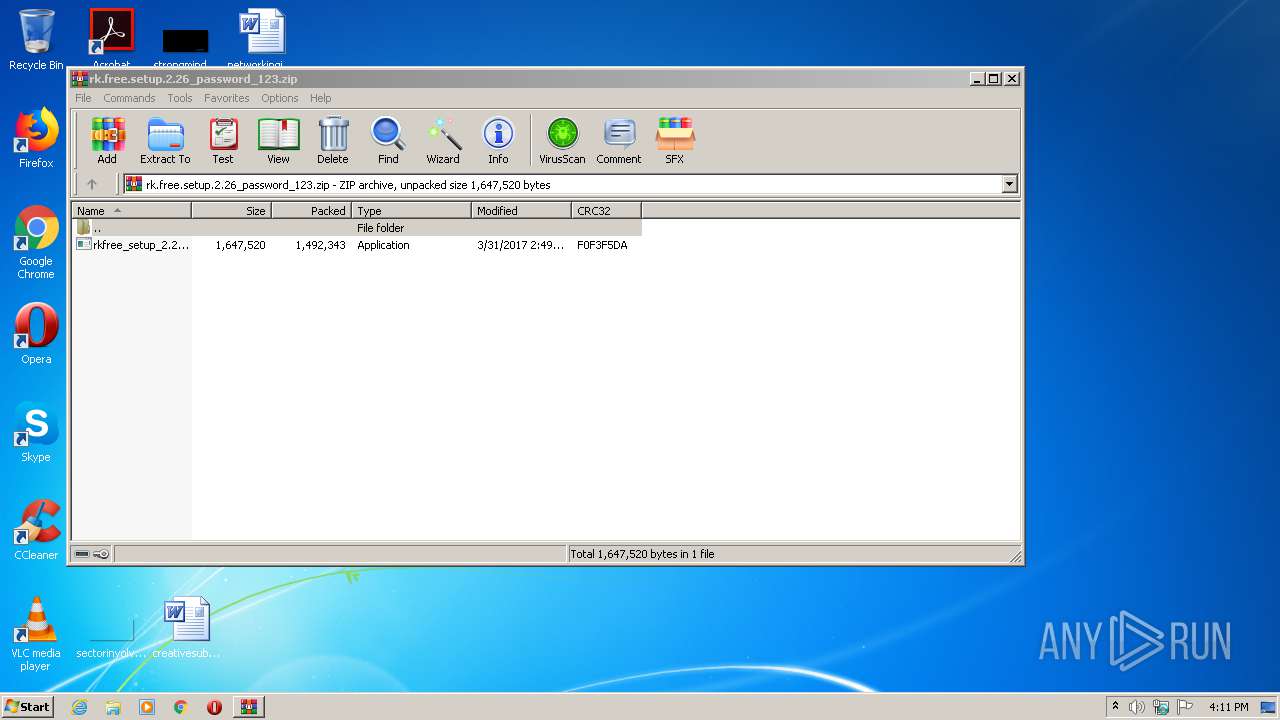
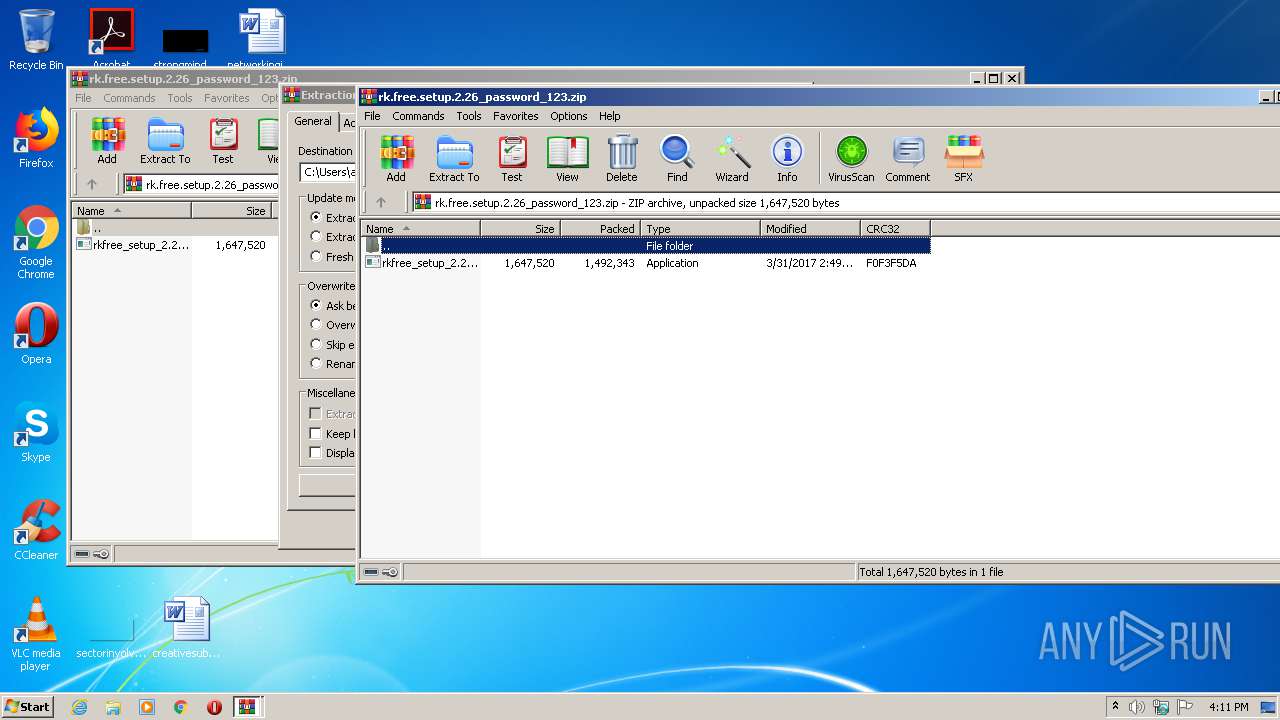
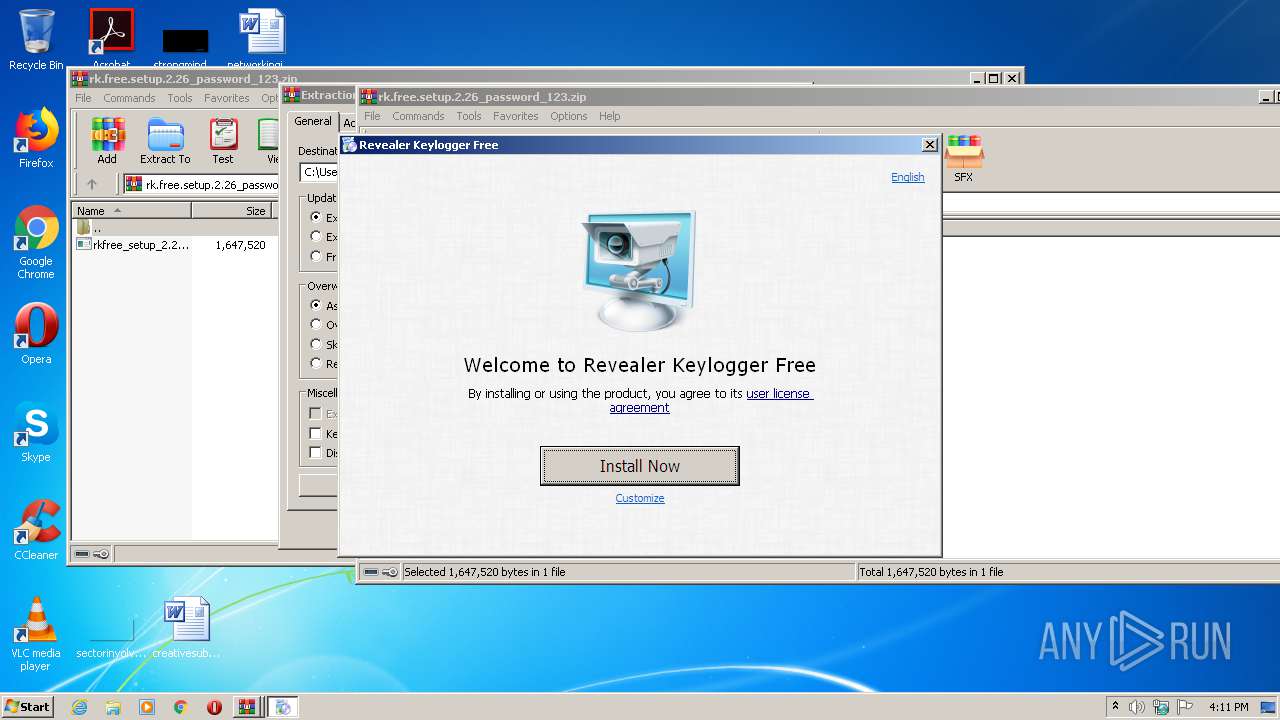
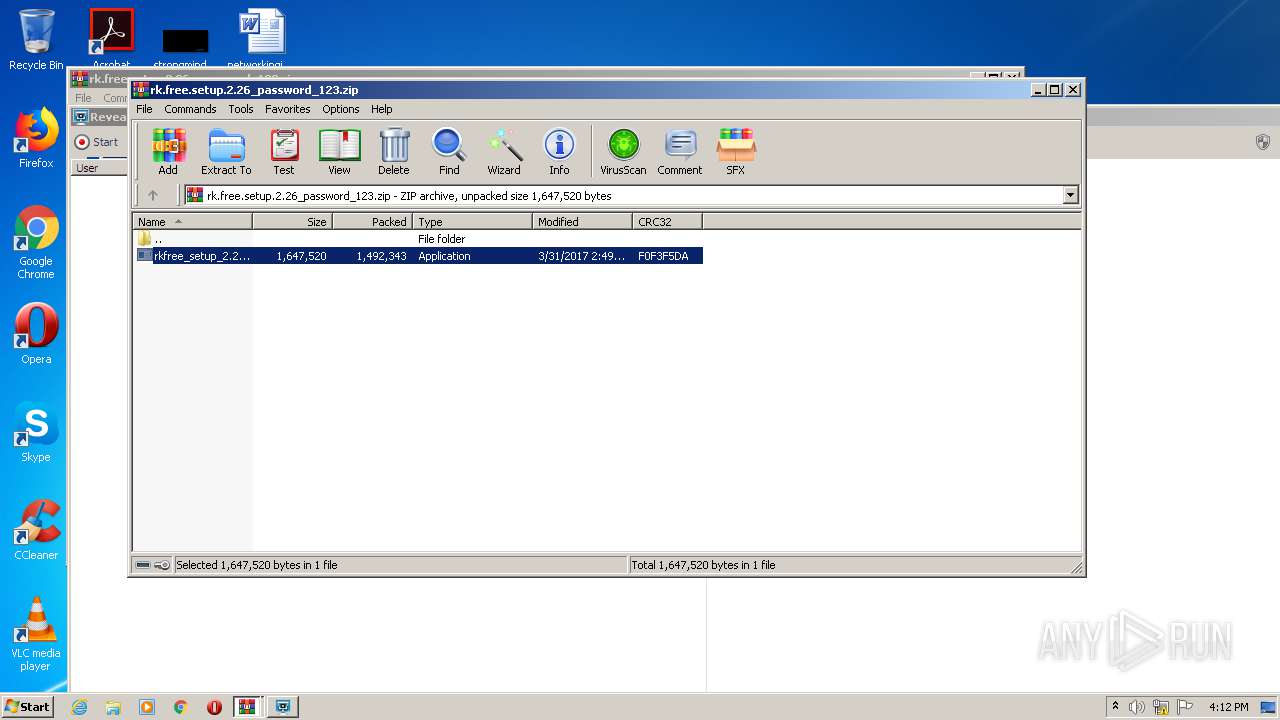
| File name: | rk.free.setup.2.26_password_123.zip |
| Full analysis: | https://app.any.run/tasks/5b3863be-658e-46f4-83ce-926043ab2965 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2020, 15:11:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1A494BD5147147C2A4BE770BE3D5DABE |
| SHA1: | 7D39E51B000A43B27650E3E2B4DEB5EAAB6189FD |
| SHA256: | 9D6C8CB8B03932BCA631CFEEDDDCF5AE7F86B0928BCFD27FD527D502FF7B555E |
| SSDEEP: | 24576:jbjTrSGbxnsXzPmortiFpdP9XAZC6AqGwDcOBJsCA6xr+mQew+0mF5:jbHrSPzPmutiFpx9XEAqZtLA6xlwo5 |
MALICIOUS
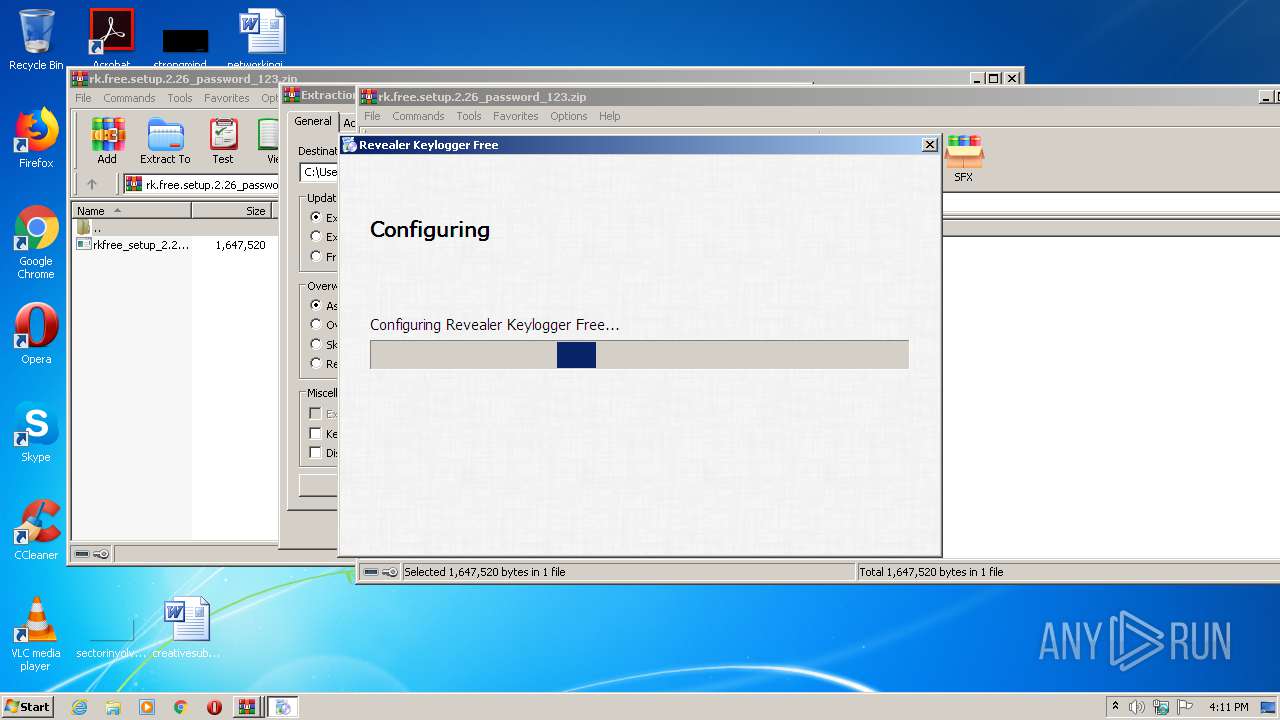
Application was dropped or rewritten from another process
- rkfree_setup_2.26_password_123.exe (PID: 2192)
- rkfree_setup_2.26_password_123.exe (PID: 4040)
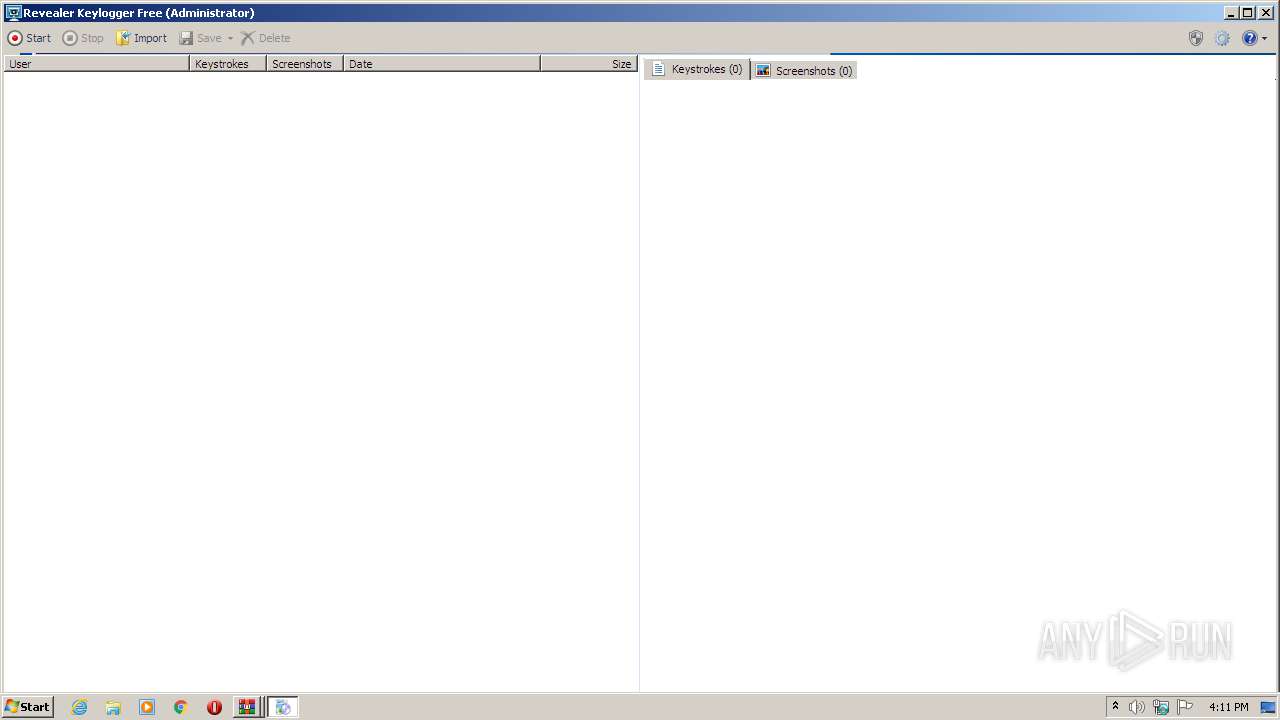
- rvlkl.exe (PID: 2516)
- rvlkl.exe (PID: 4076)
Modifies exclusions in Windows Defender
- rkfree_setup_2.26_password_123.exe (PID: 4040)
Writes to a start menu file
- rkfree_setup_2.26_password_123.exe (PID: 4040)
SUSPICIOUS
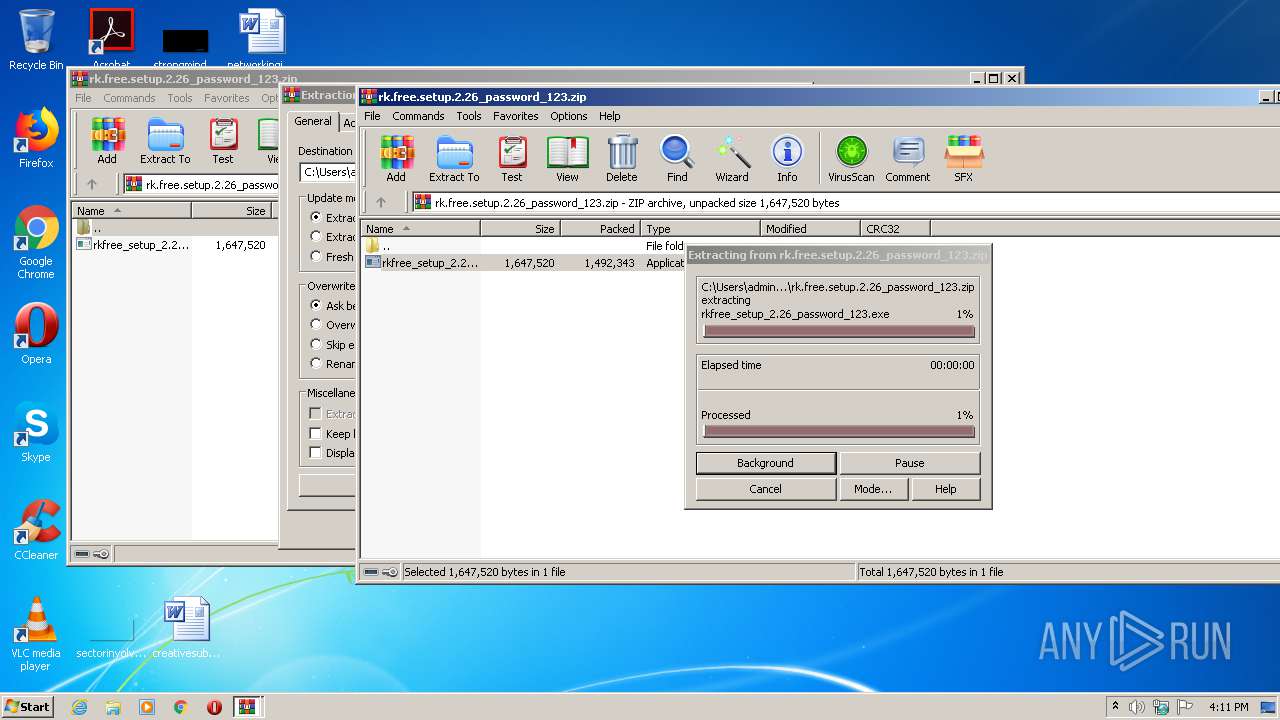
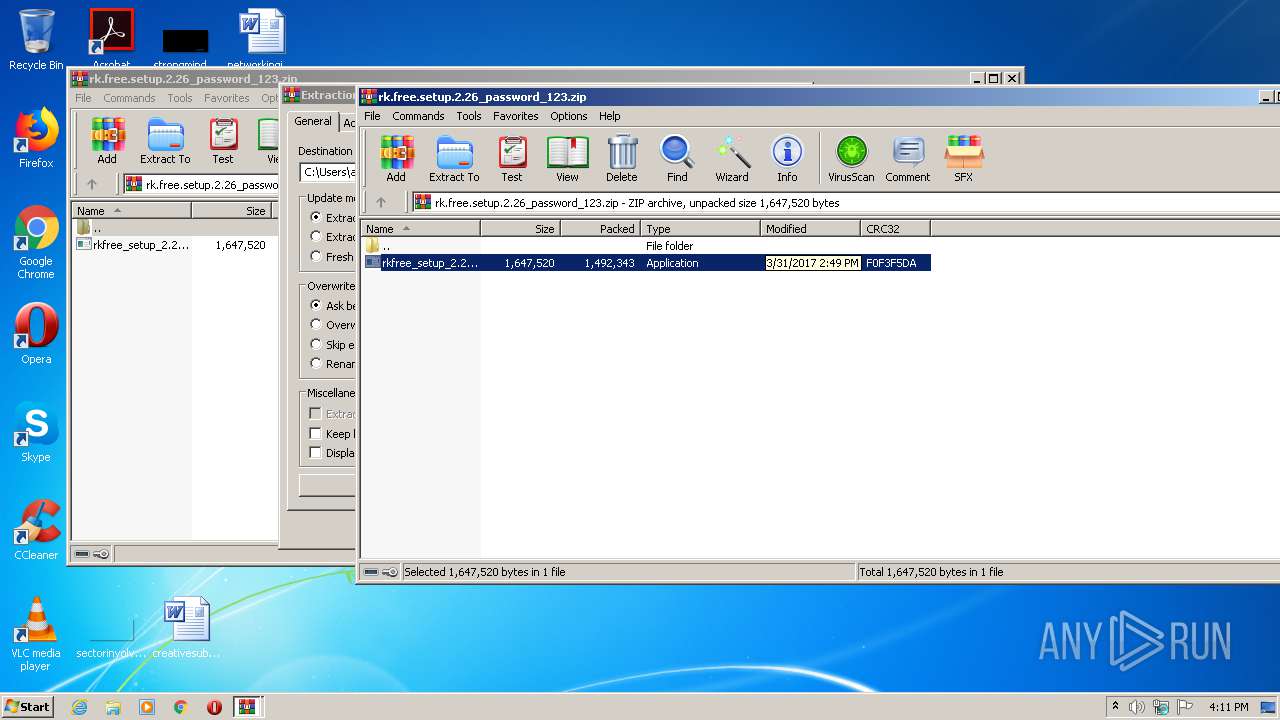
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3416)
- rkfree_setup_2.26_password_123.exe (PID: 4040)
Creates files in the program directory
- rkfree_setup_2.26_password_123.exe (PID: 4040)
- rvlkl.exe (PID: 4076)
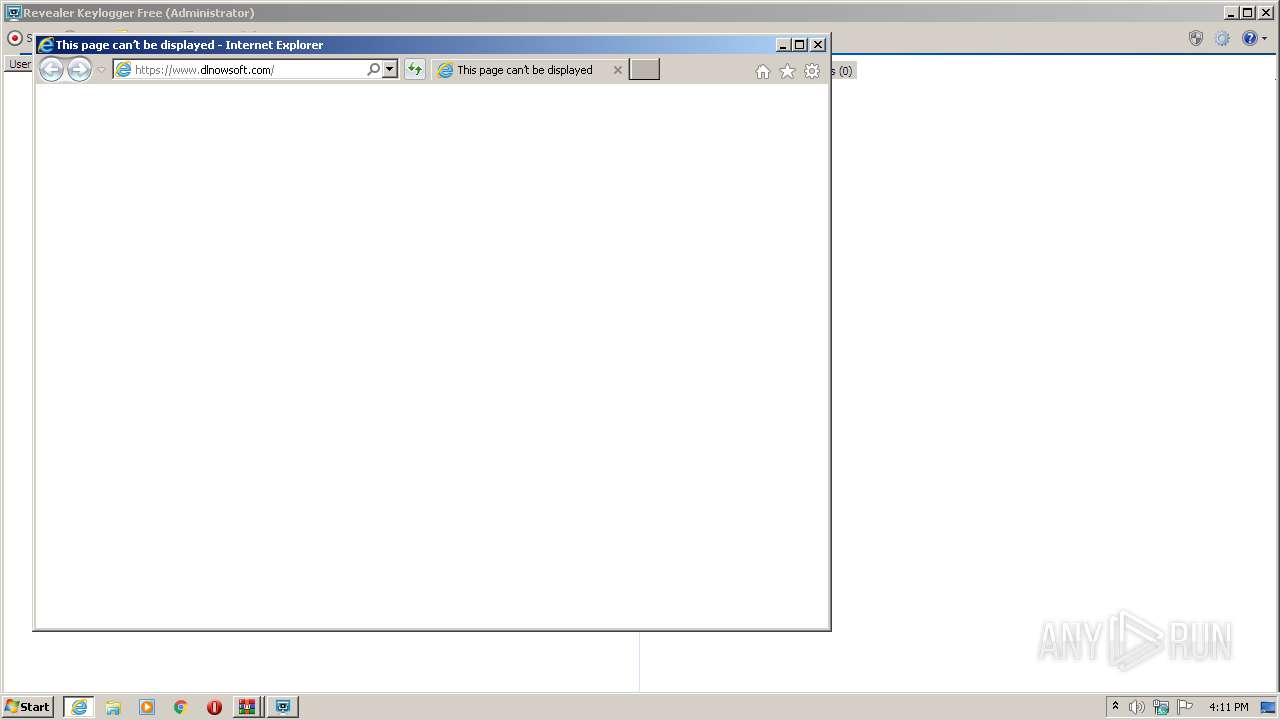
Starts Internet Explorer
- rkfree_setup_2.26_password_123.exe (PID: 4040)
Creates files in the Windows directory
- rkfree_setup_2.26_password_123.exe (PID: 4040)
INFO
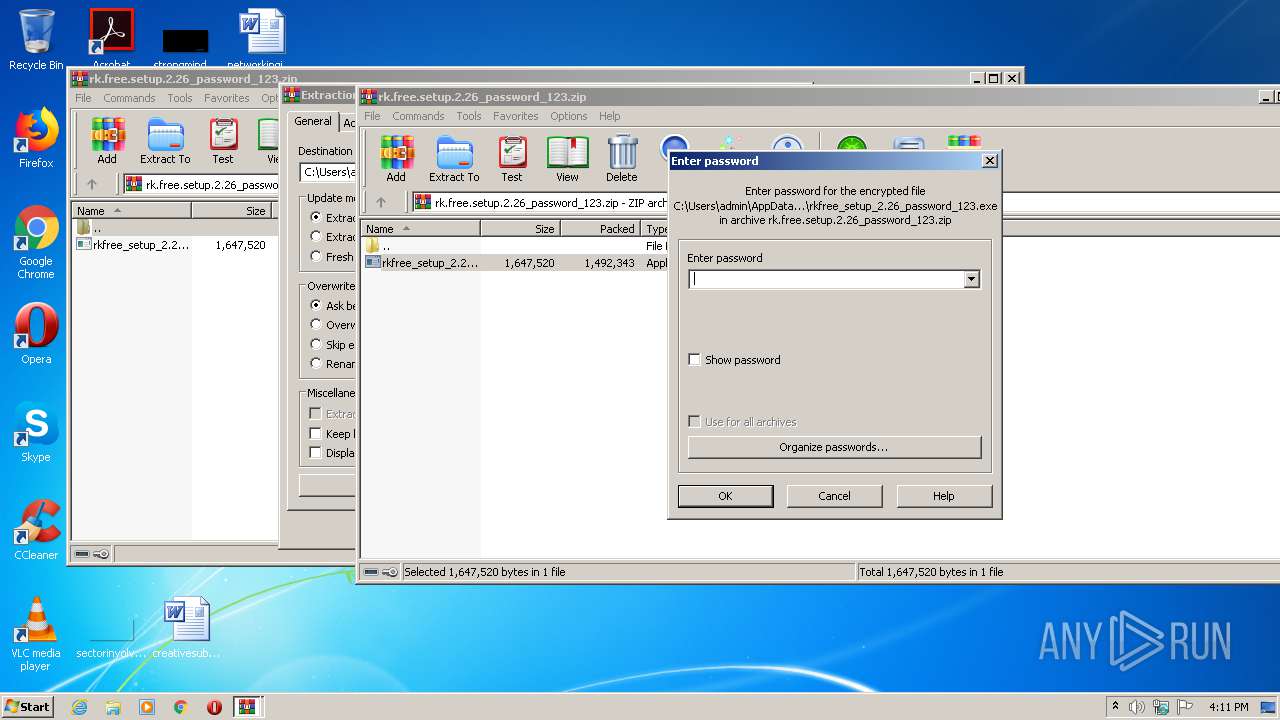
Manual execution by user
- WinRAR.exe (PID: 3416)
Application launched itself
- iexplore.exe (PID: 2236)
Reads Internet Cache Settings
- iexplore.exe (PID: 2236)
- iexplore.exe (PID: 1540)
Changes internet zones settings
- iexplore.exe (PID: 2236)
Reads internet explorer settings
- iexplore.exe (PID: 1540)
Reads settings of System Certificates
- iexplore.exe (PID: 2236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2017:03:31 15:49:24 |
| ZipCRC: | 0xf0f3f5da |
| ZipCompressedSize: | 1492343 |
| ZipUncompressedSize: | 1647520 |
| ZipFileName: | rkfree_setup_2.26_password_123.exe |
Total processes
46
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
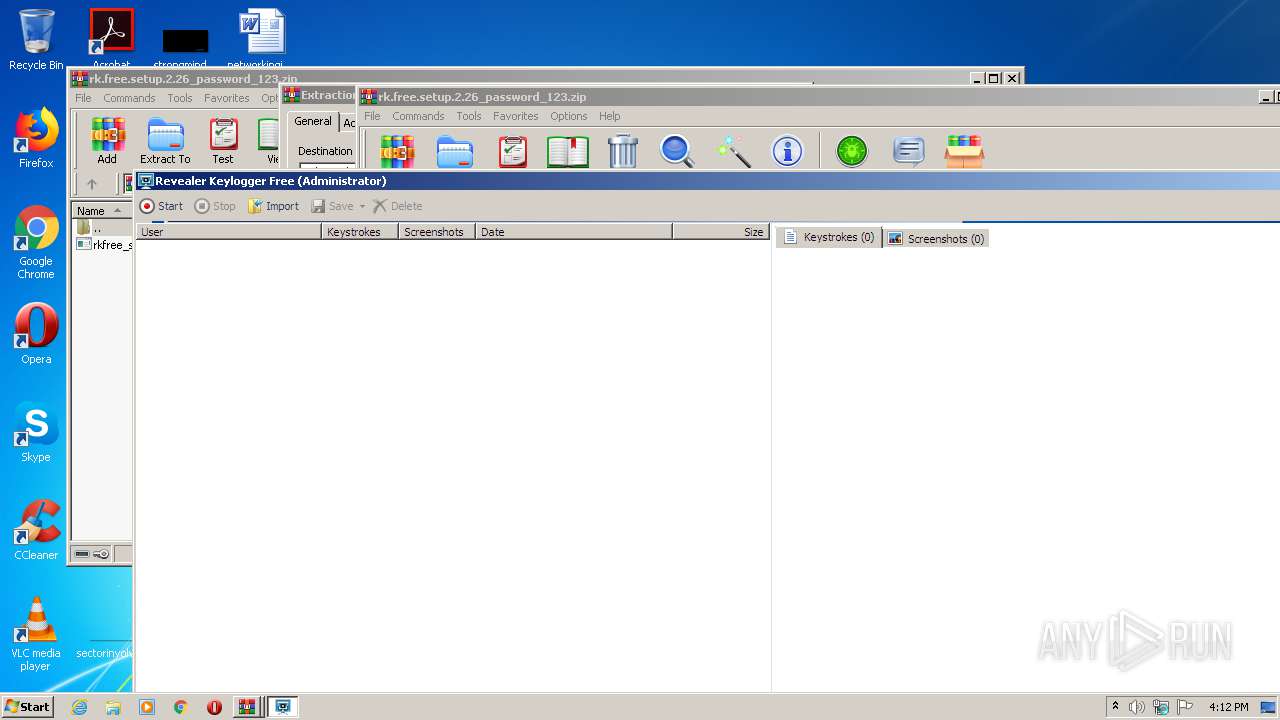
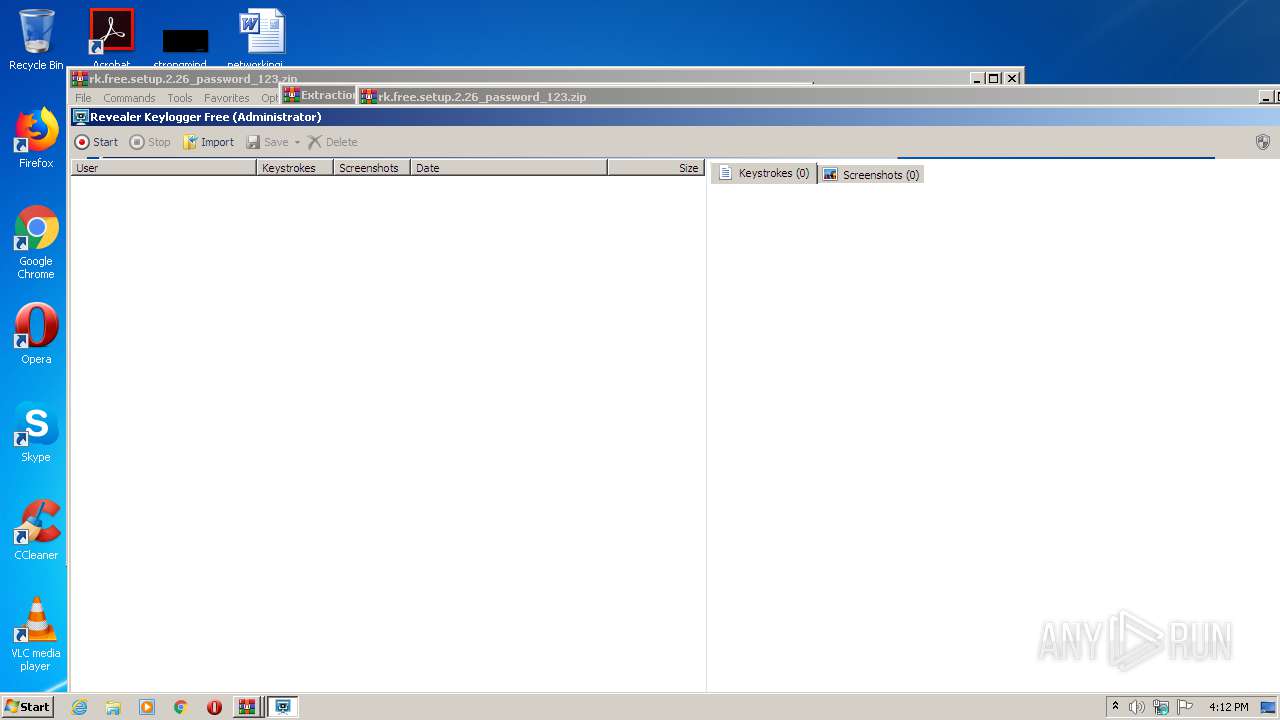
| 1024 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\rk.free.setup.2.26_password_123.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2236 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3416.42218\rkfree_setup_2.26_password_123.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3416.42218\rkfree_setup_2.26_password_123.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.dlnowsoft.com/ | C:\Program Files\Internet Explorer\iexplore.exe | rkfree_setup_2.26_password_123.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
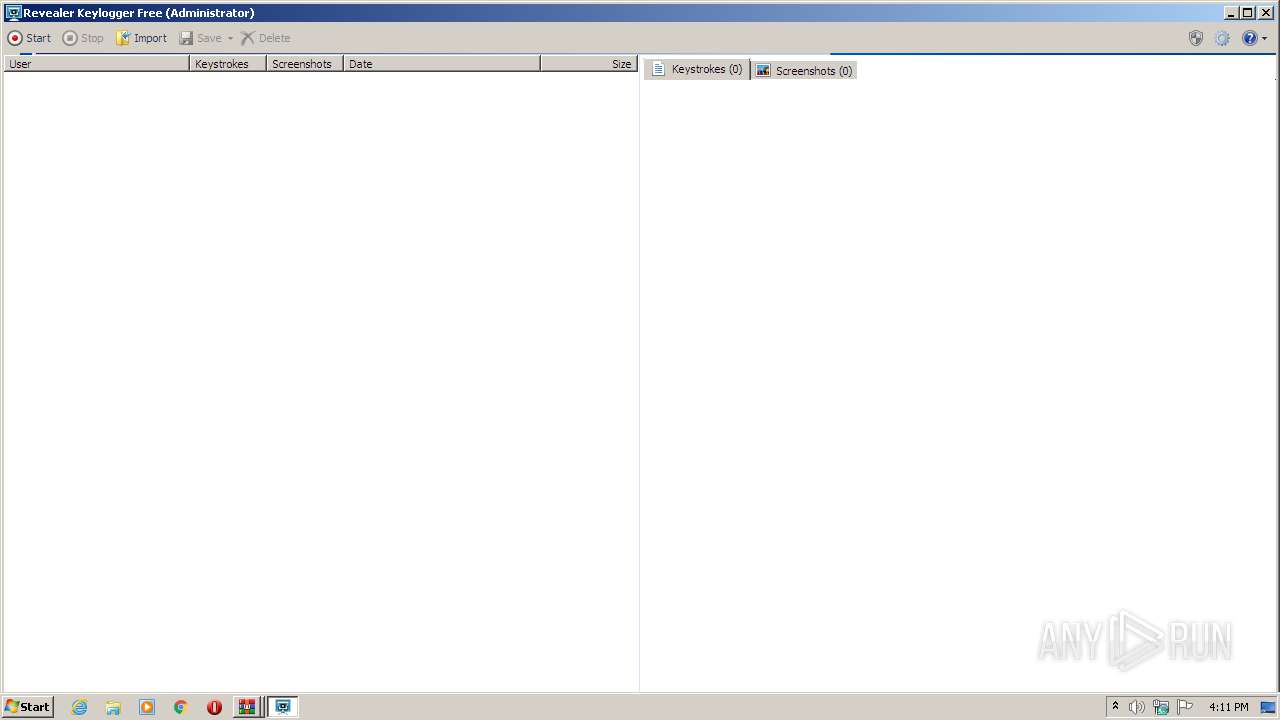
| 2516 | "C:\Windows\system32\rvlkl.exe" | C:\Windows\system32\rvlkl.exe | — | rkfree_setup_2.26_password_123.exe | |||||||||||
User: admin Company: Logixoft Integrity Level: HIGH Description: Revealer Keylogger Free Exit code: 3221226540 Version: 2.2.6.0 Modules
| |||||||||||||||
| 3416 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\rk.free.setup.2.26_password_123.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3416.42218\rkfree_setup_2.26_password_123.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3416.42218\rkfree_setup_2.26_password_123.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4076 | "C:\Windows\system32\rvlkl.exe" | C:\Windows\system32\rvlkl.exe | — | rkfree_setup_2.26_password_123.exe | |||||||||||
User: admin Company: Logixoft Integrity Level: HIGH Description: Revealer Keylogger Free Exit code: 0 Version: 2.2.6.0 Modules
| |||||||||||||||
Total events
1 259
Read events
1 175
Write events
79
Delete events
5
Modification events
| (PID) Process: | (1024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1024) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\rk.free.setup.2.26_password_123.zip | |||
| (PID) Process: | (1024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
6
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | rkfree_setup_2.26_password_123.exe | C:\ProgramData\rvlkl\conf_ | — | |
MD5:— | SHA256:— | |||
| 4040 | rkfree_setup_2.26_password_123.exe | C:\Windows\system32\rvlkl.exe_ | — | |
MD5:— | SHA256:— | |||
| 4076 | rvlkl.exe | C:\ProgramData\rvlkl\conf_ | — | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF38B3423F606115ED.TMP | — | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF698410510C7DF5A9.TMP | — | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB23176BCE338CAF7.TMP | — | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3952C645A6EAC508.TMP | — | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{FB8B84CD-C908-11EA-828F-12A9866C77DE}.dat | — | |
MD5:— | SHA256:— | |||
| 4040 | rkfree_setup_2.26_password_123.exe | C:\ProgramData\rvlkl\conf | binary | |
MD5:— | SHA256:— | |||
| 2236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Last Active\RecoveryStore.{FB8B84D0-C908-11EA-828F-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
3
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1540 | iexplore.exe | 51.38.35.38:443 | www.dlnowsoft.com | — | GB | suspicious |
2236 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dlnowsoft.com |
| malicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1540 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1540 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |