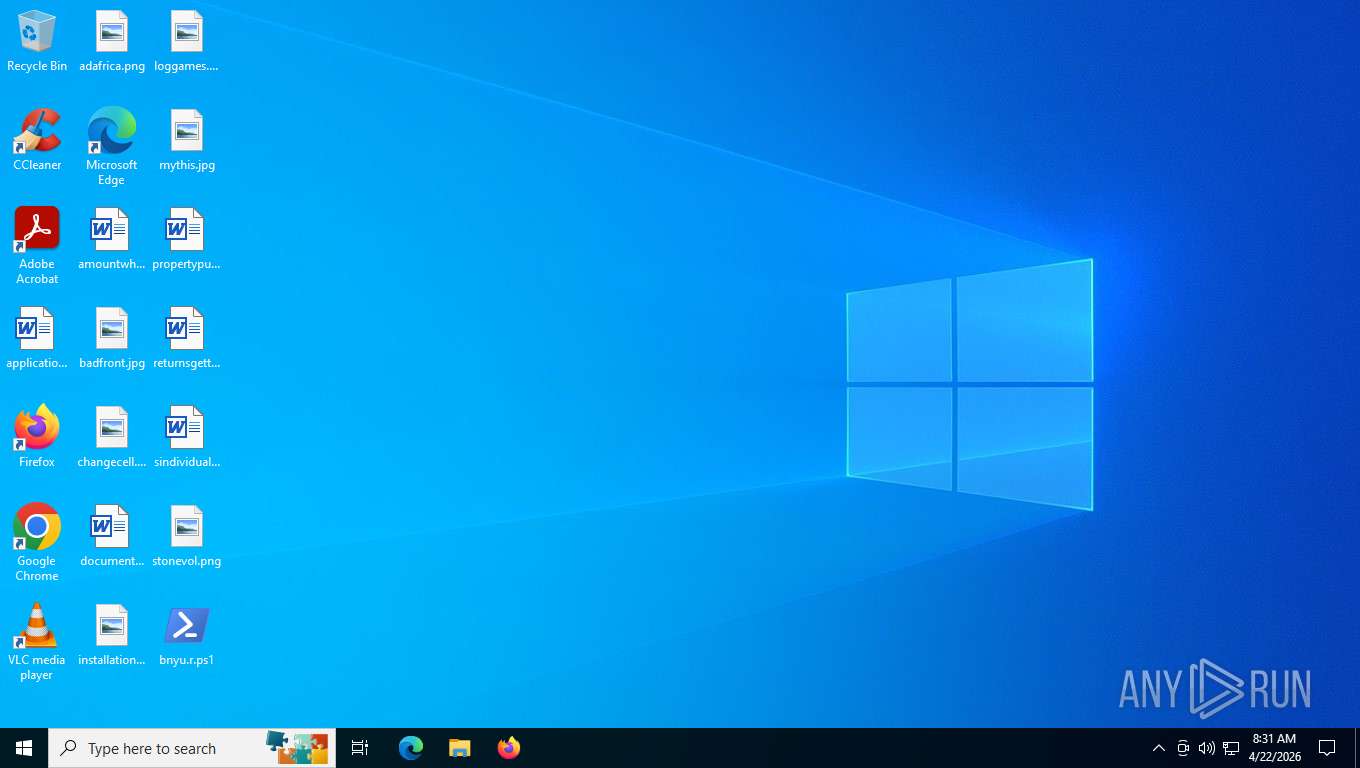
| File name: | bnyu.r |
| Full analysis: | https://app.any.run/tasks/311c6448-7c0a-461b-83ea-e13360d1383f |
| Verdict: | Malicious activity |
| Threats: | DonutLoader is a versatile, open-source-based in-memory loader that turns .NET assemblies, executables, DLLs, and scripts into position-independent shellcode for execution entirely in RAM. Originally derived from the popular Donut tool, it enables threat actors to bypass traditional antivirus and EDR solutions by avoiding disk writes and injecting payloads directly into legitimate Windows processes. |
| Analysis date: | April 22, 2026, 12:31:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (47811), with CRLF line terminators |
| MD5: | A490AB0373F922D842891125441DD896 |
| SHA1: | CBD86DB11499512F4894F0ED2FBC7ABF3BD513BD |
| SHA256: | 9D0CE7A84E62E3458B82D682C7C3F97D095CB2FBA8CAA0263EE8929994990254 |
| SSDEEP: | 1536:n0UX4RhoAhDY/aS7TWfmVmli6Tao/W4w+6mnNYS8qF3BQz308KTjsgX7ThG1PuZC:n0s4kA2LYlDkSG7DfYx+ |
MALICIOUS
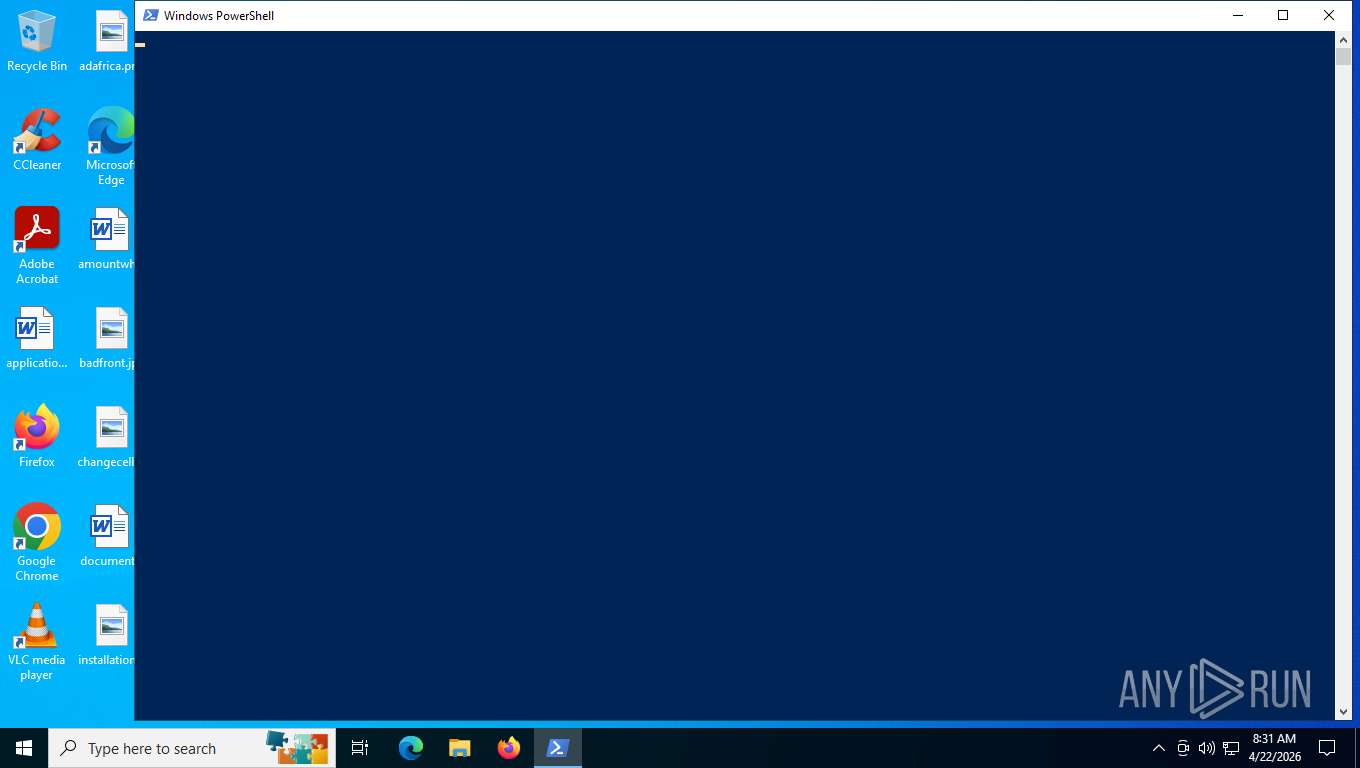
Run PowerShell with an invisible window
- powershell.exe (PID: 204)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 204)
Steals credentials from Web Browsers
- powershell.exe (PID: 204)
DONUTLOADER has been detected (YARA)
- powershell.exe (PID: 204)
Actions looks like stealing of personal data
- powershell.exe (PID: 204)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7608)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7608)
Bypass execution policy to execute commands
- powershell.exe (PID: 7608)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 204)
Possible stealing of messenger data
- powershell.exe (PID: 204)
Possible stealing from crypto wallets
- powershell.exe (PID: 204)
Possible stealing of VPN data
- powershell.exe (PID: 204)
Possible stealing of FTP data
- powershell.exe (PID: 204)
Possible stealing of email data
- powershell.exe (PID: 204)
Possible stealing from browsers
- powershell.exe (PID: 204)
Possible stealing from password managers
- powershell.exe (PID: 204)
Possible stealing from 2fa
- powershell.exe (PID: 204)
Multiple wallet extension IDs have been found
- powershell.exe (PID: 204)
INFO
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 7608)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7608)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7608)
Gets data length (POWERSHELL)
- powershell.exe (PID: 204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
164
Monitored processes
31
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -WindowStyle Hidden -Command - | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --no-startup-window --type=utility --utility-sub-type=unspecified | C:\Program Files\Google\Chrome\Application\chrome.exe | — | powershell.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Mozilla Firefox\firefox.exe" --no-startup-window --type=utility --utility-sub-type=unspecified | C:\Program Files\Mozilla Firefox\firefox.exe | — | powershell.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Mozilla Firefox\firefox.exe" --no-startup-window --type=utility --utility-sub-type=unspecified | C:\Program Files\Mozilla Firefox\firefox.exe | — | powershell.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 2364 | "C:\WINDOWS\SysWOW64\dllhost.exe" --no-startup-window --type=utility --utility-sub-type=unspecified | C:\Windows\SysWOW64\dllhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --type=utility --utility-sub-type=unspecified | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Mozilla Firefox\firefox.exe" --no-startup-window --type=utility --utility-sub-type=unspecified | C:\Program Files\Mozilla Firefox\firefox.exe | — | powershell.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 3112 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --no-startup-window --type=utility --utility-sub-type=unspecified | C:\Program Files\Google\Chrome\Application\chrome.exe | — | powershell.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --no-startup-window --type=utility --utility-sub-type=unspecified | C:\Program Files\Google\Chrome\Application\chrome.exe | — | powershell.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
13 737
Read events
13 736
Write events
1
Delete events
0
Modification events
| (PID) Process: | (8072) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
Executable files
0
Suspicious files
5
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7608 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\L1OJN83DC7ZOSMU4DY8Q.temp | binary | |
MD5:2FF56949B1995965EA251A71FECF4F3A | SHA256:CB81A9831A880FBC202AE094ED8891405BA106864E1E1C4FEC508B76B9D1E913 | |||
| 7608 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:2FF56949B1995965EA251A71FECF4F3A | SHA256:CB81A9831A880FBC202AE094ED8891405BA106864E1E1C4FEC508B76B9D1E913 | |||
| 7608 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFe0d4a.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 7608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2szvuuws.xd2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ydjzb05s.che.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 204 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bj3gg3se.3f5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 204 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2rxledaw.na3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7608 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:CED81704A99B2649EB1F03CF7D7DD1B8 | SHA256:766B01A06A3F9A828D2F3B26949AEB6AC964EAECE1A0921CE76CCA3F06DBBCC4 | |||
| 204 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:B3E9B84E6FD9AAE69ACD096485389919 | SHA256:3FC008E3BEA6F9948BFDD70F91BA2F556CBB1B77083F075292FCD87FCD7E185E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
61
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
8072 | slui.exe | POST | 500 | 128.24.231.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
— | — | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
3044 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
3044 | svchost.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6768 | SIHClient.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | NL | binary | 824 b | whitelisted |
6768 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
6768 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
6768 | SIHClient.exe | GET | 200 | 135.233.95.135:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | — |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3044 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | slui.exe | 128.24.231.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.241.205:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3044 | svchost.exe | 23.55.110.211:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.55.110.211:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
3044 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
tq.trxzidan.icu |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2232 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
204 | powershell.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |