| File name: | HijackThis.exe |
| Full analysis: | https://app.any.run/tasks/97534e2b-d84f-44b6-9d71-0f75a5d17185 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2025, 19:12:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 47811D50390A86A17102D7496E6EABB9 |
| SHA1: | 2623749CDB27887F6746ACDEE7E8065475F8B541 |
| SHA256: | 9DA5A899B9D55E1D43718EC0AD6368F9E9EF0242A4E88CD5DDB2CC6D7BFA5FB3 |
| SSDEEP: | 6144:VlTObRvp4MRMEZ40E3pItODKMsFN3pClZQIuScGGSDMpI5:jqk44k8DKfFlu3F5 |
MALICIOUS
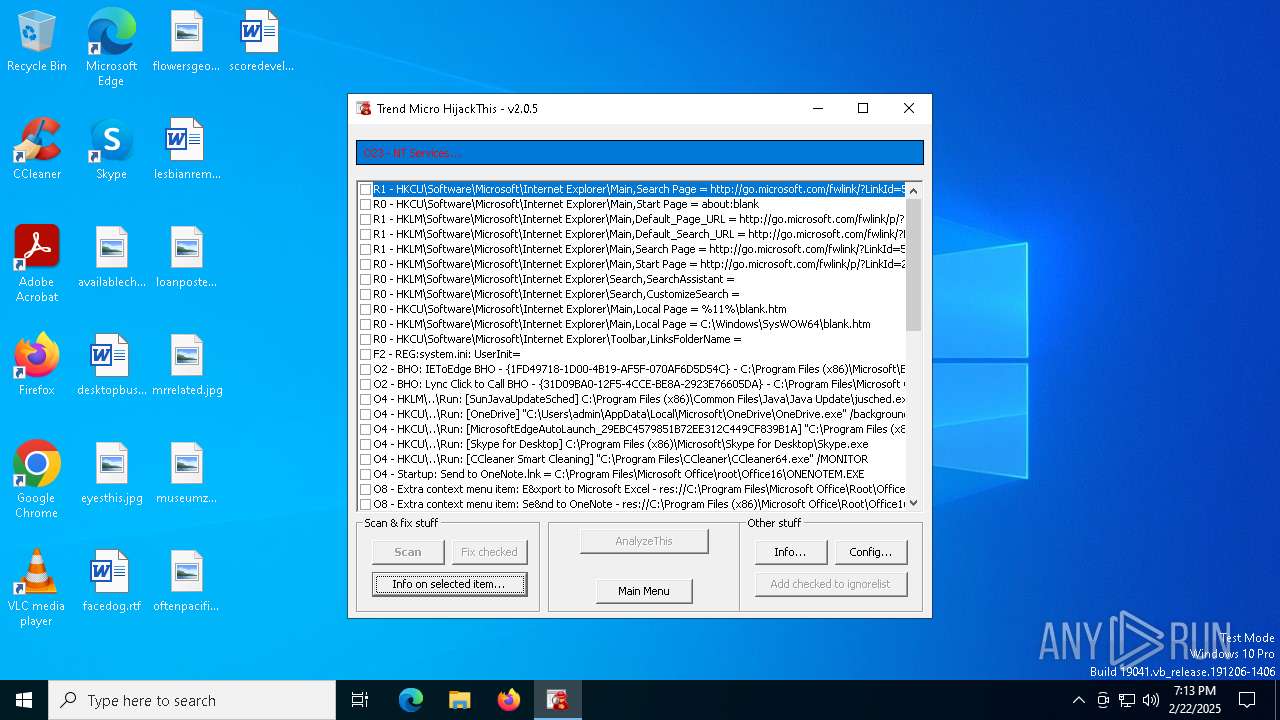
No malicious indicators.SUSPICIOUS
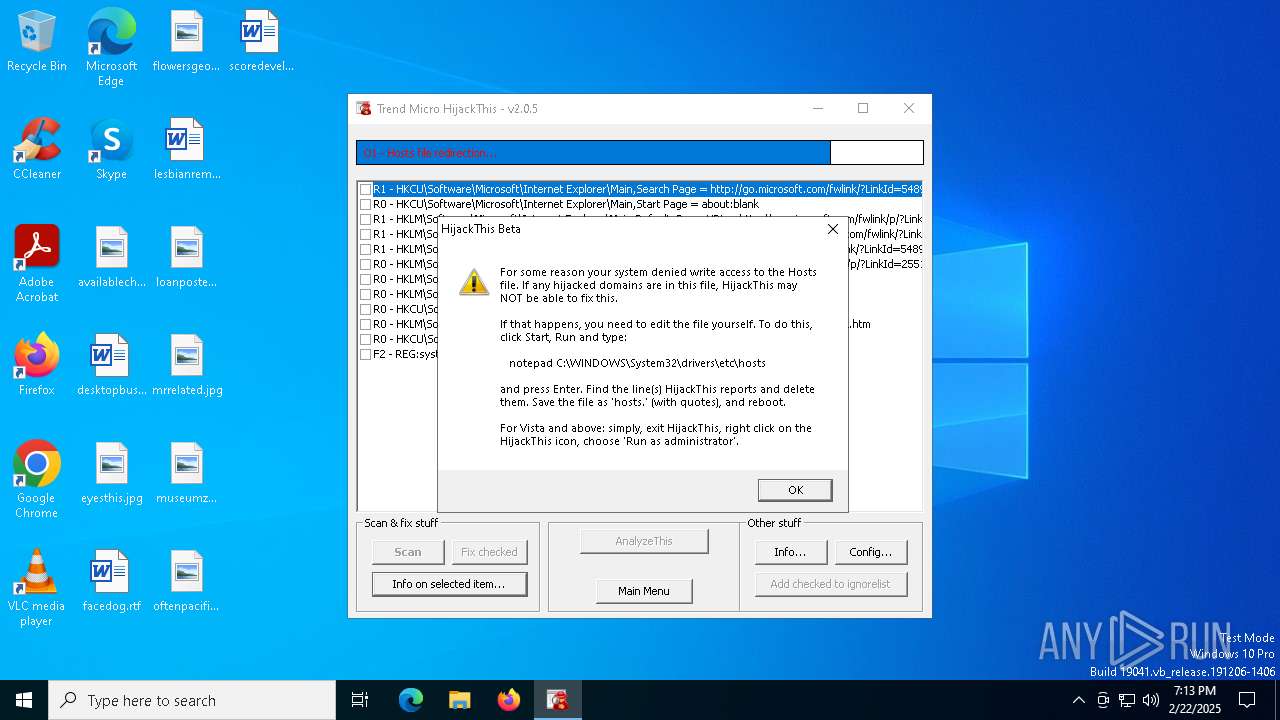
Reads security settings of Internet Explorer
- HijackThis.exe (PID: 5404)
The process checks if it is being run in the virtual environment
- HijackThis.exe (PID: 5404)
INFO
Checks supported languages
- HijackThis.exe (PID: 5404)
The sample compiled with english language support
- HijackThis.exe (PID: 5404)
Create files in a temporary directory
- HijackThis.exe (PID: 5404)
Reads the computer name
- HijackThis.exe (PID: 5404)
UPX packer has been detected
- HijackThis.exe (PID: 5404)
Reads the software policy settings
- HijackThis.exe (PID: 5404)
Checks proxy server information
- HijackThis.exe (PID: 5404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:05:09 17:08:08+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 278528 |
| InitializedDataSize: | 110592 |
| UninitializedDataSize: | 1036288 |
| EntryPoint: | 0x141920 |
| OSVersion: | 4 |
| ImageVersion: | 2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.5 |
| ProductVersionNumber: | 2.0.0.5 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Trend Micro Inc. |
| FileDescription: | HijackThis |
| LegalCopyright: | (c) 2007 Trend Micro Inc |
| LegalTrademarks: | © |
| ProductName: | HijackThis |
| FileVersion: | 2.00.0005 |
| ProductVersion: | 2.00.0005 |
| InternalName: | HijackThis |
| OriginalFileName: | HijackThis.exe |
Total processes
128
Monitored processes
1
Malicious processes
1
Suspicious processes
0
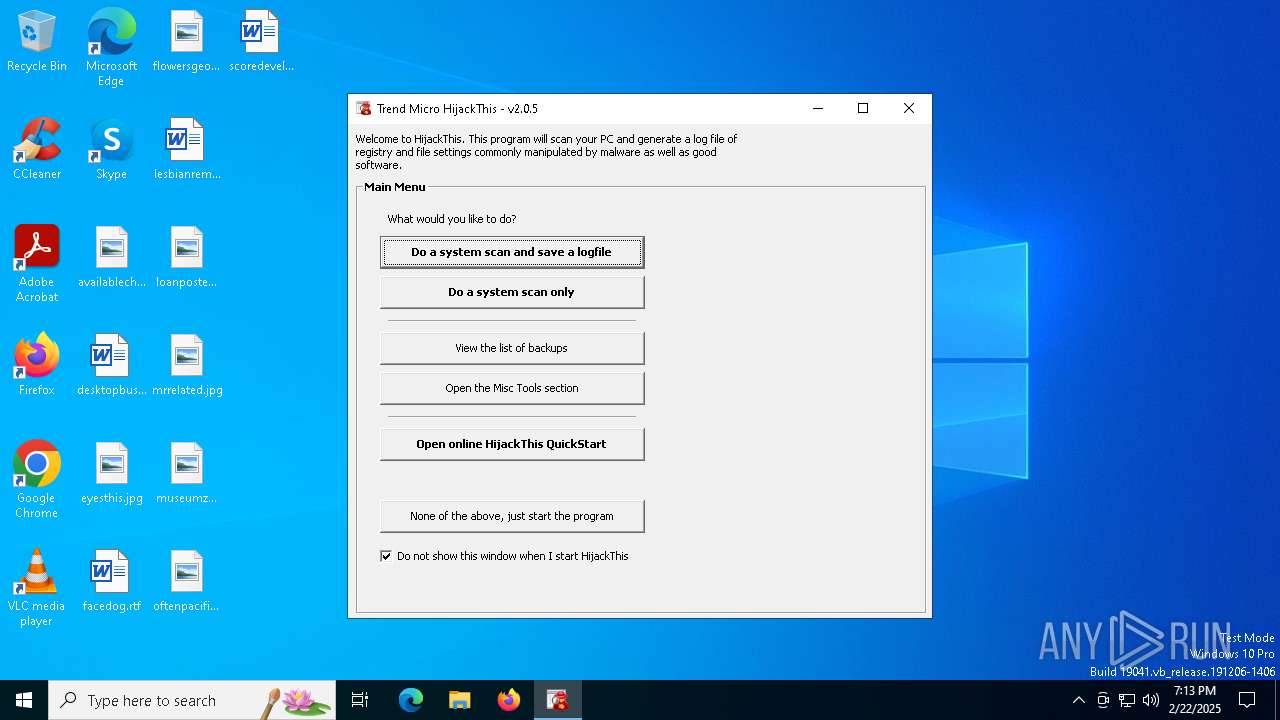
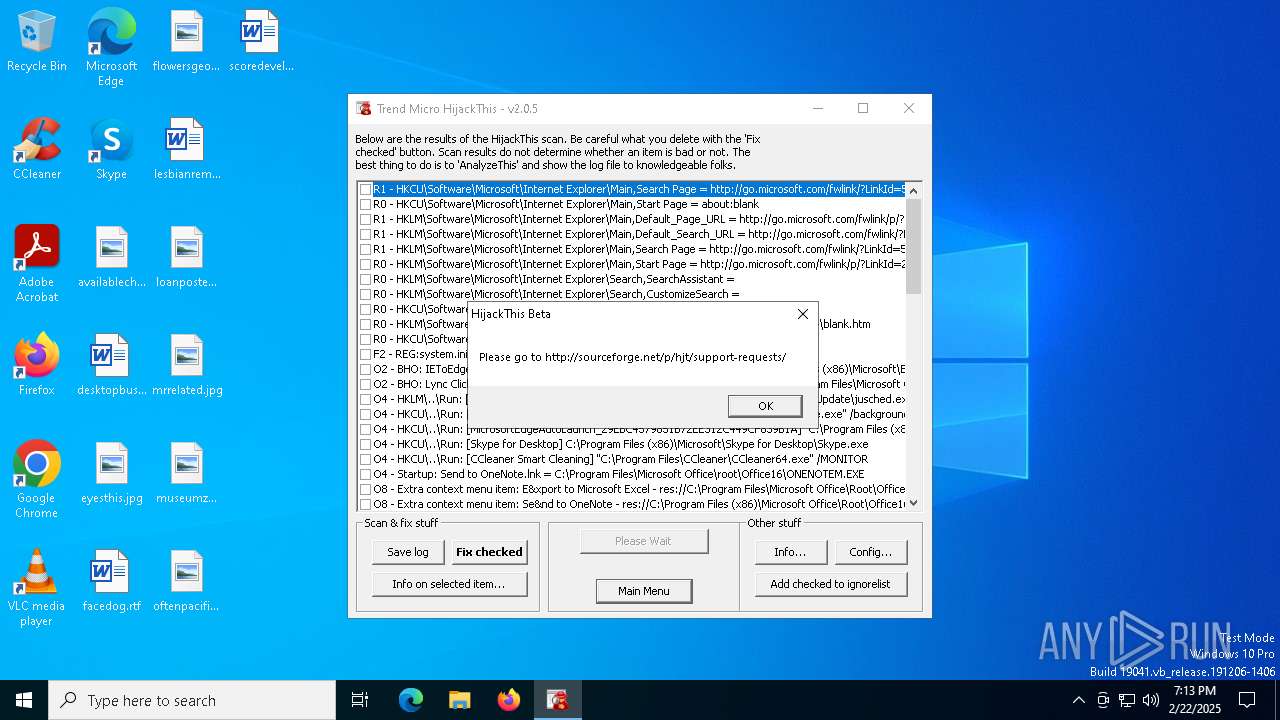
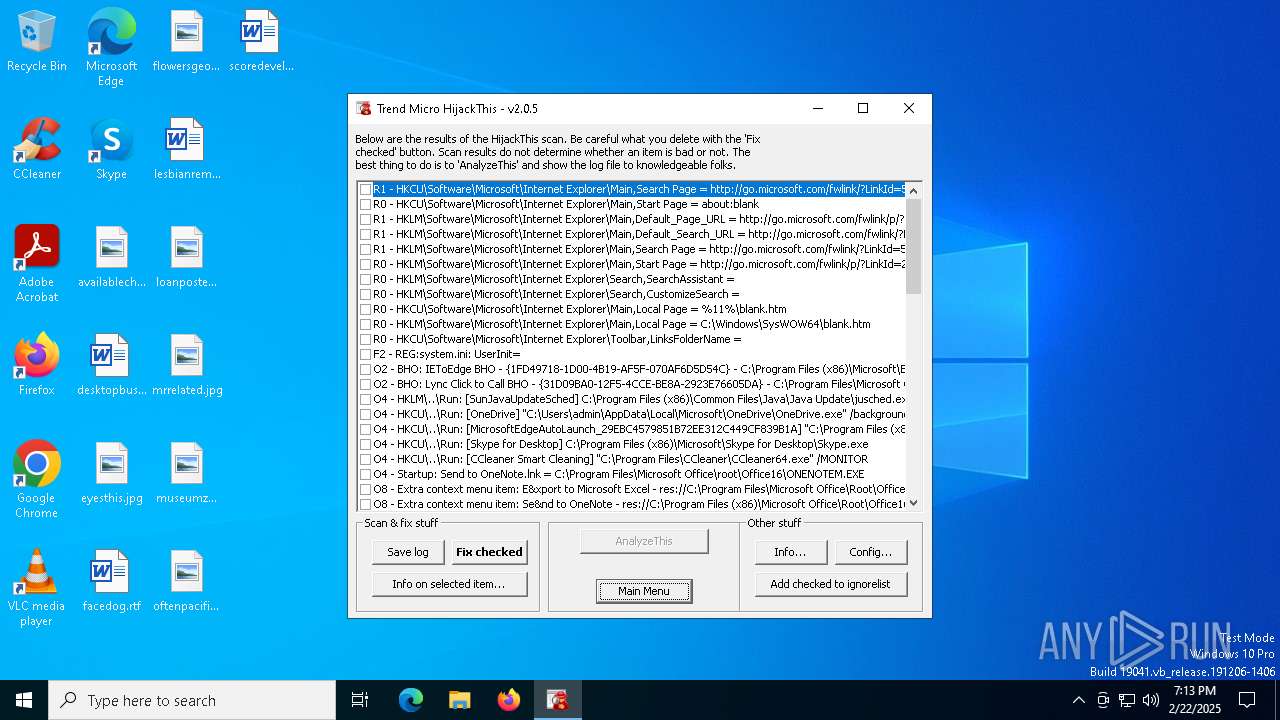
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5404 | "C:\Users\admin\AppData\Local\Temp\HijackThis.exe" | C:\Users\admin\AppData\Local\Temp\HijackThis.exe | explorer.exe | ||||||||||||
User: admin Company: Trend Micro Inc. Integrity Level: MEDIUM Description: HijackThis Exit code: 0 Version: 2.00.0005 Modules
| |||||||||||||||
Total events
5 554
Read events
5 549
Write events
4
Delete events
1
Modification events
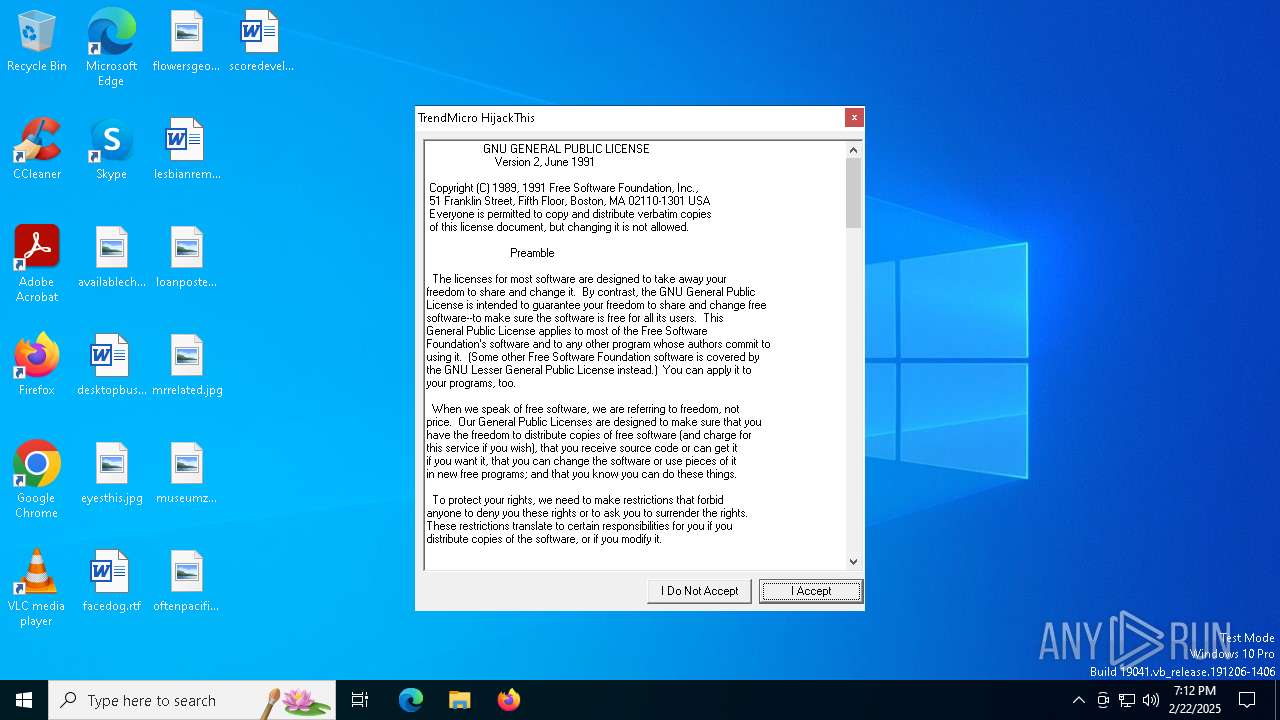
| (PID) Process: | (5404) HijackThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TrendMicro\HijackThis |
| Operation: | write | Name: | LanguageFile |
Value: (Default) | |||
| (PID) Process: | (5404) HijackThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TrendMicro\HijackThis |
| Operation: | write | Name: | ShowIntroFrame |
Value: 1 | |||
| (PID) Process: | (5404) HijackThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TrendMicro\HijackThis |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5404) HijackThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TrendMicro\HijackThis |
| Operation: | write | Name: | WinHeight |
Value: 8000 | |||
| (PID) Process: | (5404) HijackThis.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TrendMicro\HijackThis |
| Operation: | write | Name: | WinWidth |
Value: 9000 | |||
Executable files
0
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5404 | HijackThis.exe | C:\Users\admin\AppData\Local\Temp\~dummy.tmp | text | |
MD5:DADAFE066983AB646E8550013FB7DA13 | SHA256:C0A317F60910EED08BBFC7B3AC6E6DE1B2029BF4922D0B0D7D3759313A24B16C | |||
| 5404 | HijackThis.exe | C:\Users\admin\AppData\Local\Temp\~DF87E7374FFA6523FE.TMP | binary | |
MD5:94421A21F1F04094B4920B34F8D11FC5 | SHA256:BBE1F688A4AB9D760B3375D50163D67B98E9F6FC7C5164338E4460902EB4BA87 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
34
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5404 | HijackThis.exe | GET | 301 | 104.18.12.149:80 | http://sourceforge.net/p/hjt/support-requests/2.0.5 | unknown | — | — | whitelisted |
3560 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3560 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5568 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.190:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.190:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 184.86.251.17:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5160 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |