| File name: | 9d3a78f72dbd7351a999d6fd6f60b0c6ba79bc4279a347fd590af94a0224afad |
| Full analysis: | https://app.any.run/tasks/3a5cf748-59d5-4e72-a1e7-fe4a47d5b485 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 06:06:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 9B49FEC7E03C33277F188A2819B8D726 |
| SHA1: | A7B6B4A0ECBEAB9075C3E36EC2586CE8DEBBBC4F |
| SHA256: | 9D3A78F72DBD7351A999D6FD6F60B0C6BA79BC4279A347FD590AF94A0224AFAD |
| SSDEEP: | 1536:mOC0FvV4OguHxjhpA4Bm7uW0vSUsghQevBFkutIbgTuFqKRr0aF5frleGhd9TfBi:mwV4OgSzBmh04eZFkz3Rr0gwGj9Tf8 |
MALICIOUS
Writes to a start menu file
- iexplore.exe (PID: 3620)
Application was injected by another process
- windanr.exe (PID: 2140)
- explorer.exe (PID: 252)
- dwm.exe (PID: 2016)
Runs injected code in another process
- iexplore.exe (PID: 3812)
SUSPICIOUS
Starts Internet Explorer
- 9d3a78f72dbd7351a999d6fd6f60b0c6ba79bc4279a347fd590af94a0224afad.exe (PID: 2916)
Creates files in the program directory
- iexplore.exe (PID: 3620)
INFO
Creates files in the user directory
- iexplore.exe (PID: 3620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:08:23 07:00:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.4 |
| CodeSize: | 77824 |
| InitializedDataSize: | 32768 |
| UninitializedDataSize: | 237568 |
| EntryPoint: | 0x4d240 |
| OSVersion: | 5 |
| ImageVersion: | 7.2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Aug-2007 05:00:50 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000088 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 23-Aug-2007 05:00:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0003A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0003B000 | 0x00013000 | 0x00012400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97255 |
.rsrc | 0x0004E000 | 0x00020000 | 0x00008000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.99873 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.5652 | 174 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
2 | 7.55756 | 552 | UNKNOWN | Russian - Russia | RT_DIALOG |
3 | 4.34854 | 488 | UNKNOWN | Russian - Russia | RT_ICON |
4 | 3.94387 | 296 | UNKNOWN | Russian - Russia | RT_ICON |
5 | 5.10902 | 3752 | UNKNOWN | Russian - Russia | RT_ICON |
6 | 5.31319 | 2216 | UNKNOWN | Russian - Russia | RT_ICON |
7 | 5.28829 | 1736 | UNKNOWN | Russian - Russia | RT_ICON |
8 | 4.937 | 1384 | UNKNOWN | Russian - Russia | RT_ICON |
9 | 4.03069 | 9640 | UNKNOWN | Russian - Russia | RT_ICON |
10 | 4.43482 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
Imports
KERNEL32.DLL |
user32.dll |
Total processes
33
Monitored processes
6
Malicious processes
4
Suspicious processes
0
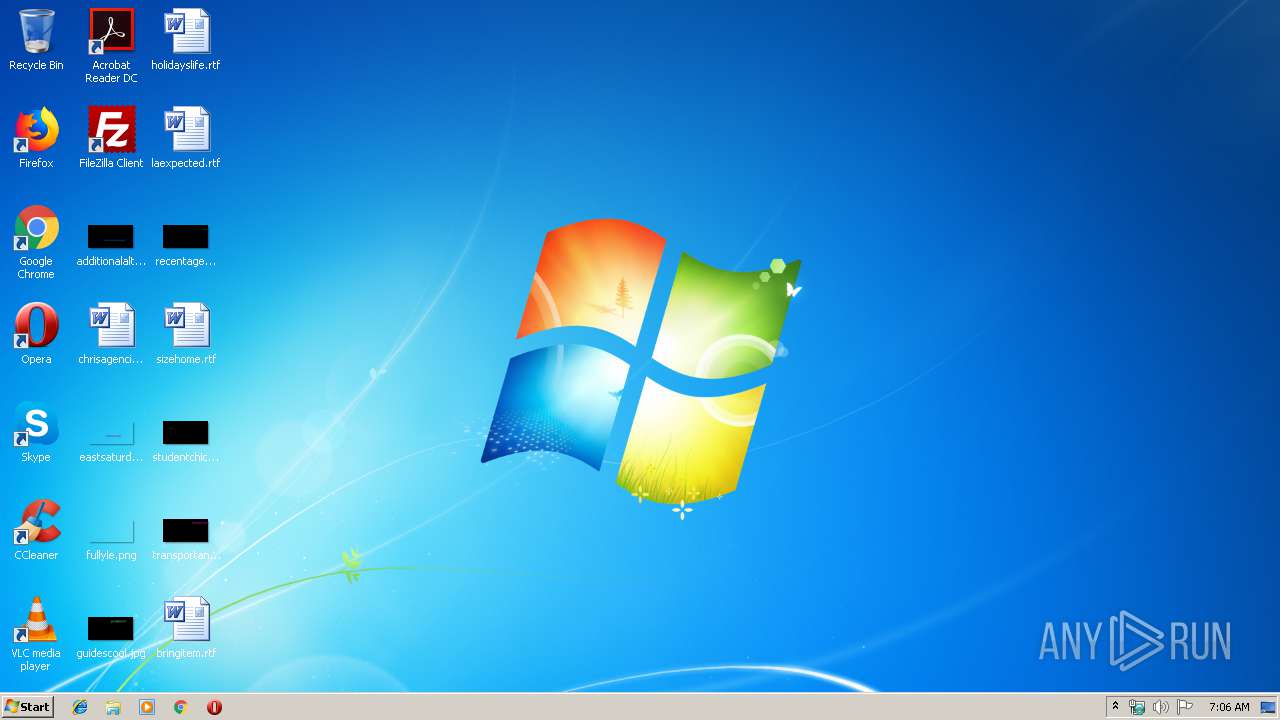
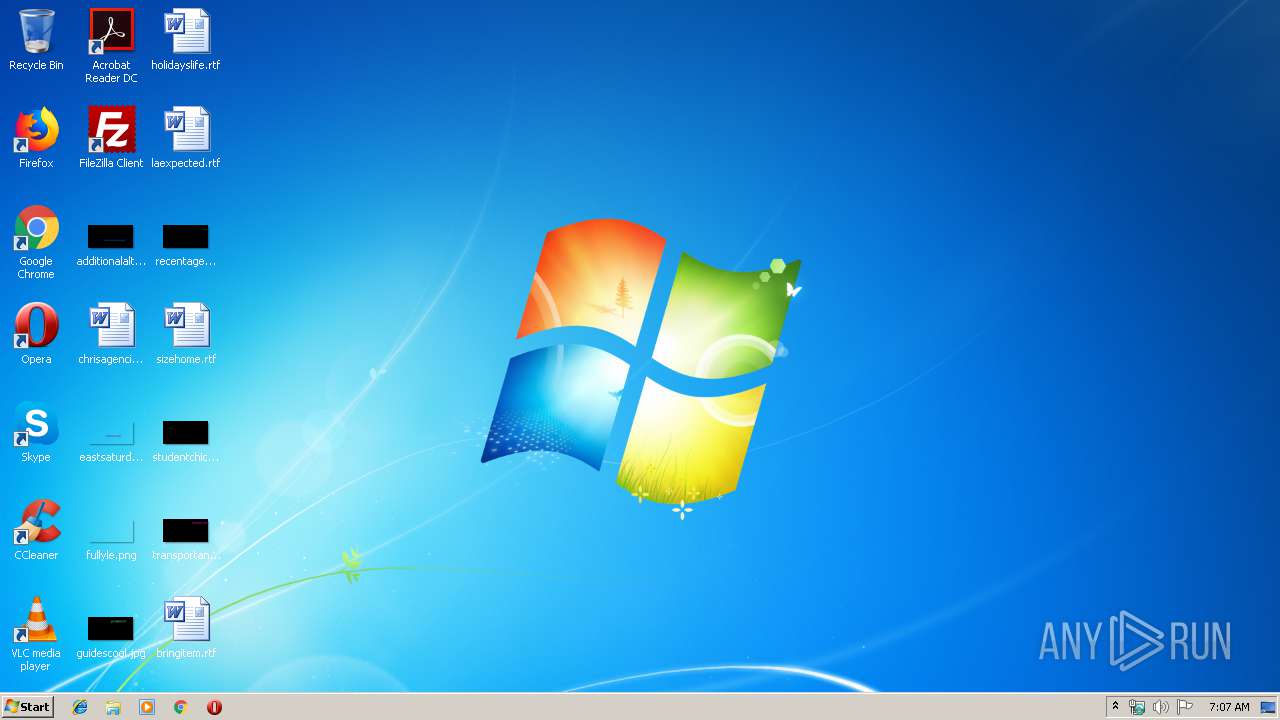
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2016 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2140 | "windanr.exe" | C:\Windows\system32\windanr.exe | qemu-ga.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2916 | "C:\Users\admin\AppData\Local\Temp\9d3a78f72dbd7351a999d6fd6f60b0c6ba79bc4279a347fd590af94a0224afad.exe" | C:\Users\admin\AppData\Local\Temp\9d3a78f72dbd7351a999d6fd6f60b0c6ba79bc4279a347fd590af94a0224afad.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3620 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | 9d3a78f72dbd7351a999d6fd6f60b0c6ba79bc4279a347fd590af94a0224afad.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3812 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | 9d3a78f72dbd7351a999d6fd6f60b0c6ba79bc4279a347fd590af94a0224afad.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
879
Read events
865
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2140) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2140) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2140) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2140) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2140) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2140) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2140) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2140) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2140) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2140) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
75
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3620 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\enbfqohg.exe | — | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Berime.htm | html | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LeesMij.htm | html | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leggimi.htm | html | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Liesmich.htm | html | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Lisezmoi.htm | html | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LueMinut.htm | html | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Llegiu-me.htm | html | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LeiaMe.htm | html | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Benioku.htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3620 | iexplore.exe | 216.58.206.14:80 | google.com | Google Inc. | US | whitelisted |
3620 | iexplore.exe | 82.112.184.197:447 | supnewdmn.com | Vysokie tehnologii Limited Liability Company | RU | malicious |
3620 | iexplore.exe | 13.107.21.200:80 | bing.com | Microsoft Corporation | US | whitelisted |
3620 | iexplore.exe | 130.211.22.95:447 | tvrstrynyvwstrtve.com | Google Inc. | US | whitelisted |
3620 | iexplore.exe | 98.138.219.232:80 | yahoo.com | Yahoo | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
supnewdmn.com |
| malicious |
bing.com |
| whitelisted |
tvrstrynyvwstrtve.com |
| malicious |
yahoo.com |
| whitelisted |