| download: | index.html |
| Full analysis: | https://app.any.run/tasks/13b45165-7e6e-4577-a67f-3d596c11d821 |
| Verdict: | No threats detected |
| Analysis date: | November 13, 2020, 00:37:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | AB9A846C21C09FD1E082156395077DF8 |
| SHA1: | 24D3DC6F6C3C6F684BCF30A1D1E55F75C6BFADD4 |
| SHA256: | 9DB39945F7C9AA8BF6186C9066370DD6FD7BC0A5C3AD758FE35285A6F4296026 |
| SSDEEP: | 384:25UDg5PnimrfIVl7ygywZXjErHH+a3/9ggs1v7f1z:25vU7ygRto+aPDyz1z |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2080)
- iexplore.exe (PID: 3712)
Reads settings of System Certificates
- iexplore.exe (PID: 2028)
- iexplore.exe (PID: 2080)
Changes internet zones settings
- iexplore.exe (PID: 2080)
Application launched itself
- iexplore.exe (PID: 2080)
- iexplore.exe (PID: 2028)
Changes settings of System certificates
- iexplore.exe (PID: 2028)
- iexplore.exe (PID: 2080)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2028)
- iexplore.exe (PID: 2080)
Reads internet explorer settings
- iexplore.exe (PID: 2028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
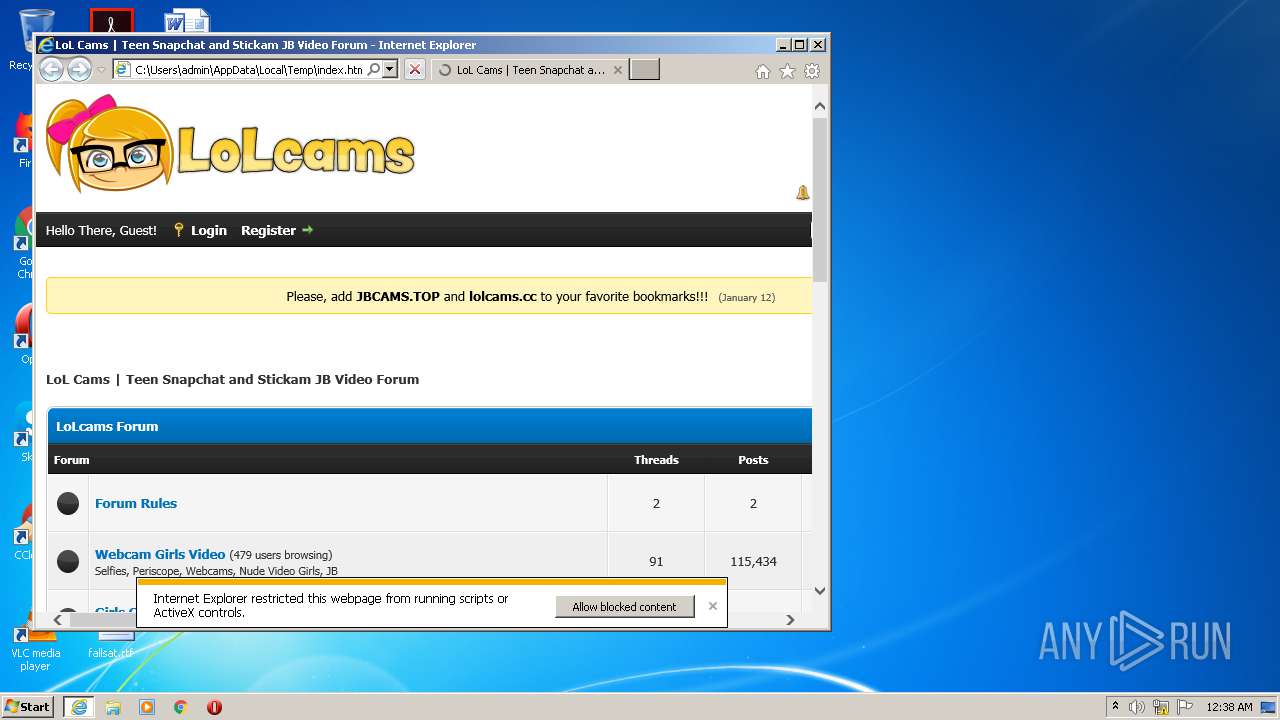
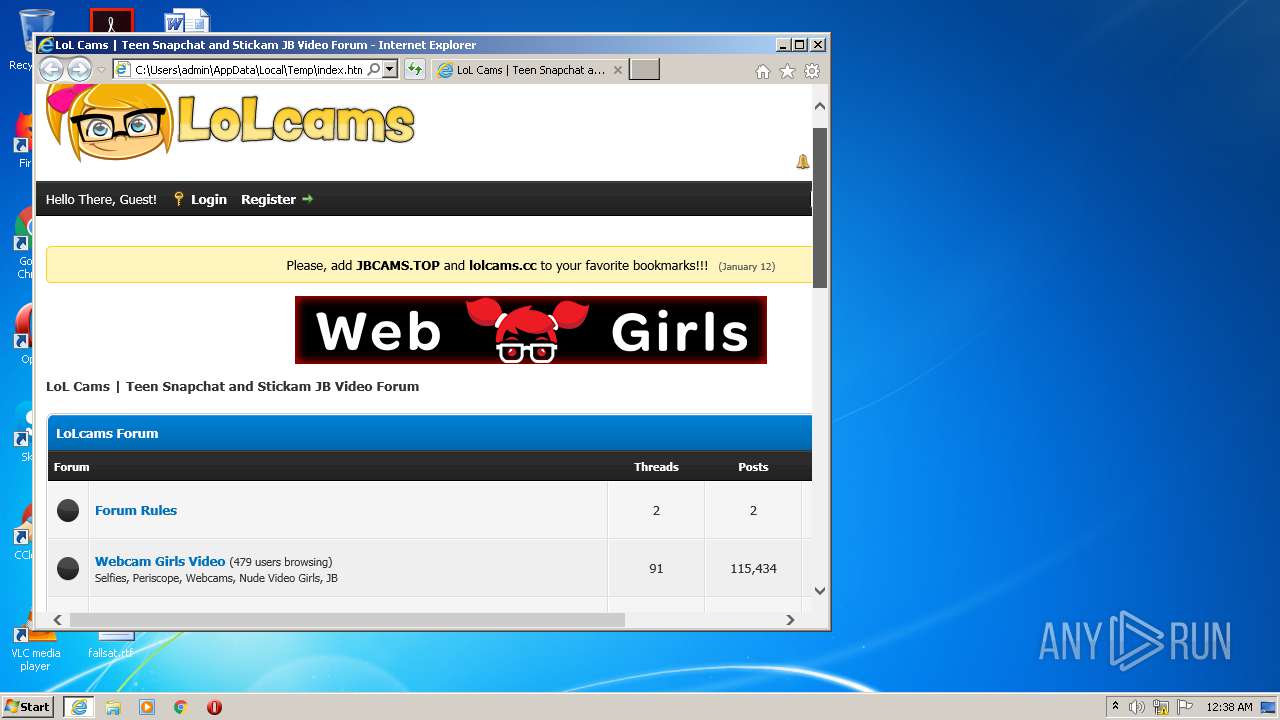
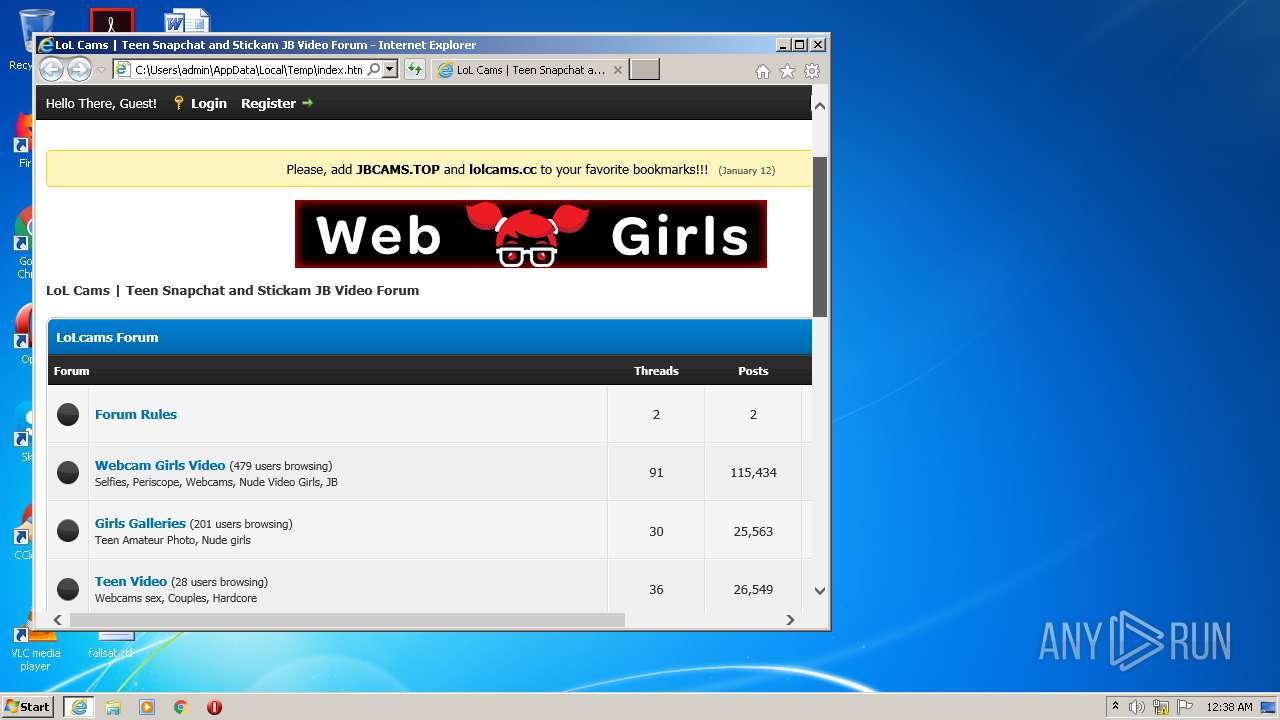
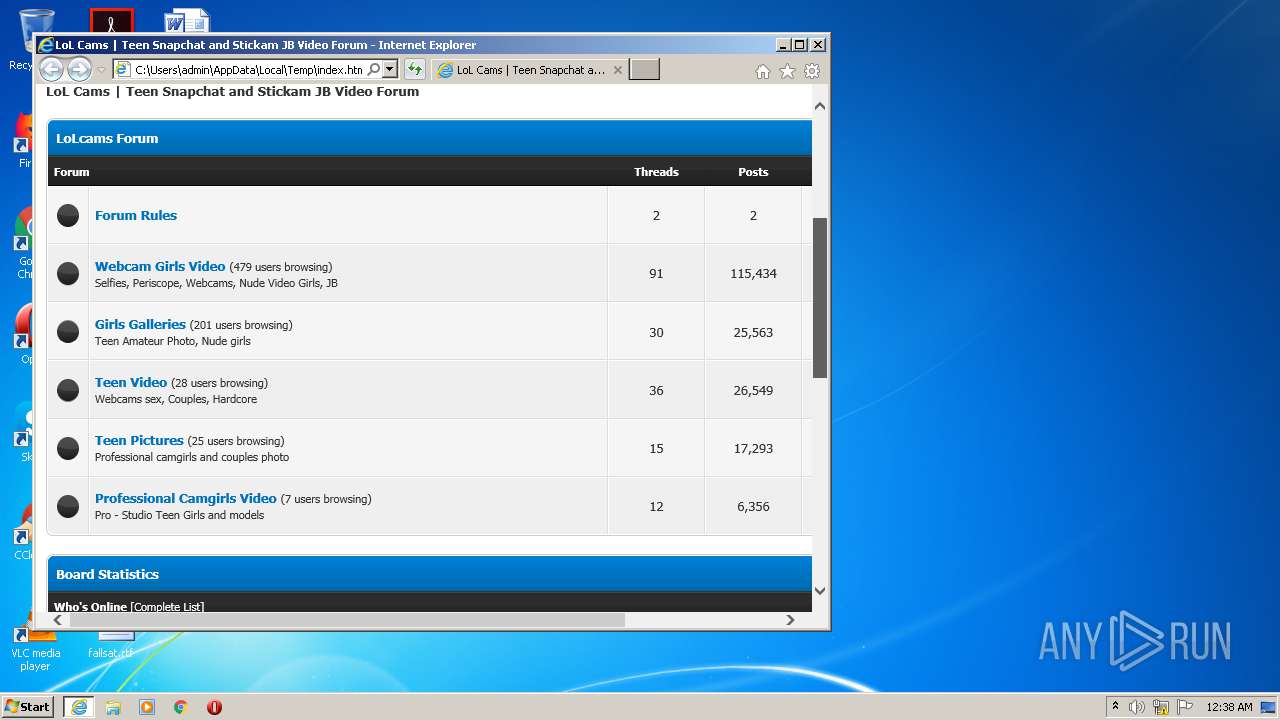
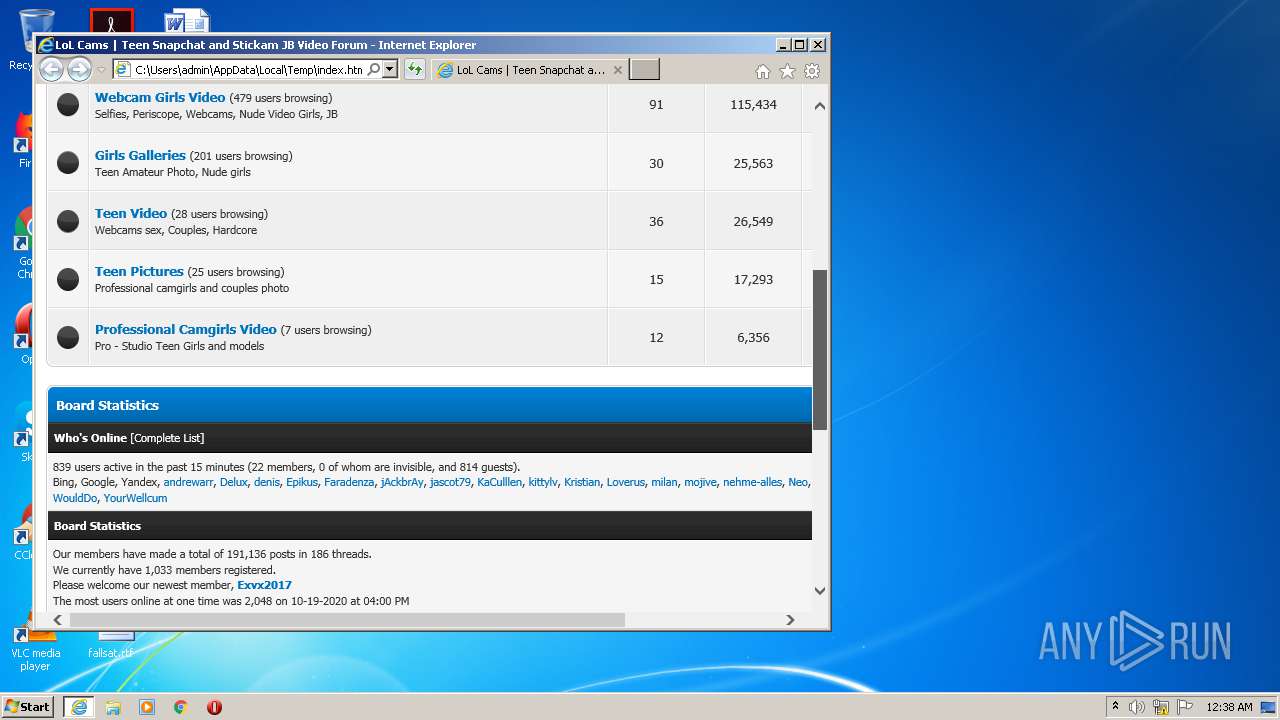
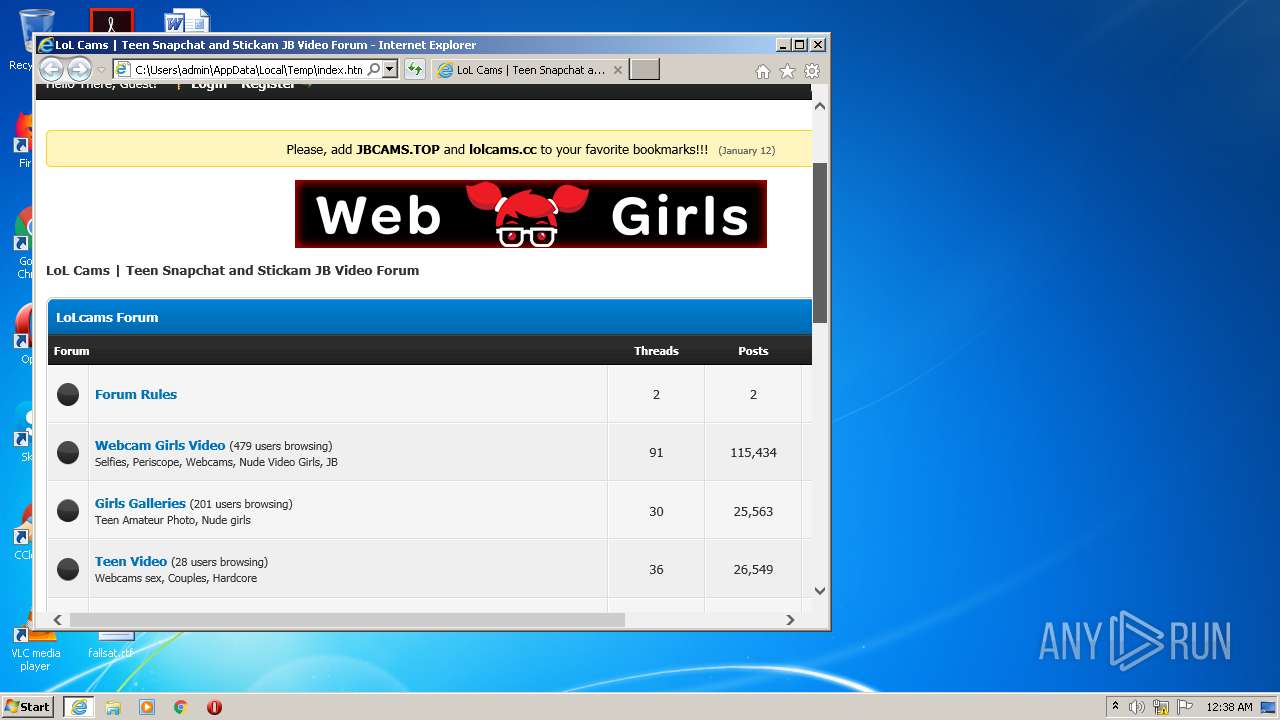
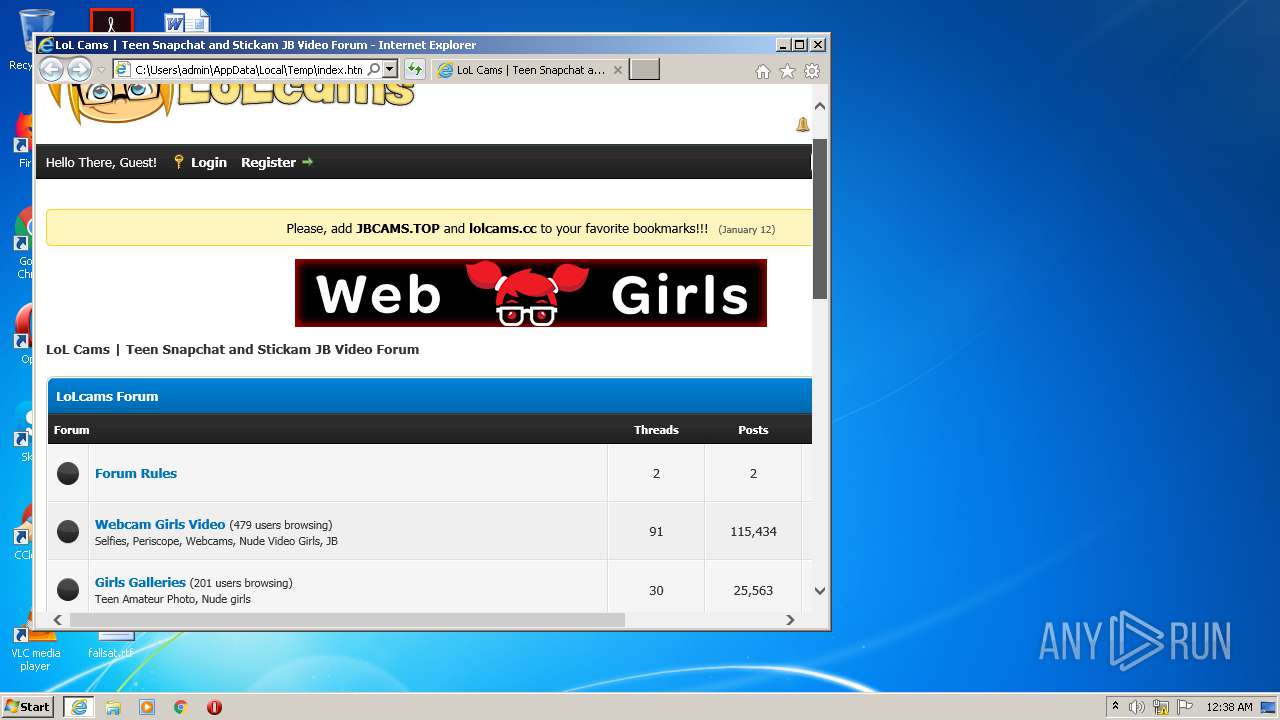
| Title: | LoL Cams | Teen Snapchat and Stickam JB Video Forum |
|---|---|
| Keywords: | ass, boobs ,cute, forum, girls, hebe, hot, jailbaits, jb, jfraction, jimperial, kingpass, kitty, kittygfs, lsmagazine, ls-models, models, mouse, nonude, nude, omegle, periscope, photos, pthc, pussy, secret, session, sets, sexy, siberian, skype, snapcamera, snapcams, snapchat, stickam, teens, tiktok, tinder, tits, vichatter, webcam, young |
| Description: | Beautiful and young girls love to show themselves on an online camera so that you drool! You will find the best pictures of young and naked schoolgirls in the rare section. New perescope broadcasts, Snapchats, Tik-Tok videos, and much more you will see on Lolcams.cc |
| ContentType: | text/html; charset=UTF-8 |
| ContentScriptType: | text/javascript |
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2080 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3712 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2080 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 438
Read events
1 334
Write events
100
Delete events
4
Modification events
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1460137960 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30849365 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2080) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
17
Text files
23
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2028 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabAE68.tmp | — | |
MD5:— | SHA256:— | |||
| 2028 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarAE69.tmp | — | |
MD5:— | SHA256:— | |||
| 2028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\banner5[1].jpg | image | |
MD5:DC92DE524154A175672B2005C8F1CCB6 | SHA256:05CEADE08D39FCC8D94FAFD3E580467D93B648268BA6AAC701D185A592B3ED82 | |||
| 2028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\big[1].png | image | |
MD5:87CB5621B285E9FC75B7EAF9CC193F8B | SHA256:4C8A367AA8967FC375C55FD5E48D271459B8A66485DB1FB419F47FF88CFDC8A2 | |||
| 2028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\jquery[1].js | text | |
MD5:506818B27683A76A07C9C026CC4BE3D7 | SHA256:869BFE77FF727251FB013C36805A83179F9DB813C149868E5CA300FD36ABEA28 | |||
| 2028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\global[1].css | text | |
MD5:E571C9D2D623A58DE5C5B4BA55A70F2D | SHA256:7CB1E11165A4428790F3348CB2F24C055F688795D062F788063D4DCB4FDCF0C9 | |||
| 2028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\logo_lol_370x100[1].png | image | |
MD5:8A711B9BDFF4511EF0899654D5BEB648 | SHA256:2FAEFAD0882C079892867C93E7B21CC8FDB201572EB88154D1A5FCA0E9195A66 | |||
| 2028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:0801939D427D90F7DE415AC7A2FEA6BB | SHA256:CBEC26A4042178CEE26CF780F1814C5E46DA3180C4460AF1D60D8F9EADD4290A | |||
| 2028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:29A2F3937E8B9F23A6D06A430DC5CF2F | SHA256:722377468EE33FC6291F2D4411DC76F6448F2DCE70DCE50C9E4F4E7B6824D59B | |||
| 2028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_138E69CF1BE7177AEB8B5C026A865608 | der | |
MD5:2CB577DE177D19B3DE5794C487D08DCF | SHA256:F3D6ED277A7141210E1A747EC4140EE90D66A241789137FED0FBE57066F9CB33 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
35
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2028 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2028 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2028 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAjNJayiXCWJo7dJZP7GzAg%3D | US | der | 279 b | whitelisted |
2028 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAqcRPxKt55CMXYtJnH1xSM%3D | US | der | 279 b | whitelisted |
2028 | iexplore.exe | GET | 200 | 103.16.26.85:80 | http://lolcams.al/cache/themes/theme1/global.css | HK | text | 30.3 Kb | unknown |
2028 | iexplore.exe | GET | 200 | 103.16.26.85:80 | http://lolcams.al/jscripts/jquery.plugins.min.js?ver=1821 | HK | text | 14.4 Kb | unknown |
2028 | iexplore.exe | GET | 200 | 103.16.26.85:80 | http://lolcams.al/cache/themes/theme1/css3.css | HK | text | 3.04 Kb | unknown |
2028 | iexplore.exe | GET | 200 | 103.16.26.85:80 | http://lolcams.al/jscripts/jquery.js?ver=1821 | HK | text | 84.8 Kb | unknown |
2028 | iexplore.exe | GET | 200 | 103.16.27.80:80 | http://snaps.al/banner5.jpg | HK | image | 9.26 Kb | suspicious |
2028 | iexplore.exe | GET | 200 | 103.16.26.85:80 | http://lolcams.al/jscripts/general.js?ver=1821 | HK | text | 15.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2028 | iexplore.exe | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
2028 | iexplore.exe | 103.16.26.85:80 | lolcams.al | Hong Kong Serverworks Limited | HK | unknown |
2028 | iexplore.exe | 103.16.27.80:80 | snaps.al | Hong Kong Serverworks Limited | HK | suspicious |
2028 | iexplore.exe | 104.21.234.41:80 | vipmodels.tv | Cloudflare Inc | US | suspicious |
2028 | iexplore.exe | 104.18.51.12:80 | toplist.2nn.xyz | Cloudflare Inc | US | suspicious |
2028 | iexplore.exe | 104.24.111.242:443 | cutetop.space | Cloudflare Inc | US | unknown |
2028 | iexplore.exe | 5.8.63.7:80 | 18top.link | Handy Networks, LLC | US | suspicious |
2028 | iexplore.exe | 172.67.221.246:443 | toplist.2nn.xyz | — | US | unknown |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2080 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lolcams.al |
| unknown |
i.imgur.com |
| malicious |
vipmodels.tv |
| suspicious |
snaps.al |
| suspicious |
cutecams.space |
| unknown |
toplist.2nn.xyz |
| suspicious |
cutetop.space |
| unknown |
tp1.2nn.xyz |
| suspicious |
18top.link |
| malicious |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2028 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |