| File name: | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9 |
| Full analysis: | https://app.any.run/tasks/57f7bd85-d522-4abc-9d01-dcf497ebc8f0 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 14:19:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AB59F07A70507156D1DAFD6F73062B8D |
| SHA1: | 2FEE7A15080EA77EAF2A80EF2024C7C41EB95555 |
| SHA256: | 9D2FBBFDC0A3903A4B68ADEABA321D42C7613870A4935C20D9217C45972077E9 |
| SSDEEP: | 3072:xuDKFkUO++dPLzCrgo+xGdqmEI6t2TQWppYW5MAjjjjjjjgLr:MD/Rpe0oDLlTQWppN5EL |
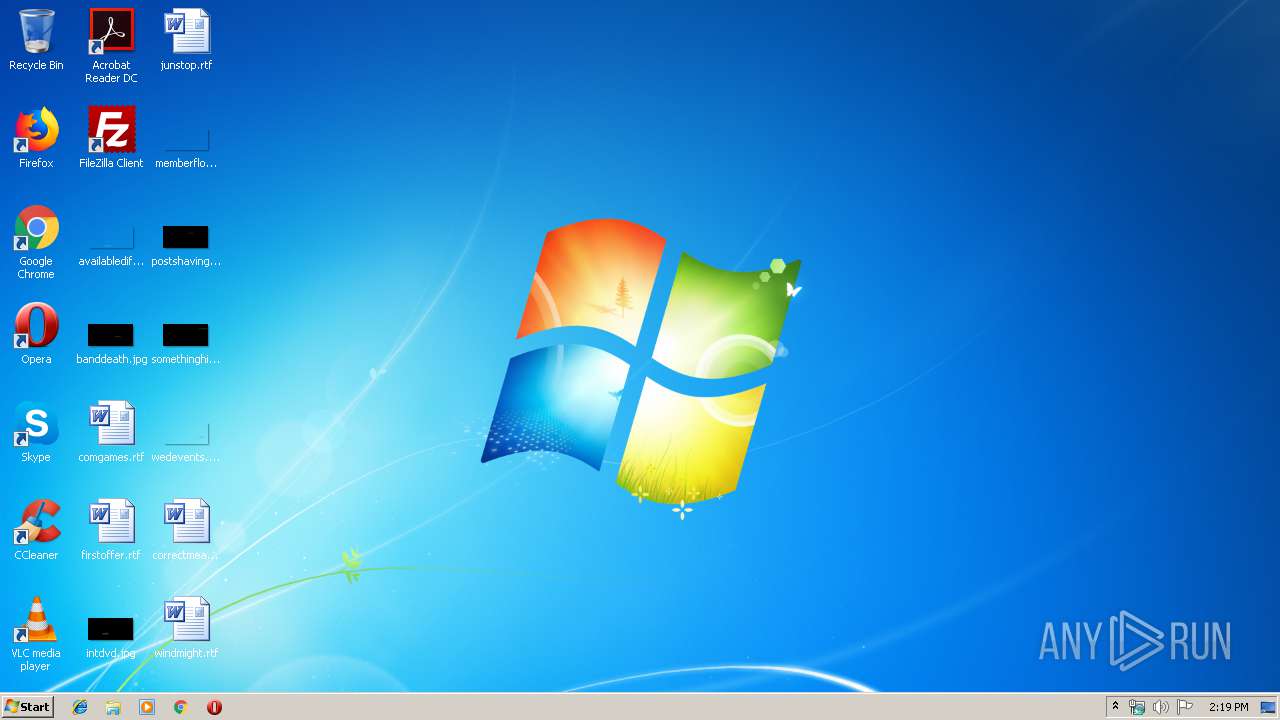
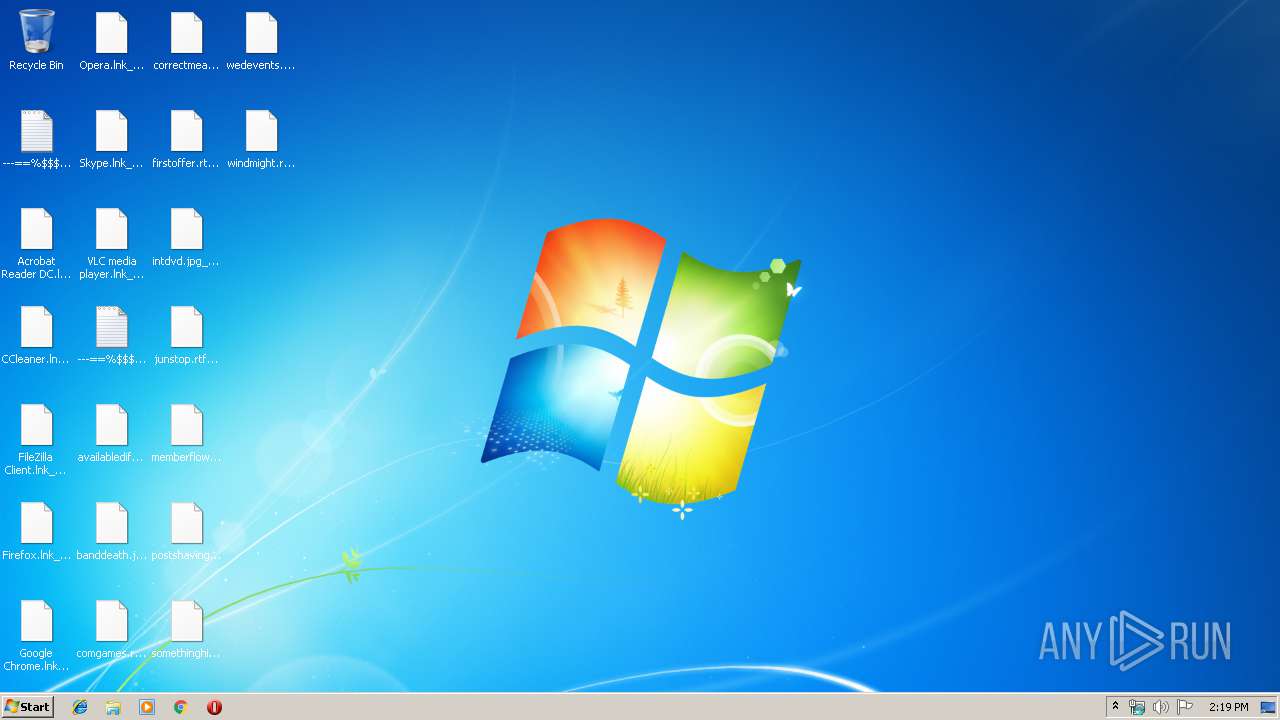
MALICIOUS
Disables Windows Defender
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Writes file to Word startup folder
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Writes to a start menu file
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Actions looks like stealing of personal data
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Changes settings of System certificates
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Modifies files in Chrome extension folder
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
SUSPICIOUS
Application launched itself
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2508)
Executable content was dropped or overwritten
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Reads the cookies of Mozilla Firefox
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Reads the cookies of Google Chrome
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Changes tracing settings of the file or console
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Writes to a desktop.ini file (may be used to cloak folders)
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Starts CMD.EXE for self-deleting
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Adds / modifies Windows certificates
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Starts CMD.EXE for commands execution
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Creates files in the user directory
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Creates files in the program directory
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
INFO
Dropped object may contain Bitcoin addresses
- 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe (PID: 2452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:20 19:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 60416 |
| InitializedDataSize: | 393728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x213e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.5.1 |
| ProductVersionNumber: | 1.1.0.1 |
| FileFlagsMask: | 0x006f |
| FileFlags: | Pre-release, Patched |
| FileOS: | Unknown (0x40304) |
| ObjectFileType: | Static library |
| FileSubtype: | 81 |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileOldVersion: | 1.0.4.4 |
| InternalName: | gjtrrh.exe |
| Copyrighd: | Copyright (C) 2020, odfgbiv |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Nov-2018 18:50:52 |
| Detected languages: |
|
| FileOldVersion: | 1.0.4.4 |
| InternalName: | gjtrrh.exe |
| Copyrighd: | Copyright (C) 2020, odfgbiv |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 20-Nov-2018 18:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000EB29 | 0x0000EC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.79497 |
.rdata | 0x00010000 | 0x000072D6 | 0x00007400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17697 |
.data | 0x00018000 | 0x00048DA0 | 0x00008E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70458 |
.rsrc | 0x00061000 | 0x0000FA38 | 0x0000FC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99818 |
.reloc | 0x00071000 | 0x000011F0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.50037 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.37831 | 412 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 4.75618 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.59621 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 6.27622 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.06631 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.36241 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.87048 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 3.5267 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.5631 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 4.29753 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
44
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | ping 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\AppData\Local\Temp\9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe" | C:\Users\admin\AppData\Local\Temp\9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2508 | "C:\Users\admin\AppData\Local\Temp\9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe" | C:\Users\admin\AppData\Local\Temp\9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3860 | "C:\Windows\system32\cmd.exe" /c ping 127.0.0.1 && del "C:\Users\admin\AppData\Local\Temp\9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe" | C:\Windows\system32\cmd.exe | — | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
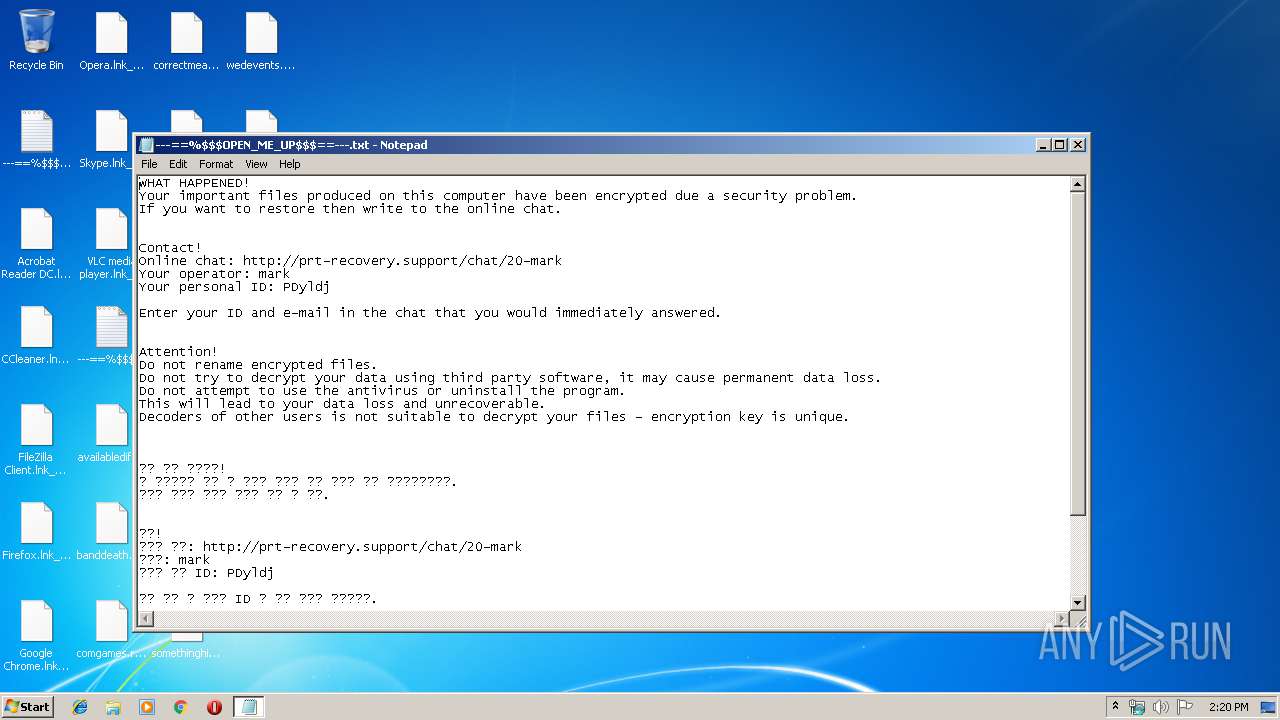
| 4028 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\---==%$$OPEN_ME_UP$$==---.txt | C:\Windows\system32\NOTEPAD.EXE | — | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
465
Read events
431
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2508) 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2508) 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2452) 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2452) 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2452) 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2452) 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2452) 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2452) 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2452) 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2452) 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
506
Text files
236
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | C:\autoexec.bat | — | |
MD5:— | SHA256:— | |||
| 2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | C:\config.sys | — | |
MD5:— | SHA256:— | |||
| 2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.msi | — | |
MD5:— | SHA256:— | |||
| 2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml | — | |
MD5:— | SHA256:— | |||
| 2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab_mark_{PDyldj}.mak | — | |
MD5:— | SHA256:— | |||
| 2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccLR.cab_mark_{PDyldj}.mak | — | |
MD5:— | SHA256:— | |||
| 2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\branding.xml | — | |
MD5:— | SHA256:— | |||
| 2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccessMUI.msi | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2452 | 9d2fbbfdc0a3903a4b68adeaba321d42c7613870a4935c20d9217c45972077e9.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
— | — | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iplogger.org |
| shared |
Threats
3 ETPRO signatures available at the full report