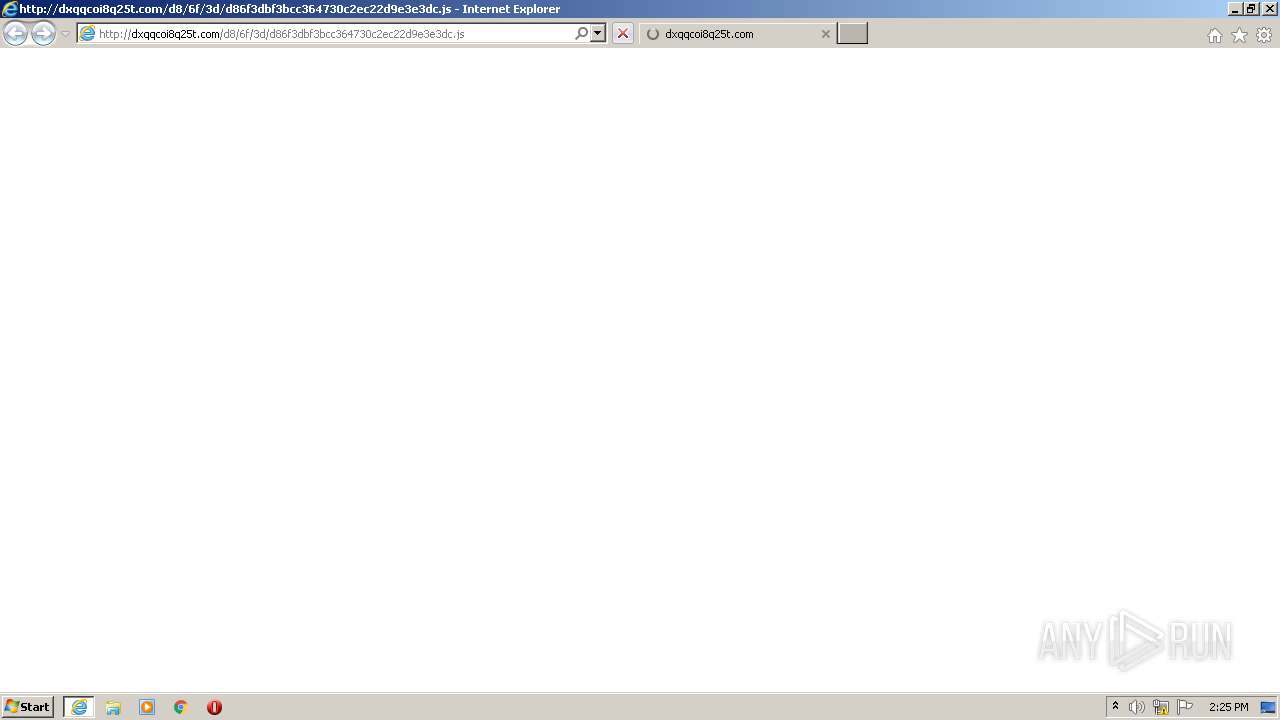
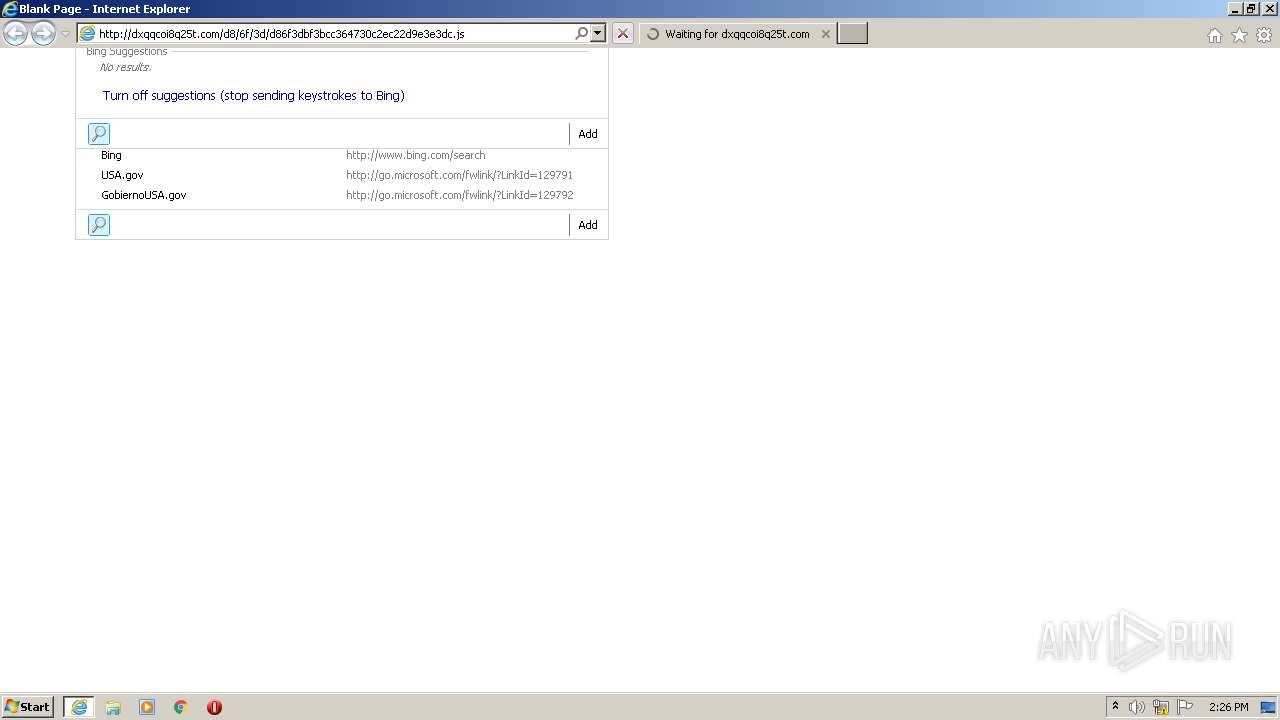
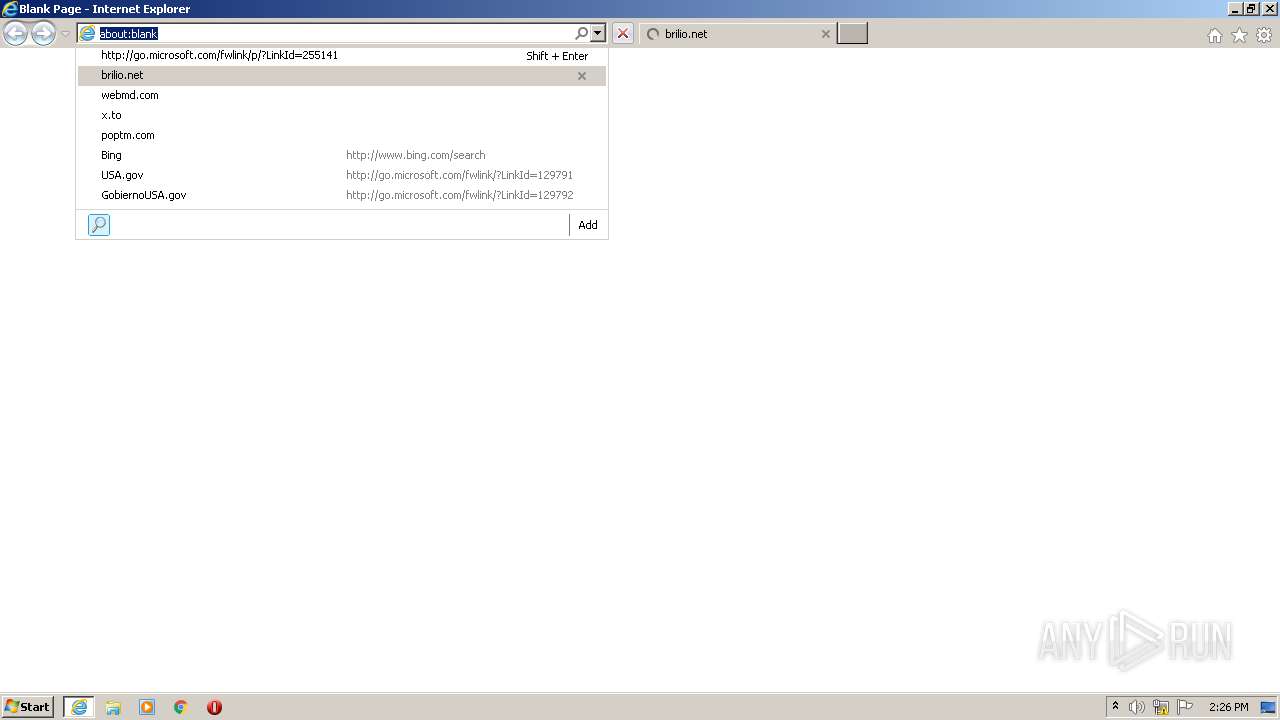
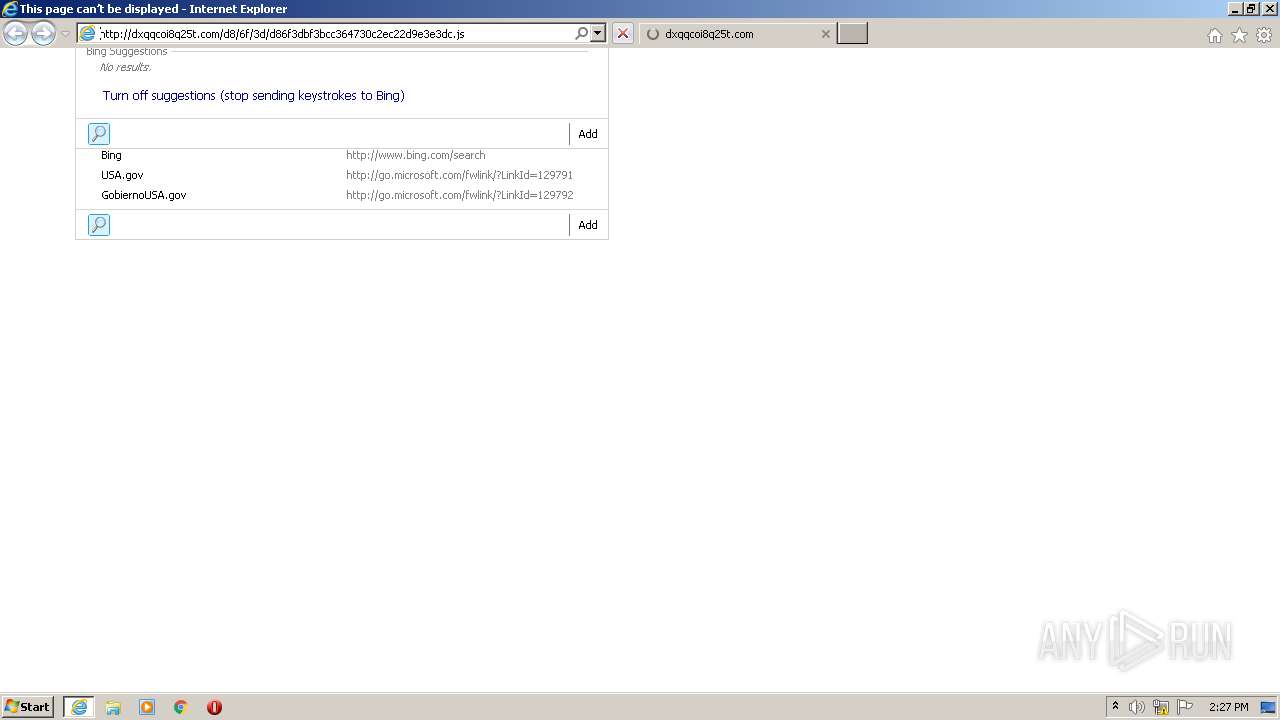
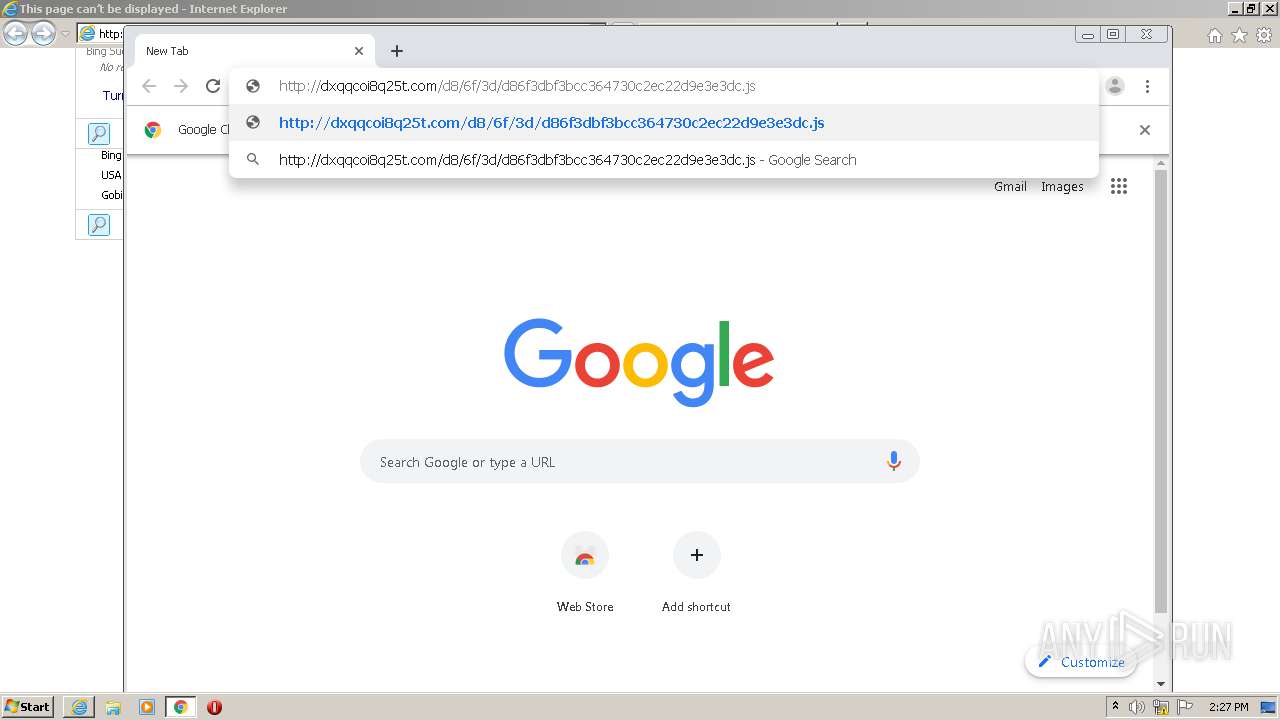
| URL: | http://dxqqcoi8q25t.com/d8/6f/3d/d86f3dbf3bcc364730c2ec22d9e3e3dc.js |
| Full analysis: | https://app.any.run/tasks/595d0abb-7c6f-44c9-89e0-39d8b1dde033 |
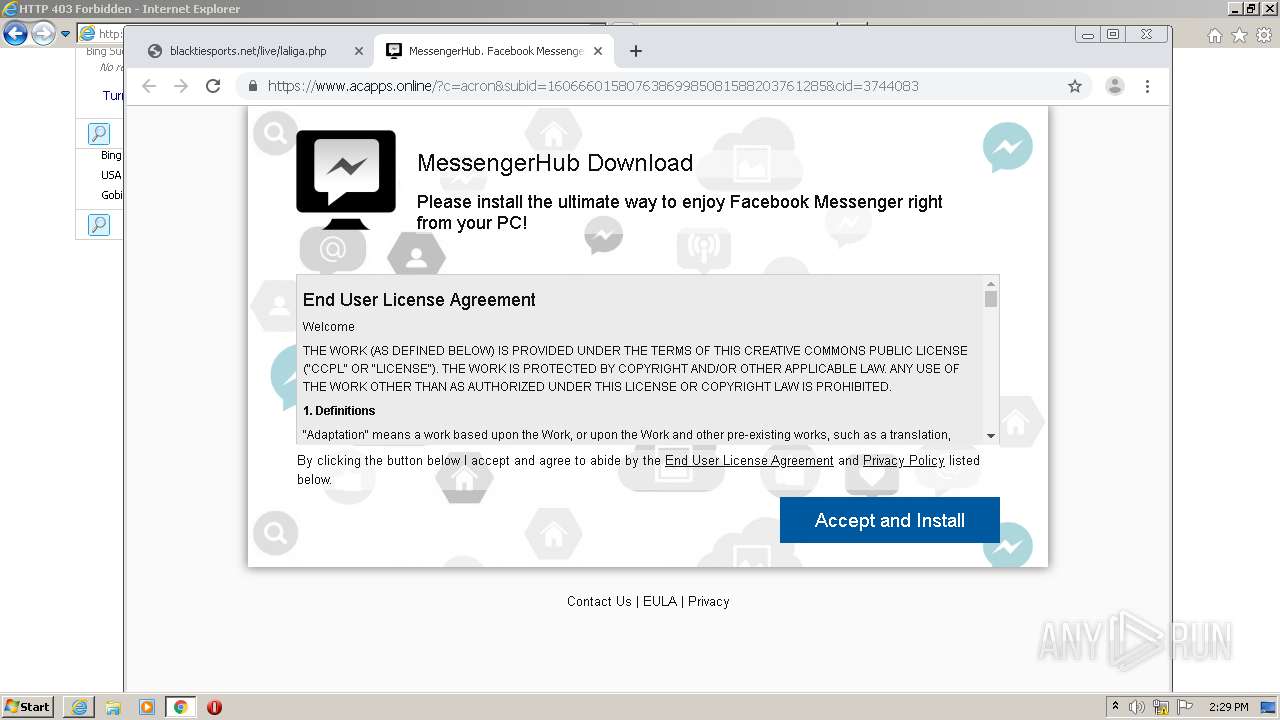
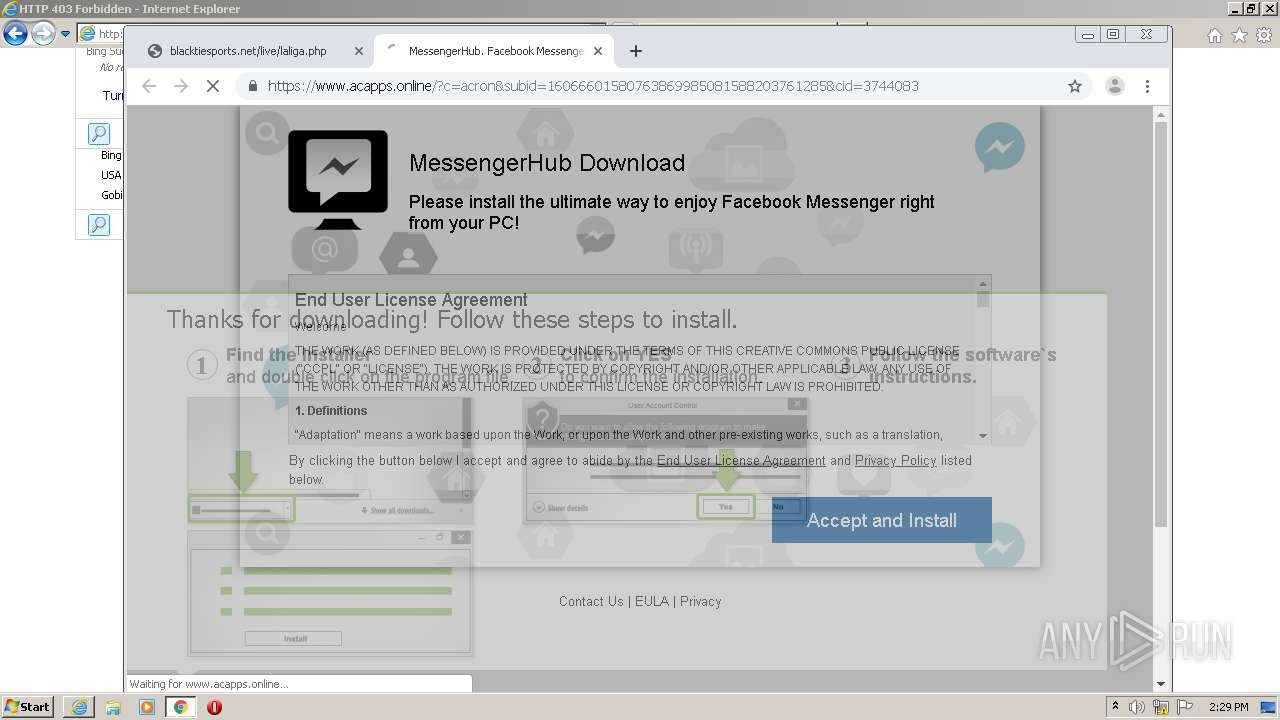
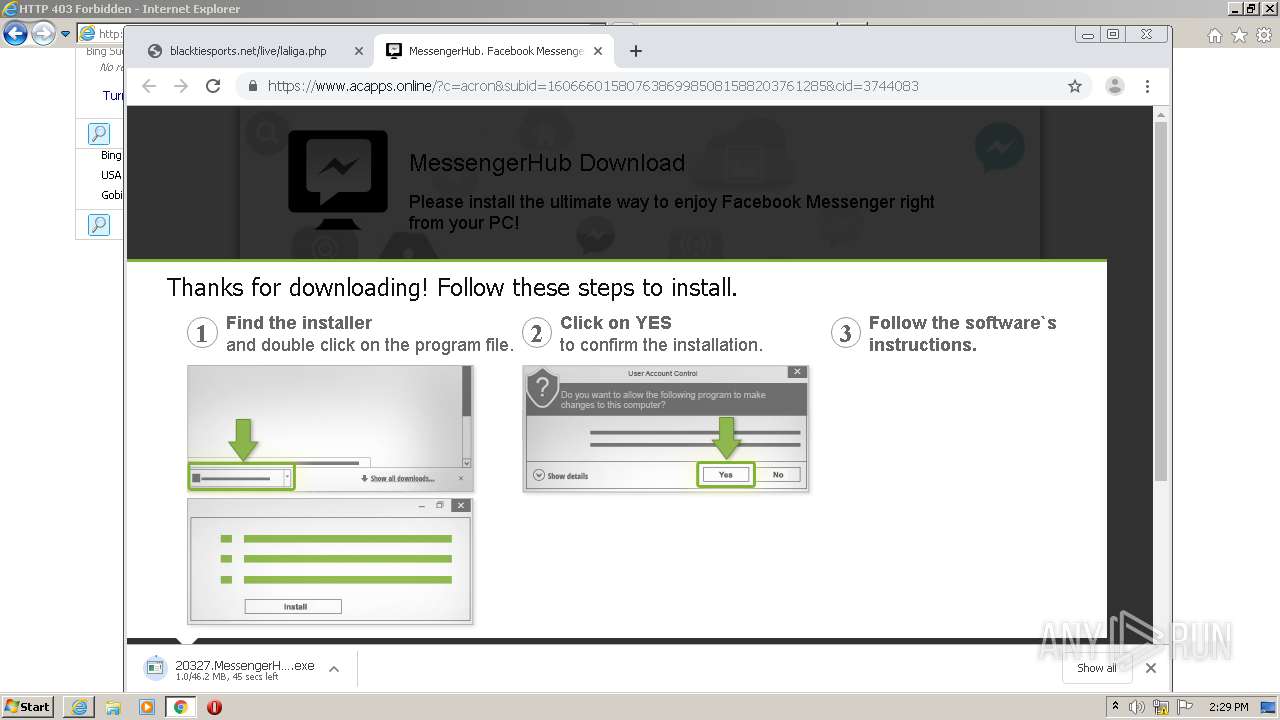
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 14:25:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 26BE939480D574DD8D4FD45F12A2DACF |
| SHA1: | C092E5C9984756C143926871C3217204C13AB85D |
| SHA256: | 9DA69AC6DD390C08F004691DFF4F2E546B4B3EE5EF73FB08B3A5AC873B8888E2 |
| SSDEEP: | 3:N1KadNOrZbcIOH2URSSAe+un:CadNOrJOWURS4+un |
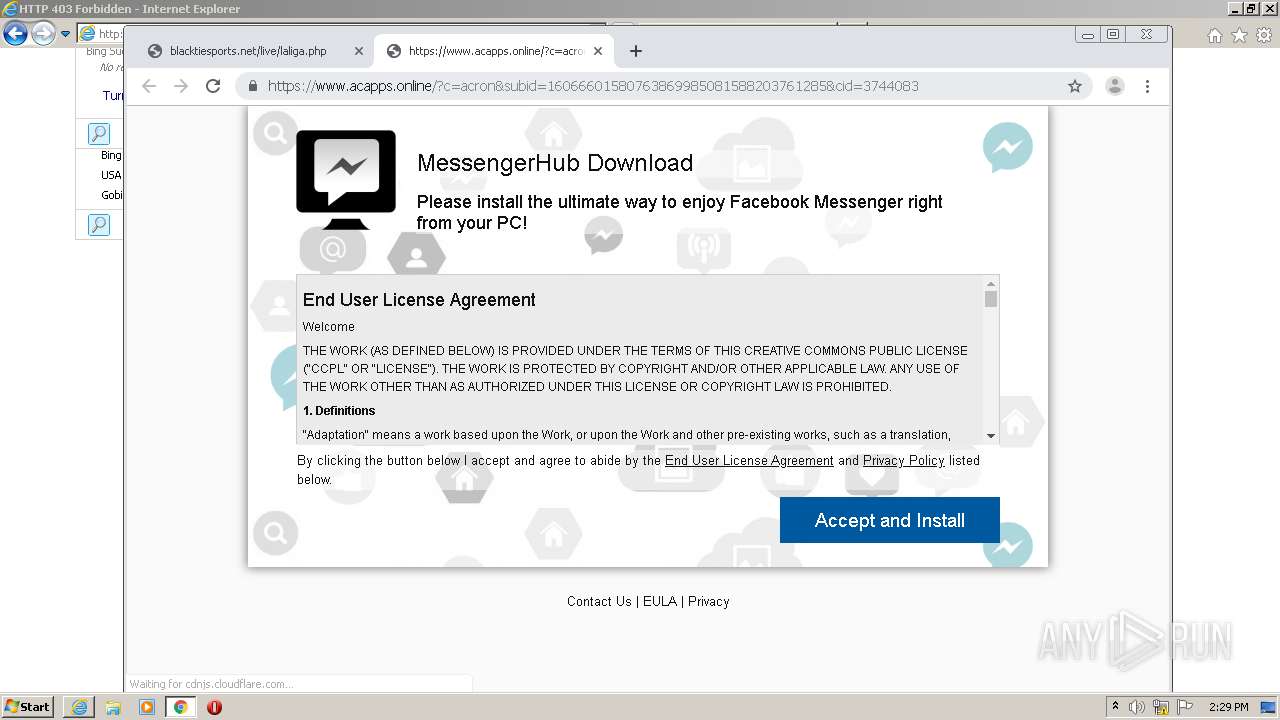
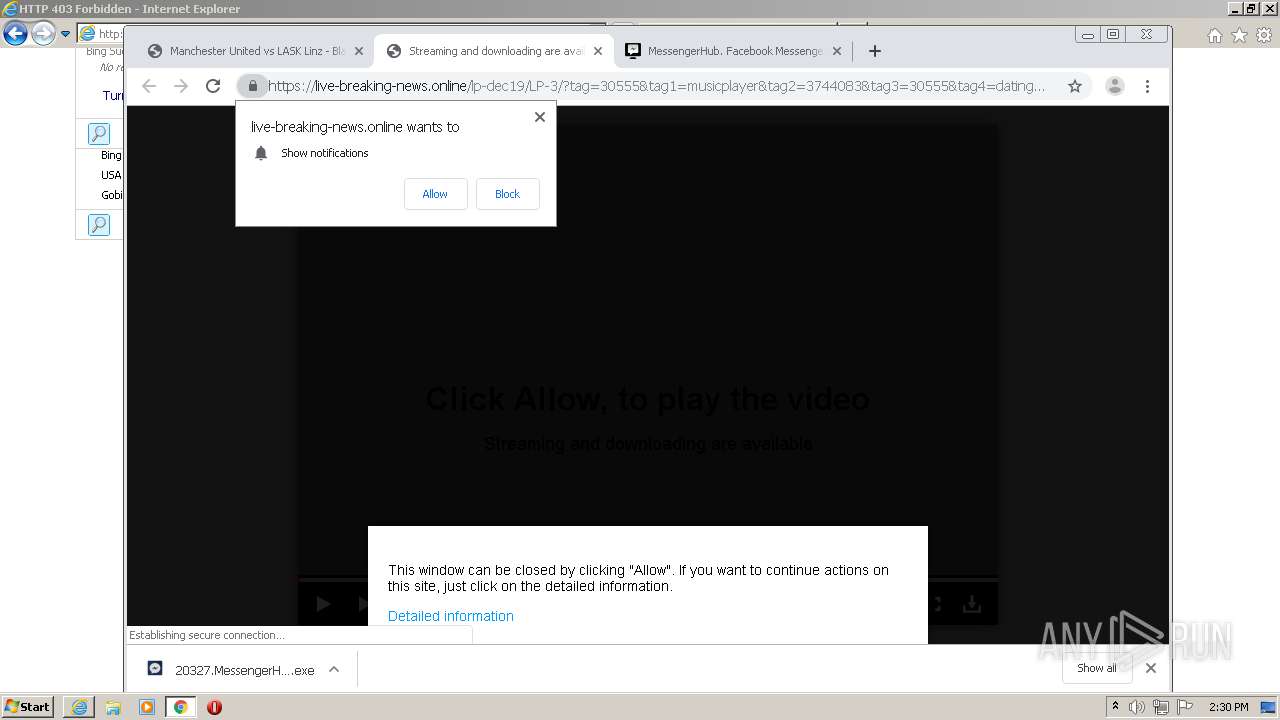
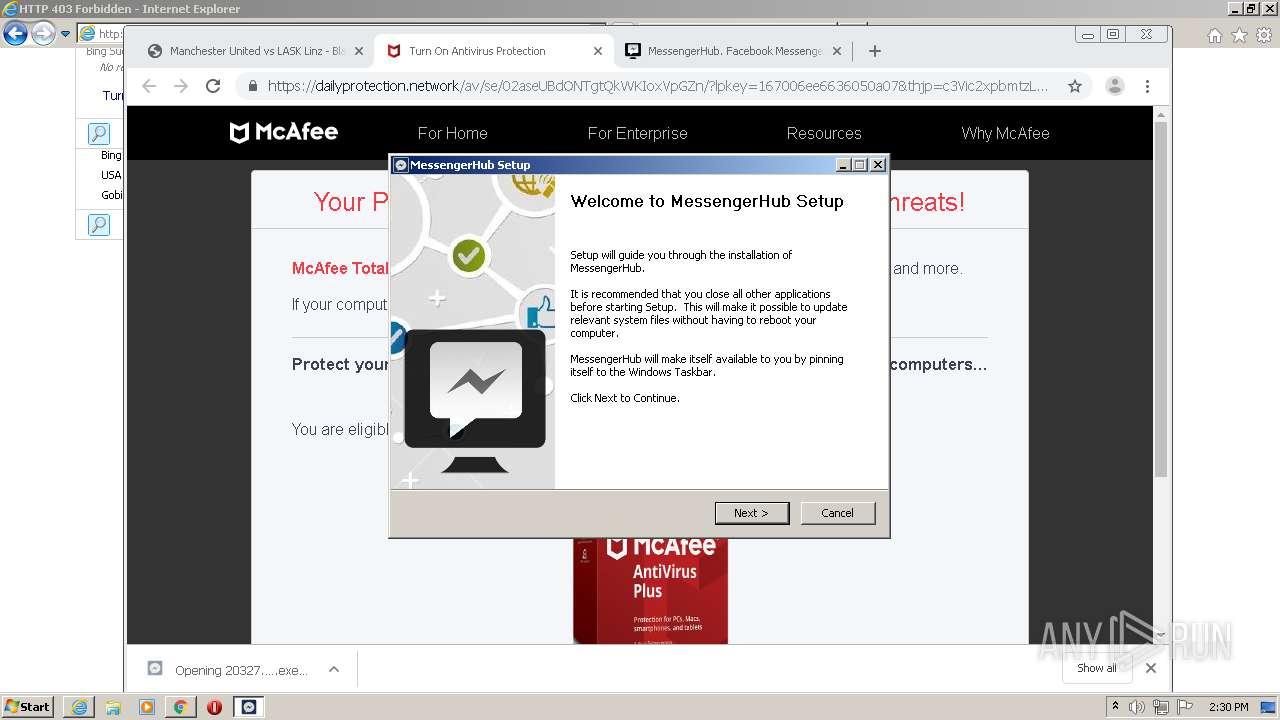
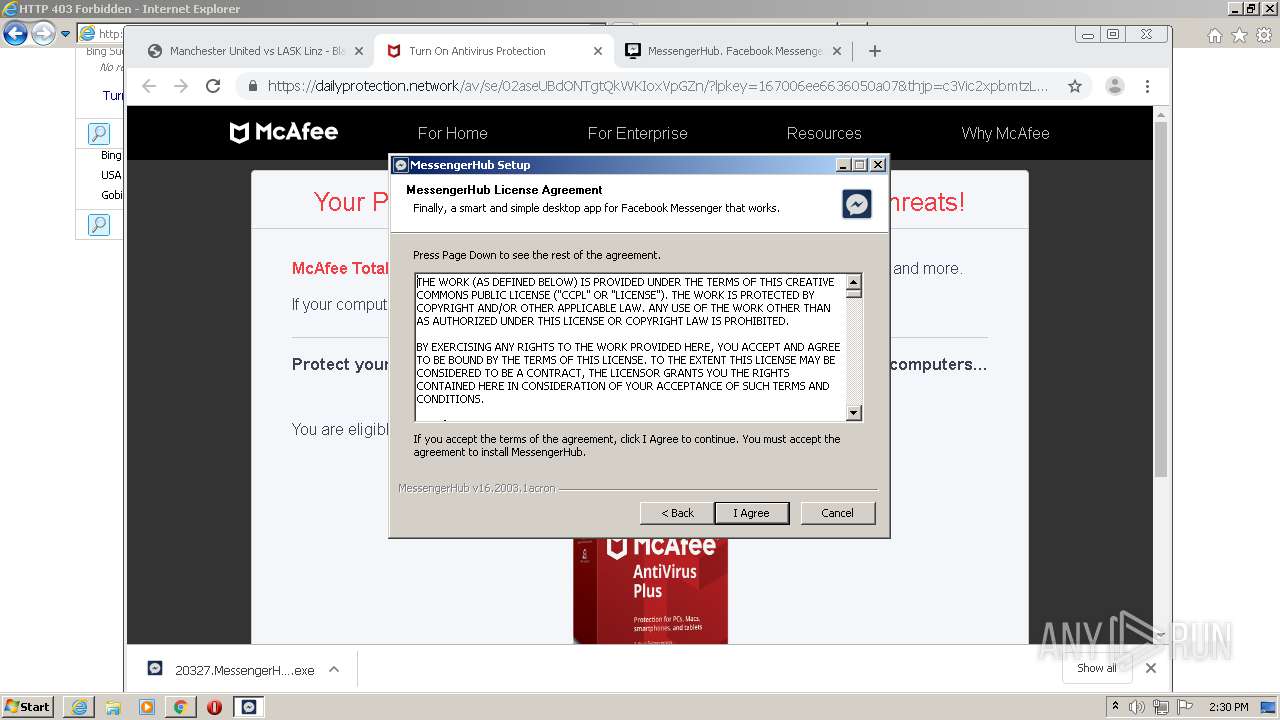
MALICIOUS
Application was dropped or rewritten from another process
- 20327.MessengerHub.16.2003.1acron.exe (PID: 2584)
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Loads dropped or rewritten executable
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Changes the autorun value in the registry
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Changes settings of System certificates
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
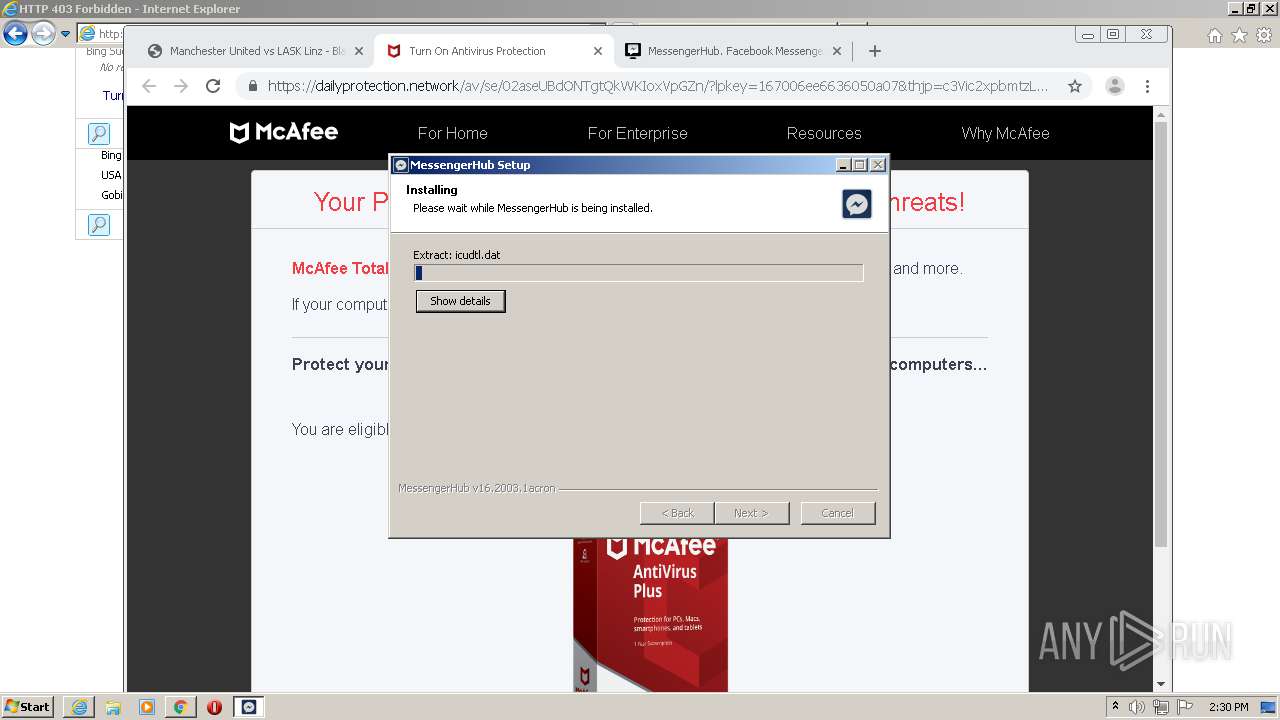
SUSPICIOUS
Executable content was dropped or overwritten
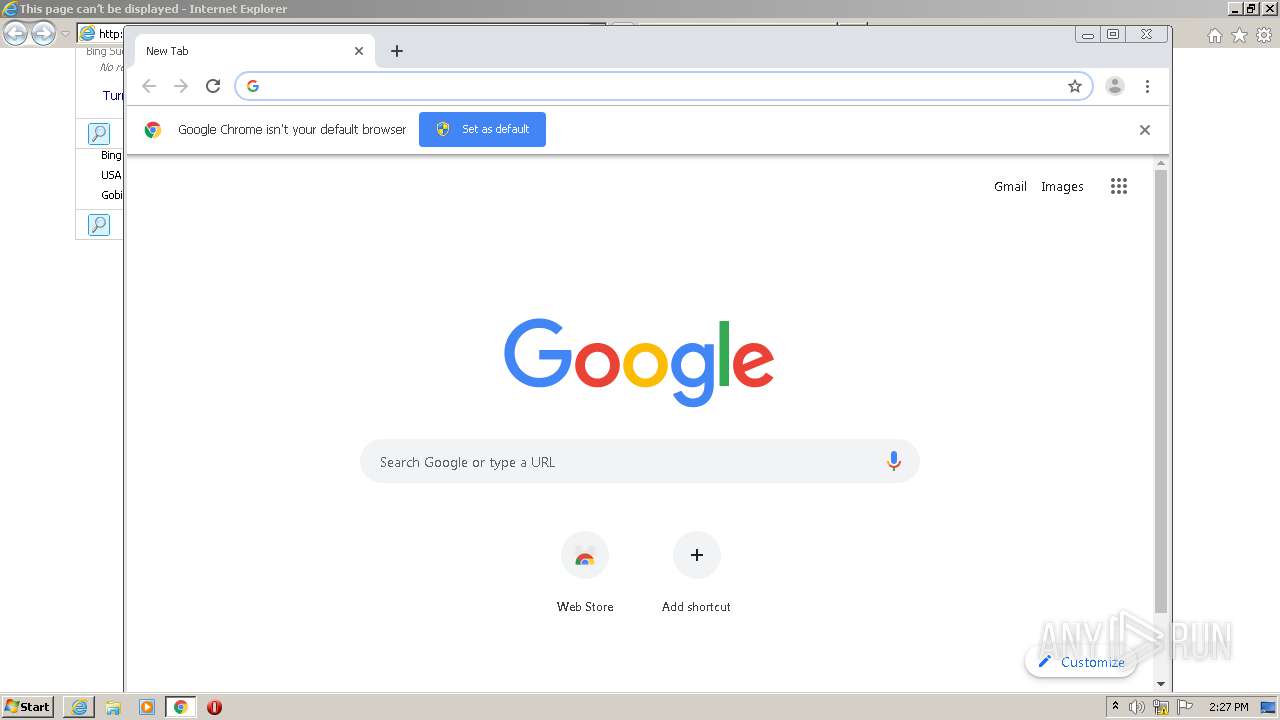
- chrome.exe (PID: 3144)
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3144)
Drops a file that was compiled in debug mode
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Drops a file with too old compile date
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Starts CMD.EXE for commands execution
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Creates files in the user directory
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Adds / modifies Windows certificates
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Creates a software uninstall entry
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Starts SC.EXE for service management
- cmd.exe (PID: 992)
INFO
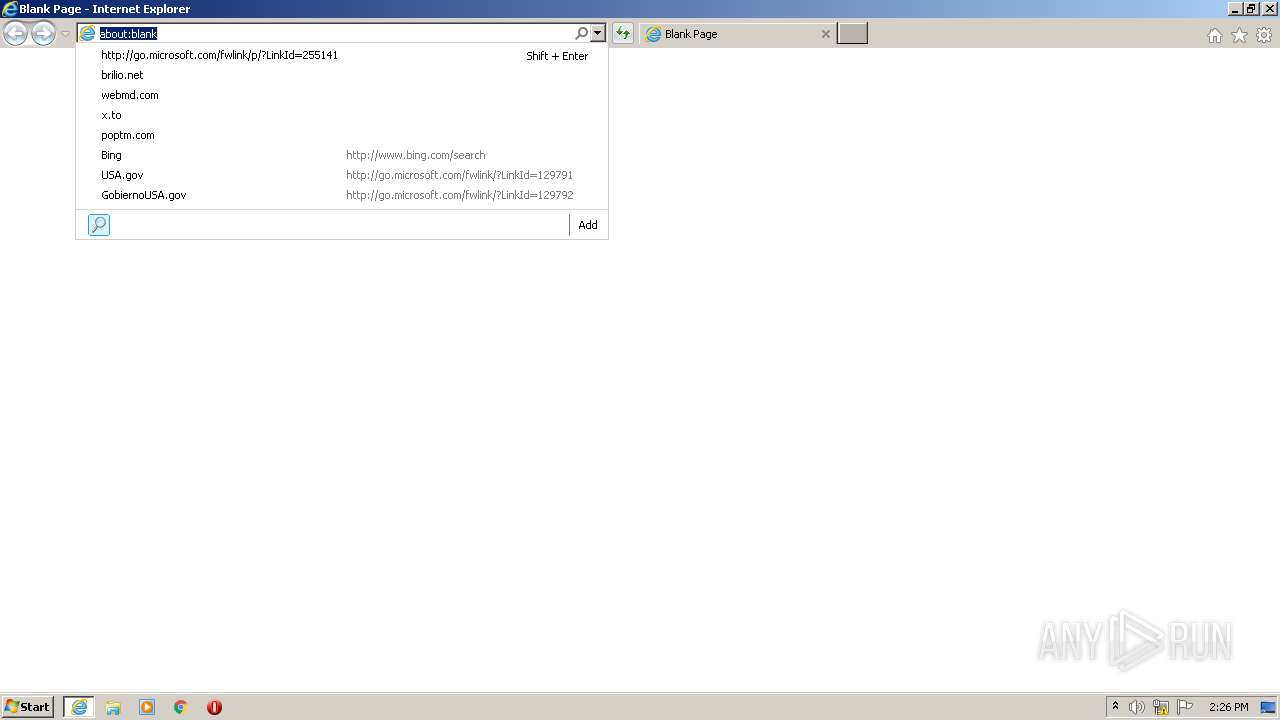
Reads internet explorer settings
- iexplore.exe (PID: 2316)
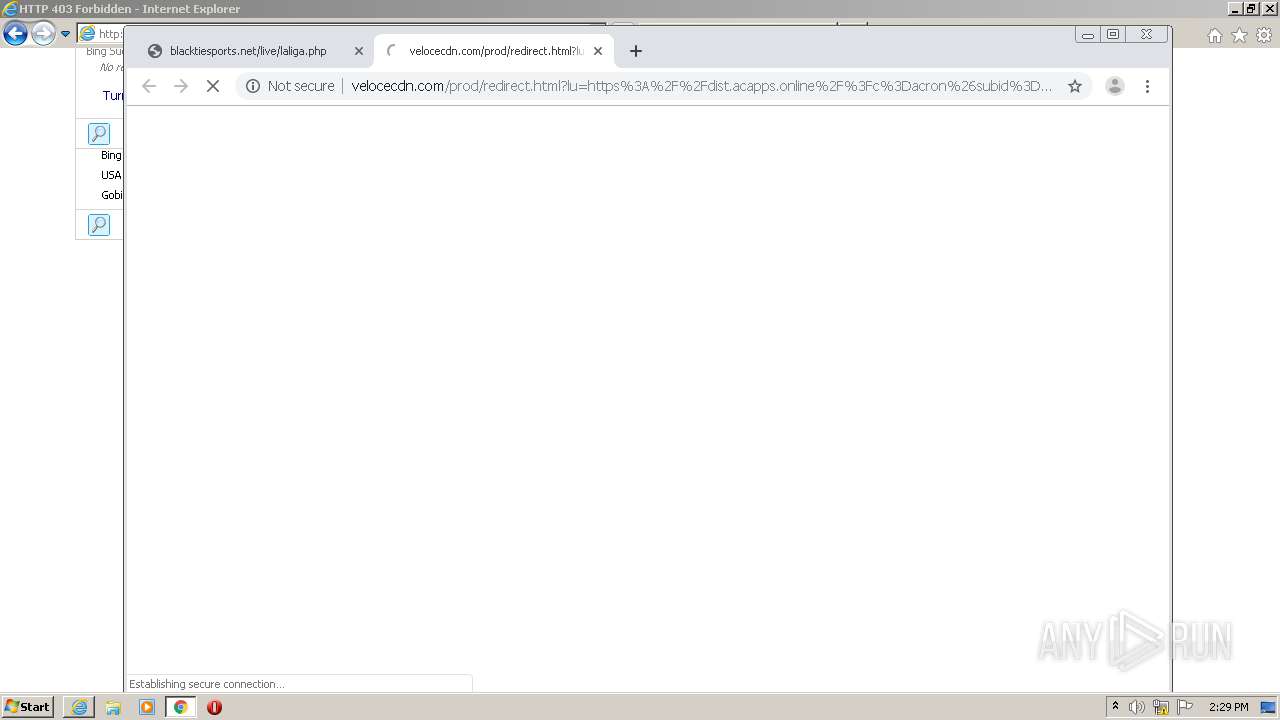
Changes internet zones settings
- iexplore.exe (PID: 2488)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2488)
Changes settings of System certificates
- iexplore.exe (PID: 2488)
- chrome.exe (PID: 2752)
Reads settings of System Certificates
- iexplore.exe (PID: 2488)
- chrome.exe (PID: 3144)
Application launched itself
- iexplore.exe (PID: 2488)
- chrome.exe (PID: 3144)
Manual execution by user
- iexplore.exe (PID: 1340)
- chrome.exe (PID: 3144)
Creates files in the user directory
- iexplore.exe (PID: 2316)
- iexplore.exe (PID: 2488)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2488)
Reads the hosts file
- chrome.exe (PID: 3144)
- chrome.exe (PID: 2752)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3144)
- 20327.MessengerHub.16.2003.1acron.exe (PID: 1524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
48
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,92510750772600983,16846094257265444056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5495199247258961630 --mojo-platform-channel-handle=3884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | C:\Windows\system32\cmd.exe /C "sc QUERY NPF | FIND /C "RUNNING"" | C:\Windows\system32\cmd.exe | — | 20327.MessengerHub.16.2003.1acron.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,92510750772600983,16846094257265444056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8729226659951286238 --mojo-platform-channel-handle=3388 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,92510750772600983,16846094257265444056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10703589766636721045 --mojo-platform-channel-handle=3416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,92510750772600983,16846094257265444056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16613709860711421553 --mojo-platform-channel-handle=2544 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,92510750772600983,16846094257265444056,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13359902189455164734 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,92510750772600983,16846094257265444056,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1510344496996254502 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,92510750772600983,16846094257265444056,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2207015339258247941 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,92510750772600983,16846094257265444056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17511118752964270520 --mojo-platform-channel-handle=3384 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 350
Read events
2 043
Write events
300
Delete events
7
Modification events
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2377443096 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30852699 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
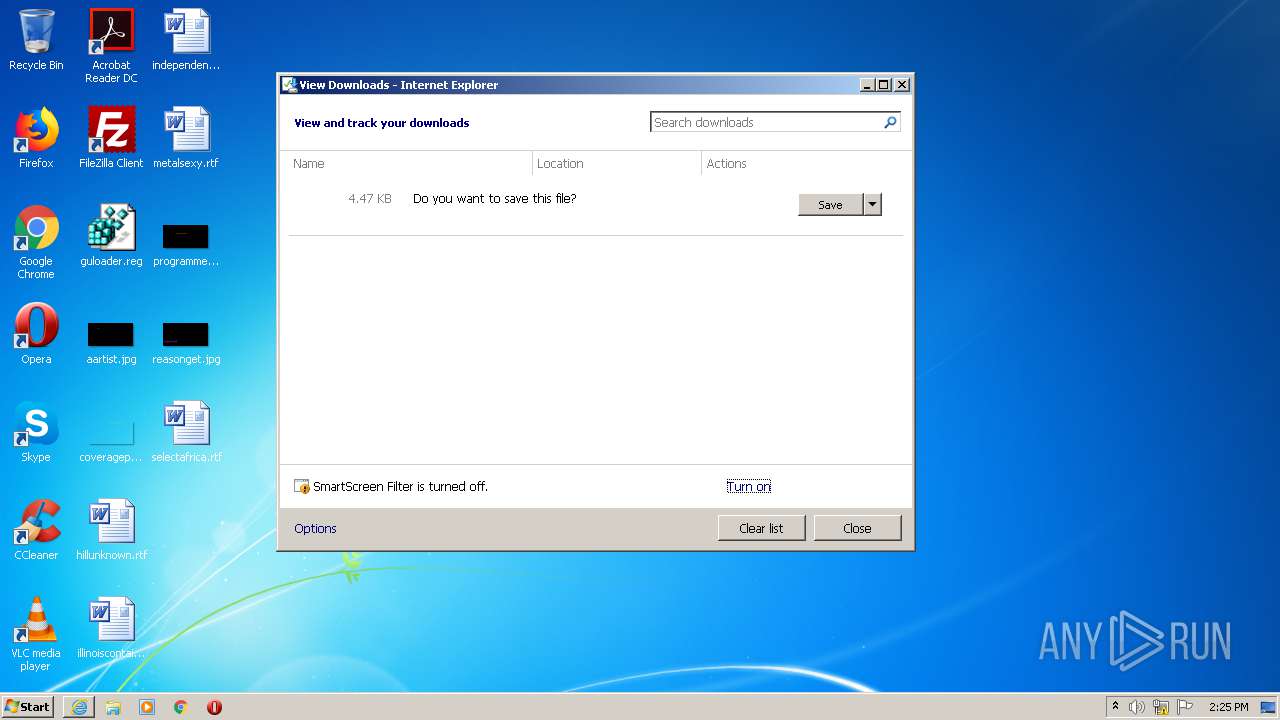
Executable files
15
Suspicious files
172
Text files
278
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\http_403[1] | — | |
MD5:— | SHA256:— | |||
| 2488 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD72E2040A5740308.TMP | — | |
MD5:— | SHA256:— | |||
| 2488 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2488 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabB890.tmp | — | |
MD5:— | SHA256:— | |||
| 2488 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarB891.tmp | — | |
MD5:— | SHA256:— | |||
| 2488 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verB8D1.tmp | — | |
MD5:— | SHA256:— | |||
| 2316 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\9KKWQS3Q.txt | — | |
MD5:— | SHA256:— | |||
| 2316 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\9Z81PRDV.txt | — | |
MD5:— | SHA256:— | |||
| 2316 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\KLDXKO86.txt | — | |
MD5:— | SHA256:— | |||
| 2316 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\XFZ84WE3.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
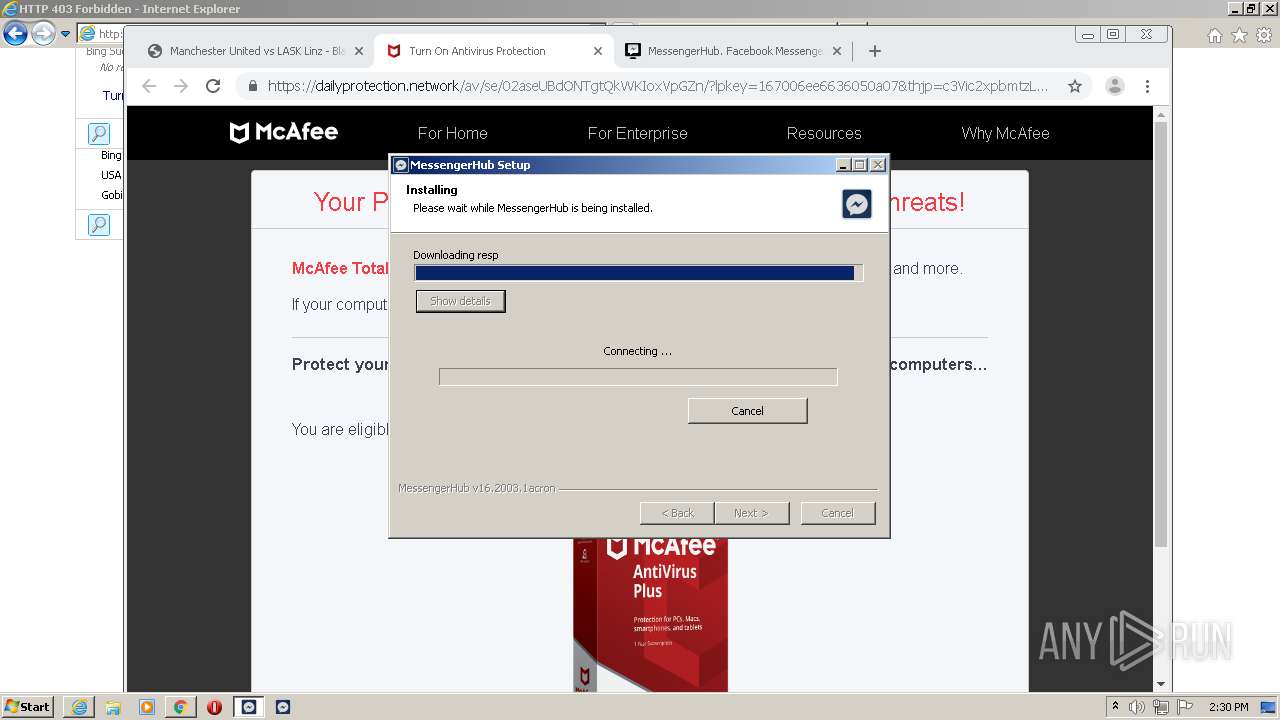
HTTP(S) requests
61
TCP/UDP connections
158
DNS requests
89
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
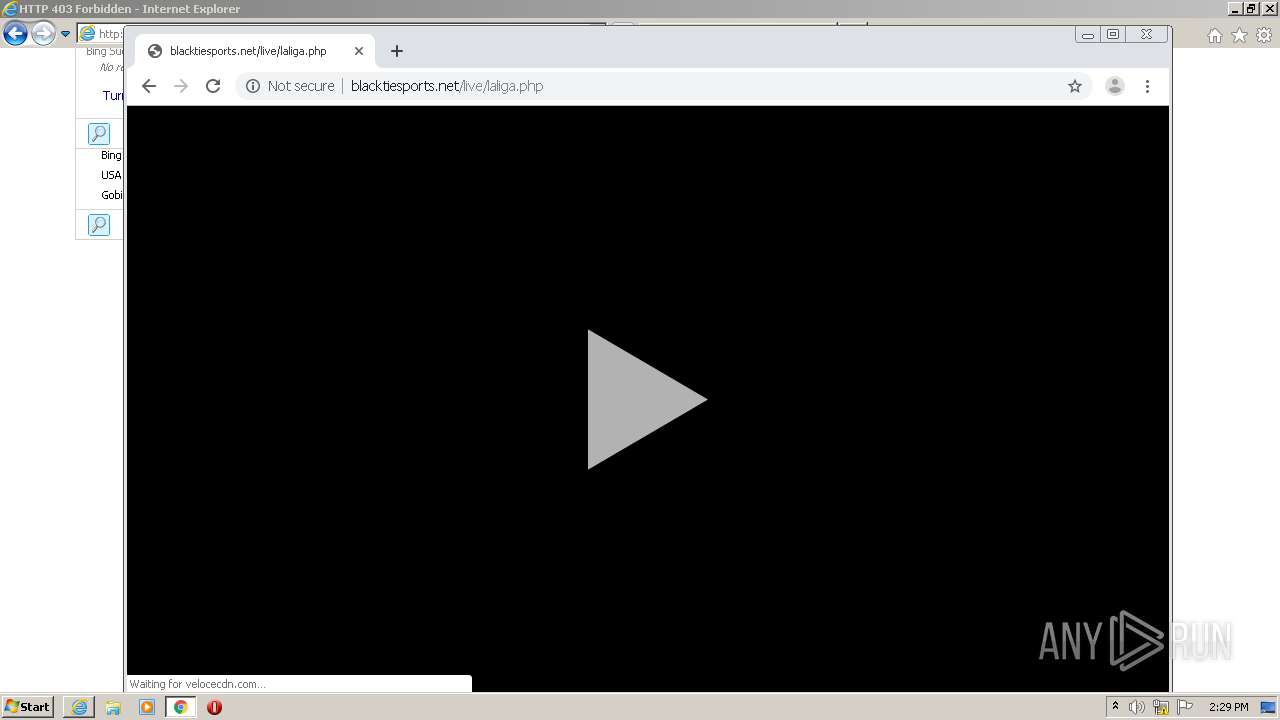
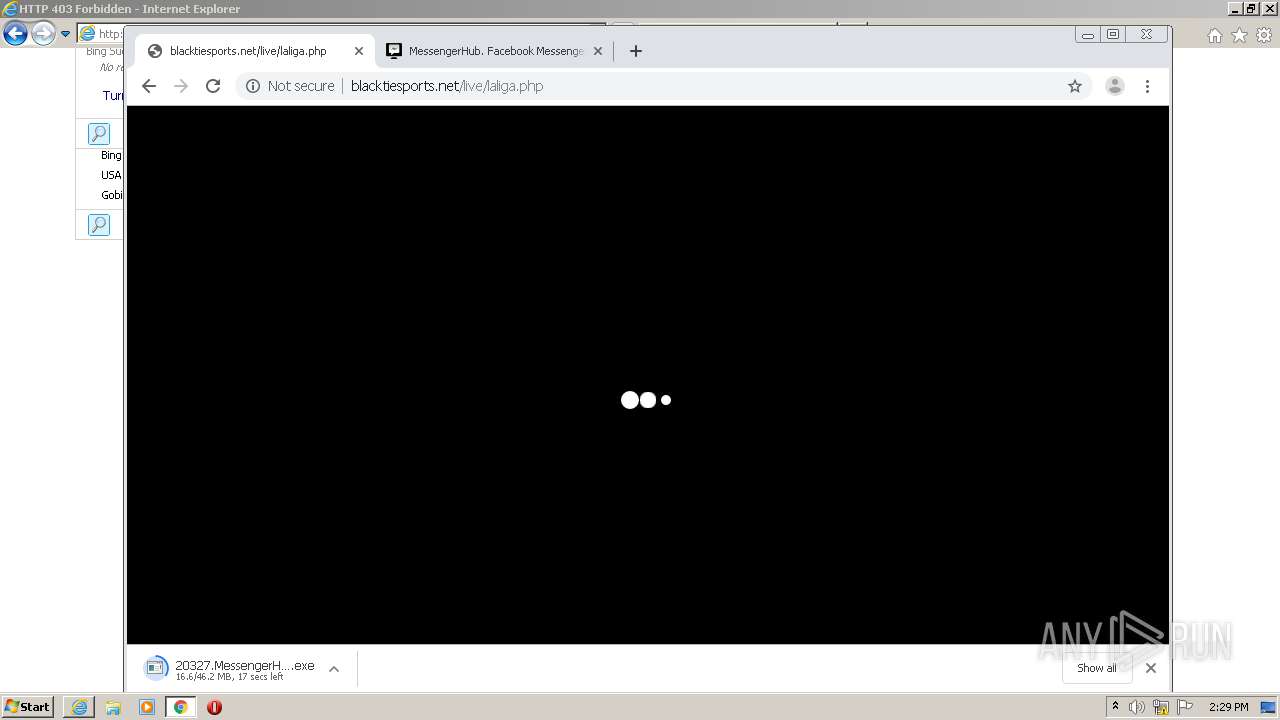
2316 | iexplore.exe | GET | — | 192.243.59.12:80 | http://dxqqcoi8q25t.com/d8/6f/3d/d86f3dbf3bcc364730c2ec22d9e3e3dc.js | US | — | — | malicious |
2752 | chrome.exe | GET | 403 | 192.243.59.13:80 | http://dxqqcoi8q25t.com/d8/6f/3d/d86f3dbf3bcc364730c2ec22d9e3e3dc.js | US | — | — | malicious |
2752 | chrome.exe | GET | 403 | 192.243.59.13:80 | http://dxqqcoi8q25t.com/d8/6f/3d/d86f3dbf3bcc364730c2ec22d9e3e3dc.js | US | — | — | malicious |
2752 | chrome.exe | GET | 403 | 192.243.59.13:80 | http://dxqqcoi8q25t.com/d8/6f/3d/d86f3dbf3bcc364730c2ec22d9e3e3dc.js | US | — | — | malicious |
2316 | iexplore.exe | GET | 403 | 192.243.59.12:80 | http://dxqqcoi8q25t.com/d8/6f/3d/d86f3dbf3bcc364730c2ec22d9e3e3dc.js | US | — | — | malicious |
2316 | iexplore.exe | GET | 403 | 192.243.59.12:80 | http://dxqqcoi8q25t.com/d8/6f/3d/d86f3dbf3bcc364730c2ec22d9e3e3dc.js | US | — | — | malicious |
2316 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fdxqqcoi8q25t.com%2Fd8%2F6f%2F3d%2Fd86f3dbf3bcc364730c2ec22d9e3e3dc.js&maxwidth=532&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 211 b | whitelisted |
2488 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2488 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2316 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fdxqqcoi8q25t.com%2Fd8%2F6f%2F3d%2Fd86f3dbf3bcc364730c2ec22d9e3e3dc.js&maxwidth=532&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 211 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2316 | iexplore.exe | 192.243.59.12:80 | dxqqcoi8q25t.com | DataWeb Global Group B.V. | US | malicious |
2488 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2488 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2488 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2316 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
2488 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2316 | iexplore.exe | 104.199.248.22:443 | brilio.net | Google Inc. | US | suspicious |
2316 | iexplore.exe | 104.199.214.191:80 | brilio.net | Google Inc. | US | unknown |
2752 | chrome.exe | 172.217.12.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 142.250.74.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dxqqcoi8q25t.com |
| malicious |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
brilio.net |
| whitelisted |
www.brilio.net |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2316 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2316 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2752 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2752 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2752 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2752 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |