| File name: | INF_allOS_9.4.0.1027.exe |
| Full analysis: | https://app.any.run/tasks/77260517-299d-42bf-92db-48ce9268683b |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2024, 16:31:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9CE528D9FE5554F364CB9926317D726B |
| SHA1: | 9CADC177B080205CCDFD1EE7B45F6B1F73690B2B |
| SHA256: | 9D66885A4D988559C8FF453C1BB8F74D4696D15ACFA6290FCB28F64251FAB183 |
| SSDEEP: | 98304:TUI5hnvaWk9i4U2CTEHfCsyOPHHXnaOJ59Zlkrjnud+M3PgiSAHhVcRa+ThOKlPy:655z |
MALICIOUS
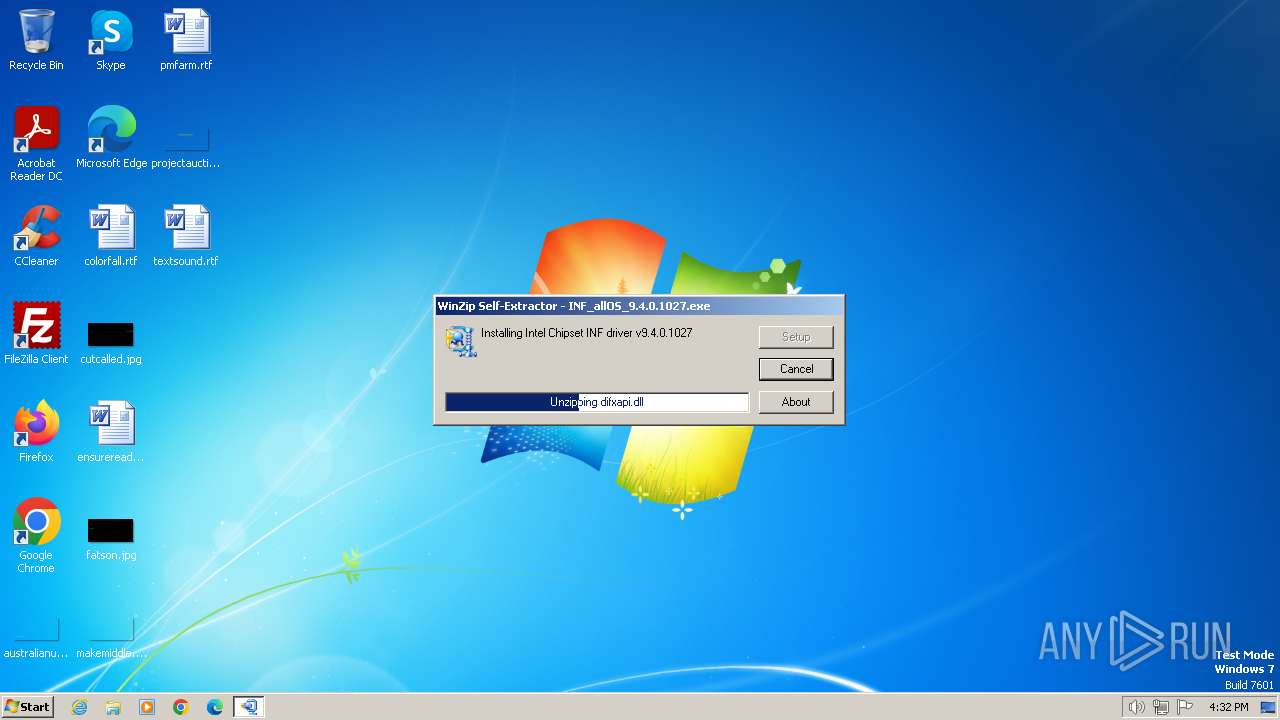
Drops the executable file immediately after the start
- Setup.exe (PID: 3216)
- INF_allOS_9.4.0.1027.exe (PID: 3892)
Creates a writable file in the system directory
- Setup.exe (PID: 3216)
SUSPICIOUS
Executable content was dropped or overwritten
- INF_allOS_9.4.0.1027.exe (PID: 3892)
- Setup.exe (PID: 3216)
Process drops legitimate windows executable
- INF_allOS_9.4.0.1027.exe (PID: 3892)
INFO
Checks supported languages
- INF_allOS_9.4.0.1027.exe (PID: 3892)
- Setup.exe (PID: 3216)
Create files in a temporary directory
- INF_allOS_9.4.0.1027.exe (PID: 3892)
Reads the computer name
- Setup.exe (PID: 3216)
Creates files in the program directory
- Setup.exe (PID: 3216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (32.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (28.5) |
| .exe | | | Winzip Win32 self-extracting archive (generic) (23.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:11:02 20:24:15+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 77824 |
| InitializedDataSize: | 65536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaf1e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Users\admin\AppData\Local\Temp\INF_allOS_9.4.0.1027.exe" | C:\Users\admin\AppData\Local\Temp\INF_allOS_9.4.0.1027.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
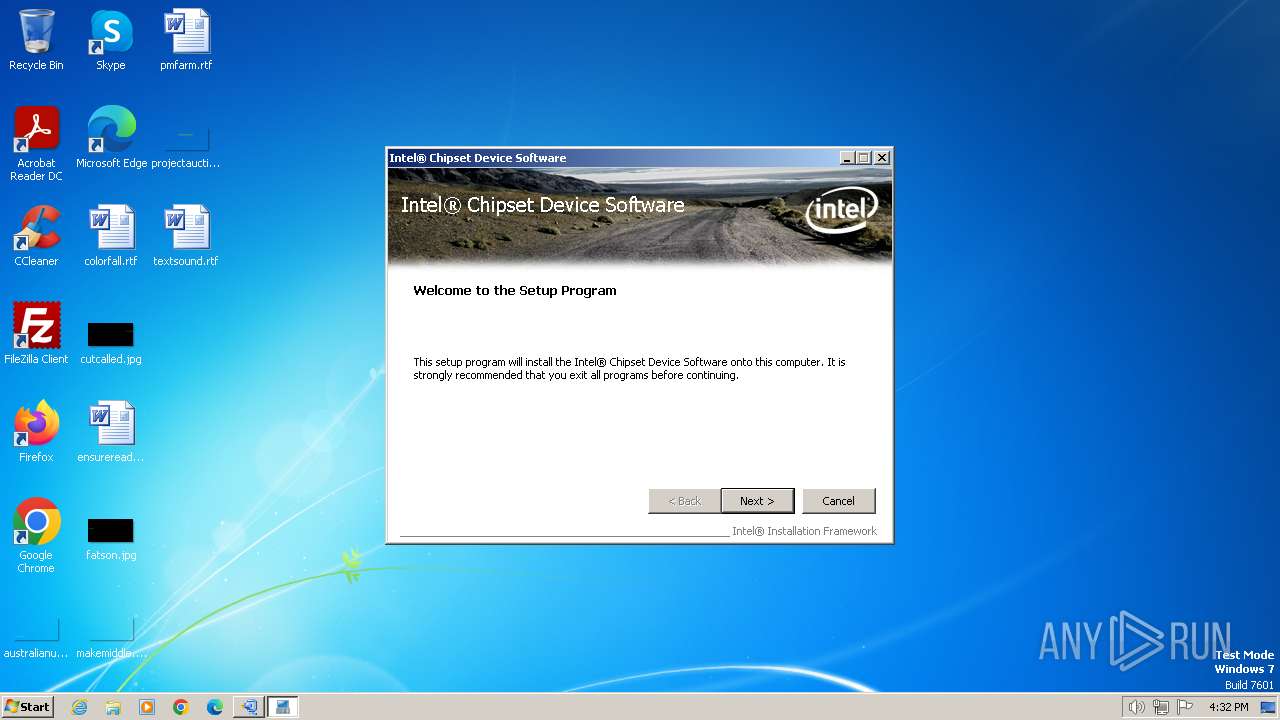
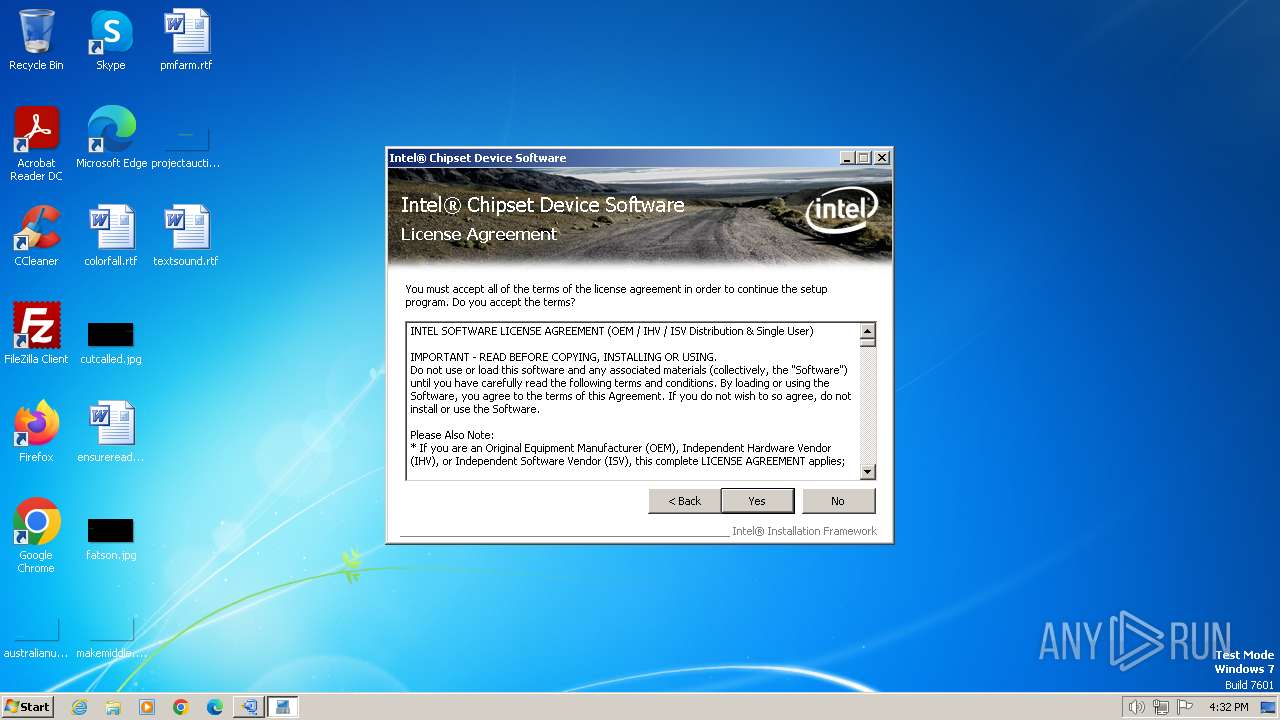
| 3216 | ".\Setup.exe" | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\Setup.exe | INF_allOS_9.4.0.1027.exe | ||||||||||||
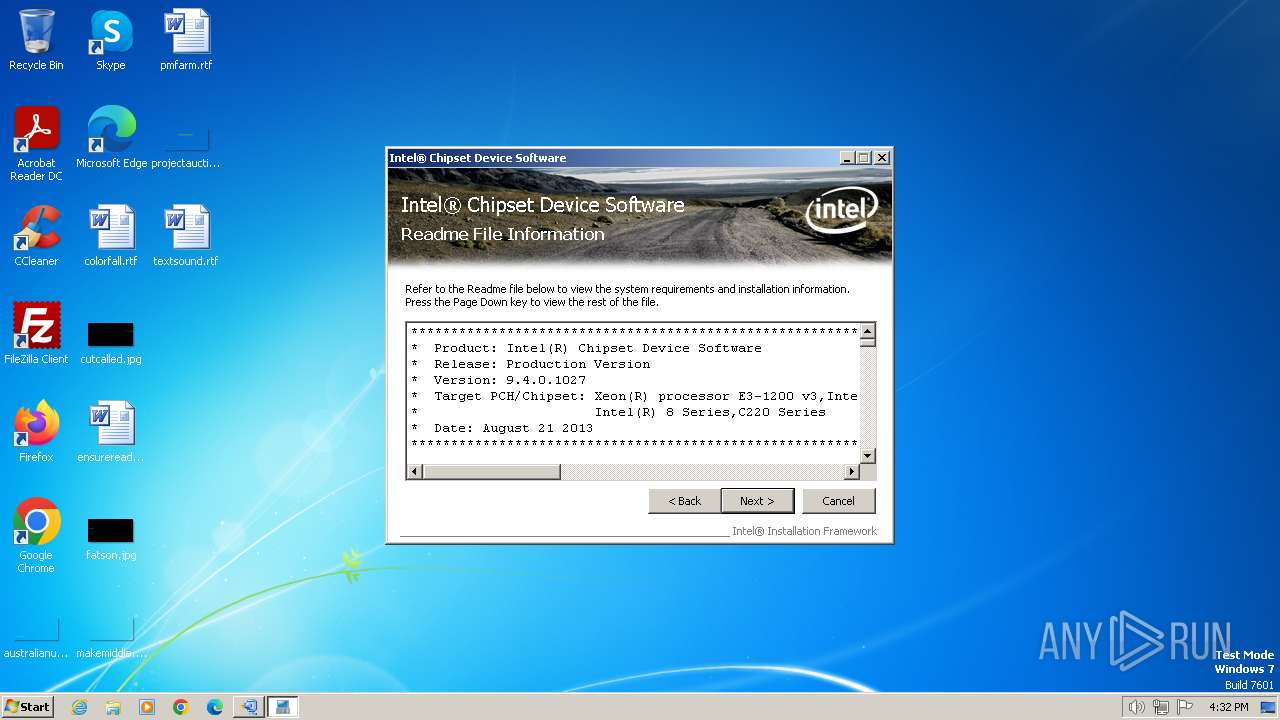
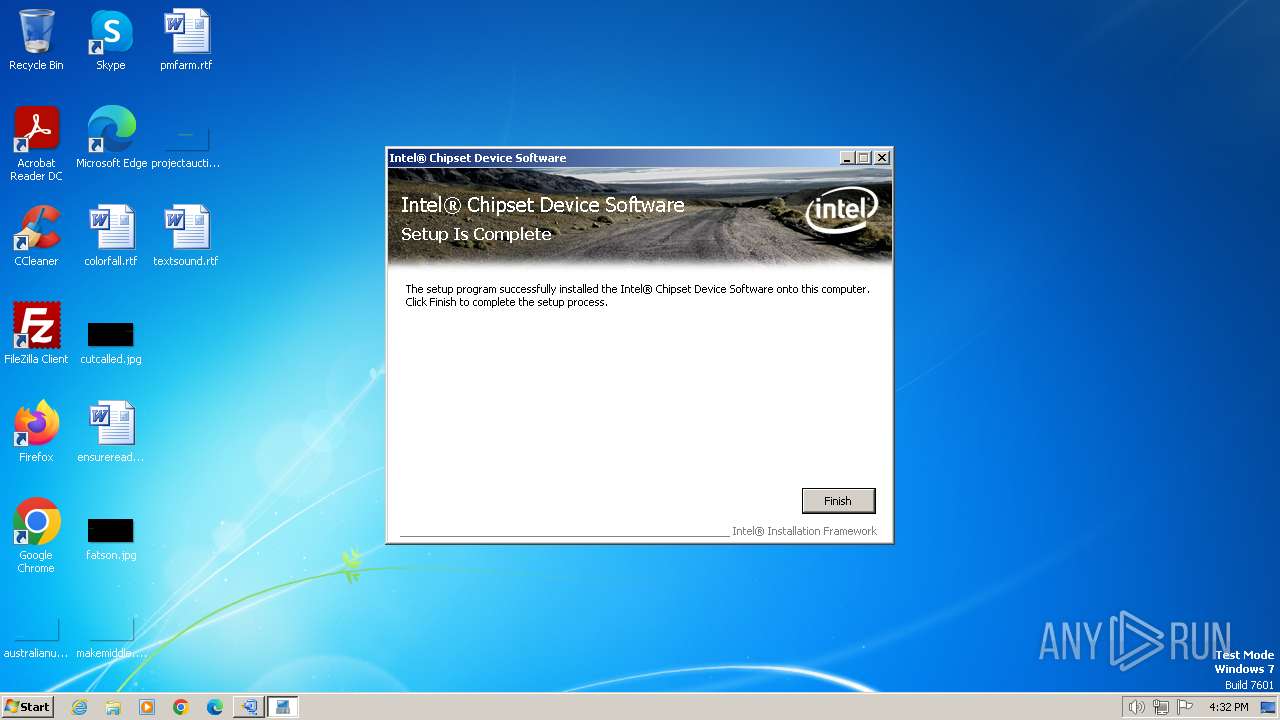
User: admin Company: Intel Corporation Integrity Level: HIGH Description: Intel® Chipset Device Software installer Exit code: 0 Version: 1, 1, 54, 0 Modules
| |||||||||||||||
| 3892 | "C:\Users\admin\AppData\Local\Temp\INF_allOS_9.4.0.1027.exe" | C:\Users\admin\AppData\Local\Temp\INF_allOS_9.4.0.1027.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
361
Read events
350
Write events
11
Delete events
0
Modification events
| (PID) Process: | (3216) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Intel\Infinst\Uninstall |
| Operation: | write | Name: | copyfile0 |
Value: destination=C:\Windows\system32\CSVer.dll | |||
| (PID) Process: | (3216) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Intel\Infinst\Uninstall |
| Operation: | write | Name: | keys |
Value: copyfile0 | |||
| (PID) Process: | (3216) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Intel\Infinst\Uninstall |
| Operation: | write | Name: | registry0 |
Value: keyroot=HKLM | |||
| (PID) Process: | (3216) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Intel\Infinst |
| Operation: | write | Name: | Language |
Value: ENU | |||
| (PID) Process: | (3216) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Intel\Infinst\Uninstall |
| Operation: | write | Name: | registry1 |
Value: keyroot=HKLM | |||
| (PID) Process: | (3216) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Intel\Infinst |
| Operation: | write | Name: | RefCount |
Value: 1 | |||
| (PID) Process: | (3216) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Intel\Infinst |
| Operation: | write | Name: | Version |
Value: 9.4.0.1027 | |||
| (PID) Process: | (3216) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Intel\Infinst |
| Operation: | write | Name: | Reboot |
Value: no | |||
| (PID) Process: | (3216) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Intel\Infinst |
| Operation: | write | Name: | Install |
Value: success | |||
Executable files
33
Suspicious files
386
Text files
35
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | INF_allOS_9.4.0.1027.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\All\2008s4el.cat | binary | |
MD5:366E6AF60721D868CA6D6A65233847E6 | SHA256:3A997E463B1515DB9FA84A82BC524E02E83F334B2172C78D025867BB10F9C6E8 | |||
| 3892 | INF_allOS_9.4.0.1027.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\All\5000XZVP.inf | binary | |
MD5:F594205EAA48374730D217FF55B9B32E | SHA256:449E899FDAF74936EA0F14A78915EF71FD10B59F6A3DFF5992952F4640412FE5 | |||
| 3892 | INF_allOS_9.4.0.1027.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\All\865.cat | binary | |
MD5:77EAB48924367BA439F32249892A6811 | SHA256:FE0B176FEDEC43686BE9341C5824DFD4E8BF6EF44ED8DEF01CAB82B517662806 | |||
| 3892 | INF_allOS_9.4.0.1027.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\All\5000xzvp.cat | binary | |
MD5:61DEADF6CD5CCE77414F62A8196F3D7C | SHA256:5A459F85E89EAD11EECF7B9DA074A872722A3DB7335DEB74F4E64C75806D6443 | |||
| 3892 | INF_allOS_9.4.0.1027.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\All\2008s4el.inf | binary | |
MD5:003C29AF525F1BE1816E92F5E2132AE0 | SHA256:FEC58FF9E2883B2688537551AE9C75E1C91FD2E510EFE45EAD71F90A72E04300 | |||
| 3892 | INF_allOS_9.4.0.1027.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\All\5400.cat | binary | |
MD5:A63FDED6F3287360E7D18B33A309F865 | SHA256:85A2219CB766024CA9DBBB7D7F3867327F05AA425D4CB61FB8CA238EE89374D8 | |||
| 3892 | INF_allOS_9.4.0.1027.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\All\852.cat | binary | |
MD5:85A9D54F2F89439BE6244DE1E2520B6B | SHA256:C5451E787B300A56BF3E2ADA08C2098AA3A36331B90B16AF7B641E3F4EC414C6 | |||
| 3892 | INF_allOS_9.4.0.1027.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\All\865.inf | binary | |
MD5:D30CD9AC9AFB716F0D0BF40E3BBCA20E | SHA256:0FCBD4041E20843E9E163F764533CA170B313656027460692079A2314A55D1F1 | |||
| 3892 | INF_allOS_9.4.0.1027.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\All\915.inf | binary | |
MD5:3671422D8F87A3E66CEECEBA3B069572 | SHA256:1E7BBEC8E35E3F2644AE11DEEC01BA498A0880BFE8DBB0F8BE63F307FA3B52C0 | |||
| 3892 | INF_allOS_9.4.0.1027.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\All\915M.inf | binary | |
MD5:577BC8DF93F38E9F5B4A2DB2763E58C5 | SHA256:7E69406AB406C7083BC079F0BE46F1110A821A804116FC3AAC98F0664A4677FB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |