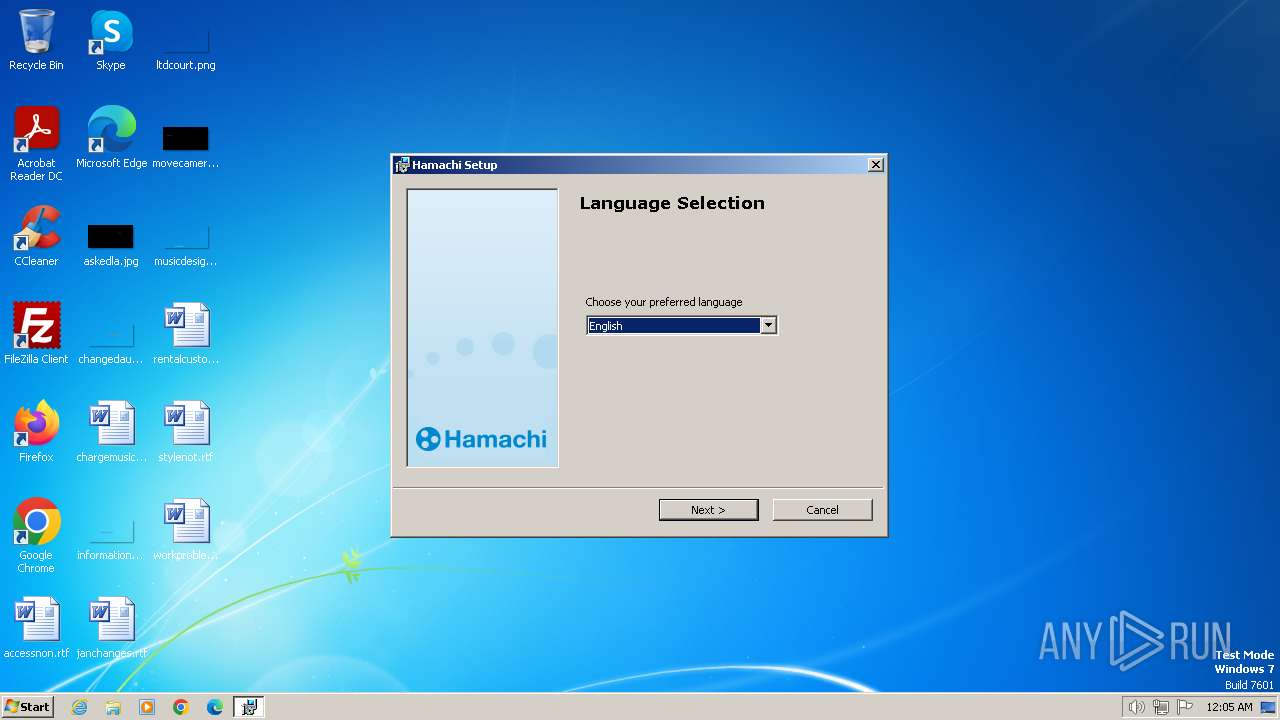
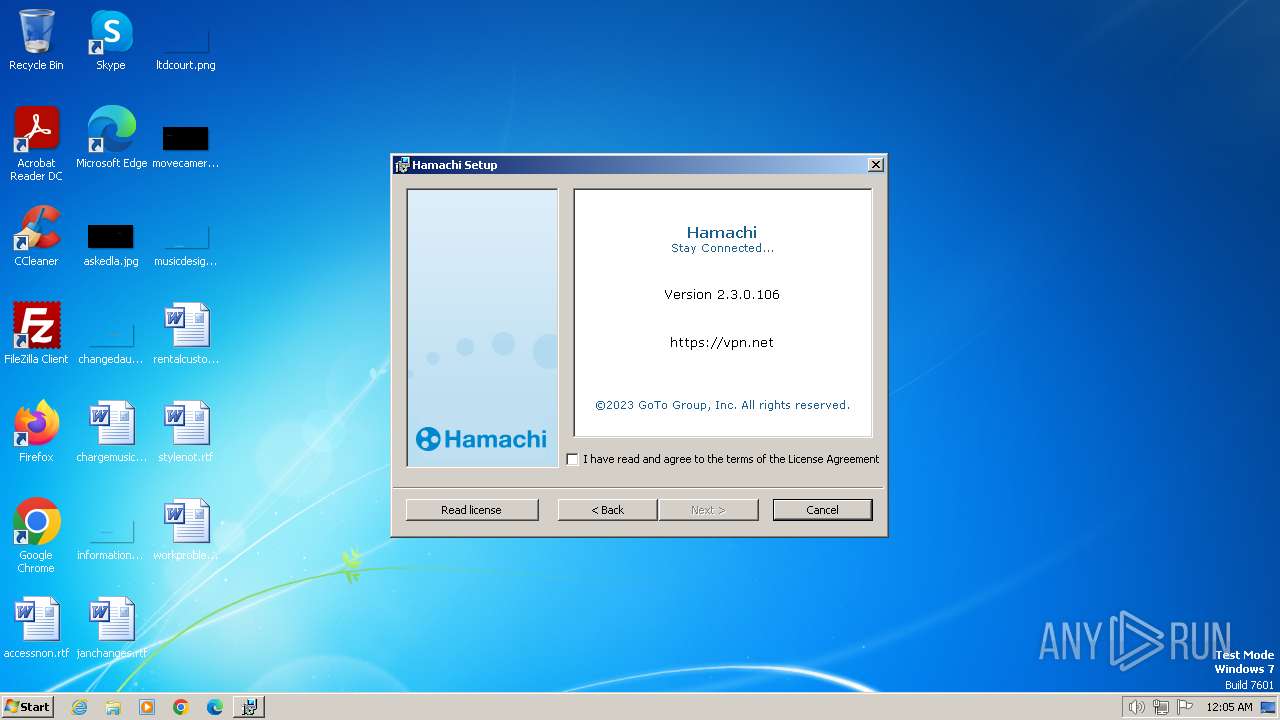
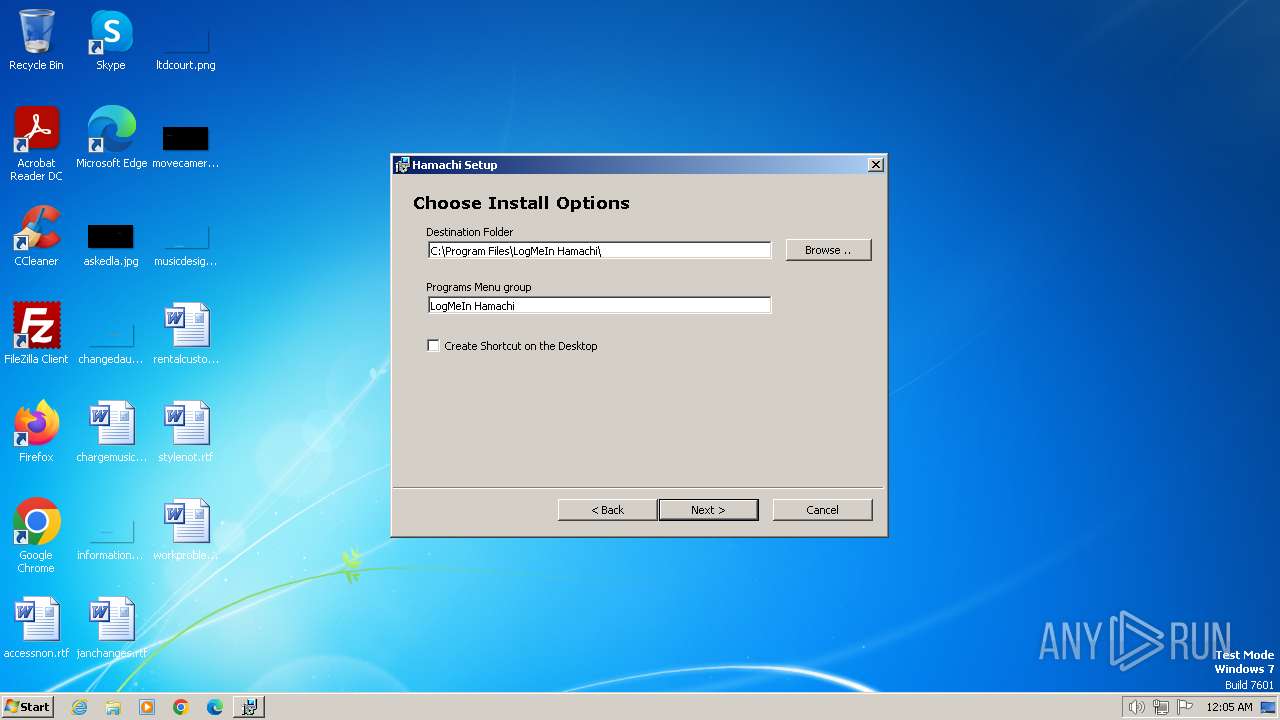
| File name: | hamachi.msi |
| Full analysis: | https://app.any.run/tasks/f6e4d92c-9082-44cb-a3a0-ab14c8cf508c |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2024, 00:04:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Hamachi Installer, Author: LogMeIn, Inc., Keywords: Installer, Comments: This installer database contains the logic and data required to install Hamachi., Template: ;1033, Number of Pages: 200, Number of Words: 2, Security: 2, Revision Number: {6B7DAA44-747B-45EB-9E86-0EF63D3D8A2D}, Create Time/Date: Mon Nov 6 11:52:41 2023, Last Saved Time/Date: Mon Nov 6 11:52:41 2023, Name of Creating Application: Windows Installer XML v2.0.5805.0 (candle/light) |
| MD5: | A44011365AB1EEE08BC055879967058C |
| SHA1: | 17EB9E944AD9CF0FFD68BD3FA61E43F4FB14A88D |
| SHA256: | 9D933EFB6C74180A8BE55C42F7FE9B58BC9F92E2B3217750796D547803DCACC3 |
| SSDEEP: | 98304:+u8eueXuHc5VLHlGoFJahcc2qCHdlrHmtscQLGtaF9qEH2Dr9h7LSH3j90IdKSFW:W0uqyhfgM2R14FTQPbT2 |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 1432)
Creates a writable file in the system directory
- LMIGuardianSvc.exe (PID: 3492)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 3212)
- hamachi-2.exe (PID: 3760)
- LMIGuardianSvc.exe (PID: 3492)
- hamachi-2.exe (PID: 3316)
Connects to unusual port
- hamachi-2.exe (PID: 3316)
Suspicious use of NETSH.EXE
- hamachi-2.exe (PID: 3316)
INFO
Reads the computer name
- LMIGuardianSvc.exe (PID: 3544)
- LMIGuardianSvc.exe (PID: 1124)
- hamachi-2.exe (PID: 3760)
- LMIGuardianSvc.exe (PID: 4084)
- LMIGuardianSvc.exe (PID: 3492)
- hamachi-2.exe (PID: 3316)
- LMIGuardianSvc.exe (PID: 2436)
- LMIGuardianSvc.exe (PID: 3412)
- wmpnscfg.exe (PID: 3080)
- wmpnscfg.exe (PID: 864)
- wmpnscfg.exe (PID: 2404)
- wmpnscfg.exe (PID: 2376)
- wmpnscfg.exe (PID: 2480)
- wmpnscfg.exe (PID: 3688)
- wmpnscfg.exe (PID: 1840)
Checks supported languages
- LMIGuardianSvc.exe (PID: 3544)
- LMIGuardianSvc.exe (PID: 1124)
- hamachi-2.exe (PID: 3760)
- LMIGuardianSvc.exe (PID: 4084)
- LMIGuardianSvc.exe (PID: 3492)
- hamachi-2.exe (PID: 3316)
- LMIGuardianSvc.exe (PID: 3412)
- LMIGuardianSvc.exe (PID: 2436)
- wmpnscfg.exe (PID: 3080)
- wmpnscfg.exe (PID: 2480)
- wmpnscfg.exe (PID: 3688)
- wmpnscfg.exe (PID: 864)
- wmpnscfg.exe (PID: 2404)
- wmpnscfg.exe (PID: 2376)
- wmpnscfg.exe (PID: 1840)
Reads the software policy settings
- msiexec.exe (PID: 1432)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1432)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1432)
Reads the machine GUID from the registry
- LMIGuardianSvc.exe (PID: 4084)
- hamachi-2.exe (PID: 3760)
- LMIGuardianSvc.exe (PID: 3492)
- LMIGuardianSvc.exe (PID: 3412)
- hamachi-2.exe (PID: 3316)
- LMIGuardianSvc.exe (PID: 2436)
Creates files or folders in the user directory
- LMIGuardianSvc.exe (PID: 2436)
Creates files in the program directory
- LMIGuardianSvc.exe (PID: 2436)
- LMIGuardianSvc.exe (PID: 3492)
Manual execution by a user
- wmpnscfg.exe (PID: 3080)
- wmpnscfg.exe (PID: 864)
- wmpnscfg.exe (PID: 2404)
- wmpnscfg.exe (PID: 2376)
- wmpnscfg.exe (PID: 2480)
- wmpnscfg.exe (PID: 1840)
- wmpnscfg.exe (PID: 3688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Hamachi Installer |
| Author: | LogMeIn, Inc. |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Hamachi. |
| Template: | ;1033 |
| Pages: | 200 |
| Words: | 2 |
| Security: | Read-only recommended |
| RevisionNumber: | {6B7DAA44-747B-45EB-9E86-0EF63D3D8A2D} |
| CreateDate: | 2023:11:06 11:52:41 |
| ModifyDate: | 2023:11:06 11:52:41 |
| Software: | Windows Installer XML v2.0.5805.0 (candle/light) |
Total processes
83
Monitored processes
24
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1124 | "C:\Program Files\LogMeIn Hamachi\LMIGuardianSvc.exe" /escort 3172 /CUSTOM Hamachi | C:\Program Files\LogMeIn Hamachi\LMIGuardianSvc.exe | — | hamachi-2.exe | |||||||||||
User: SYSTEM Company: LogMeIn, Inc. Integrity Level: SYSTEM Description: LMIGuardianSvc Exit code: 0 Version: 10.1.1742 Modules
| |||||||||||||||
| 1432 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\hamachi.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1808 | netsh interface ipv6 add address interface="18" address=2620:9b::1901:c802 type=unicast store=persistent | C:\Windows\System32\netsh.exe | — | hamachi-2.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2020 | netsh interface ipv6 add route ::/0 "18" 2620:9b::1900:1 metric=9000 publish=yes | C:\Windows\System32\netsh.exe | — | hamachi-2.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | "C:\Program Files\LogMeIn Hamachi\LMIGuardianSvc.exe" /escort 2952 /CUSTOM Hamachi | C:\Program Files\LogMeIn Hamachi\LMIGuardianSvc.exe | — | hamachi-2-ui.exe | |||||||||||
User: admin Company: LogMeIn, Inc. Integrity Level: MEDIUM Description: LMIGuardianSvc Exit code: 0 Version: 10.1.1742 Modules
| |||||||||||||||
Total events
15 411
Read events
14 878
Write events
526
Delete events
7
Modification events
| (PID) Process: | (1432) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000008AD7B8101174DA018C0C00000C0A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000008AD7B8101174DA018C0C0000780F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000008AD7B8101174DA018C0C000078000000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000008AD7B8101174DA018C0C0000640F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000E439BB101174DA018C0C0000780F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000E439BB101174DA018C0C00000C0A0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000003E9CBD101174DA018C0C0000640F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000003E9CBD101174DA018C0C000078000000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3212) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SwProvider_{b5946137-7b9f-4925-af80-51abd60b20d5} |
| Operation: | write | Name: | PROVIDER_BEGINPREPARE (Enter) |
Value: 4000000000000000848C12121174DA018C0C00007800000001040000010000000000000000000000EBD10992D17B28408674FF222EE53EAD0000000000000000 | |||
Executable files
6
Suspicious files
3
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1432 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF9C2.tmp | executable | |
MD5:571C9E902F85252BC7A1B2CFB7A7BD27 | SHA256:79252837D553EDD9DF816D3959D48E127740D6C21D24B0ADE6605EDC31639830 | |||
| 1432 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIDBF6.tmp | executable | |
MD5:571C9E902F85252BC7A1B2CFB7A7BD27 | SHA256:79252837D553EDD9DF816D3959D48E127740D6C21D24B0ADE6605EDC31639830 | |||
| 1432 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI1932.tmp | executable | |
MD5:571C9E902F85252BC7A1B2CFB7A7BD27 | SHA256:79252837D553EDD9DF816D3959D48E127740D6C21D24B0ADE6605EDC31639830 | |||
| 1432 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF963.tmp | executable | |
MD5:571C9E902F85252BC7A1B2CFB7A7BD27 | SHA256:79252837D553EDD9DF816D3959D48E127740D6C21D24B0ADE6605EDC31639830 | |||
| 1432 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIE1C4.tmp | executable | |
MD5:571C9E902F85252BC7A1B2CFB7A7BD27 | SHA256:79252837D553EDD9DF816D3959D48E127740D6C21D24B0ADE6605EDC31639830 | |||
| 3316 | hamachi-2.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\LogMeIn Hamachi\h2-engine.ini | text | |
MD5:E723DFE4E5BF655B6586CD4BE8937BC1 | SHA256:1C89F654F433102B00A9D74C203FC228D016D7A3A2F864F6517FA43806AF4913 | |||
| 1432 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIA880.tmp | executable | |
MD5:571C9E902F85252BC7A1B2CFB7A7BD27 | SHA256:79252837D553EDD9DF816D3959D48E127740D6C21D24B0ADE6605EDC31639830 | |||
| 3316 | hamachi-2.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\LogMeIn Hamachi\h2-server.key | binary | |
MD5:3E57FB6553F6280DC873CD4B15FF572B | SHA256:AFE44706908A1E349C7DFBC79419F5FE8D62ACF9B07DCA7D29AC2BA97BD73B19 | |||
| 3316 | hamachi-2.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\LogMeIn Hamachi\h2-engine.ini.bak | text | |
MD5:E723DFE4E5BF655B6586CD4BE8937BC1 | SHA256:1C89F654F433102B00A9D74C203FC228D016D7A3A2F864F6517FA43806AF4913 | |||
| 3316 | hamachi-2.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\LogMeIn Hamachi\h2-engine.cfg | text | |
MD5:5919A4242A1FB169C68317D18ADF2746 | SHA256:7E5ADB2F62EB88481057A6E469ED552B15BEEA681C3CC4AB37C96B458D1969BA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
47
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2952 | hamachi-2-ui.exe | GET | 304 | 62.115.253.41:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1b2c67b9db6f7f0d | ES | — | — | unknown |
2952 | hamachi-2-ui.exe | GET | 304 | 62.115.253.64:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7006048780059c7a | ES | — | — | unknown |
2952 | hamachi-2-ui.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | binary | 471 b | unknown |
2952 | hamachi-2-ui.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
2952 | hamachi-2-ui.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCimReIRyQtphKmdTNhBzaE | US | binary | 472 b | unknown |
2952 | hamachi-2-ui.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
2952 | hamachi-2-ui.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | unknown |
2952 | hamachi-2-ui.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3316 | hamachi-2.exe | 158.120.16.27:12975 | — | ORACLE-BMC-31898 | DE | unknown |
3316 | hamachi-2.exe | 239.255.255.250:1900 | — | — | — | unknown |
2952 | hamachi-2-ui.exe | 158.120.16.205:443 | secure.logmein.com | ORACLE-BMC-31898 | DE | unknown |
2952 | hamachi-2-ui.exe | 62.115.253.41:80 | ctldl.windowsupdate.com | Telia Company AB | ES | unknown |
2952 | hamachi-2-ui.exe | 62.115.253.64:80 | ctldl.windowsupdate.com | Telia Company AB | ES | unknown |
2952 | hamachi-2-ui.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hamachi-data-center.logmein-gateway.com |
| unknown |
hamachi-list.24.logmein-gateway.com |
| unknown |
secure.logmein.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
accounts.logme.in |
| unknown |
az416426.vo.msecnd.net |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |