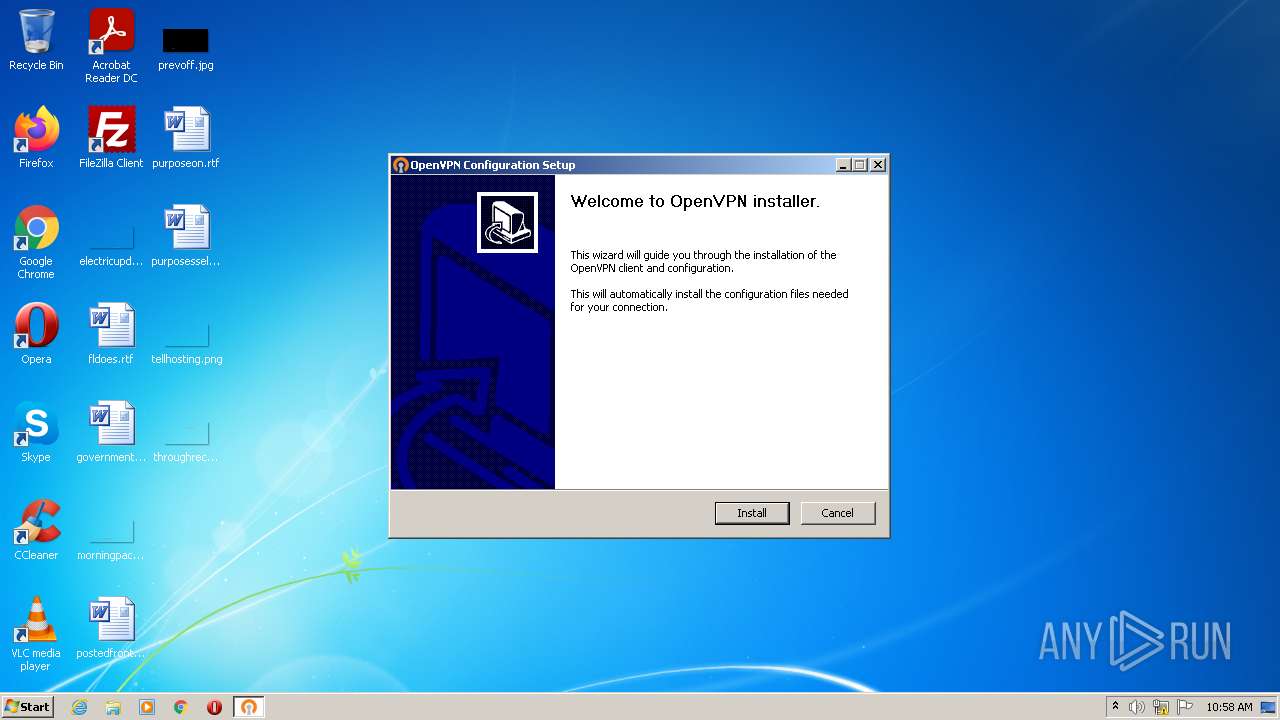
| File name: | openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe |
| Full analysis: | https://app.any.run/tasks/5cf4ef1e-c7ca-4e6e-91a9-566be8a96d3f |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2022, 10:58:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 21BD6086E4D0481E09C2C362CA53C501 |
| SHA1: | 87A3BBD81D071DFE5095ECDB6BBD869DE331AD7C |
| SHA256: | 9CF80B09A24A9B73721DFDC3611E296832C6537F01CE6A175013EFF8A43EFB79 |
| SSDEEP: | 98304:zgwRfSNUtMJd7kdeCdl44lNhVyx4nsi18fG65jZvAohb0kcxsICQ3:zgDUCdAnln7yqjmG65Noo0xsIR3 |
MALICIOUS
Application was dropped or rewritten from another process
- openvpn-postinstall.exe (PID: 2096)
- openvpn-postinstall.exe (PID: 2552)
Loads dropped or rewritten executable
- openvpn-postinstall.exe (PID: 2552)
Drops executable file immediately after starts
- openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe (PID: 3504)
- openvpn-postinstall.exe (PID: 2552)
SUSPICIOUS
Checks supported languages
- openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe (PID: 3504)
- openvpn-postinstall.exe (PID: 2552)
Reads the computer name
- openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe (PID: 3504)
- openvpn-postinstall.exe (PID: 2552)
Executable content was dropped or overwritten
- openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe (PID: 3504)
- openvpn-postinstall.exe (PID: 2552)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| ProductVersion: | 1.6.0.2712 |
|---|---|
| ProductName: | 7-Zip SFX |
| PrivateBuild: | December 30, 2012 |
| OriginalFileName: | 7ZSfxMod_x86.exe |
| LegalCopyright: | Copyright © 2005-2012 Oleg N. Scherbakov |
| InternalName: | 7ZSfxMod |
| FileVersion: | 1.6.0.2712 |
| FileDescription: | 7z Setup SFX (x86) |
| CompanyName: | Oleg N. Scherbakov |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | Private build |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.6.0.2712 |
| FileVersionNumber: | 1.6.0.2712 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1942f |
| UninitializedDataSize: | - |
| InitializedDataSize: | 23552 |
| CodeSize: | 101888 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2012:12:31 01:38:51+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Dec-2012 00:38:51 |
| Detected languages: |
|
| CompanyName: | Oleg N. Scherbakov |
| FileDescription: | 7z Setup SFX (x86) |
| FileVersion: | 1.6.0.2712 |
| InternalName: | 7ZSfxMod |
| LegalCopyright: | Copyright © 2005-2012 Oleg N. Scherbakov |
| OriginalFilename: | 7ZSfxMod_x86.exe |
| PrivateBuild: | December 30, 2012 |
| ProductName: | 7-Zip SFX |
| ProductVersion: | 1.6.0.2712 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 31-Dec-2012 00:38:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00018DDE | 0x00018E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67402 |
.rdata | 0x0001A000 | 0x00003BCA | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.71339 |
.data | 0x0001E000 | 0x00004DEC | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.45098 |
.rsrc | 0x00023000 | 0x00001500 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.97891 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.23138 | 838 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.60602 | 744 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 2.63074 | 488 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 2.3817 | 296 | Latin 1 / Western European | Russian - Russia | RT_ICON |
101 | 2.73443 | 62 | Latin 1 / Western European | Russian - Russia | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\openvpn-postinstall.exe" | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\openvpn-postinstall.exe | — | openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2552 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\openvpn-postinstall.exe" | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\openvpn-postinstall.exe | openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3504 | "C:\Users\admin\AppData\Local\Temp\openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe" | C:\Users\admin\AppData\Local\Temp\openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | Explorer.EXE | ||||||||||||
User: admin Company: Oleg N. Scherbakov Integrity Level: MEDIUM Description: 7z Setup SFX (x86) Exit code: 0 Version: 1.6.0.2712 Modules
| |||||||||||||||
Total events
1 487
Read events
1 479
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3504) openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3504) openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3504) openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3504) openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
4
Suspicious files
0
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\config\cerbero-UDP4-12012-OVPN_ICO-config.ovpn | text | |
MD5:— | SHA256:— | |||
| 3504 | openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\config\cerbero-UDP4-12012-OVPN_ICO.p12 | der | |
MD5:— | SHA256:— | |||
| 2552 | openvpn-postinstall.exe | C:\Users\admin\AppData\Local\Temp\nsq5CA6.tmp\nsDialogs.dll | executable | |
MD5:65373B20DBFF5C3834548DD7330BB0C1 | SHA256:57A001C9770C864F983AA33E4C81E60CAC4335B83DC036E269F0727A629DD221 | |||
| 3504 | openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\config\cerbero-UDP4-12012-OVPN_ICO-tls.key | text | |
MD5:1F70AD600752D6E264B9EC69831FBA7C | SHA256:4AD4D58B9C8947A06D095744165091FD6B13F8EF2D44F97ED08990AD2D671E6B | |||
| 2552 | openvpn-postinstall.exe | C:\Users\admin\AppData\Local\Temp\nsq5CA6.tmp\System.dll | executable | |
MD5:2E025E2CEE2953CCE0160C3CD2E1A64E | SHA256:D821A62802900B068DCF61DDC9FDFF2F7ADA04B706815AB6E5038B21543DA8A5 | |||
| 2552 | openvpn-postinstall.exe | C:\Users\admin\AppData\Local\Temp\nsq5CA6.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3504 | openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\openvpn-install.exe | executable | |
MD5:B04C1B28BAAC54B415CB88635B4DC815 | SHA256:0237BE0BE0156F869F38FB2F38842E3AB5DF46C79B914EBA580DE3031C116651 | |||
| 3504 | openvpn-cerbero-UDP4-12012-OVPN_ICO-install-2.4.7-I603.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\openvpn-postinstall.exe | executable | |
MD5:DDB1035FB1AB9AEF3C36F465E5103F86 | SHA256:120D5F1A791671B563E7344593B8ACAC265AF3332748971BB8AB3261096D9ABA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report