| File name: | CH341SER.EXE |
| Full analysis: | https://app.any.run/tasks/21b03d86-74e8-42a0-a82b-5931e9b29f1f |
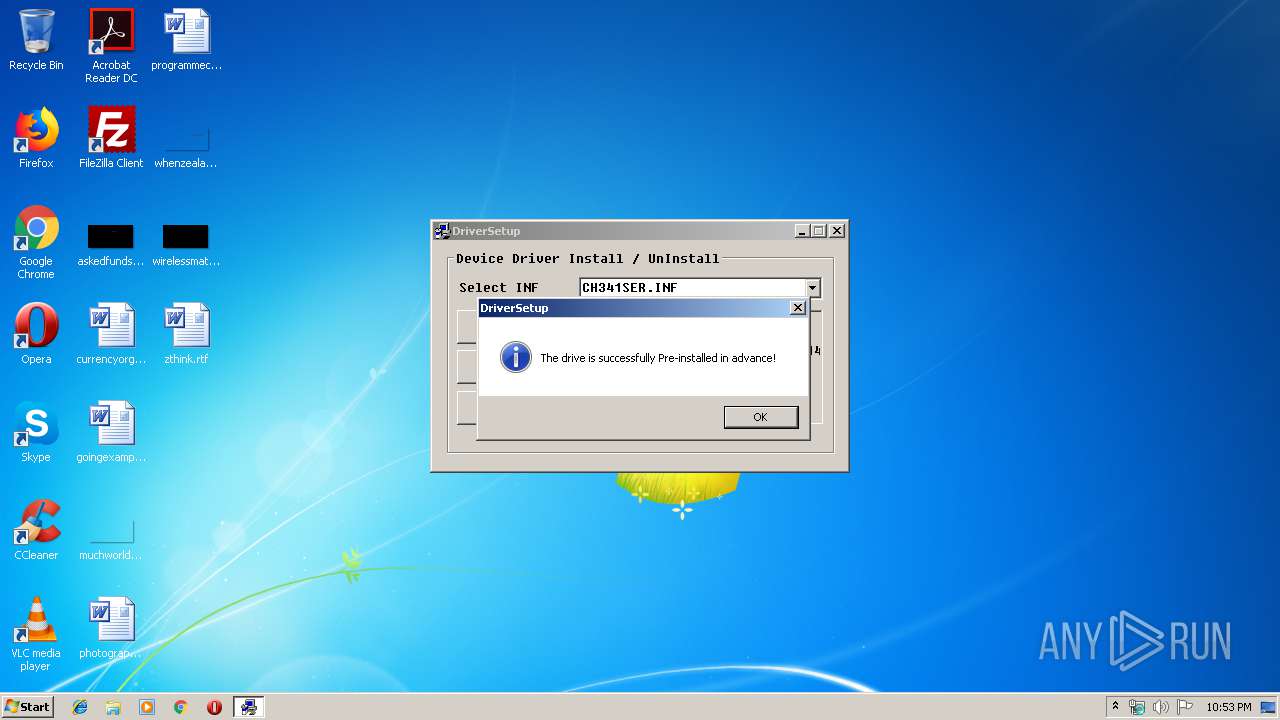
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 21:52:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 1AF3FDEBFBAB3E247FEB588AEA64DD64 |
| SHA1: | D557A8978877199BAFE2E7BAAC63ADAB17BED05D |
| SHA256: | 9CF96FDDF474EDA80F2B4C09F8EF19443CF6768429819E4CBA7B869291B7B8B5 |
| SSDEEP: | 3072:h8U2yJN5f661xRZbALxB1Ojdgx8GYXfPGJ6I7onkduFJcc0WMc23dFORPSPo46Om:h8U2qy6rRZb7jxGYXDFJmWM93dYlGAGs |
MALICIOUS
Application was dropped or rewritten from another process
- SETUP.EXE (PID: 2720)
- SETUP.EXE (PID: 2372)
Loads dropped or rewritten executable
- SETUP.EXE (PID: 2372)
SUSPICIOUS
Executable content was dropped or overwritten
- CH341SER.EXE (PID: 3592)
- SETUP.EXE (PID: 2372)
Executed via COM
- DrvInst.exe (PID: 2804)
Removes files from Windows directory
- DrvInst.exe (PID: 2804)
- SETUP.EXE (PID: 2372)
Creates files in the Windows directory
- DrvInst.exe (PID: 2804)
- SETUP.EXE (PID: 2372)
Creates files in the driver directory
- DrvInst.exe (PID: 2804)
- SETUP.EXE (PID: 2372)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.3) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.1) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Win32 Executable Watcom C++ (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:05:22 06:59:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 81920 |
| InitializedDataSize: | 22016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-May-2007 04:59:14 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-May-2007 04:59:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00014000 | 0x00013600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44419 |
.data | 0x00015000 | 0x00007000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.91827 |
.idata | 0x0001C000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.1239 |
.rsrc | 0x0001D000 | 0x00004000 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.52866 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06643 | 831 | Latin 1 / Western European | Russian - Russia | RT_MANIFEST |
7 | 3.24143 | 556 | Latin 1 / Western European | Russian - Russia | RT_STRING |
8 | 3.28574 | 946 | Latin 1 / Western European | Russian - Russia | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | Russian - Russia | RT_STRING |
10 | 3.15563 | 638 | Latin 1 / Western European | Russian - Russia | RT_STRING |
100 | 1.83321 | 20 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
101 | 4.19099 | 2998 | Latin 1 / Western European | Russian - Russia | RT_BITMAP |
ASKNEXTVOL | 3.42532 | 642 | Latin 1 / Western European | Russian - Russia | RT_DIALOG |
GETPASSWORD1 | 3.29928 | 314 | Latin 1 / Western European | Russian - Russia | RT_DIALOG |
LICENSEDLG | 3.17045 | 232 | Latin 1 / Western European | Russian - Russia | RT_DIALOG |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
38
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
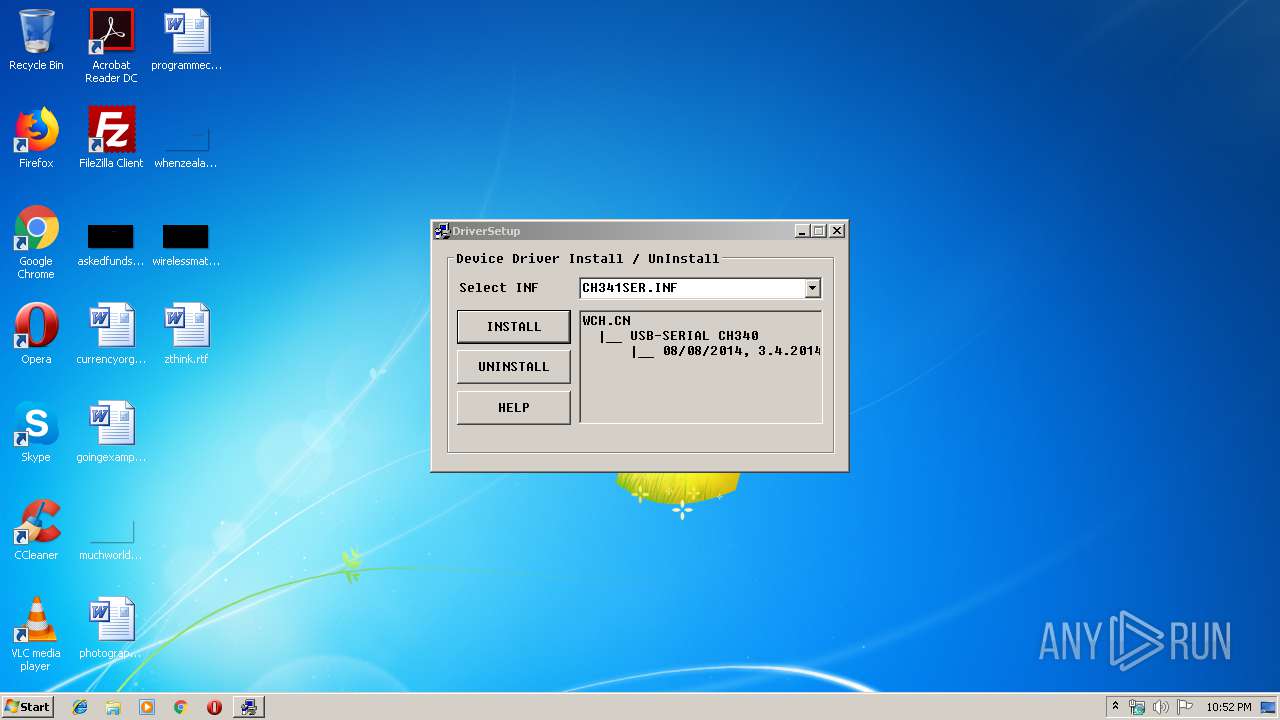
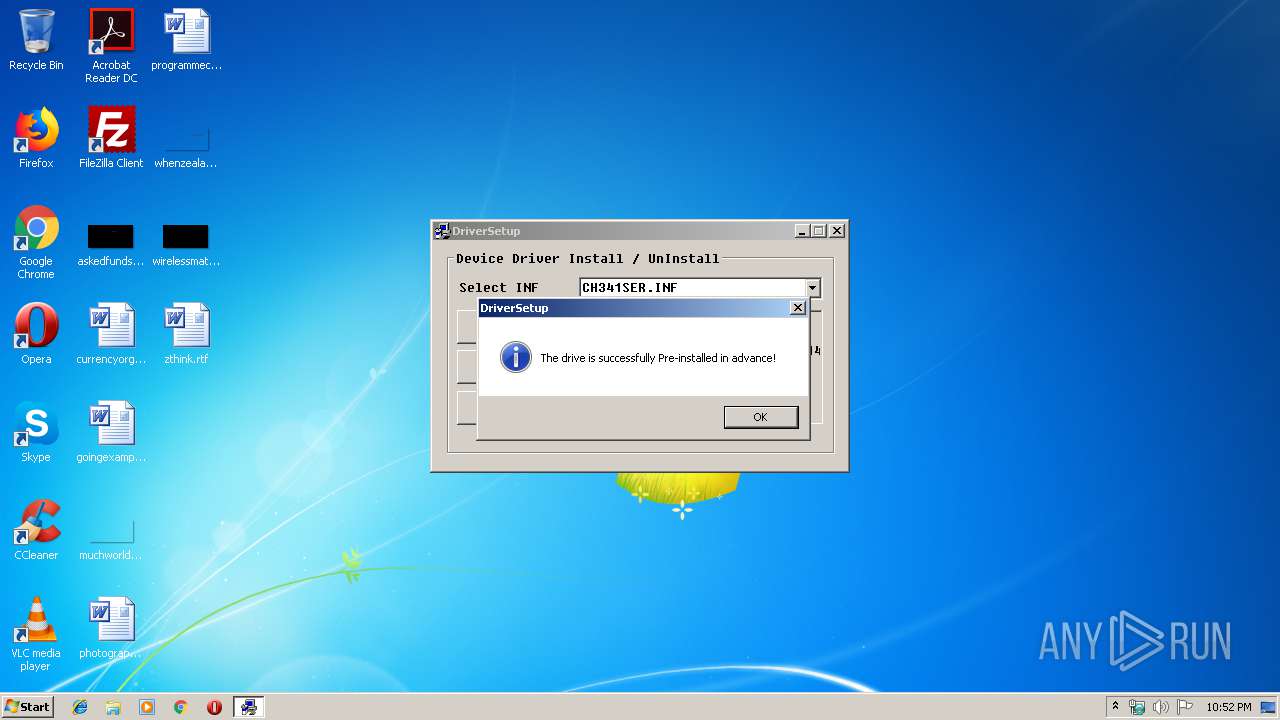
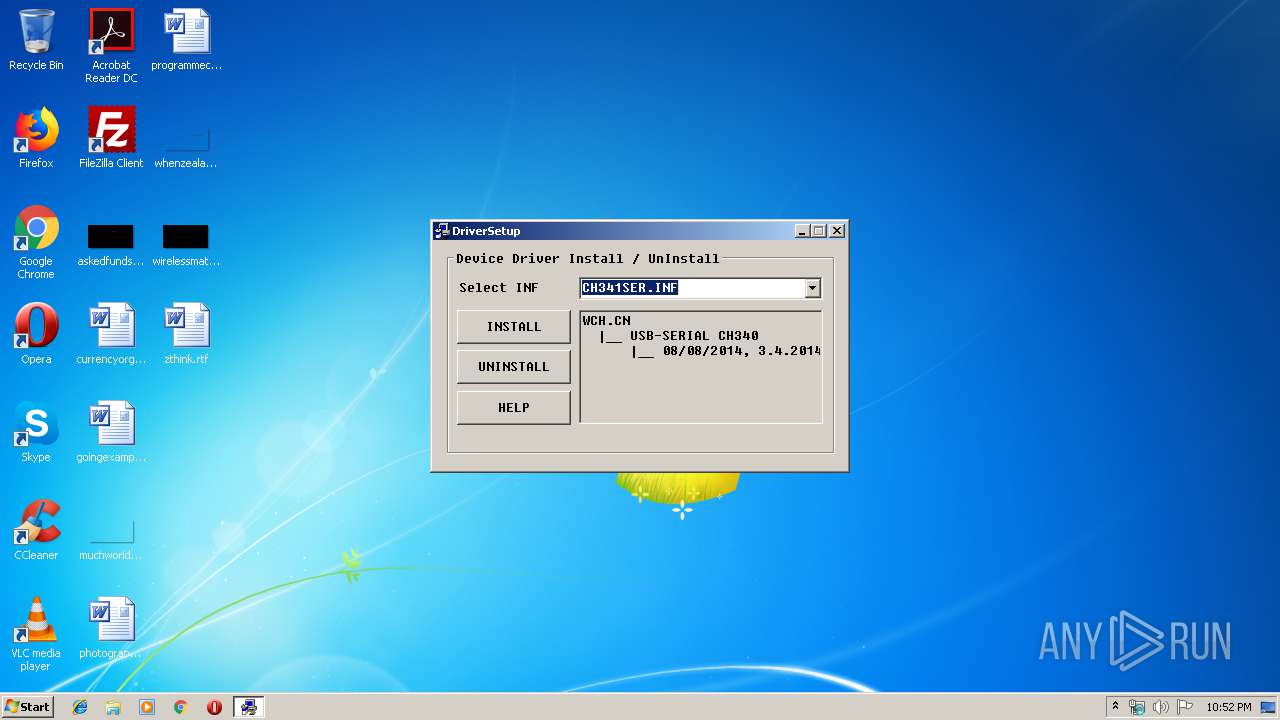
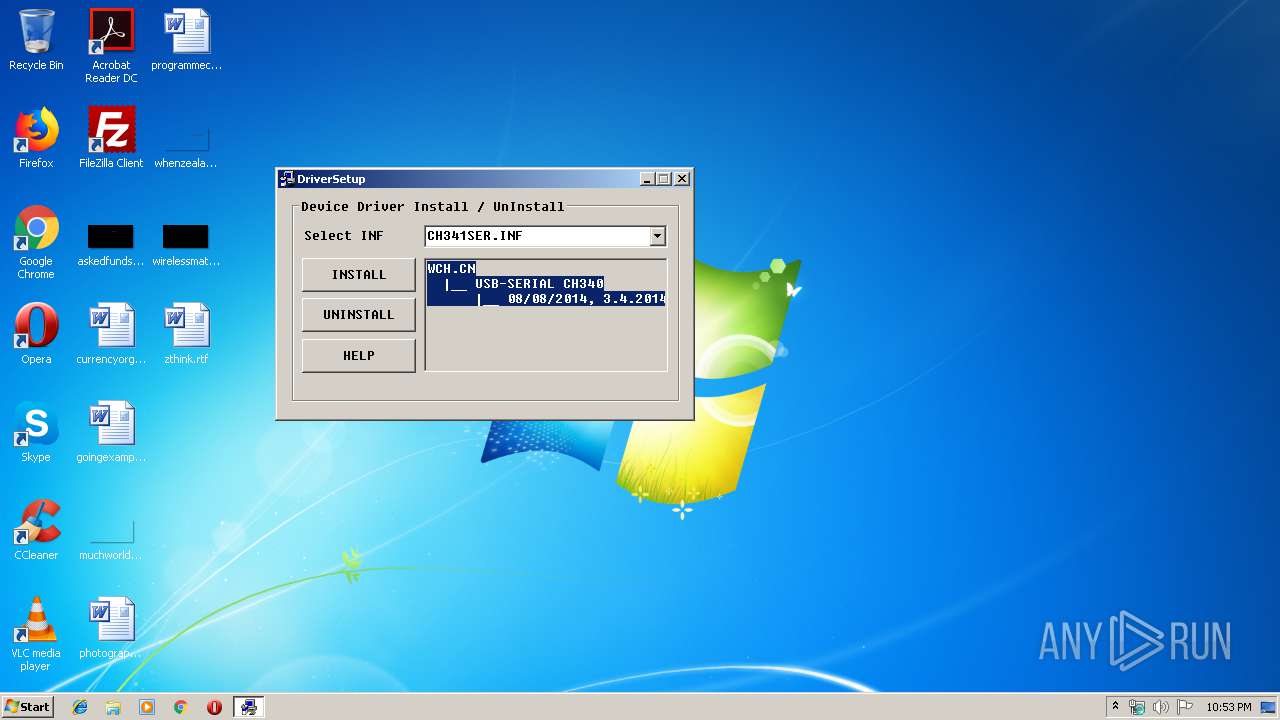
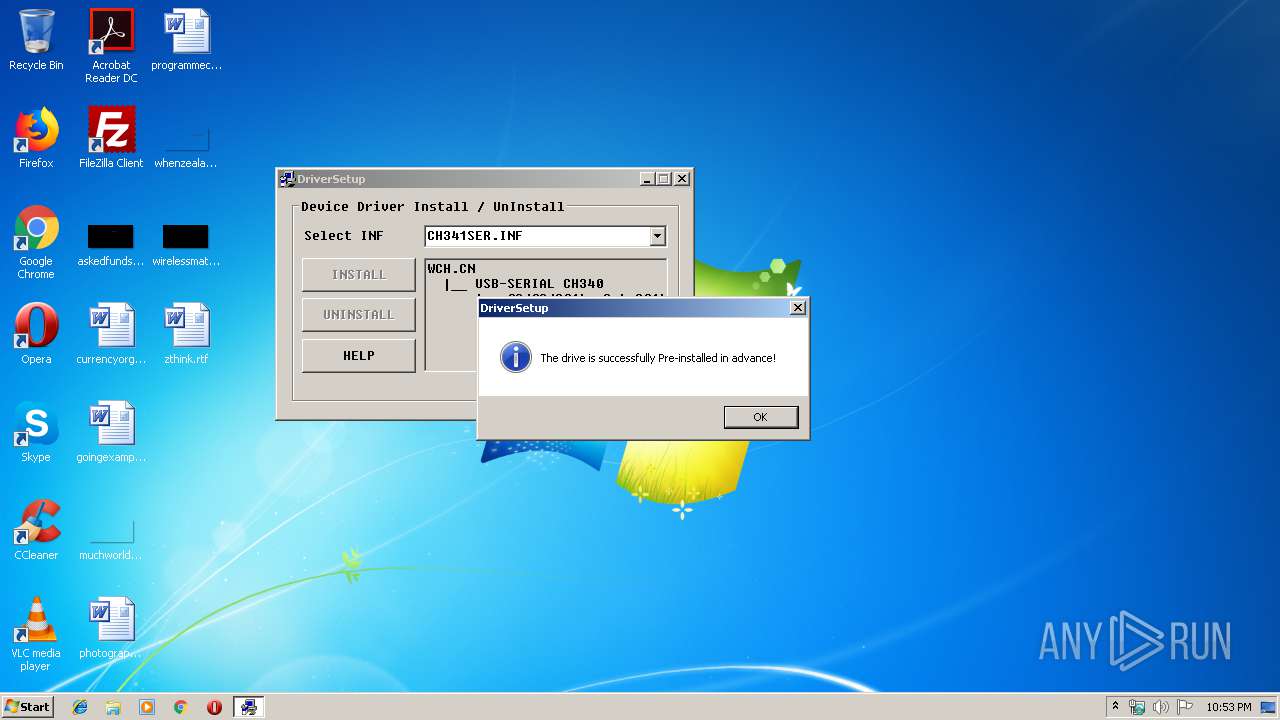
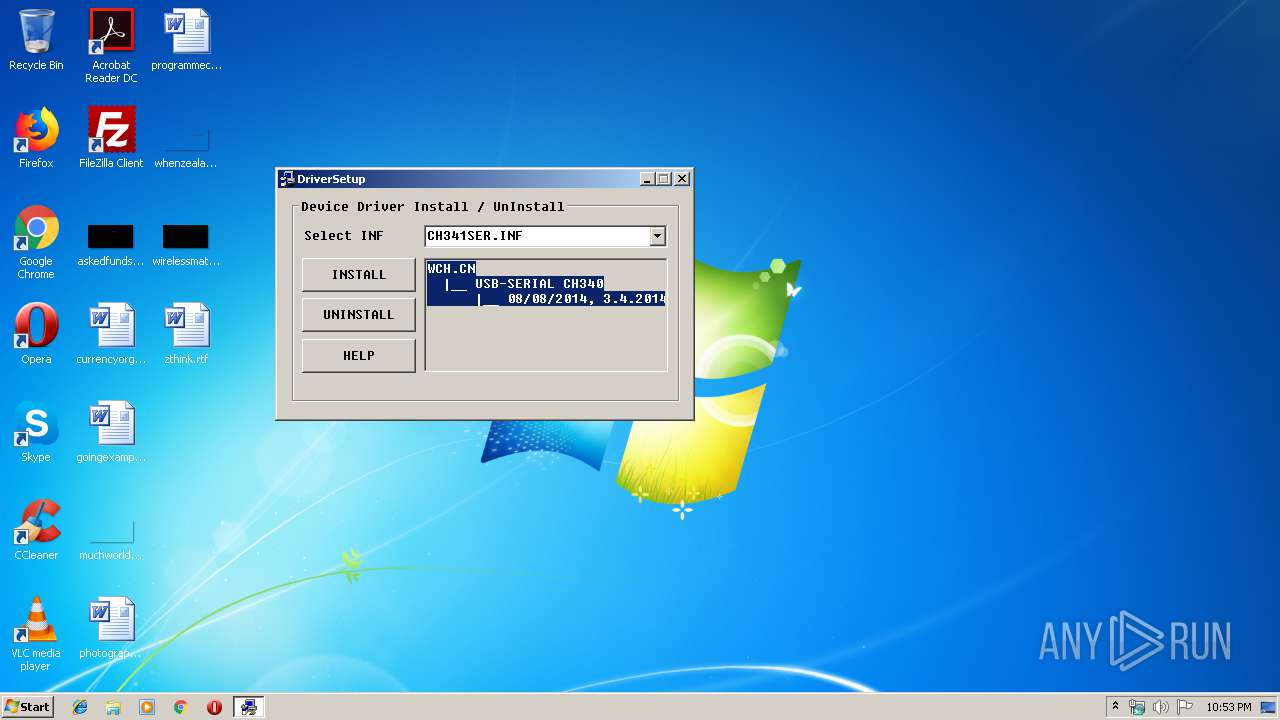
| 2372 | "C:\WCH.CN\CH341SER\SETUP.EXE" | C:\WCH.CN\CH341SER\SETUP.EXE | CH341SER.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: EXE For Driver Installation Exit code: 0 Version: 1, 6, 8, 0 Modules
| |||||||||||||||
| 2720 | "C:\WCH.CN\CH341SER\SETUP.EXE" | C:\WCH.CN\CH341SER\SETUP.EXE | — | CH341SER.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: EXE For Driver Installation Exit code: 3221226540 Version: 1, 6, 8, 0 Modules
| |||||||||||||||
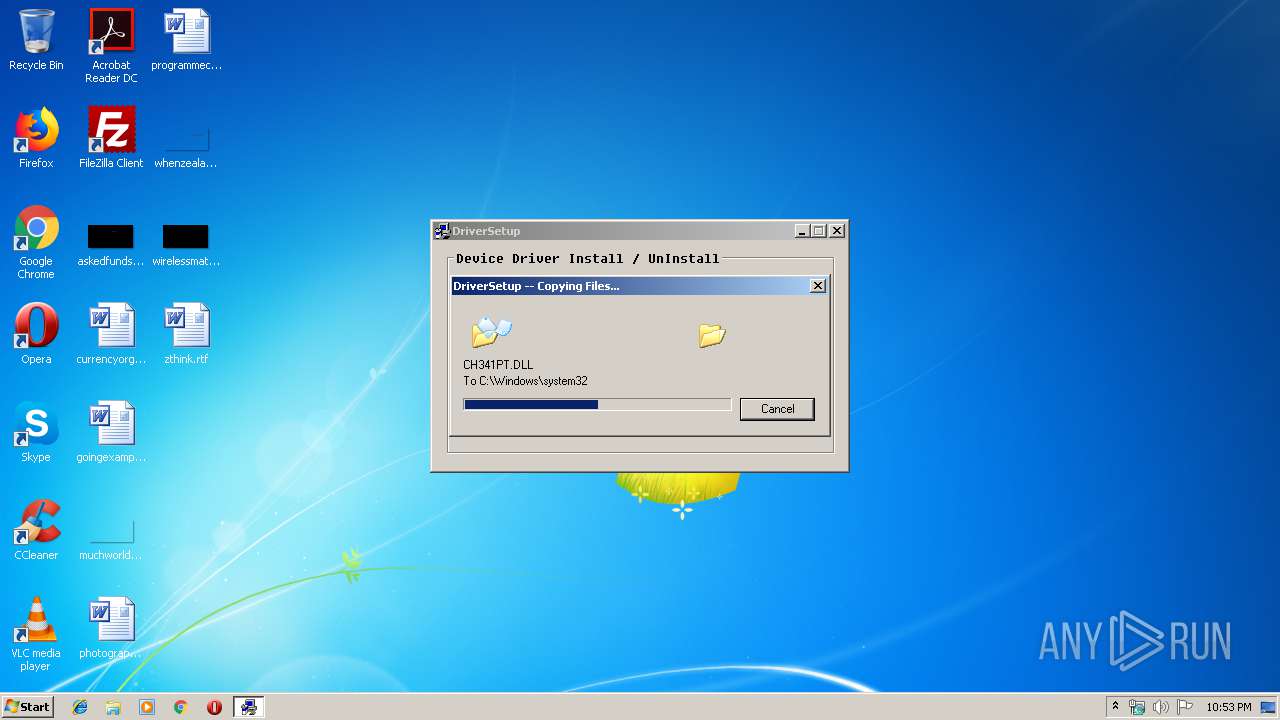
| 2804 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{22c0f6f5-9494-641c-cf00-42493c8fb36d}\CH341SER.INF" "0" "6dbd0d02f" "0000058C" "WinSta0\Default" "00000300" "208" "C:\WCH.CN\CH341SER" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3592 | "C:\Users\admin\AppData\Local\Temp\CH341SER.EXE" | C:\Users\admin\AppData\Local\Temp\CH341SER.EXE | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
69
Read events
42
Write events
27
Delete events
0
Modification events
| (PID) Process: | (3592) CH341SER.EXE | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | C%%WCH.CN%CH341SER |
Value: C:\WCH.CN\CH341SER | |||
| (PID) Process: | (3592) CH341SER.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3592) CH341SER.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2372) SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (2372) SETUP.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2804) DrvInst.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2372) SETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
Executable files
16
Suspicious files
8
Text files
353
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2372 | SETUP.EXE | C:\Users\admin\AppData\Local\Temp\{22c0f6f5-9494-641c-cf00-42493c8fb36d}\SET19DE.tmp | — | |
MD5:— | SHA256:— | |||
| 2372 | SETUP.EXE | C:\Users\admin\AppData\Local\Temp\{22c0f6f5-9494-641c-cf00-42493c8fb36d}\SET19DF.tmp | — | |
MD5:— | SHA256:— | |||
| 2372 | SETUP.EXE | C:\Users\admin\AppData\Local\Temp\{22c0f6f5-9494-641c-cf00-42493c8fb36d}\SET19E0.tmp | — | |
MD5:— | SHA256:— | |||
| 2372 | SETUP.EXE | C:\Users\admin\AppData\Local\Temp\{22c0f6f5-9494-641c-cf00-42493c8fb36d}\SET19F1.tmp | — | |
MD5:— | SHA256:— | |||
| 3592 | CH341SER.EXE | C:\WCH.CN\CH341SER\CH341S98.SYS | executable | |
MD5:B6F4A83911336E84BEAD8F8905285FAB | SHA256:0ECD1222627271EA31D3B64796992B6DAF5133D64CC26D43B3873CBE32FD59CB | |||
| 3592 | CH341SER.EXE | C:\WCH.CN\CH341SER\SETUP.EXE | executable | |
MD5:181F68547D52360FC142AC3ADC2436B7 | SHA256:A8F306D5BA1A23F587283FD410313F50AC1AC5CE1268938B065130A0DC84C658 | |||
| 2804 | DrvInst.exe | C:\Windows\System32\DriverStore\Temp\{60f1be18-4c32-6627-8066-5c0b2811627a}\SET1A4B.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | DrvInst.exe | C:\Windows\System32\DriverStore\Temp\{60f1be18-4c32-6627-8066-5c0b2811627a}\CH341SER.CAT | — | |
MD5:— | SHA256:— | |||
| 2804 | DrvInst.exe | C:\Windows\System32\DriverStore\Temp\{60f1be18-4c32-6627-8066-5c0b2811627a}\SET1A5C.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | DrvInst.exe | C:\Windows\System32\DriverStore\Temp\{60f1be18-4c32-6627-8066-5c0b2811627a}\CH341SER.INF | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report