| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/98ecce2e-d1b5-42c6-8215-5d513aa24196 |
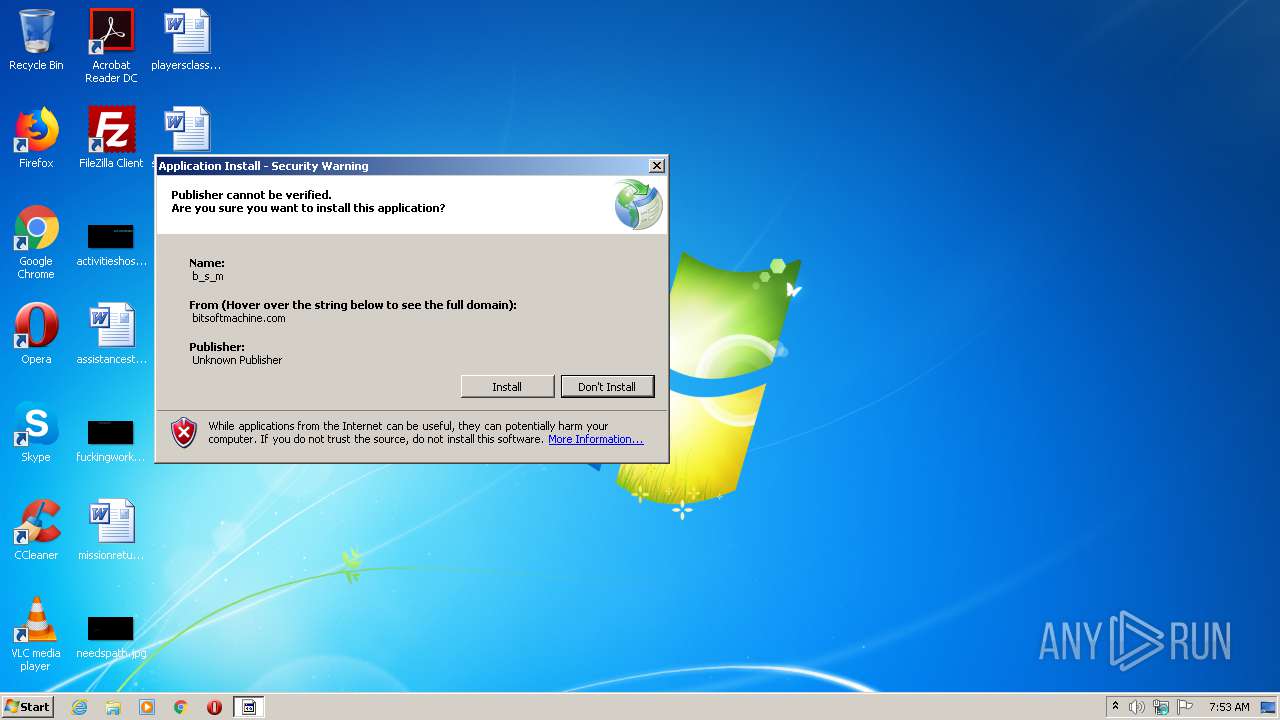
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2020, 06:52:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9C81E83C39B38FF41B3F743750A8645A |
| SHA1: | 47CE7A861D54D7A536551B0C50C6296995030133 |
| SHA256: | 9CFD8FC3DC3ABDF31750DF9D2967CB1118CBCC072B553424BAD3230FF7C2BF2B |
| SSDEEP: | 12288:ADuWNvtS/PHV4c1JwX2afK+ixeCzweMb01JQntLOCrweM10K:ADlvEPTJmix5zwemro9 |
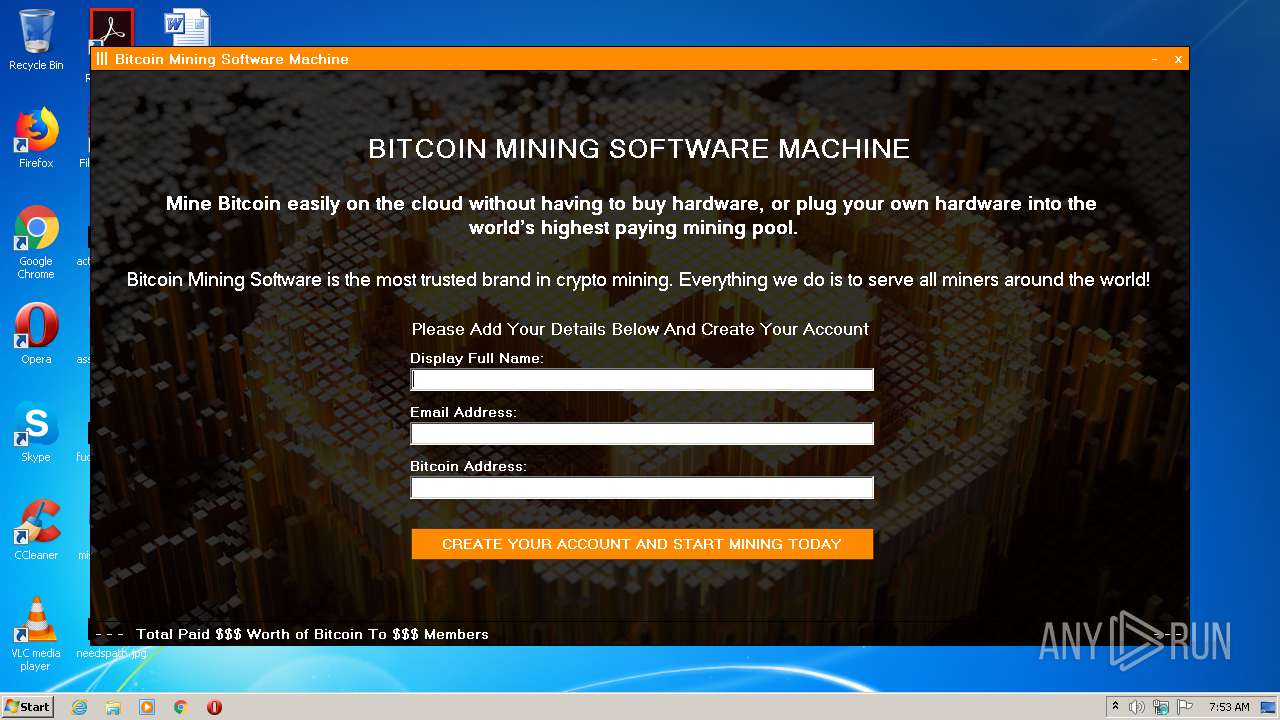
MALICIOUS
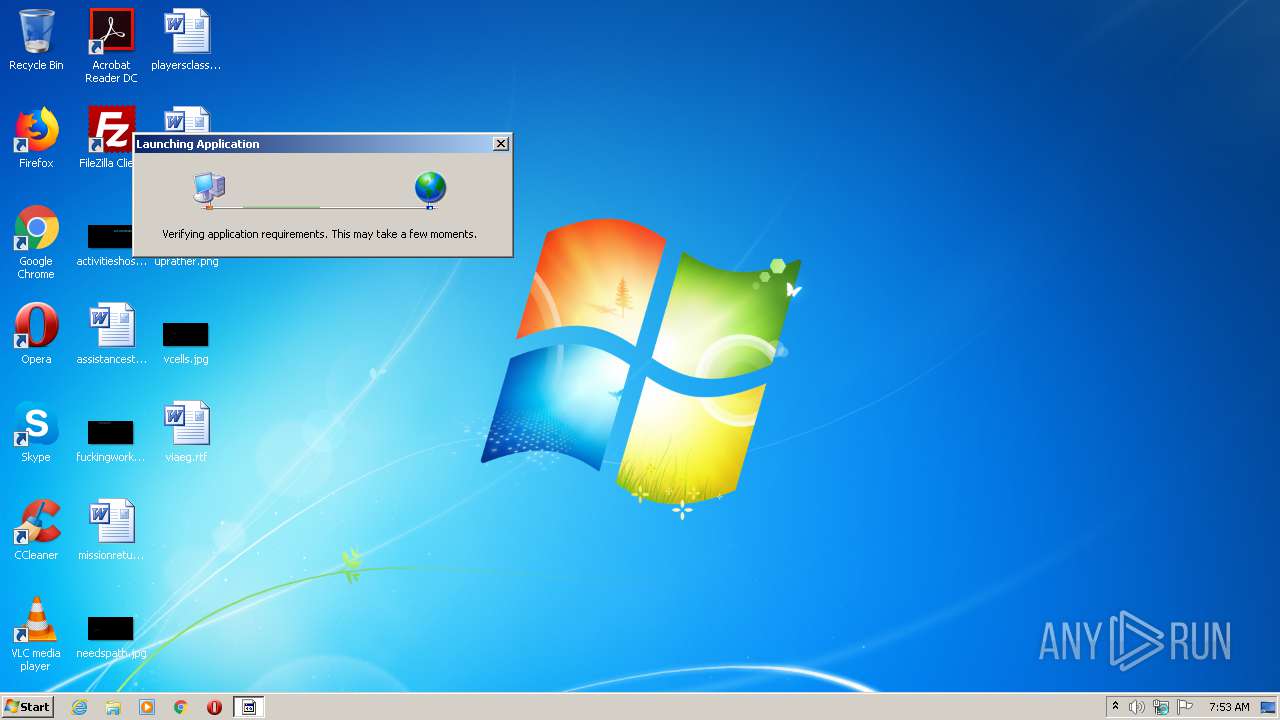
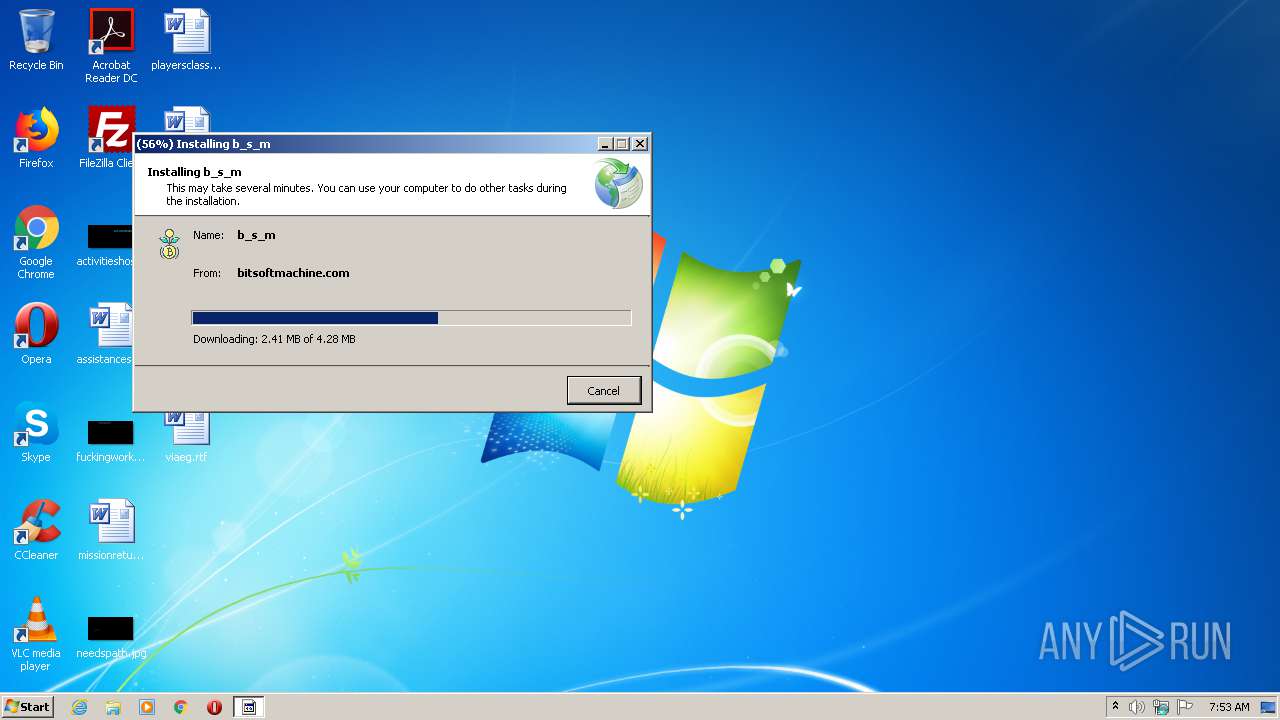
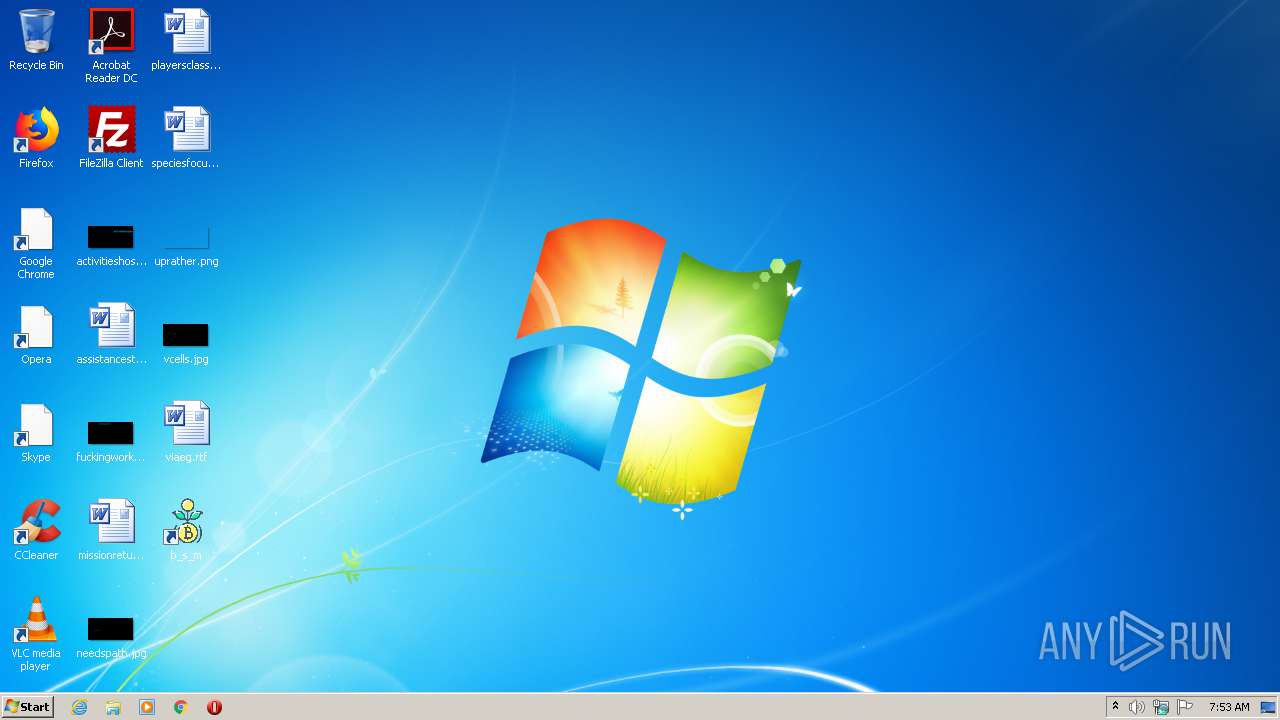
Application was dropped or rewritten from another process
- b_s_m.exe (PID: 1940)
Loads dropped or rewritten executable
- b_s_m.exe (PID: 1940)
- dfsvc.exe (PID: 2828)
SUSPICIOUS
Reads Environment values
- dfsvc.exe (PID: 2828)
Creates a software uninstall entry
- dfsvc.exe (PID: 2828)
Reads Internet Cache Settings
- setup.exe (PID: 2392)
- dfsvc.exe (PID: 2828)
Reads internet explorer settings
- dfsvc.exe (PID: 2828)
Creates files in the user directory
- dfsvc.exe (PID: 2828)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 2828)
INFO
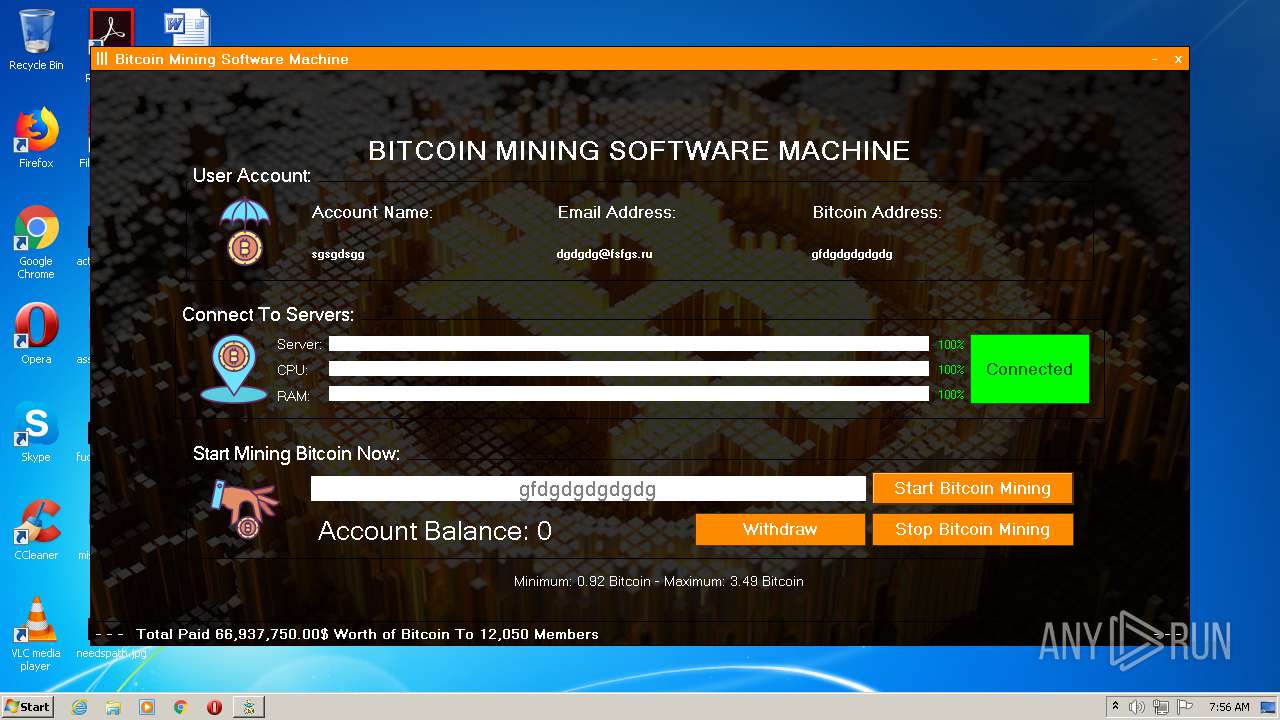
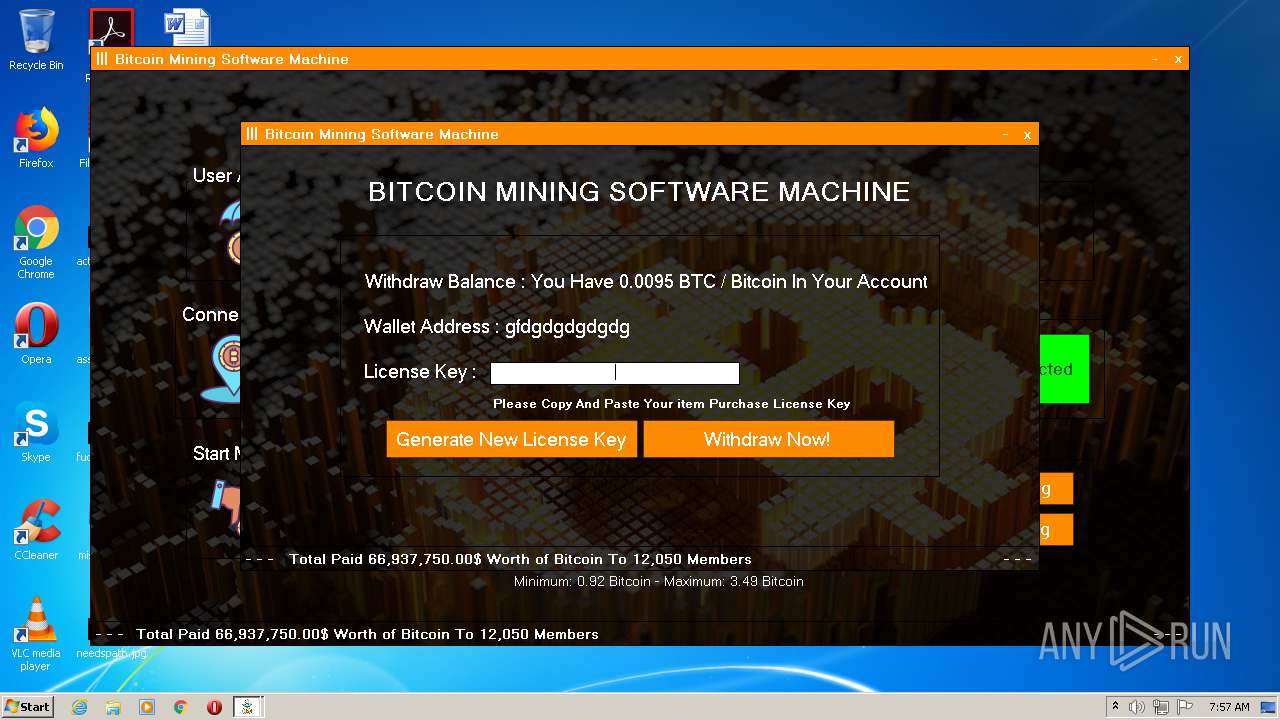
Dropped object may contain Bitcoin addresses
- dfsvc.exe (PID: 2828)
Reads settings of System Certificates
- dfsvc.exe (PID: 2828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:15 23:29:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.1 |
| CodeSize: | 374784 |
| InitializedDataSize: | 168448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x352a7 |
| OSVersion: | 5.1 |
| ImageVersion: | 10 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.0.28315.86 |
| ProductVersionNumber: | 16.0.28315.86 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 16.0.28315.86 built by: D16.0 |
| InternalName: | setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | setup.exe |
| ProductName: | - |
| ProductVersion: | 16.0.28315.86 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2018 22:29:32 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 16.0.28315.86 built by: D16.0 |
| InternalName: | setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | setup.exe |
| ProductName: | - |
| ProductVersion: | 16.0.28315.86 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Nov-2018 22:29:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0005B768 | 0x0005B800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44319 |
.data | 0x0005D000 | 0x0000260C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.44844 |
.idata | 0x00060000 | 0x0000152E | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.45391 |
.rsrc | 0x00062000 | 0x00022A18 | 0x00022C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.74213 |
.reloc | 0x00085000 | 0x00003B60 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62056 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22945 | 1378 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.59785 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.61852 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 1.63426 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 7.87399 | 7820 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.07929 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.33247 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.65064 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.99341 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 7.07398 | 1885 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll (delay-loaded) |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
Secur32.dll |
USER32.dll |
WININET.dll |
msi.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_DecodePointerInternal@4 | 1 | 0x000225E6 |
_EncodePointerInternal@4 | 2 | 0x00022601 |
Total processes
40
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
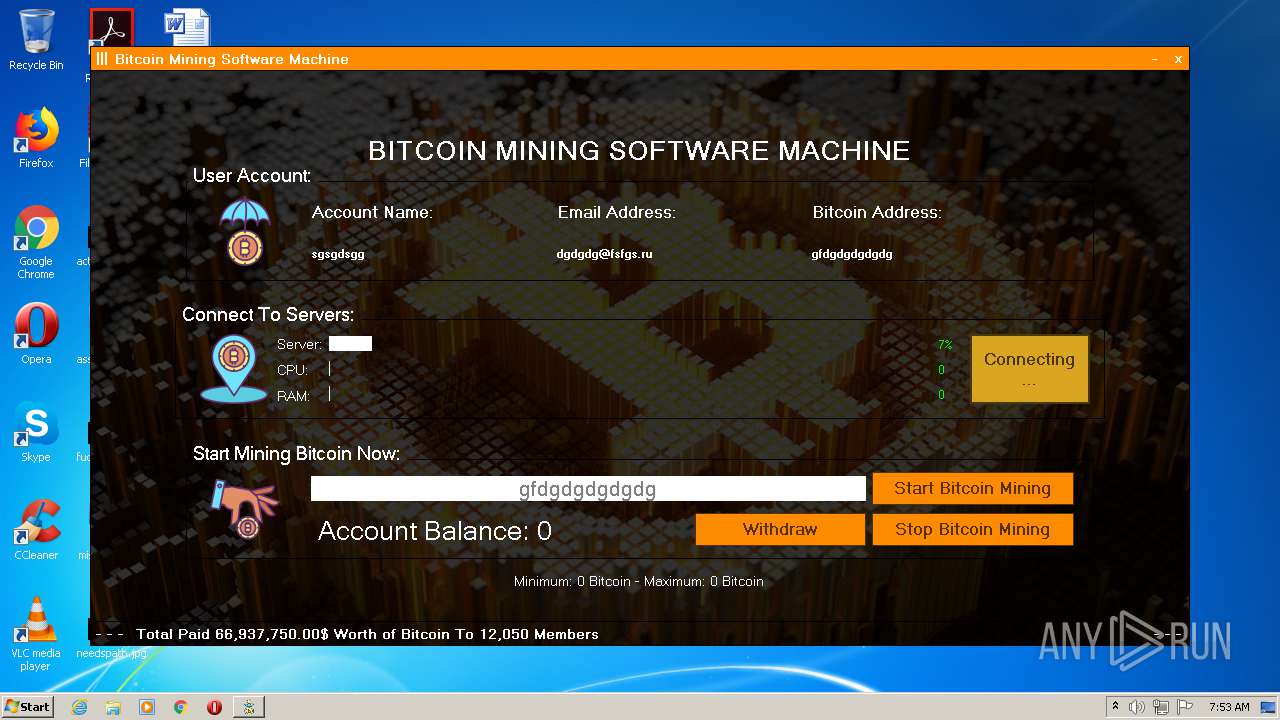
| 1940 | "C:\Users\admin\AppData\Local\Apps\2.0\DGHLZ6LK.682\YVGJE23H.NBV\b_s_..tion_b4ba41b11bdbd1f0_0001.0000_59eed639da6ce6f3\b_s_m.exe" | C:\Users\admin\AppData\Local\Apps\2.0\DGHLZ6LK.682\YVGJE23H.NBV\b_s_..tion_b4ba41b11bdbd1f0_0001.0000_59eed639da6ce6f3\b_s_m.exe | dfsvc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: b_s_m Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2392 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Exit code: 0 Version: 16.0.28315.86 built by: D16.0 Modules
| |||||||||||||||
| 2828 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
Total events
411
Read events
205
Write events
190
Delete events
16
Modification events
| (PID) Process: | (2392) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2392) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2392) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2392) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2392) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2392) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2392) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2392) setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2828) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: XZG3R5YOXREGRR6QN6BHHK5A | |||
| (PID) Process: | (2828) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete value | Name: | ComponentStore_RandomString |
Value: XZG3R5YOXREGRR6QN6BHHK5A | |||
Executable files
8
Suspicious files
16
Text files
17
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2392 | setup.exe | C:\Users\admin\AppData\Local\Temp\Cab6B6D.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | setup.exe | C:\Users\admin\AppData\Local\Temp\Tar6B6E.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Cab74C3.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Tar74C4.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Cab74E4.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Tar74E5.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Cab7573.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Tar7574.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Cab75D3.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Tar75D4.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2392 | setup.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
2828 | dfsvc.exe | GET | 200 | 8.248.131.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.7 Kb | whitelisted |
2828 | dfsvc.exe | GET | 304 | 8.248.131.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.7 Kb | whitelisted |
2392 | setup.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCCThph0aSN8W | US | der | 1.73 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2392 | setup.exe | 160.153.133.77:443 | bitsoftmachine.com | GoDaddy.com, LLC | US | malicious |
2392 | setup.exe | 192.124.249.23:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2828 | dfsvc.exe | 160.153.133.77:443 | bitsoftmachine.com | GoDaddy.com, LLC | US | malicious |
2828 | dfsvc.exe | 8.248.131.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1940 | b_s_m.exe | 160.153.133.77:3306 | bitsoftmachine.com | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bitsoftmachine.com |
| suspicious |
ocsp.godaddy.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1940 | b_s_m.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] Remote MySQL Administration |
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status Originated: -1073741772
*** Source File: d:\iso_whid\x86fre\base\isolation\win32\isoreg_direct.cpp, line 1127
|