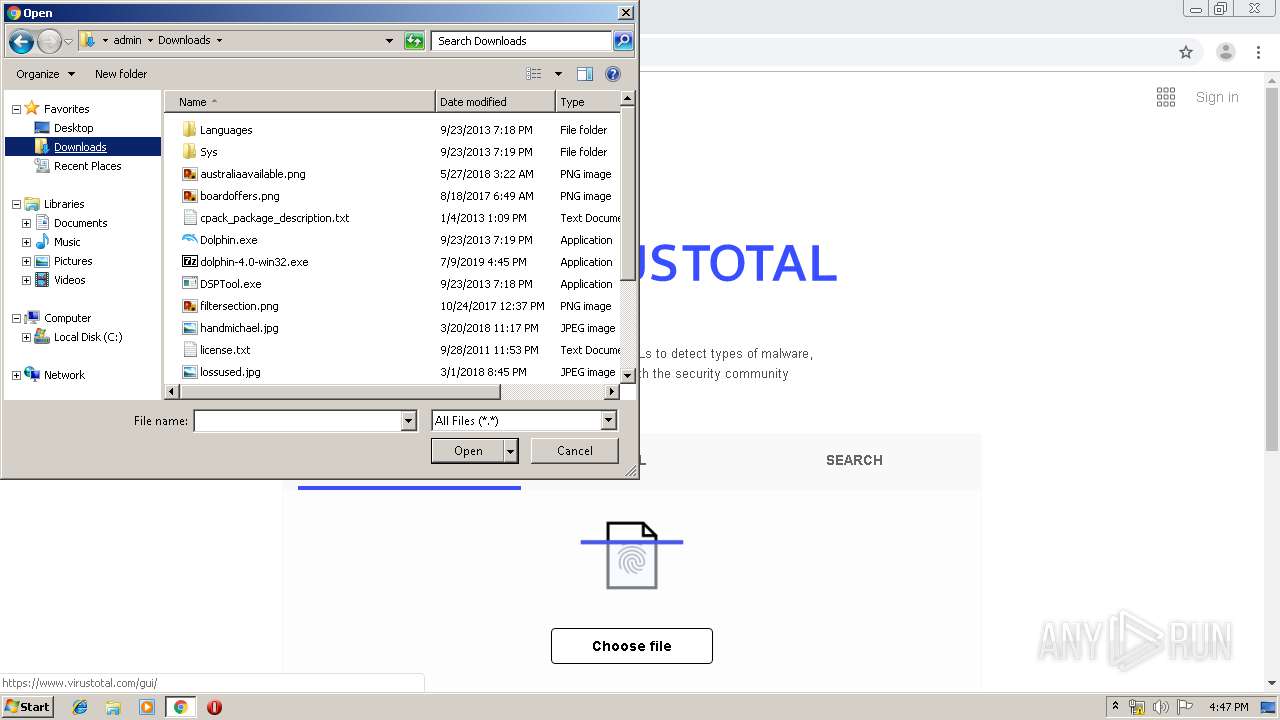
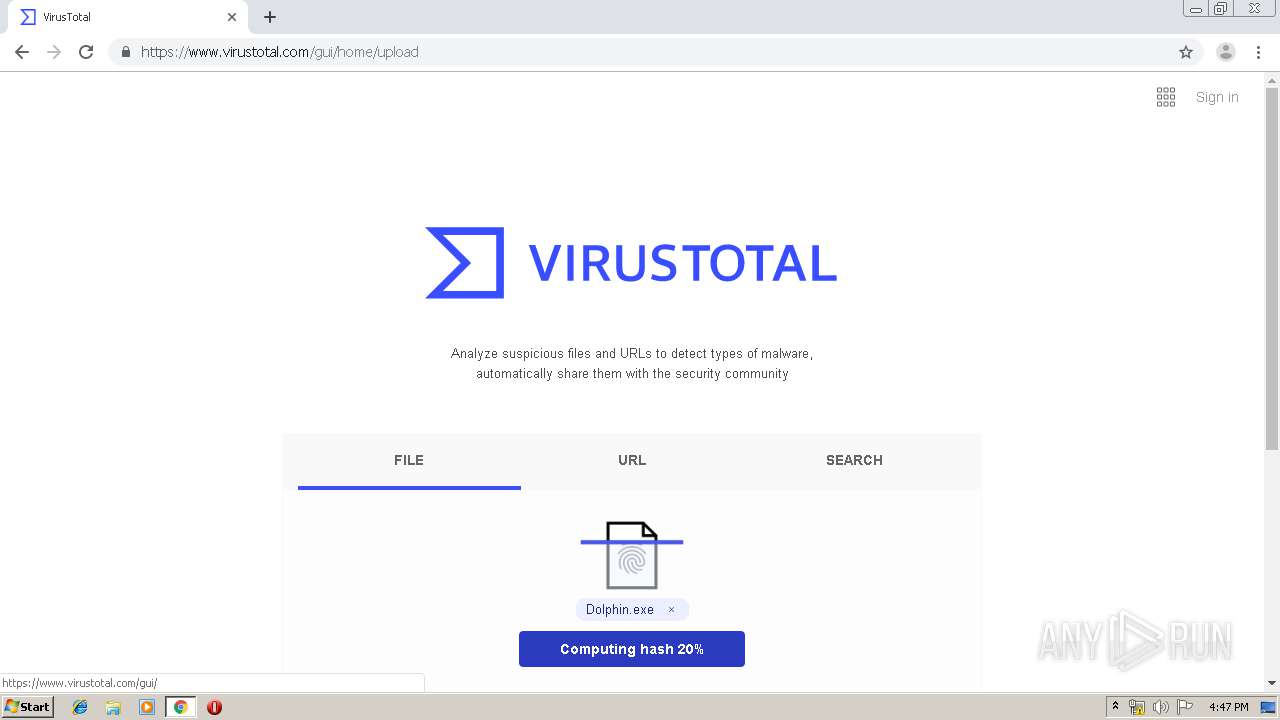
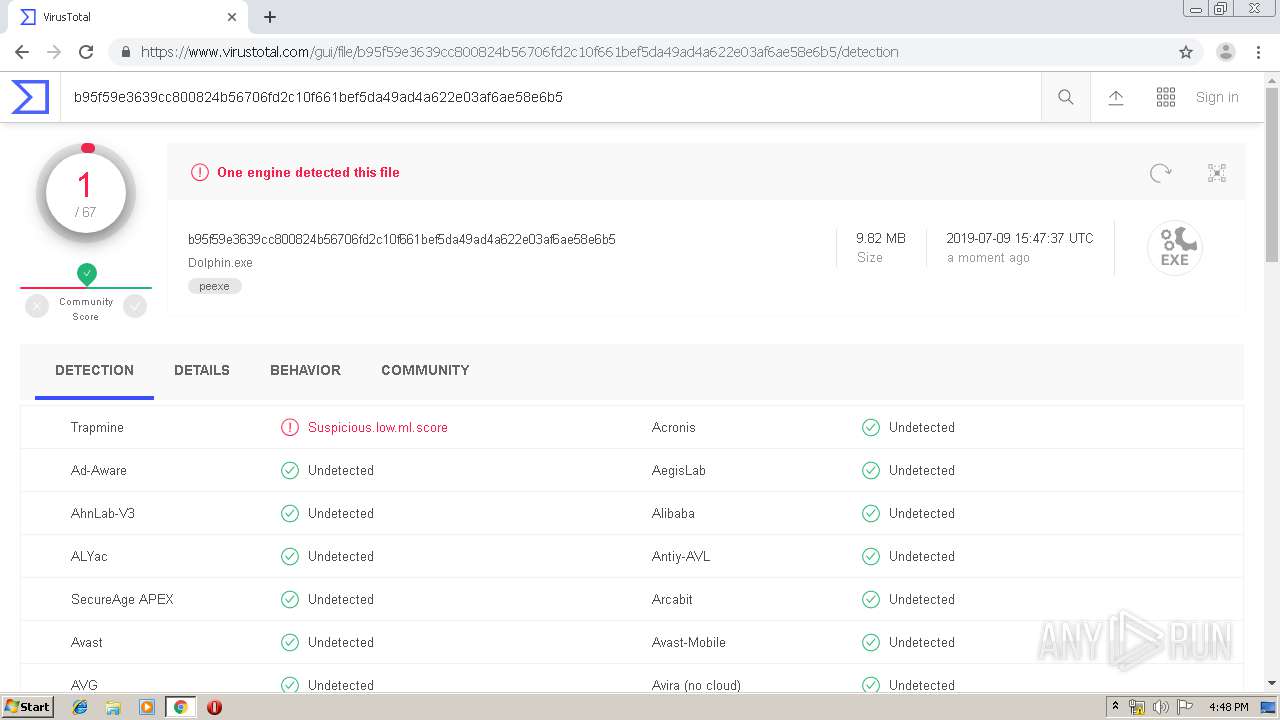
| File name: | dolphin-4.0-win32.exe |
| Full analysis: | https://app.any.run/tasks/44d5eb23-a82d-4507-8d1d-63a2e39392b5 |
| Verdict: | Malicious activity |
| Analysis date: | July 09, 2019, 15:45:16 |
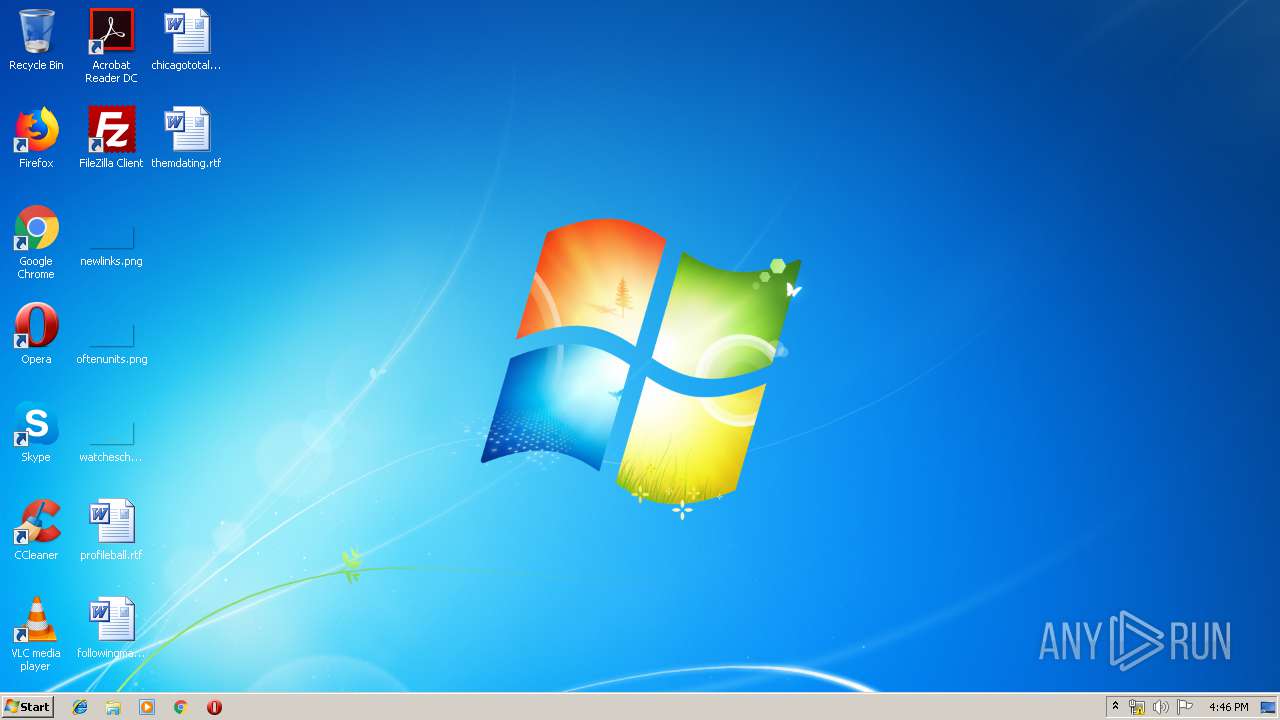
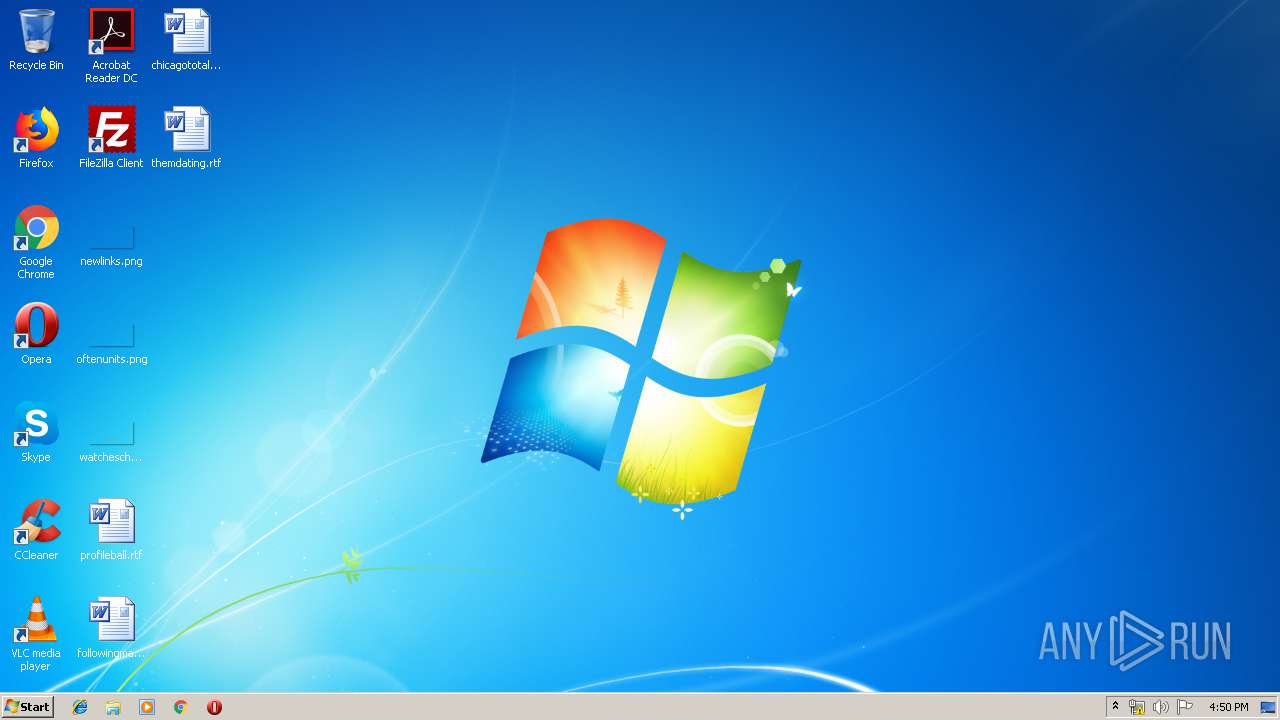
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E6194BFC579050D8DA1AE91E1BE9BC58 |
| SHA1: | 2893E763CB3CB7E061DBA73C5EDFD1E623FBD02B |
| SHA256: | 9D9A77B4A1FF95C7B1E0BD5AD618C07BF67C9FED7C5B43C4AF828D39FA4C29C9 |
| SSDEEP: | 98304:6G50ntD3uyamC+qa7pWOtm4ZwLsf1uh8OA28D3:6GupuFmC+qa1Tt4gduhrA28D3 |
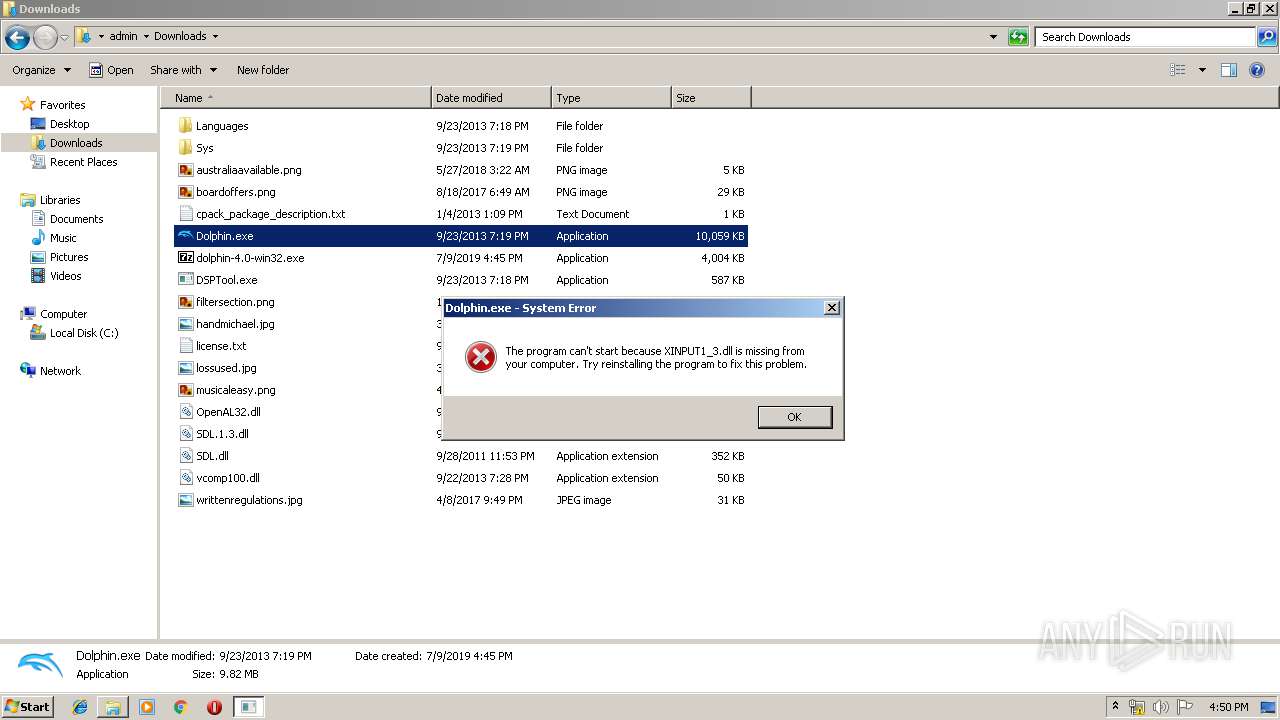
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 856)
- Dolphin.exe (PID: 792)
- Dolphin.exe (PID: 3804)
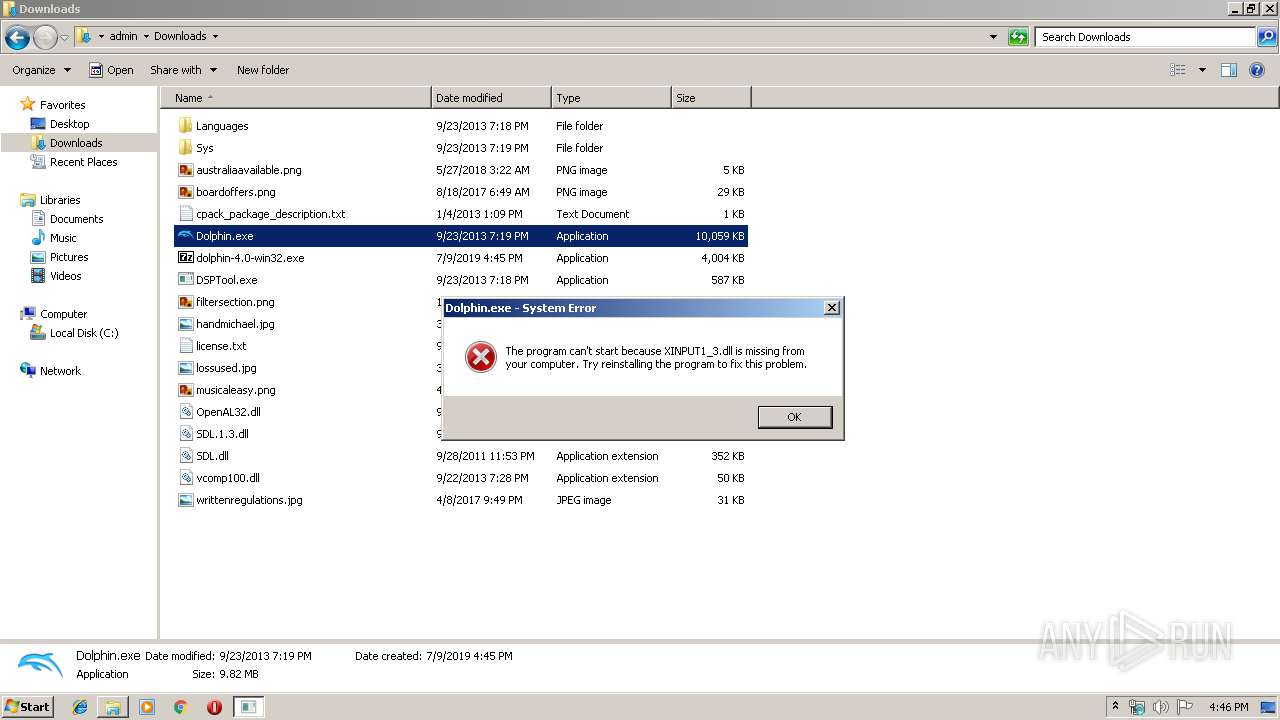
Application was dropped or rewritten from another process
- Dolphin.exe (PID: 792)
- Dolphin.exe (PID: 3804)
SUSPICIOUS
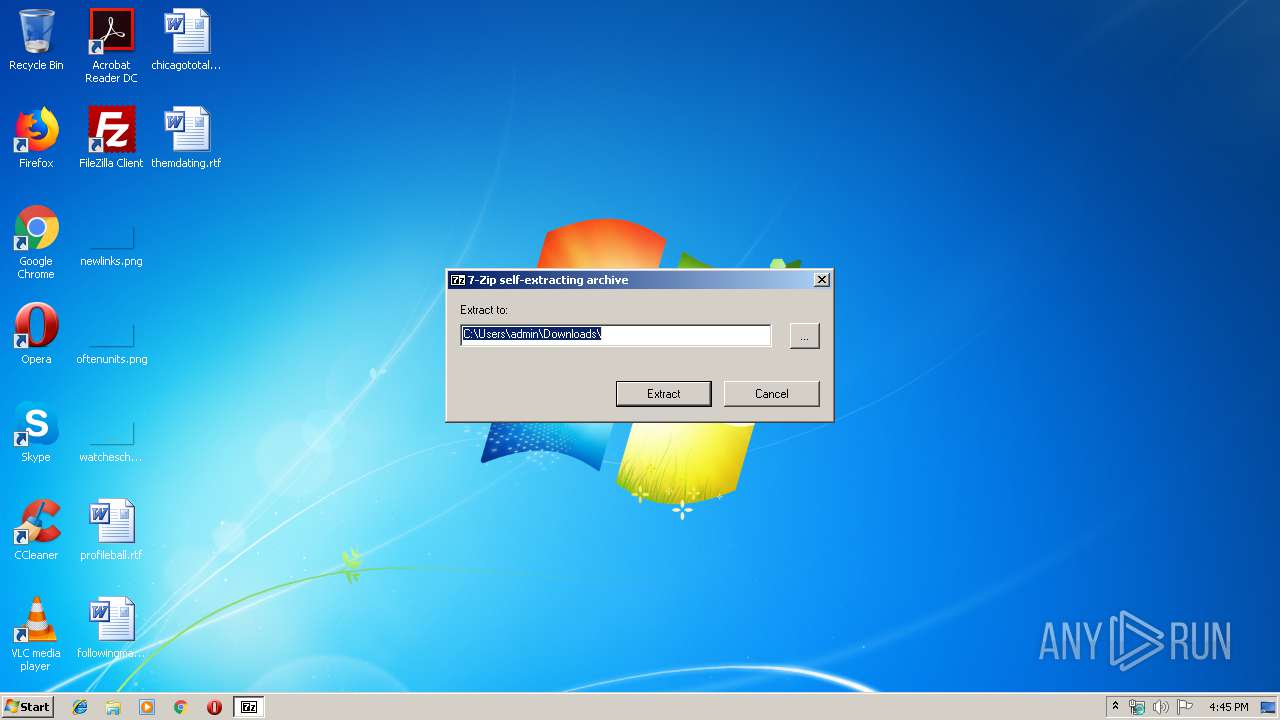
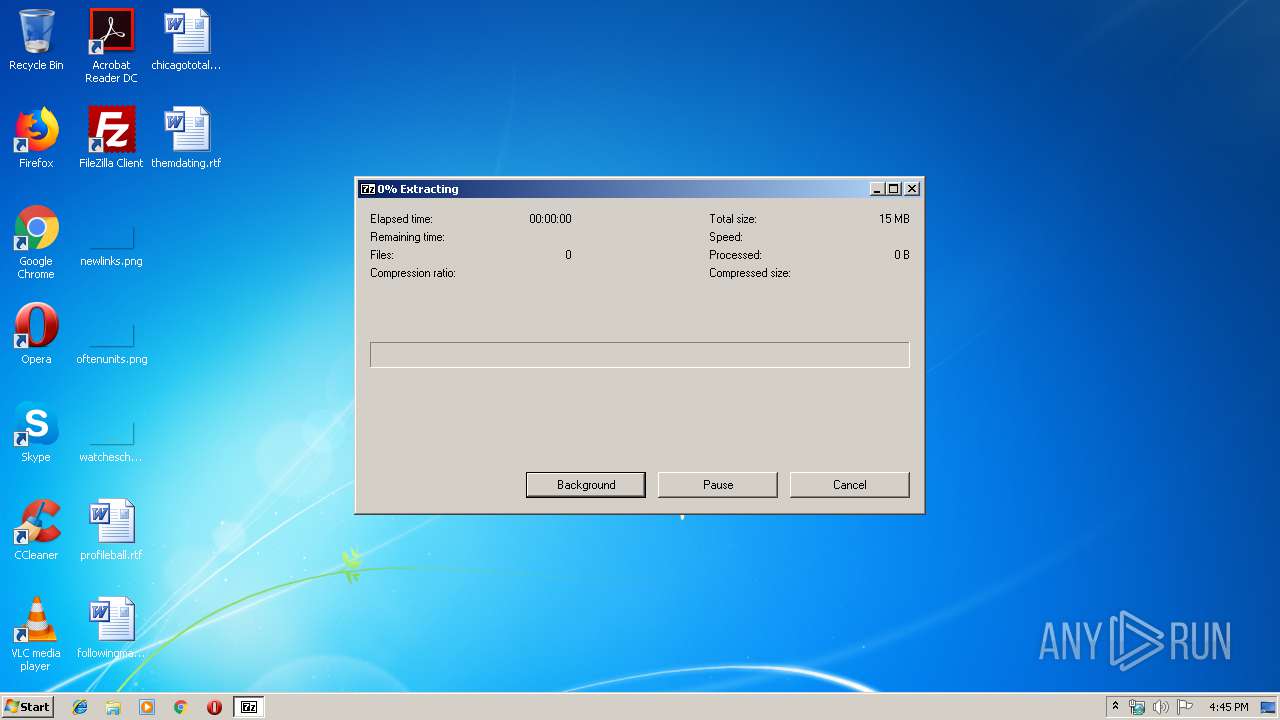
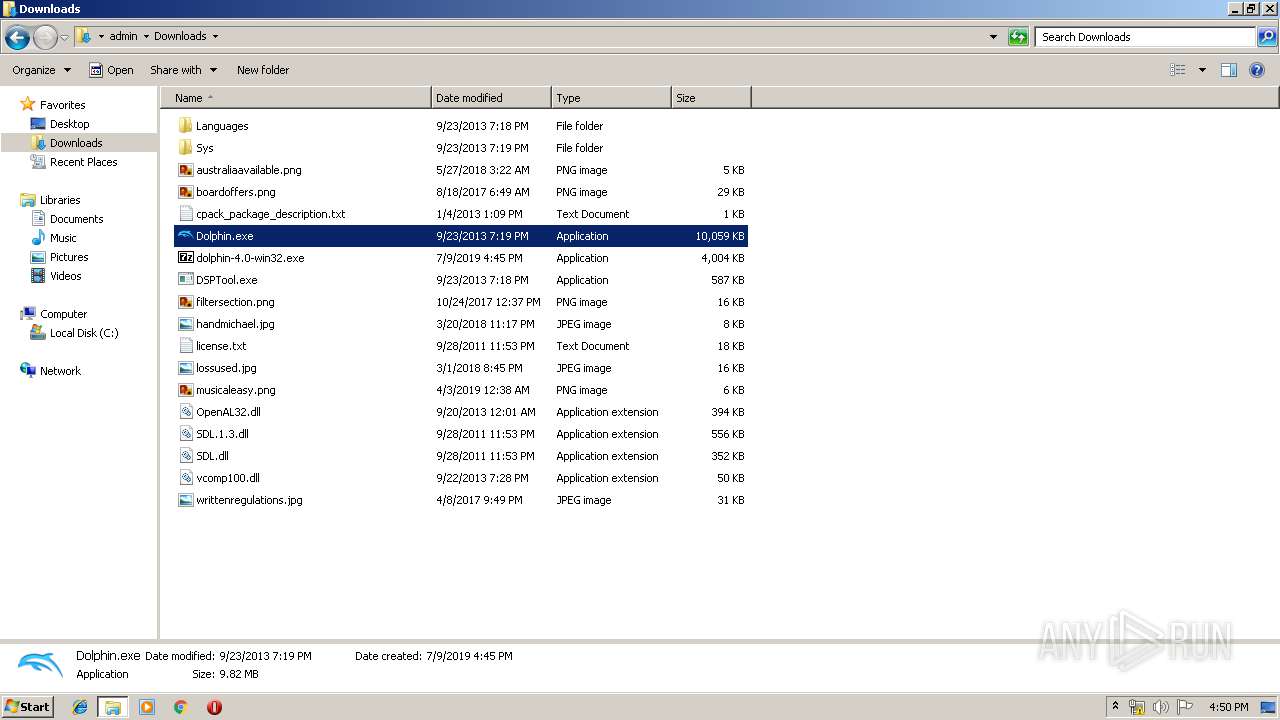
Executable content was dropped or overwritten
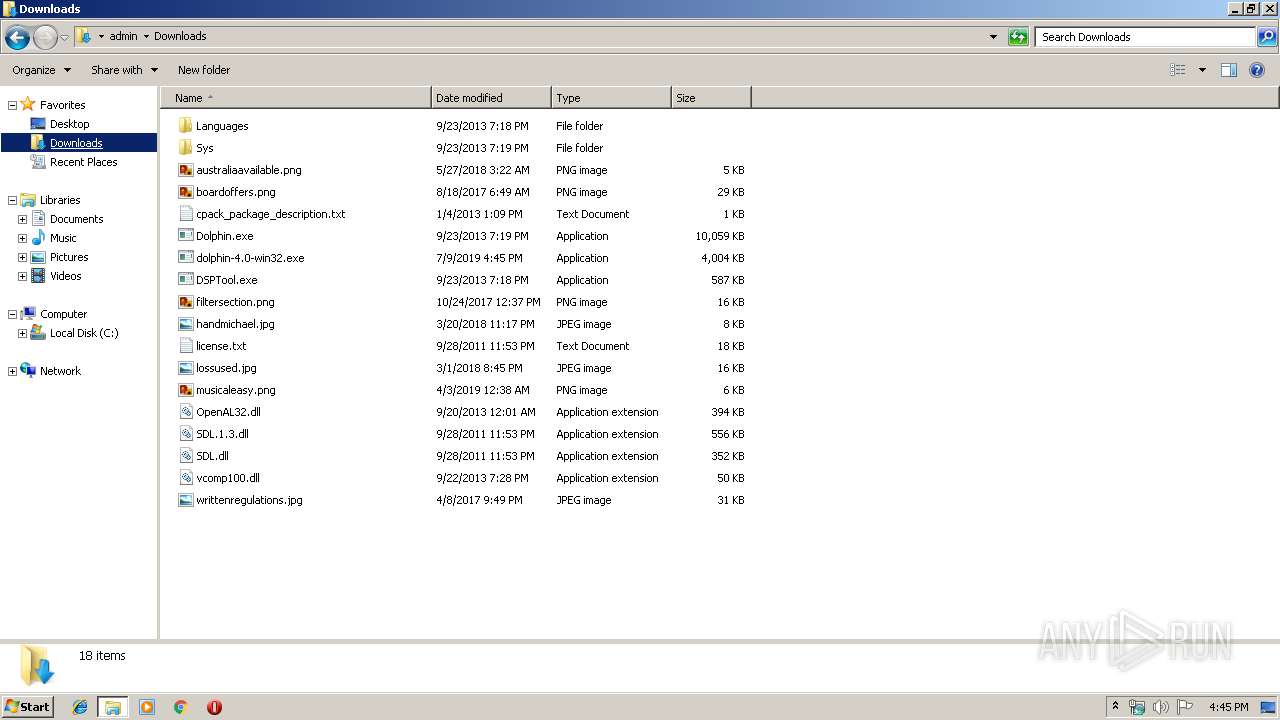
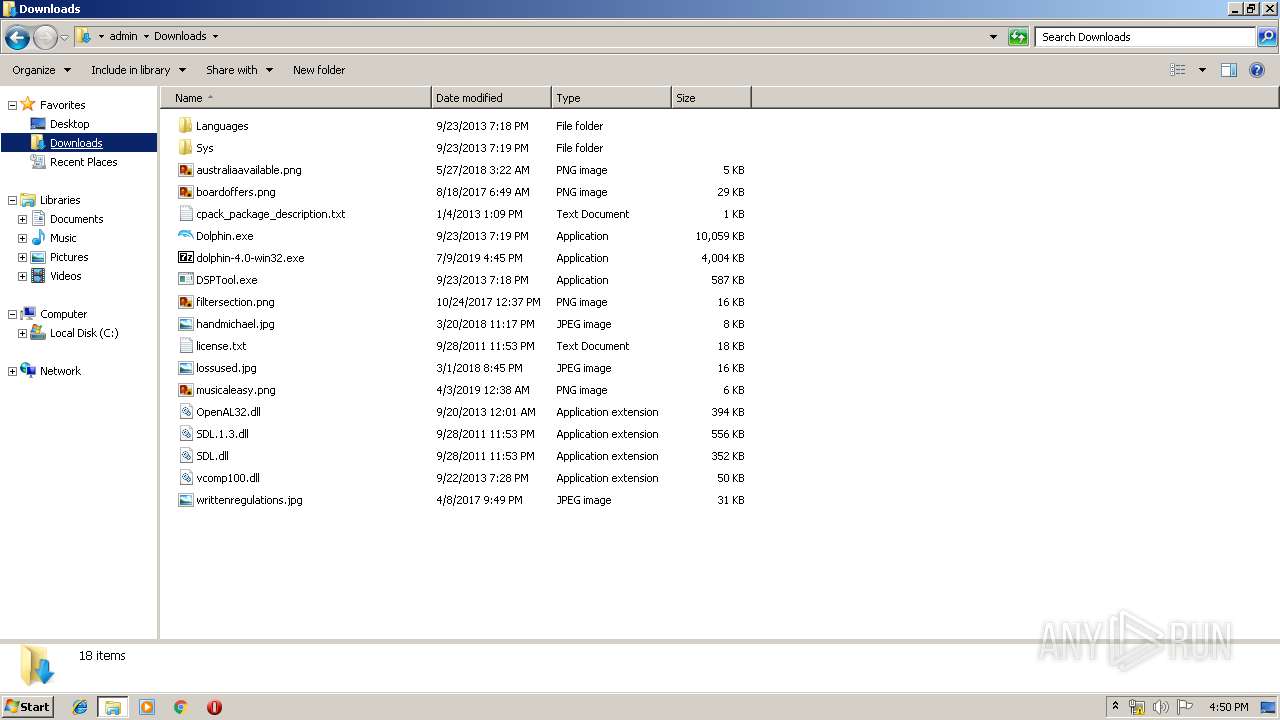
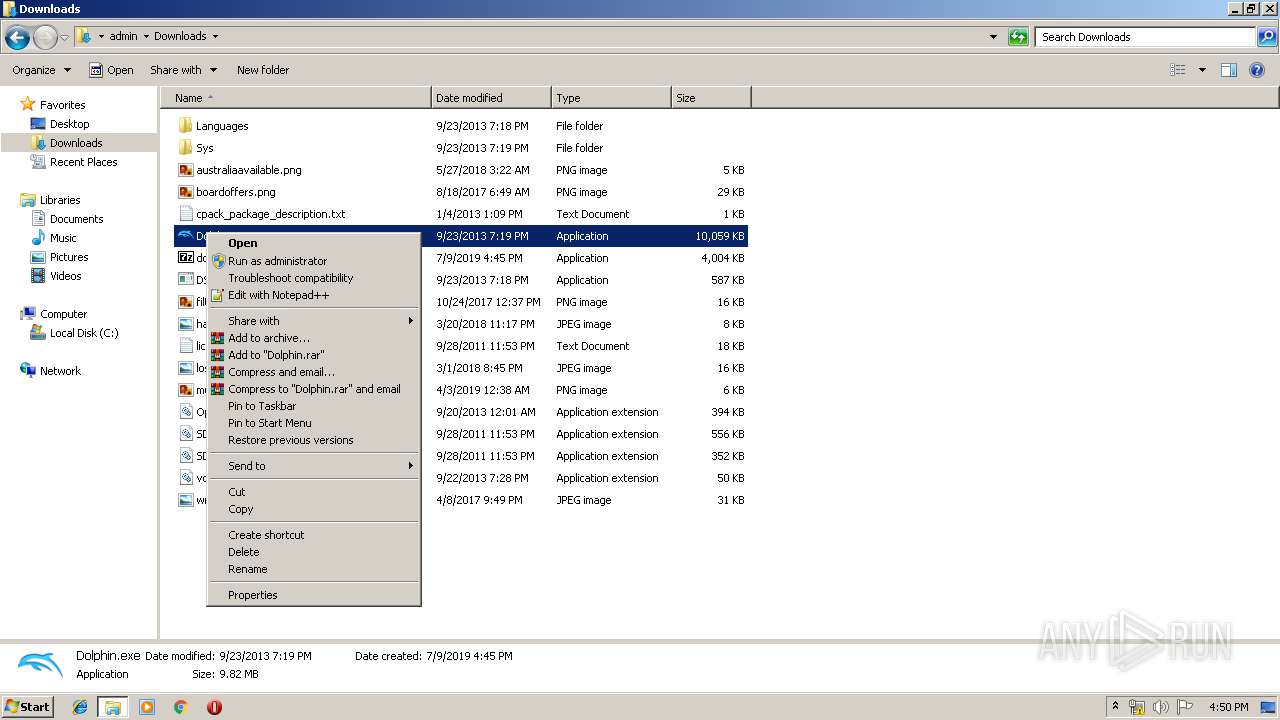
- dolphin-4.0-win32.exe (PID: 3464)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3396)
Application launched itself
- taskmgr.exe (PID: 3572)
INFO
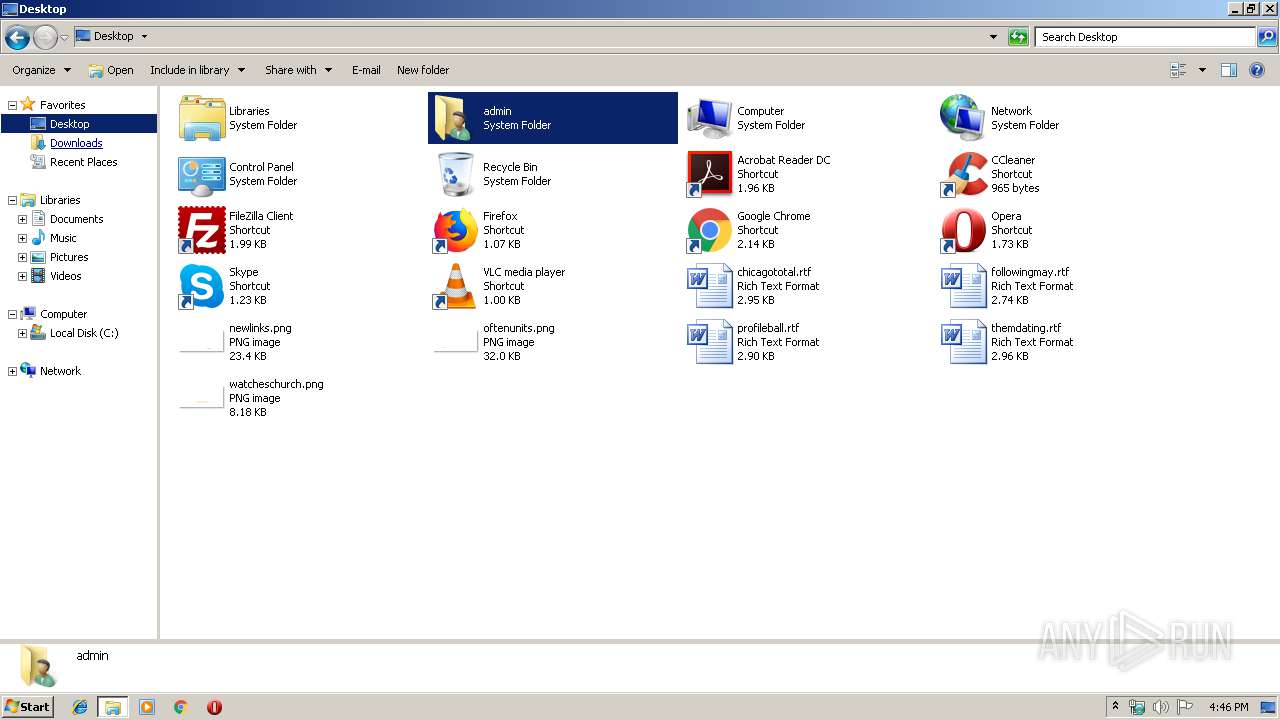
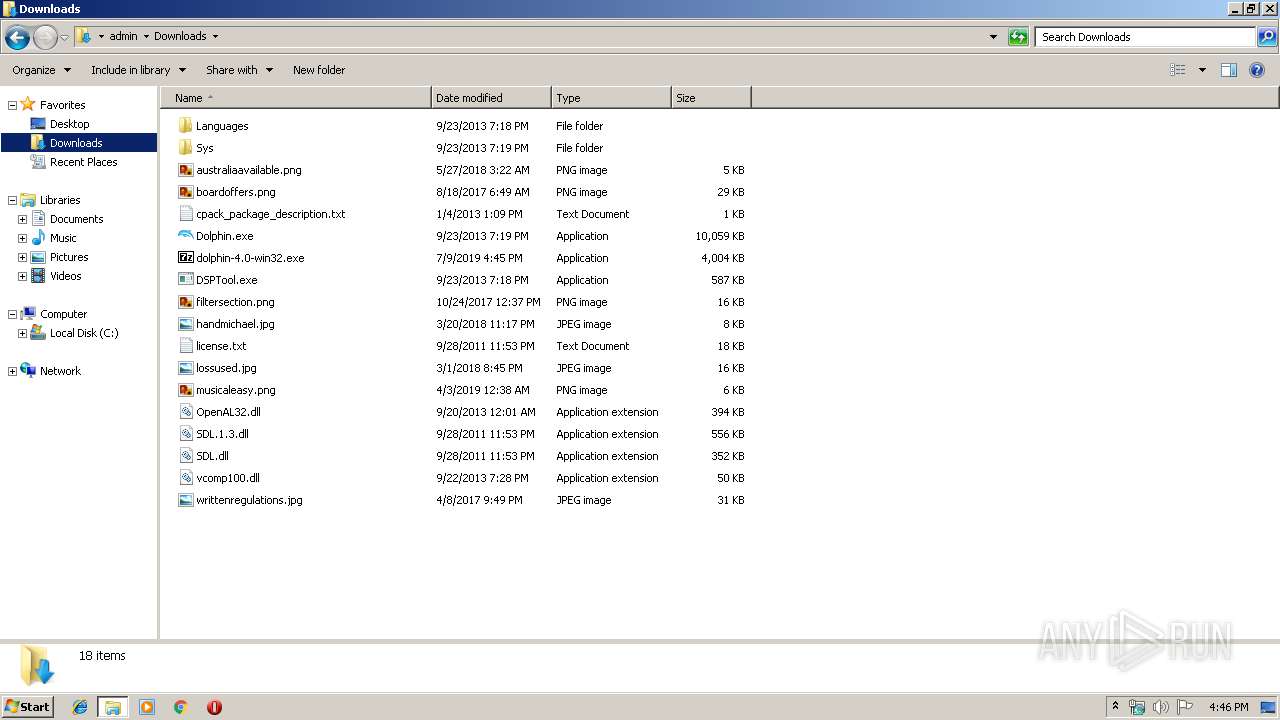
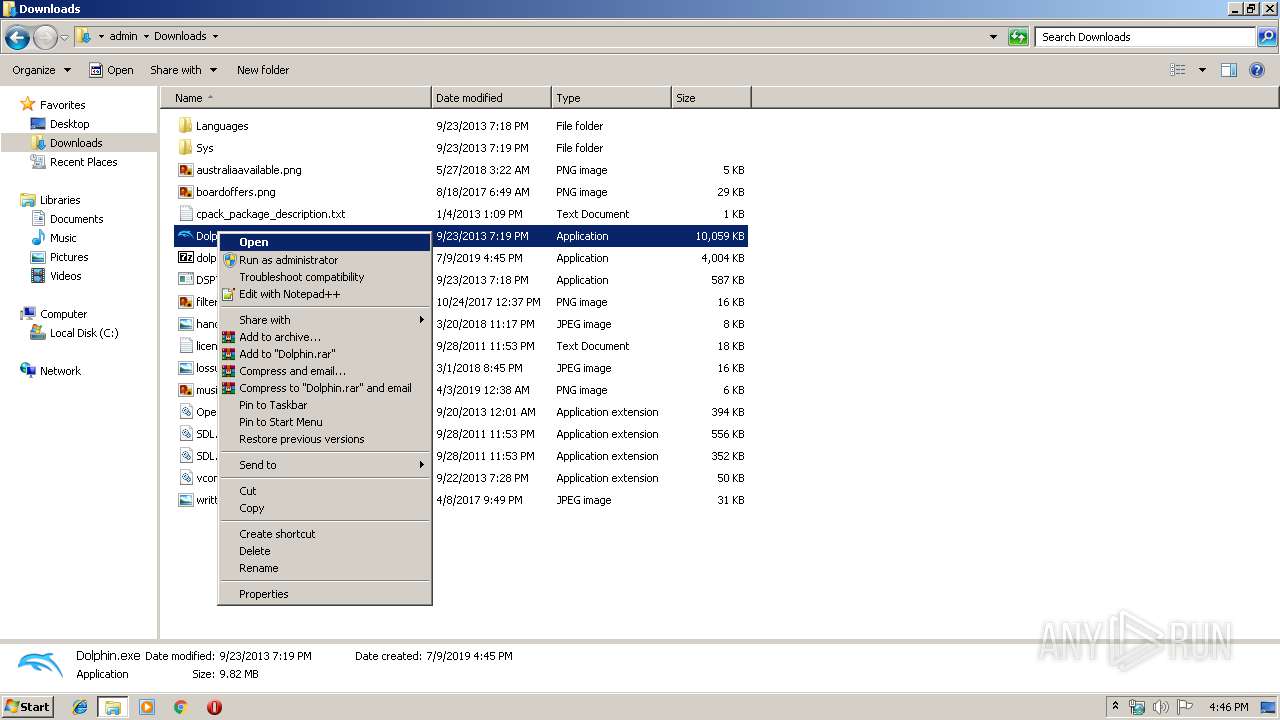
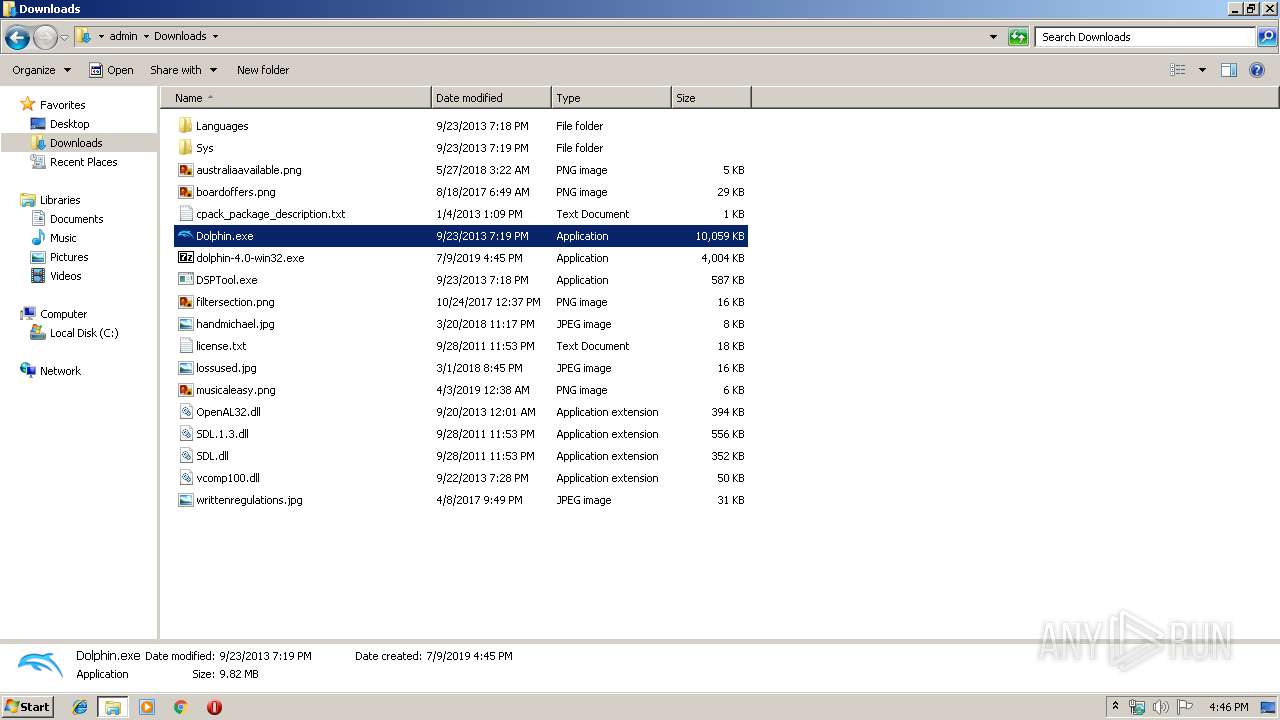
Manual execution by user
- Dolphin.exe (PID: 792)
- chrome.exe (PID: 3396)
- taskmgr.exe (PID: 3572)
- explorer.exe (PID: 3236)
- explorer.exe (PID: 1008)
- Dolphin.exe (PID: 3804)
Application launched itself
- chrome.exe (PID: 3396)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3396)
- chrome.exe (PID: 2716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:18 17:27:33+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 127488 |
| InitializedDataSize: | 51200 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d262 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.20.0.0 |
| ProductVersionNumber: | 9.20.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z SFX |
| FileVersion: | 9.2 |
| InternalName: | 7z.sfx |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| OriginalFileName: | 7z.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 9.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2010 16:27:33 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z SFX |
| FileVersion: | 9.20 |
| InternalName: | 7z.sfx |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| OriginalFilename: | 7z.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 9.20 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Nov-2010 16:27:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F01A | 0x0001F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59059 |
.rdata | 0x00021000 | 0x00005A5C | 0x00005C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.16805 |
.data | 0x00027000 | 0x00004D98 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.10058 |
.sxdata | 0x0002C000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x0002D000 | 0x00001BC0 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.29296 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41402 | 688 | UNKNOWN | English - United States | RT_VERSION |
2 | 1.68942 | 296 | UNKNOWN | English - United States | RT_ICON |
7 | 3.16186 | 392 | UNKNOWN | English - United States | RT_STRING |
13 | 3.27682 | 756 | UNKNOWN | English - United States | RT_STRING |
14 | 2.58196 | 114 | UNKNOWN | English - United States | RT_STRING |
32 | 1.10136 | 46 | UNKNOWN | English - United States | RT_STRING |
38 | 2.11169 | 72 | UNKNOWN | English - United States | RT_STRING |
44 | 2.76378 | 148 | UNKNOWN | English - United States | RT_STRING |
45 | 1.07875 | 44 | UNKNOWN | English - United States | RT_STRING |
66 | 3.07708 | 244 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
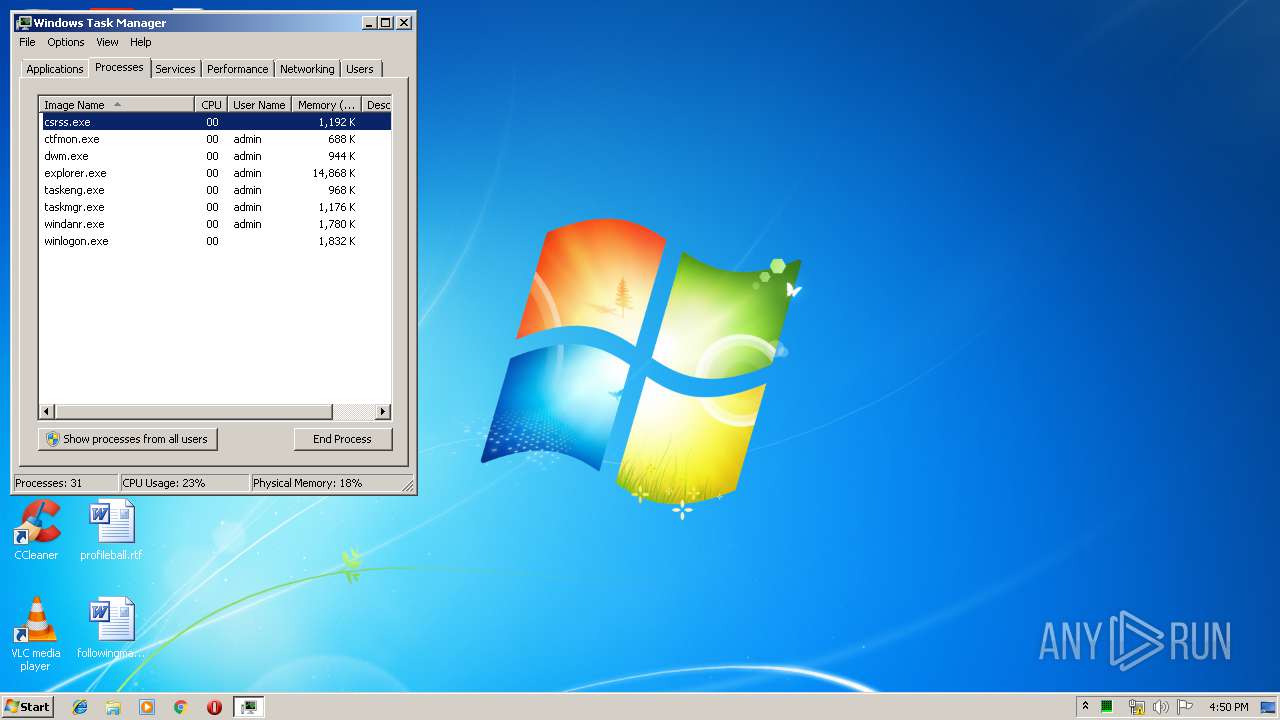
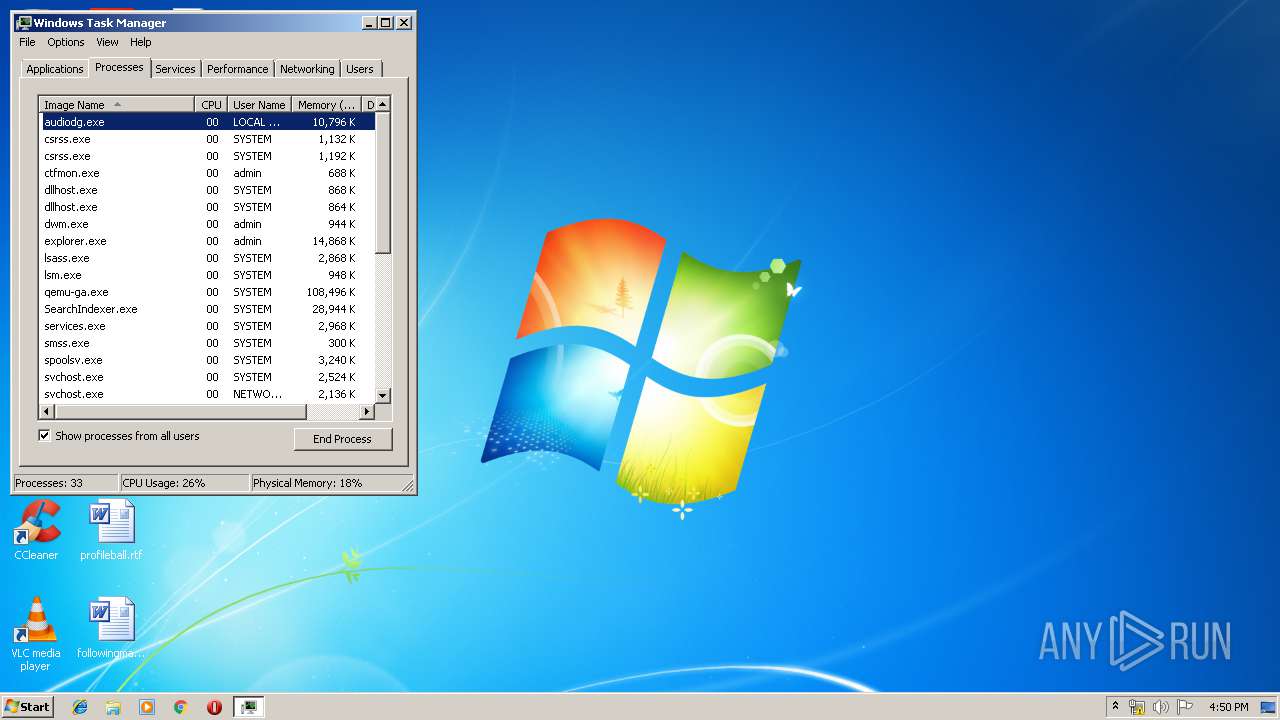
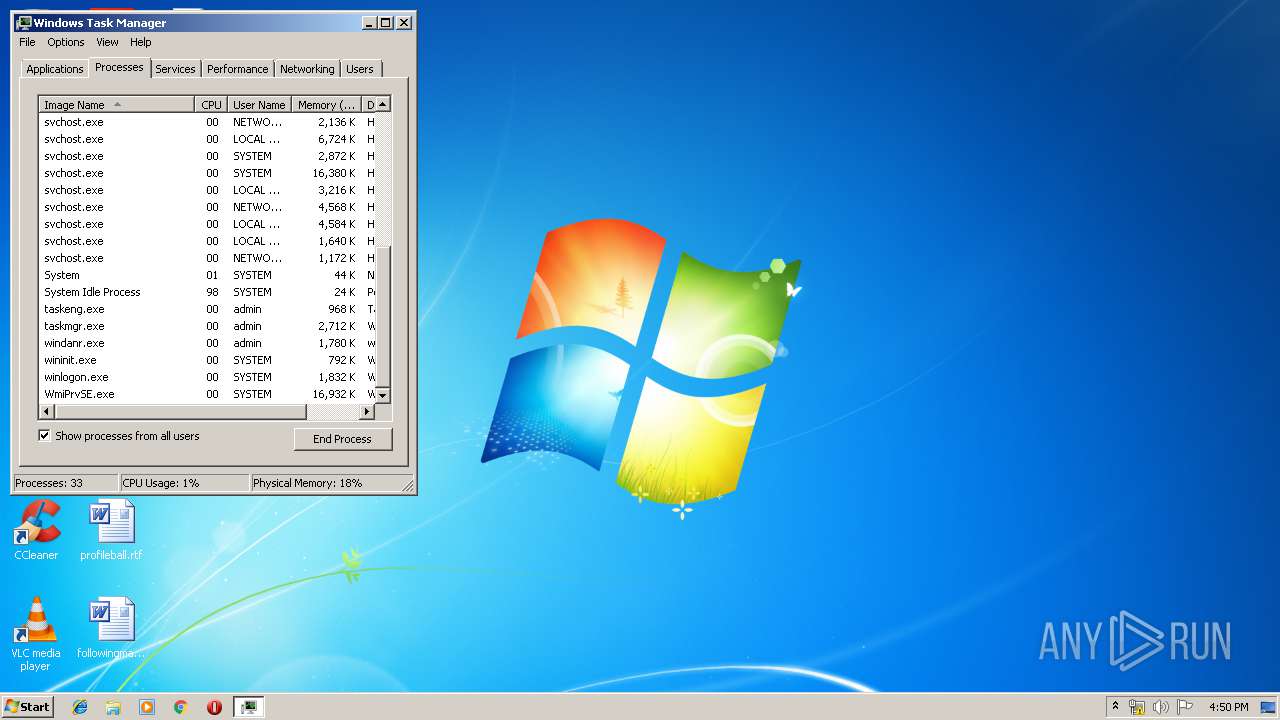
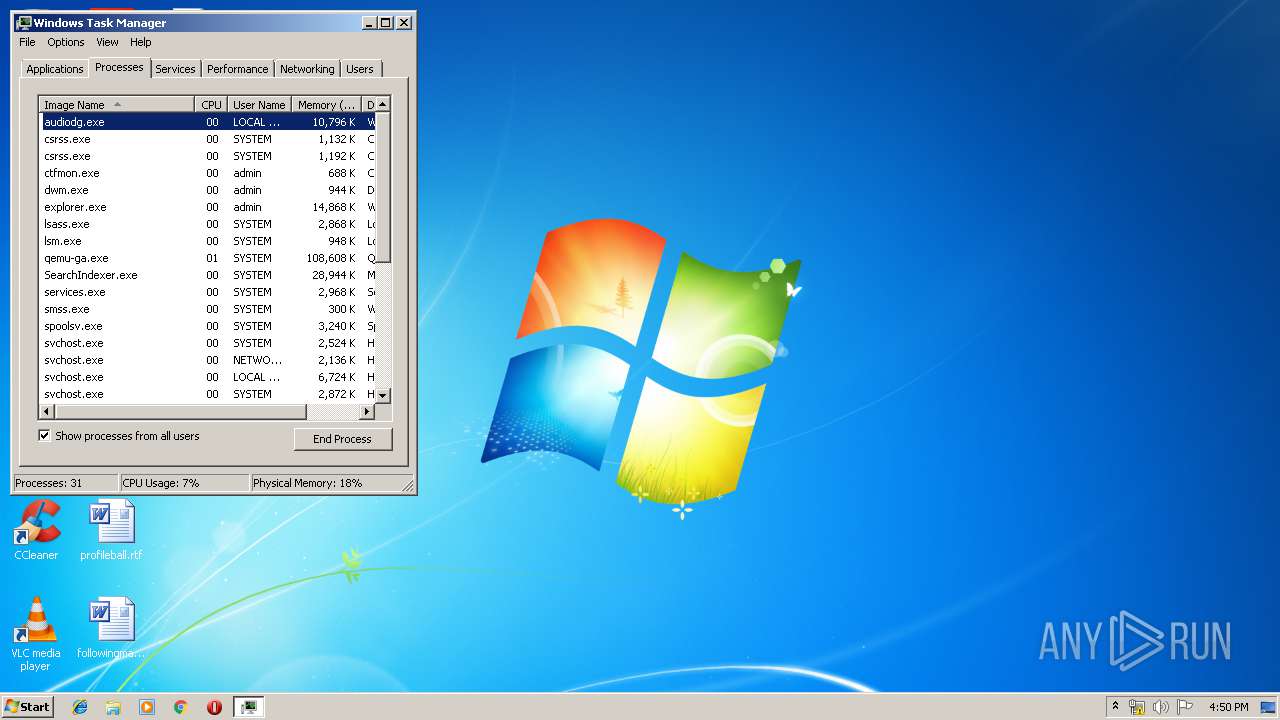
Total processes
81
Monitored processes
36
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,274335324853369296,6196712777976569203,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10515255999658071078 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Users\admin\Downloads\Dolphin.exe" | C:\Users\admin\Downloads\Dolphin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225781 Modules
| |||||||||||||||
| 856 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe7_ Global\UsGthrCtrlFltPipeMssGthrPipe7 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,274335324853369296,6196712777976569203,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13044581310859733210 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,274335324853369296,6196712777976569203,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5775335961232395988 --mojo-platform-channel-handle=3380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,274335324853369296,6196712777976569203,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12090734500728511541 --mojo-platform-channel-handle=3260 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Windows\system32\taskmgr.exe" /1 | C:\Windows\system32\taskmgr.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,274335324853369296,6196712777976569203,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2904325807707400420 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,274335324853369296,6196712777976569203,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=623514642757996342 --mojo-platform-channel-handle=3308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 319
Read events
1 154
Write events
160
Delete events
5
Modification events
| (PID) Process: | (856) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (856) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (3348) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3396-13207160792735679 |
Value: 259 | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
6
Suspicious files
221
Text files
1 888
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3464 | dolphin-4.0-win32.exe | C:\Users\admin\Downloads\Sys\Themes\Boomy\browse.png | image | |
MD5:93CEB827A42897C5DF8190E14CD11A52 | SHA256:3A1571E9AAE1964969BFC5F1805DC2645E06C4C17A781200313AFA8D550AE297 | |||
| 3464 | dolphin-4.0-win32.exe | C:\Users\admin\Downloads\Sys\Themes\Clean Pink\browse.png | image | |
MD5:D93DDF7D41DE46F18F373E047A517A34 | SHA256:617C479AAAC6EC64BF28B3D12EB04F719F962AF1CD61235864A12AF3F8823442 | |||
| 3464 | dolphin-4.0-win32.exe | C:\Users\admin\Downloads\Sys\Themes\Clean Blue\dsp.png | image | |
MD5:82EF9C274867E629F5A715F39CE7D796 | SHA256:77F9272239887CC00CE55D15A89D6D0D363279045808B1EA842C543D4CDADC71 | |||
| 3464 | dolphin-4.0-win32.exe | C:\Users\admin\Downloads\Sys\Themes\Clean Pink\config.png | image | |
MD5:FE19C1709918CBD6AC0597B8722689E9 | SHA256:49F33F31B18B0E0E4F1A3F2D46E4D620DB599145765F06813D83454BC8980C4B | |||
| 3464 | dolphin-4.0-win32.exe | C:\Users\admin\Downloads\Sys\Themes\Clean Blue\browse.png | image | |
MD5:9B3B206209B8BBD536913FD24CF7DEE6 | SHA256:E619DD5A8A02953093039BFD8CEEA2269BB3EFCAC1FC3C16610BB5C90D2F60C2 | |||
| 3464 | dolphin-4.0-win32.exe | C:\Users\admin\Downloads\Sys\Wii\shared2\sys\SYSCONF | binary | |
MD5:9473C879A5E51040E7A202B4538773A7 | SHA256:A8EC1EC377EE3A3C93A27F74DADF9EDF95112CE167FC23D1ABDBEB4FA15EB179 | |||
| 3464 | dolphin-4.0-win32.exe | C:\Users\admin\Downloads\Sys\Themes\Clean Lite\browse.png | image | |
MD5:FFA0D034EEEDC9BA1DB99972521DE330 | SHA256:64FB7374470AA272709174B5CBE09FCCDC5CF4760768536713CA7A7AED834C05 | |||
| 3464 | dolphin-4.0-win32.exe | C:\Users\admin\Downloads\Sys\Themes\Clean\browse.png | image | |
MD5:56D66F9CC42289F076A002D0C1D06456 | SHA256:AE163363F0876FAC306E6487466385F7458E3F467F27040D93D93910E82B21C7 | |||
| 3464 | dolphin-4.0-win32.exe | C:\Users\admin\Downloads\Sys\Themes\Clean Blue\config.png | image | |
MD5:D515F3CED1C81BAD162625F066C0CA05 | SHA256:D127B6DC8C749AD22731E7F3ACDF3BD169864F4C00DAB491B6004EBC4A5937EE | |||
| 3464 | dolphin-4.0-win32.exe | C:\Users\admin\Downloads\Sys\Themes\Boomy\config.png | image | |
MD5:4E380B7F03557B6A5B8E325173B676EA | SHA256:7BE3A86886870B2D527CB5F61F9BDE3E099E964923AF3C05FFB5985F5E64C664 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
33
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
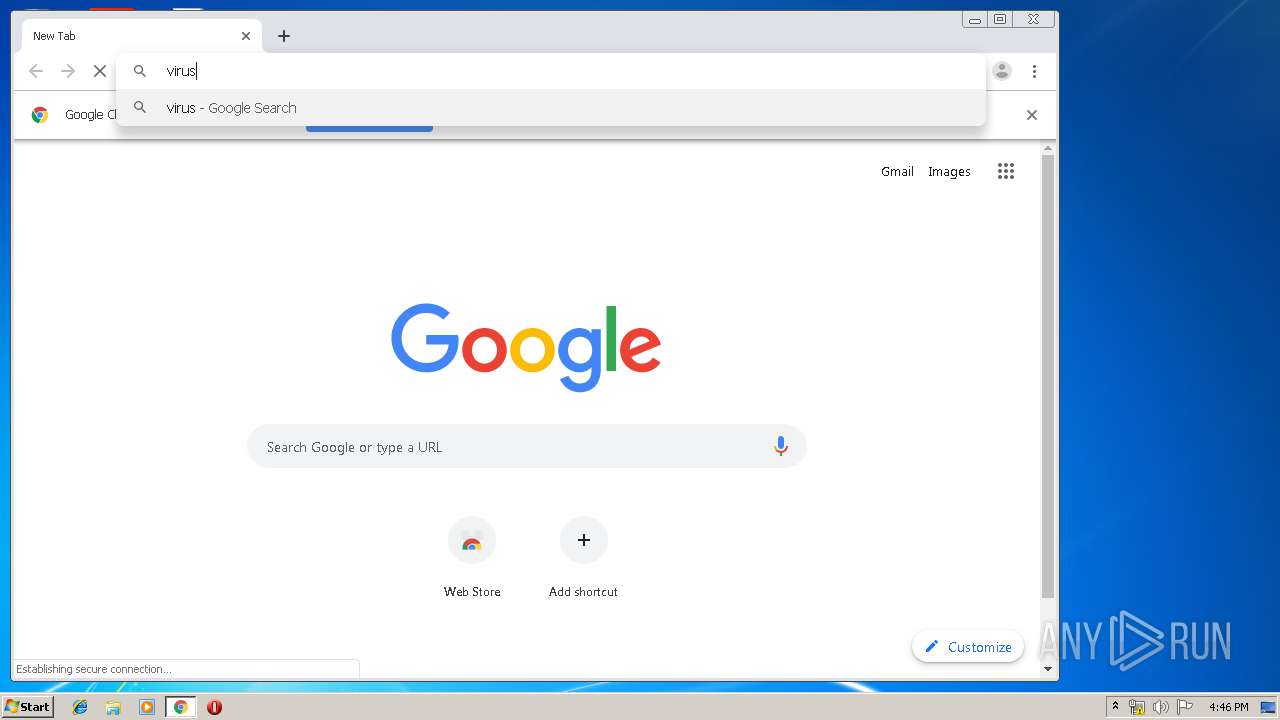
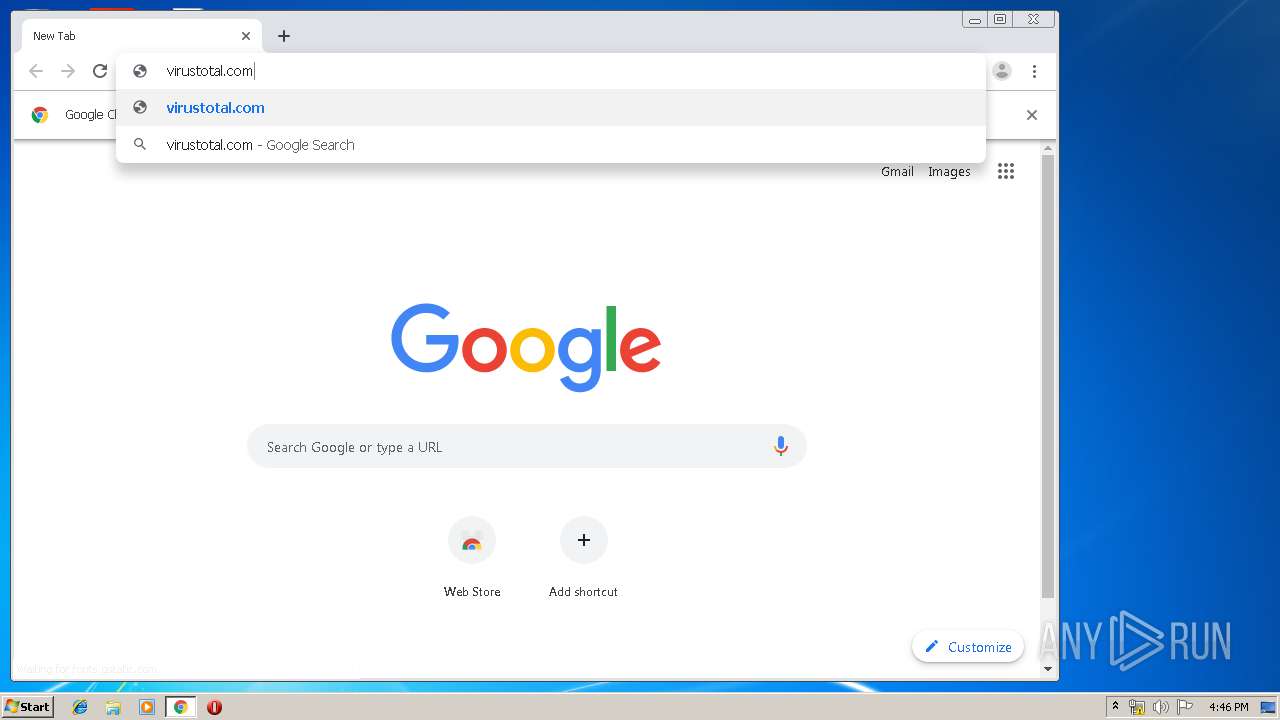
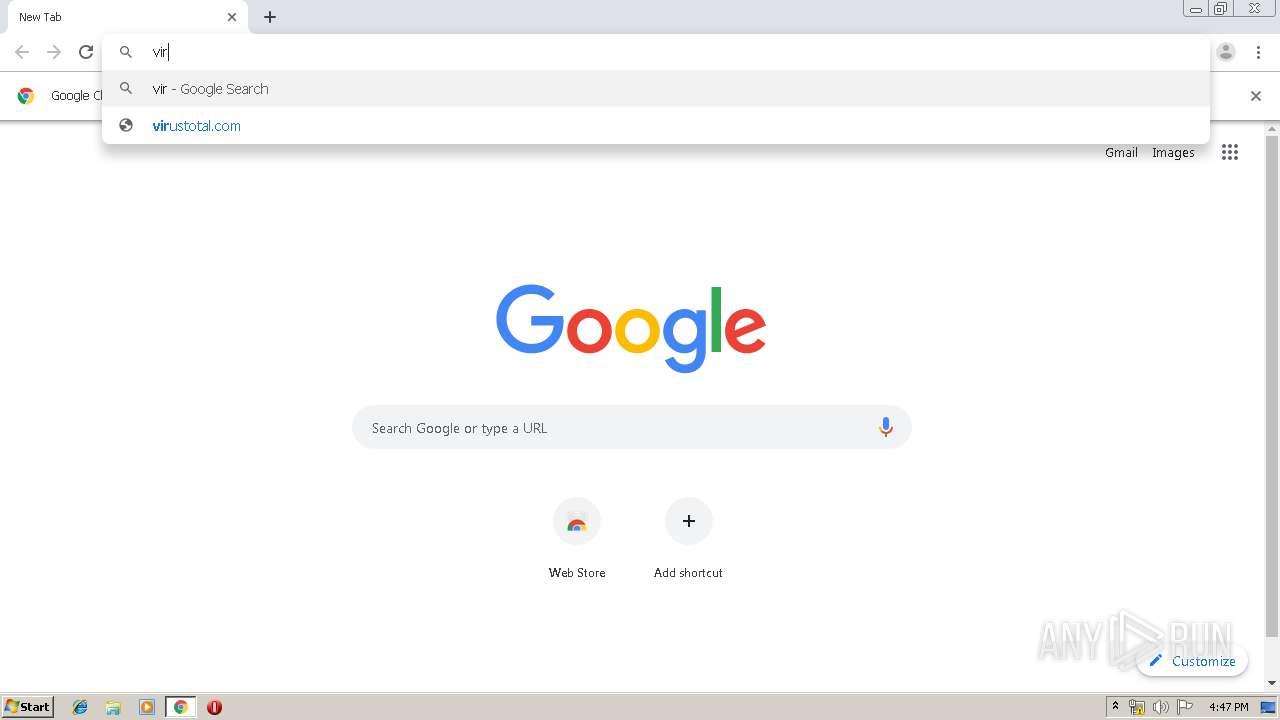
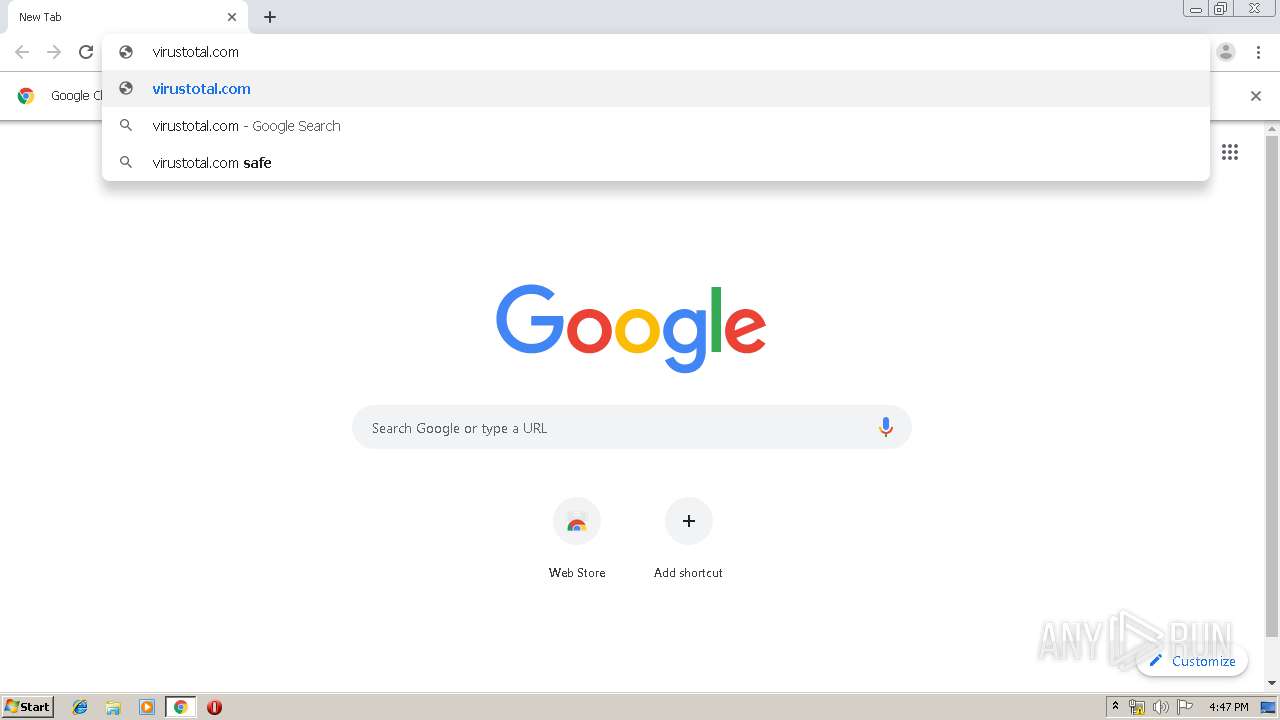
2716 | chrome.exe | GET | 302 | 216.239.38.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
2716 | chrome.exe | GET | 200 | 74.125.8.140:80 | http://r6---sn-5hnednlk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.107.47.171&mm=28&mn=sn-5hnednlk&ms=nvh&mt=1562687127&mv=m&mvi=5&pl=22&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2716 | chrome.exe | GET | 302 | 172.217.17.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2716 | chrome.exe | 172.217.19.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2716 | chrome.exe | 172.217.169.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2716 | chrome.exe | 172.217.17.46:443 | apis.google.com | Google Inc. | US | whitelisted |
2716 | chrome.exe | 172.217.169.206:443 | ogs.google.com | Google Inc. | US | whitelisted |
2716 | chrome.exe | 172.217.168.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2716 | chrome.exe | 216.58.208.100:443 | www.google.com | Google Inc. | US | whitelisted |
2716 | chrome.exe | 172.217.17.195:443 | www.google.nl | Google Inc. | US | whitelisted |
2716 | chrome.exe | 216.239.38.21:80 | virustotal.com | Google Inc. | US | whitelisted |
2716 | chrome.exe | 172.217.19.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2716 | chrome.exe | 172.217.169.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
virustotal.com |
| whitelisted |