| File name: | Keygen для 2014.exe |
| Full analysis: | https://app.any.run/tasks/3d698fde-8631-4361-b962-a7e103eb96ac |
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2024, 18:30:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 36D599ACBF8D50C1BCC2723FF3A52D59 |
| SHA1: | 5D265BA4AA8430AADD6103BECE31B728B684D8C0 |
| SHA256: | 9D81D37BF7D9E83B1532D80643223FCDA6812420A40871C359FBD81153BA71E4 |
| SSDEEP: | 6144:w3u0oi/k0xuKScp/JDHvZ8uEoJ2u9U18I+cu3sgEz2ZCZtGE7:w3u0ois8ScpBLKuE07Zcu3Sz2az7 |
MALICIOUS
XORed URL has been found (YARA)
- Keygen для 2014.exe (PID: 6308)
SUSPICIOUS
Reads security settings of Internet Explorer
- Keygen для 2014.exe (PID: 6308)
INFO
Checks supported languages
- Keygen для 2014.exe (PID: 6308)
Reads the computer name
- Keygen для 2014.exe (PID: 6308)
Reads the machine GUID from the registry
- Keygen для 2014.exe (PID: 6308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(6308) Keygen для 2014.exe
Decrypted-URLs (3)http://www.w3.org/2000/09/xmldsig#dsa-sha1
http://www.w3.org/2000/09/xmldsig#rsa-sha1+ylm!ghmdr!)+/ylm(
http://www.w3.org/2001/10/xml-exc-c14n#kwws9,,ttt-t0-lqd,1333,3:,
Decrypted-URLs (6)http://schemas.microsoft.com/2003/10/Serialization/@
http://www.w3.org/2000/09/xmldsig#dsa-sha1
http://www.w3.org/2000/09/xmldsig#rsa-sha1+ylm!ghmdr!)+/ylm(
http://www.w3.org/2001/10/xml-exc-c14n#kwws9,,ttt-t0-lqd,1333,3:,
http://www.w3.org/2001/XMLSchema
http://www.w3.org/2001/XMLSchema-instance
Decrypted-URLs (5)http://www.w3.org/2000/09/xmldsig#dsa-sha1
http://www.w3.org/2000/09/xmldsig#dsa-sha1Bsxqunfs
http://www.w3.org/2000/09/xmldsig#rsa-sha1
http://www.w3.org/2000/09/xmldsig#rsa-sha1+ylm!ghmdr!)+/ylm(
http://www.w3.org/2001/10/xml-exc-c14n#kwws9,,ttt-t0-lqd,1333,3:,
Decrypted-URLs (8)http://schemas.microsoft.com/2003/10/Serialization/@
http://www.w3.org/2000/09/xmldsig#dsa-sha1
http://www.w3.org/2000/09/xmldsig#dsa-sha1Bsxqunfs
http://www.w3.org/2000/09/xmldsig#rsa-sha1
http://www.w3.org/2000/09/xmldsig#rsa-sha1+ylm!ghmdr!)+/ylm(
http://www.w3.org/2001/10/xml-exc-c14n#kwws9,,ttt-t0-lqd,1333,3:,
http://www.w3.org/2001/XMLSchema
http://www.w3.org/2001/XMLSchema-instance
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:11:17 06:12:05+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 242688 |
| InitializedDataSize: | 22016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3d3b2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
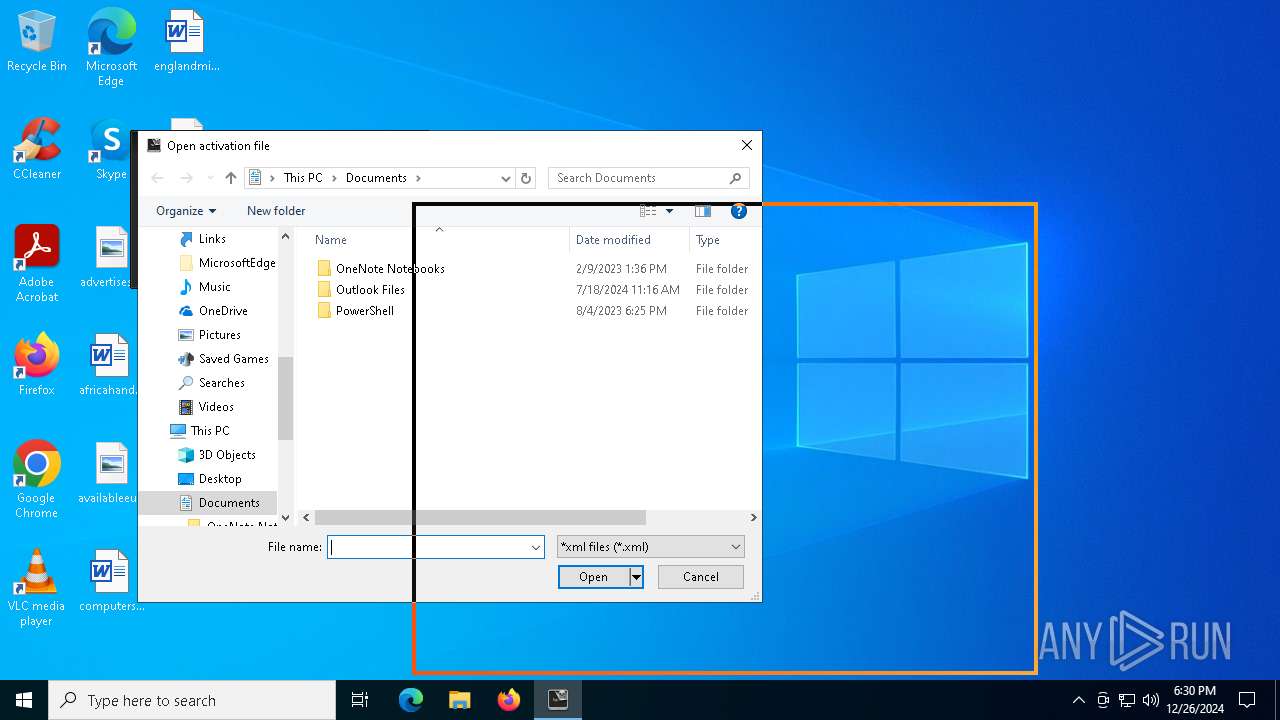
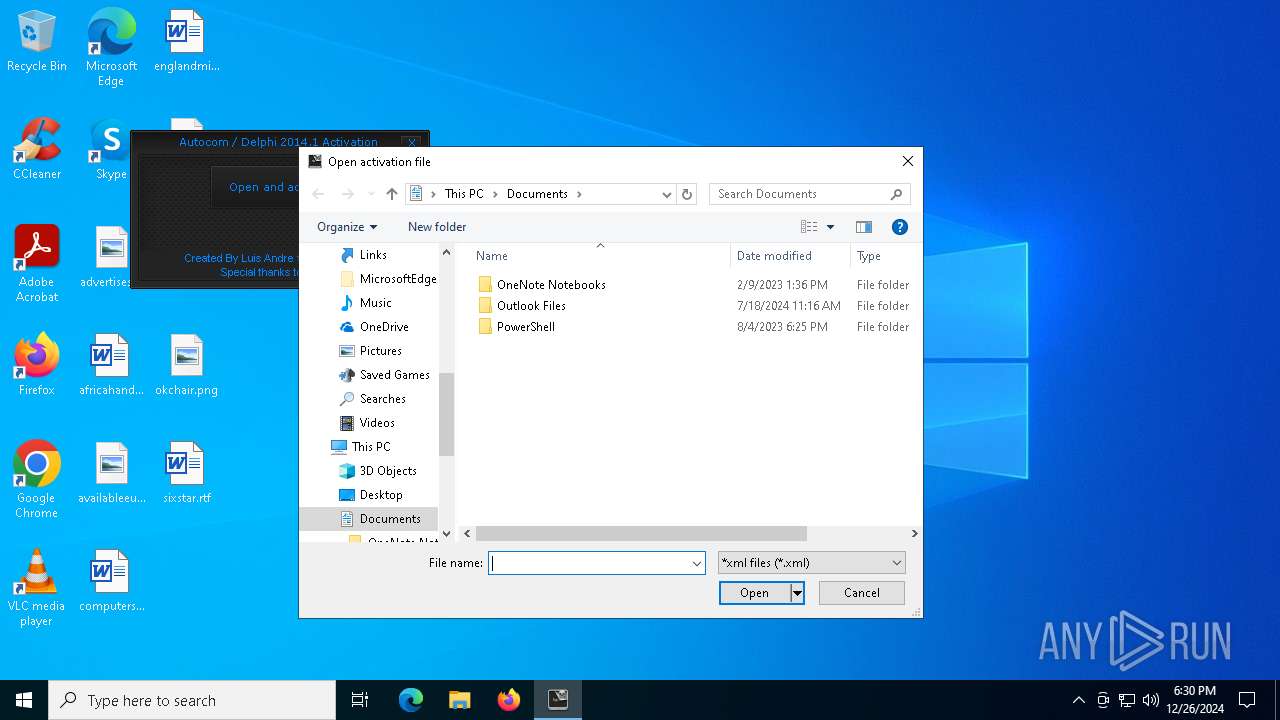
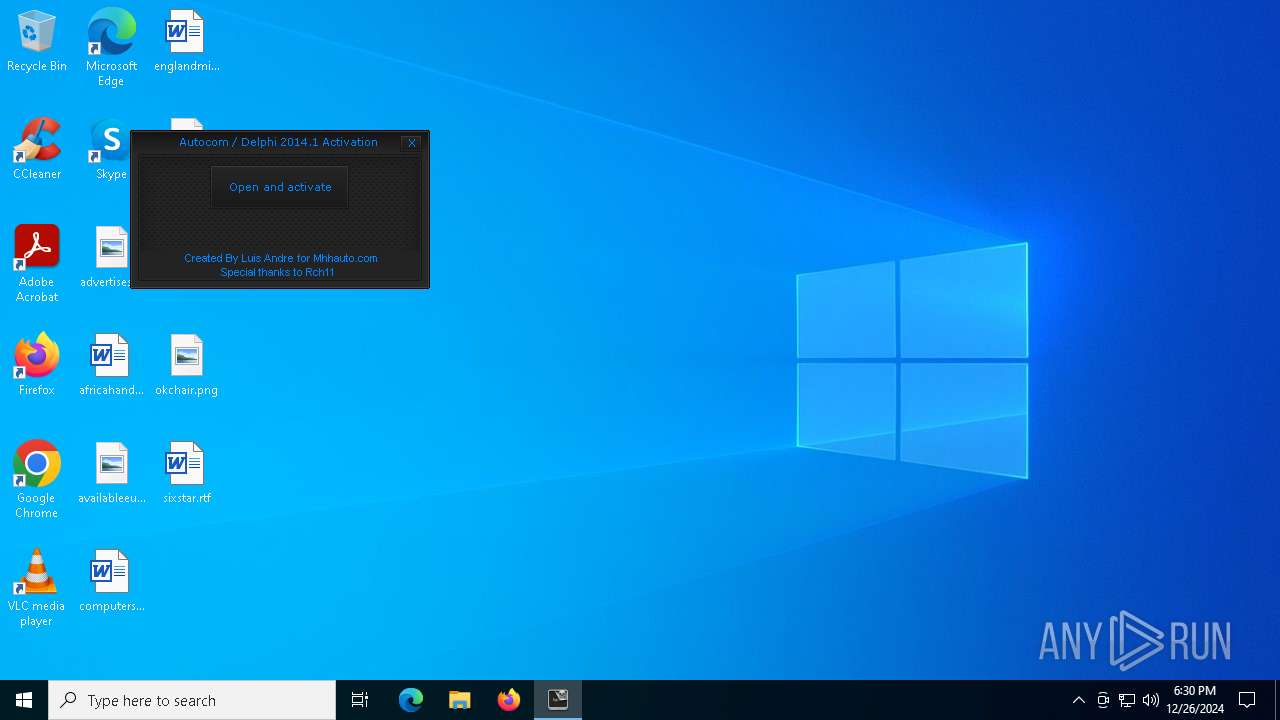
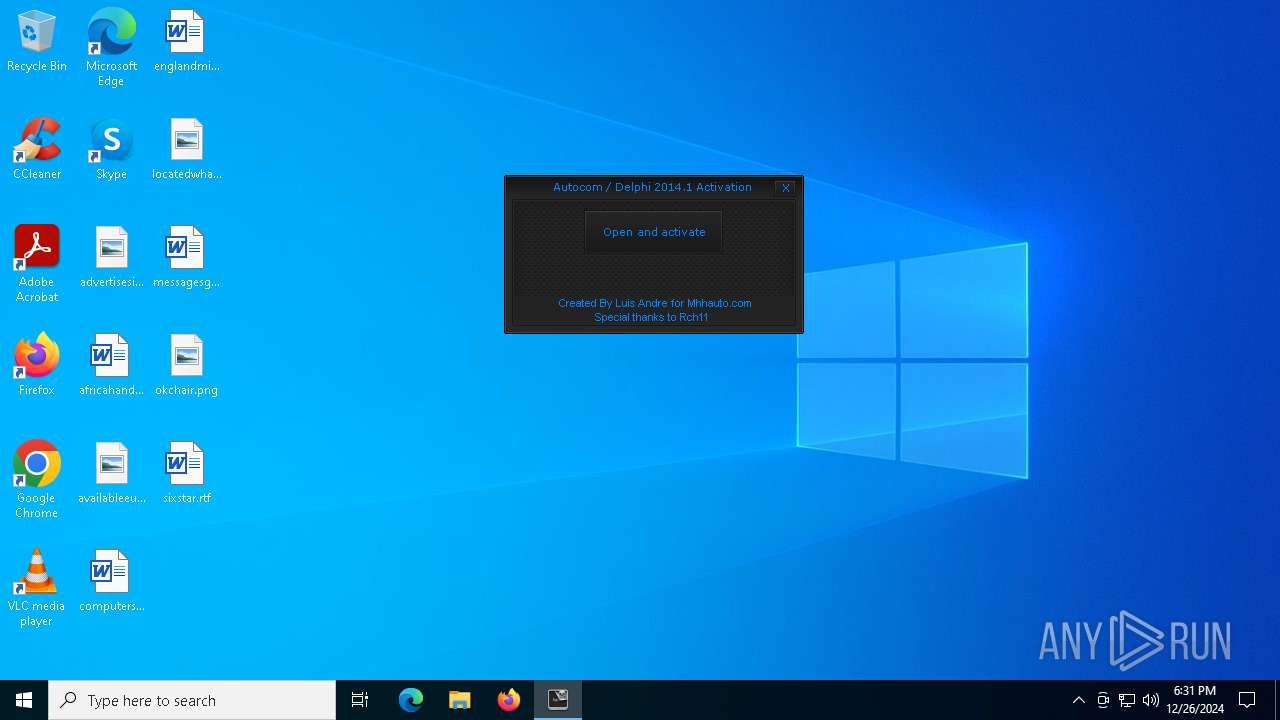
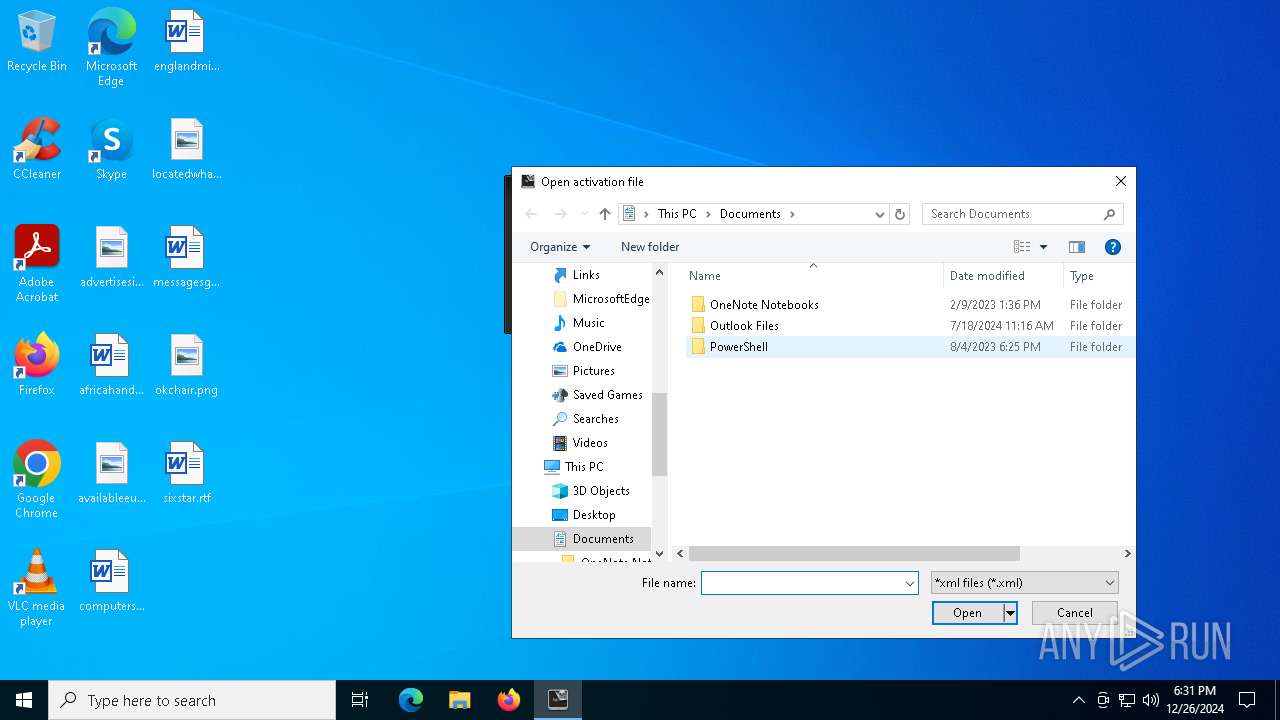
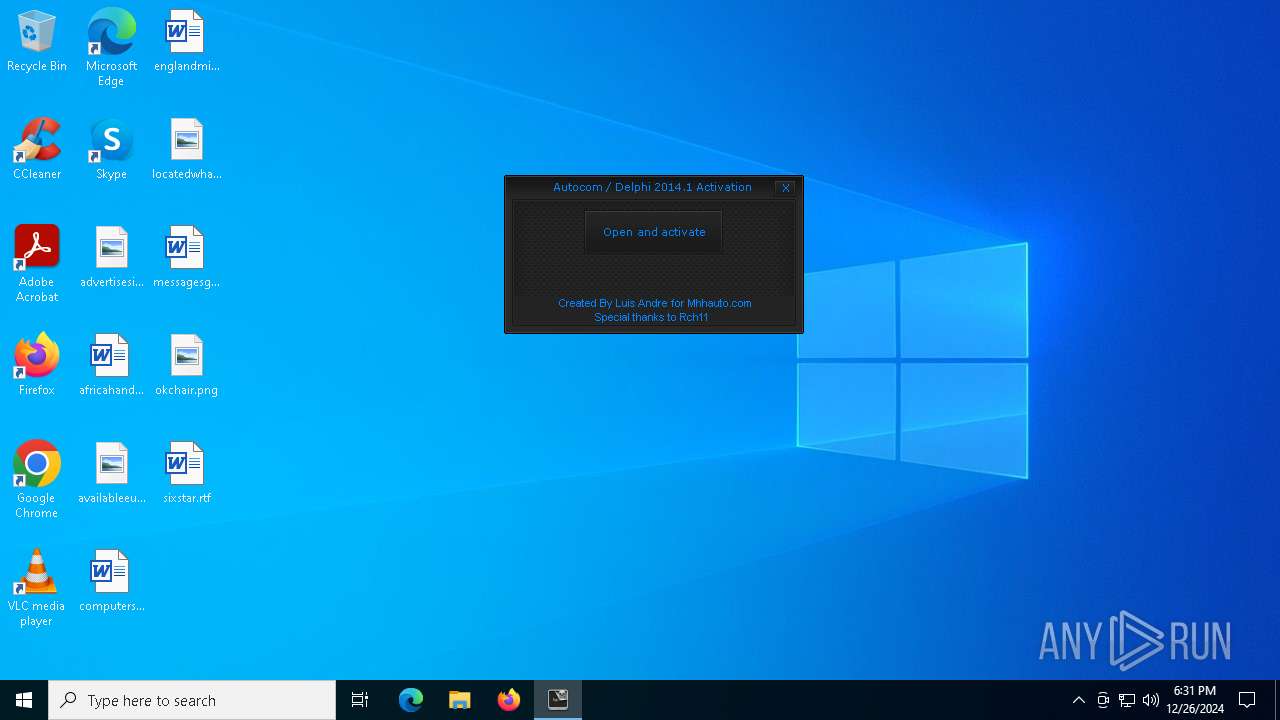
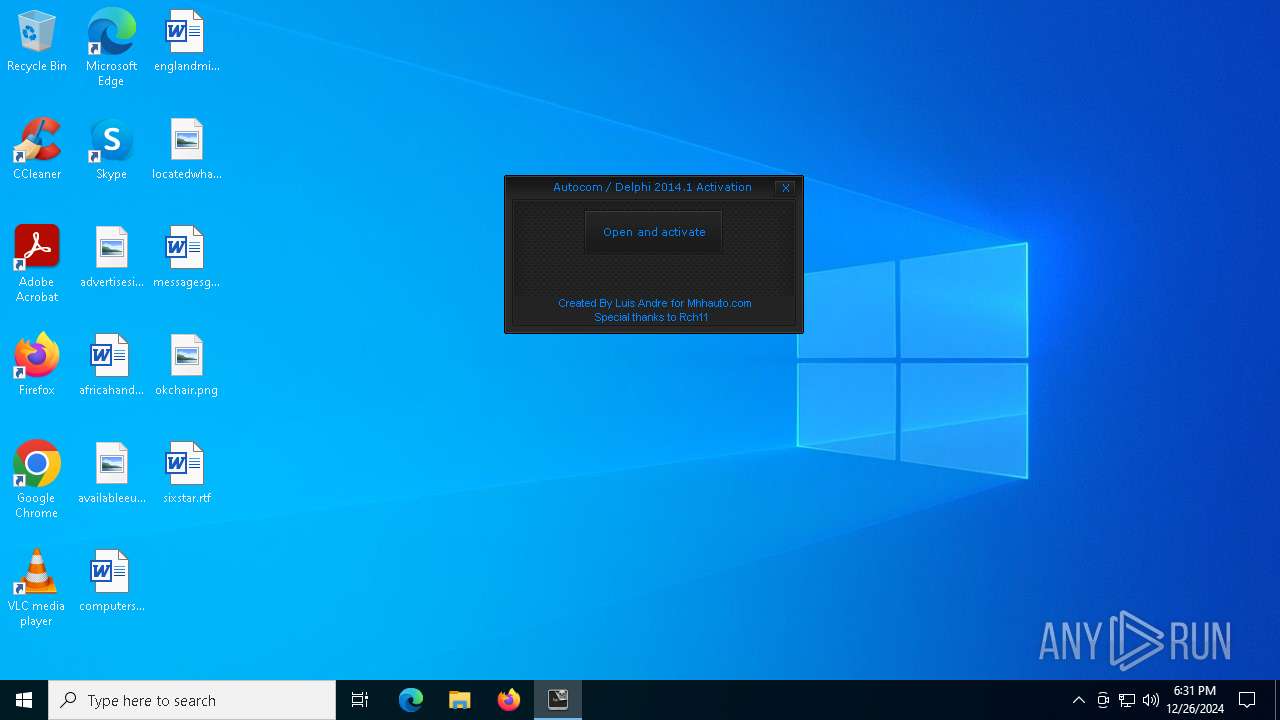
| FileDescription: | AutocomDelphiActivator |
| FileVersion: | 2.0.0.0 |
| InternalName: | Autocom Delphi Keygen 2014R1.exe |
| LegalCopyright: | Copyright © 2012 |
| OriginalFileName: | Autocom Delphi Keygen 2014R1.exe |
| ProductName: | AutocomDelphiActivator |
| ProductVersion: | 2.0.0.0 |
| AssemblyVersion: | 2.0.0.0 |
Total processes
128
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6308 | "C:\Users\admin\AppData\Local\Temp\Keygen для 2014.exe" | C:\Users\admin\AppData\Local\Temp\Keygen для 2014.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AutocomDelphiActivator Version: 2.0.0.0 Modules
xor-url(PID) Process(6308) Keygen для 2014.exe Decrypted-URLs (3)http://www.w3.org/2000/09/xmldsig#dsa-sha1 http://www.w3.org/2000/09/xmldsig#rsa-sha1+ylm!ghmdr!)+/ylm( http://www.w3.org/2001/10/xml-exc-c14n#kwws9,,ttt-t0-lqd,1333,3:, (PID) Process(6308) Keygen для 2014.exe Decrypted-URLs (6)http://schemas.microsoft.com/2003/10/Serialization/@ http://www.w3.org/2000/09/xmldsig#dsa-sha1 http://www.w3.org/2000/09/xmldsig#rsa-sha1+ylm!ghmdr!)+/ylm( http://www.w3.org/2001/10/xml-exc-c14n#kwws9,,ttt-t0-lqd,1333,3:, http://www.w3.org/2001/XMLSchema http://www.w3.org/2001/XMLSchema-instance (PID) Process(6308) Keygen для 2014.exe Decrypted-URLs (5)http://www.w3.org/2000/09/xmldsig#dsa-sha1 http://www.w3.org/2000/09/xmldsig#dsa-sha1Bsxqunfs http://www.w3.org/2000/09/xmldsig#rsa-sha1 http://www.w3.org/2000/09/xmldsig#rsa-sha1+ylm!ghmdr!)+/ylm( http://www.w3.org/2001/10/xml-exc-c14n#kwws9,,ttt-t0-lqd,1333,3:, (PID) Process(6308) Keygen для 2014.exe Decrypted-URLs (8)http://schemas.microsoft.com/2003/10/Serialization/@ http://www.w3.org/2000/09/xmldsig#dsa-sha1 http://www.w3.org/2000/09/xmldsig#dsa-sha1Bsxqunfs http://www.w3.org/2000/09/xmldsig#rsa-sha1 http://www.w3.org/2000/09/xmldsig#rsa-sha1+ylm!ghmdr!)+/ylm( http://www.w3.org/2001/10/xml-exc-c14n#kwws9,,ttt-t0-lqd,1333,3:, http://www.w3.org/2001/XMLSchema http://www.w3.org/2001/XMLSchema-instance | |||||||||||||||
Total events
5 508
Read events
5 441
Write events
64
Delete events
3
Modification events
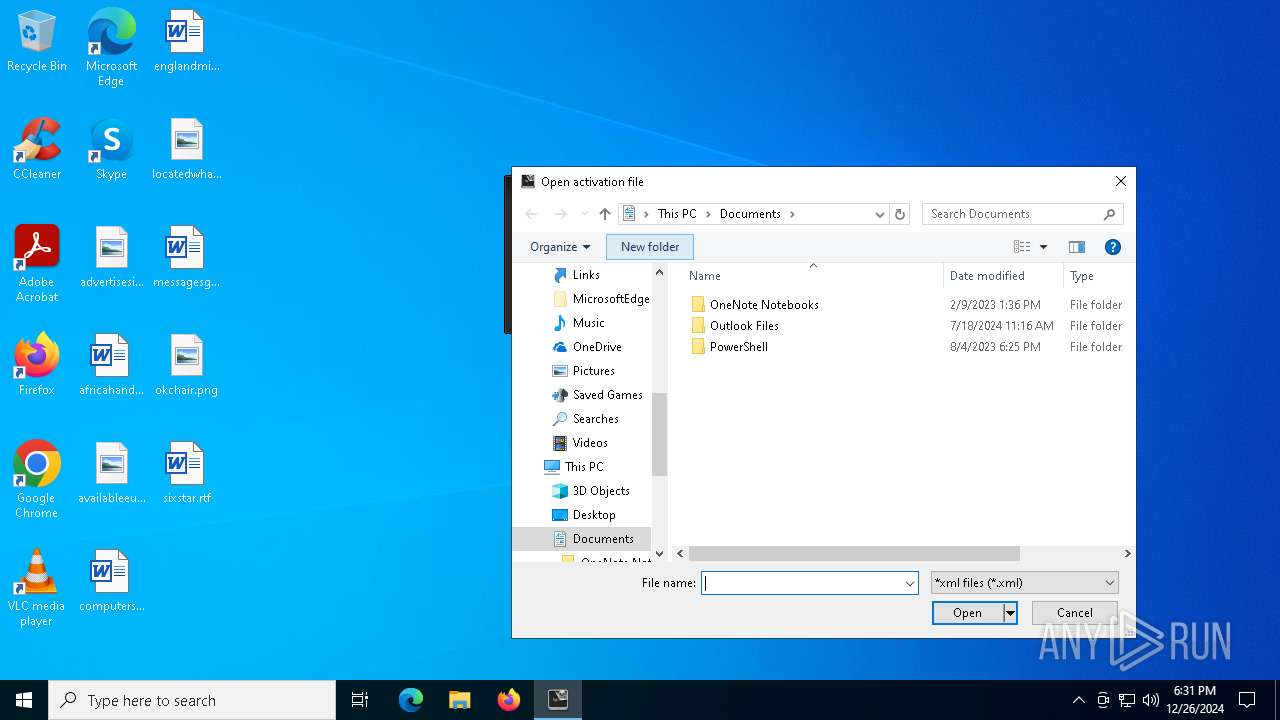
| (PID) Process: | (6308) Keygen для 2014.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (6308) Keygen для 2014.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (6308) Keygen для 2014.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000005000000020000000100000003000000FFFFFFFF | |||
| (PID) Process: | (6308) Keygen для 2014.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (6308) Keygen для 2014.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 105 | |||
| (PID) Process: | (6308) Keygen для 2014.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: E1A06D6700000000 | |||
| (PID) Process: | (6308) Keygen для 2014.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (6308) Keygen для 2014.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (6308) Keygen для 2014.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | FFlags |
Value: | |||
| (PID) Process: | (6308) Keygen для 2014.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2536 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5064 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |