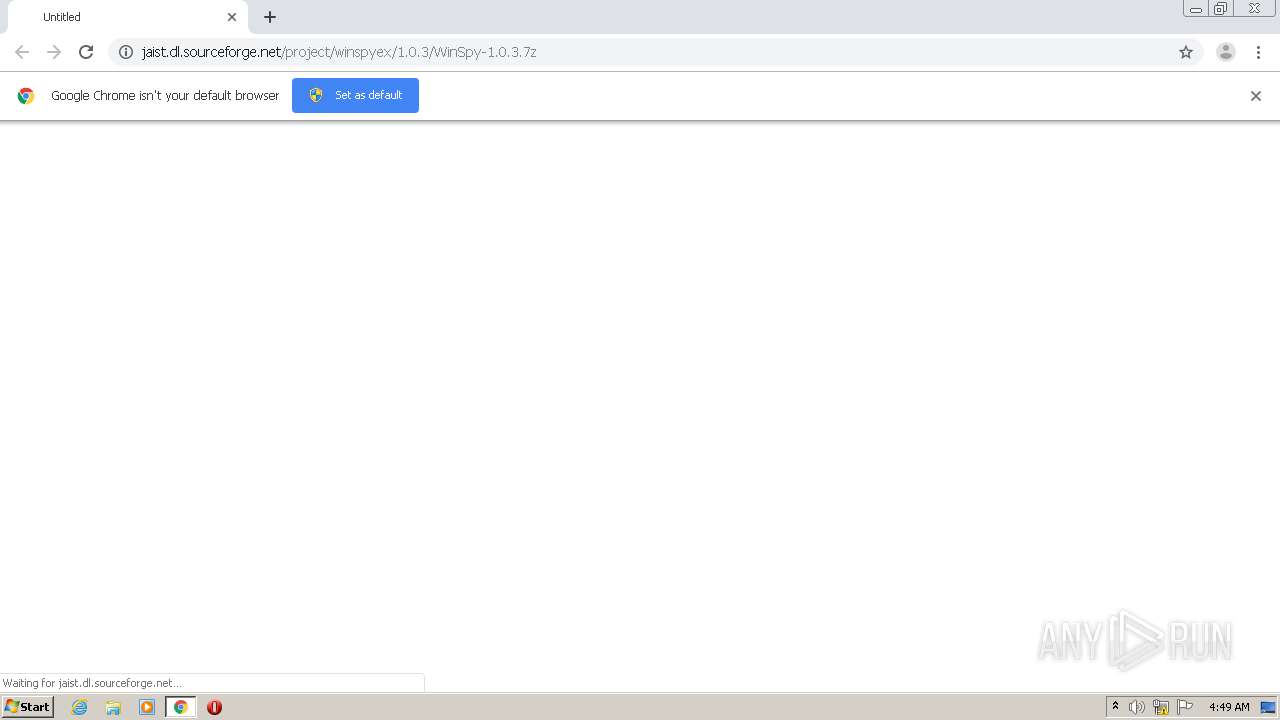
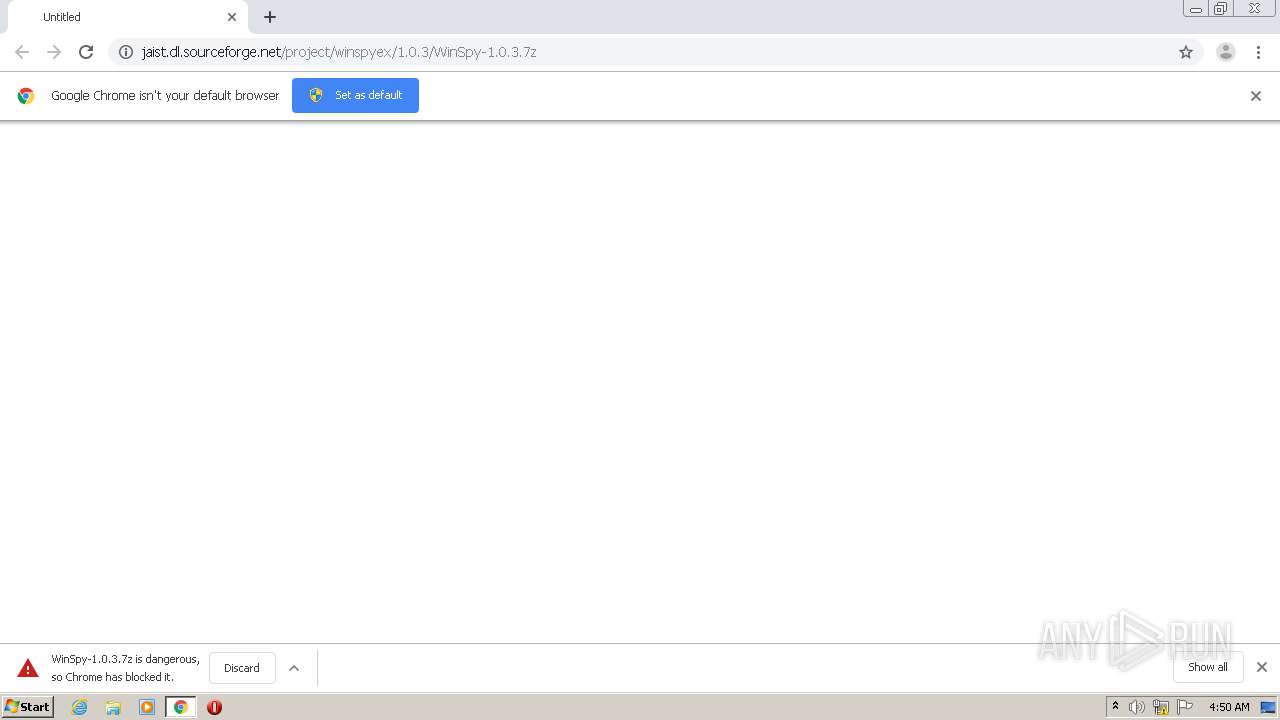
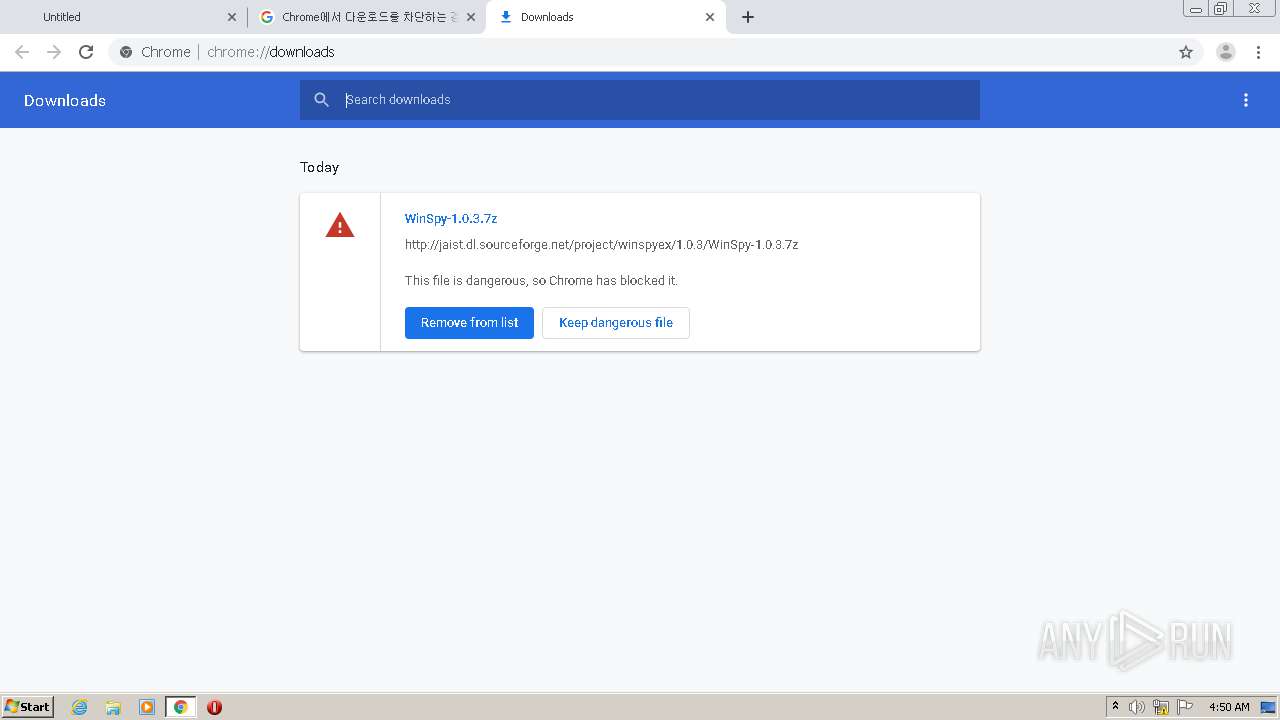
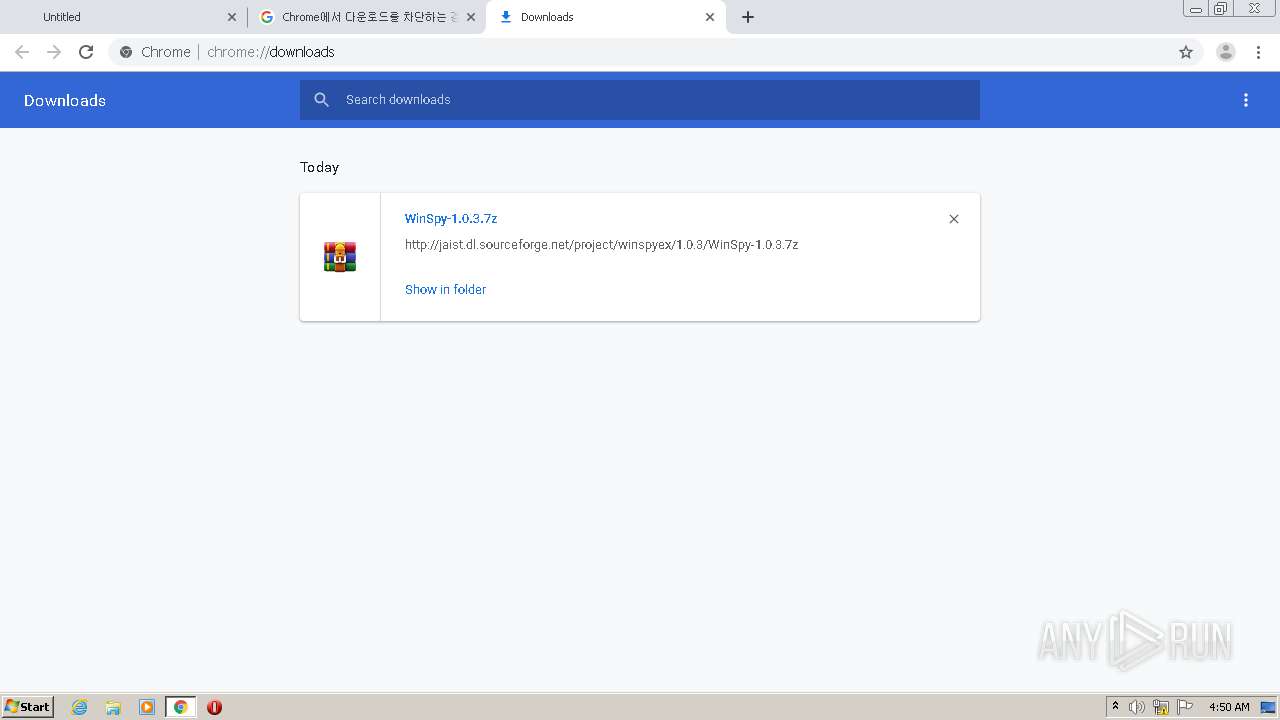
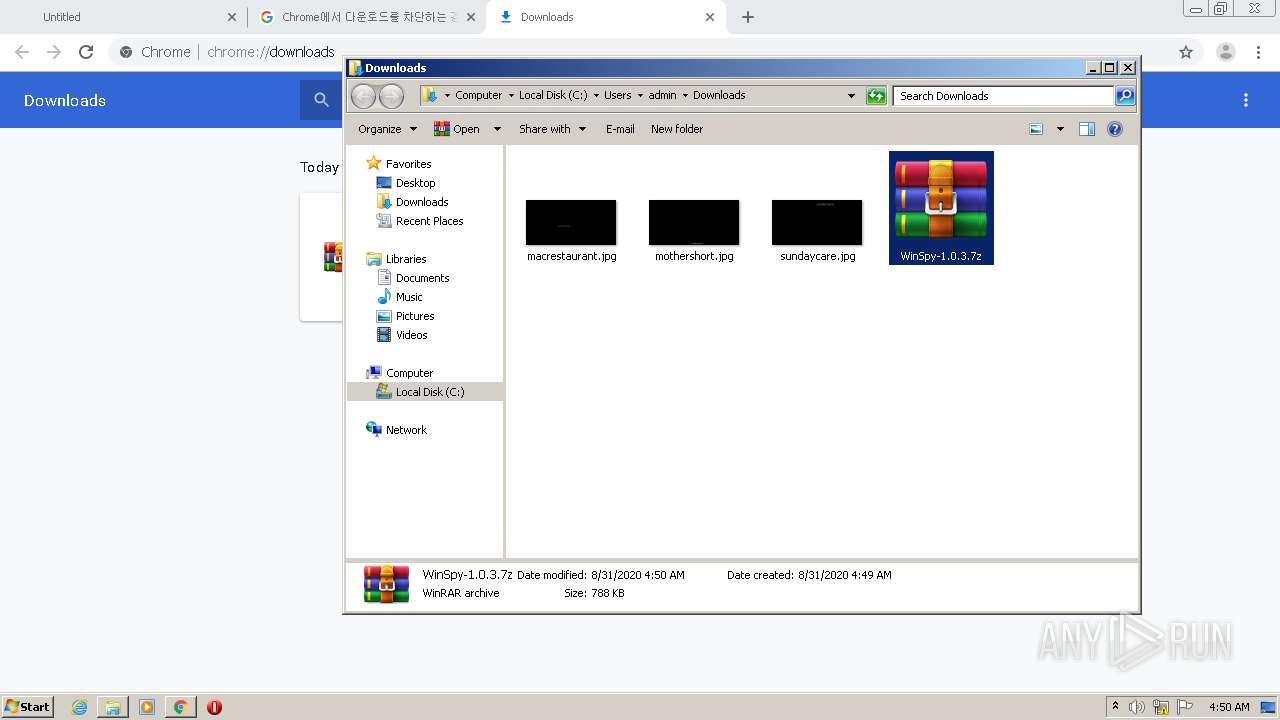
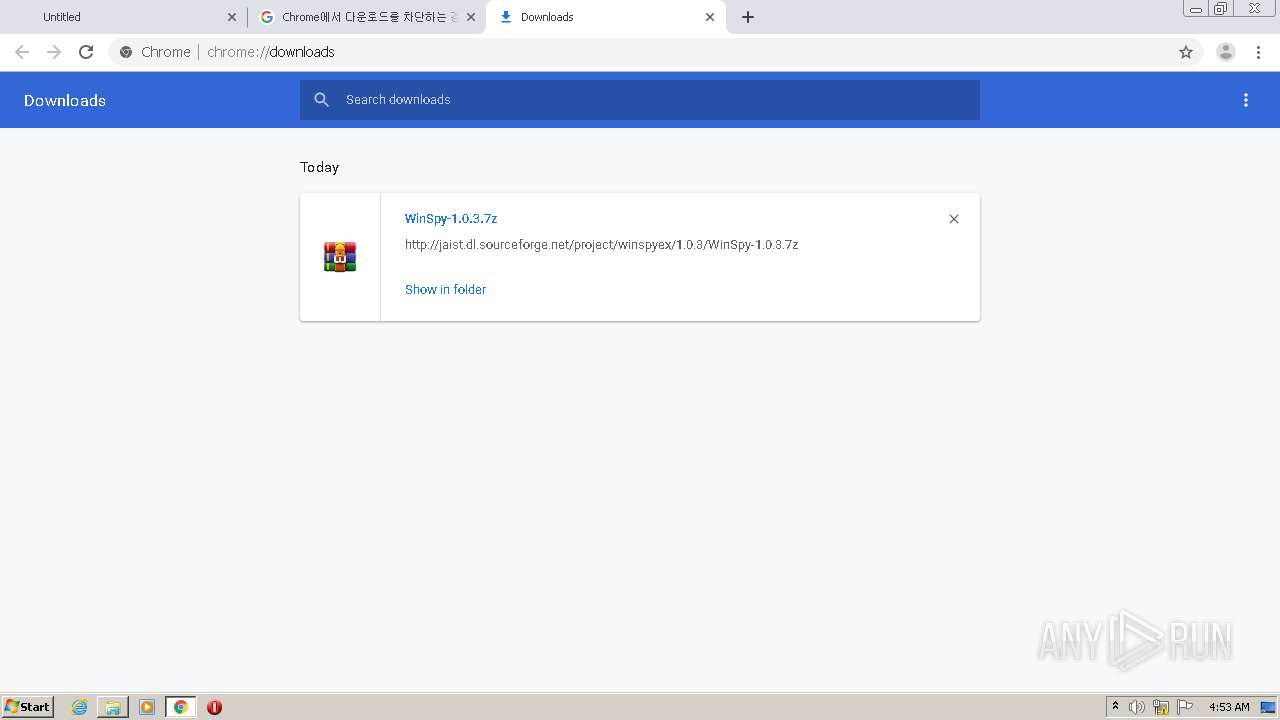
| URL: | http://jaist.dl.sourceforge.net/project/winspyex/1.0.3/WinSpy-1.0.3.7z |
| Full analysis: | https://app.any.run/tasks/6fa9a4f7-15b4-49ca-9d81-ad24a5c9a477 |
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2020, 03:49:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 36D7C501470D0B01020DA59344BD363A |
| SHA1: | 7CA7F309375A35A6135DDD78862CD7AA76AF19CF |
| SHA256: | 9CEA9E73C79BC81D7C2BE80F76DA7E6870C6D222A736EF455A07968552615BE3 |
| SSDEEP: | 3:N1KUMRXC2SuLAuUtZbj2KhMSf:CUMRXVnCtZbKKdf |
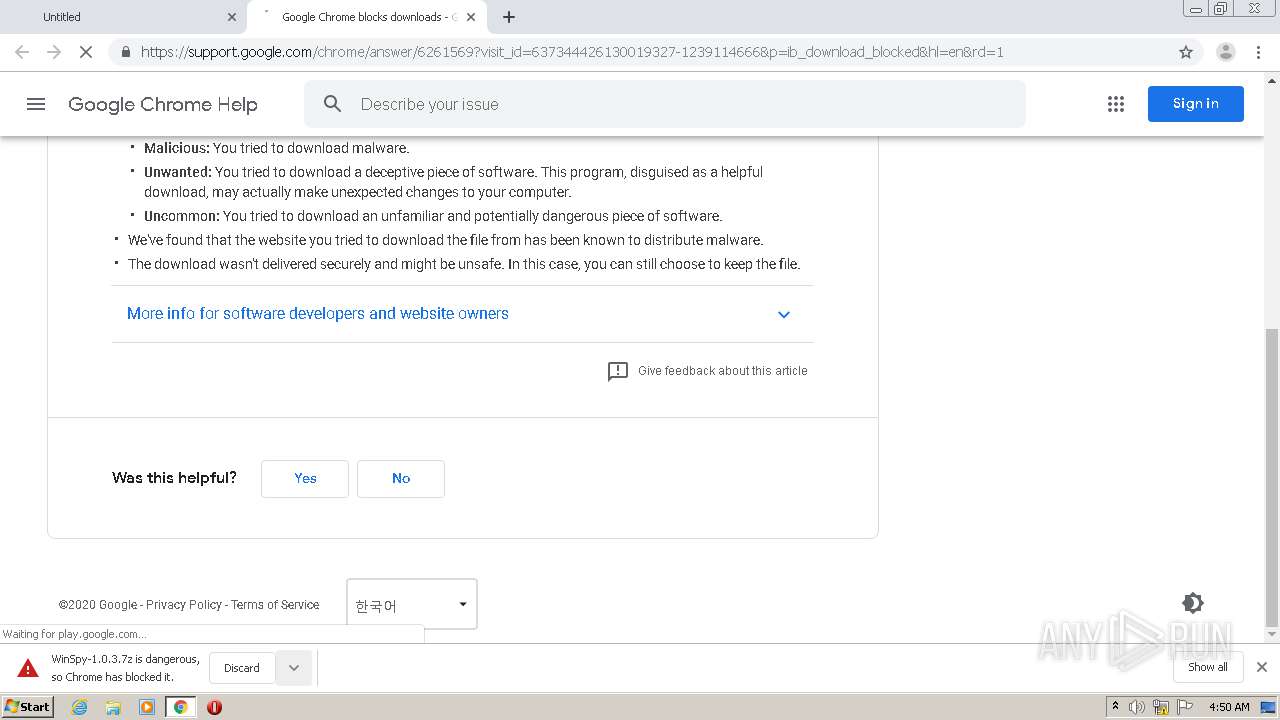
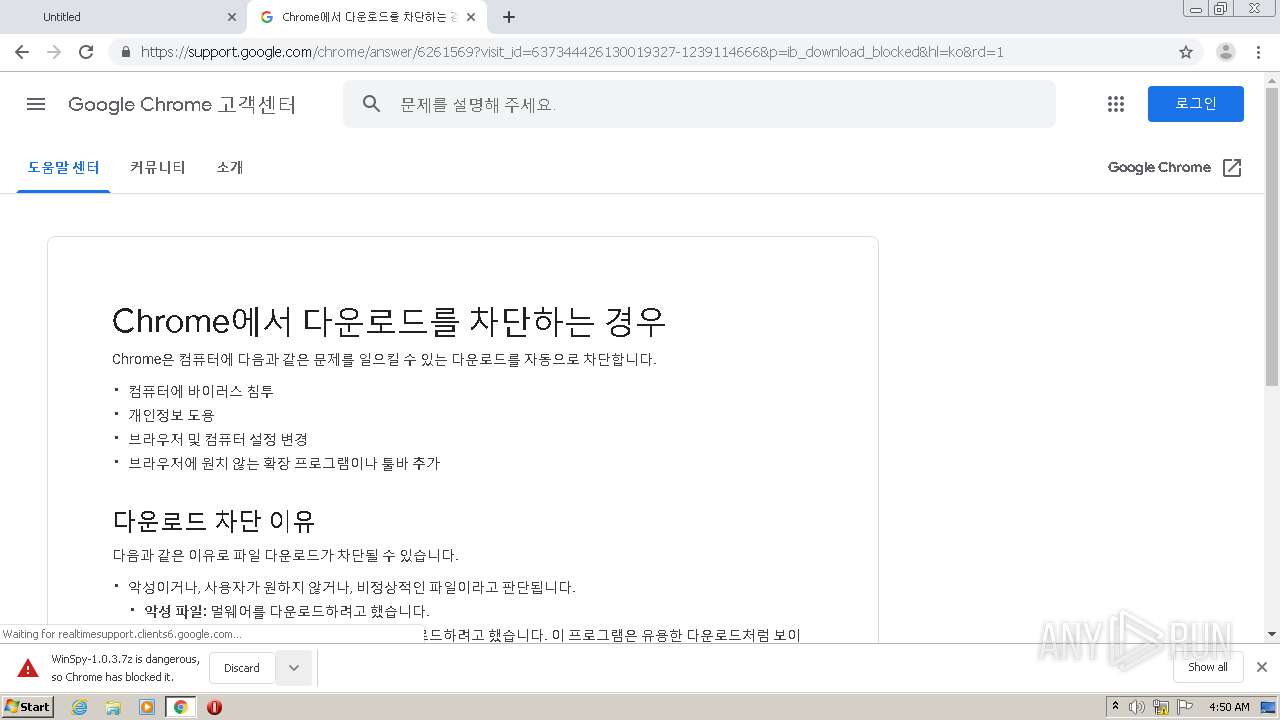
MALICIOUS
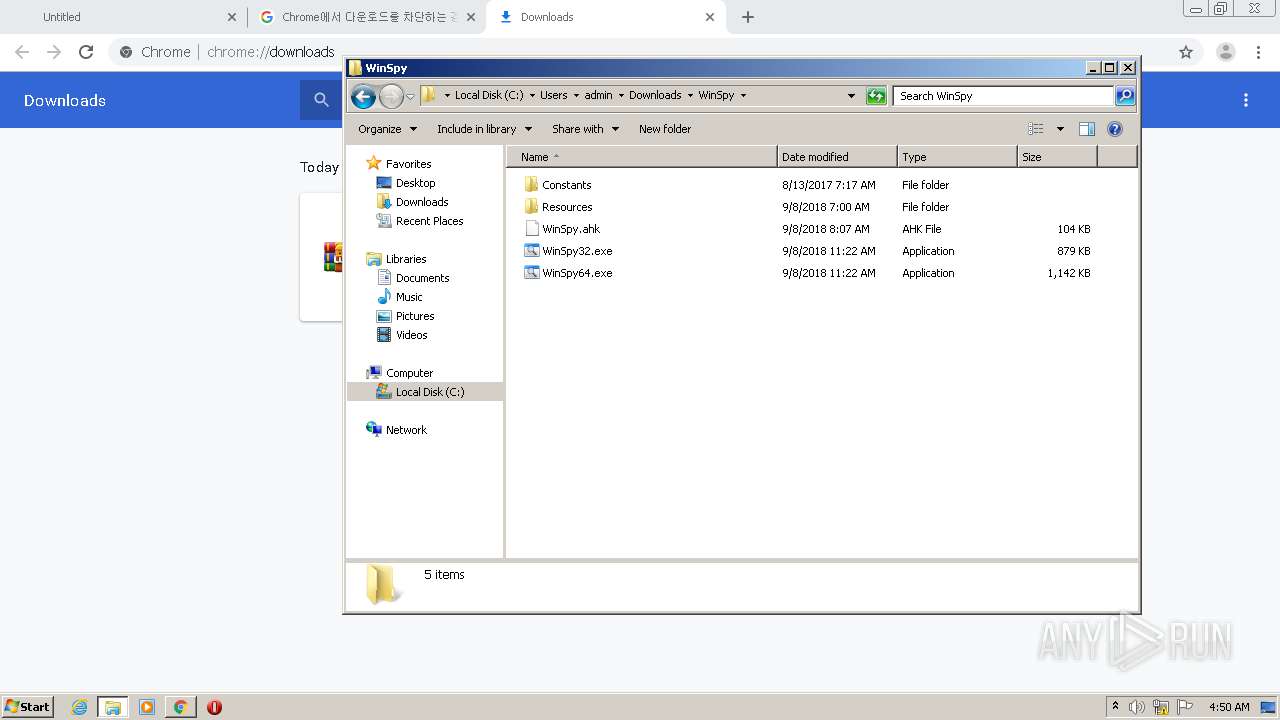
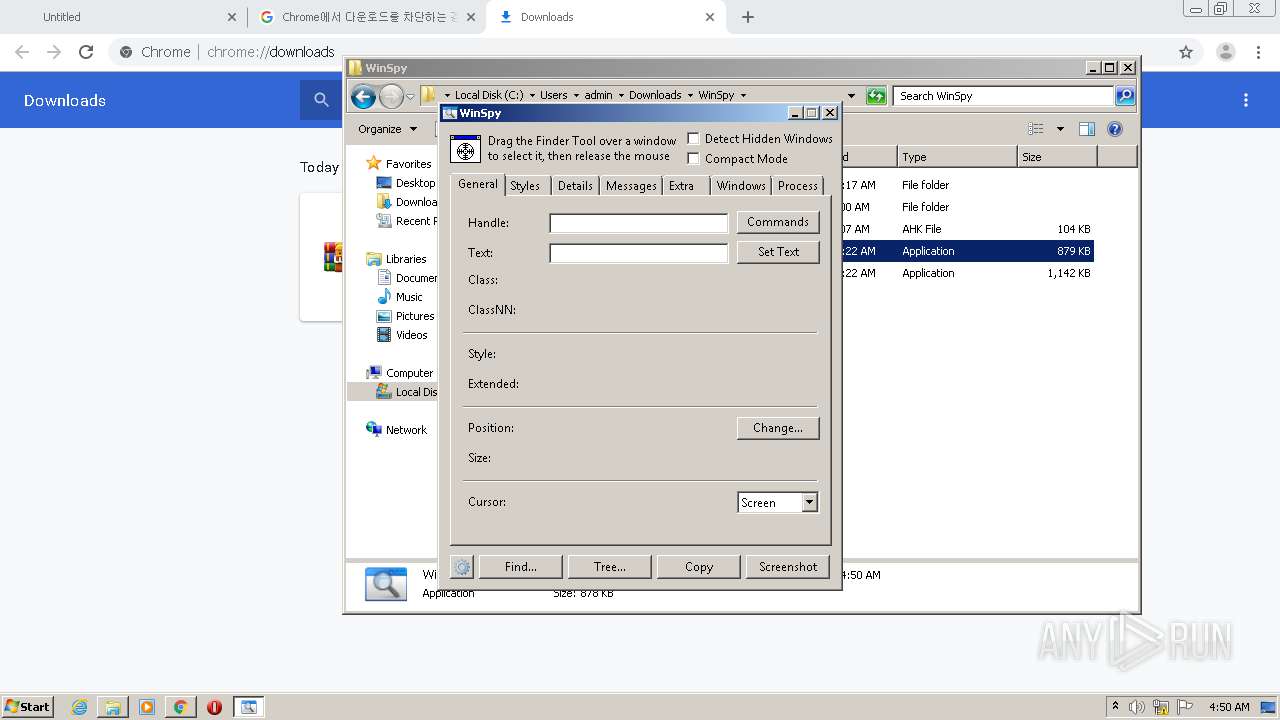
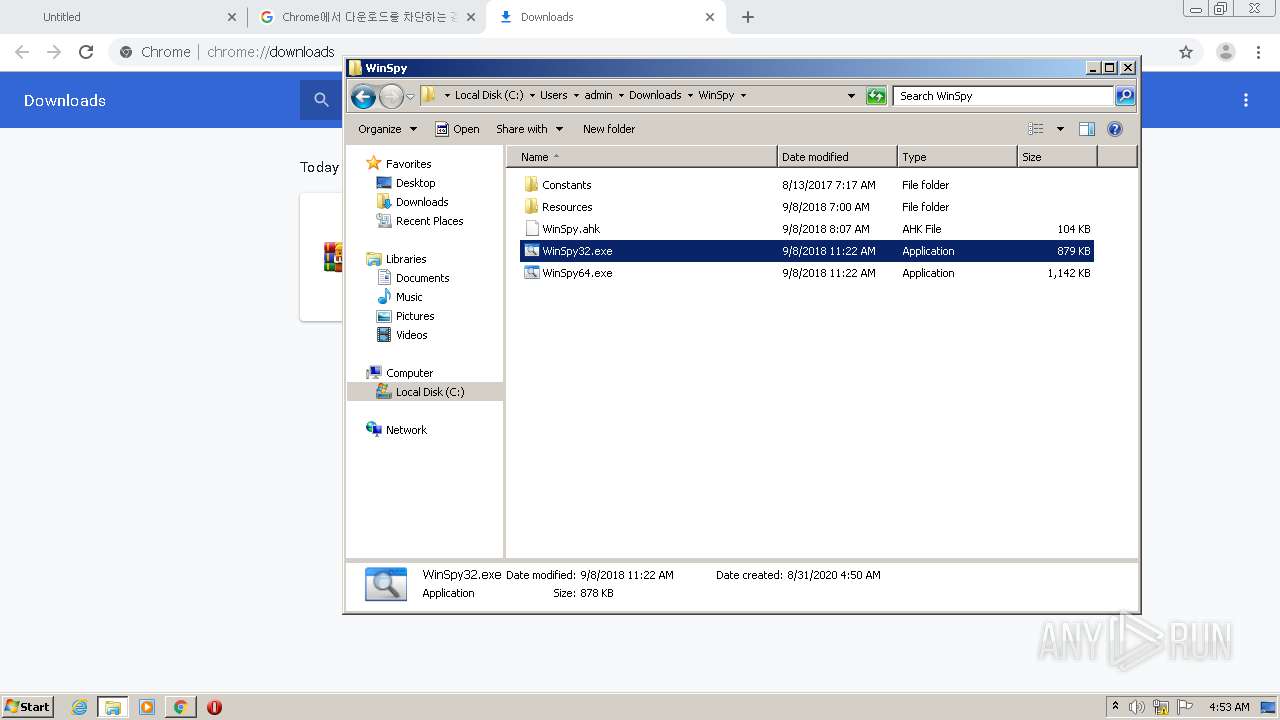
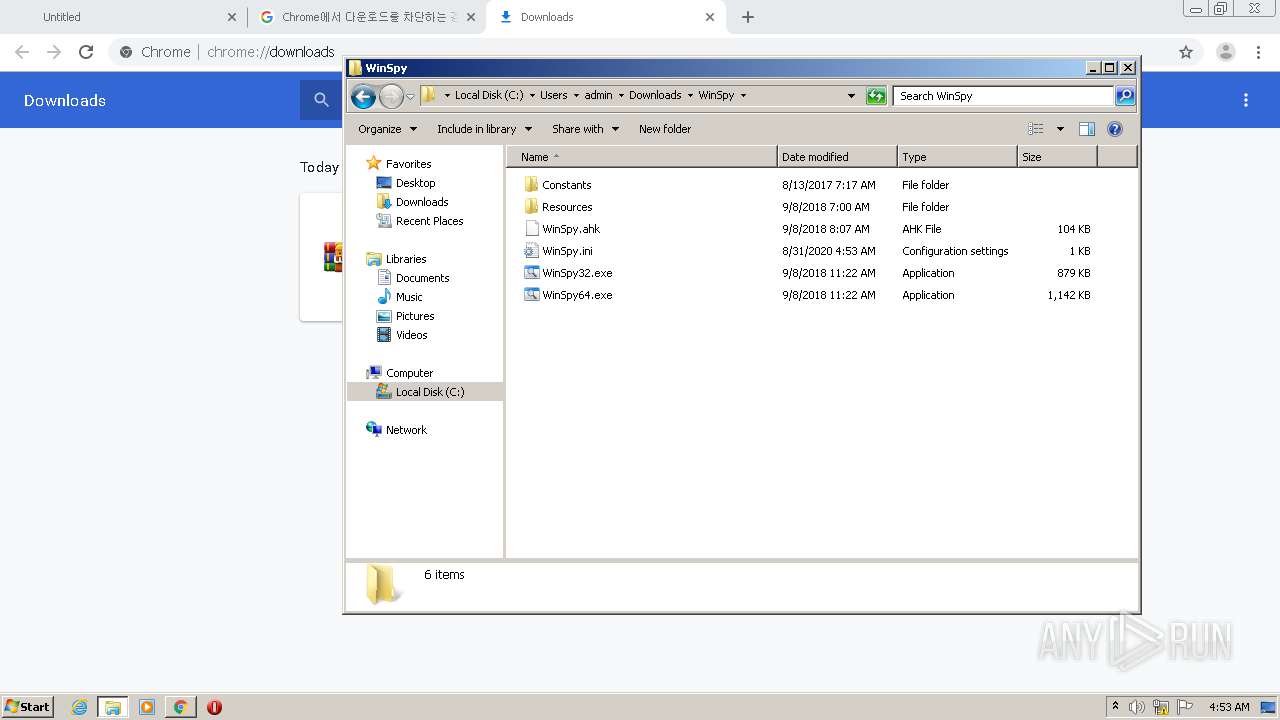
Application was dropped or rewritten from another process
- WinSpy32.exe (PID: 3576)
SUSPICIOUS
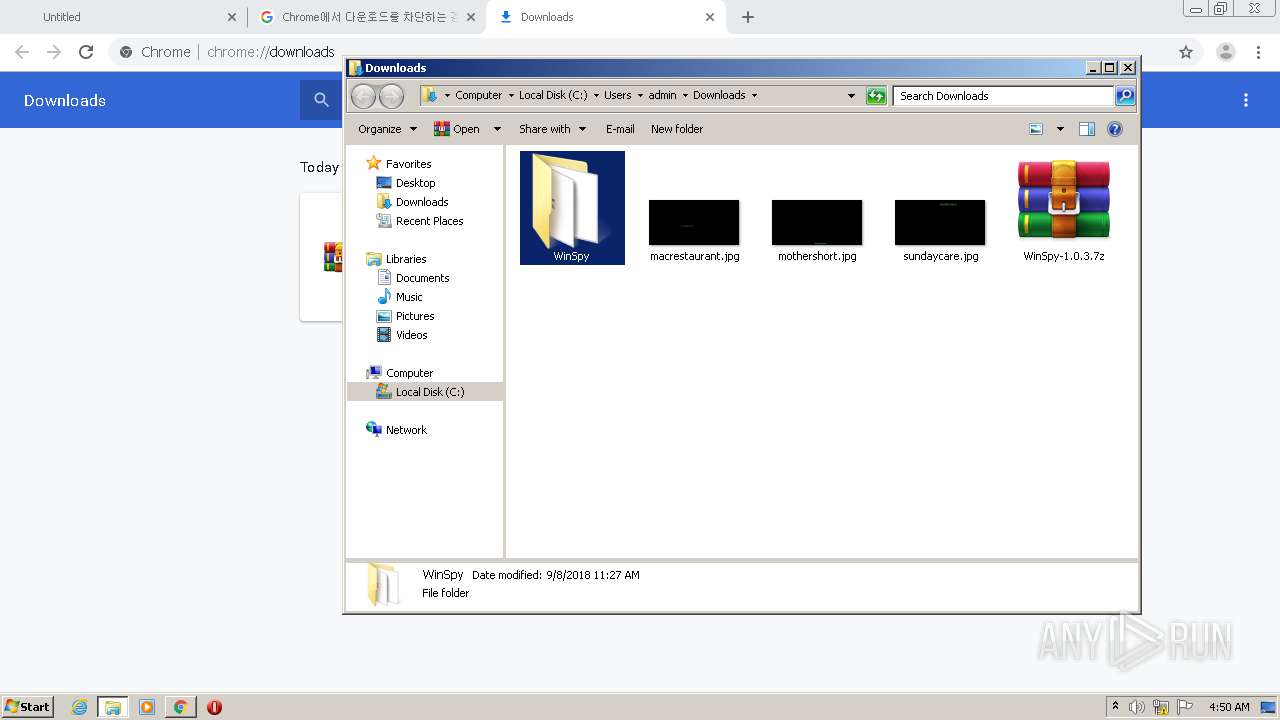
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1848)
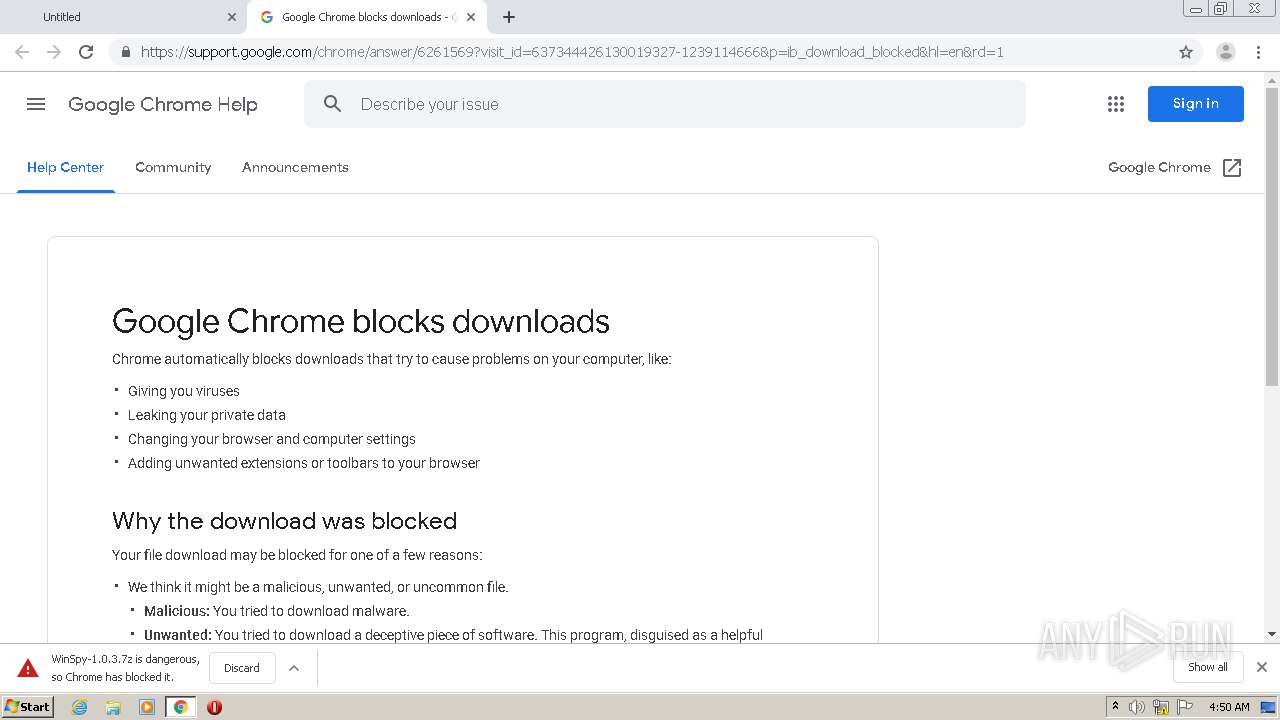
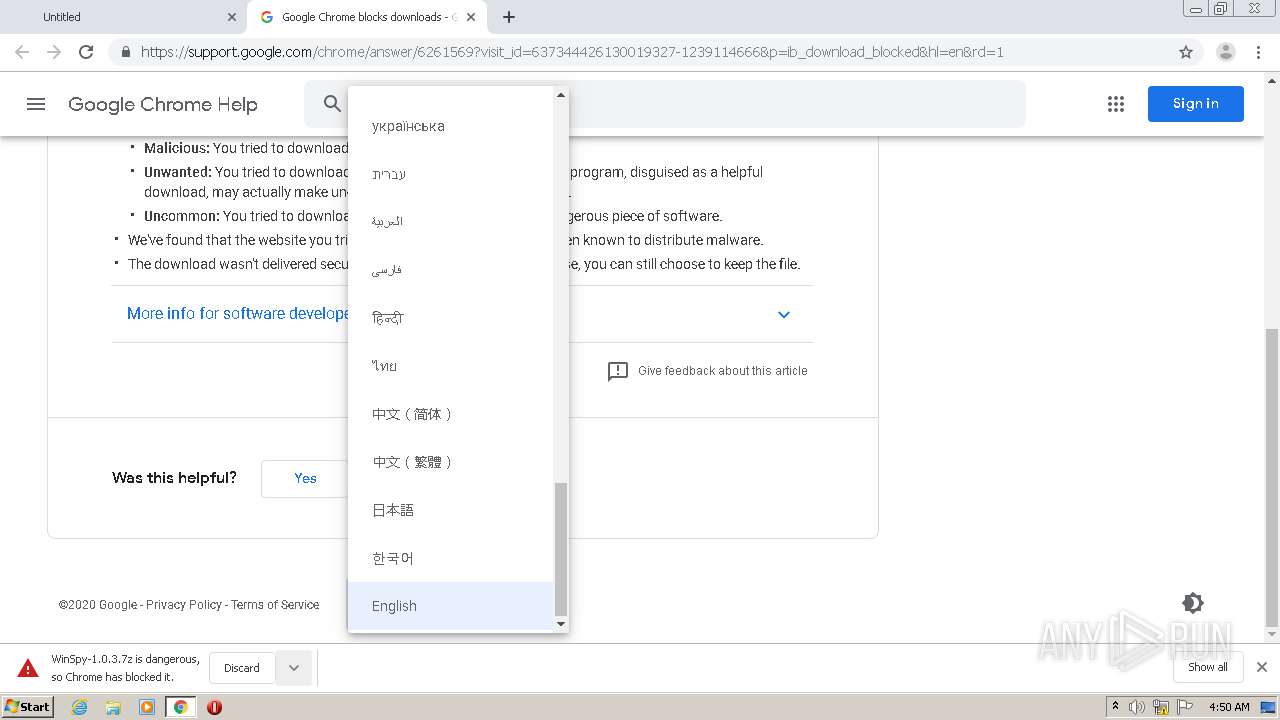
Checks supported languages
- WinSpy32.exe (PID: 3576)
INFO
Application launched itself
- chrome.exe (PID: 2212)
Reads the hosts file
- chrome.exe (PID: 2212)
- chrome.exe (PID: 2580)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 1848)
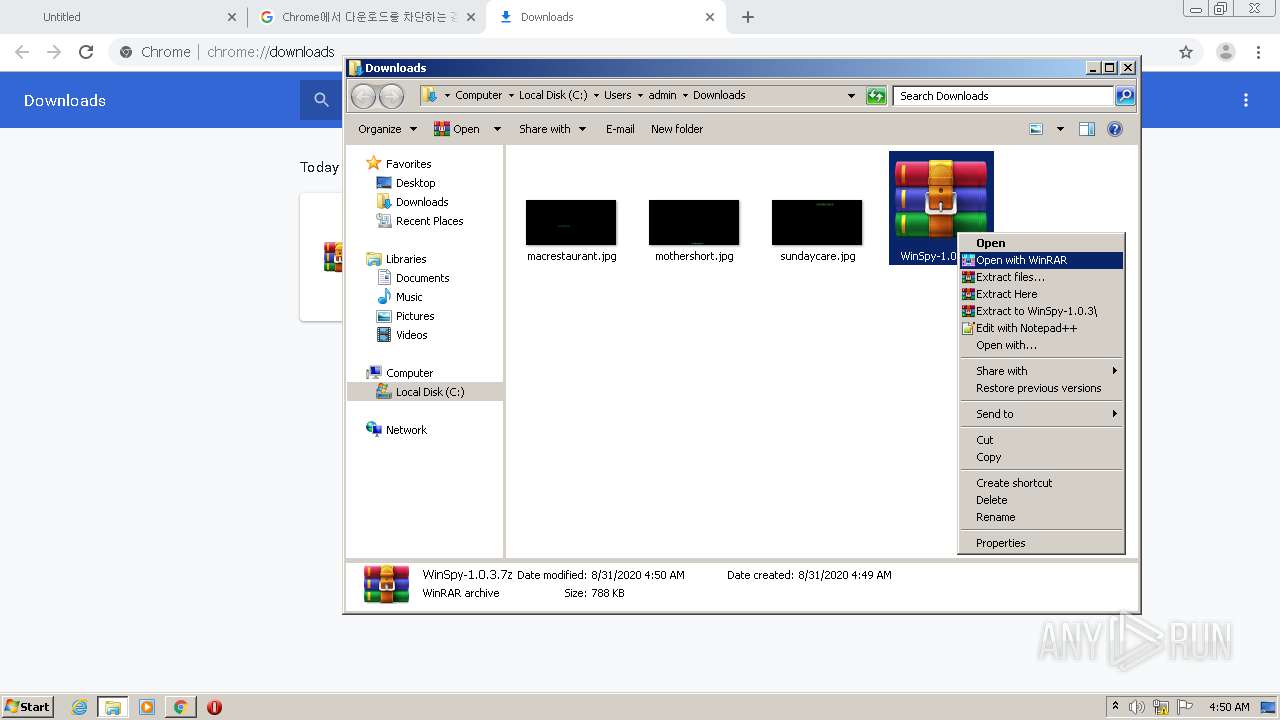
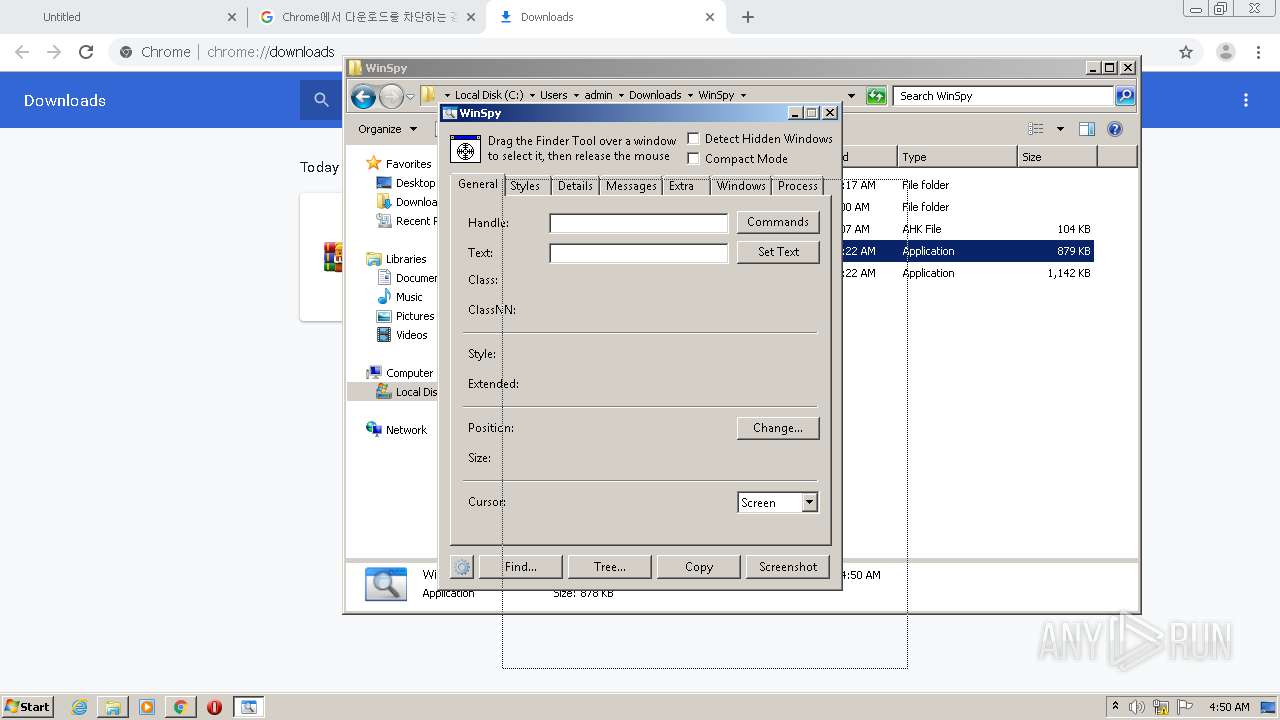
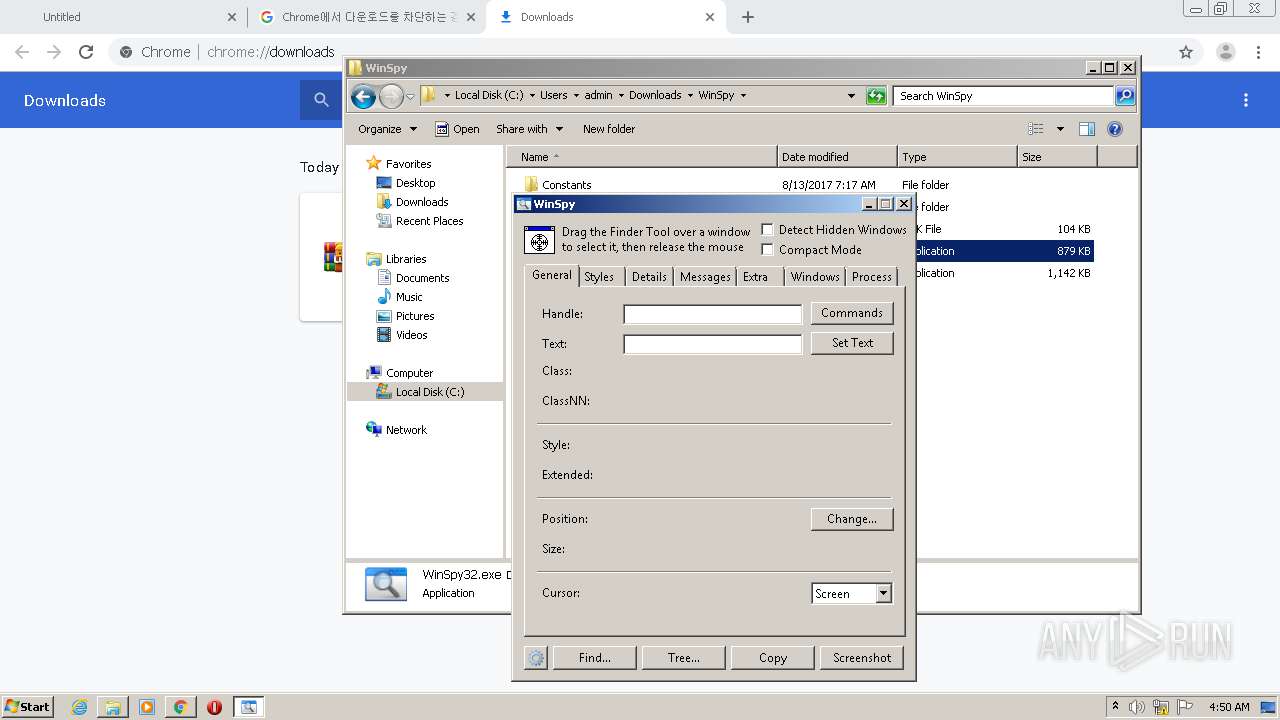
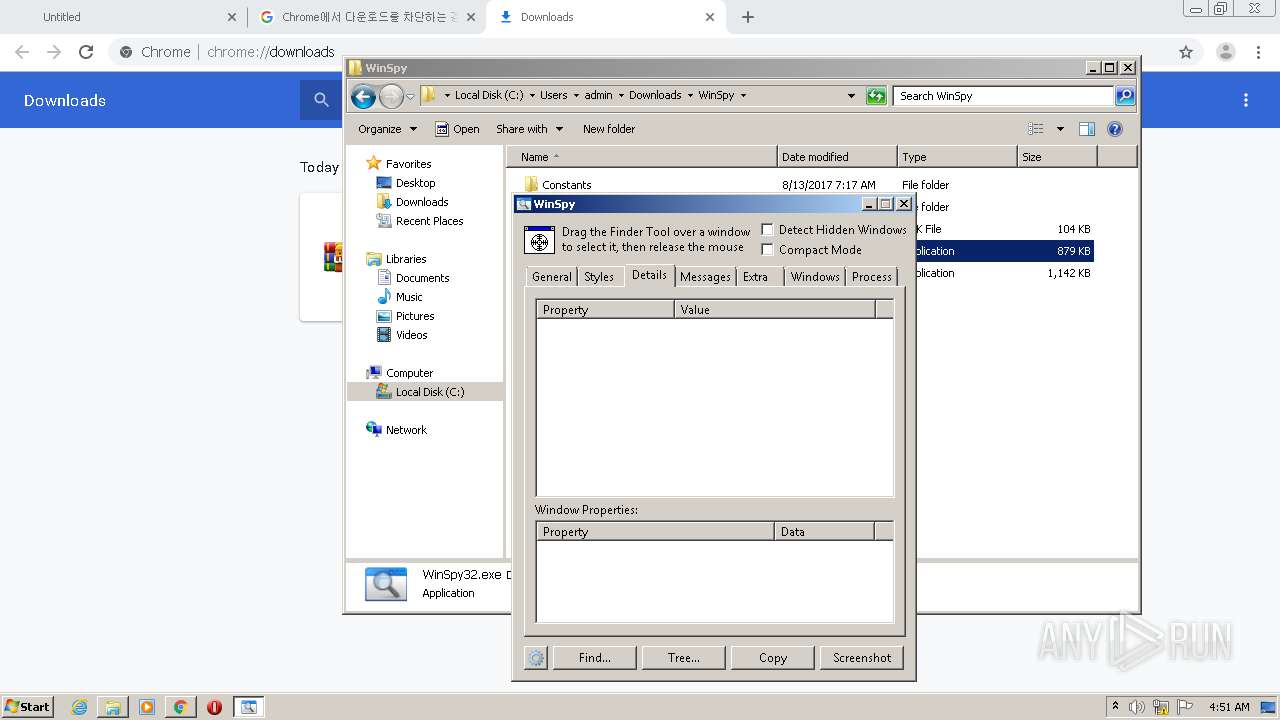
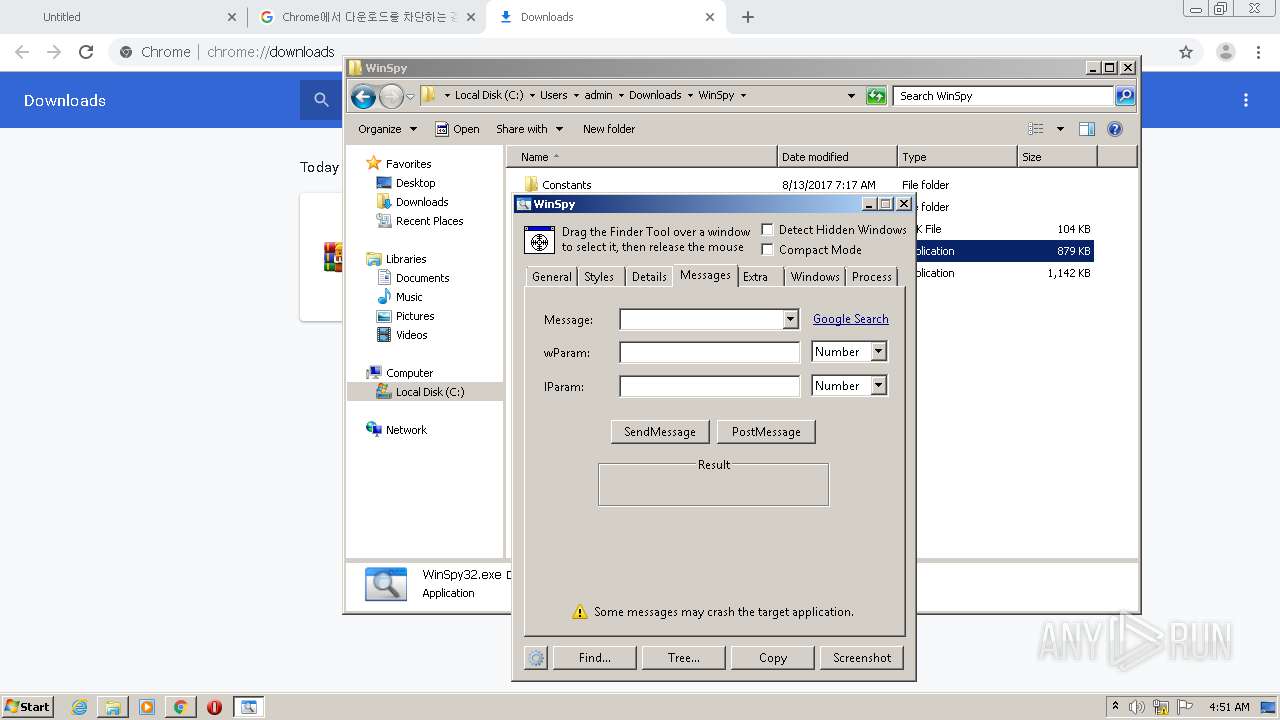
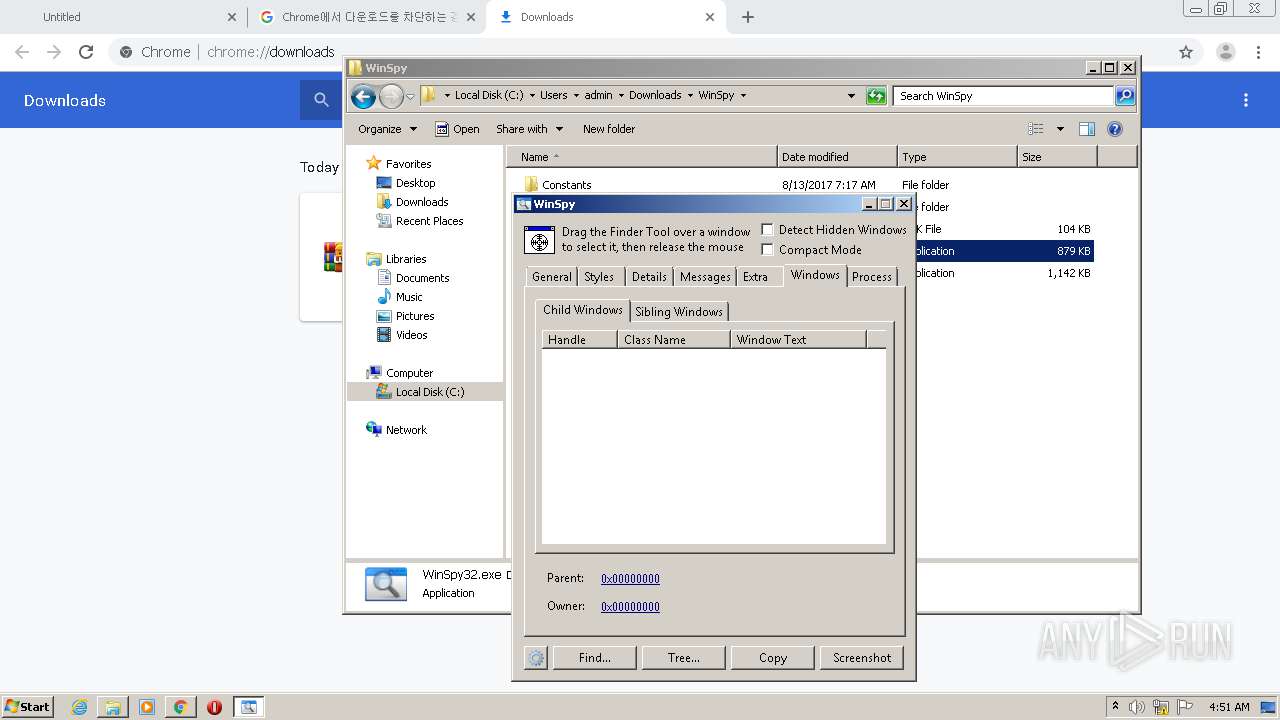
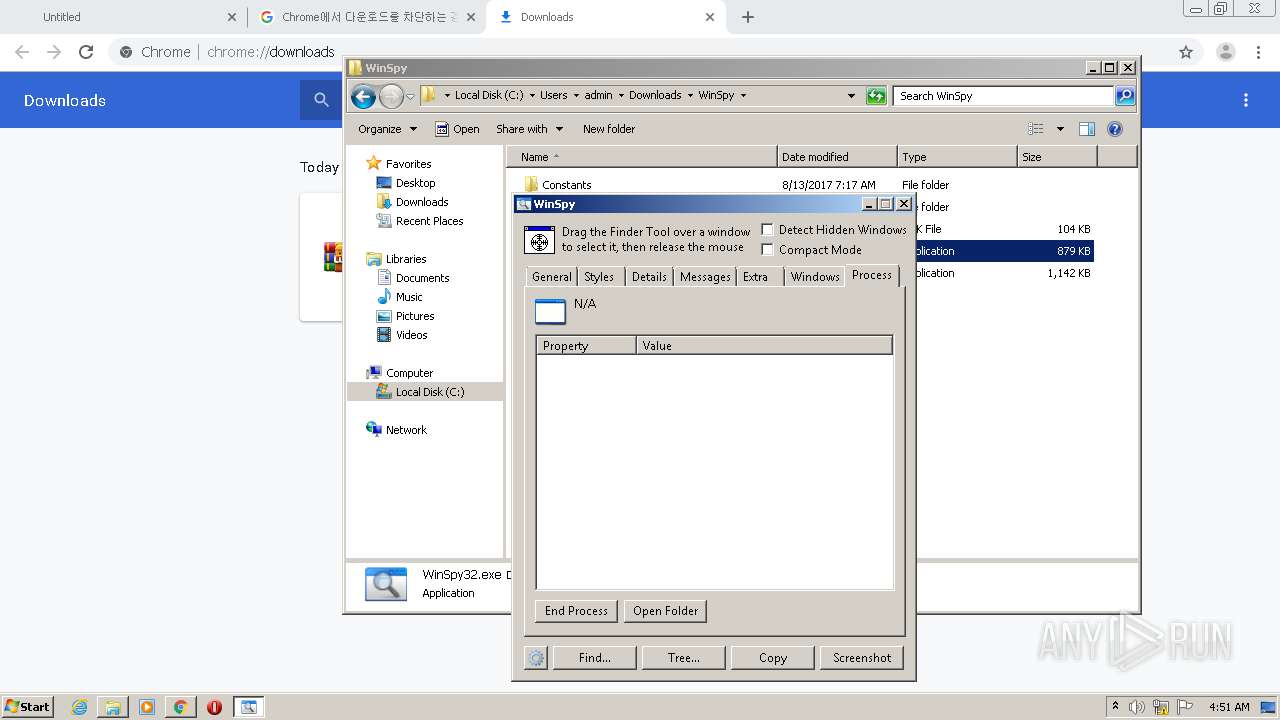
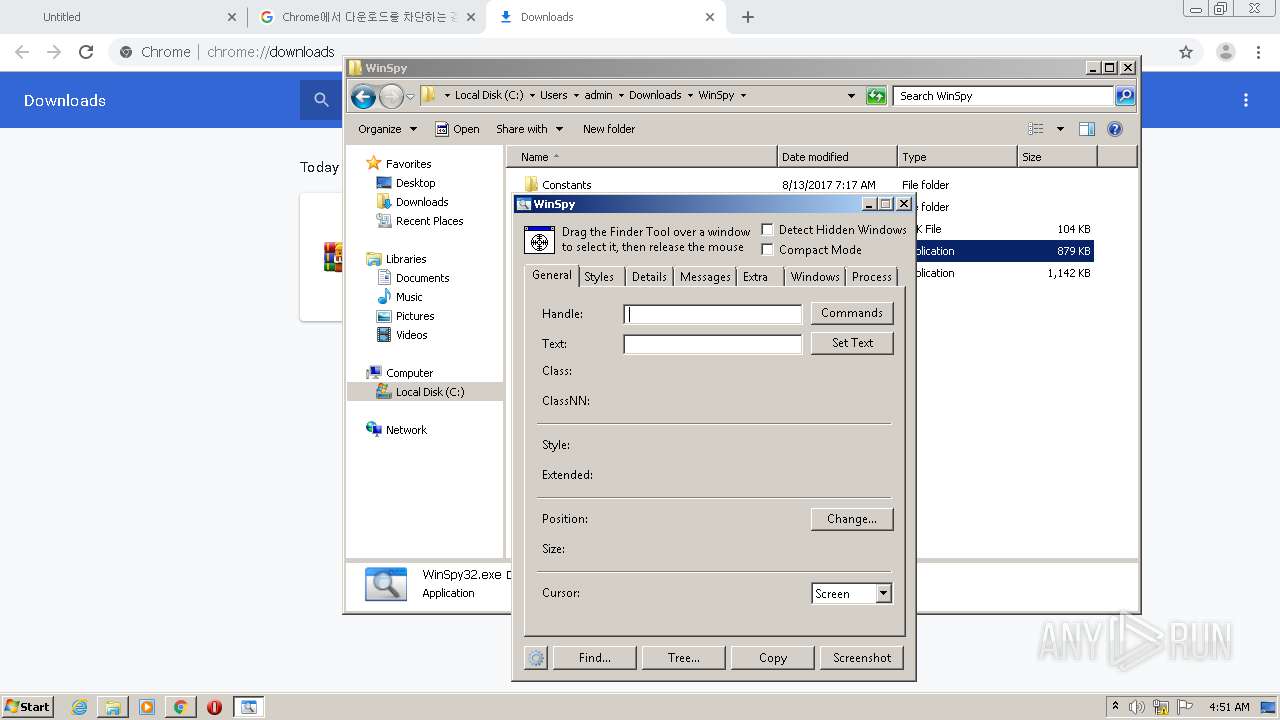
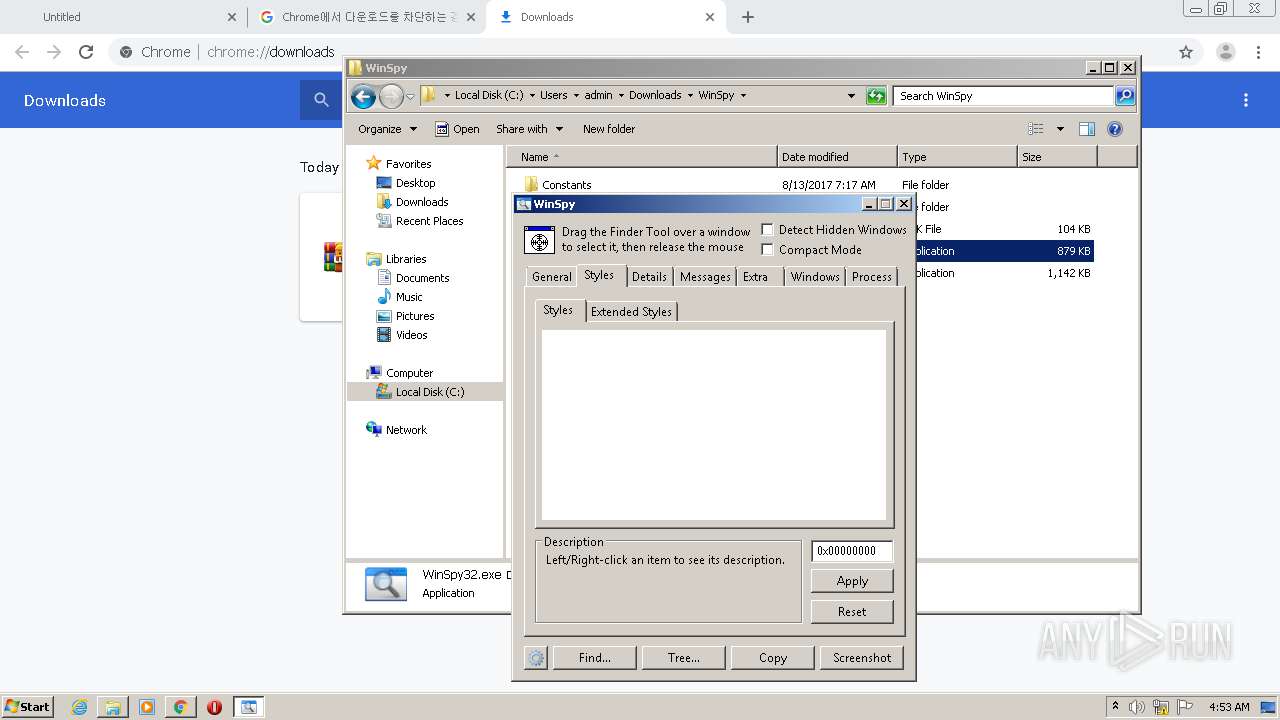
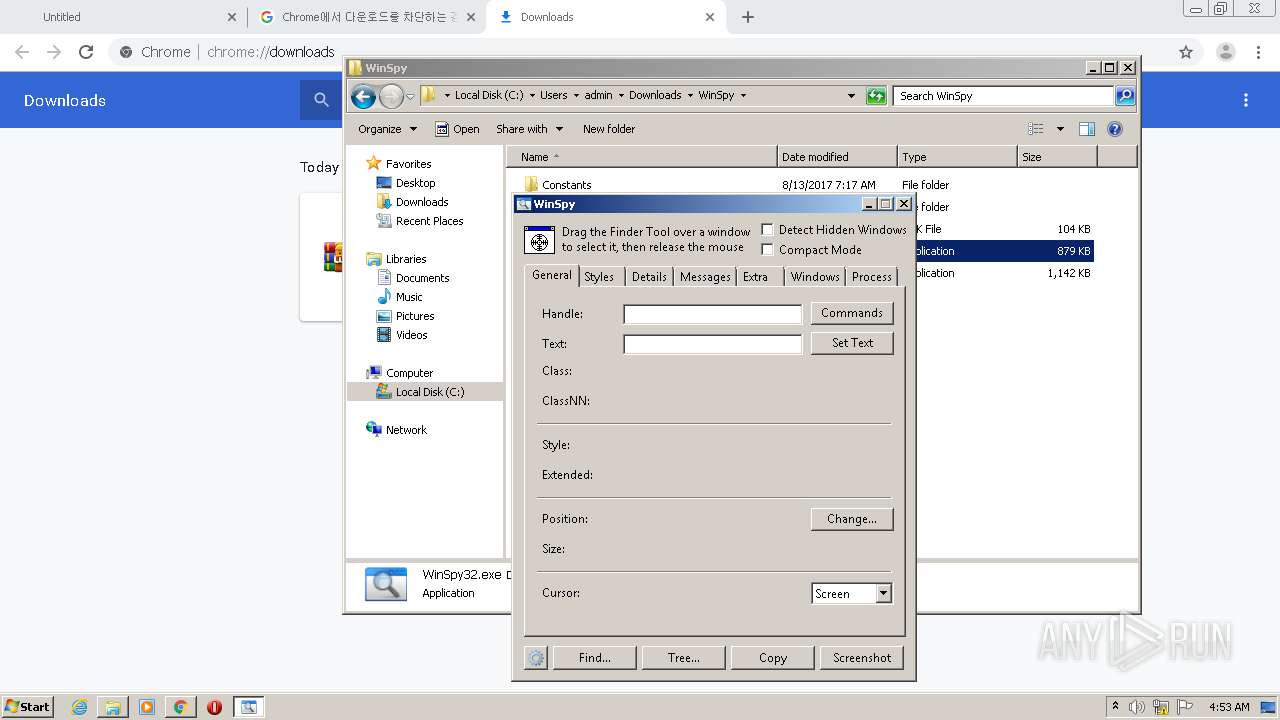
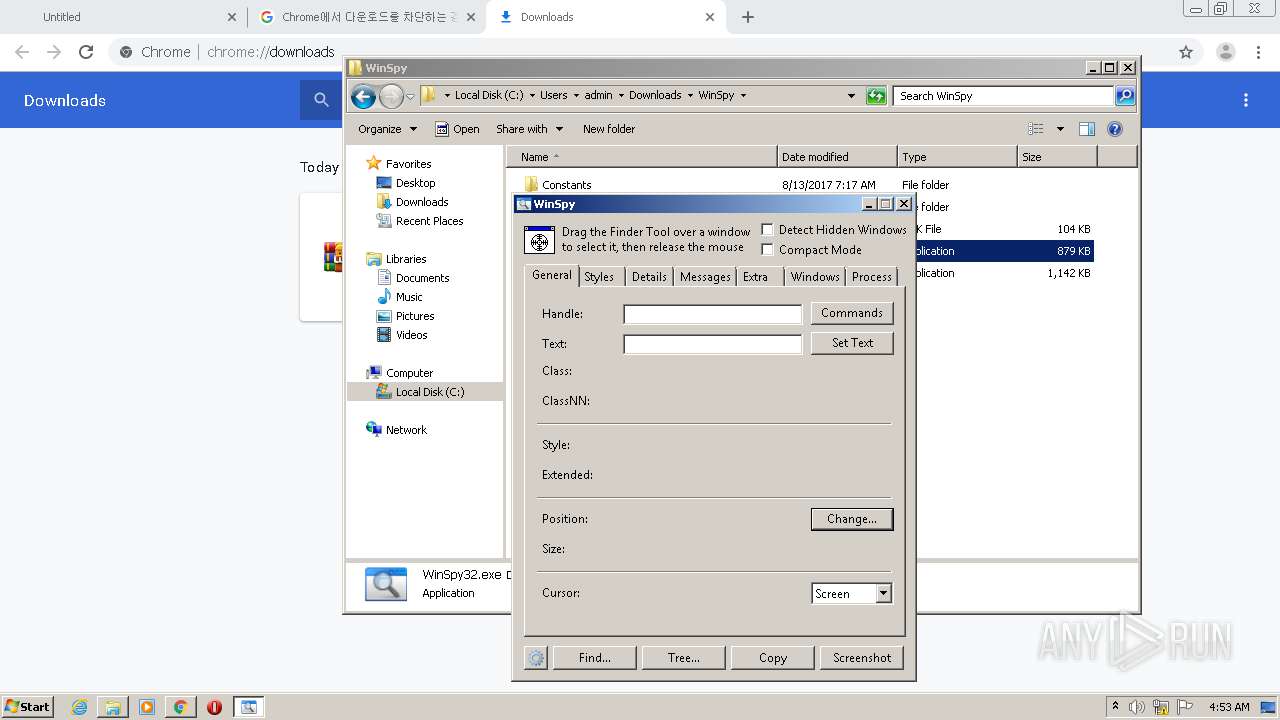
Manual execution by user
- WinSpy32.exe (PID: 3576)
- WinRAR.exe (PID: 1848)
Reads Internet Cache Settings
- chrome.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3314876267171976875,1942514326700158500,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10400628748307018250 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3314876267171976875,1942514326700158500,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10949969337121966847 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
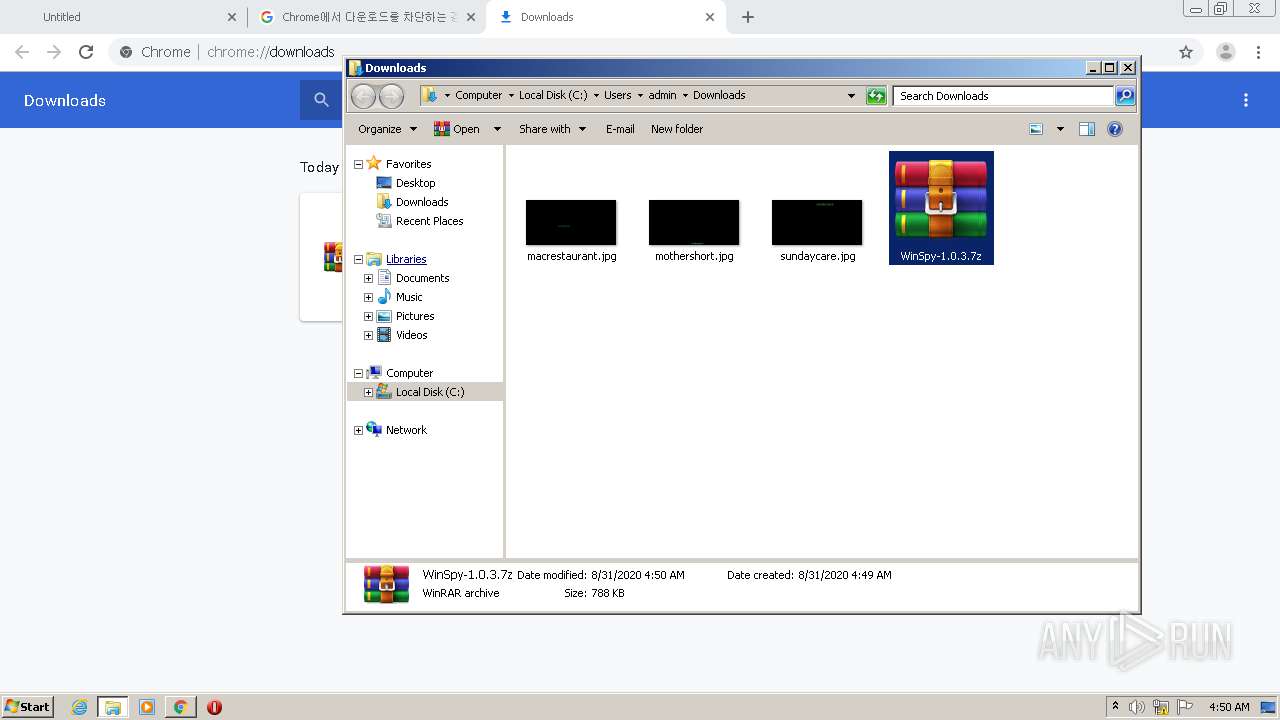
| 1848 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\WinSpy-1.0.3.7z" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3314876267171976875,1942514326700158500,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5527278622499494765 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,3314876267171976875,1942514326700158500,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3713459761782188604 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://jaist.dl.sourceforge.net/project/winspyex/1.0.3/WinSpy-1.0.3.7z" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3314876267171976875,1942514326700158500,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13488395838396052018 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3314876267171976875,1942514326700158500,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9475121486852004906 --mojo-platform-channel-handle=3600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3314876267171976875,1942514326700158500,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12262514255031045053 --mojo-platform-channel-handle=1628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3314876267171976875,1942514326700158500,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11132683107498566096 --mojo-platform-channel-handle=4088 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 032
Read events
936
Write events
92
Delete events
4
Modification events
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2212-13243319394608875 |
Value: 259 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
3
Suspicious files
57
Text files
106
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4ee5bbd3-e6b9-4a09-9598-27f231f4e3a2.tmp | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:D11C35B3D5258F594933332C11C6F0F2 | SHA256:DC2EB16E16FA3FB258AC31A481F817208CF0C917AF4224F2832588D3A64ADD05 | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:1B8E44CB8872BF26BC5219E37A700F8A | SHA256:FD3D4BC8A7D28A05D1321F1D175FB59FC2BCC3532B92274A50133C22F0A0480A | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF145ac1.TMP | text | |
MD5:D11C35B3D5258F594933332C11C6F0F2 | SHA256:DC2EB16E16FA3FB258AC31A481F817208CF0C917AF4224F2832588D3A64ADD05 | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF145cb5.TMP | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF145aa1.TMP | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
32
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2580 | chrome.exe | GET | 200 | 150.65.7.130:80 | http://jaist.dl.sourceforge.net/project/winspyex/1.0.3/WinSpy-1.0.3.7z | JP | compressed | 788 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | chrome.exe | 216.58.212.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 150.65.7.130:80 | jaist.dl.sourceforge.net | Japan Advanced Institute of Science and Technology | JP | suspicious |
2580 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 172.217.22.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 216.58.210.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 216.58.212.142:443 | support.google.com | Google Inc. | US | whitelisted |
— | — | 216.58.212.142:443 | support.google.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jaist.dl.sourceforge.net |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
support.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |