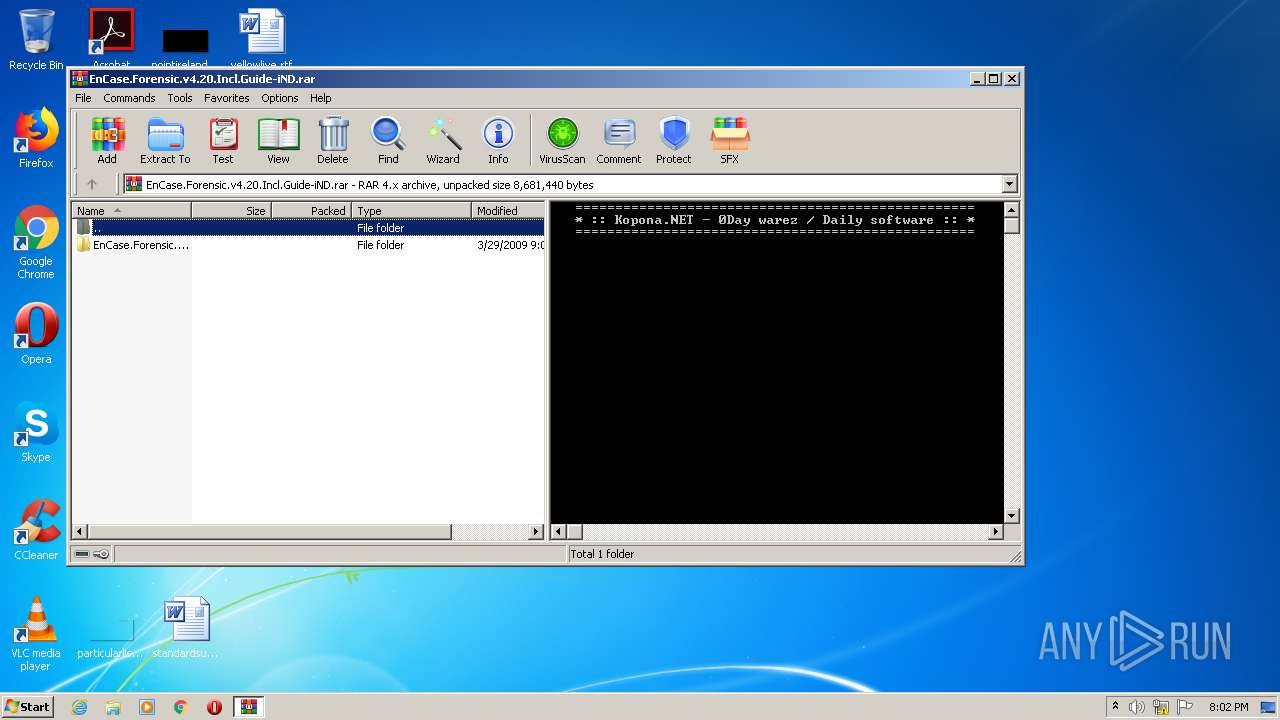
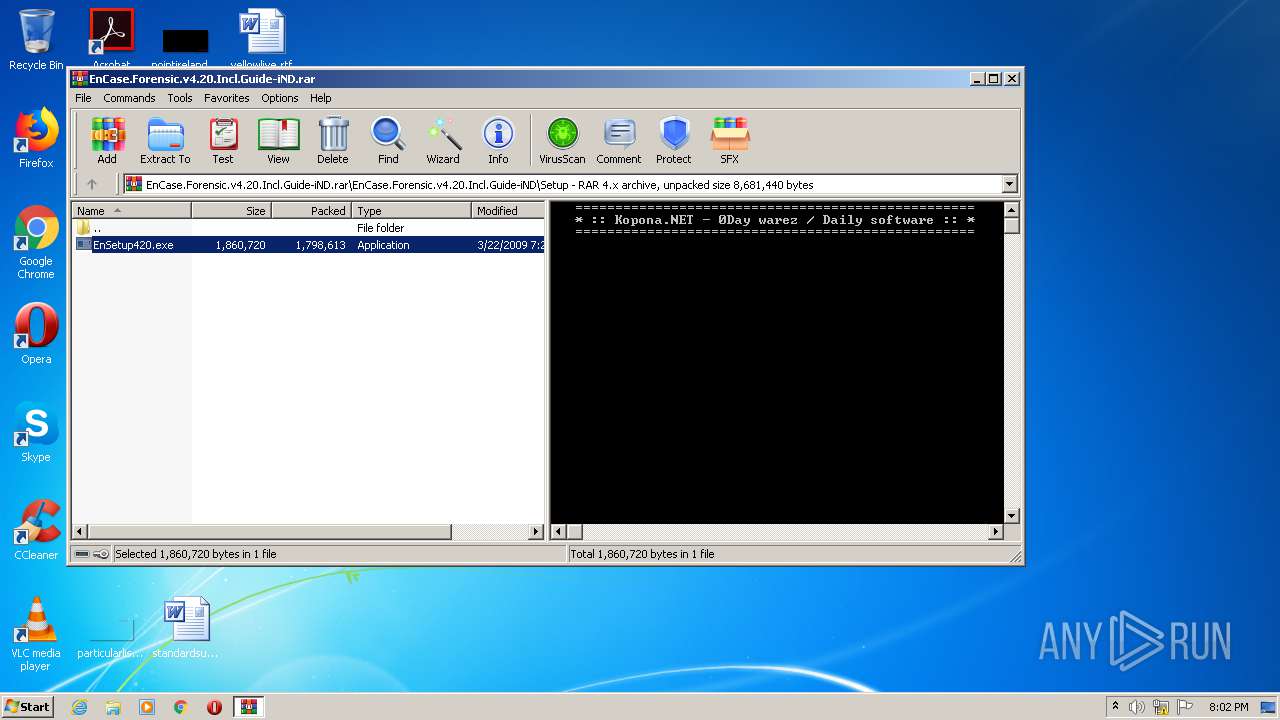
| File name: | EnCase.Forensic.v4.20.Incl.Guide-iND.rar |
| Full analysis: | https://app.any.run/tasks/bda4465a-87c2-4e4f-91c7-58fd5034c148 |
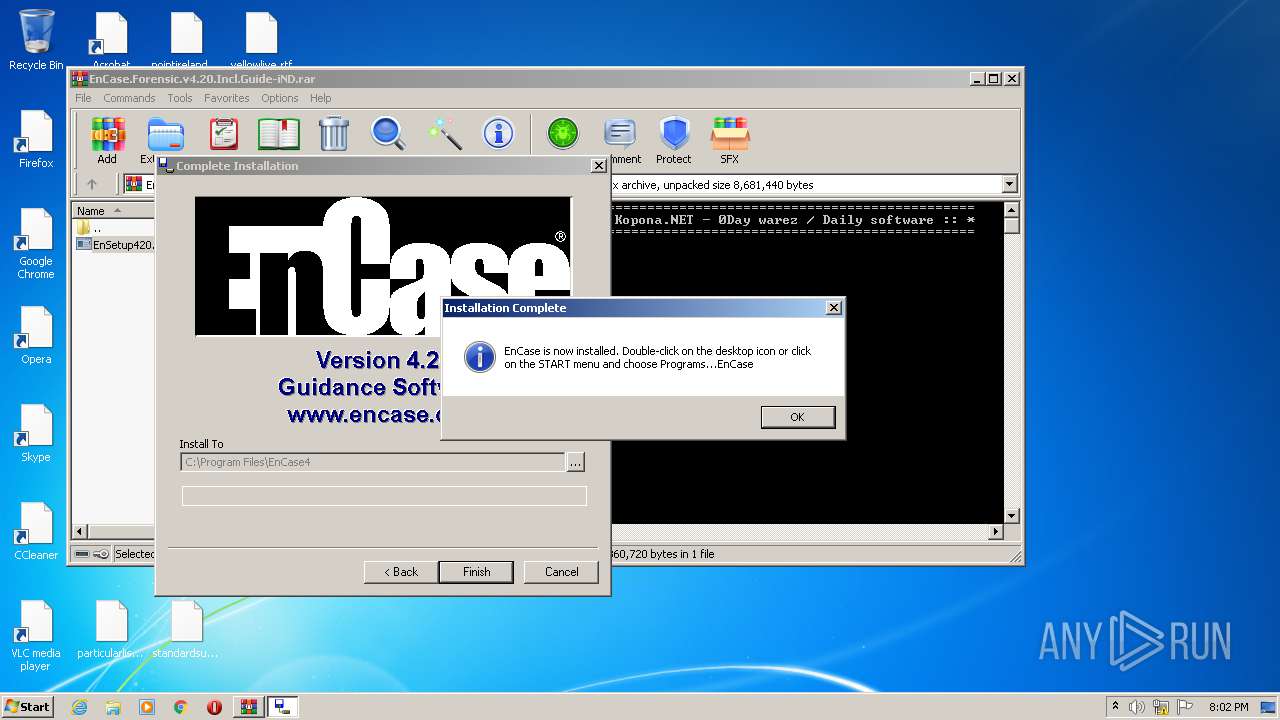
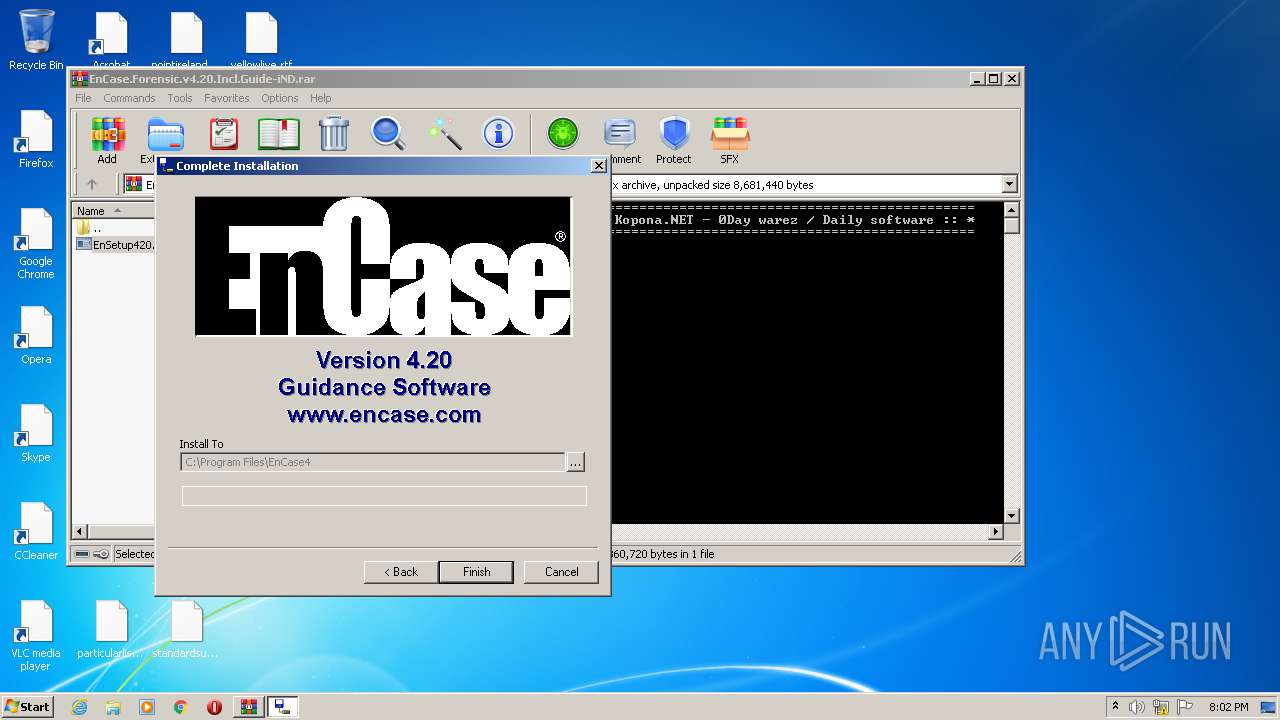
| Verdict: | Malicious activity |
| Analysis date: | November 05, 2020, 20:01:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 477FFB1994F48358EC3F835F227CA5B3 |
| SHA1: | 5F8068A4FF17DD9EB101C6DA98A5A740B35E0B05 |
| SHA256: | 9D169F96CF3921774E5E395FC6A62114DA7F953A57A173749E75850EF2D337D6 |
| SSDEEP: | 196608:V1YipDLpU4xzbzqsszuuOwEsHvd8lMvrxQfU9nfm/Vja:V1JU4xPzqsslzFbvtQfU9CVja |
MALICIOUS
Application was dropped or rewritten from another process
- EnSetup420.exe (PID: 3988)
- EnSetup420.exe (PID: 1596)
SUSPICIOUS
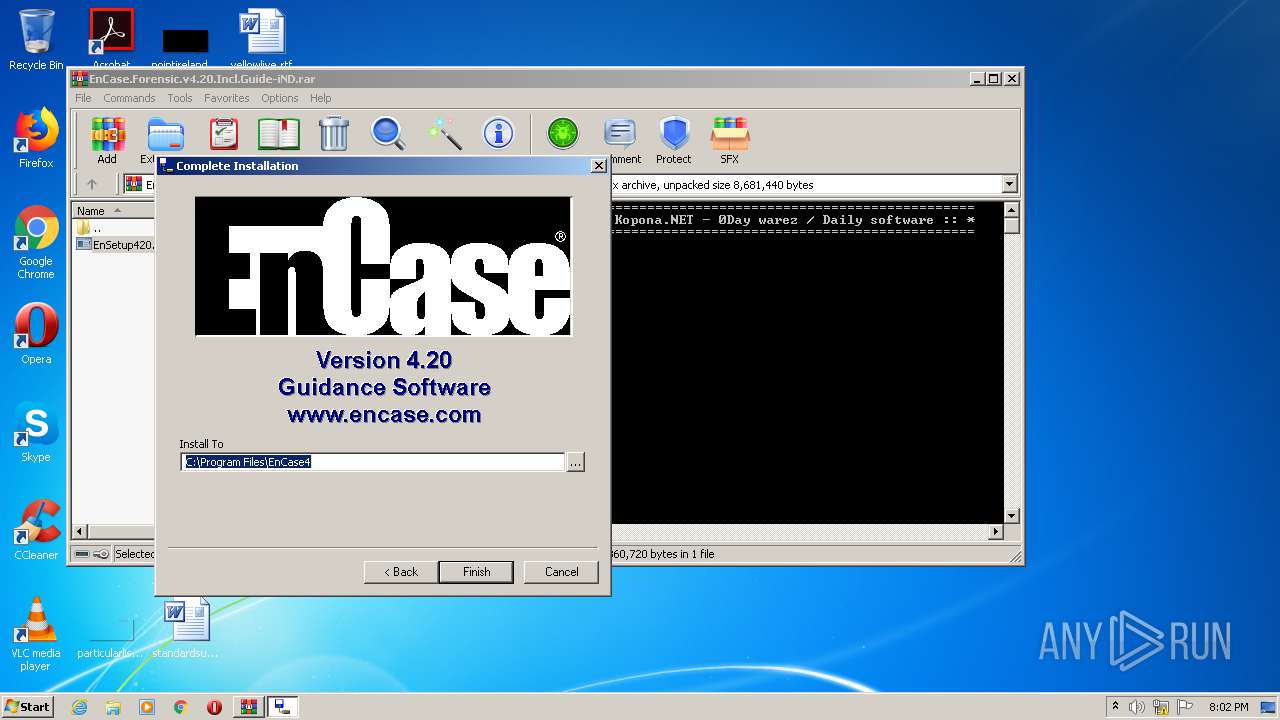
Creates files in the Windows directory
- EnSetup420.exe (PID: 1596)
Creates files in the driver directory
- EnSetup420.exe (PID: 1596)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2628)
- EnSetup420.exe (PID: 1596)
Modifies the open verb of a shell class
- EnSetup420.exe (PID: 1596)
Creates files in the program directory
- EnSetup420.exe (PID: 1596)
INFO
Dropped object may contain Bitcoin addresses
- EnSetup420.exe (PID: 1596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 194 |
|---|---|
| UncompressedSize: | 117 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2009:02:14 07:37:01 |
| PackingMethod: | Stored |
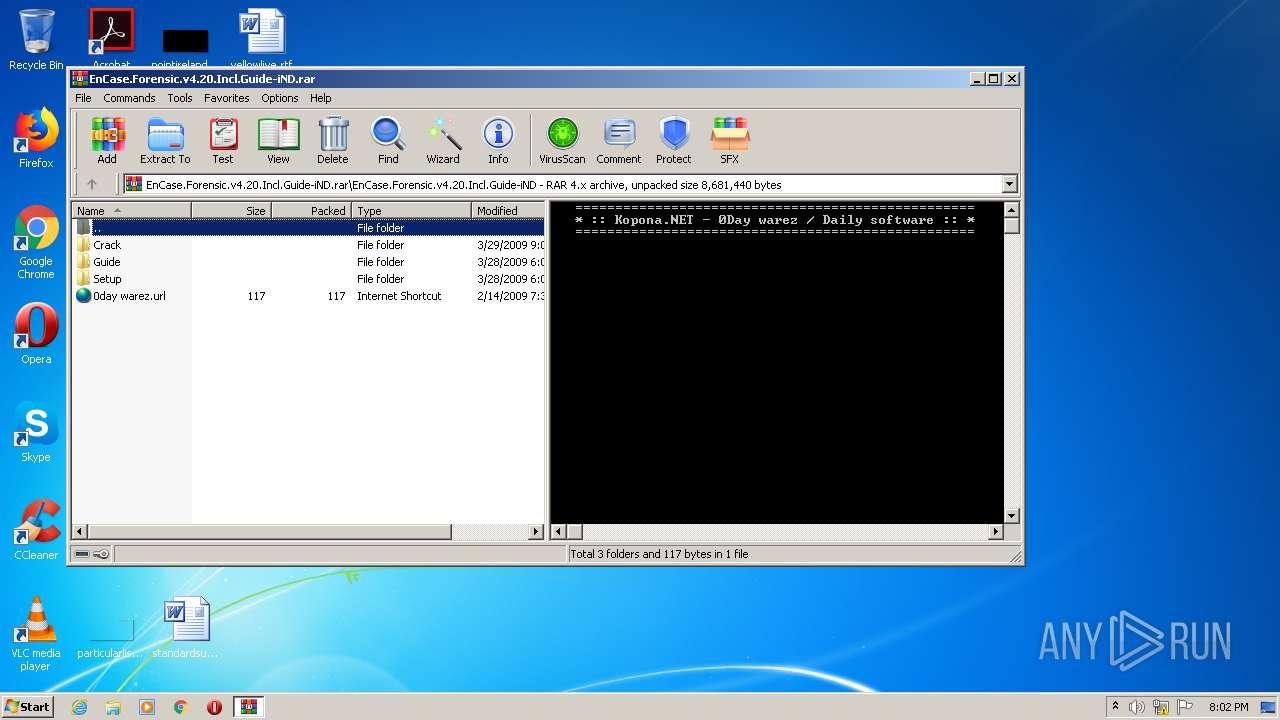
| ArchivedFileName: | EnCase.Forensic.v4.20.Incl.Guide-iND\0day warez.url |
Total processes
46
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
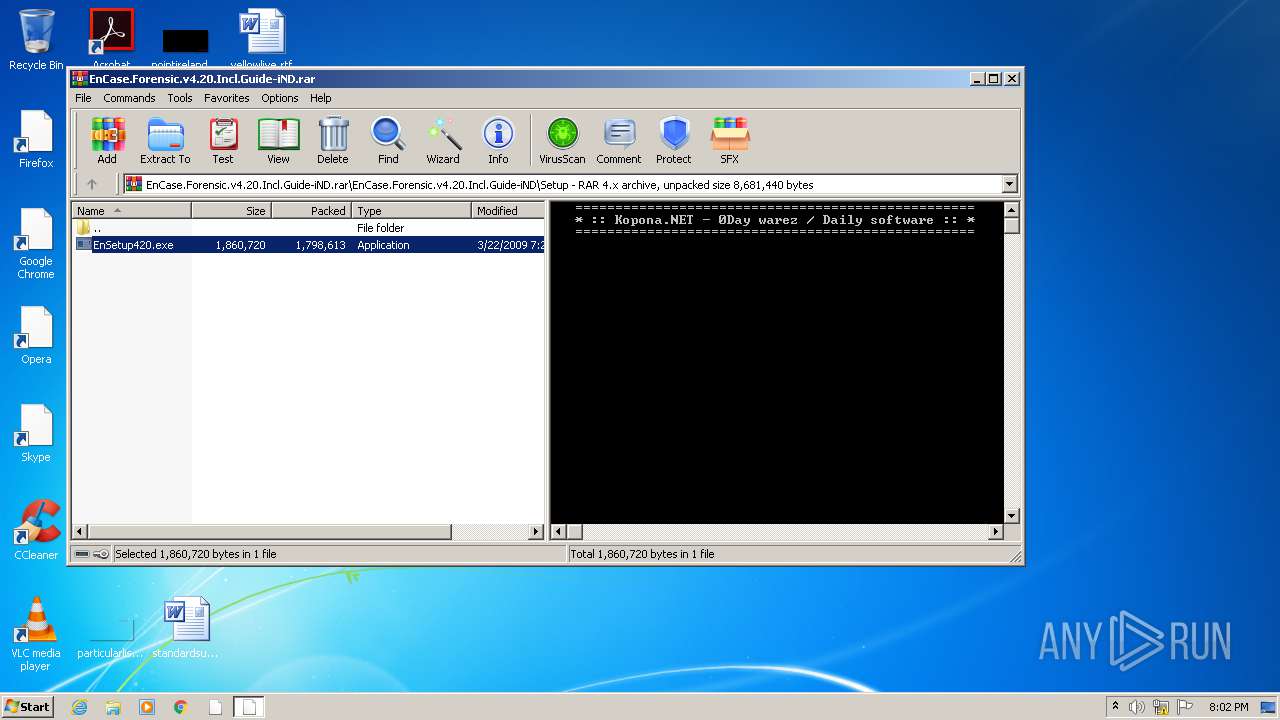
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
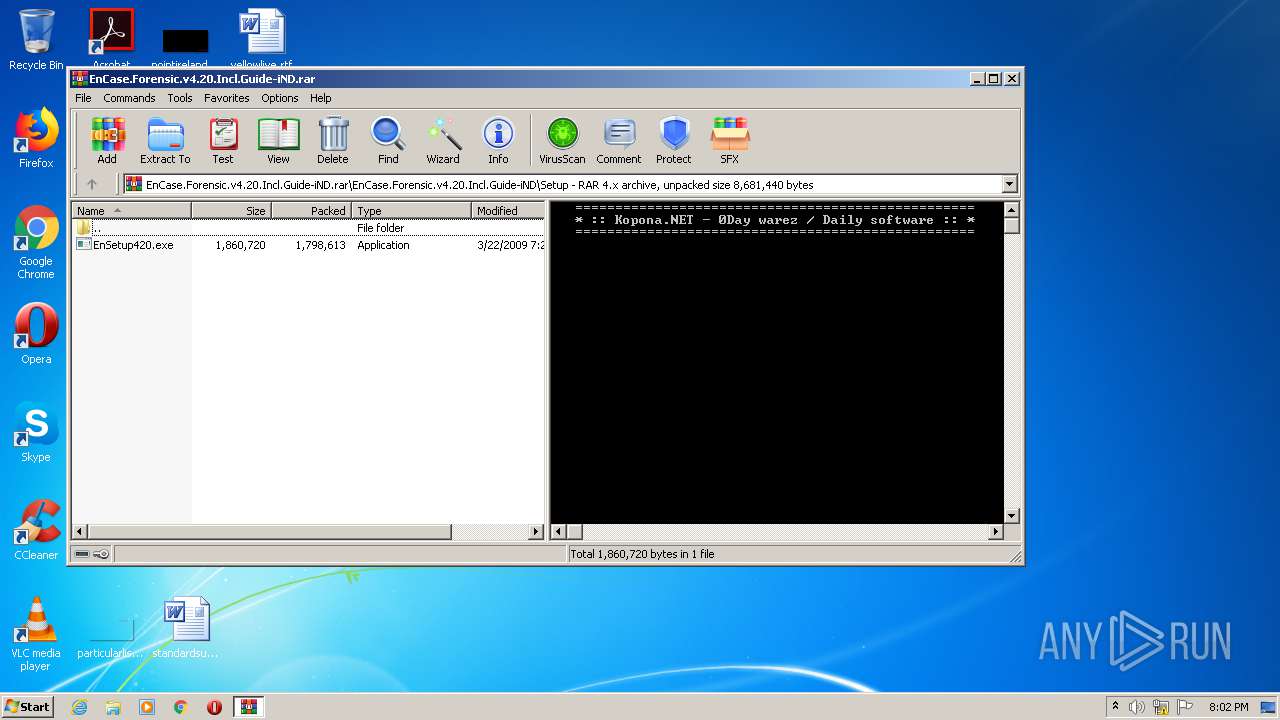
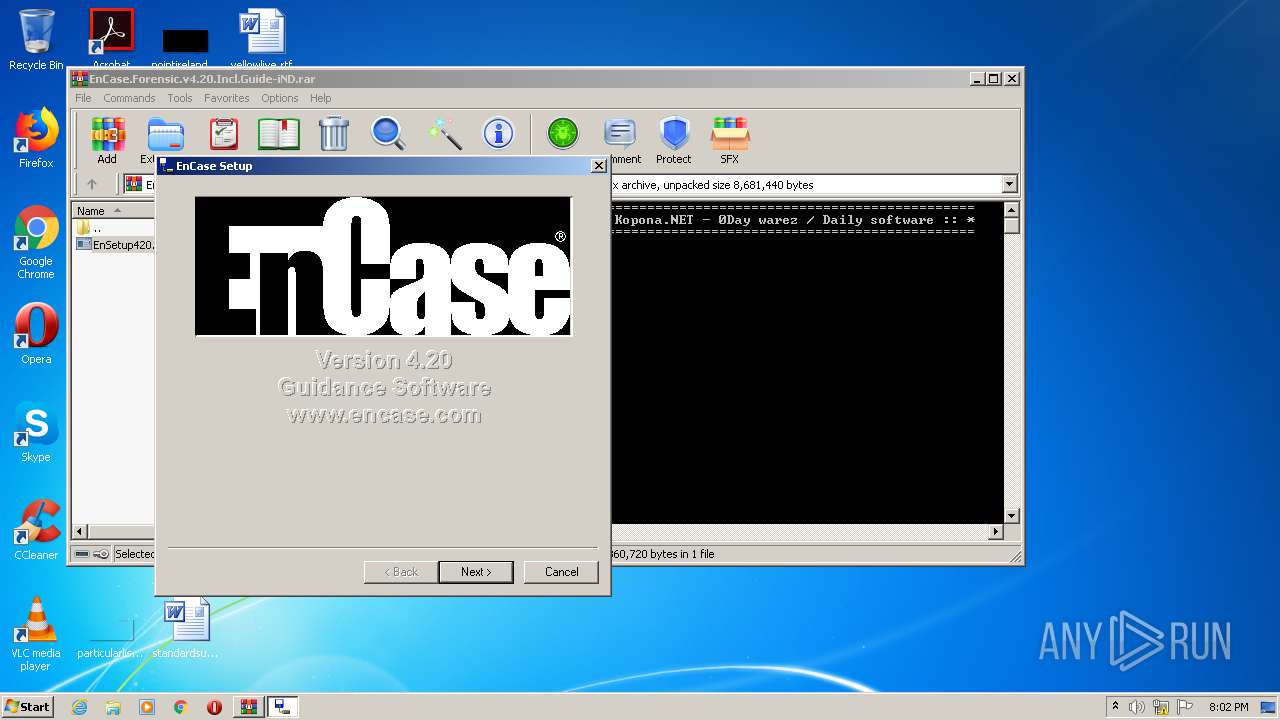
| 1596 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2628.38357\EnCase.Forensic.v4.20.Incl.Guide-iND\Setup\EnSetup420.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2628.38357\EnCase.Forensic.v4.20.Incl.Guide-iND\Setup\EnSetup420.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\EnCase.Forensic.v4.20.Incl.Guide-iND.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1073807364 Version: 5.60.0 Modules
| |||||||||||||||
| 3988 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2628.38357\EnCase.Forensic.v4.20.Incl.Guide-iND\Setup\EnSetup420.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2628.38357\EnCase.Forensic.v4.20.Incl.Guide-iND\Setup\EnSetup420.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
674
Read events
643
Write events
31
Delete events
0
Modification events
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\EnCase.Forensic.v4.20.Incl.Guide-iND.rar | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-10046 |
Value: Internet Shortcut | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
10
Suspicious files
3
Text files
49
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2628.38357\EnCase.Forensic.v4.20.Incl.Guide-iND\Guide\EFE_Manual_English_rev420_C.pdf | — | |
MD5:— | SHA256:— | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2628.38357\EnCase.Forensic.v4.20.Incl.Guide-iND\0day warez.url | text | |
MD5:— | SHA256:— | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2628.38357\EnCase.Forensic.v4.20.Incl.Guide-iND\Crack\ind-encase420.nfo | text | |
MD5:— | SHA256:— | |||
| 1596 | EnSetup420.exe | C:\Windows\system32\drivers\gsimrx.sys | executable | |
MD5:— | SHA256:— | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2628.38357\EnCase.Forensic.v4.20.Incl.Guide-iND\Crack\Enhkey.dll | executable | |
MD5:— | SHA256:— | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2628.38357\EnCase.Forensic.v4.20.Incl.Guide-iND\Crack\file_id.diz | text | |
MD5:— | SHA256:— | |||
| 1596 | EnSetup420.exe | C:\Program Files\EnCase4\gsiata.inf | binary | |
MD5:— | SHA256:— | |||
| 1596 | EnSetup420.exe | C:\Program Files\EnCase4\FileTypes.ini | text | |
MD5:— | SHA256:— | |||
| 1596 | EnSetup420.exe | C:\Windows\system32\drivers\enport.sys | executable | |
MD5:— | SHA256:— | |||
| 1596 | EnSetup420.exe | C:\Program Files\EnCase4\Keywords.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report