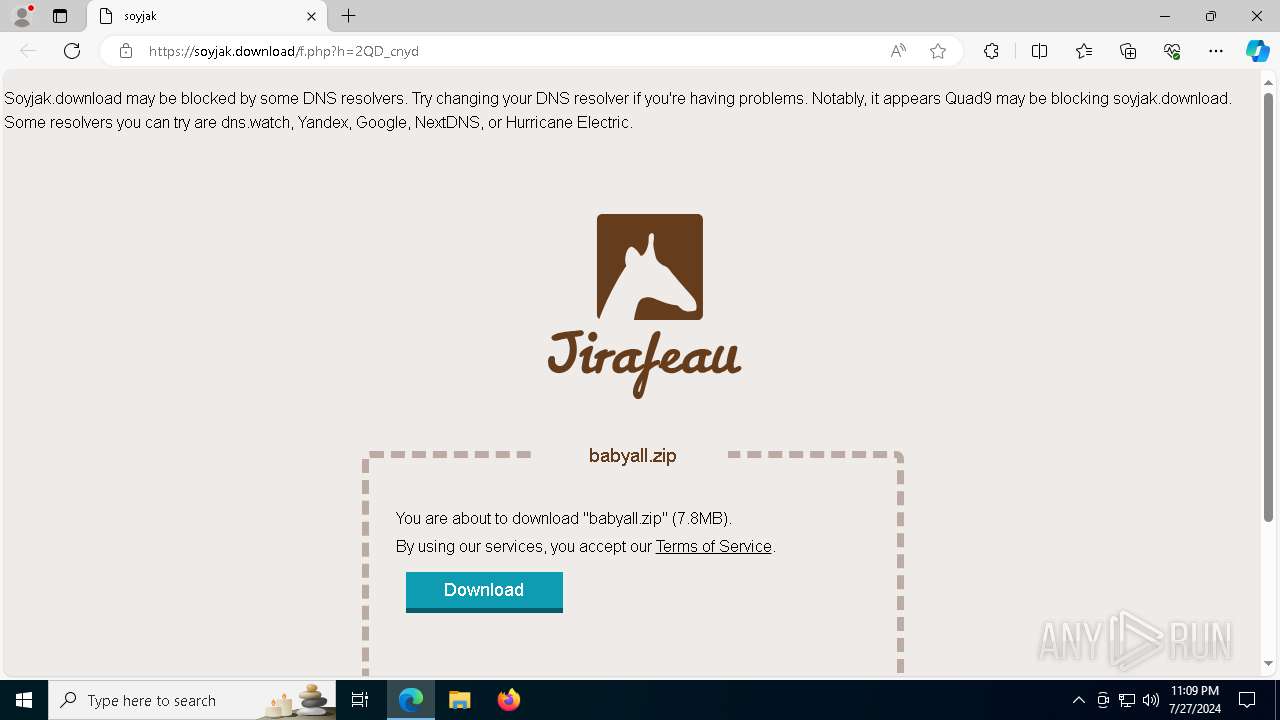
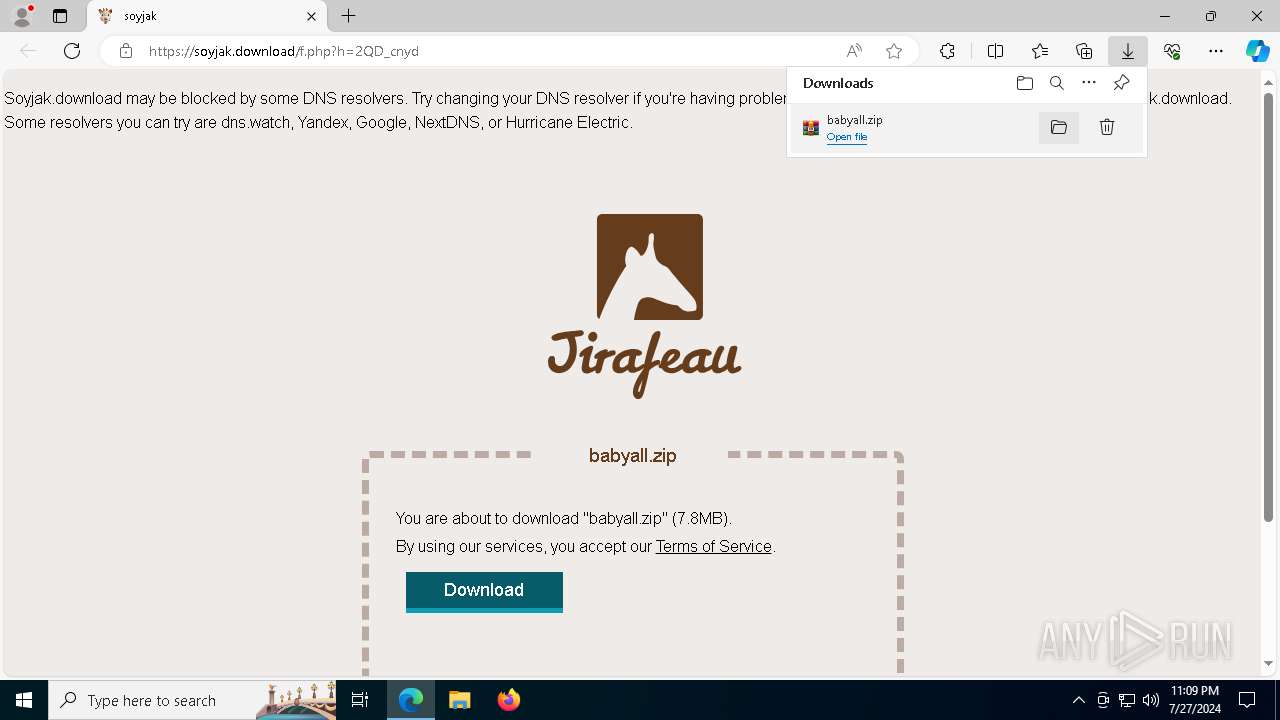
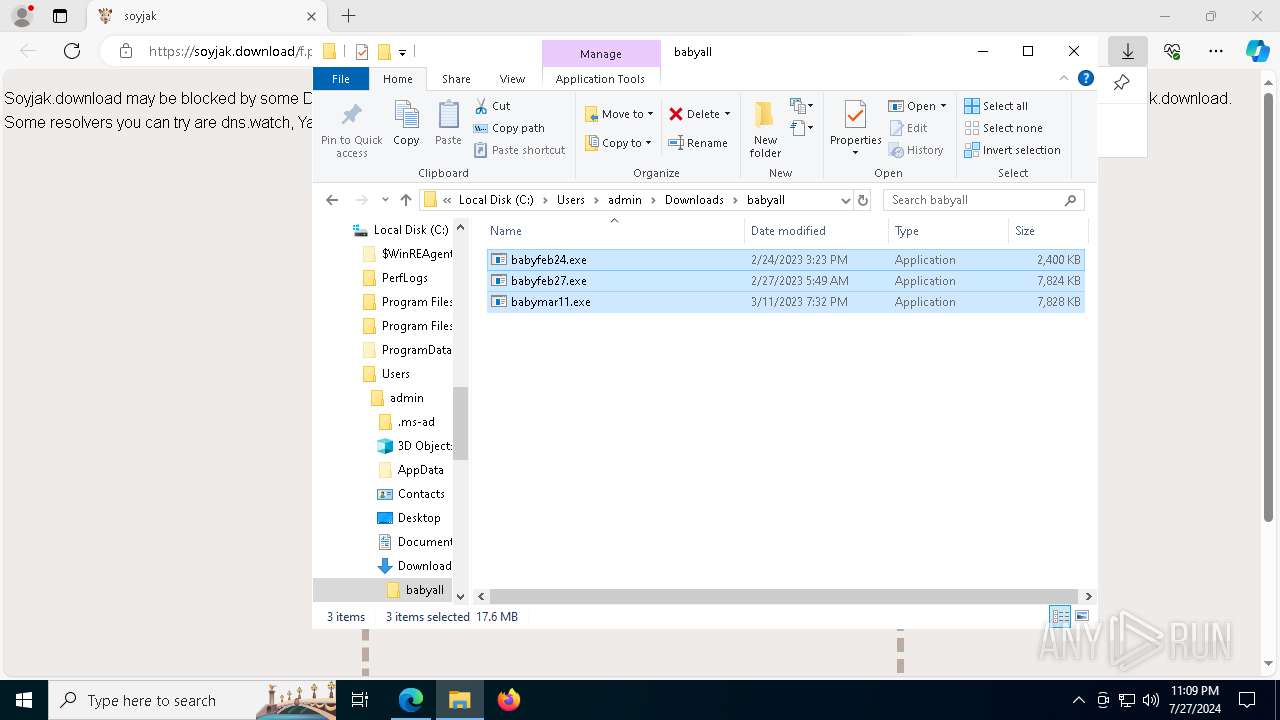
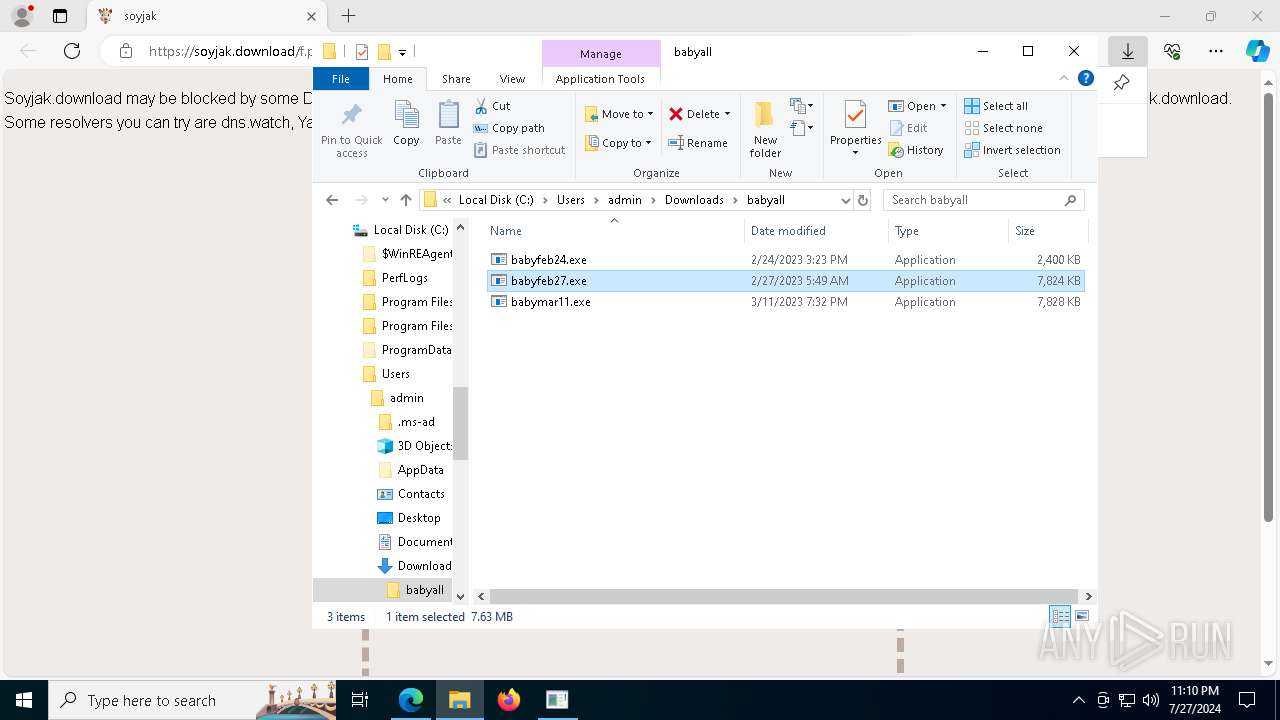
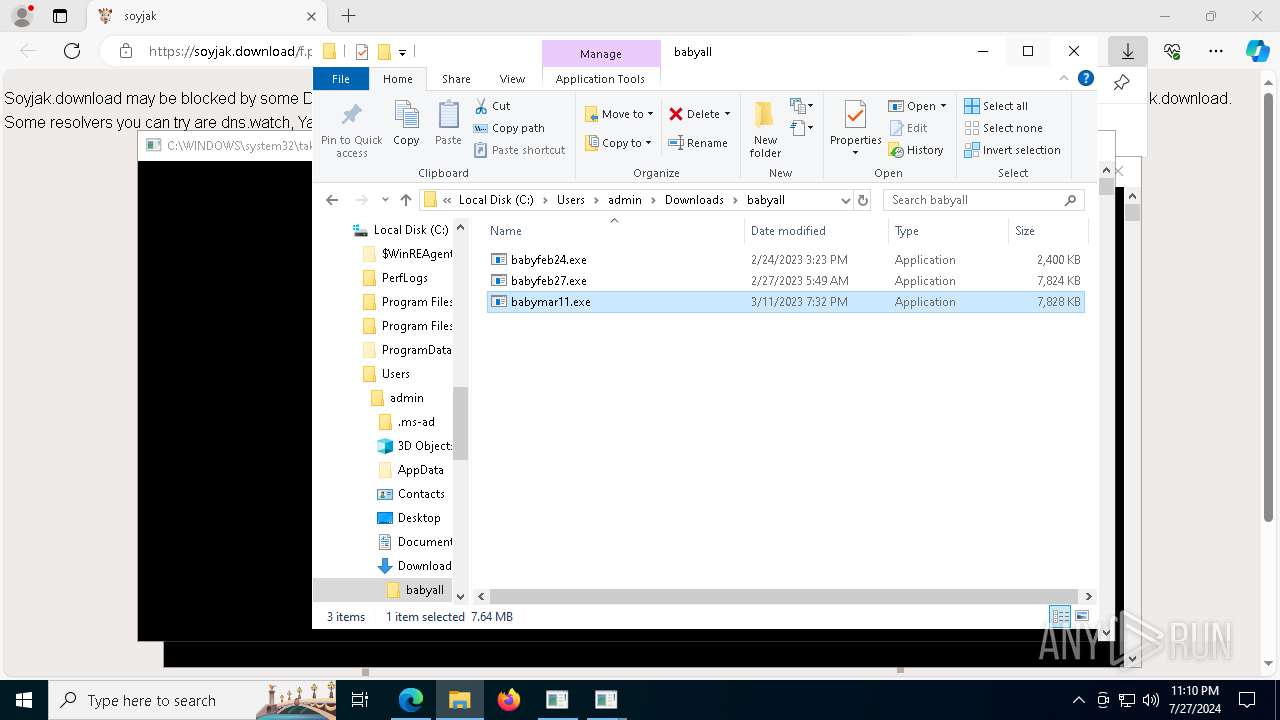
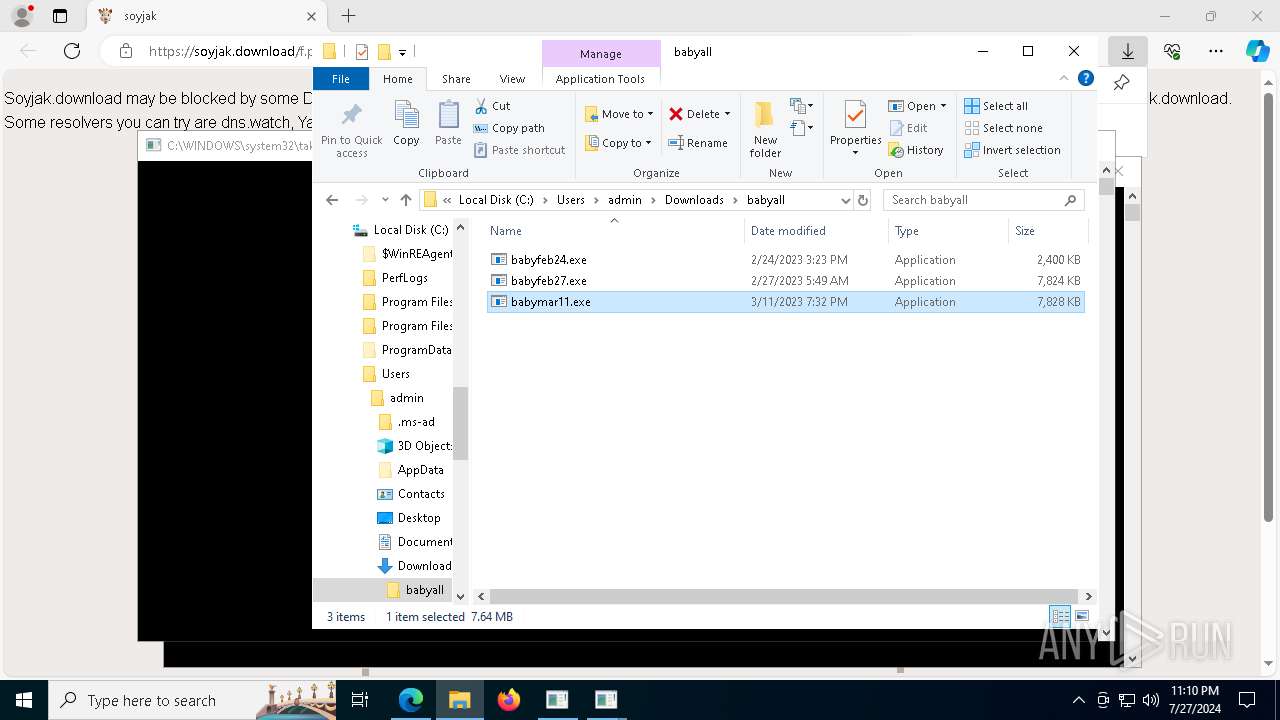
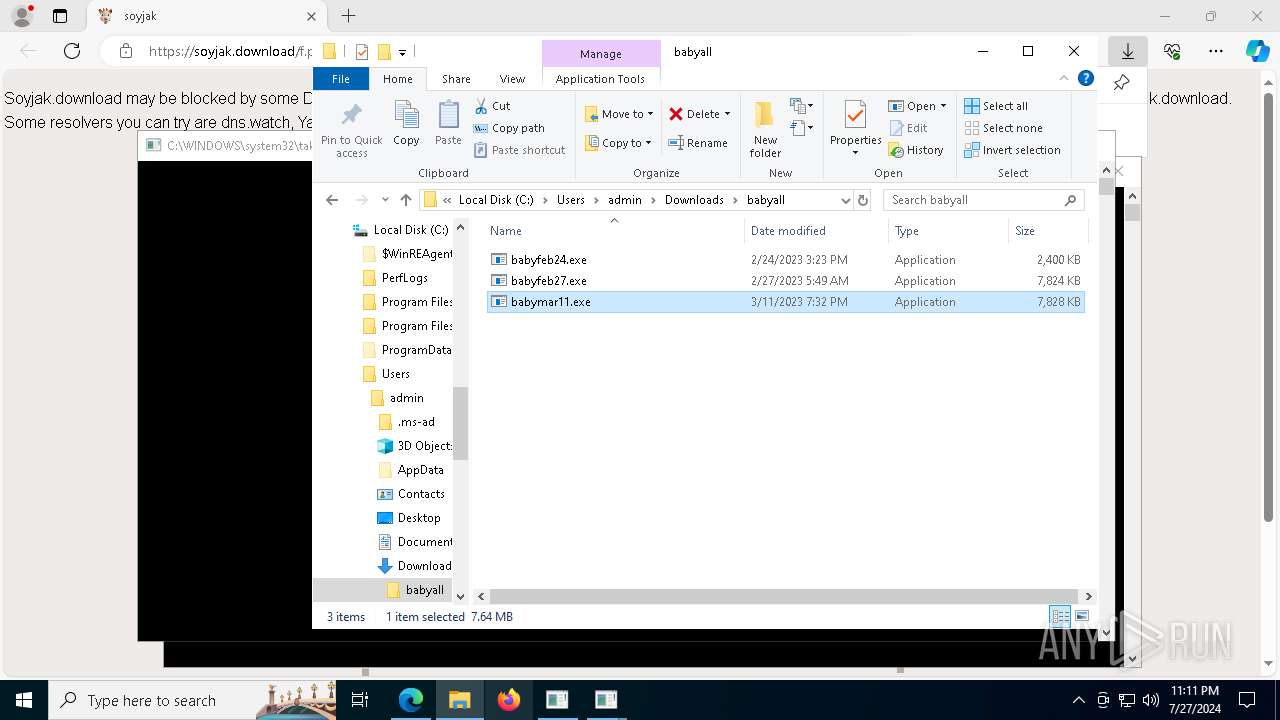
| URL: | https://soyjak.download/f.php?h=2QD_cnyd |
| Full analysis: | https://app.any.run/tasks/c9f773a5-faf1-481d-8996-0451cb99fa34 |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2024, 23:09:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | CE47D897D98C71D7AF958066FE15BE0F |
| SHA1: | 7F9EDAF68F62F28061516B270B2481FCD514A65B |
| SHA256: | 9D34F09E75222F87E6988CDE3844C32349FC6E9ACE98A225E38509D23C98E50A |
| SSDEEP: | 3:N8H+EOL8jXA1c:2eEc1c |
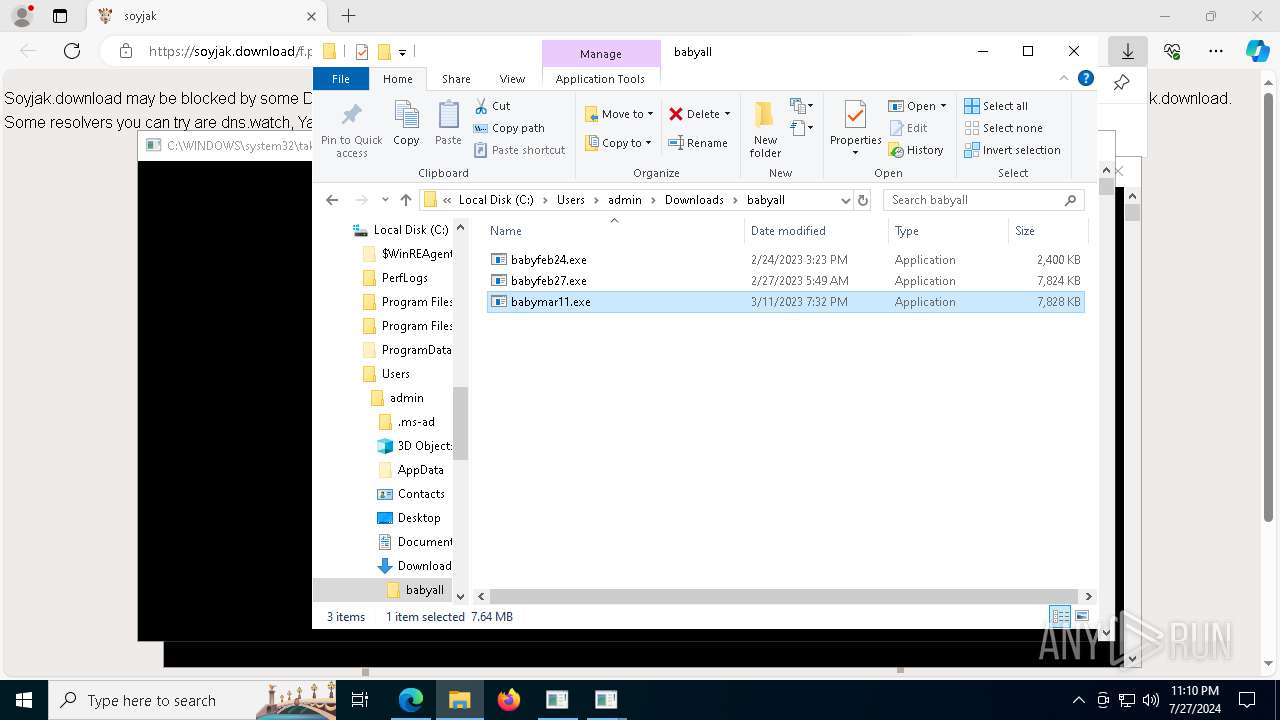
MALICIOUS
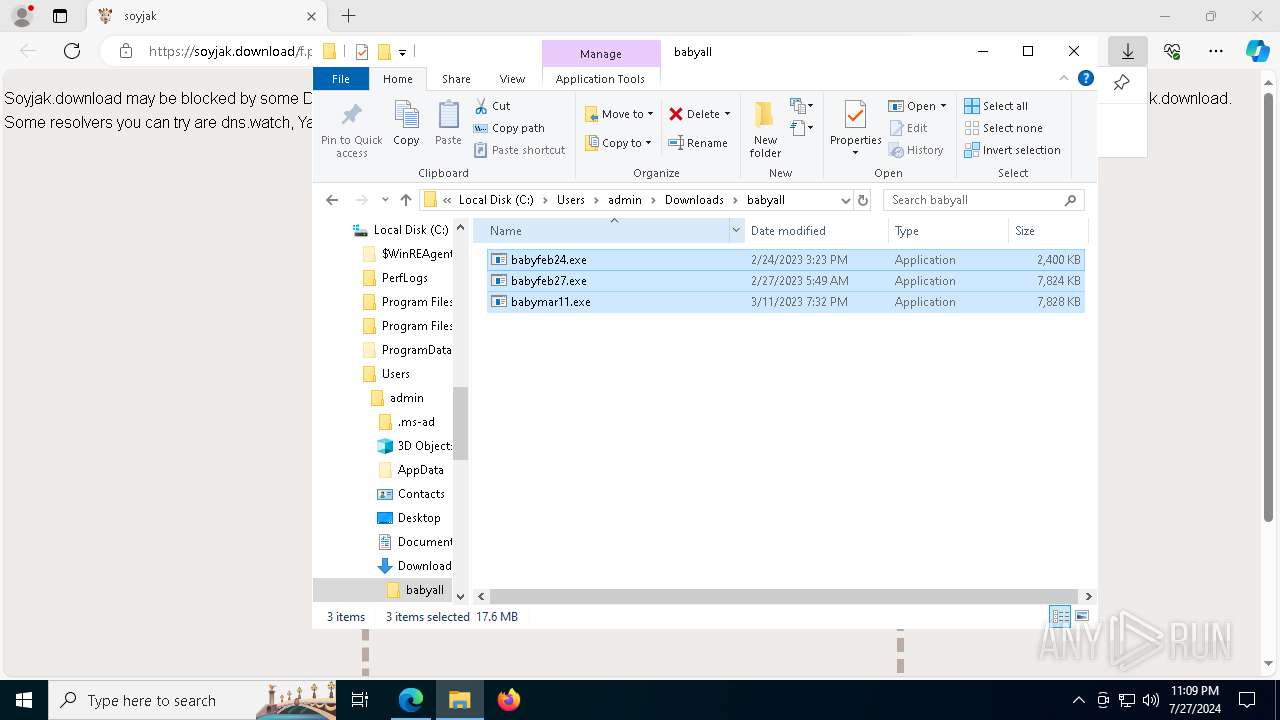
Bypass execution policy to execute commands
- powershell.exe (PID: 7676)
- powershell.exe (PID: 4316)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 3632)
- powershell.exe (PID: 4400)
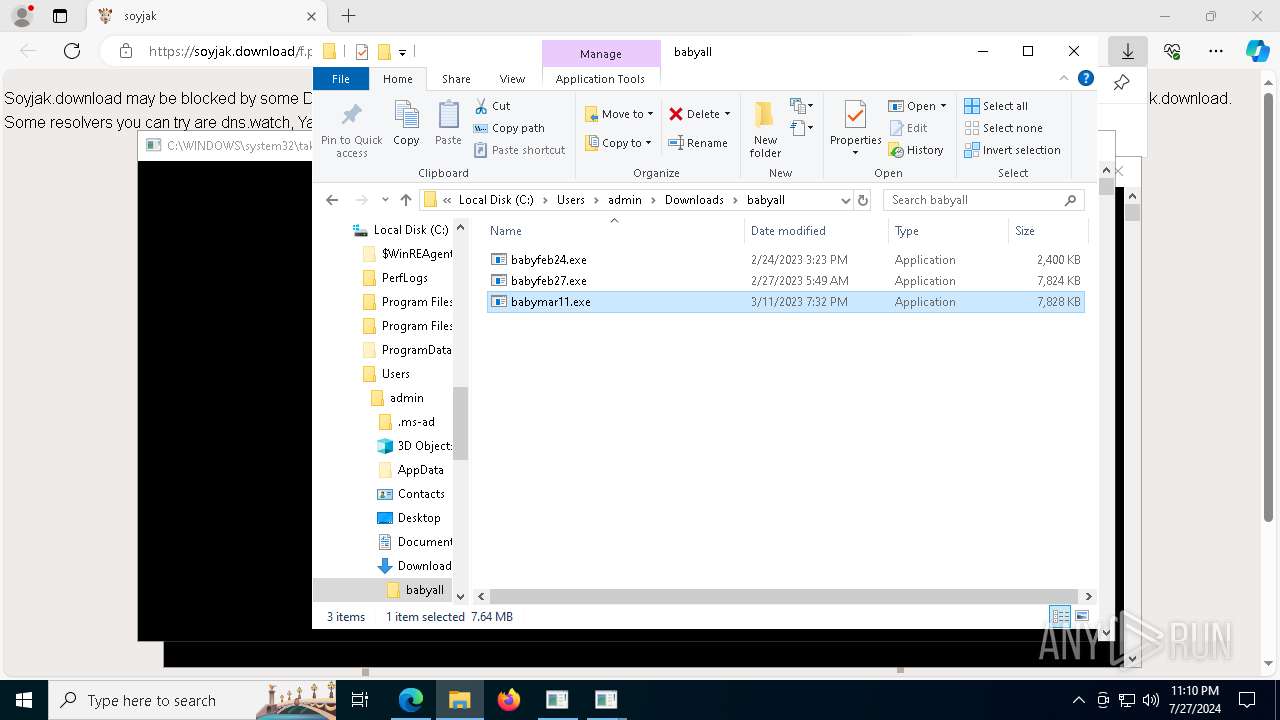
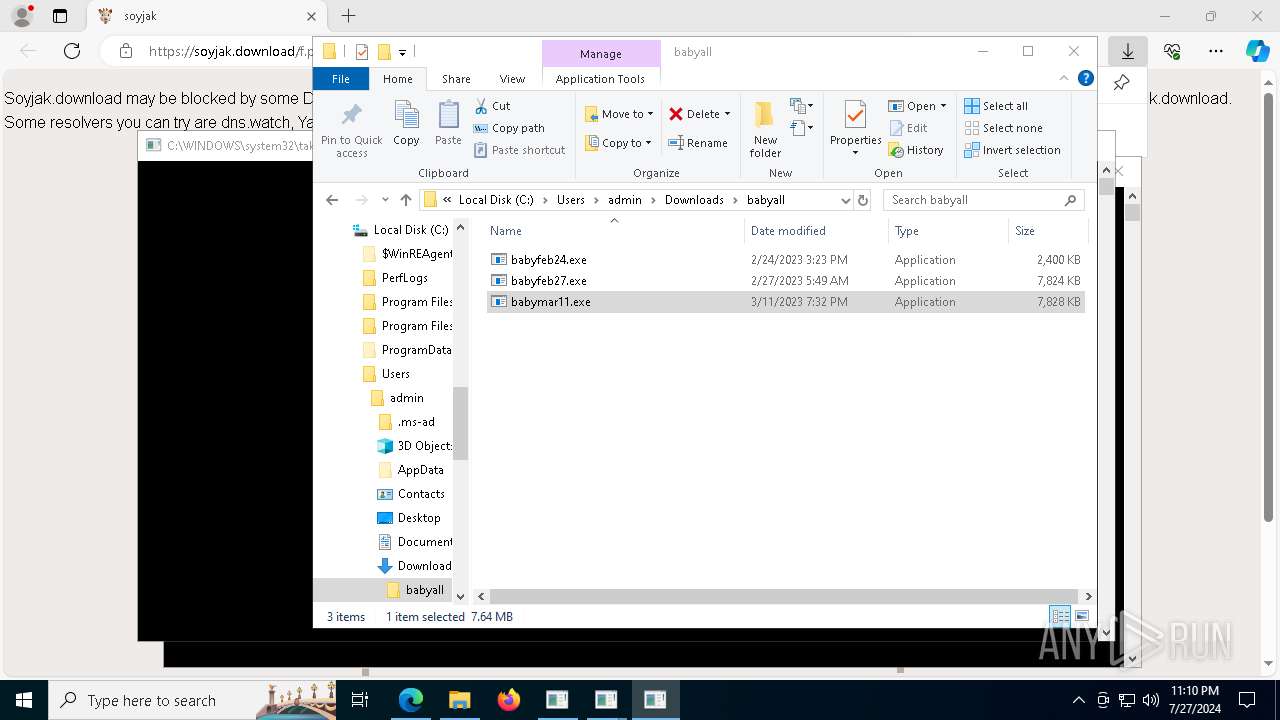
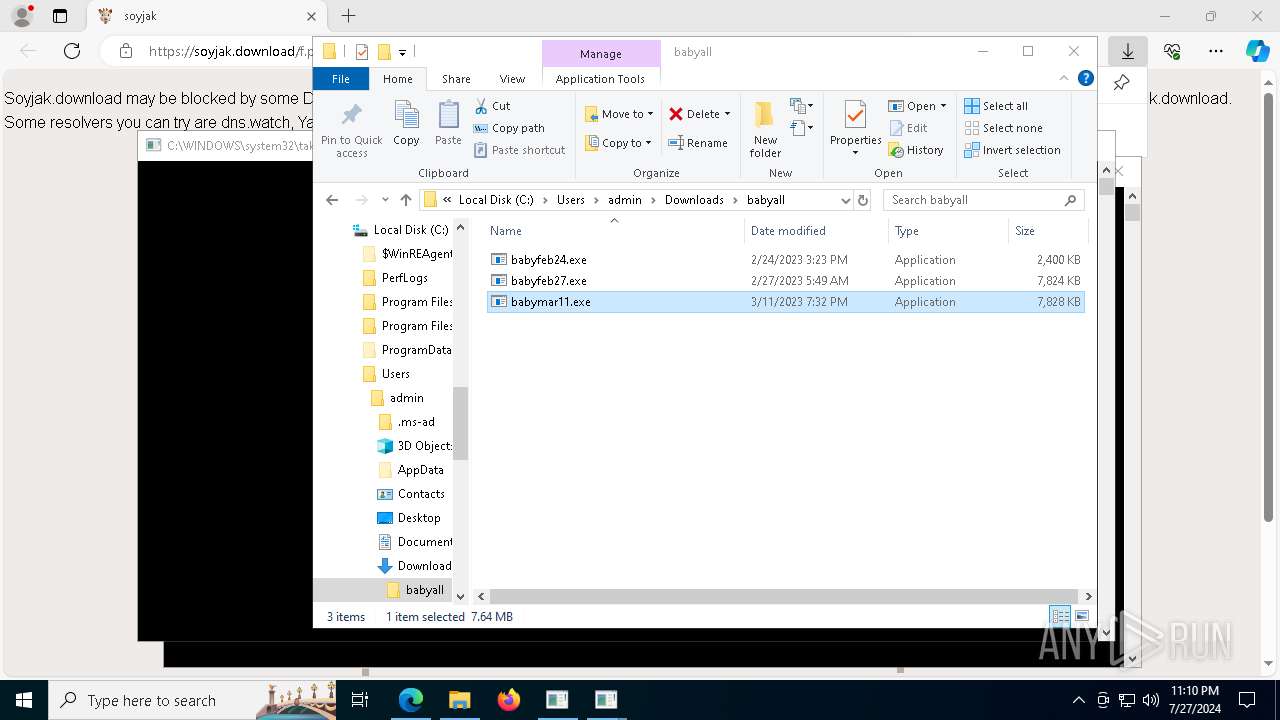
Changes powershell execution policy (Bypass)
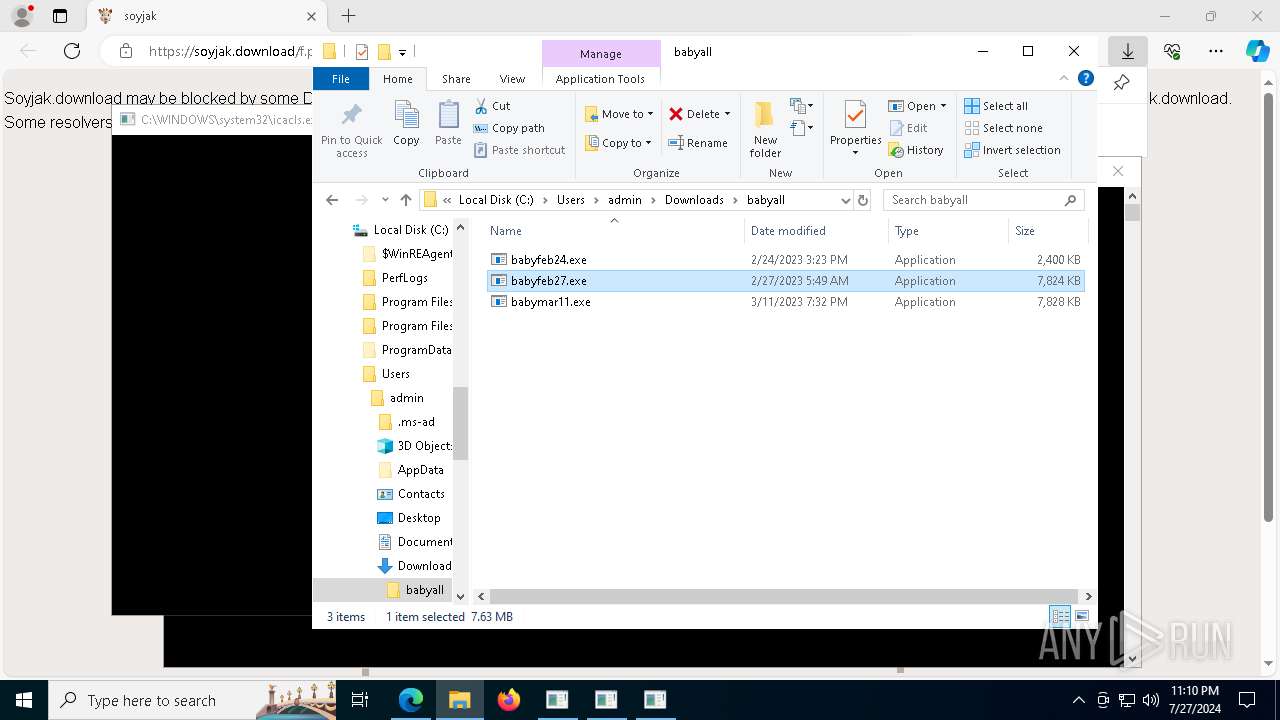
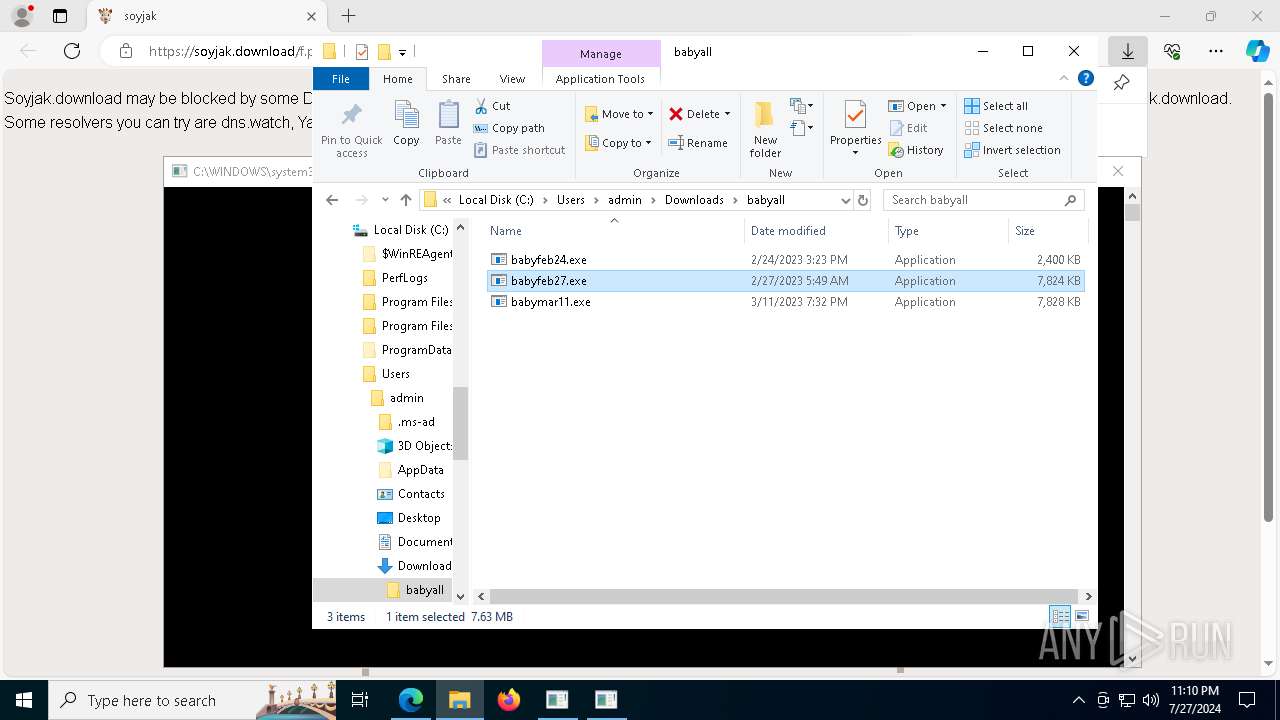
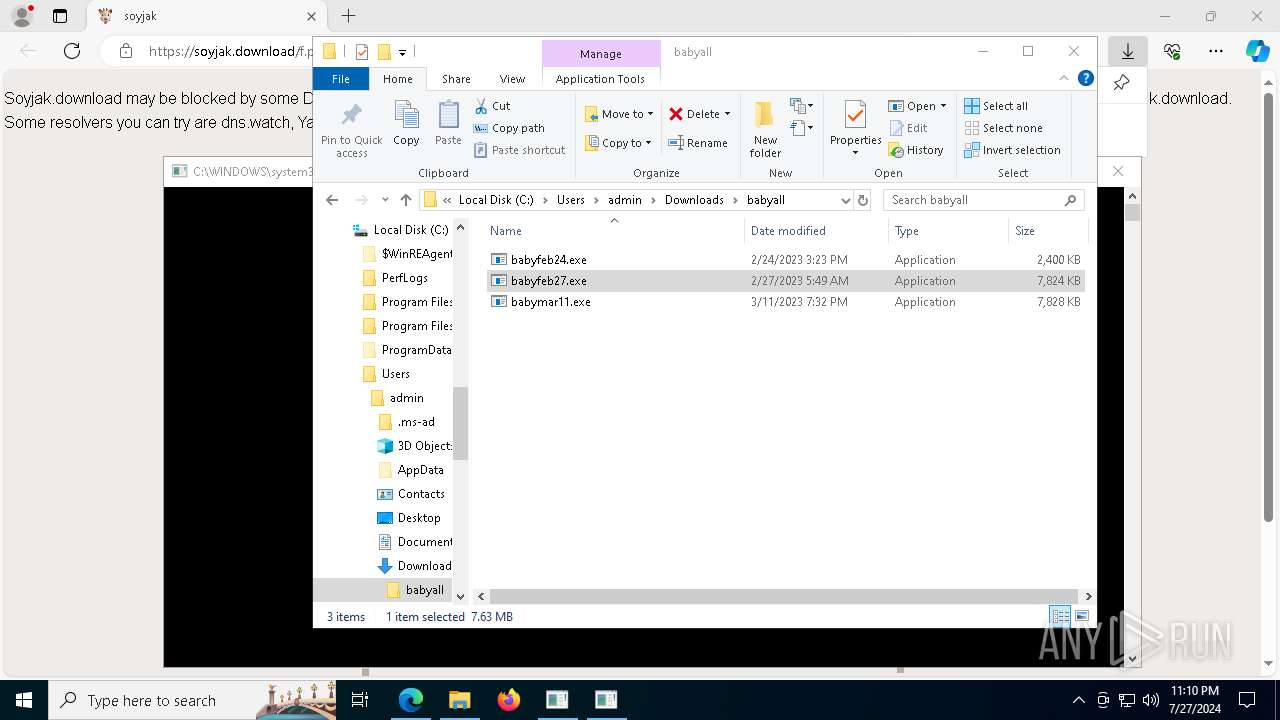
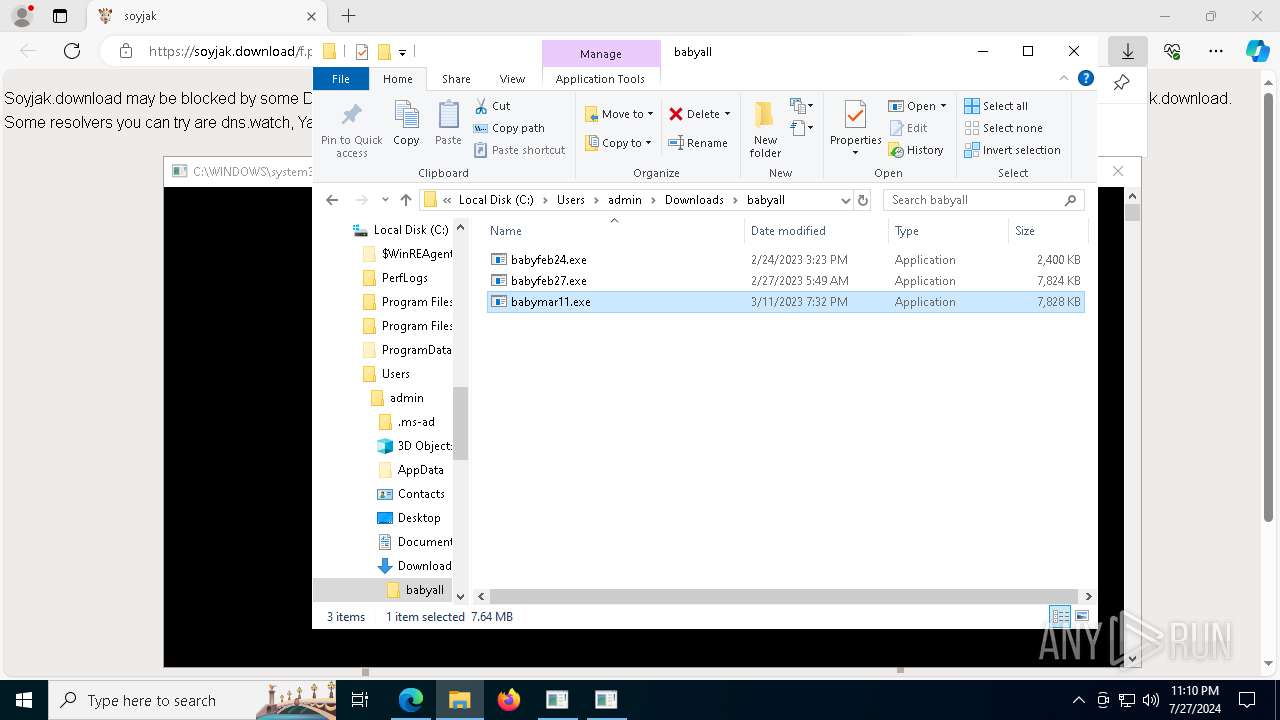
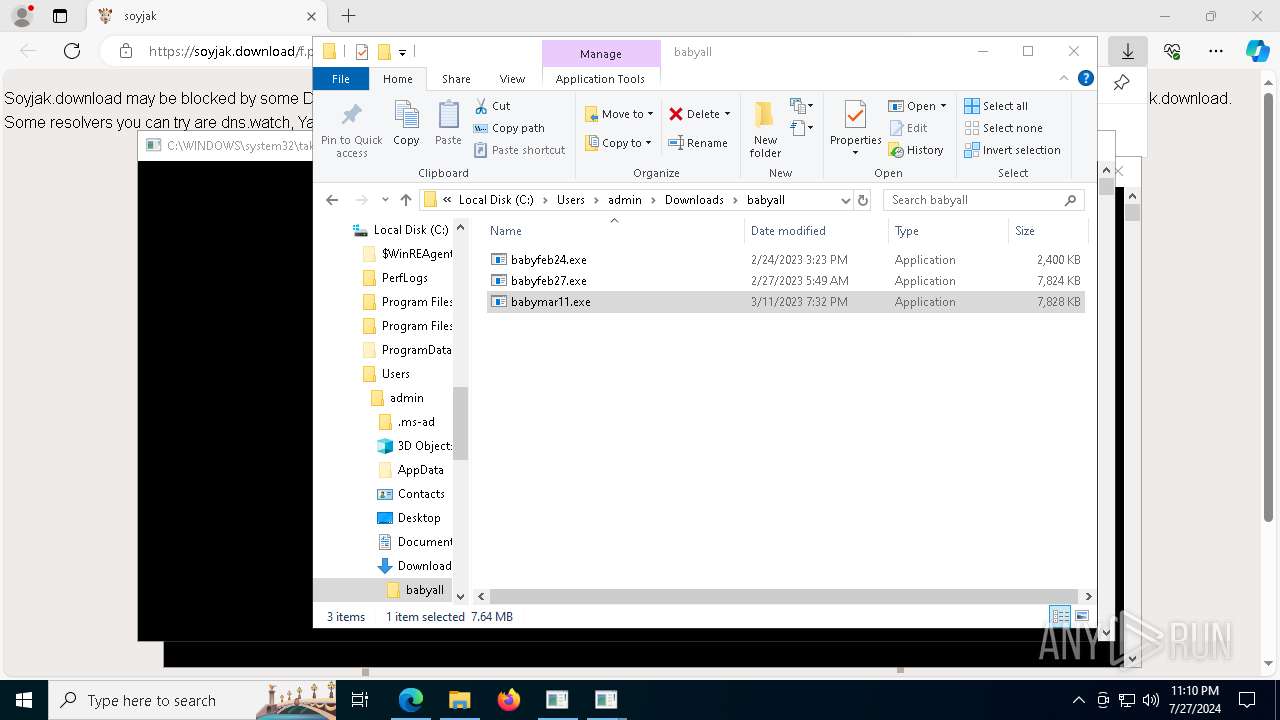
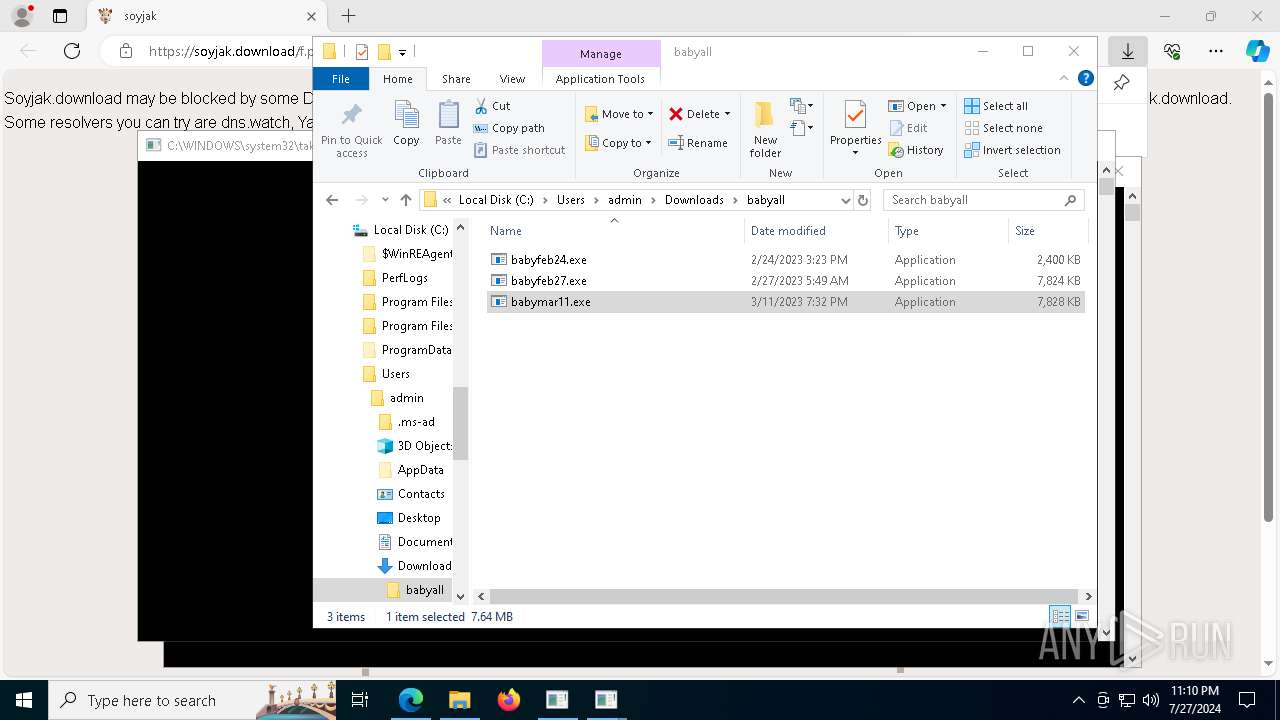
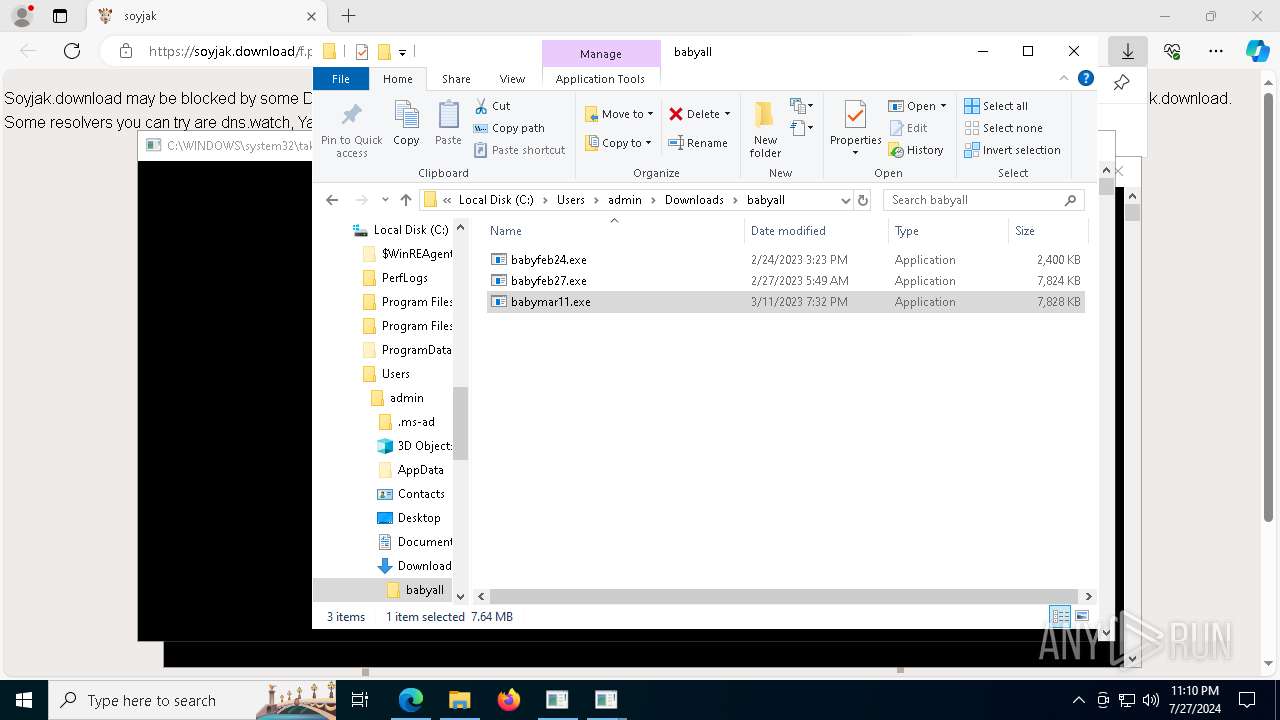
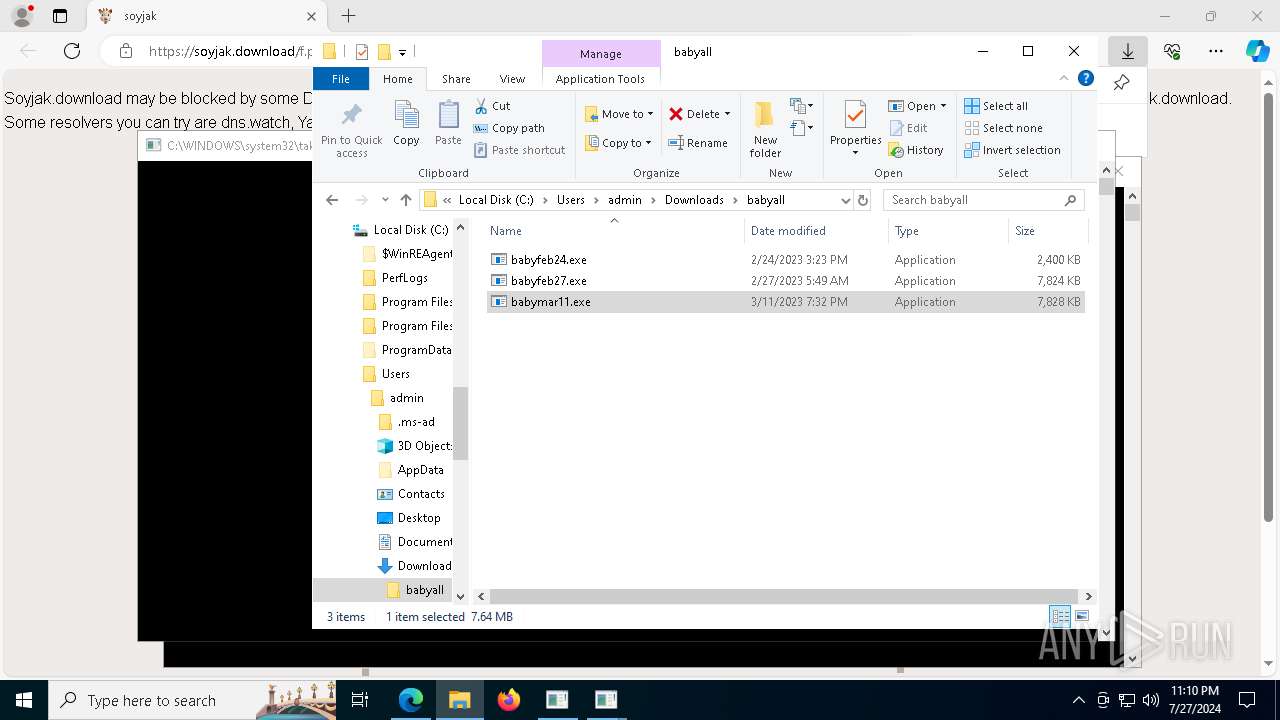
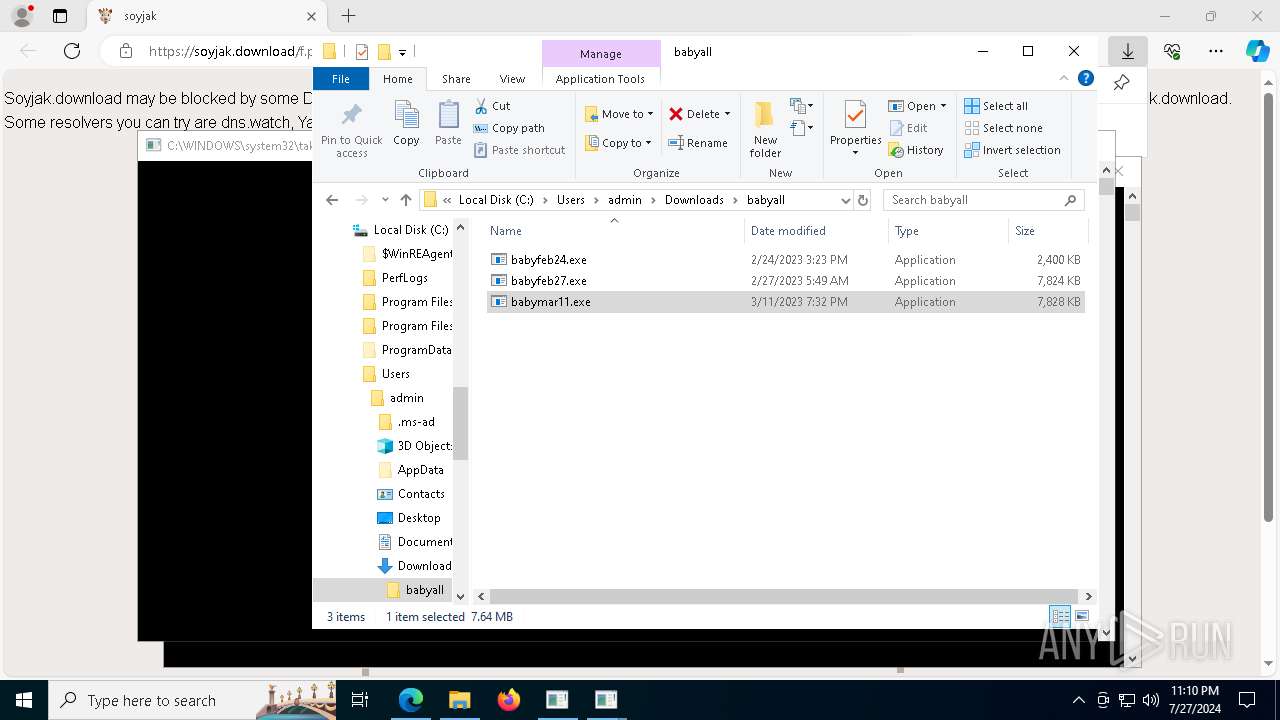
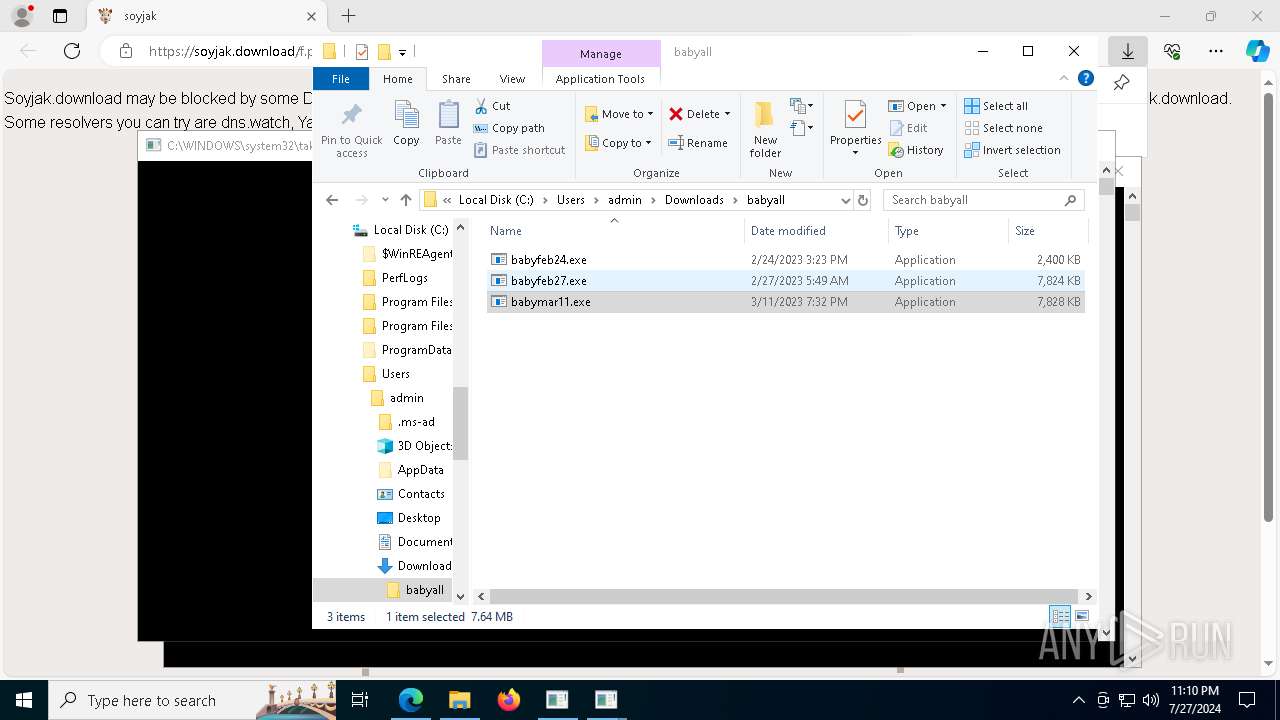
- babyfeb27.exe (PID: 1644)
- babymar11.exe (PID: 3360)
- babyfeb27.exe (PID: 5948)
- babymar11.exe (PID: 5296)
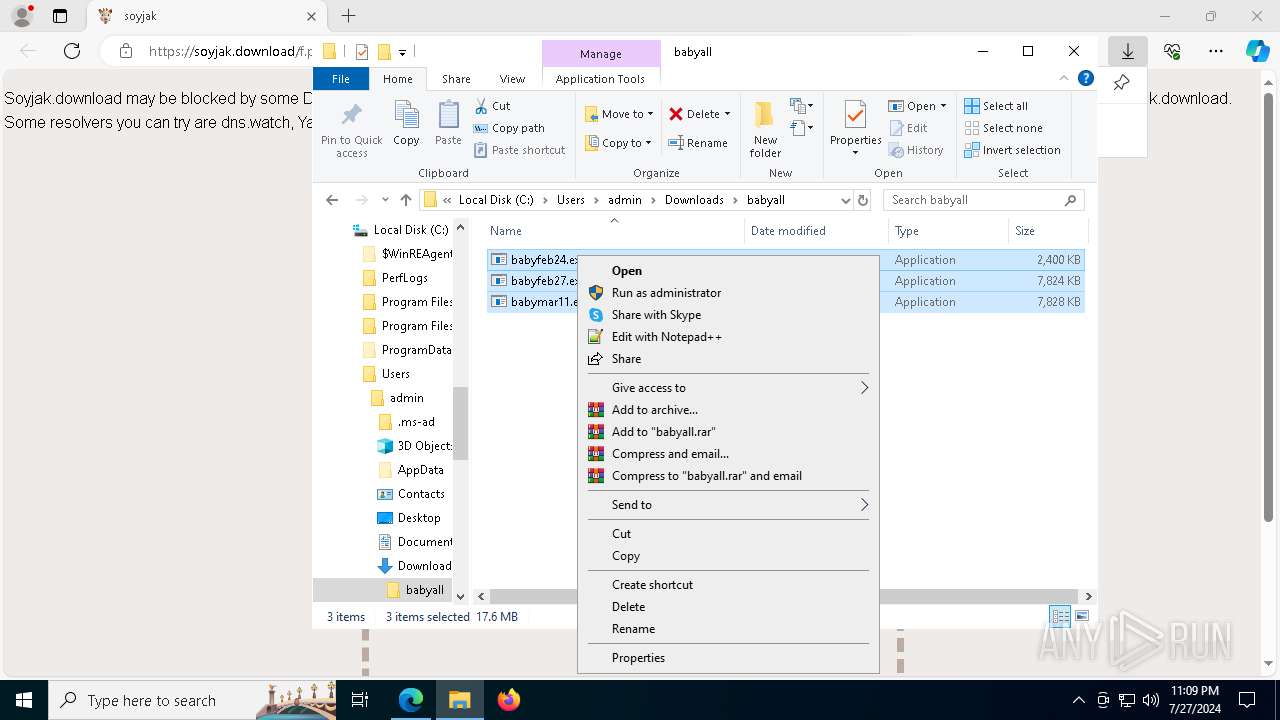
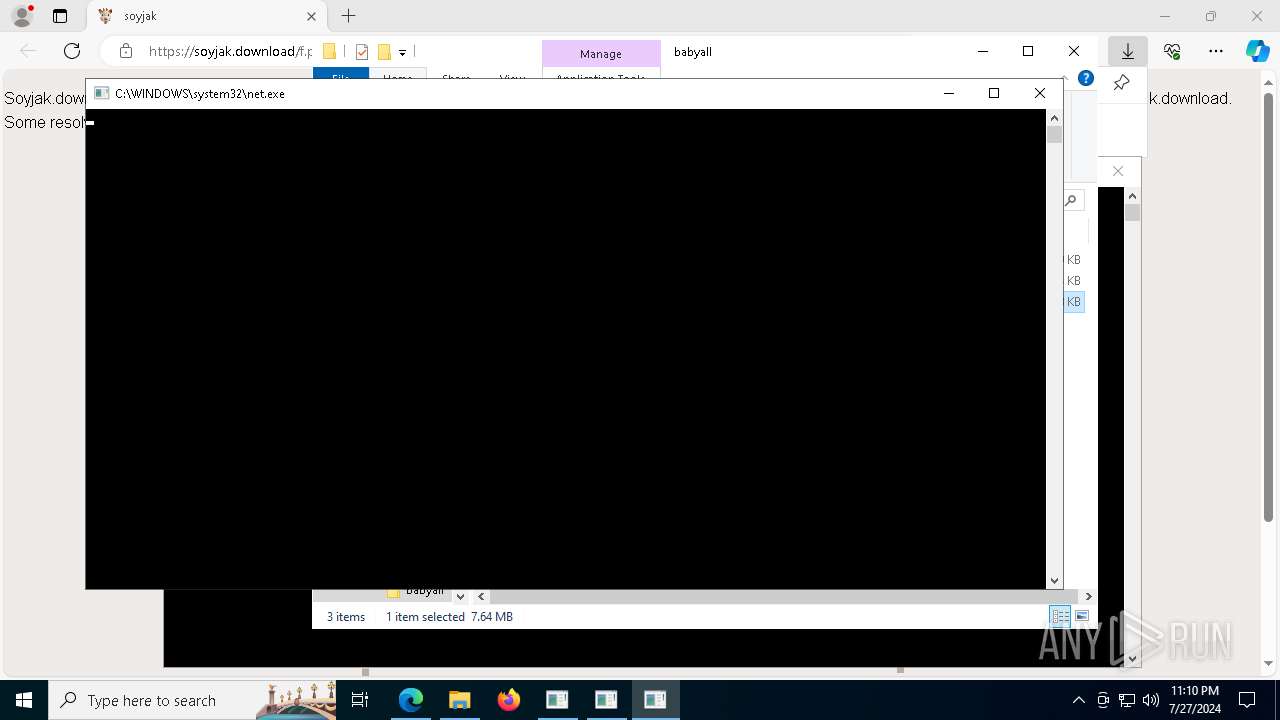
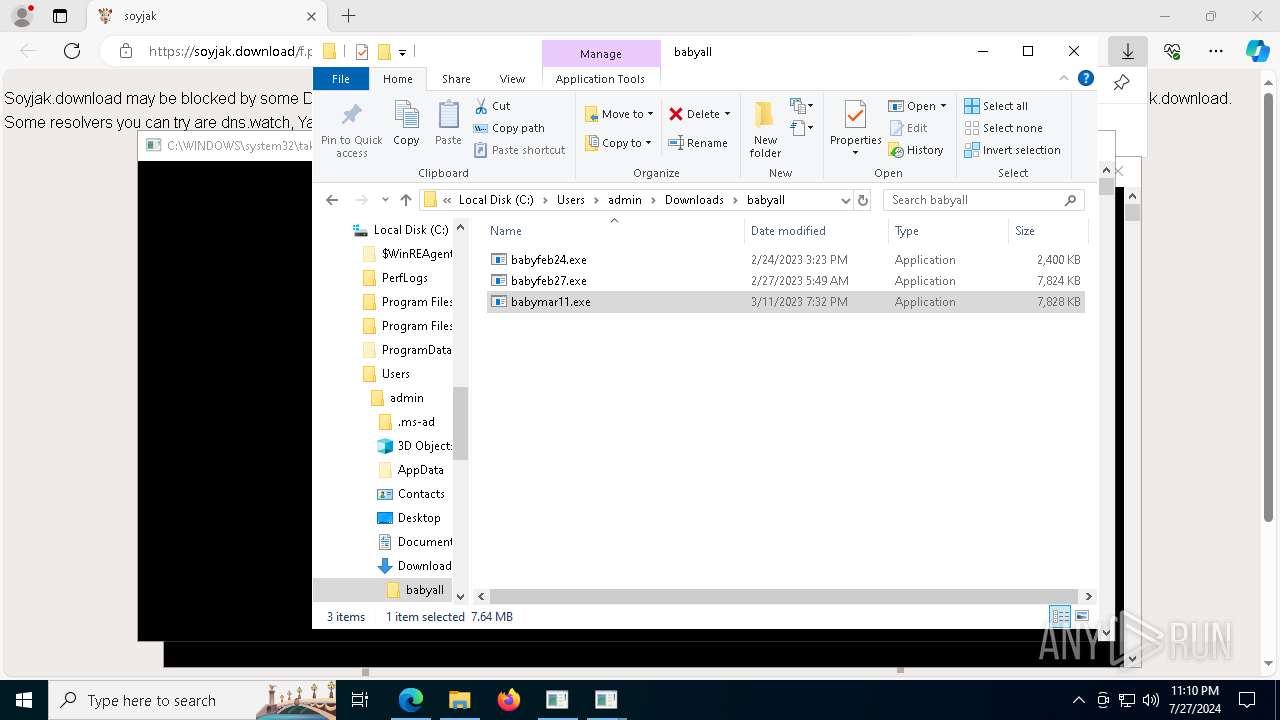
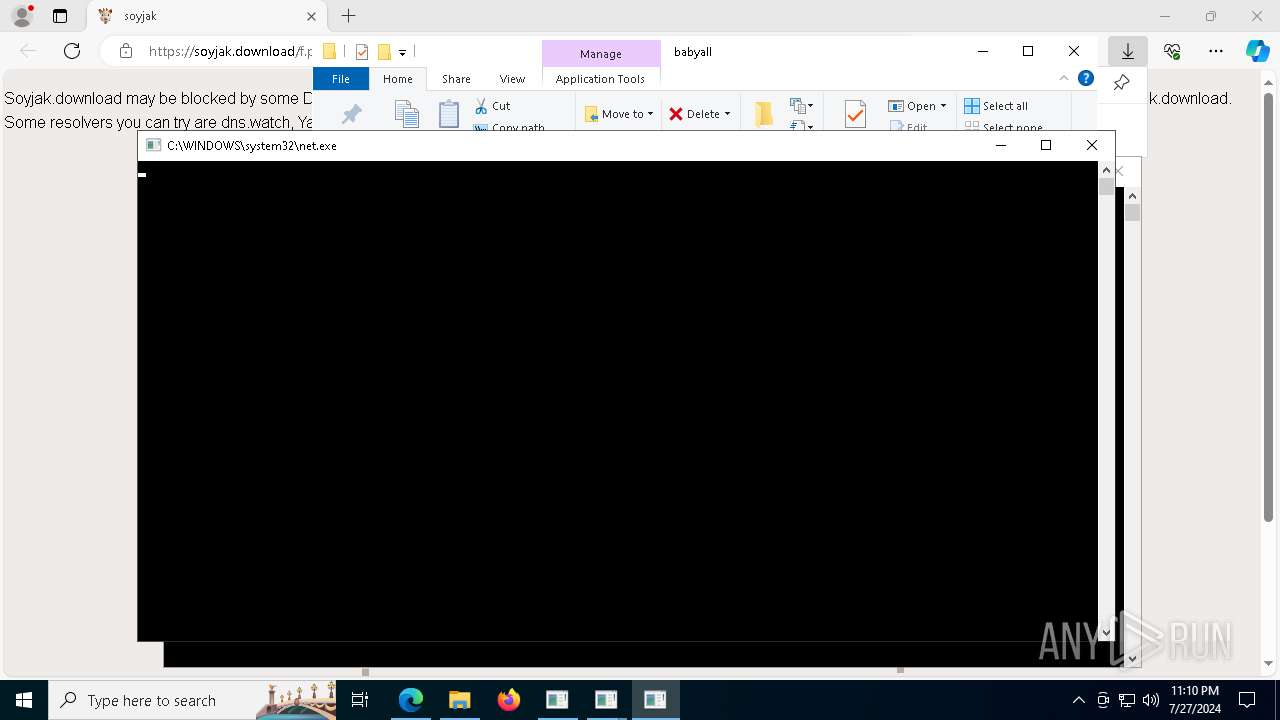
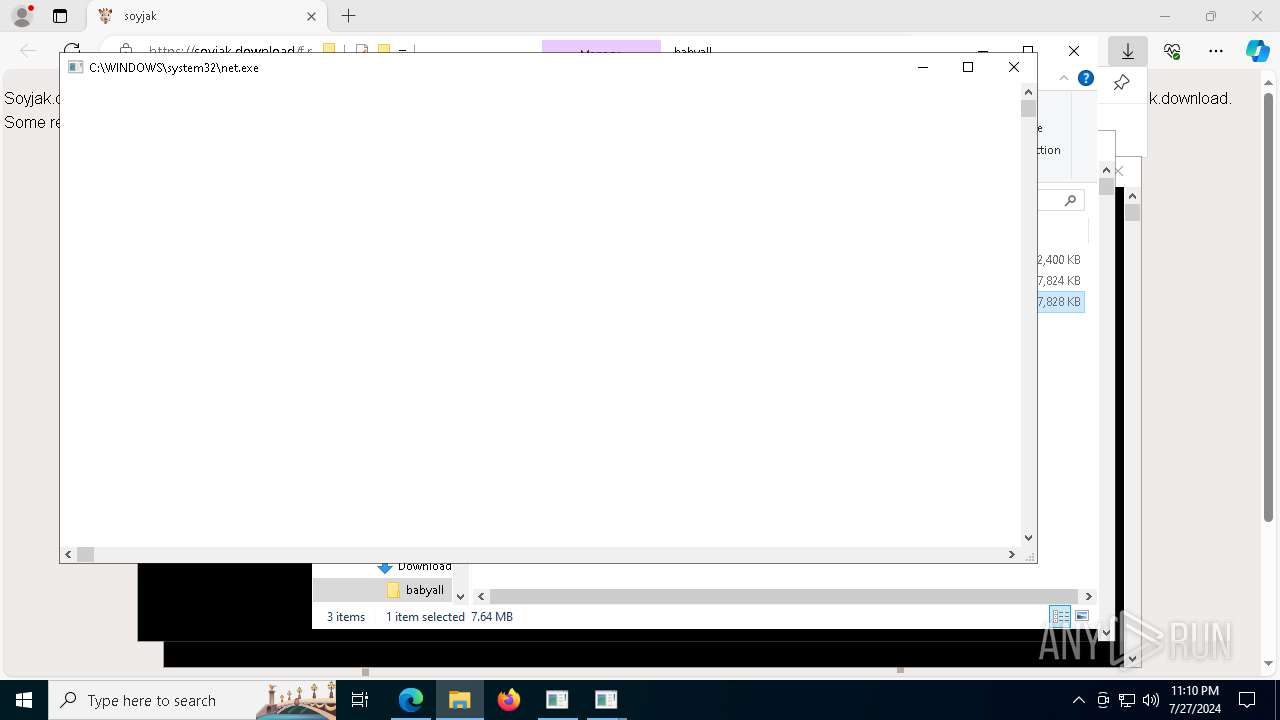
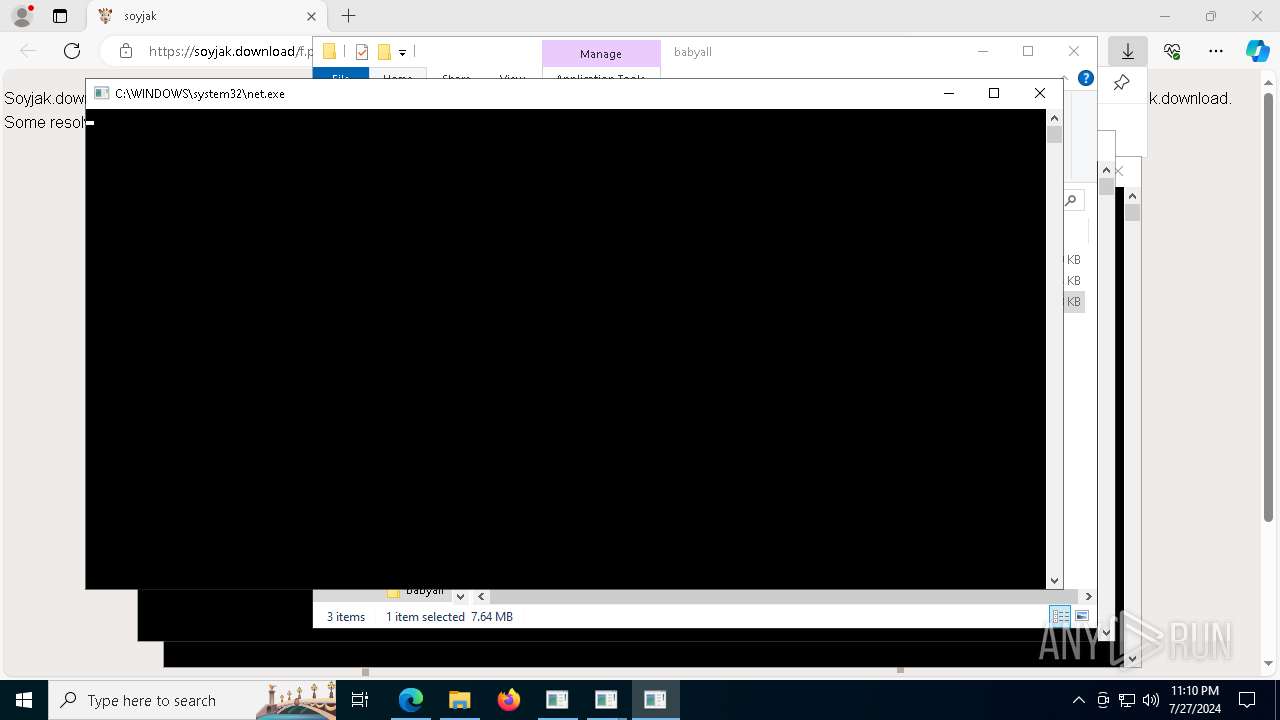
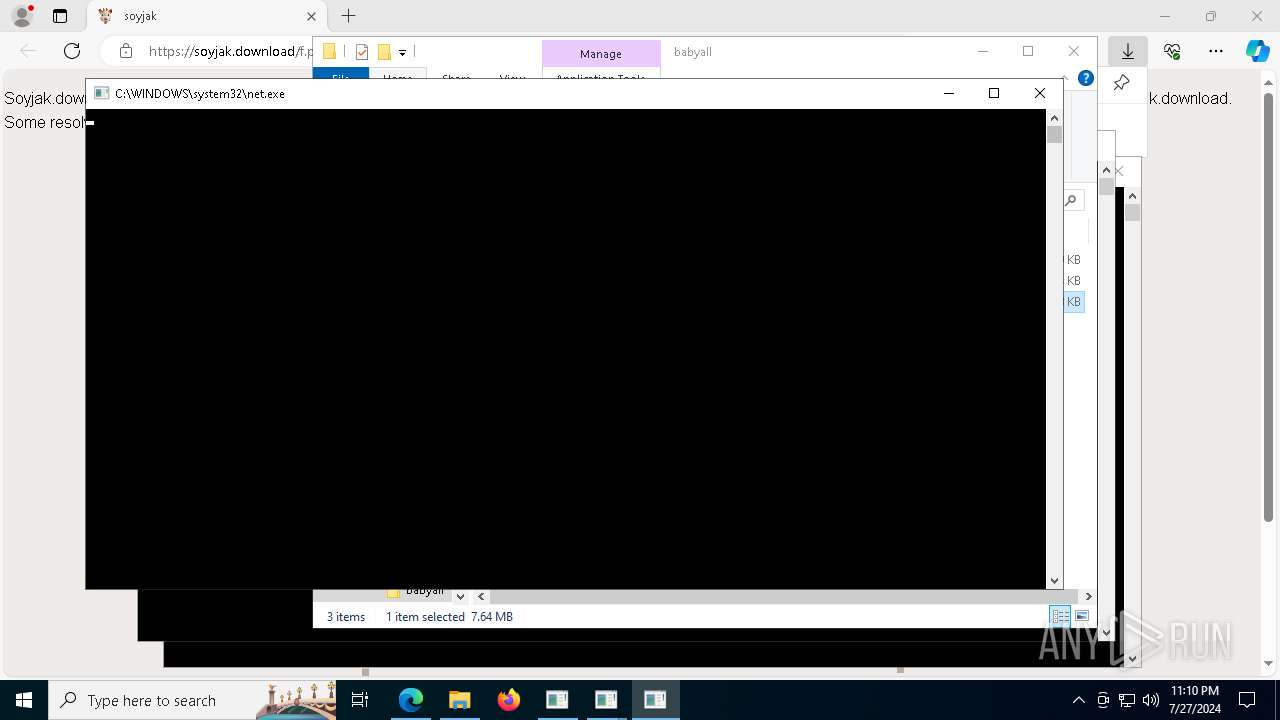
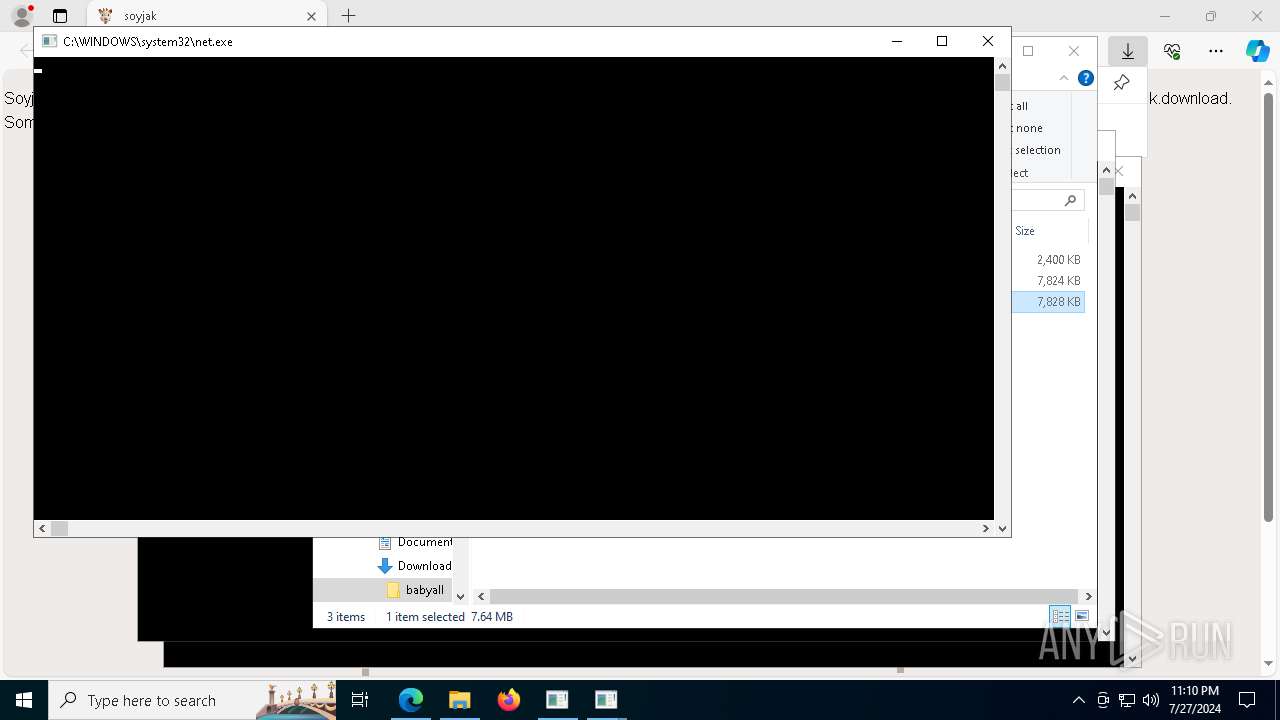
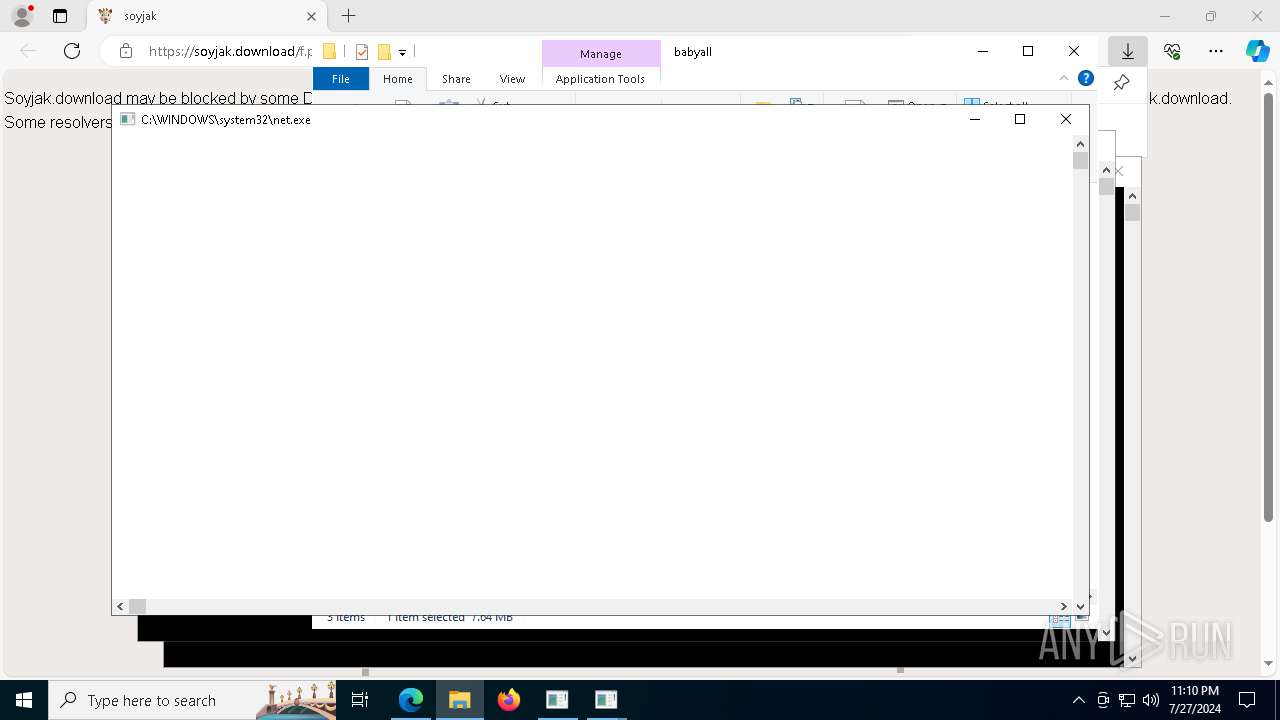
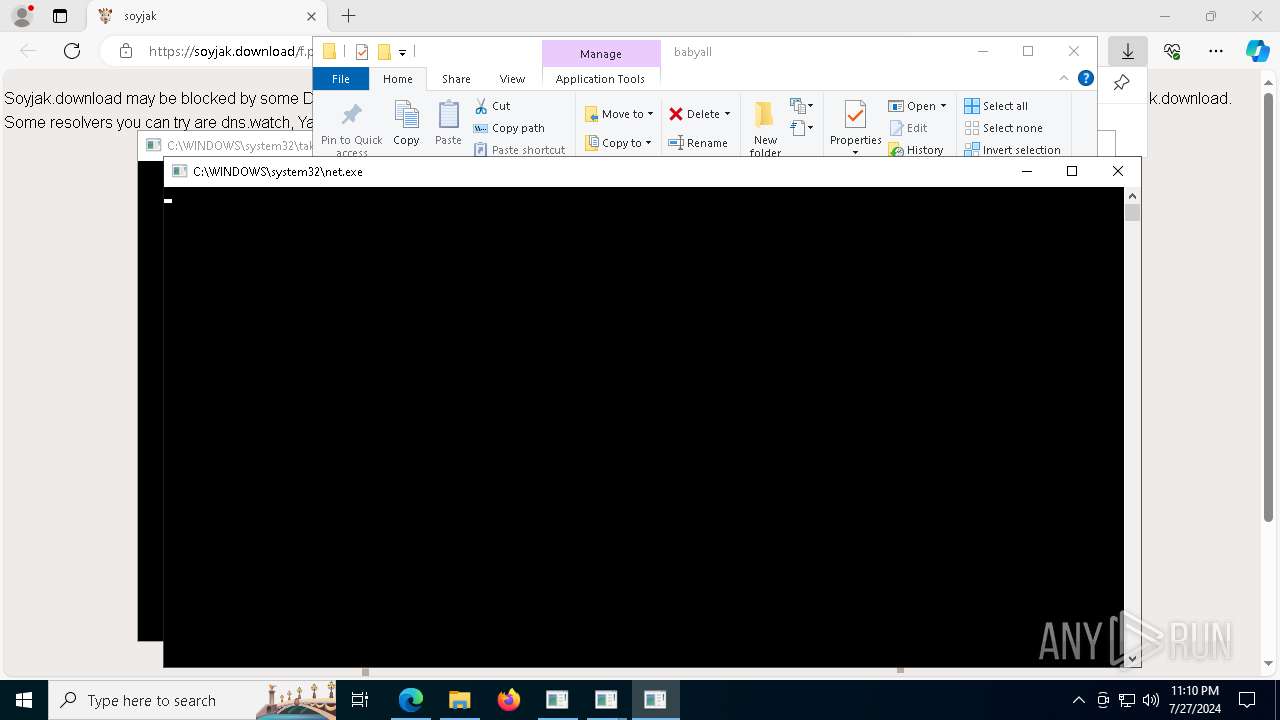
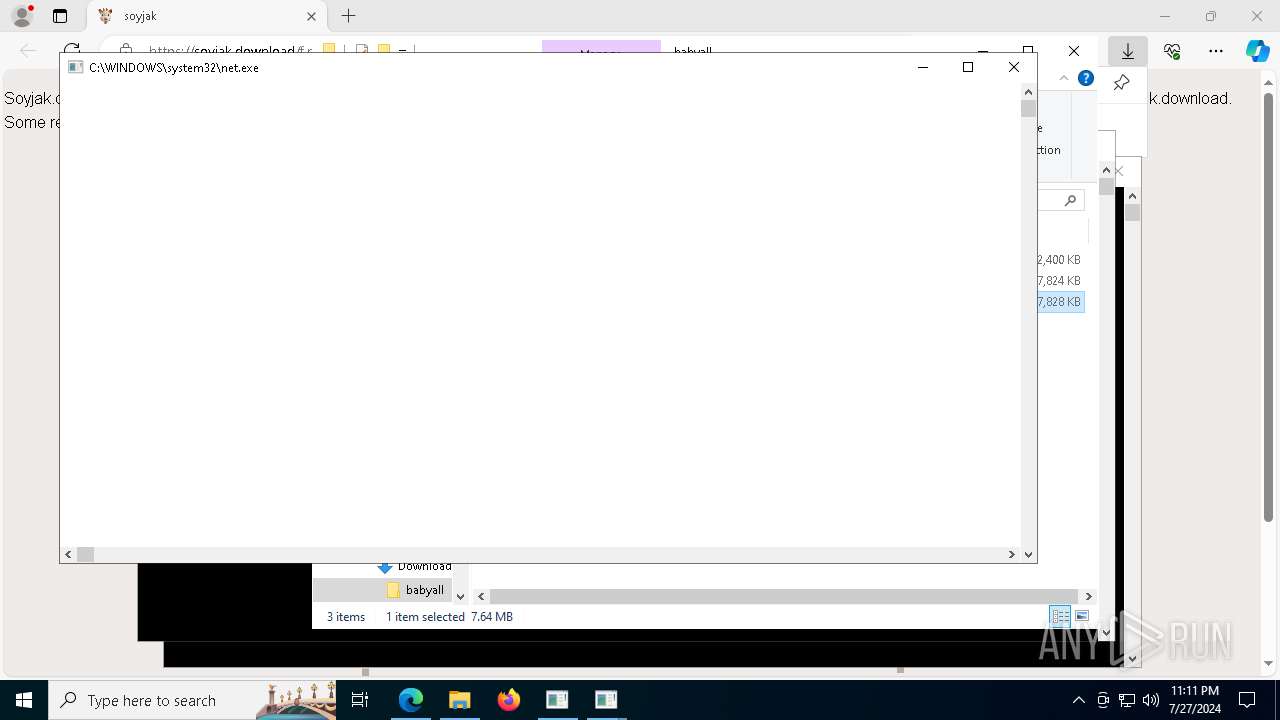
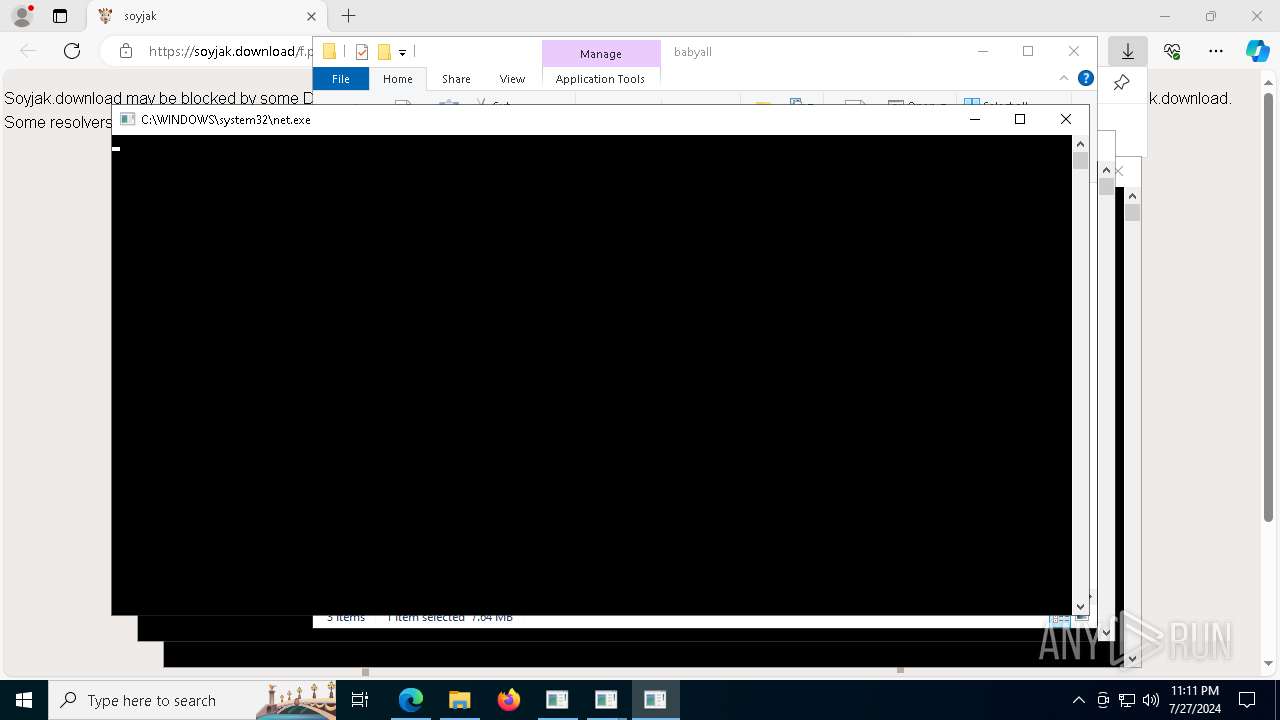
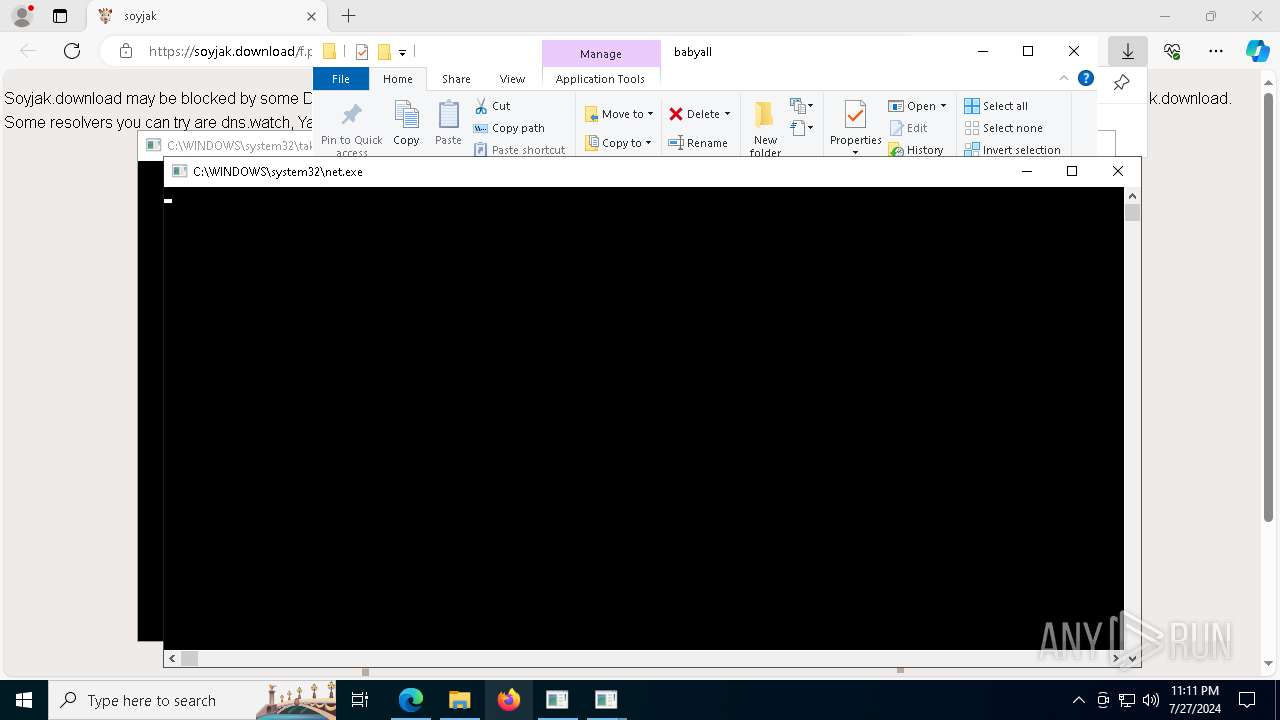
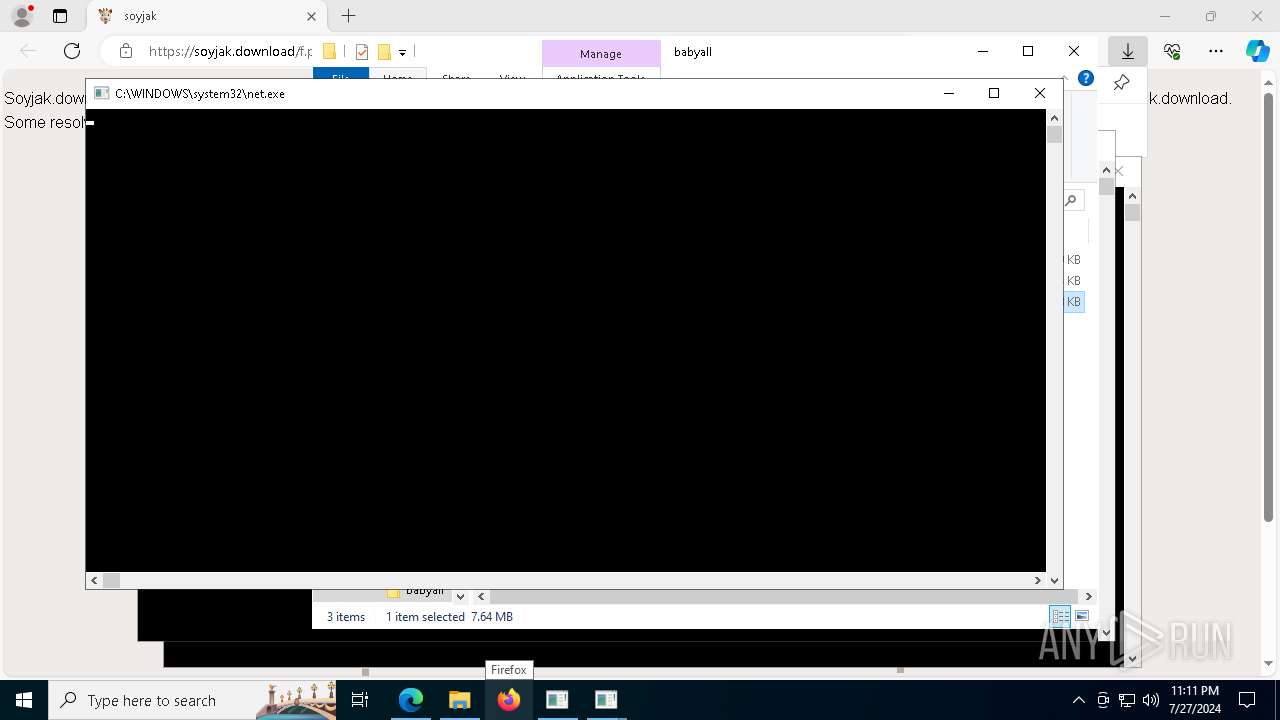
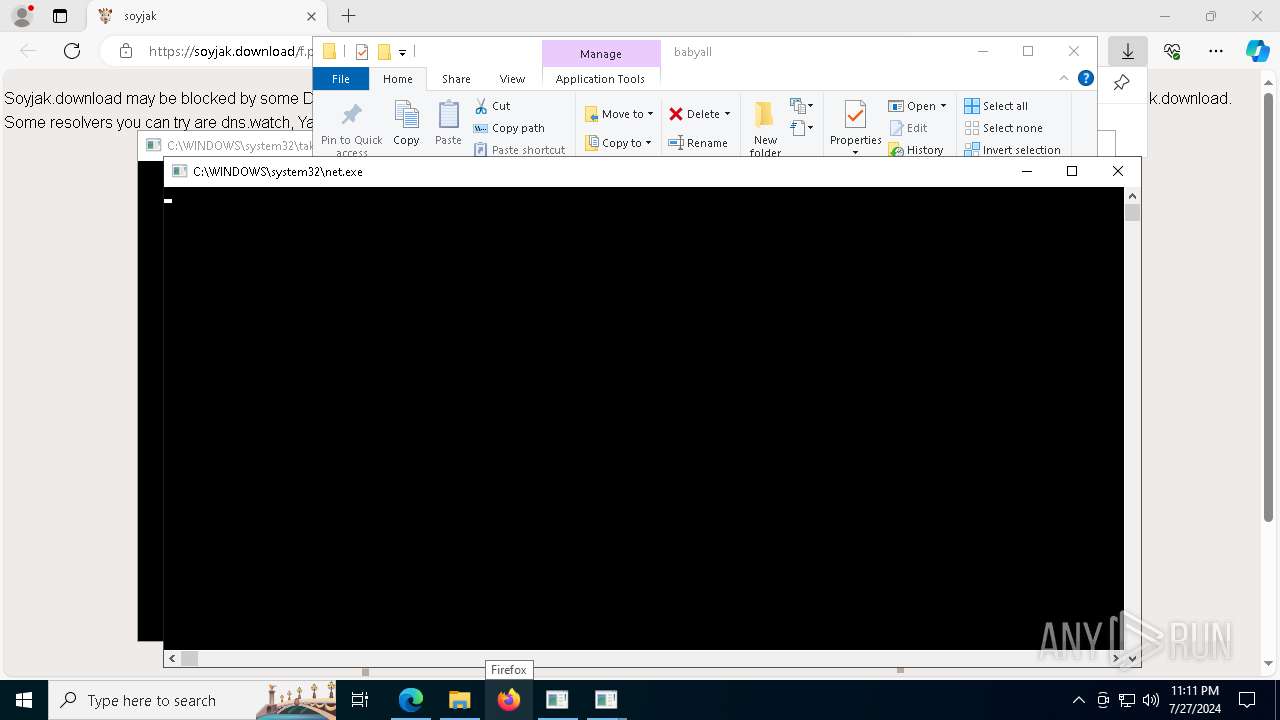
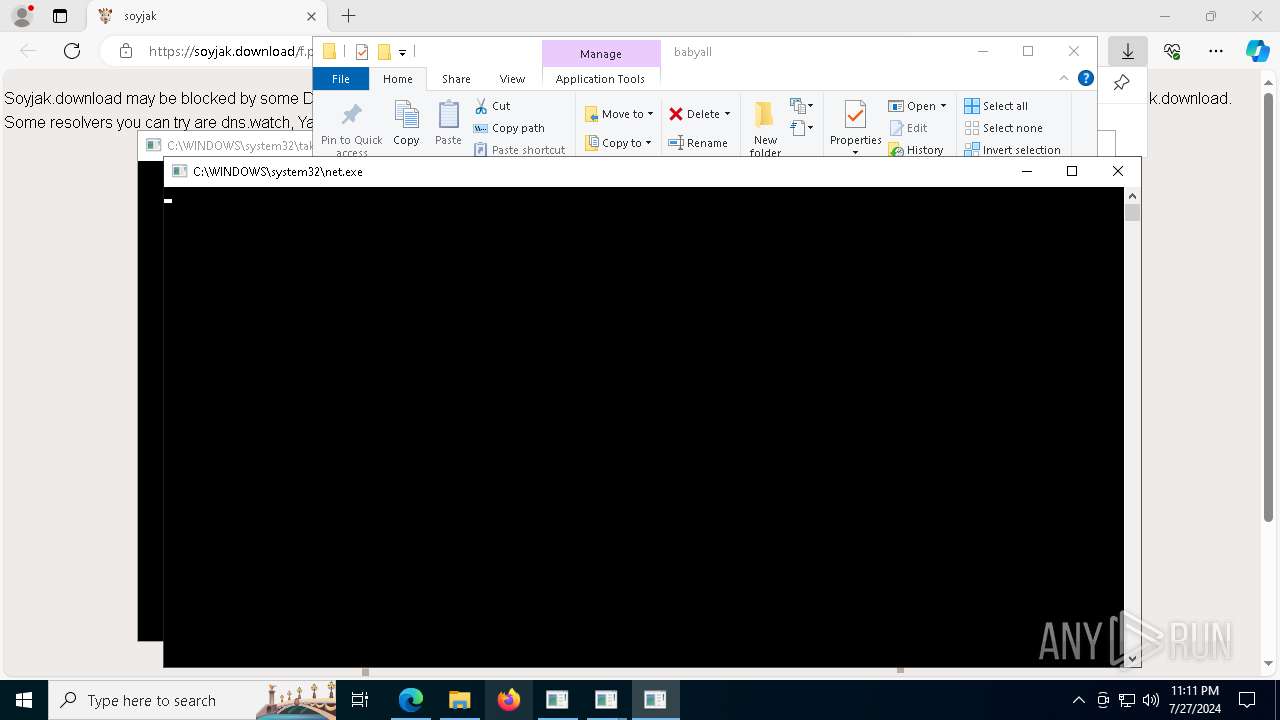
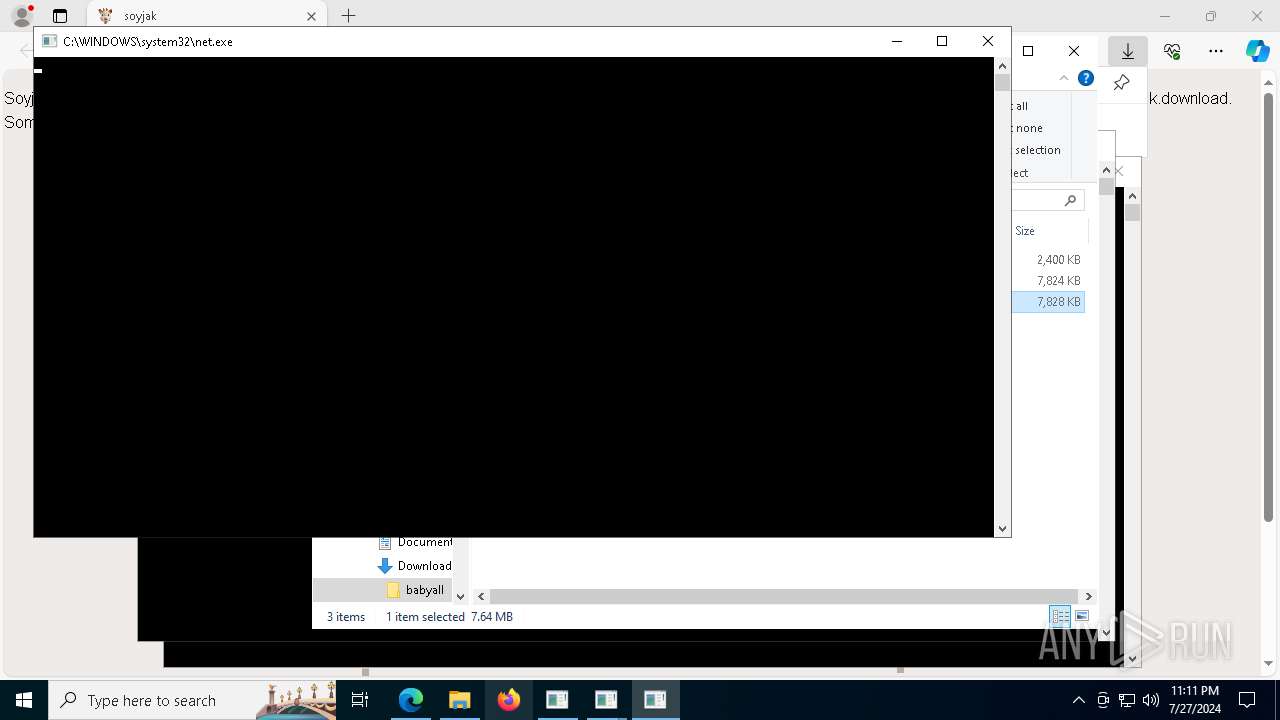
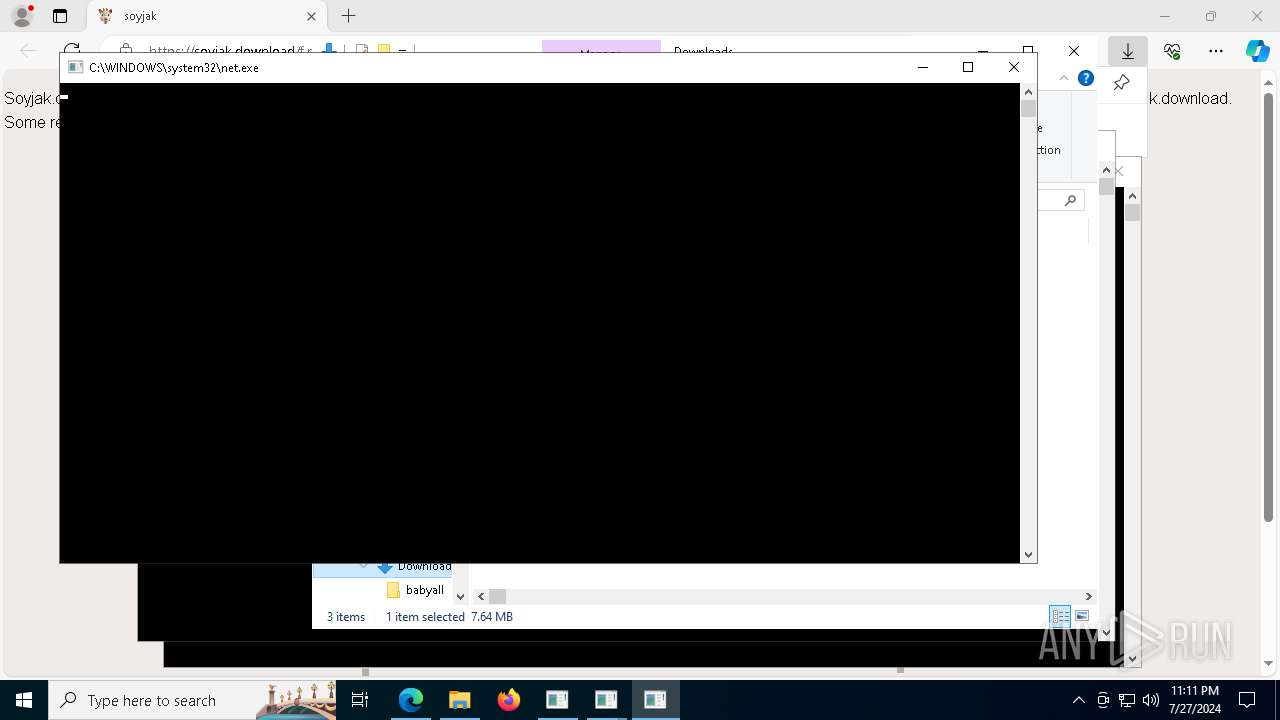
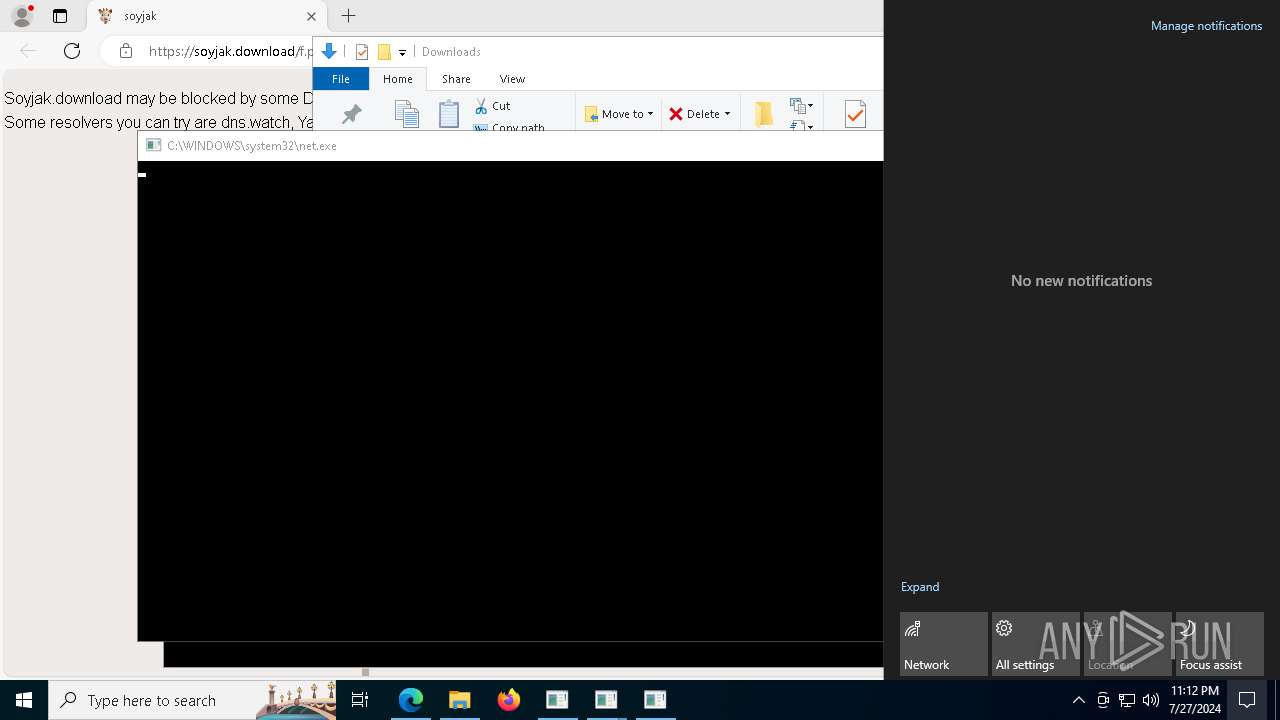
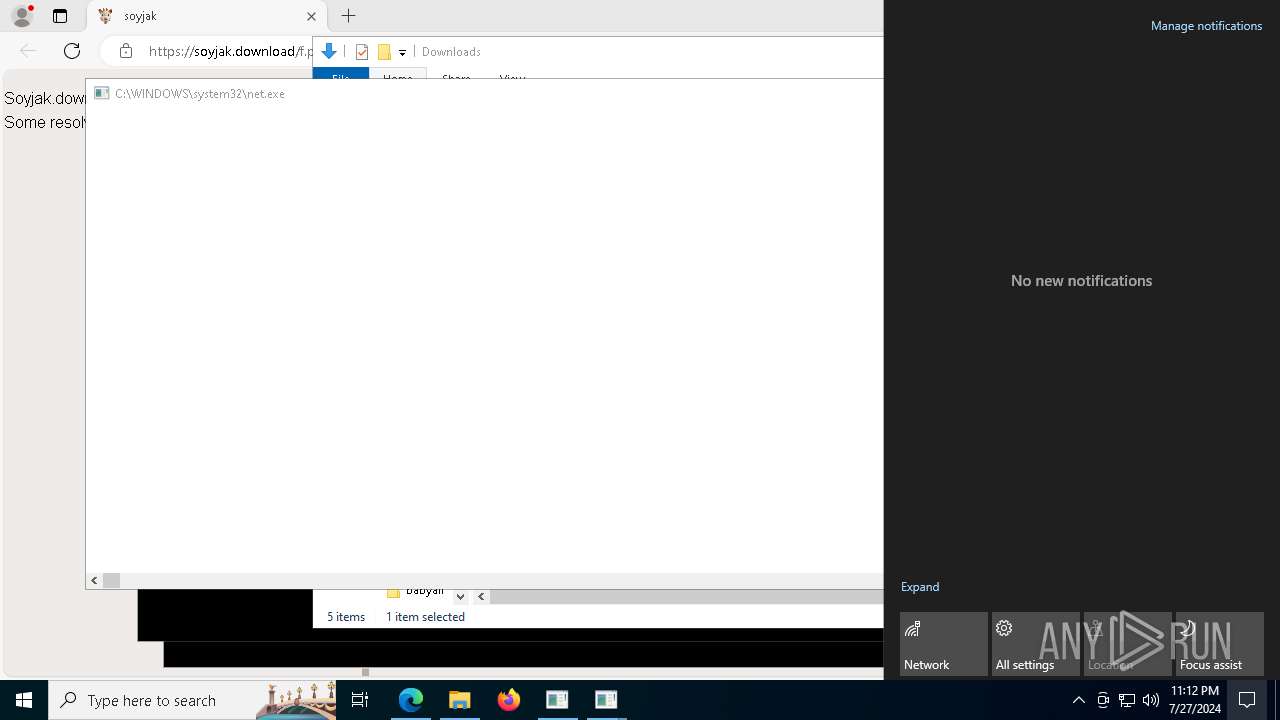
Starts NET.EXE to view/add/change user profiles
- babymar11.exe (PID: 3360)
- net.exe (PID: 7976)
- net.exe (PID: 1992)
- net.exe (PID: 8096)
- net.exe (PID: 4032)
- net.exe (PID: 5788)
- net.exe (PID: 6260)
- net.exe (PID: 7656)
- net.exe (PID: 7096)
- net.exe (PID: 5832)
- net.exe (PID: 7588)
- net.exe (PID: 8116)
- net.exe (PID: 1432)
- net.exe (PID: 6564)
- net.exe (PID: 7936)
- net.exe (PID: 1468)
- net.exe (PID: 6164)
- net.exe (PID: 8080)
- net.exe (PID: 3856)
- net.exe (PID: 6124)
- net.exe (PID: 3280)
- net.exe (PID: 6308)
- net.exe (PID: 6376)
- net.exe (PID: 968)
- net.exe (PID: 4028)
- net.exe (PID: 4244)
- net.exe (PID: 3684)
- net.exe (PID: 1432)
- net.exe (PID: 5732)
- net.exe (PID: 5832)
- net.exe (PID: 1752)
- net.exe (PID: 5068)
- net.exe (PID: 7232)
- net.exe (PID: 7228)
- net.exe (PID: 6788)
- net.exe (PID: 5660)
- net.exe (PID: 6136)
- net.exe (PID: 4936)
- net.exe (PID: 2996)
- net.exe (PID: 6084)
- net.exe (PID: 5832)
- net.exe (PID: 5240)
- net.exe (PID: 4320)
- net.exe (PID: 7608)
- net.exe (PID: 1244)
- net.exe (PID: 1028)
- net.exe (PID: 4040)
- net.exe (PID: 3580)
- net.exe (PID: 6716)
- net.exe (PID: 6524)
- net.exe (PID: 3936)
- net.exe (PID: 8036)
- net.exe (PID: 1596)
- net.exe (PID: 3196)
- net.exe (PID: 7232)
- net.exe (PID: 4520)
- net.exe (PID: 3864)
- net.exe (PID: 7636)
- net.exe (PID: 2912)
- net.exe (PID: 5808)
- net.exe (PID: 3680)
- net.exe (PID: 1324)
- net.exe (PID: 3684)
- net.exe (PID: 7892)
- net.exe (PID: 6676)
- net.exe (PID: 1244)
- net.exe (PID: 2476)
- net.exe (PID: 4028)
- net.exe (PID: 7972)
- net.exe (PID: 6440)
- net.exe (PID: 3816)
- net.exe (PID: 4128)
- net.exe (PID: 5936)
- net.exe (PID: 3632)
- net.exe (PID: 5220)
- net.exe (PID: 3616)
- net.exe (PID: 5488)
- net.exe (PID: 8128)
- net.exe (PID: 7016)
- net.exe (PID: 7896)
- net.exe (PID: 7760)
- net.exe (PID: 4564)
- net.exe (PID: 3808)
- net.exe (PID: 7972)
- net.exe (PID: 5268)
- net.exe (PID: 1176)
- net.exe (PID: 3404)
- net.exe (PID: 3936)
- net.exe (PID: 2884)
- net.exe (PID: 7936)
- net.exe (PID: 3836)
- net.exe (PID: 1996)
- net.exe (PID: 1596)
- net.exe (PID: 7232)
- net.exe (PID: 4636)
- net.exe (PID: 456)
- net.exe (PID: 3668)
- net.exe (PID: 6136)
- net.exe (PID: 3608)
- net.exe (PID: 812)
- net.exe (PID: 2884)
- net.exe (PID: 6812)
- net.exe (PID: 2976)
- net.exe (PID: 6440)
- net.exe (PID: 1712)
- net.exe (PID: 3280)
- net.exe (PID: 3616)
- net.exe (PID: 3196)
- net.exe (PID: 7124)
- net.exe (PID: 3632)
- net.exe (PID: 704)
- net.exe (PID: 7048)
- net.exe (PID: 4656)
- net.exe (PID: 5196)
- net.exe (PID: 3548)
- net.exe (PID: 4820)
- babymar11.exe (PID: 5296)
- net.exe (PID: 6304)
- net.exe (PID: 1012)
- net.exe (PID: 7972)
- net.exe (PID: 8016)
- net.exe (PID: 2856)
- net.exe (PID: 7808)
- net.exe (PID: 5920)
- net.exe (PID: 6120)
- net.exe (PID: 4128)
- net.exe (PID: 7680)
- net.exe (PID: 3808)
- net.exe (PID: 5660)
- net.exe (PID: 5448)
- net.exe (PID: 1712)
- net.exe (PID: 5776)
- net.exe (PID: 7632)
- net.exe (PID: 7976)
- net.exe (PID: 4228)
- net.exe (PID: 4044)
- net.exe (PID: 4632)
- net.exe (PID: 6640)
- net.exe (PID: 6628)
- net.exe (PID: 7036)
- net.exe (PID: 5956)
- net.exe (PID: 4660)
- net.exe (PID: 3340)
- net.exe (PID: 2816)
- net.exe (PID: 788)
- net.exe (PID: 8012)
- net.exe (PID: 6672)
- net.exe (PID: 5336)
- net.exe (PID: 7716)
- net.exe (PID: 7688)
- net.exe (PID: 7636)
- net.exe (PID: 7632)
- net.exe (PID: 2856)
- net.exe (PID: 8100)
- net.exe (PID: 7596)
- net.exe (PID: 7608)
- net.exe (PID: 6328)
- net.exe (PID: 1588)
- net.exe (PID: 7744)
- net.exe (PID: 5964)
- net.exe (PID: 884)
- net.exe (PID: 3608)
- net.exe (PID: 2616)
- net.exe (PID: 6448)
- net.exe (PID: 3680)
- net.exe (PID: 5556)
- net.exe (PID: 968)
- net.exe (PID: 3196)
- net.exe (PID: 5876)
- net.exe (PID: 2300)
- net.exe (PID: 6820)
- net.exe (PID: 7644)
- net.exe (PID: 7584)
- net.exe (PID: 788)
- net.exe (PID: 4384)
- net.exe (PID: 3788)
- net.exe (PID: 4012)
- net.exe (PID: 1752)
- net.exe (PID: 5488)
- net.exe (PID: 6352)
- net.exe (PID: 4656)
- net.exe (PID: 1432)
- net.exe (PID: 6164)
- net.exe (PID: 5668)
- net.exe (PID: 6304)
- net.exe (PID: 2616)
- net.exe (PID: 1800)
- net.exe (PID: 5068)
- net.exe (PID: 6232)
- net.exe (PID: 7148)
- net.exe (PID: 7036)
- net.exe (PID: 5608)
- net.exe (PID: 1432)
- net.exe (PID: 6812)
- net.exe (PID: 5776)
- net.exe (PID: 8080)
- net.exe (PID: 8116)
- net.exe (PID: 5876)
- net.exe (PID: 2936)
- net.exe (PID: 6332)
- net.exe (PID: 7628)
- net.exe (PID: 6640)
SUSPICIOUS
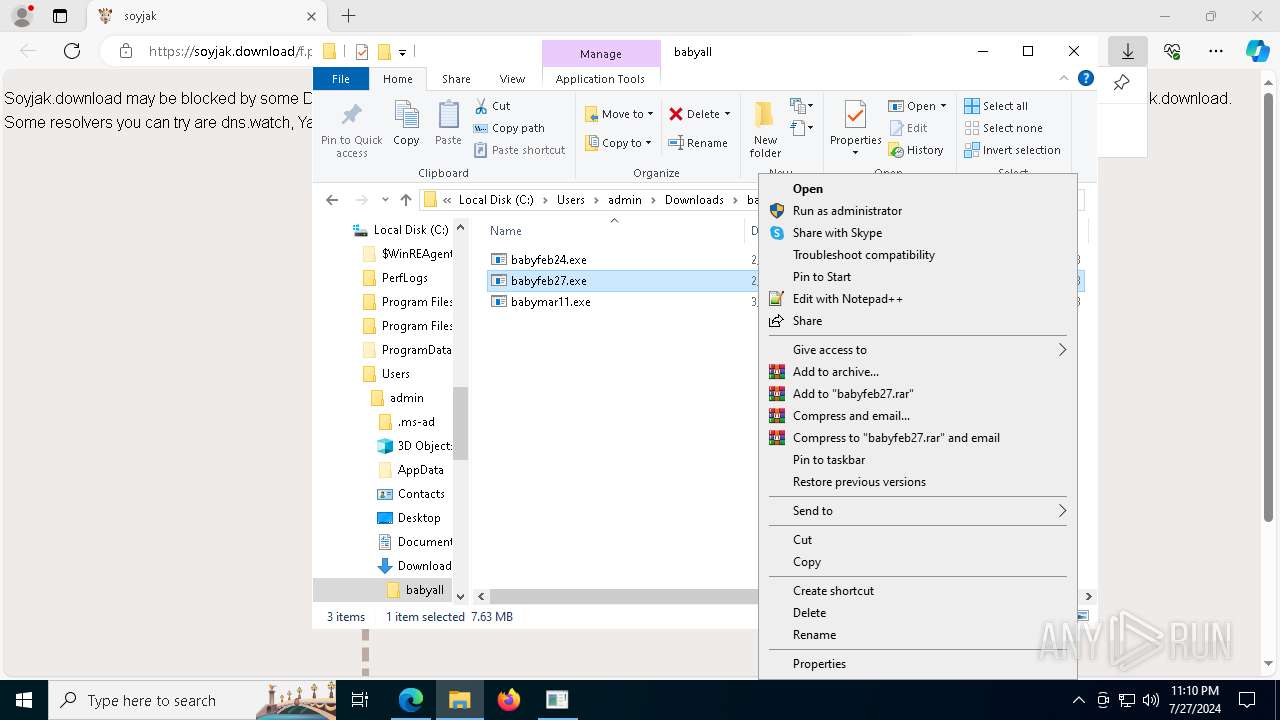
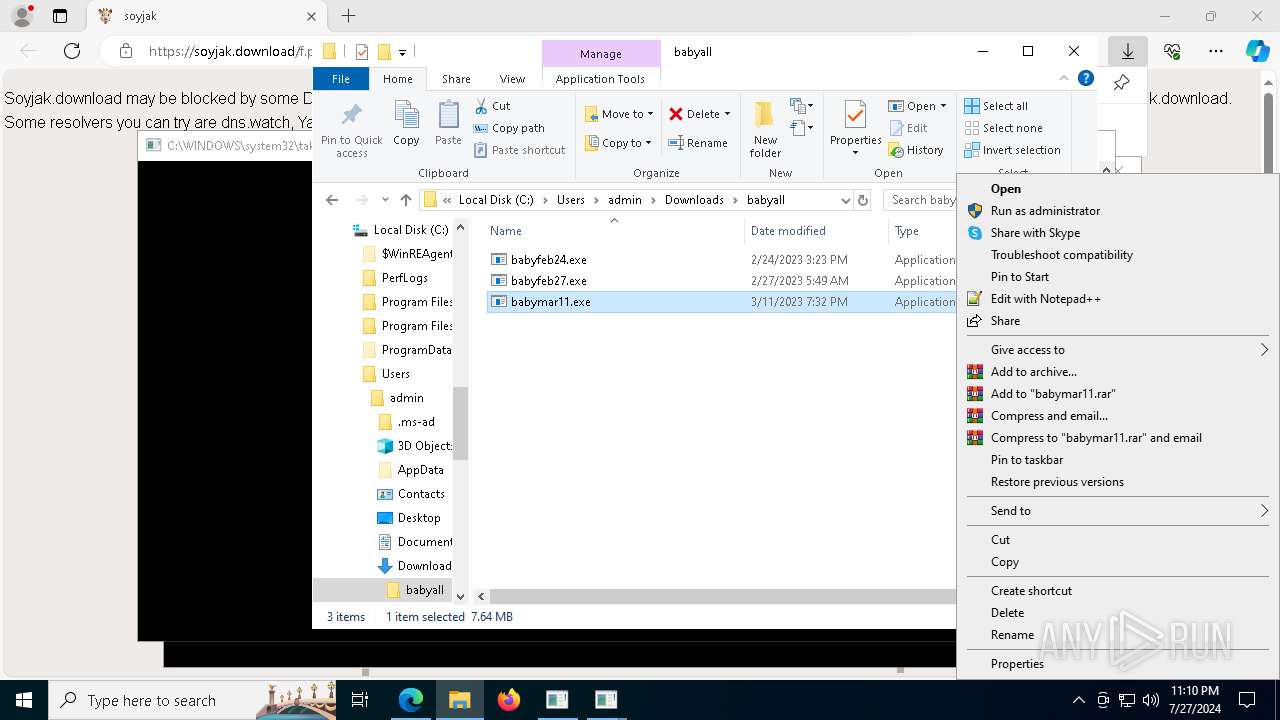
Starts POWERSHELL.EXE for commands execution
- babyfeb27.exe (PID: 1644)
- babymar11.exe (PID: 3360)
- babyfeb27.exe (PID: 5948)
- babymar11.exe (PID: 5296)
The process bypasses the loading of PowerShell profile settings
- babyfeb27.exe (PID: 1644)
- babymar11.exe (PID: 3360)
- babyfeb27.exe (PID: 5948)
- babymar11.exe (PID: 5296)
The process executes Powershell scripts
- babymar11.exe (PID: 3360)
- babyfeb27.exe (PID: 1644)
- babyfeb27.exe (PID: 5948)
- babymar11.exe (PID: 5296)
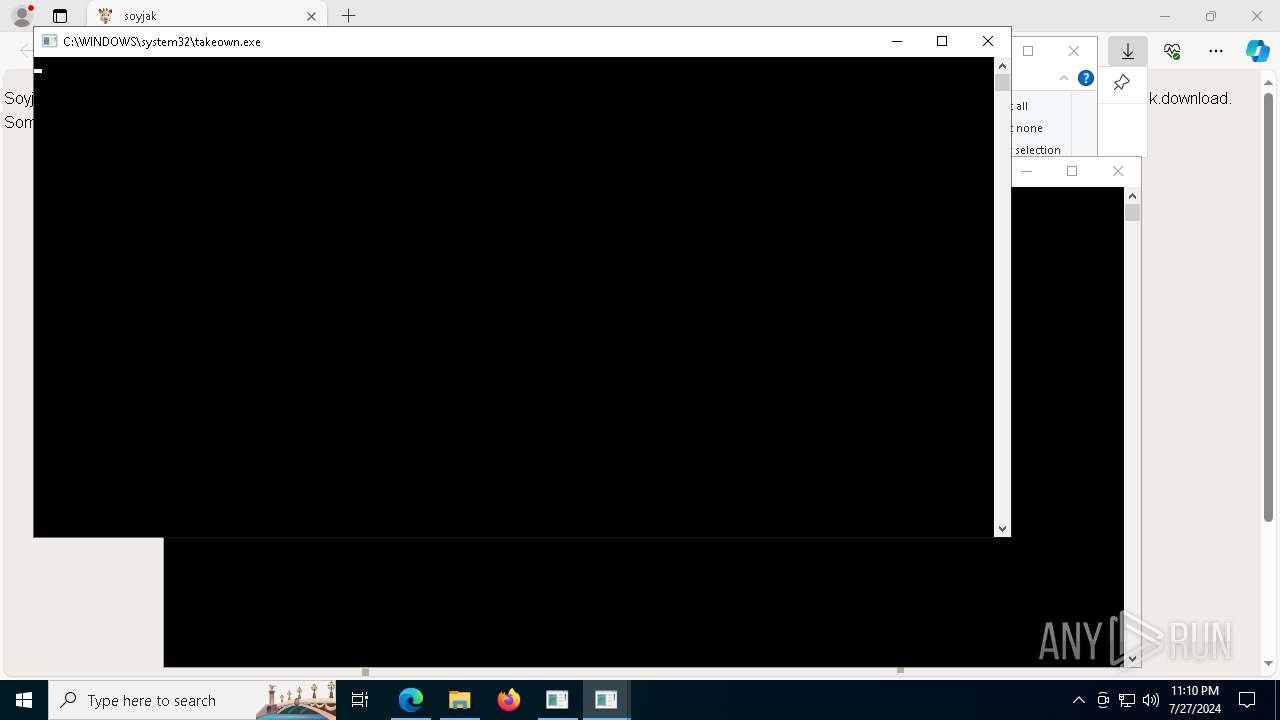
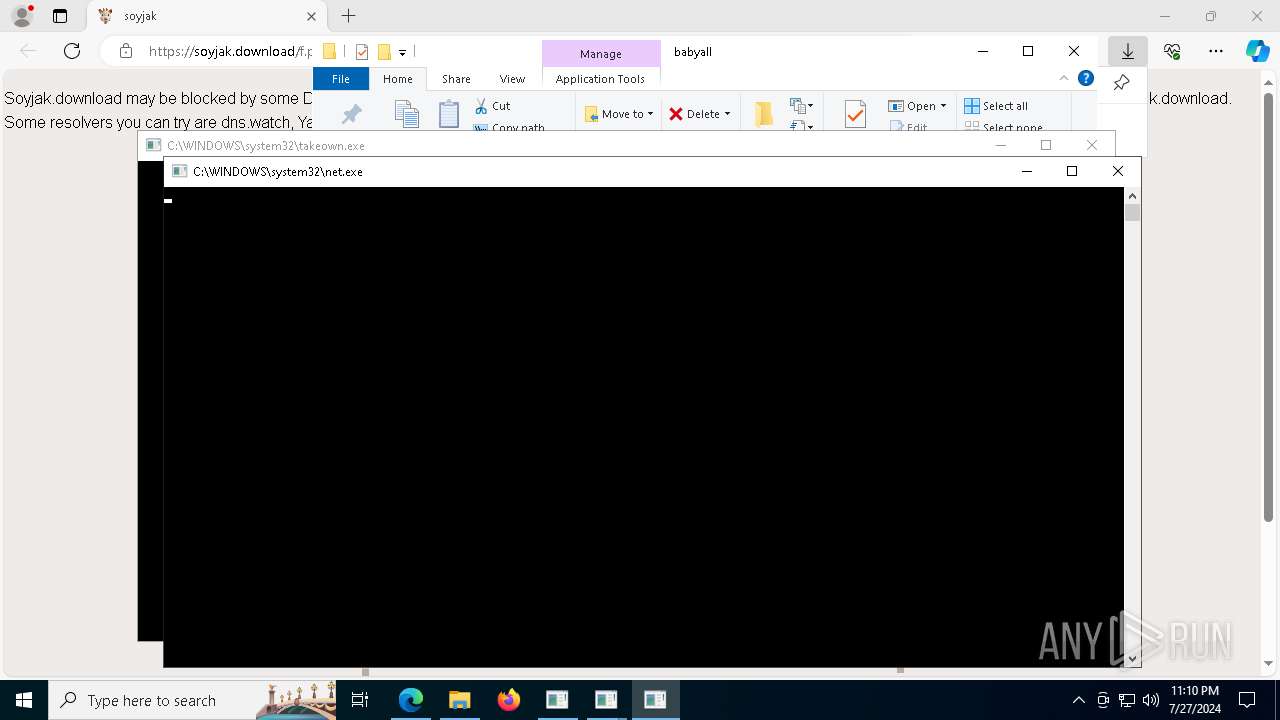
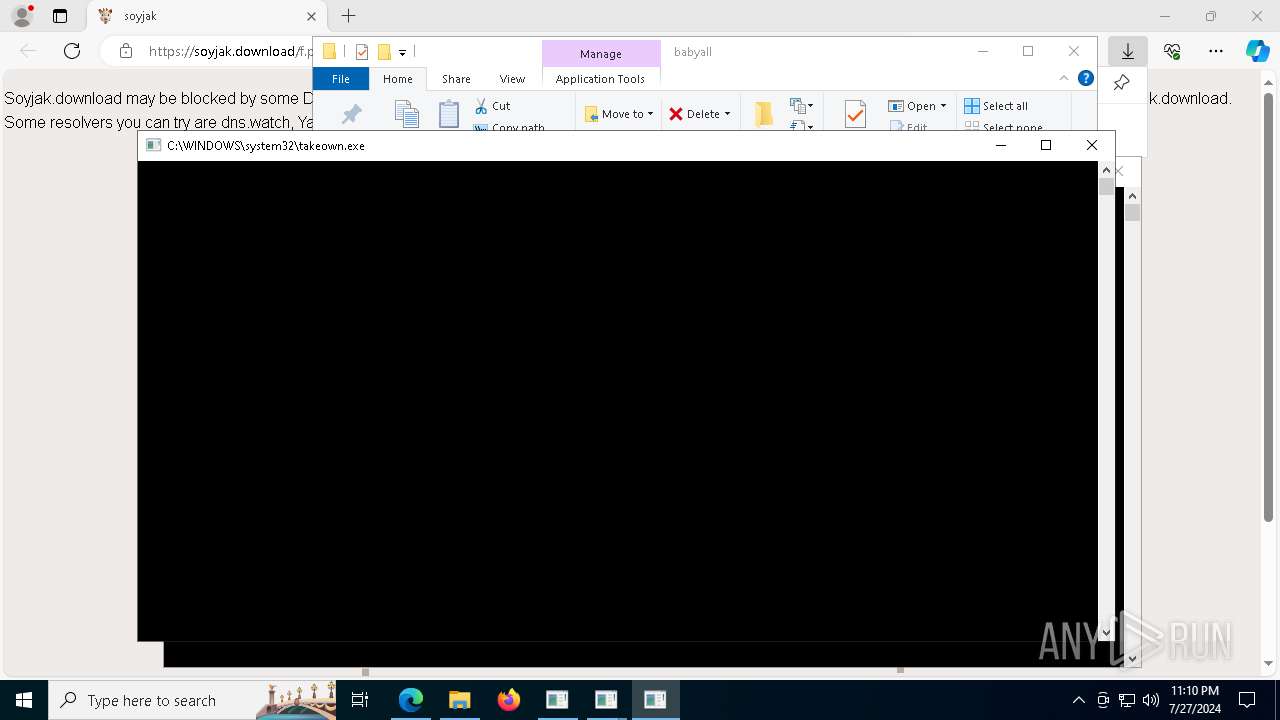
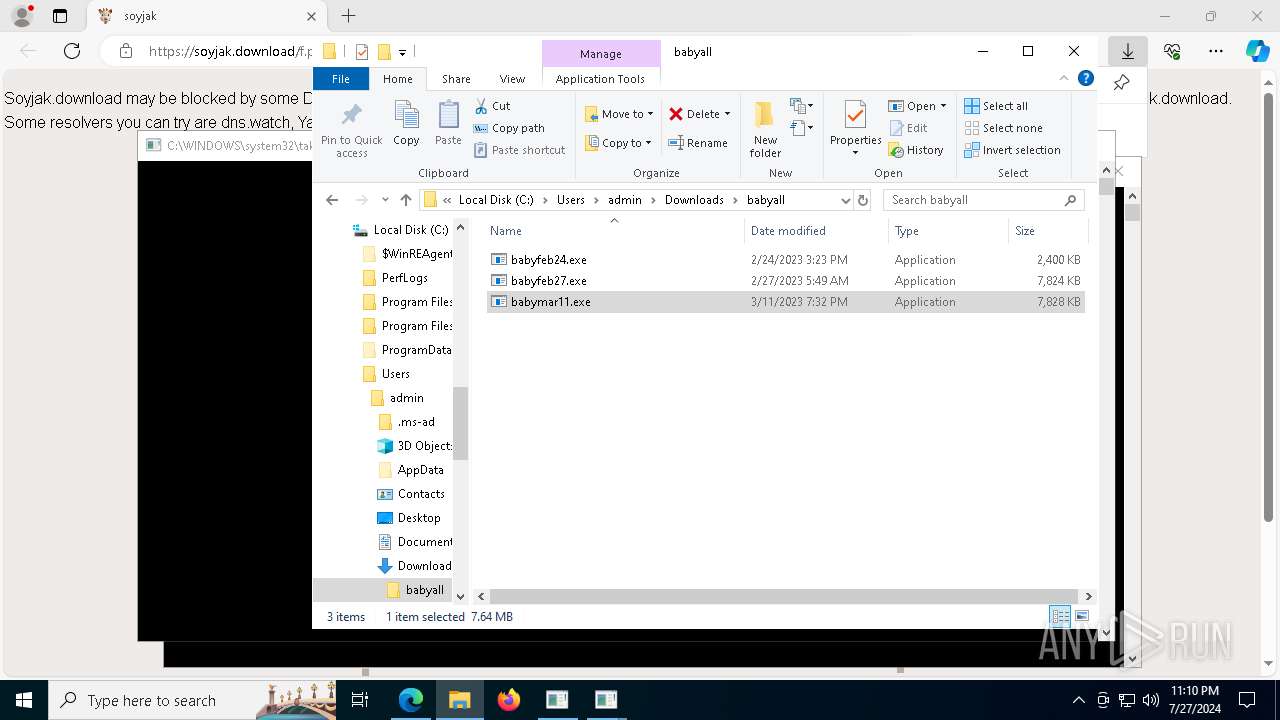
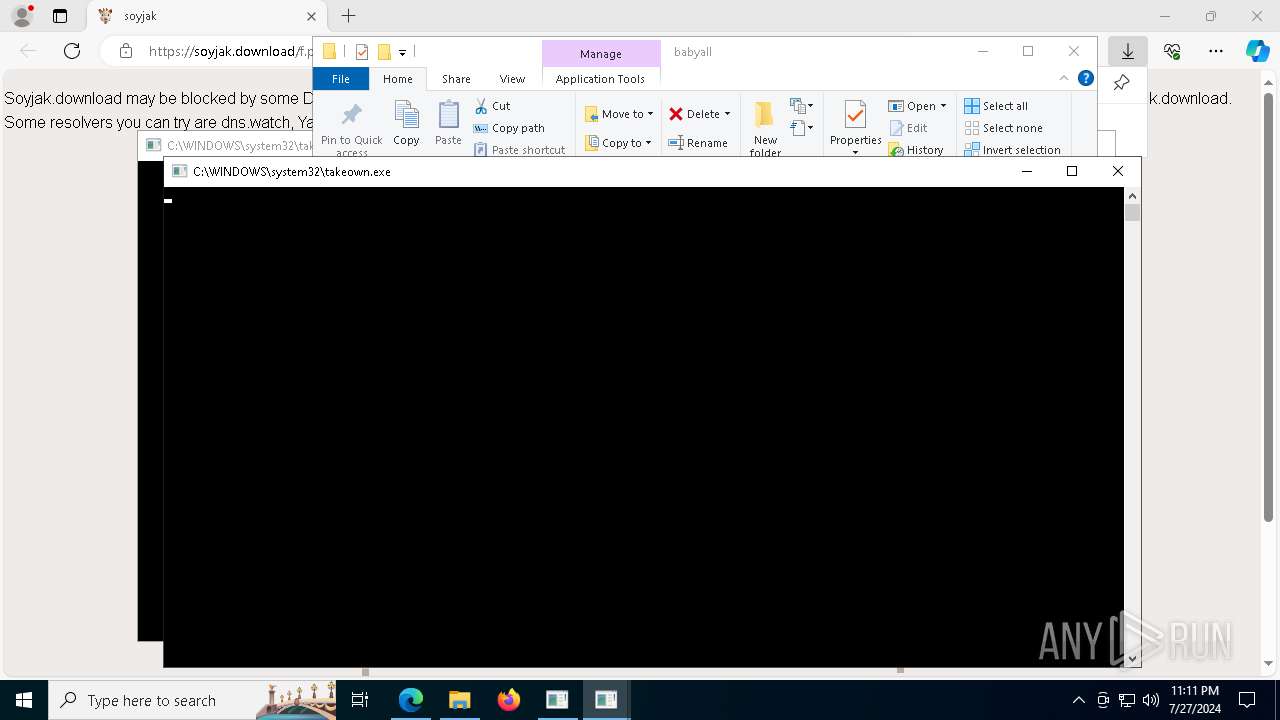
Takes ownership (TAKEOWN.EXE)
- babymar11.exe (PID: 3360)
- babyfeb27.exe (PID: 1644)
- babyfeb27.exe (PID: 5948)
- babymar11.exe (PID: 5296)
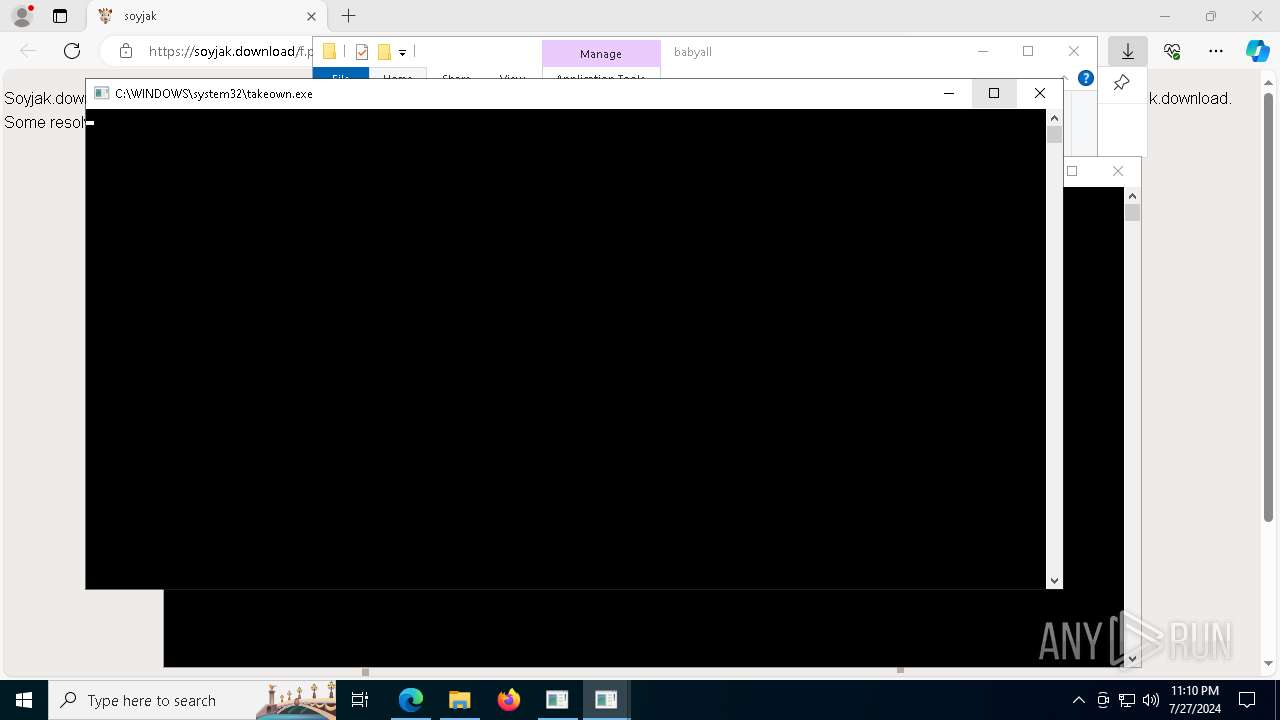
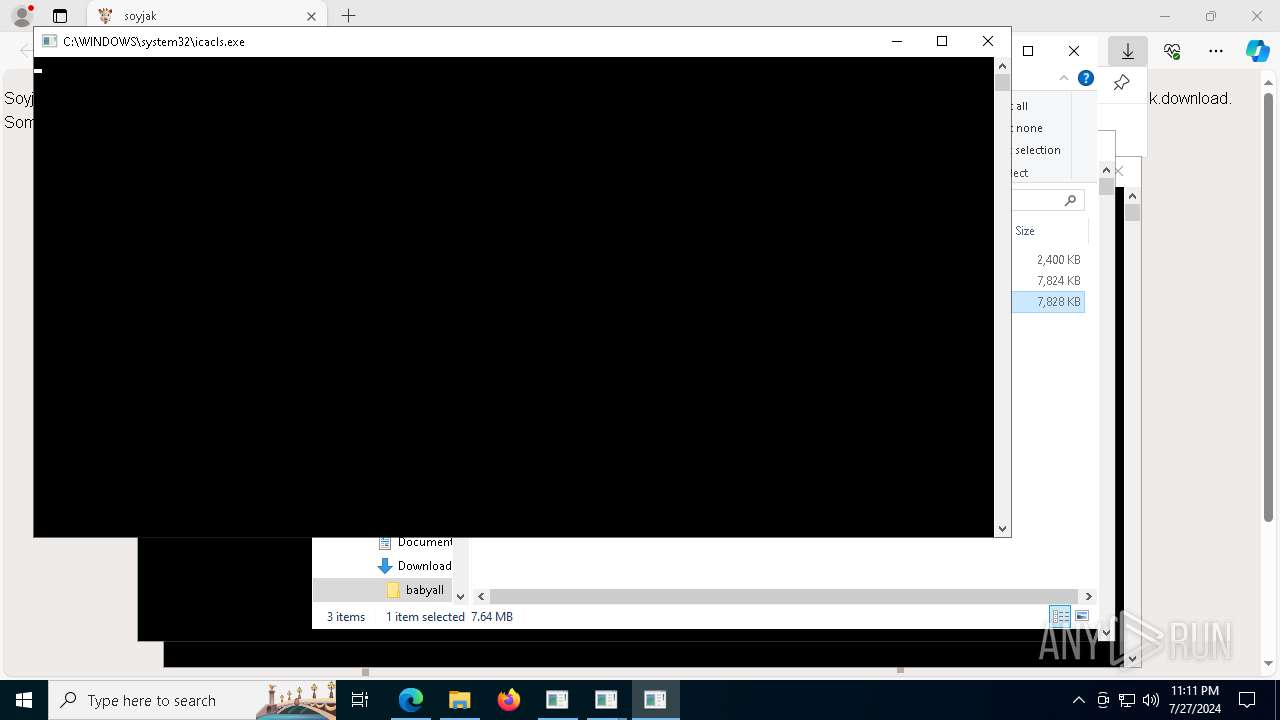
Uses ICACLS.EXE to modify access control lists
- babymar11.exe (PID: 3360)
- babymar11.exe (PID: 5296)
Detected use of alternative data streams (AltDS)
- babymar11.exe (PID: 3360)
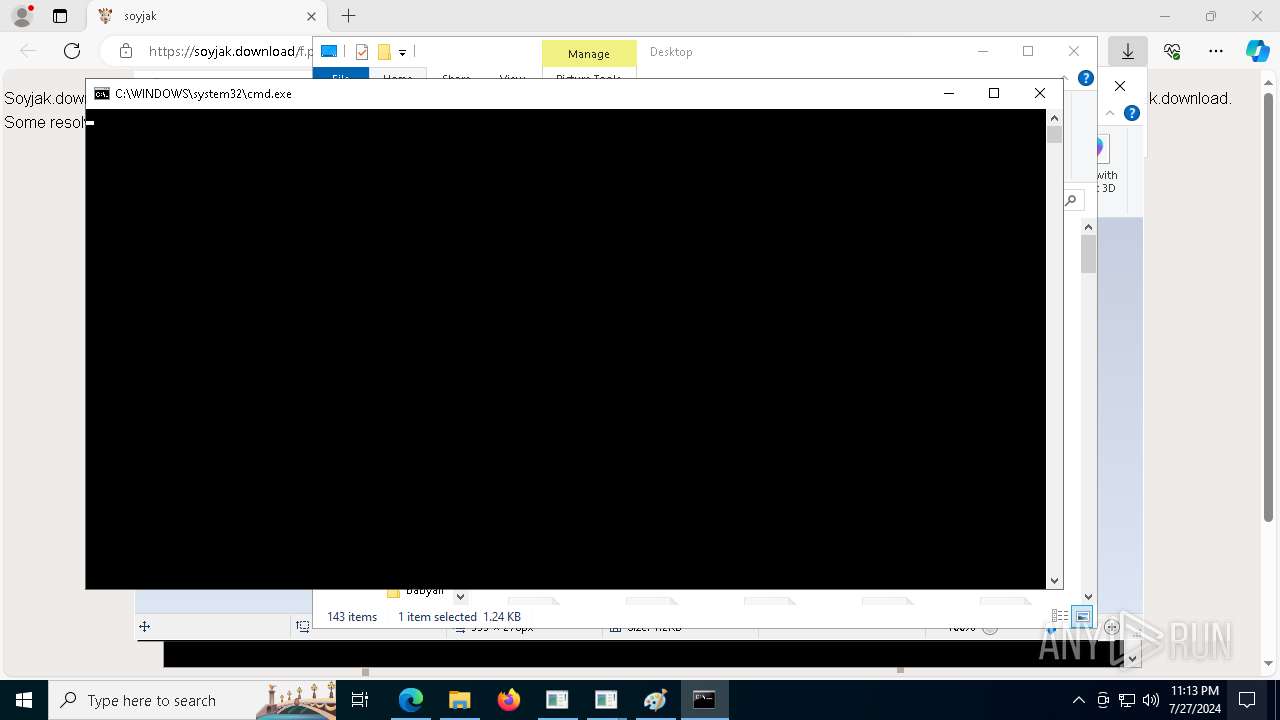
Starts CMD.EXE for commands execution
- babymar11.exe (PID: 3360)
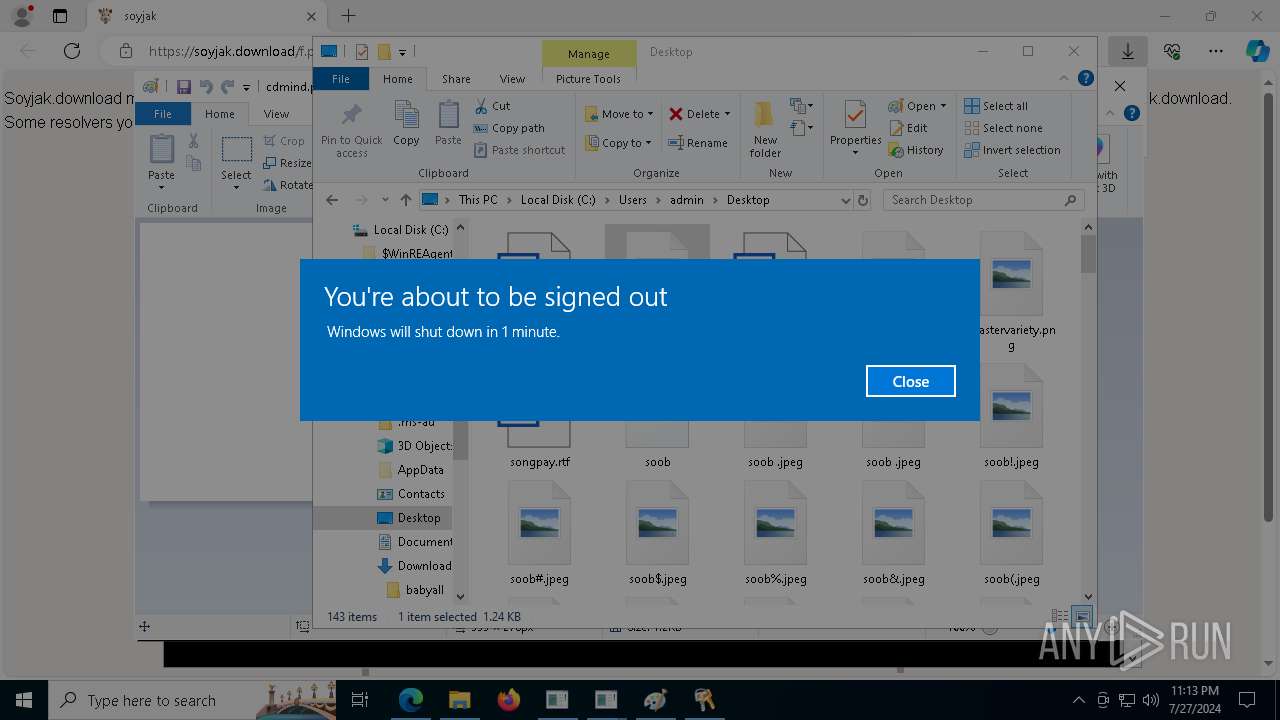
The system shut down or reboot
- cmd.exe (PID: 7036)
INFO
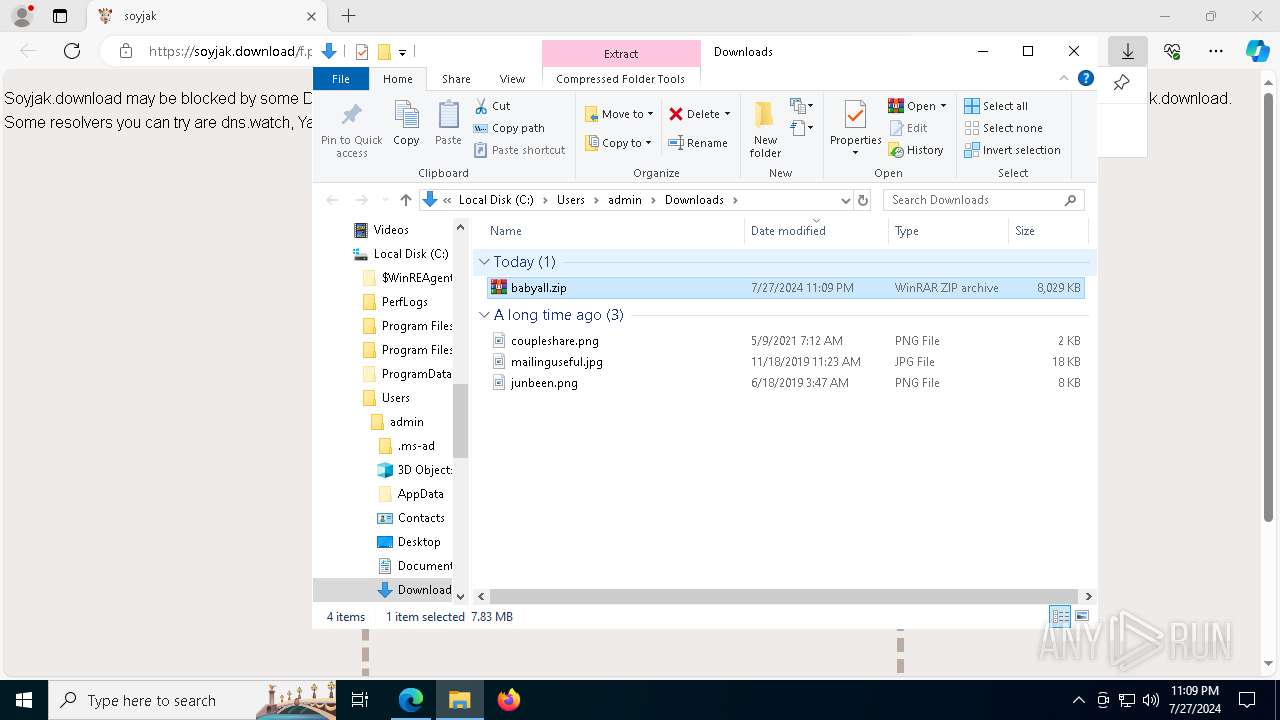
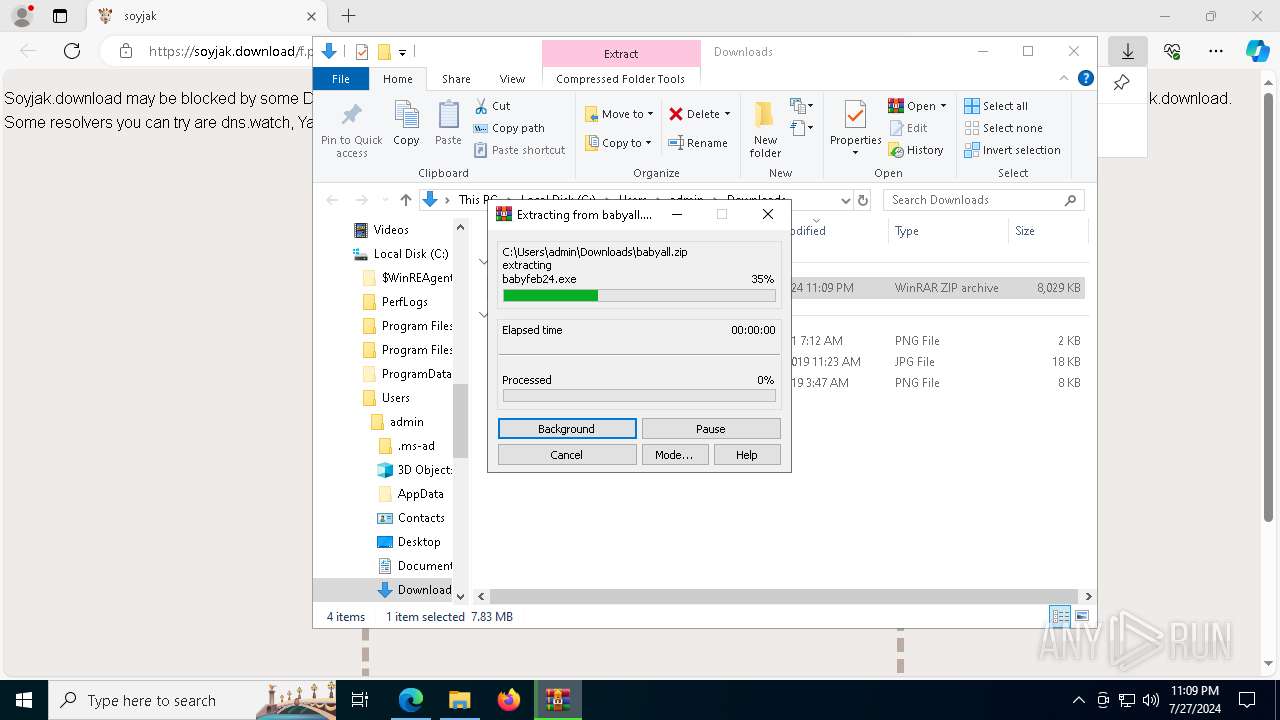
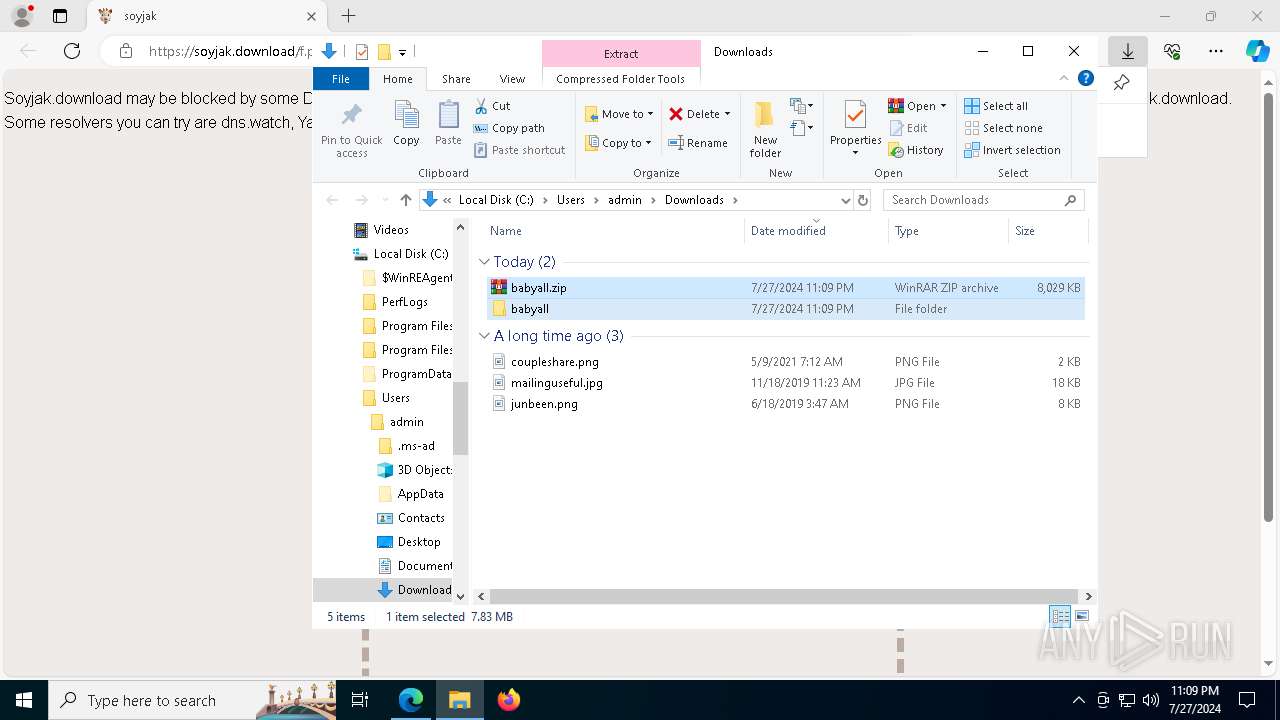
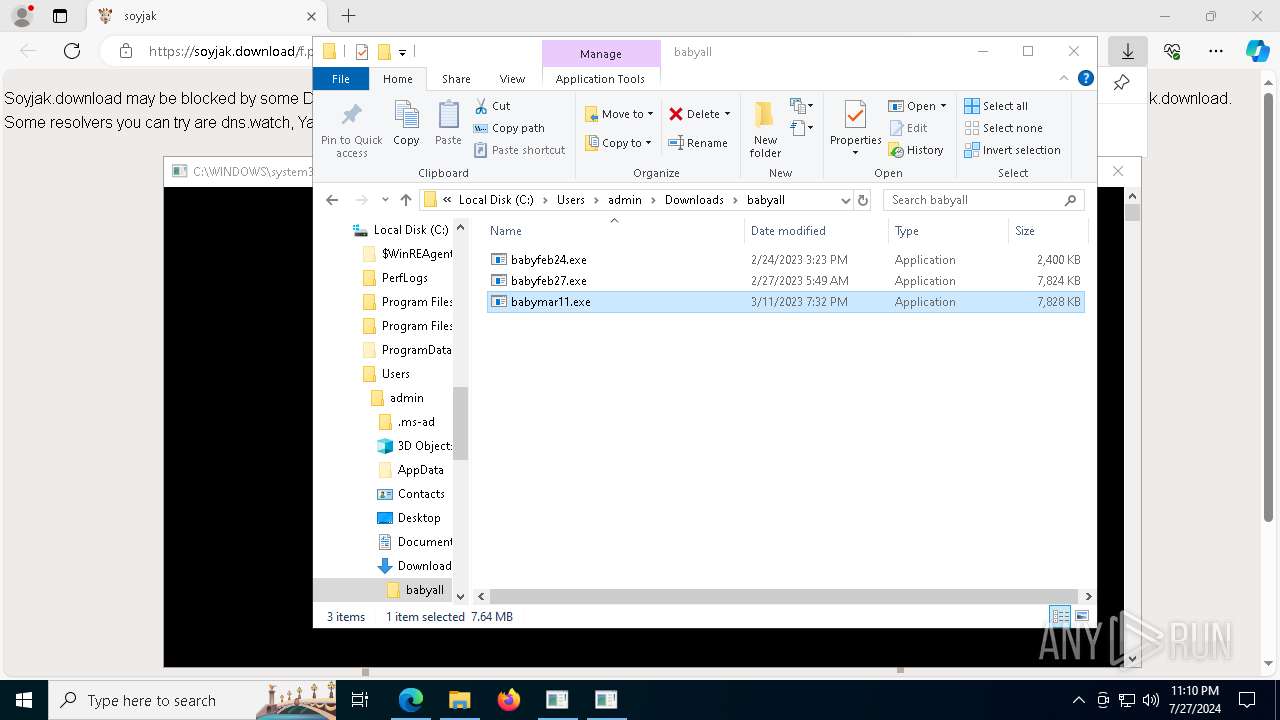
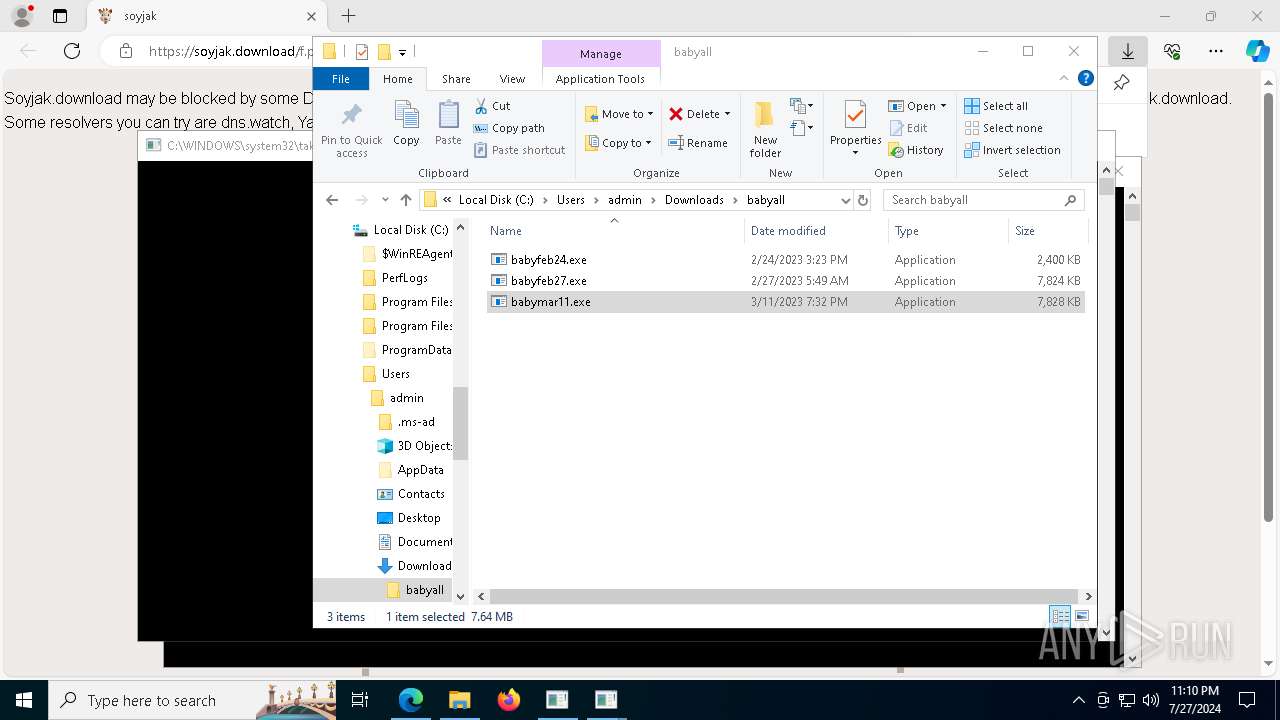
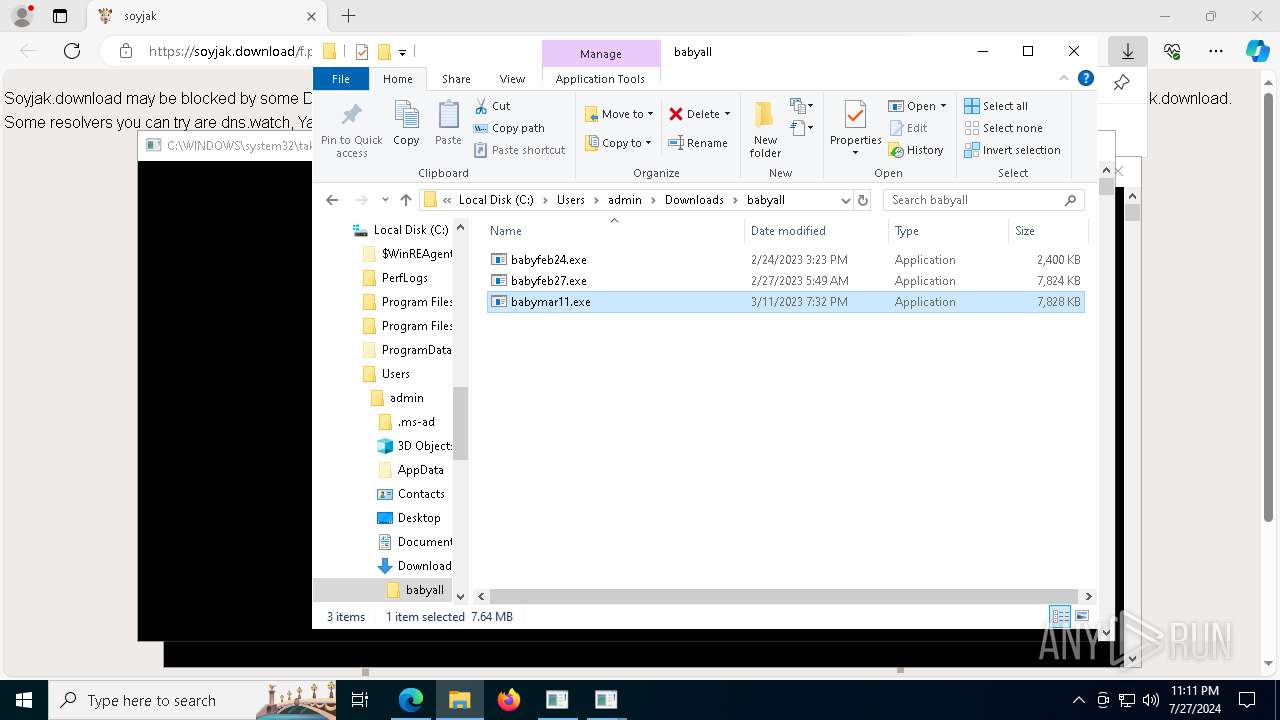
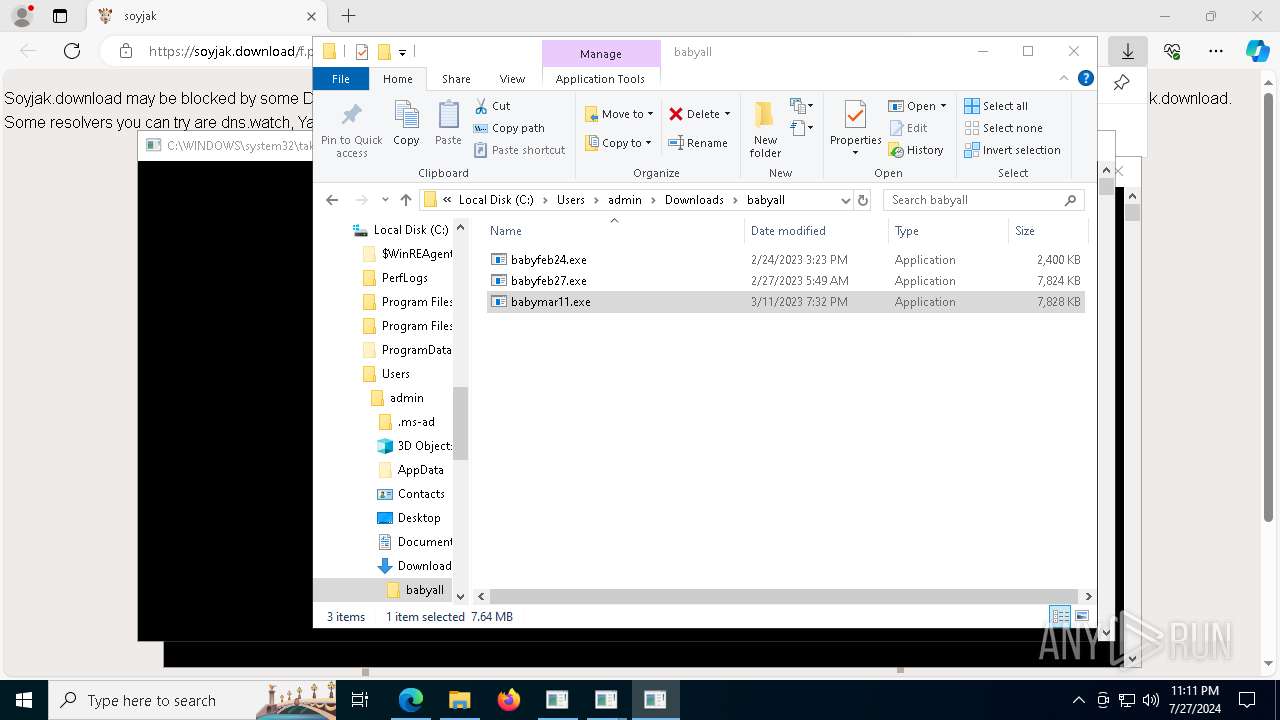
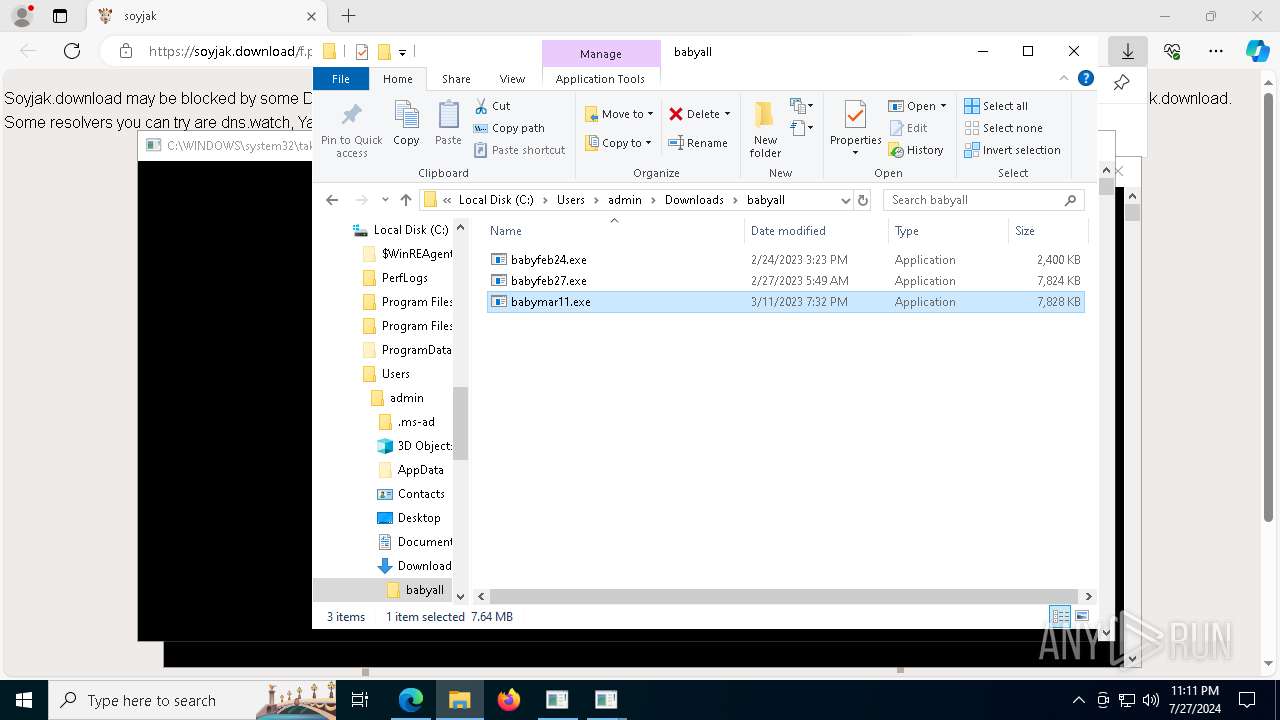
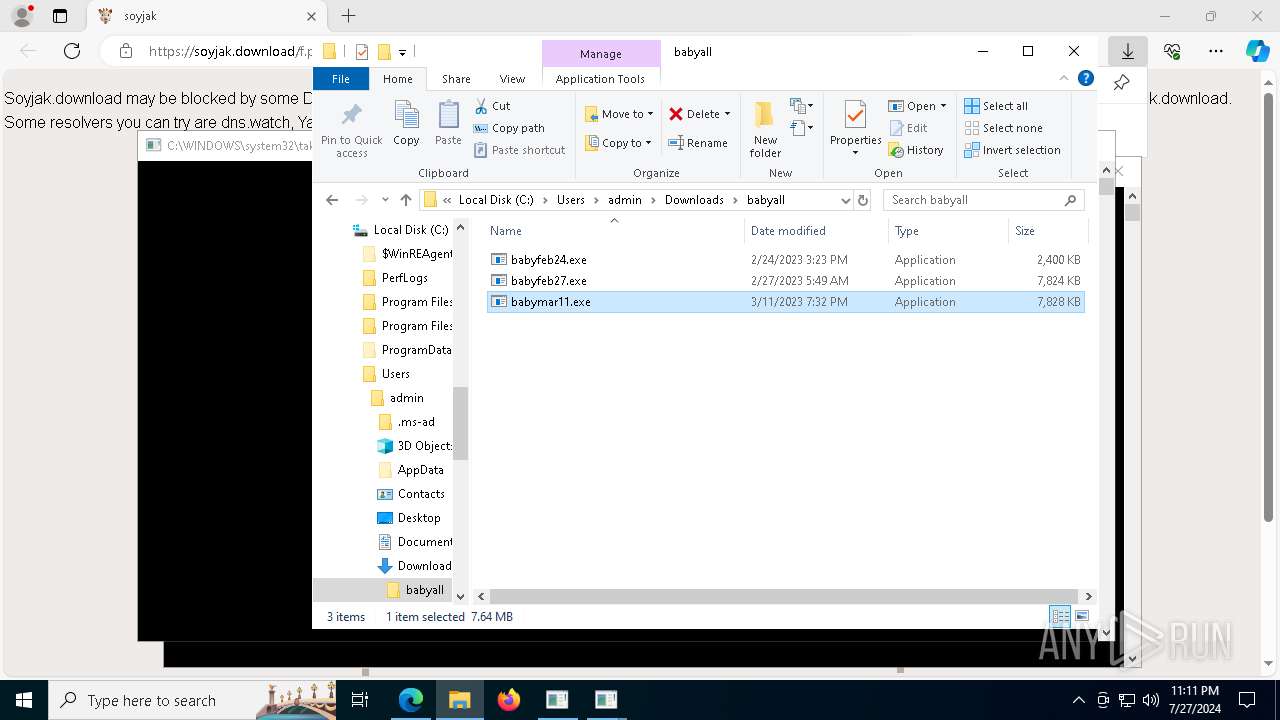
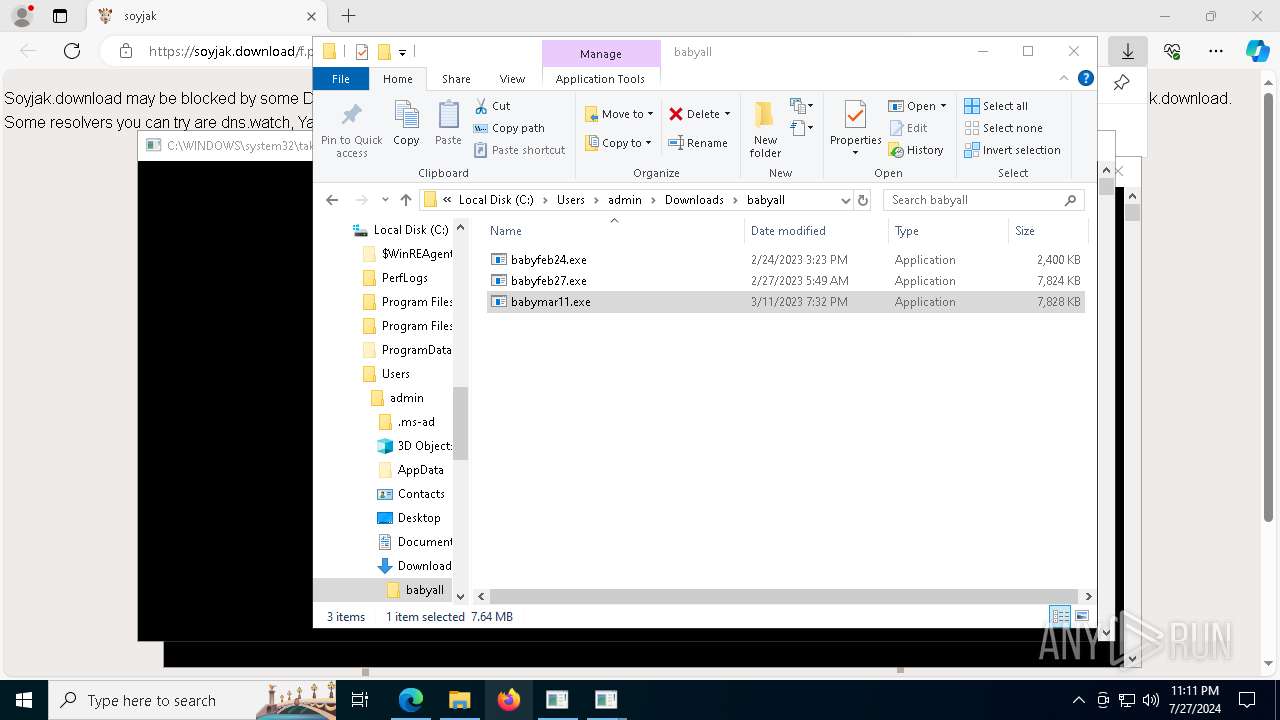
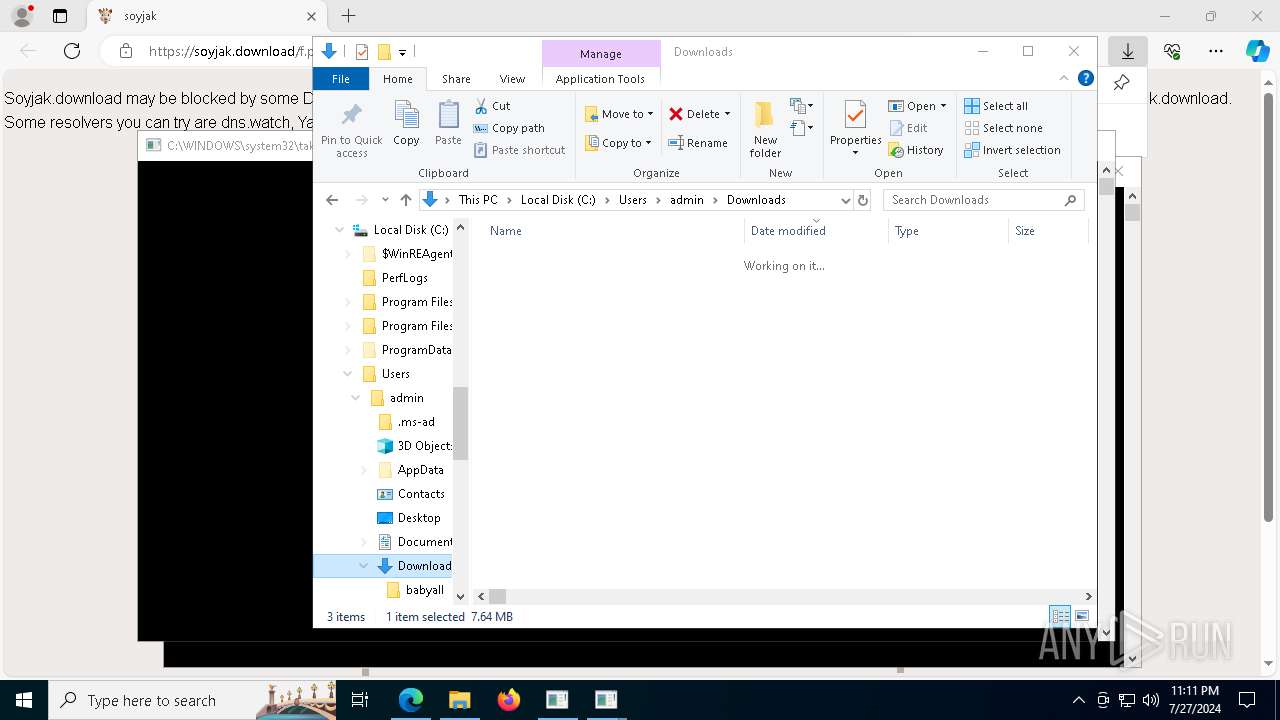
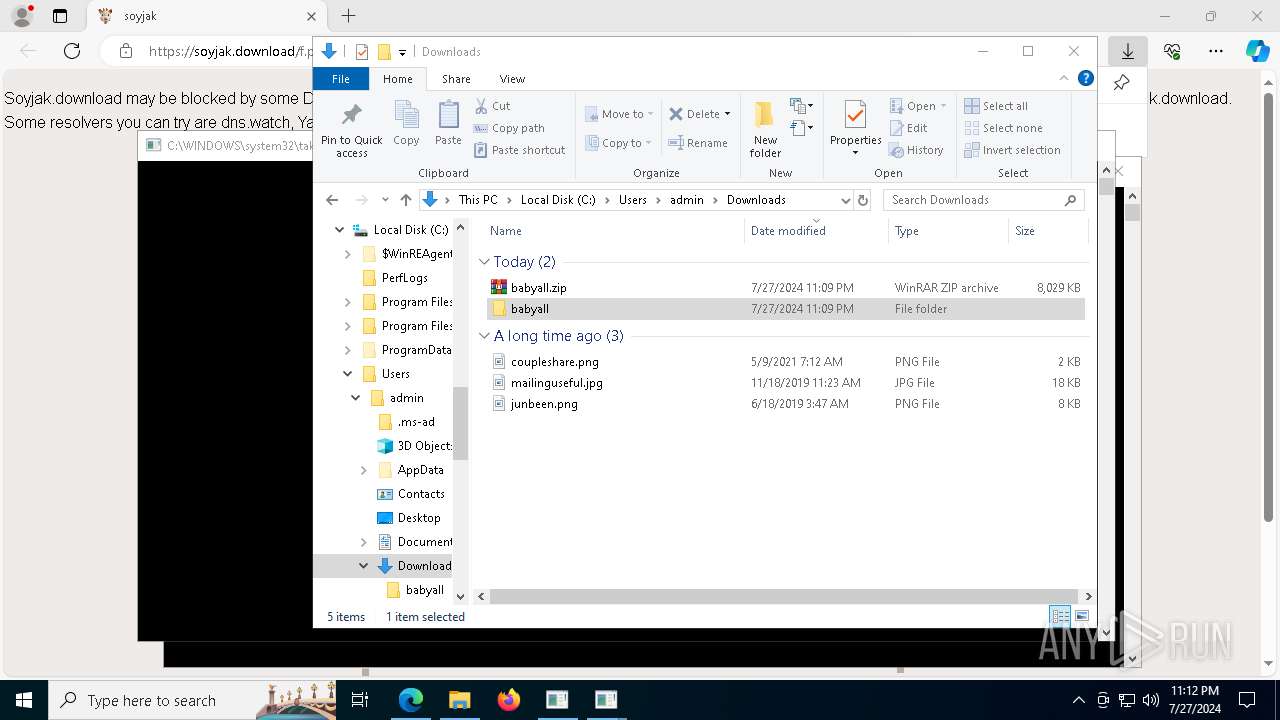
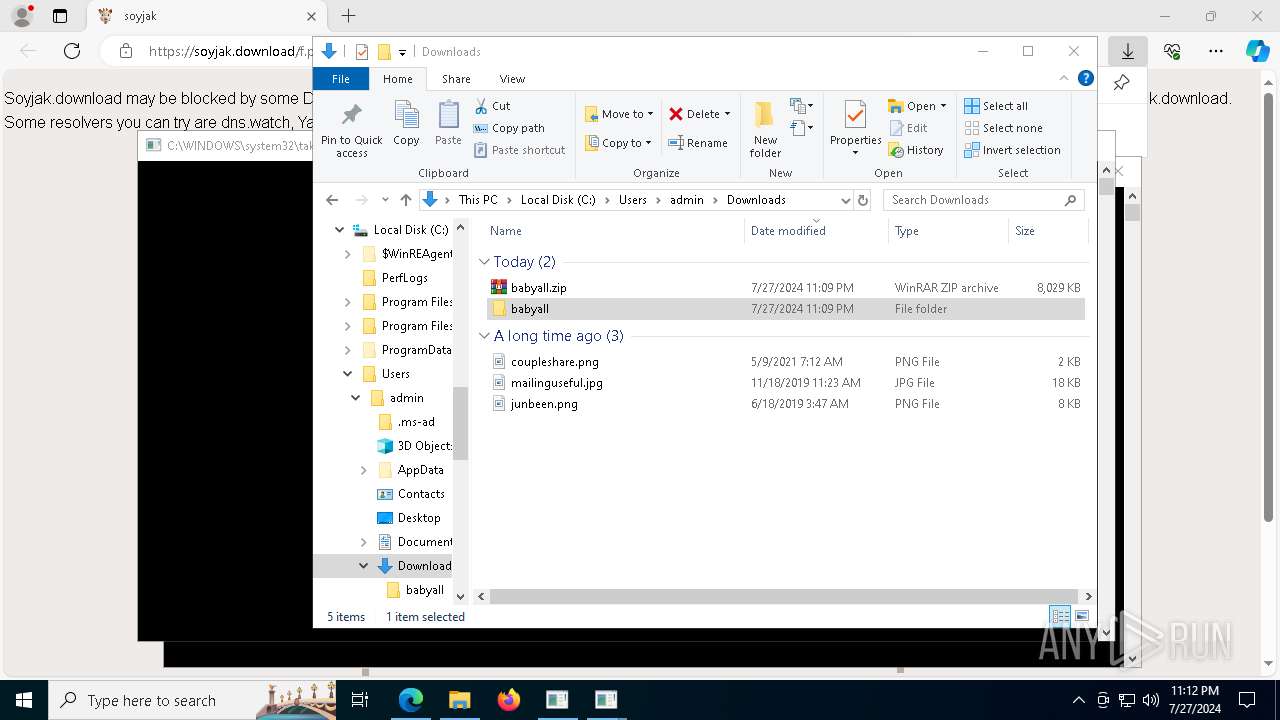
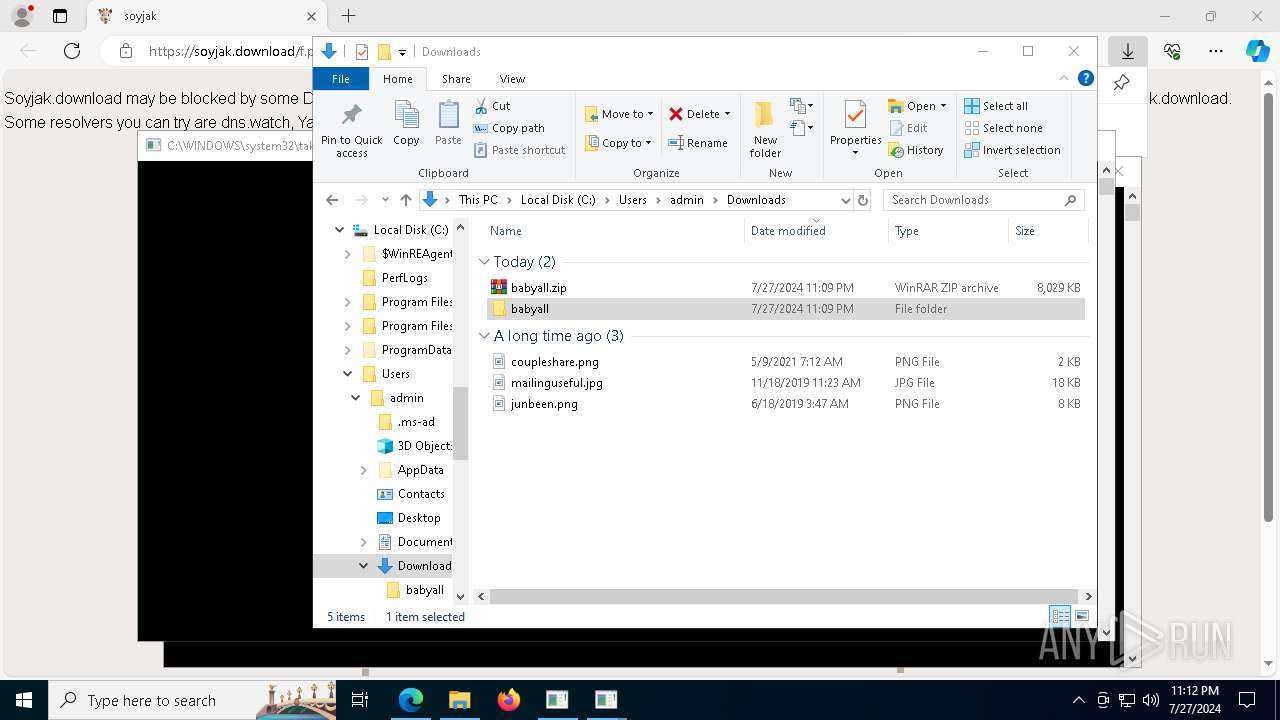
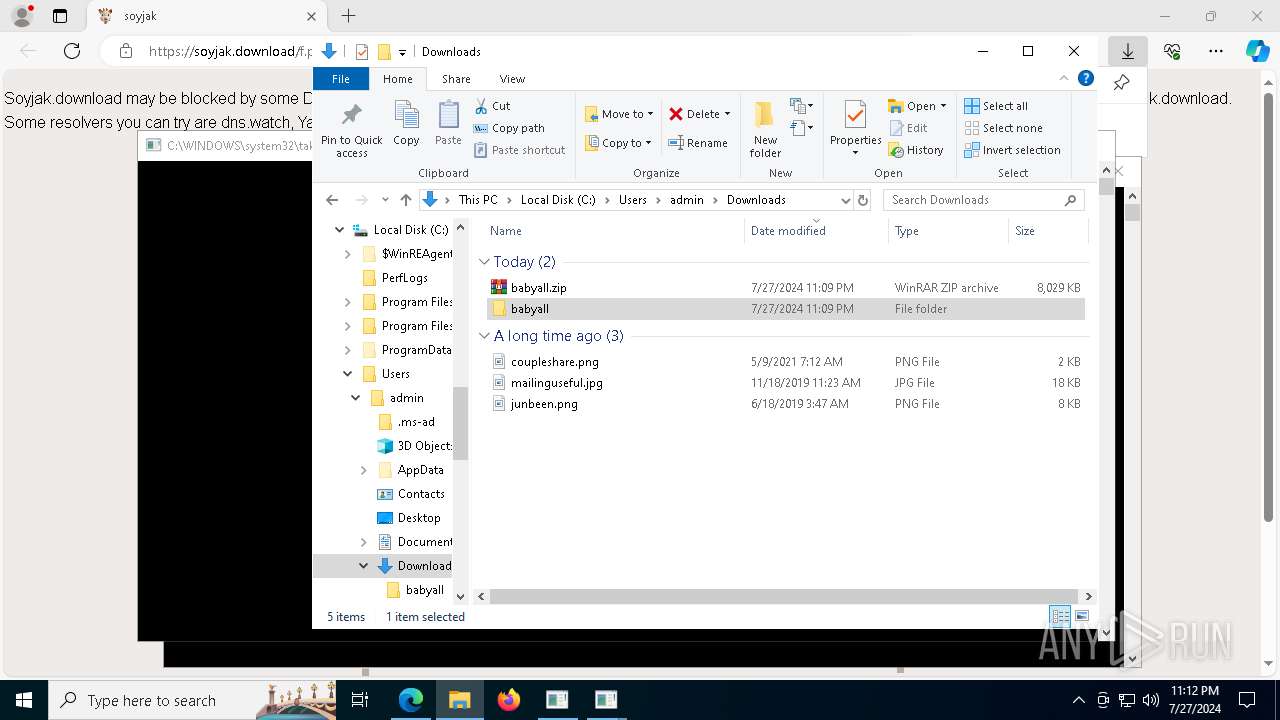
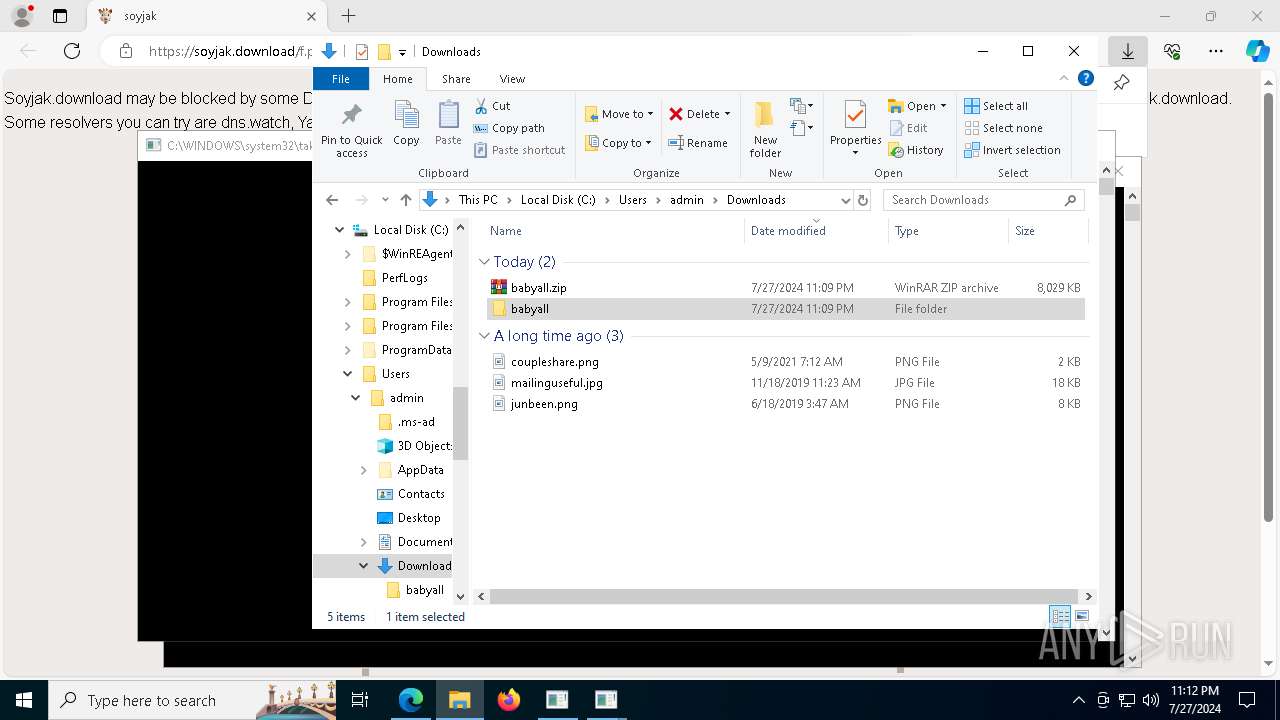
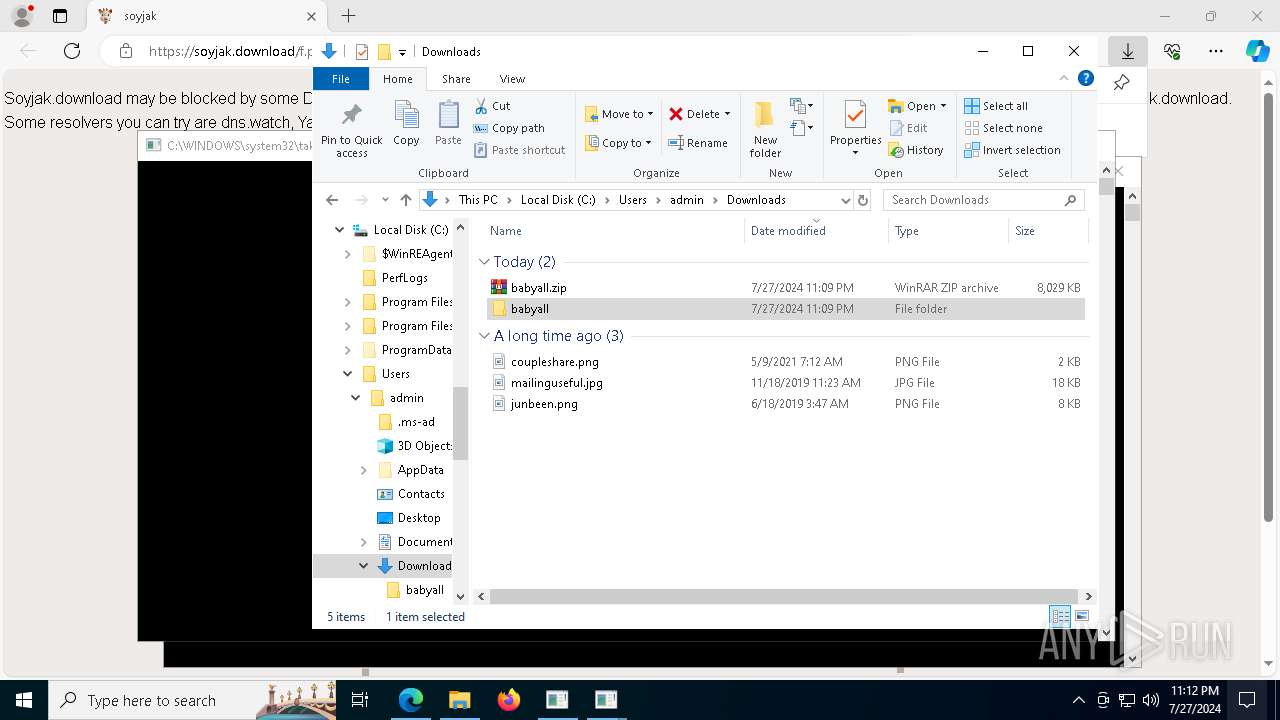
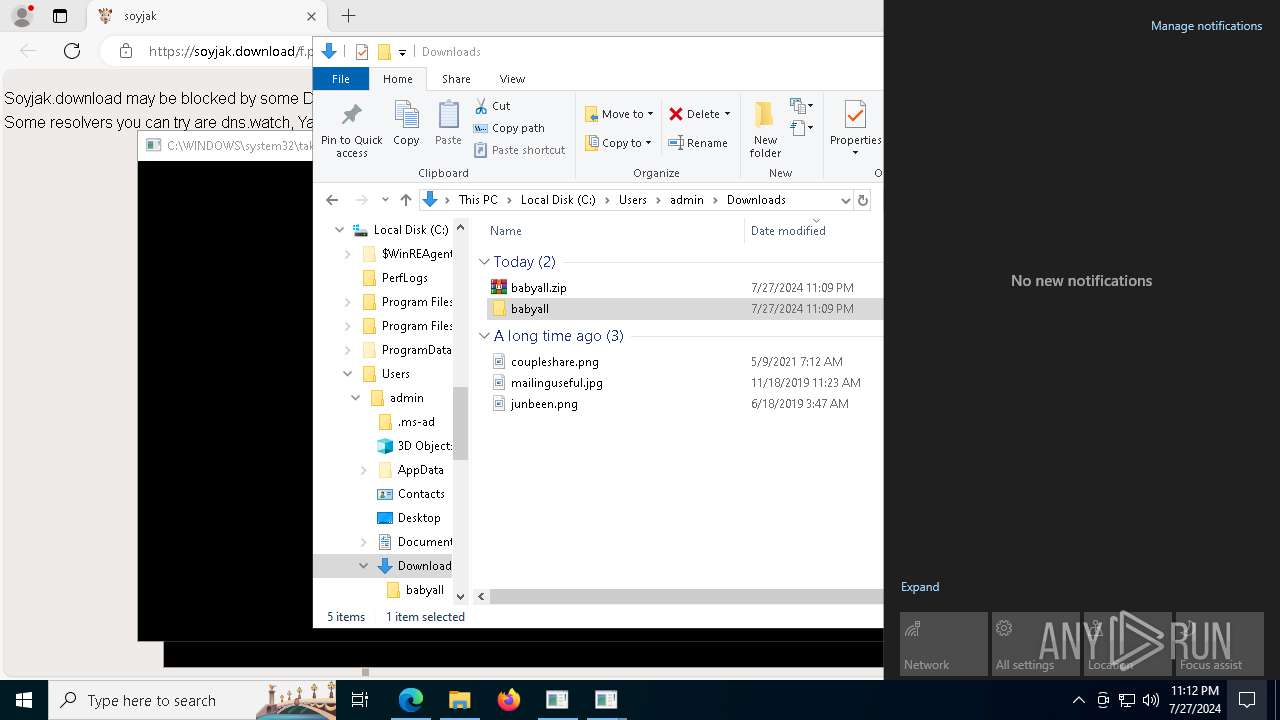
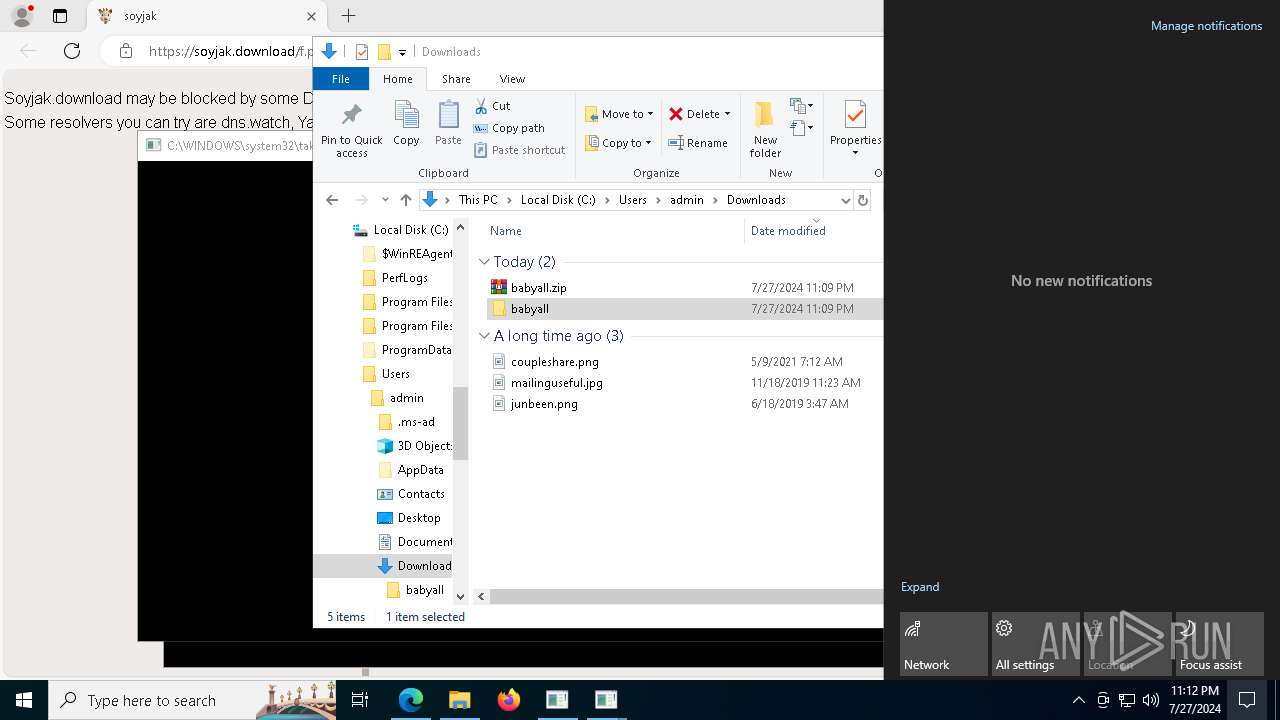
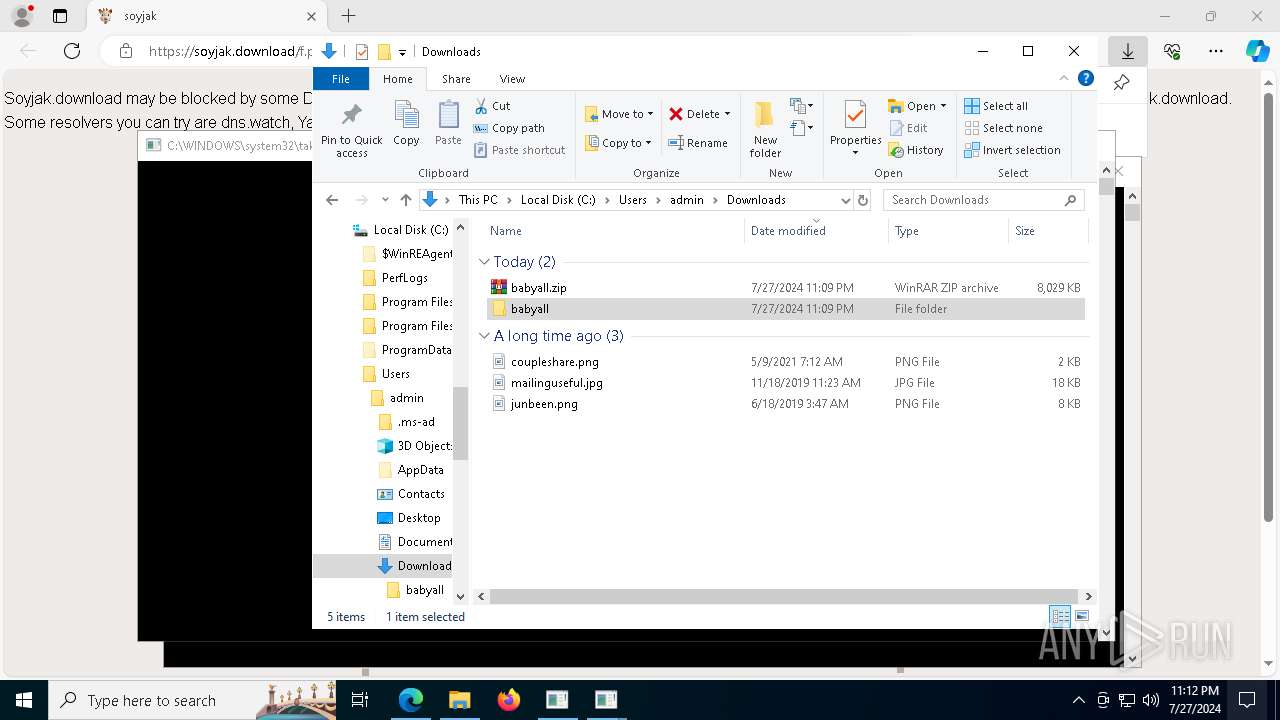
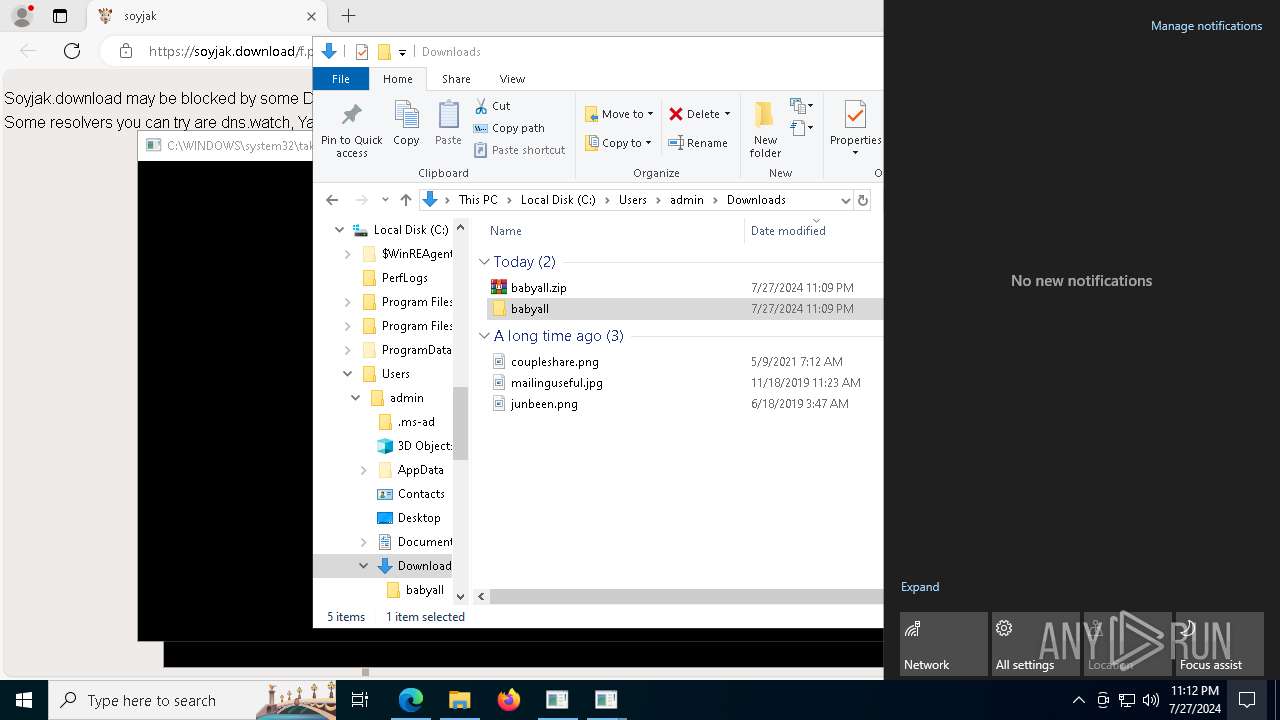
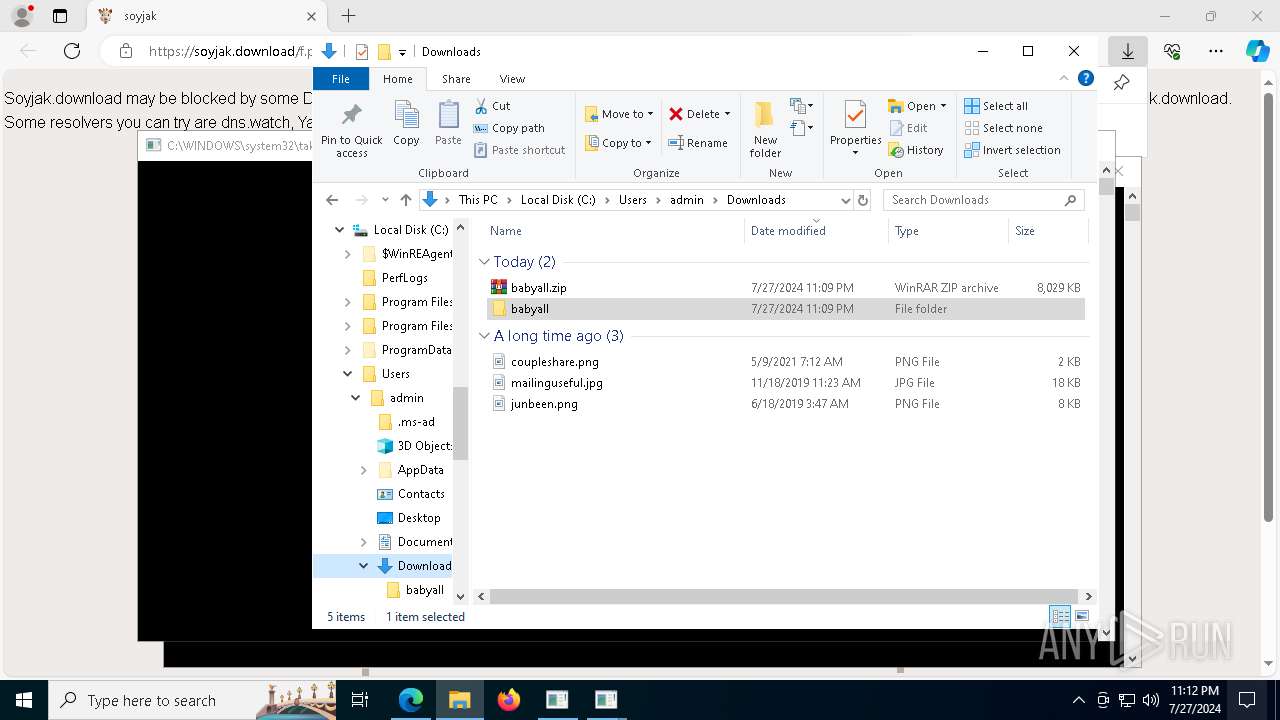
Drops the executable file immediately after the start
- msedge.exe (PID: 132)
- msedge.exe (PID: 7216)
- WinRAR.exe (PID: 1780)
The process uses the downloaded file
- msedge.exe (PID: 6124)
- WinRAR.exe (PID: 1780)
Reads Environment values
- identity_helper.exe (PID: 6224)
Reads the computer name
- identity_helper.exe (PID: 6224)
Checks supported languages
- identity_helper.exe (PID: 6224)
- babyfeb27.exe (PID: 1644)
- babymar11.exe (PID: 3360)
- babyfeb27.exe (PID: 5948)
- babyfeb24.exe (PID: 3656)
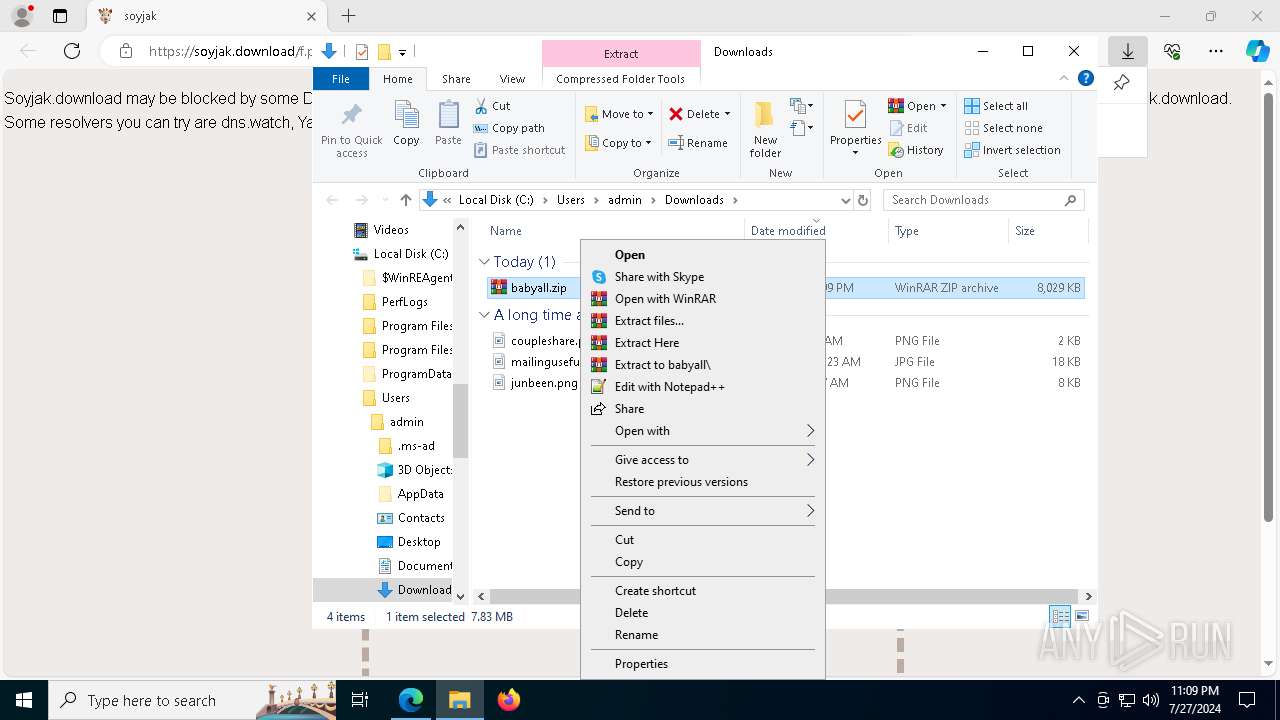
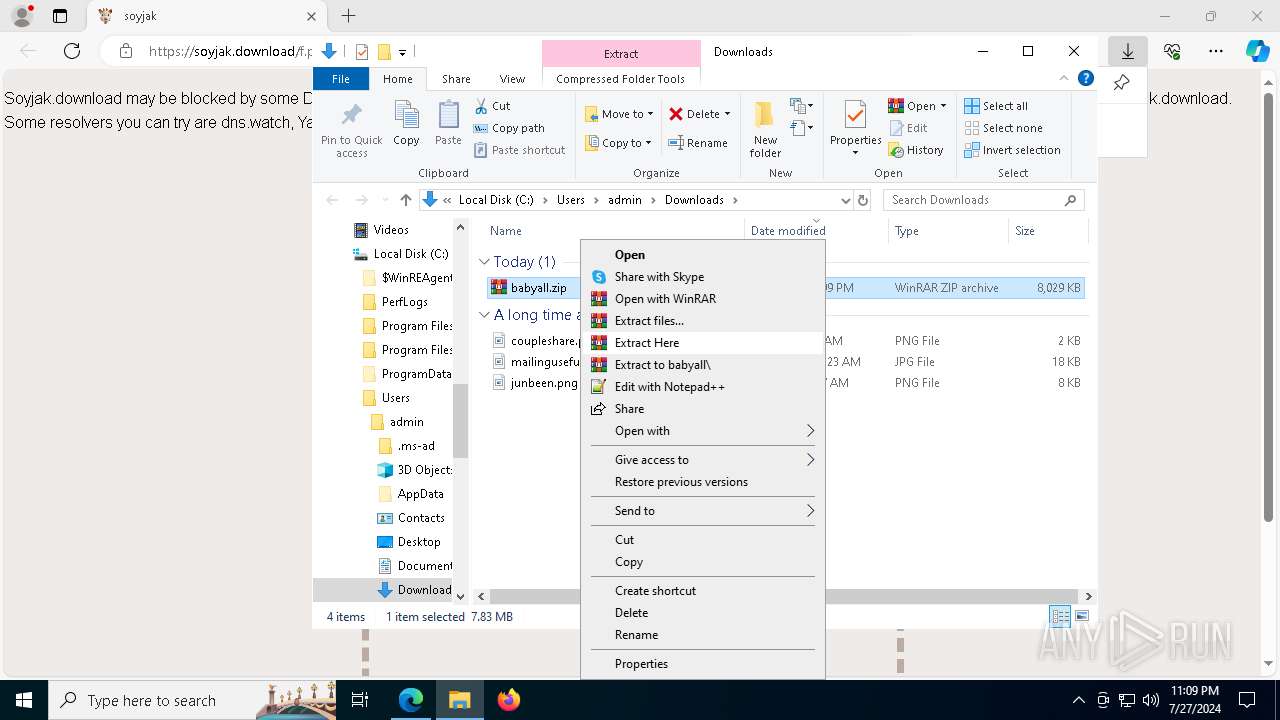
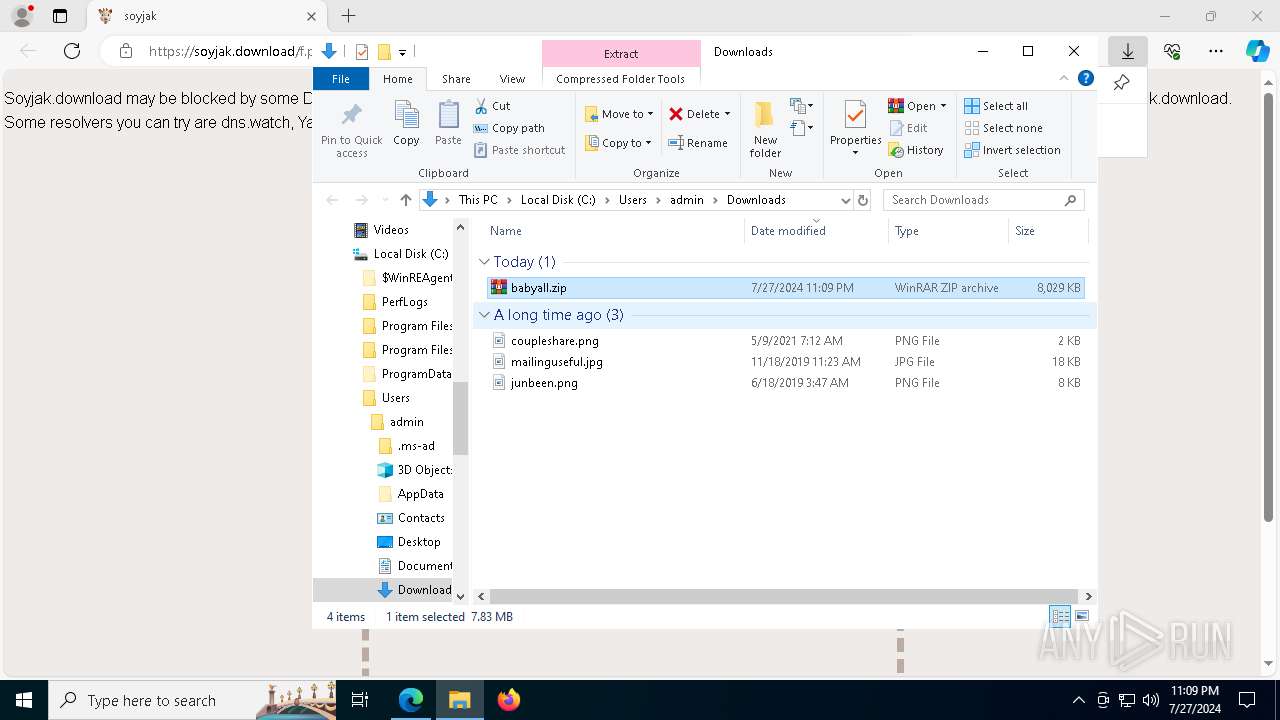
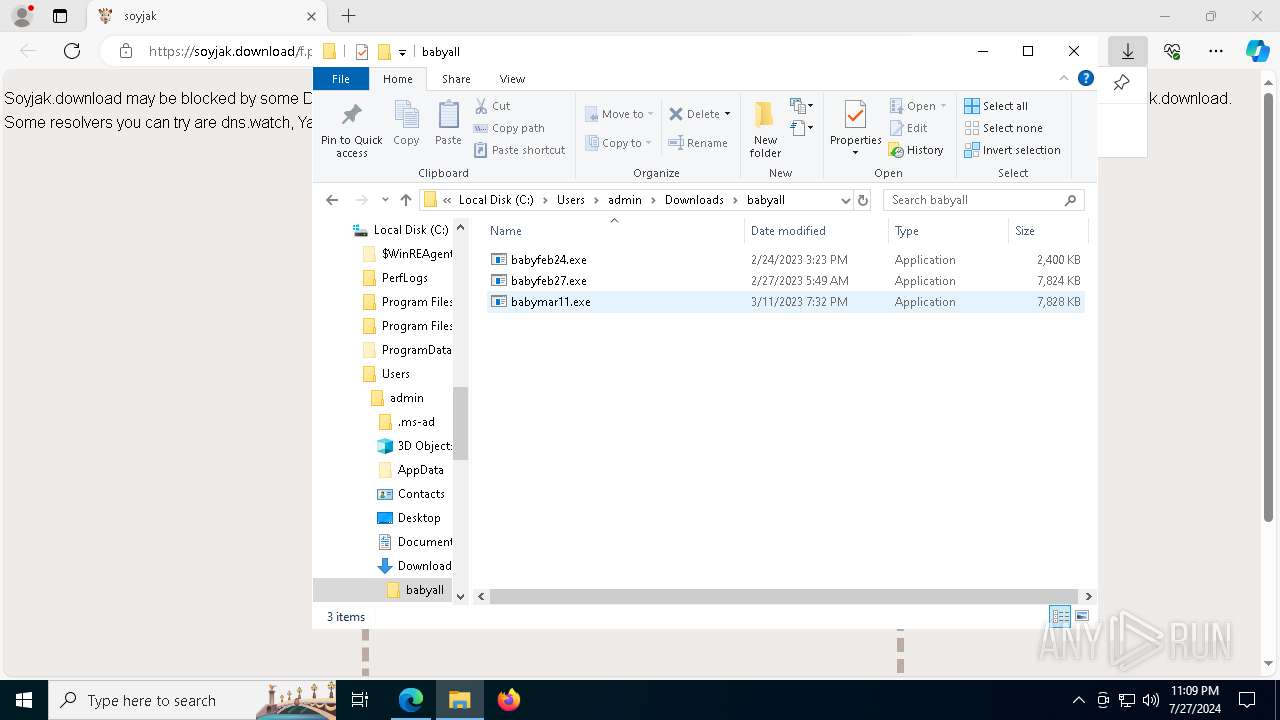
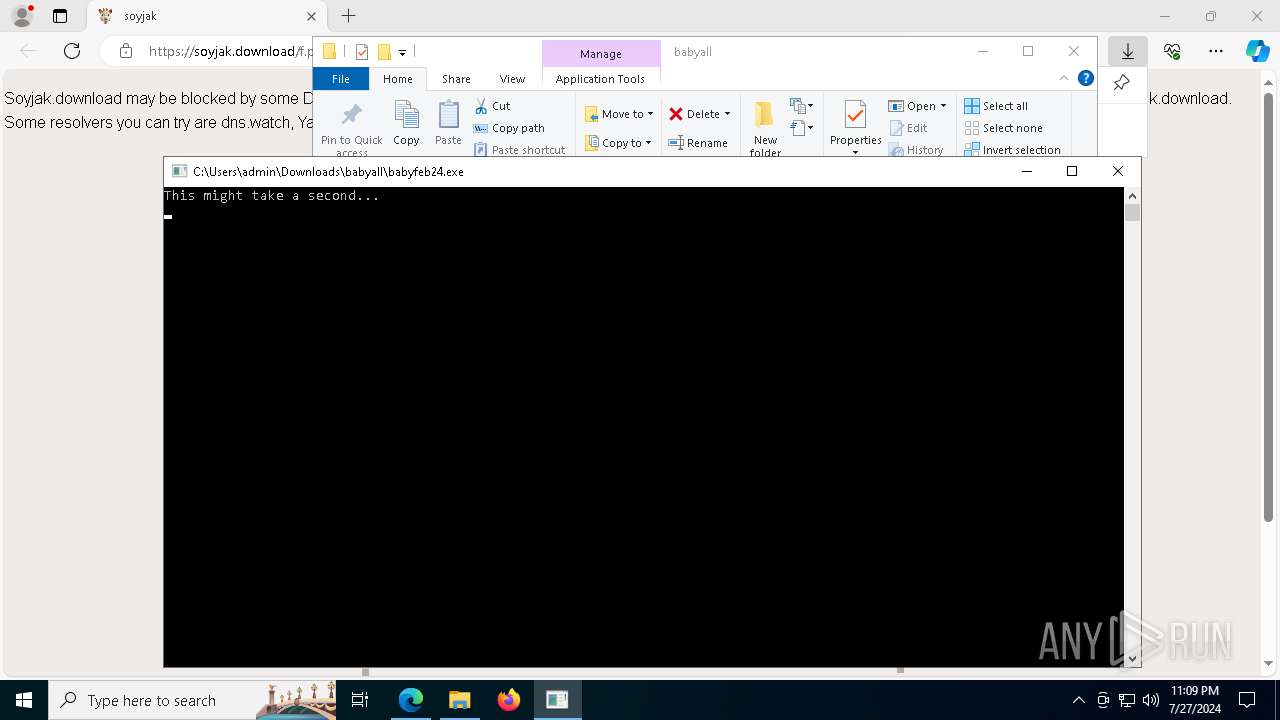
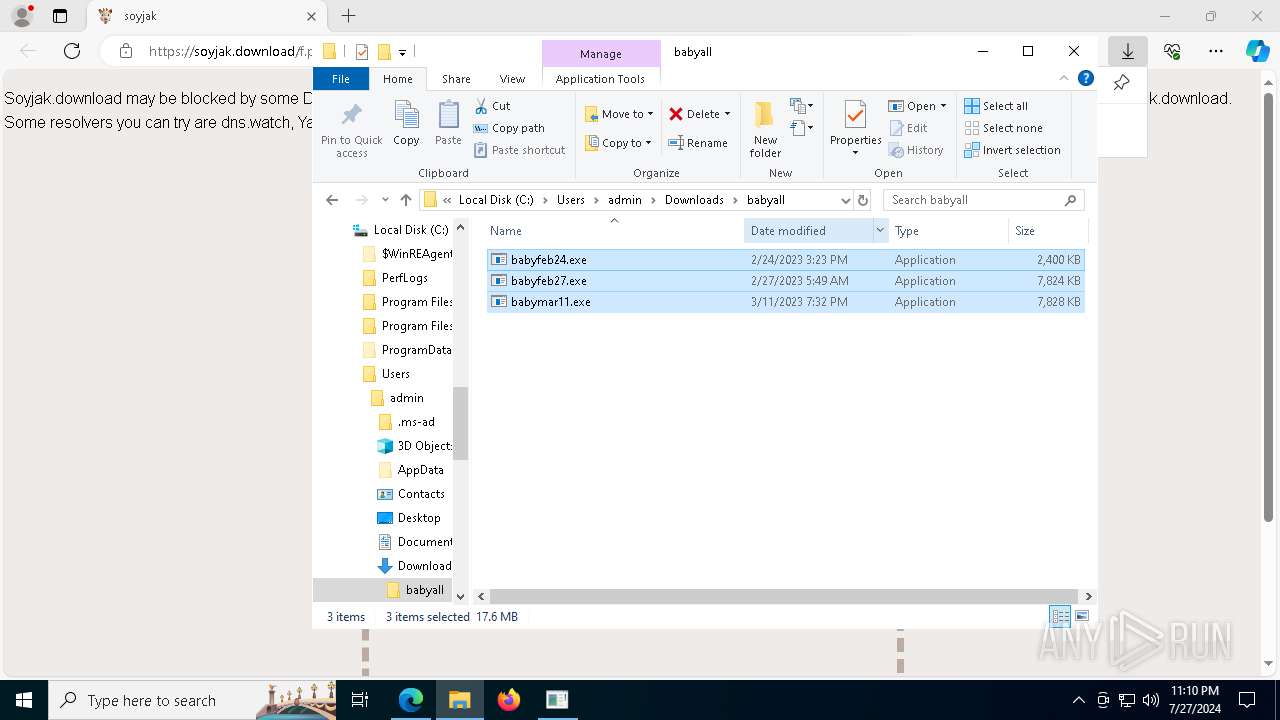
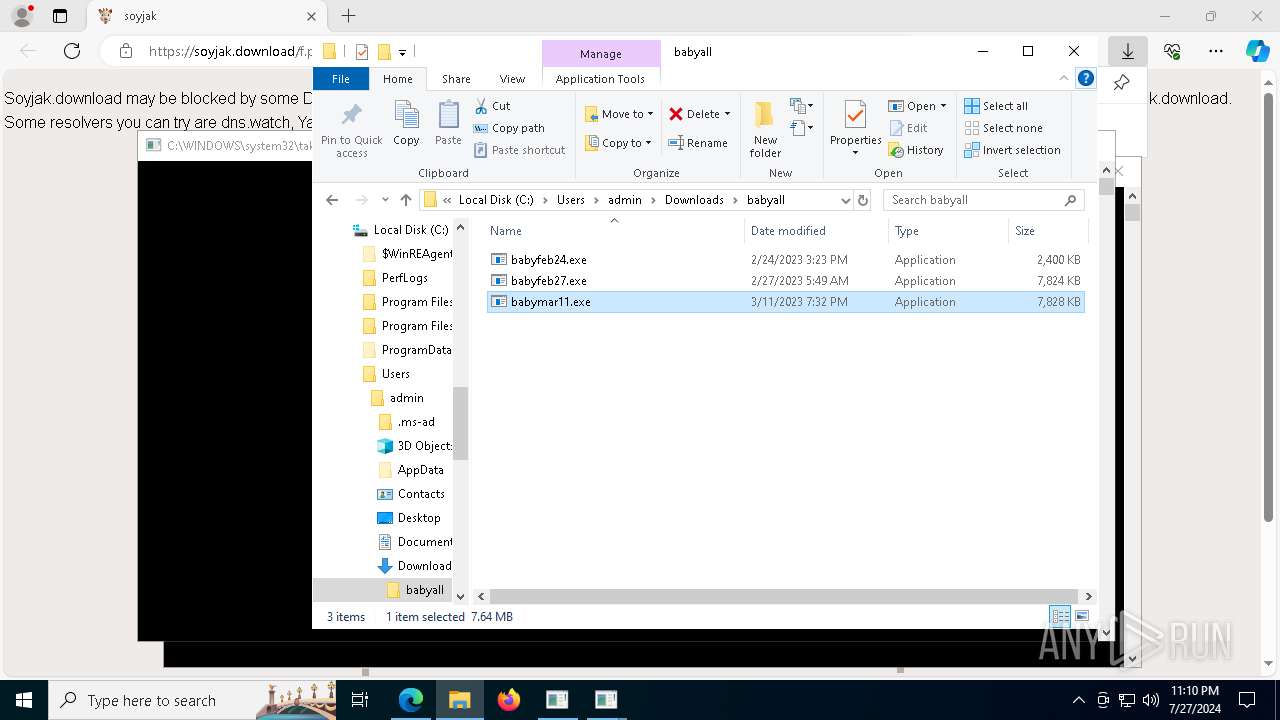
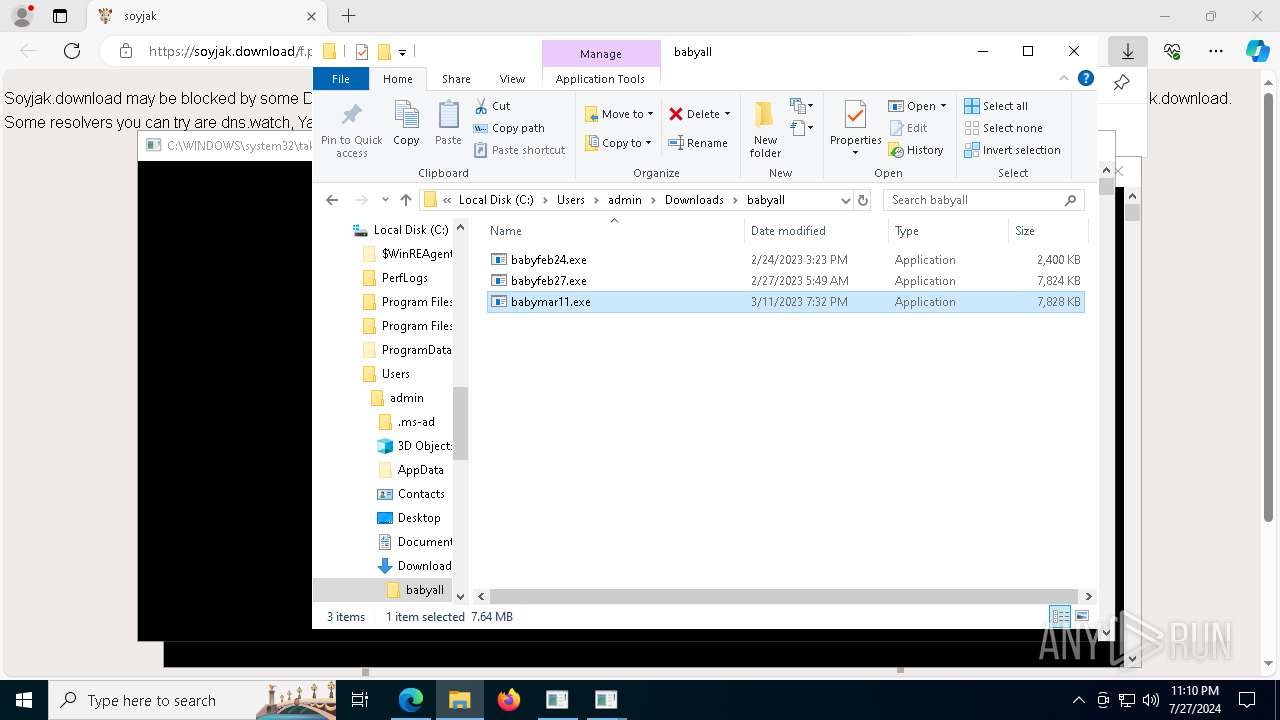
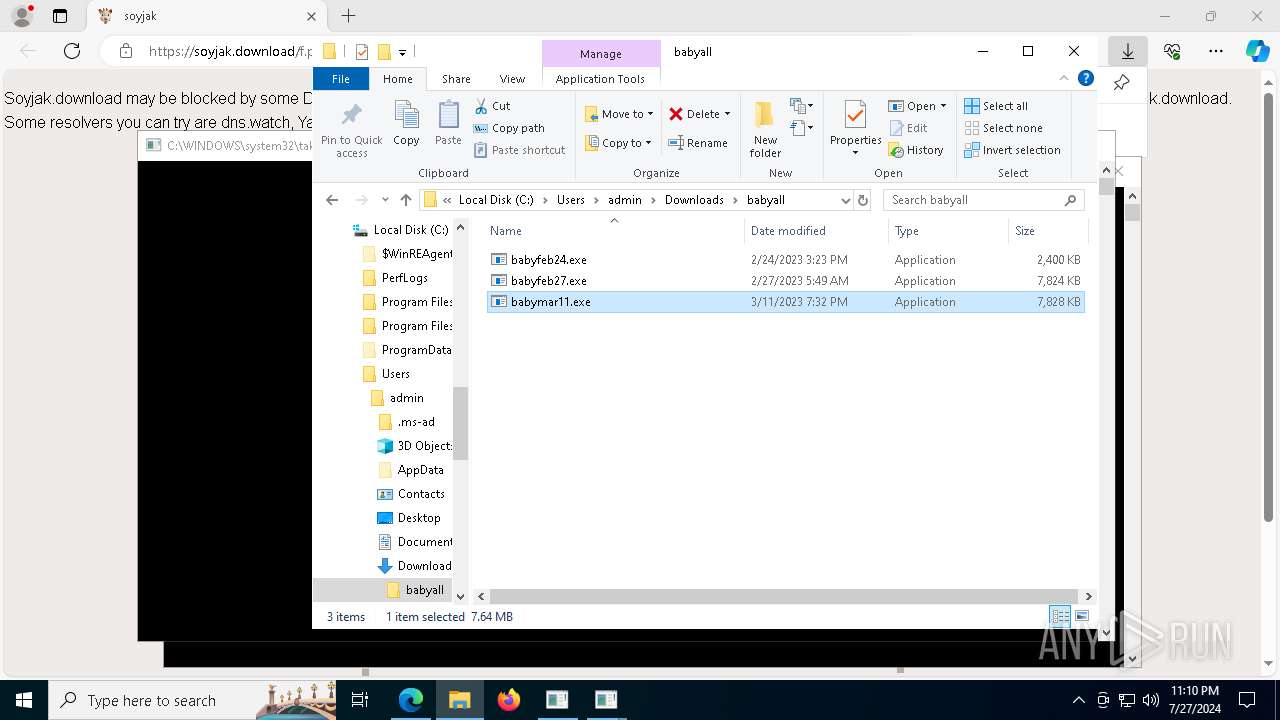
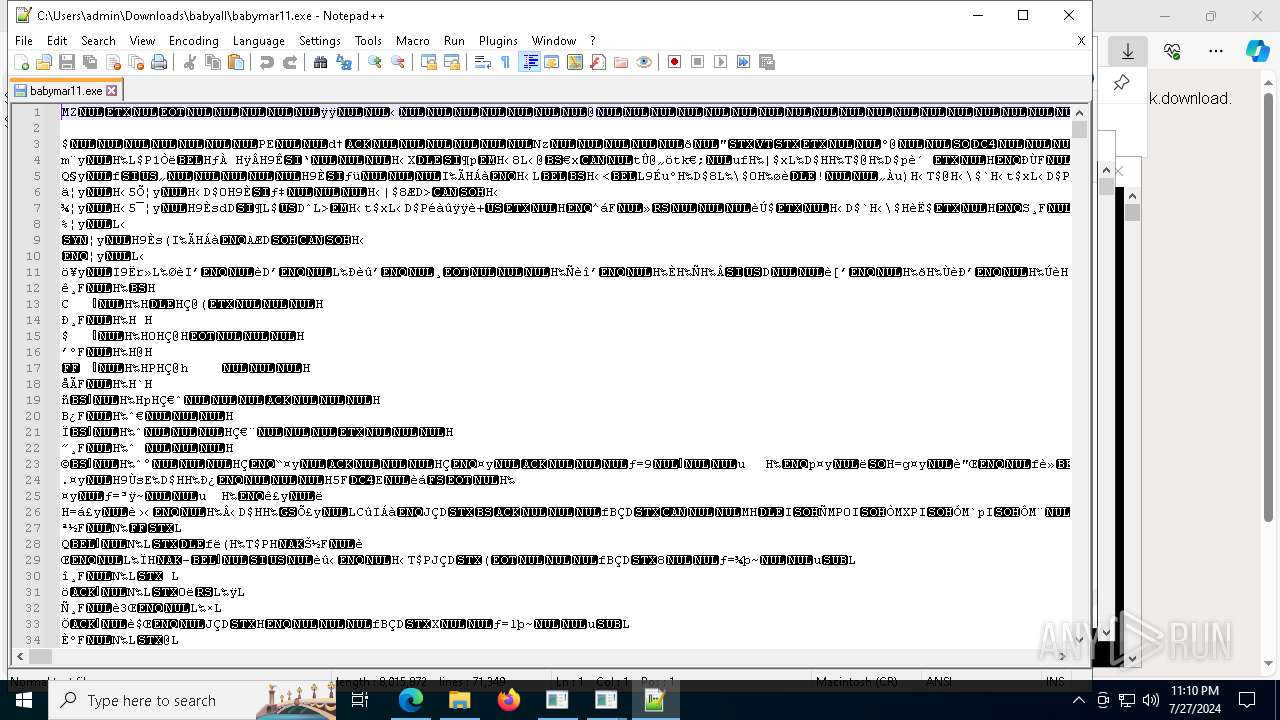
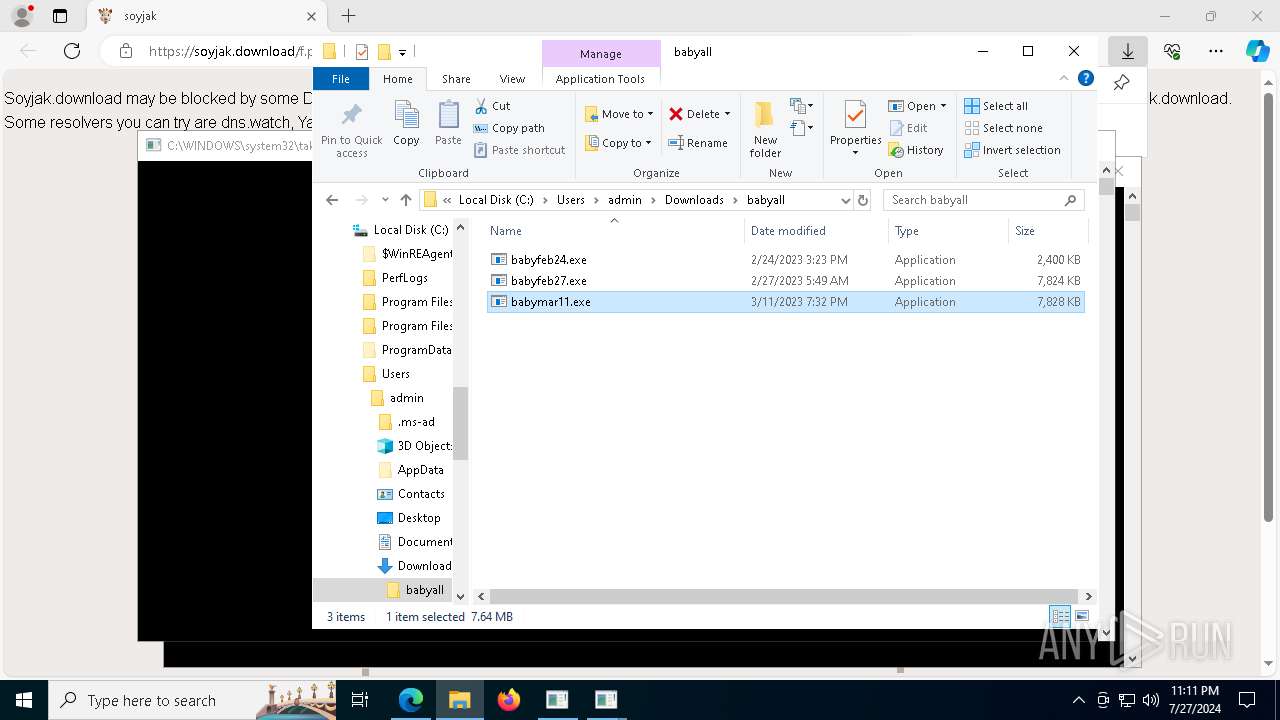
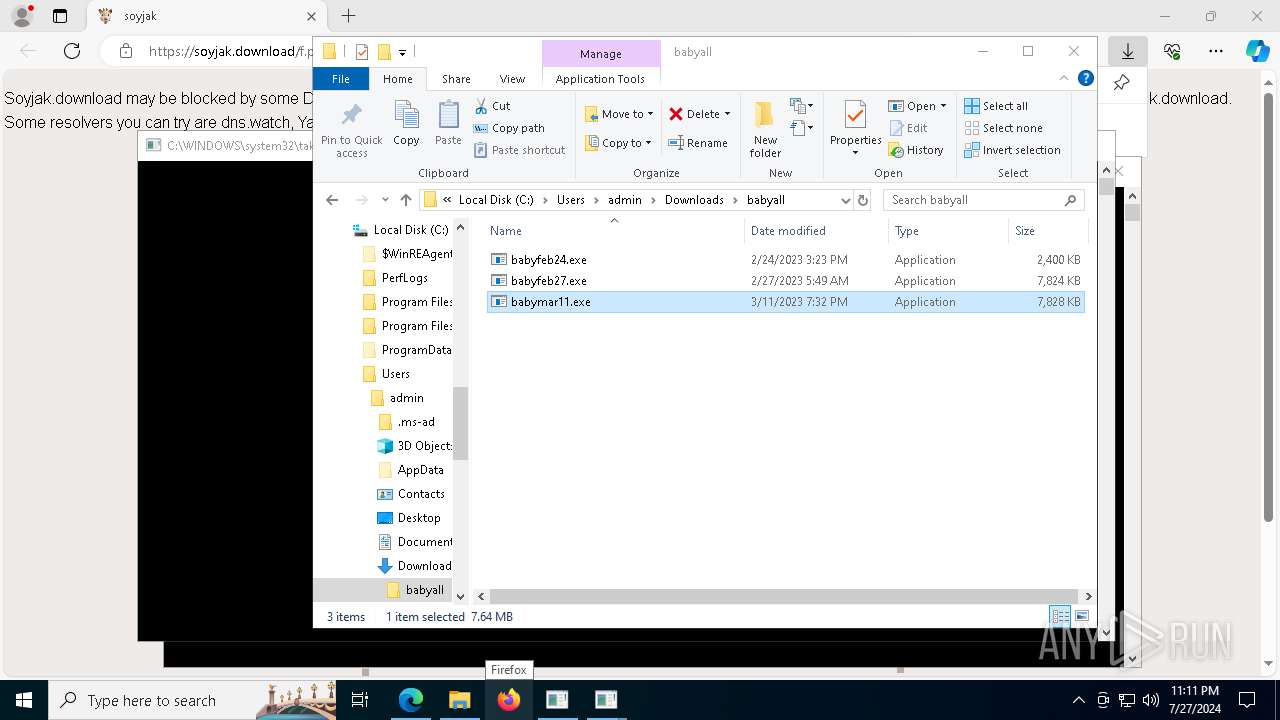
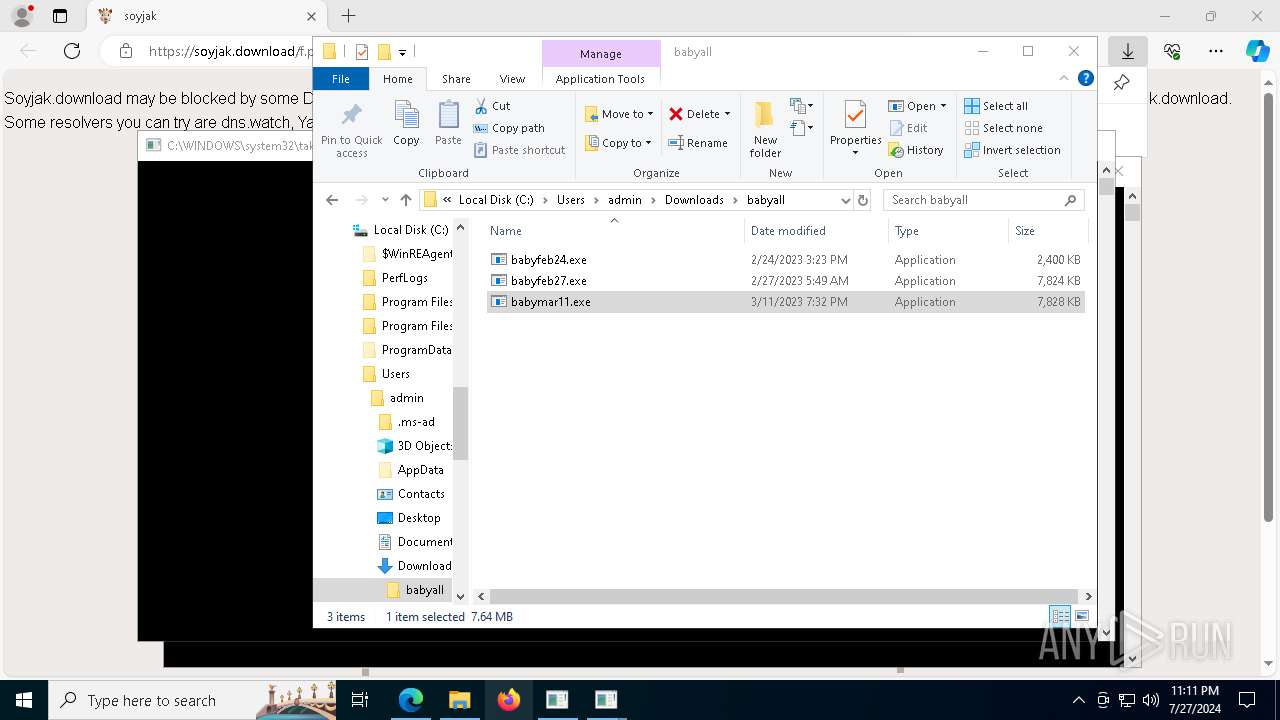
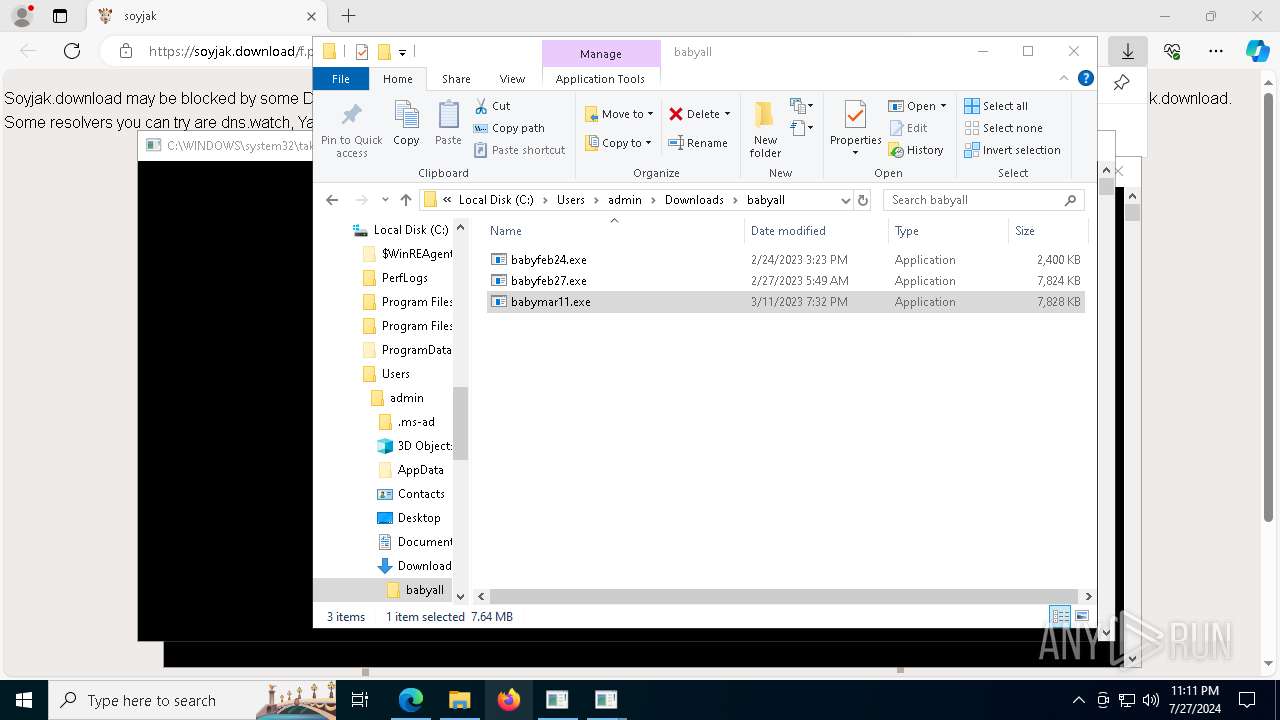
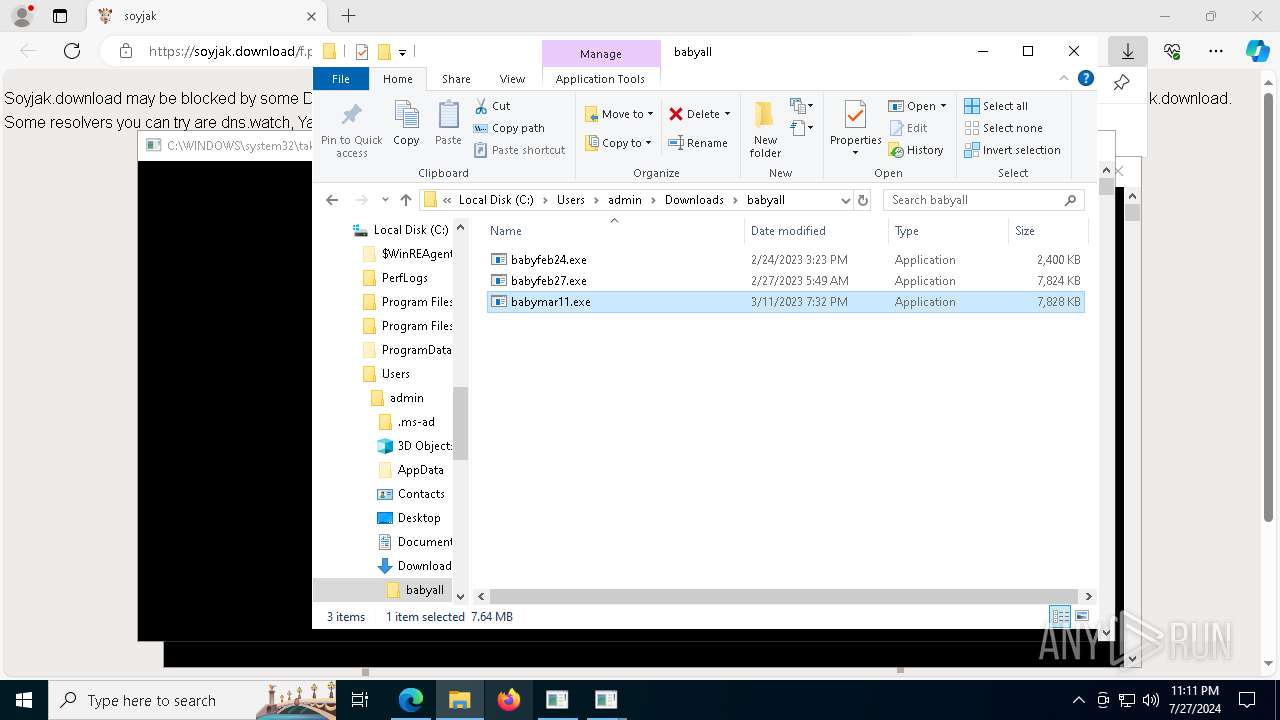
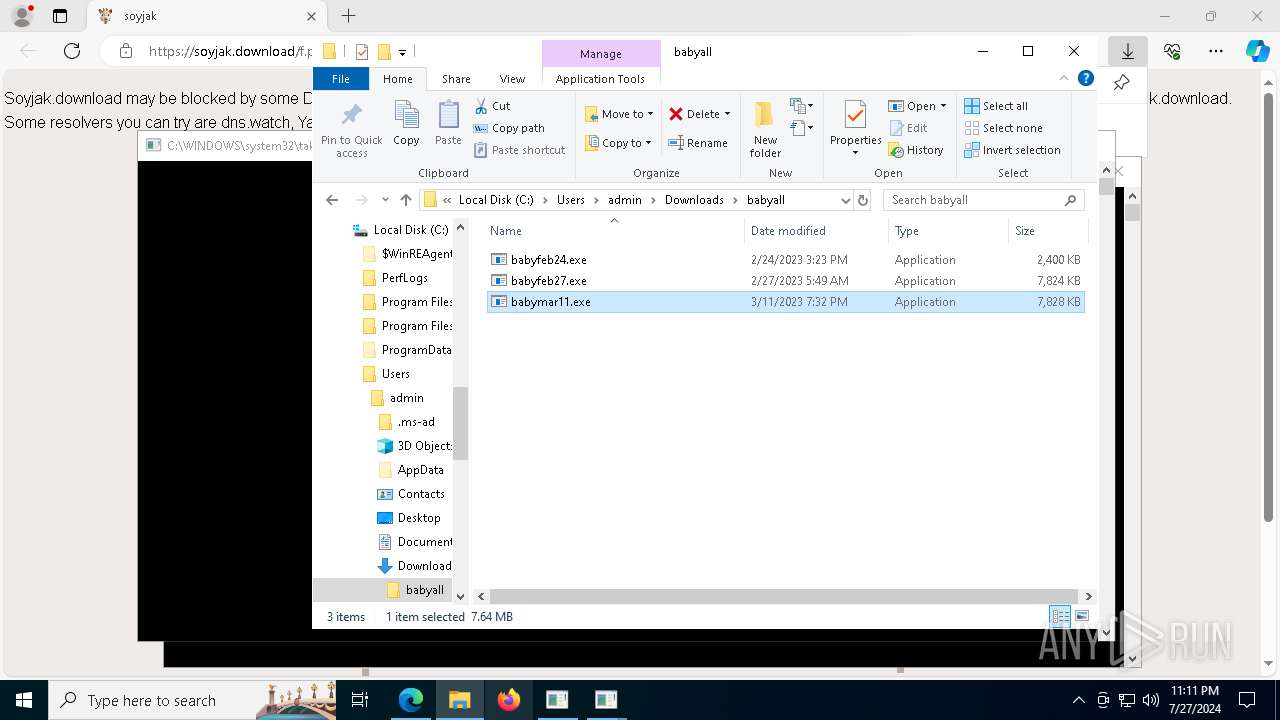
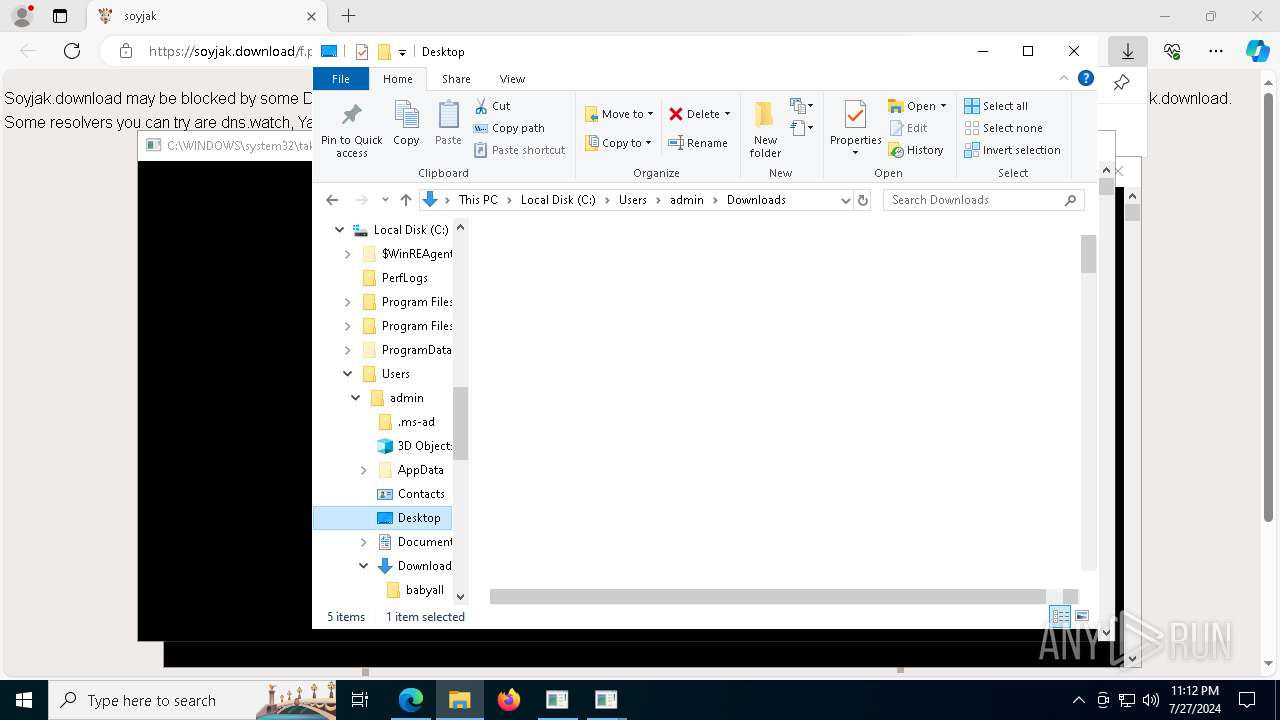
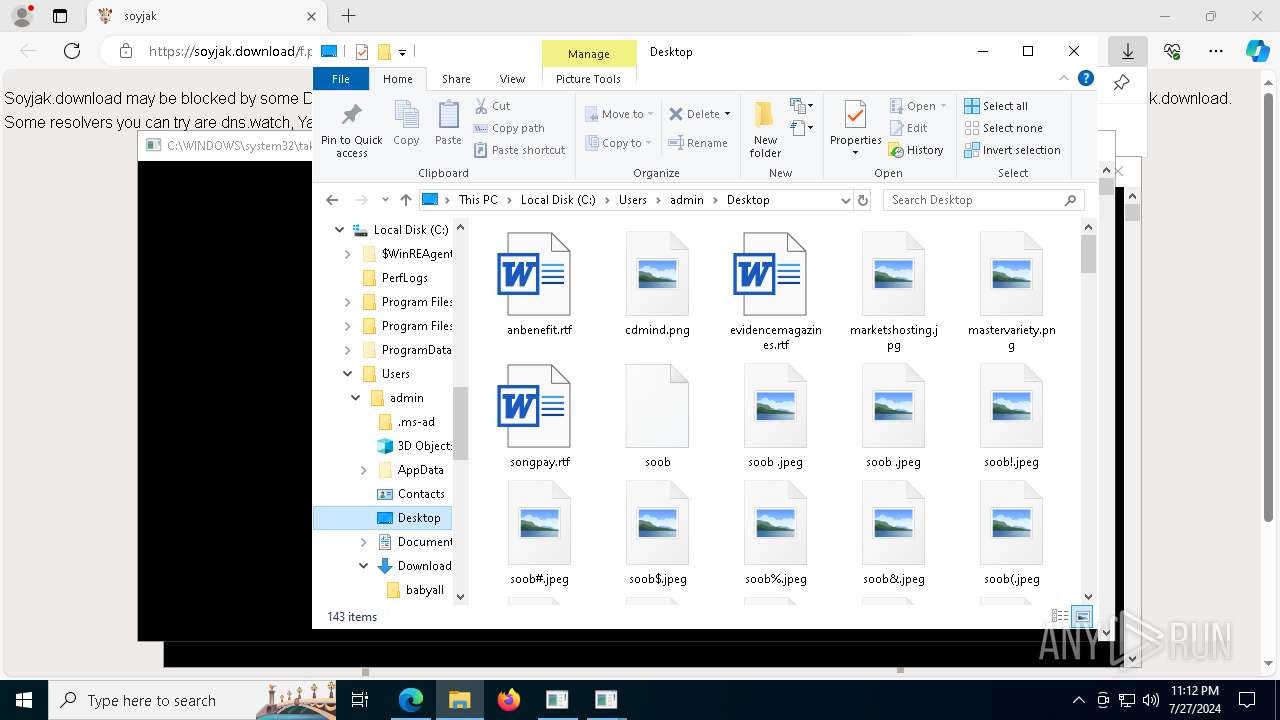
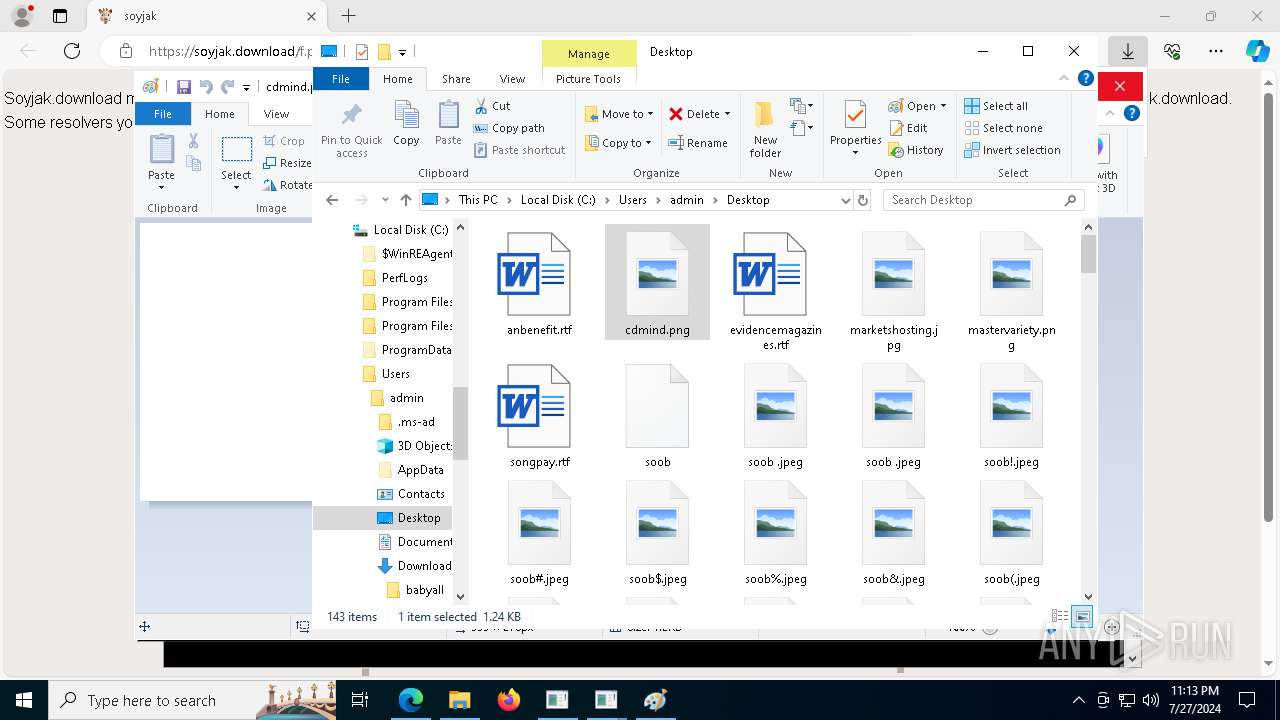
Manual execution by a user
- WinRAR.exe (PID: 1780)
- babyfeb24.exe (PID: 3656)
- babyfeb27.exe (PID: 1644)
- babymar11.exe (PID: 3360)
- babyfeb27.exe (PID: 5948)
- babymar11.exe (PID: 5296)
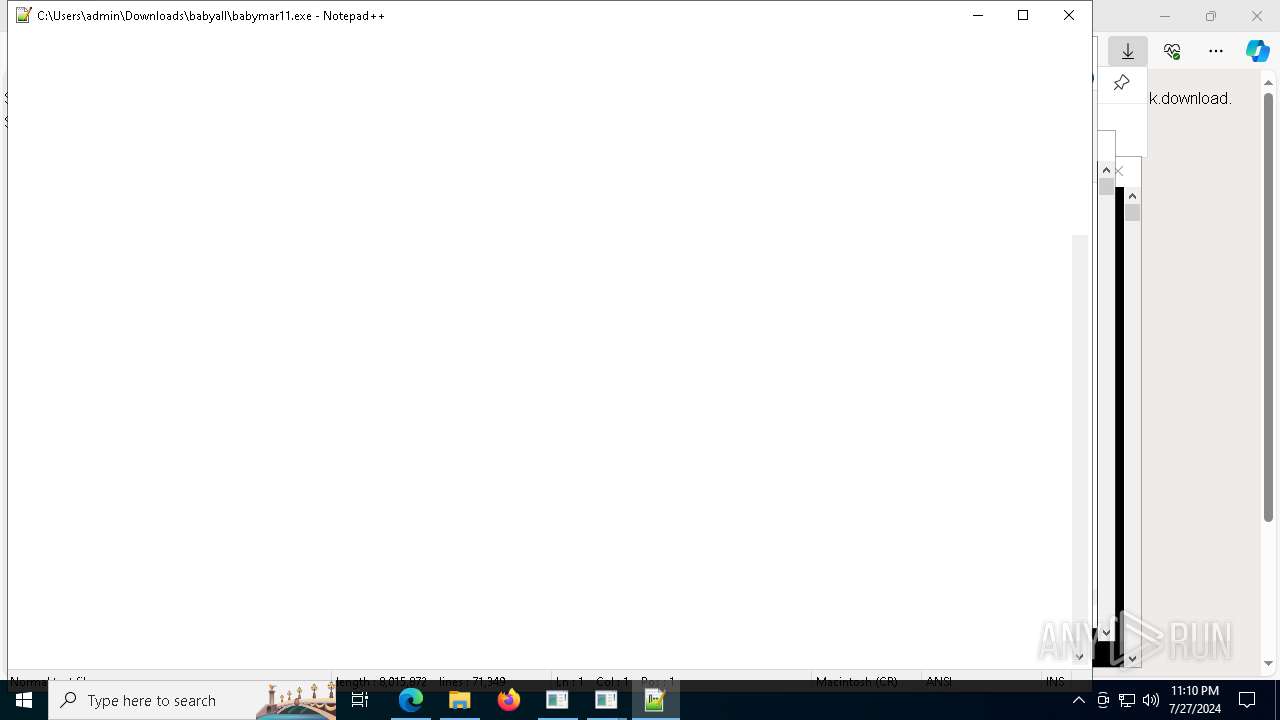
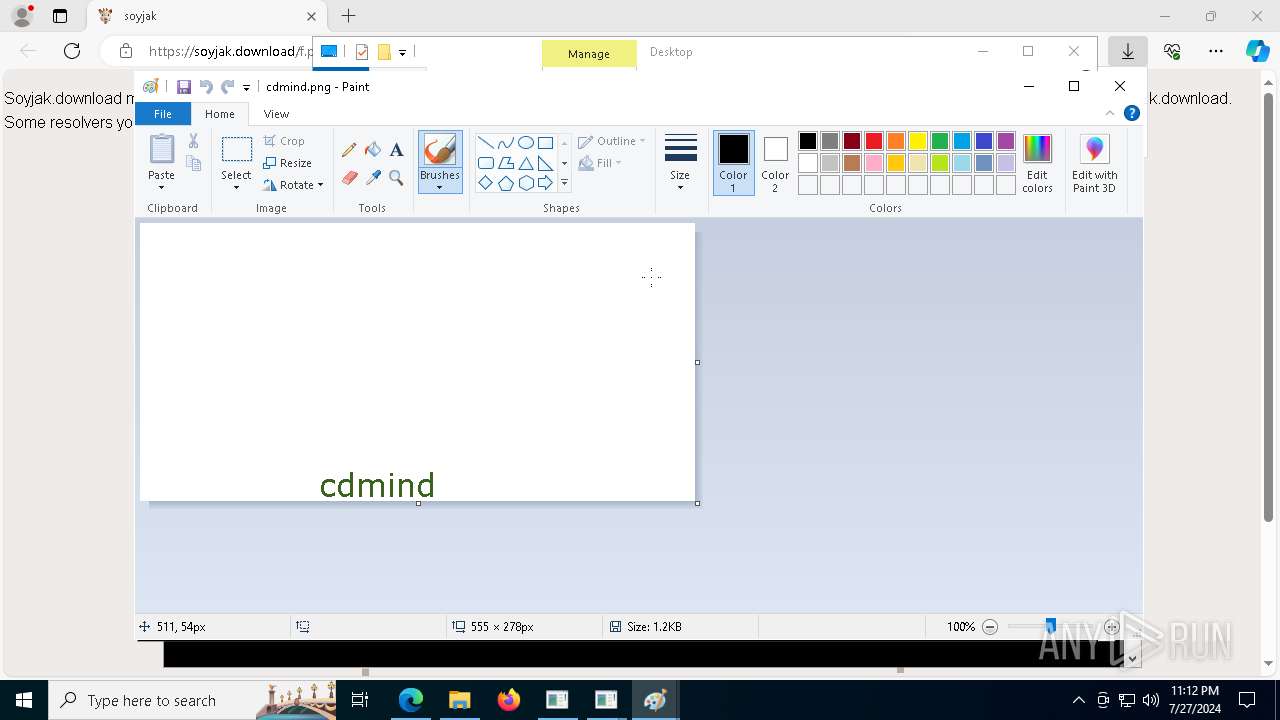
- notepad++.exe (PID: 2492)
- mspaint.exe (PID: 6628)
- mspaint.exe (PID: 1924)
Creates files in the program directory
- babyfeb24.exe (PID: 3656)
- babymar11.exe (PID: 3360)
Create files in a temporary directory
- babyfeb27.exe (PID: 1644)
- babymar11.exe (PID: 3360)
- babyfeb27.exe (PID: 5948)
Checks proxy server information
- slui.exe (PID: 7988)
Reads the software policy settings
- slui.exe (PID: 7988)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1780)
Application launched itself
- msedge.exe (PID: 132)
Reads Microsoft Office registry keys
- msedge.exe (PID: 132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
863
Monitored processes
708
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://soyjak.download/f.php?h=2QD_cnyd" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 256 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5528 --field-trial-handle=2360,i,14123389832151935697,5041814826377735566,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | net user soor99 soor /add | C:\Windows\System32\net.exe | — | babymar11.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | C:\WINDOWS\system32\net1 user soor46 soor /add | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1512 --field-trial-handle=2360,i,14123389832151935697,5041814826377735566,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 524 | C:\WINDOWS\system32\net1 user soor70 soor /add | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | C:\WINDOWS\system32\net1 user soor95 soor /add | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
71 436
Read events
71 385
Write events
50
Delete events
1
Modification events
| (PID) Process: | (132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (132) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (132) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
4
Suspicious files
220
Text files
7 058
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1c12d4.TMP | — | |
MD5:— | SHA256:— | |||
| 132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1c1276.TMP | — | |
MD5:— | SHA256:— | |||
| 132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1c1322.TMP | — | |
MD5:— | SHA256:— | |||
| 132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1c1341.TMP | — | |
MD5:— | SHA256:— | |||
| 132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1c1351.TMP | — | |
MD5:— | SHA256:— | |||
| 132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1c1351.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
76
DNS requests
57
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7032 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8ee9a644-4296-4fb1-b90f-7c4d7ea948c5?P1=1722624388&P2=404&P3=2&P4=NnvhO5obpC79PbdQuPyc92U8N65FxNxXQ8ZwDFLuGcYncmSKGqbXIxhI1J1wT5lSu6z%2bZgOPnY3bPfXVSRCnKg%3d%3d | unknown | — | — | whitelisted |
2908 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7032 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8ee9a644-4296-4fb1-b90f-7c4d7ea948c5?P1=1722624388&P2=404&P3=2&P4=NnvhO5obpC79PbdQuPyc92U8N65FxNxXQ8ZwDFLuGcYncmSKGqbXIxhI1J1wT5lSu6z%2bZgOPnY3bPfXVSRCnKg%3d%3d | unknown | — | — | whitelisted |
7032 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8ee9a644-4296-4fb1-b90f-7c4d7ea948c5?P1=1722624388&P2=404&P3=2&P4=NnvhO5obpC79PbdQuPyc92U8N65FxNxXQ8ZwDFLuGcYncmSKGqbXIxhI1J1wT5lSu6z%2bZgOPnY3bPfXVSRCnKg%3d%3d | unknown | — | — | whitelisted |
7032 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8ee9a644-4296-4fb1-b90f-7c4d7ea948c5?P1=1722624388&P2=404&P3=2&P4=NnvhO5obpC79PbdQuPyc92U8N65FxNxXQ8ZwDFLuGcYncmSKGqbXIxhI1J1wT5lSu6z%2bZgOPnY3bPfXVSRCnKg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5368 | SearchApp.exe | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1180 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5368 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | unknown |
6012 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1996 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4028 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2308 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
soyjak.download |
| unknown |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |