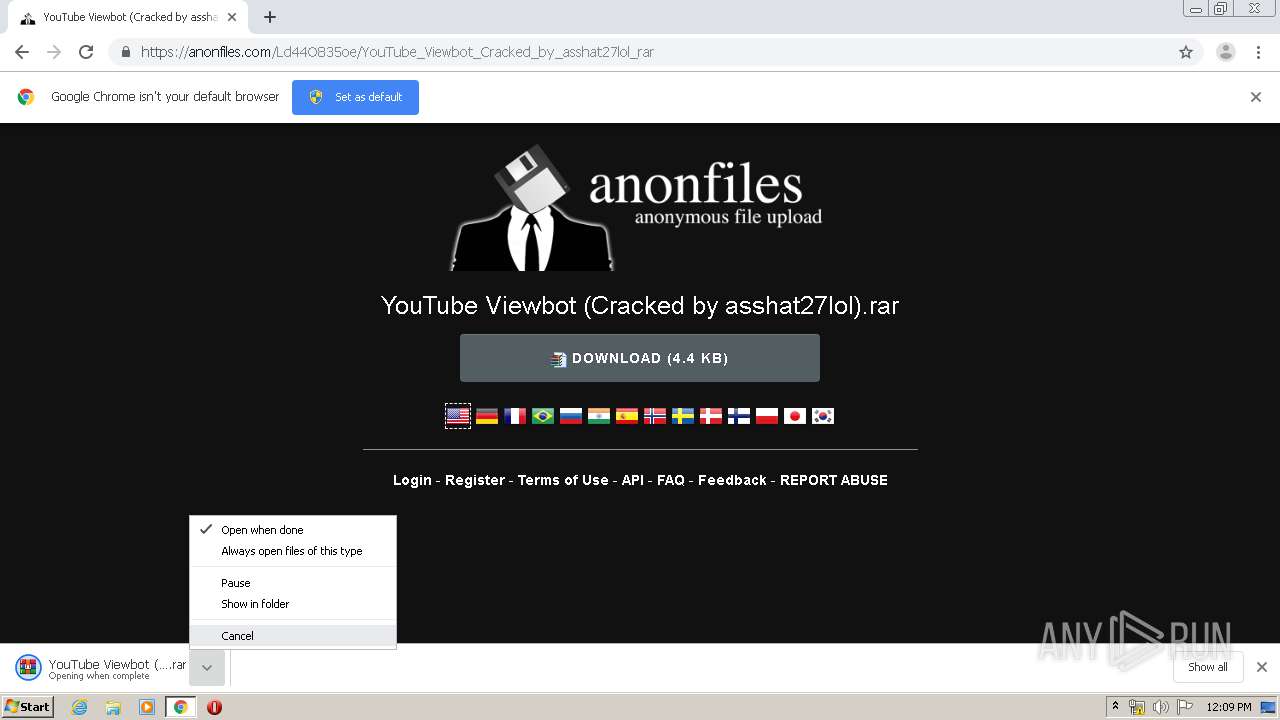
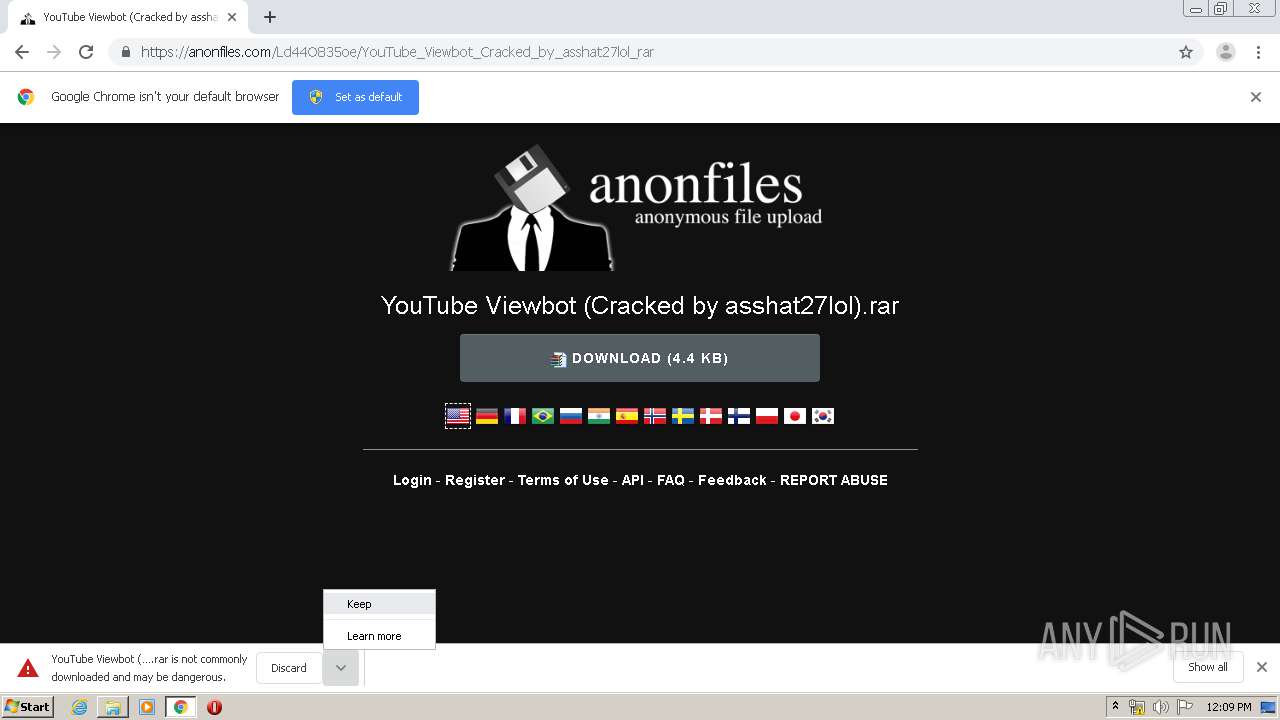
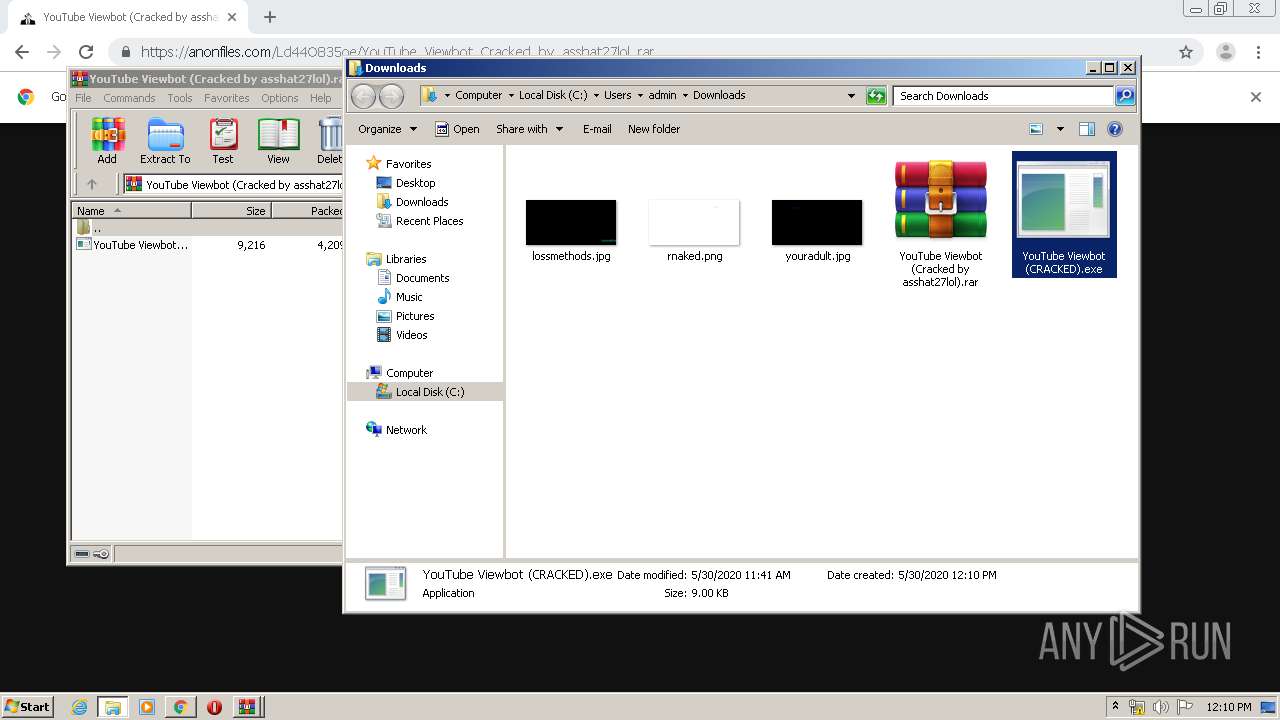
| URL: | https://anonfiles.com/Ld44O835oe/YouTube_Viewbot_Cracked_by_asshat27lol_rar |
| Full analysis: | https://app.any.run/tasks/3f7943d5-73a8-4def-93a1-213a2379bc01 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 11:09:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4DC3F94401722147E40B0DAE3E2A4443 |
| SHA1: | 74B5F995655FF9CBB1B7E3BFC871335A534BB3B5 |
| SHA256: | 9DC88C7ABCD013DA359806581B0C56390D1AD825160FBD516C5800EF765CD710 |
| SSDEEP: | 3:N8M2D+bQAAYB4ZfOEX:2M2D+1bB4ZGEX |
MALICIOUS
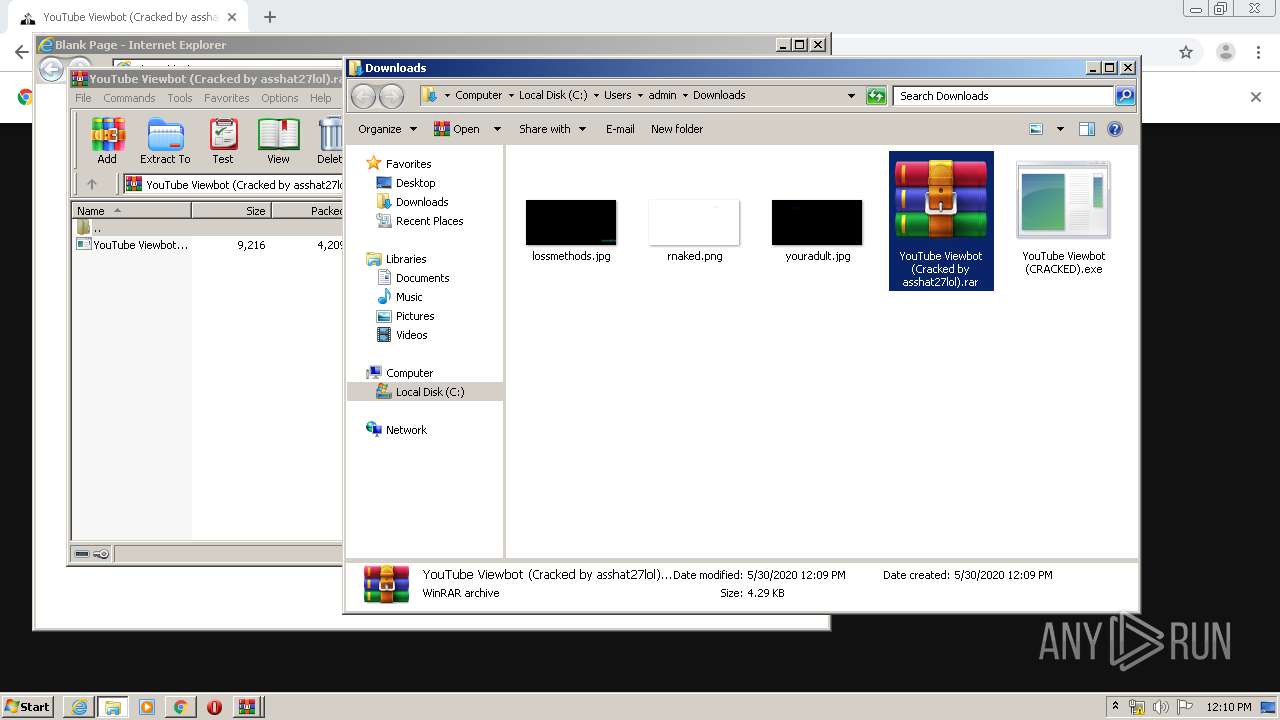
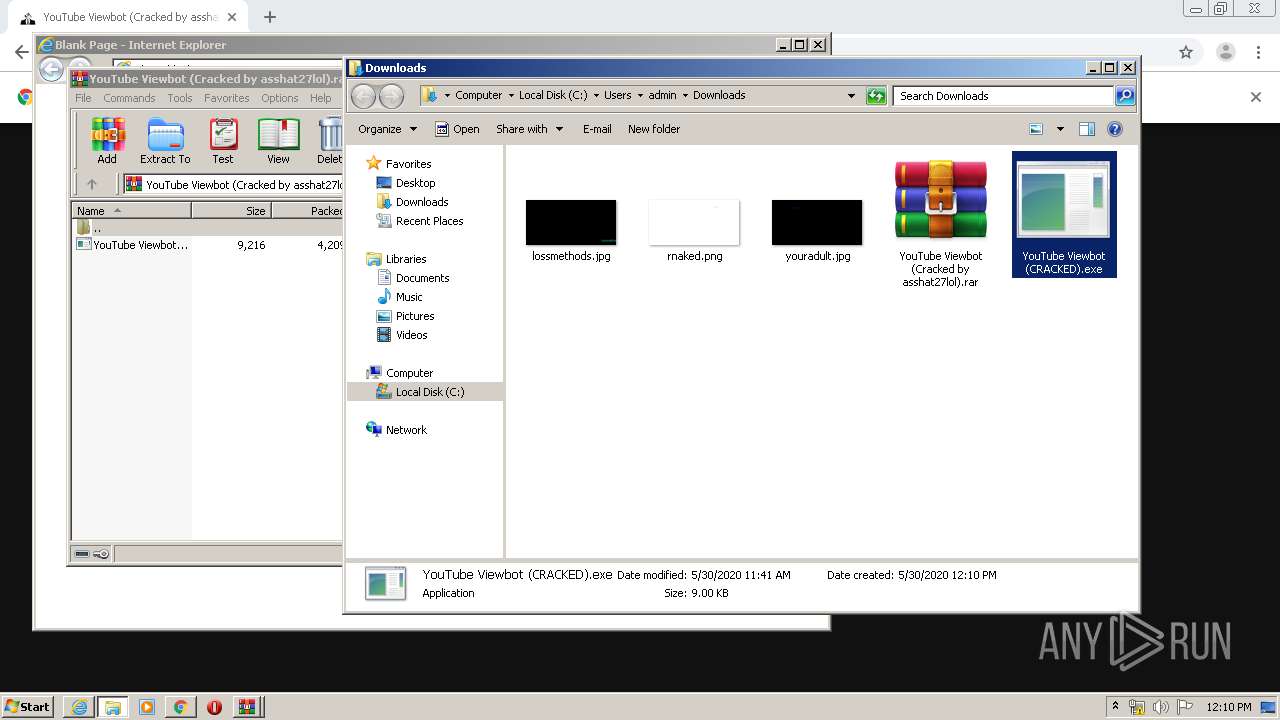
Application was dropped or rewritten from another process
- YouTube Viewbot (CRACKED).exe (PID: 2240)
Actions looks like stealing of personal data
- YouTube Viewbot (CRACKED).exe (PID: 2240)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1196)
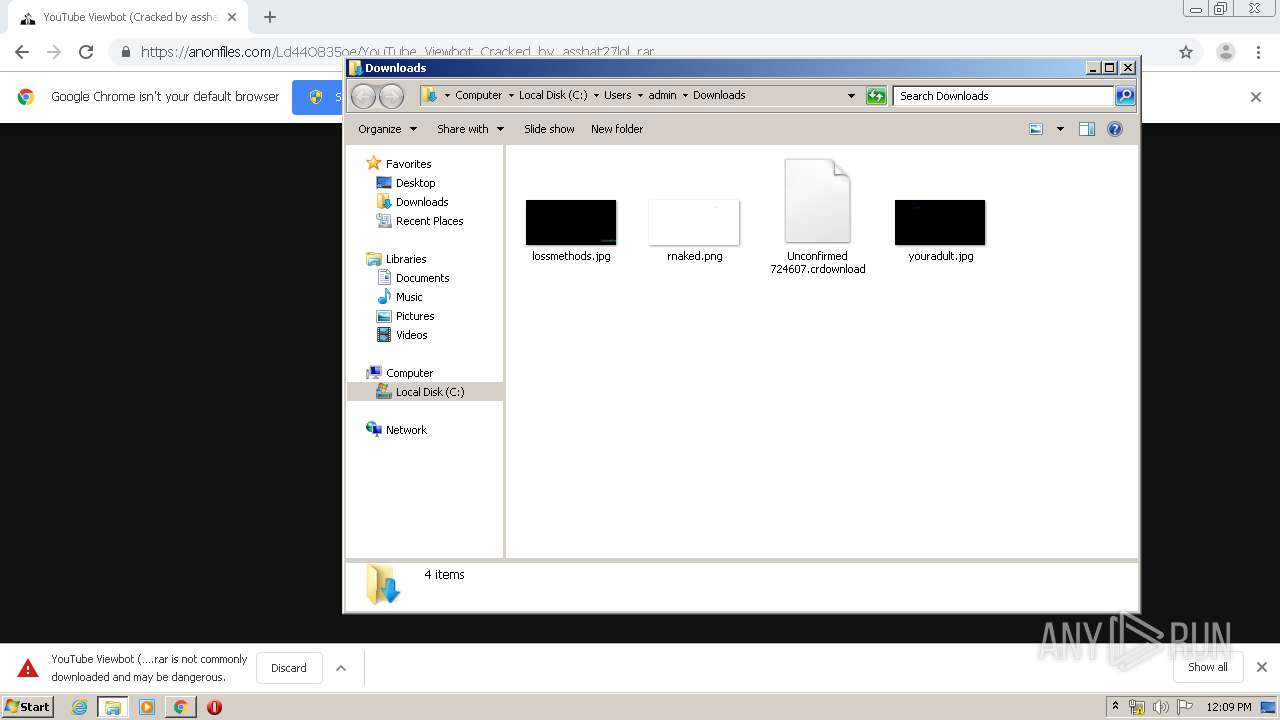
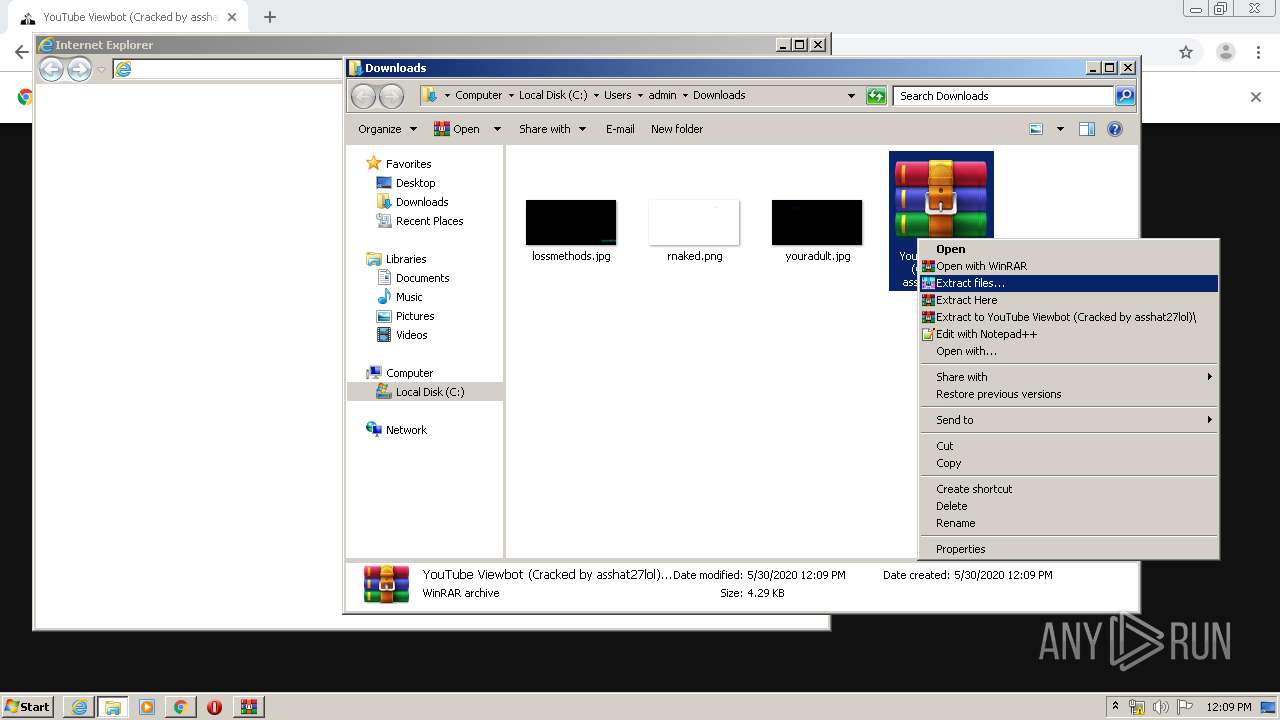
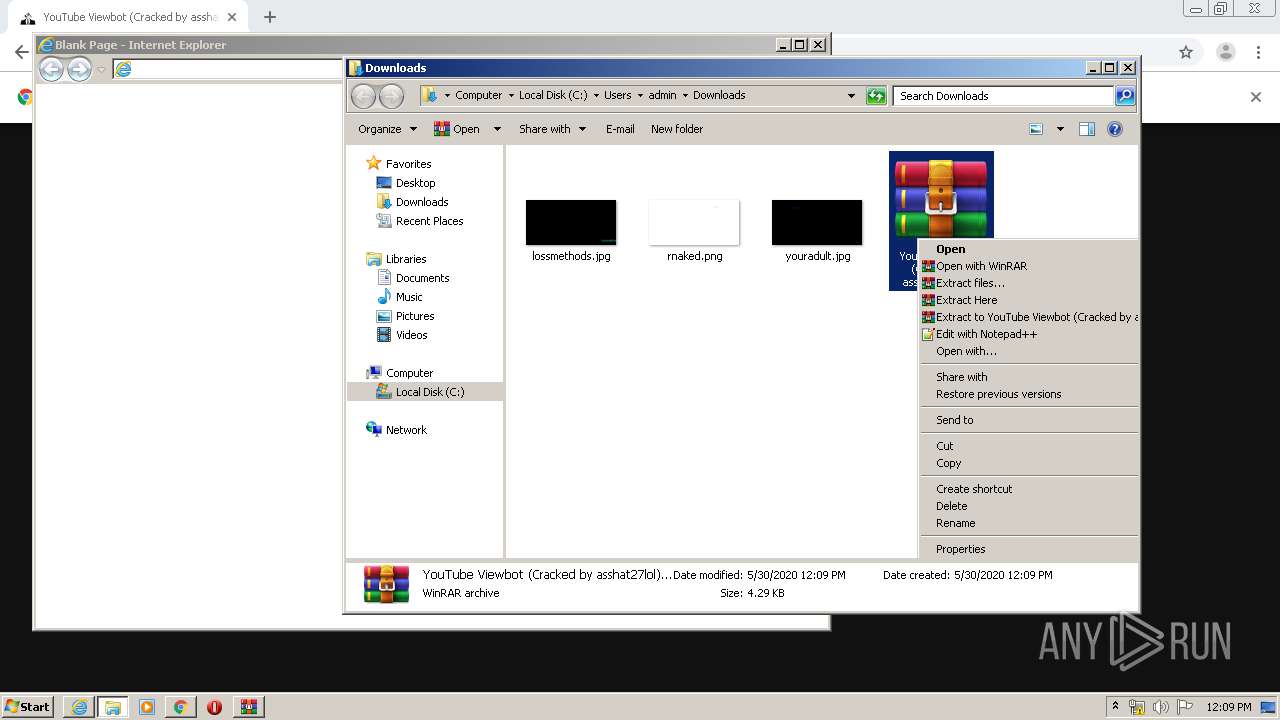
Executable content was dropped or overwritten
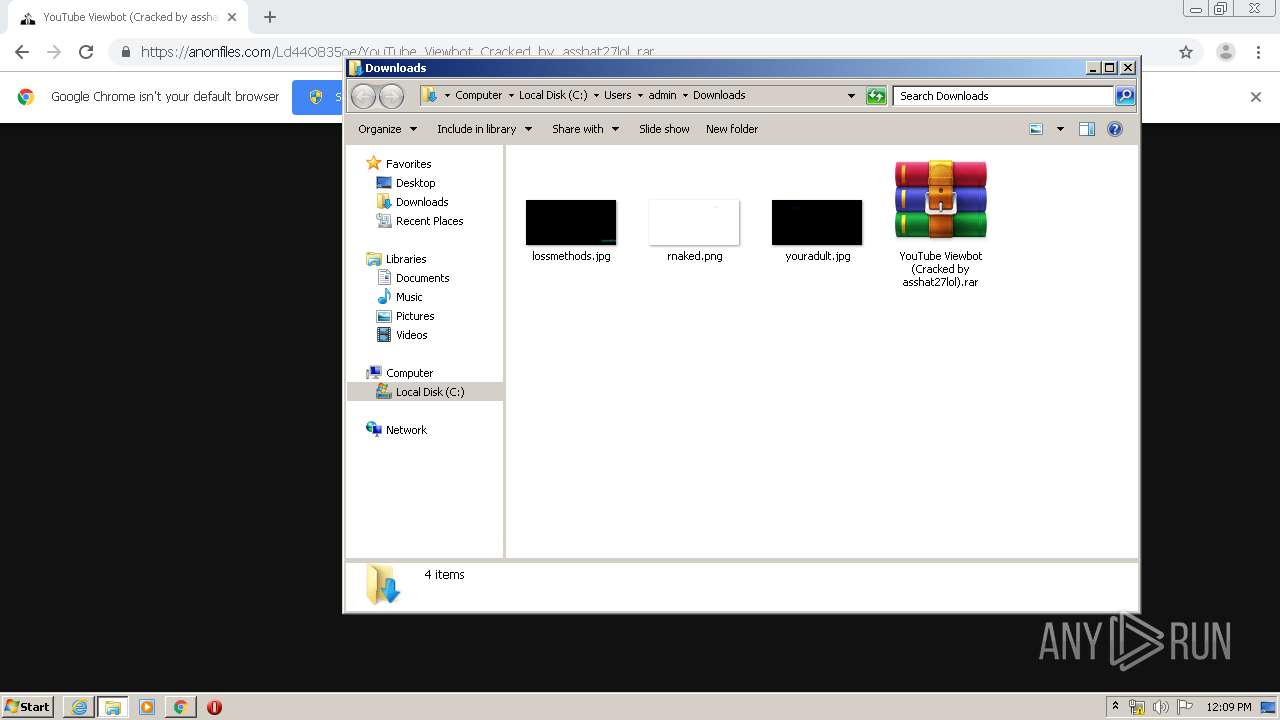
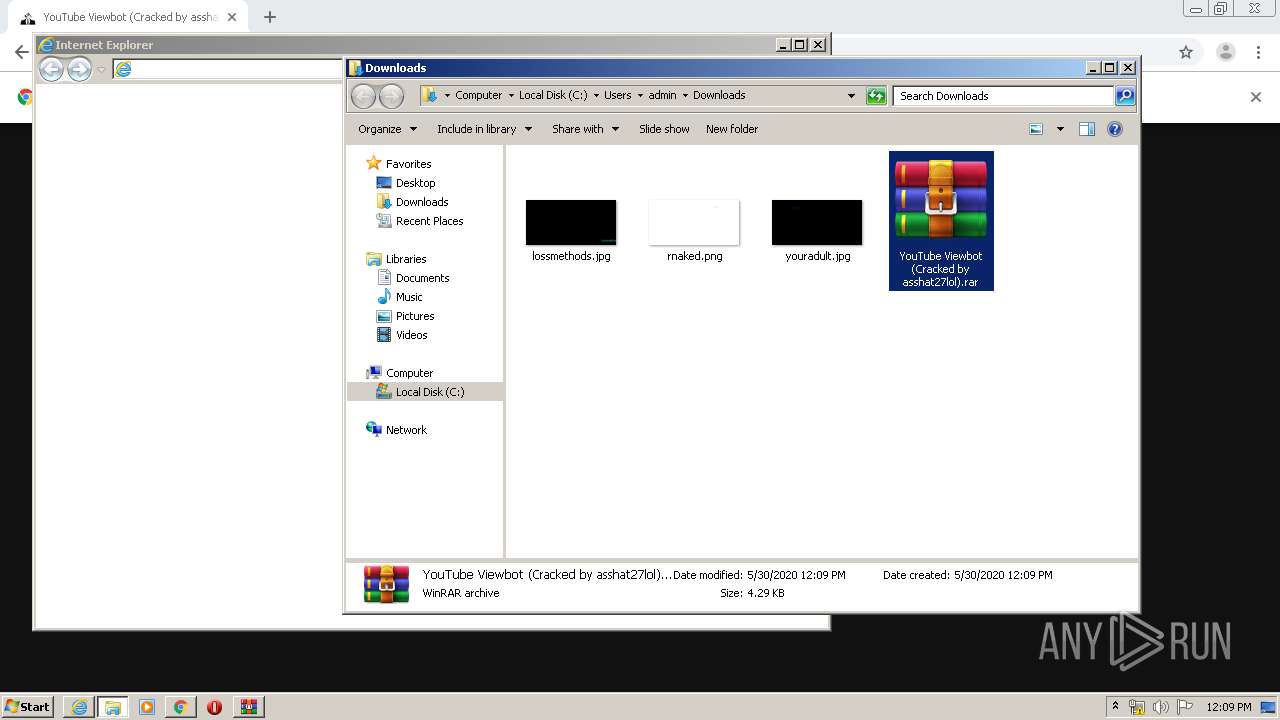
- WinRAR.exe (PID: 3708)
INFO
Reads the hosts file
- chrome.exe (PID: 1196)
- chrome.exe (PID: 884)
Reads Internet Cache Settings
- chrome.exe (PID: 1196)
- iexplore.exe (PID: 3488)
- iexplore.exe (PID: 1524)
Application launched itself
- iexplore.exe (PID: 3488)
- chrome.exe (PID: 1196)
Changes internet zones settings
- iexplore.exe (PID: 3488)
Manual execution by user
- iexplore.exe (PID: 3488)
- WinRAR.exe (PID: 2724)
- WinRAR.exe (PID: 3708)
- YouTube Viewbot (CRACKED).exe (PID: 2240)
Reads internet explorer settings
- iexplore.exe (PID: 1524)
Reads settings of System Certificates
- chrome.exe (PID: 884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
36
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9330651059784833268,18280779383953532130,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3847020193465867715 --mojo-platform-channel-handle=504 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9330651059784833268,18280779383953532130,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16905503004960072156 --mojo-platform-channel-handle=4172 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9330651059784833268,18280779383953532130,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16423293690382844382 --mojo-platform-channel-handle=1604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://anonfiles.com/Ld44O835oe/YouTube_Viewbot_Cracked_by_asshat27lol_rar" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9330651059784833268,18280779383953532130,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4295673240041931402 --mojo-platform-channel-handle=4572 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9330651059784833268,18280779383953532130,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7737597306024549160 --mojo-platform-channel-handle=4980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3488 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,9330651059784833268,18280779383953532130,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5253314679026828510 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9330651059784833268,18280779383953532130,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8651819040900583930 --mojo-platform-channel-handle=3896 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9330651059784833268,18280779383953532130,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17079343337061663090 --mojo-platform-channel-handle=5032 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 278
Read events
2 109
Write events
160
Delete events
9
Modification events
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1196-13235310566997625 |
Value: 259 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
50
Text files
212
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED23EE7-4AC.pma | — | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\179acbfa-642a-4028-8d95-a1fa0be58125.tmp | — | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12988f.TMP | text | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF12989e.TMP | text | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF129a92.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
38
DNS requests
30
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | chrome.exe | GET | — | 139.99.155.250:80 | http://mismos.xyz/lp/14/jquery-1.12.4.min.js | AU | — | — | whitelisted |
884 | chrome.exe | GET | — | 139.99.155.250:80 | http://mismos.xyz/lp/14/jquery-ui.js | AU | — | — | whitelisted |
884 | chrome.exe | GET | — | 139.99.155.250:80 | http://mismos.xyz/lp/14/iconNotify.png | AU | — | — | whitelisted |
884 | chrome.exe | GET | — | 139.99.155.250:80 | http://mismos.xyz/lp/14/fav.png | AU | — | — | whitelisted |
884 | chrome.exe | GET | 200 | 139.99.155.250:80 | http://mismos.xyz/lp/14/?v=500 | AU | html | 34.3 Kb | whitelisted |
884 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
884 | chrome.exe | GET | 200 | 139.99.155.250:80 | http://mismos.xyz/lp/14/modernArrow5.png | AU | image | 2.10 Kb | whitelisted |
884 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
884 | chrome.exe | GET | 200 | 74.125.4.216:80 | http://r2---sn-aigzrney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.217.117.39&mm=28&mn=sn-aigzrney&ms=nvh&mt=1590836897&mv=m&mvi=1&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
884 | chrome.exe | GET | 200 | 74.125.4.203:80 | http://r5---sn-aigzrner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.217.117.39&mm=28&mn=sn-aigzrner&ms=nvh&mt=1590836897&mv=m&mvi=4&pl=25&shardbypass=yes | US | crx | 816 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
884 | chrome.exe | 172.67.219.188:443 | anonfiles.com | — | US | unknown |
884 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
884 | chrome.exe | 143.204.201.46:443 | traintincre.fun | — | US | suspicious |
884 | chrome.exe | 104.16.108.36:443 | providentsopport.site | Cloudflare Inc | US | unknown |
884 | chrome.exe | 54.144.3.29:443 | baconaces.pro | Amazon.com, Inc. | US | suspicious |
884 | chrome.exe | 13.225.87.21:443 | appearedsoci.fun | — | US | suspicious |
884 | chrome.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
884 | chrome.exe | 18.195.195.71:443 | hanner-blobal.com | Amazon.com, Inc. | DE | suspicious |
884 | chrome.exe | 139.99.155.250:80 | mismos.xyz | OVH SAS | AU | suspicious |
— | — | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
baconaces.pro |
| shared |
www.google.com |
| malicious |
appearedsoci.fun |
| malicious |
traintincre.fun |
| suspicious |
providentsopport.site |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
884 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
884 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
884 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
884 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
884 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
884 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |