| File name: | CapturePlus_v3.0.0.0.exe |
| Full analysis: | https://app.any.run/tasks/5a664201-c9b7-448b-a058-7532699a6a86 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 04:50:26 |
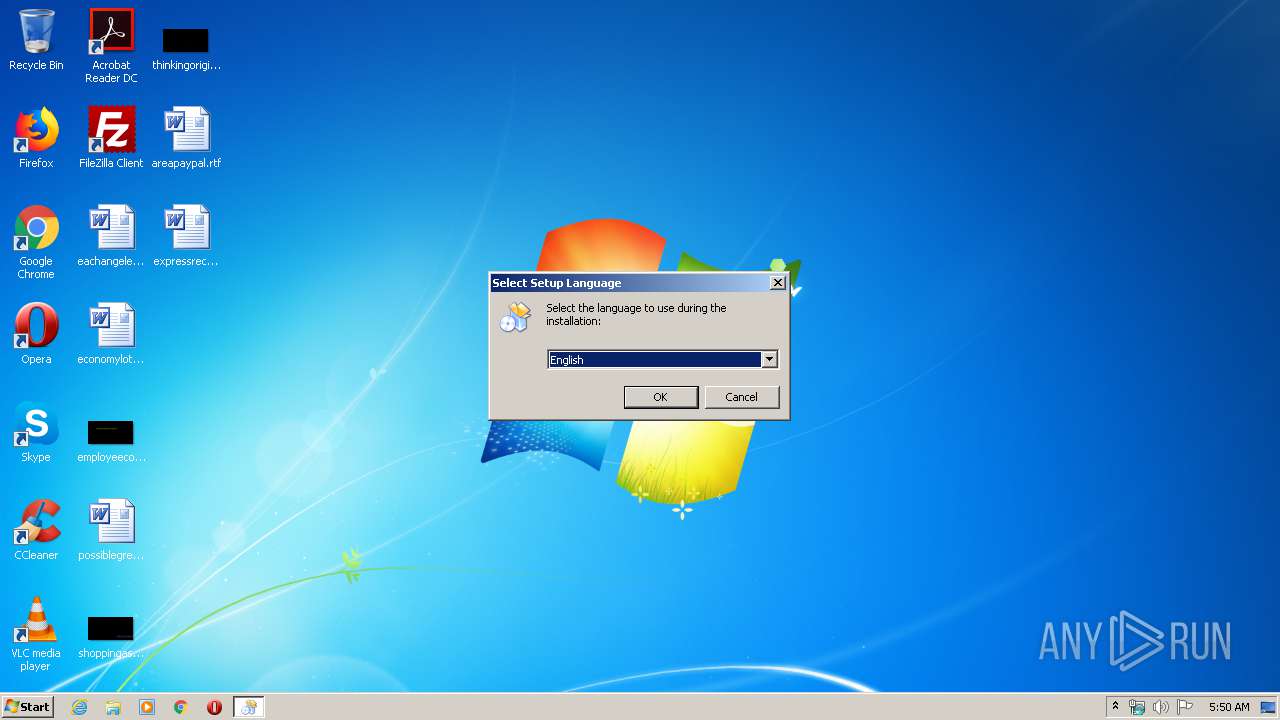
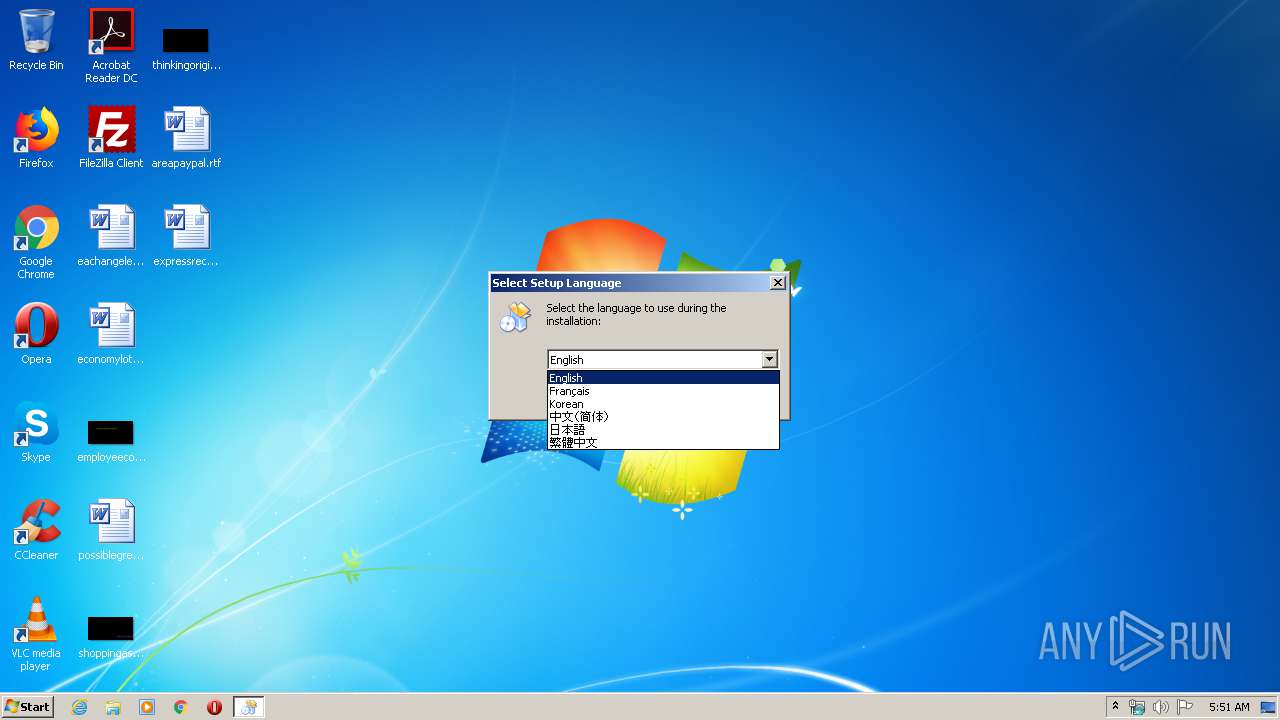
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C614FCE50829FC441F0D09F18AA82A51 |
| SHA1: | 7443E4975F457765992B4E83AA1A76783ABC789E |
| SHA256: | 9CE4AD239A47ADE3D3287C90584F8A102B2849658D7B642C4F013BECD3807A11 |
| SSDEEP: | 98304:4IjQiBlA3E1pLgnWpzJvY46EkE7Byot+ay2NDwAY41Q:+ijioRJA4627BhtYN/41Q |
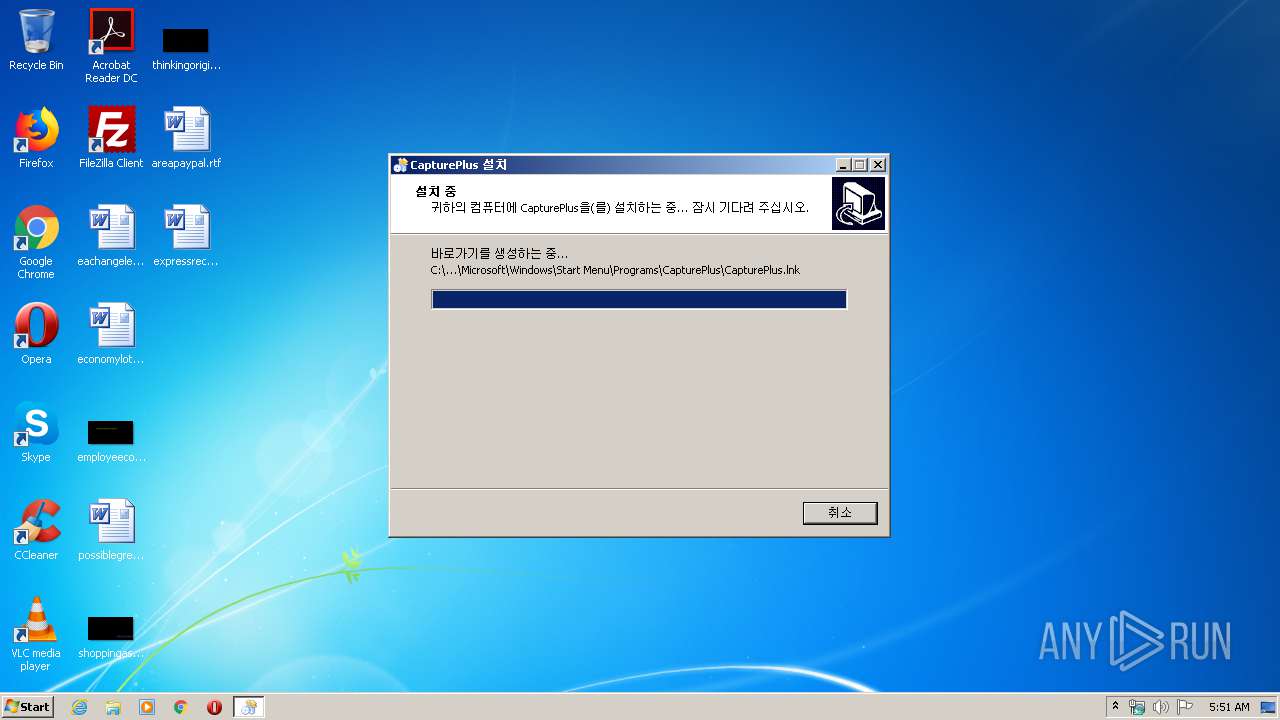
MALICIOUS
Loads dropped or rewritten executable
- CapturePlus.exe (PID: 1536)
- CapturePlus.exe (PID: 3408)
Application was dropped or rewritten from another process
- CapturePlus.exe (PID: 1536)
- CapturePlus.exe (PID: 3408)
SUSPICIOUS
Executable content was dropped or overwritten
- CapturePlus_v3.0.0.0.exe (PID: 3148)
- CapturePlus_v3.0.0.0.exe (PID: 1780)
- CapturePlus_v3.0.0.0.tmp (PID: 2696)
Creates files in the user directory
- CapturePlus_v3.0.0.0.tmp (PID: 2696)
Reads the Windows organization settings
- CapturePlus_v3.0.0.0.tmp (PID: 2696)
Reads Windows owner or organization settings
- CapturePlus_v3.0.0.0.tmp (PID: 2696)
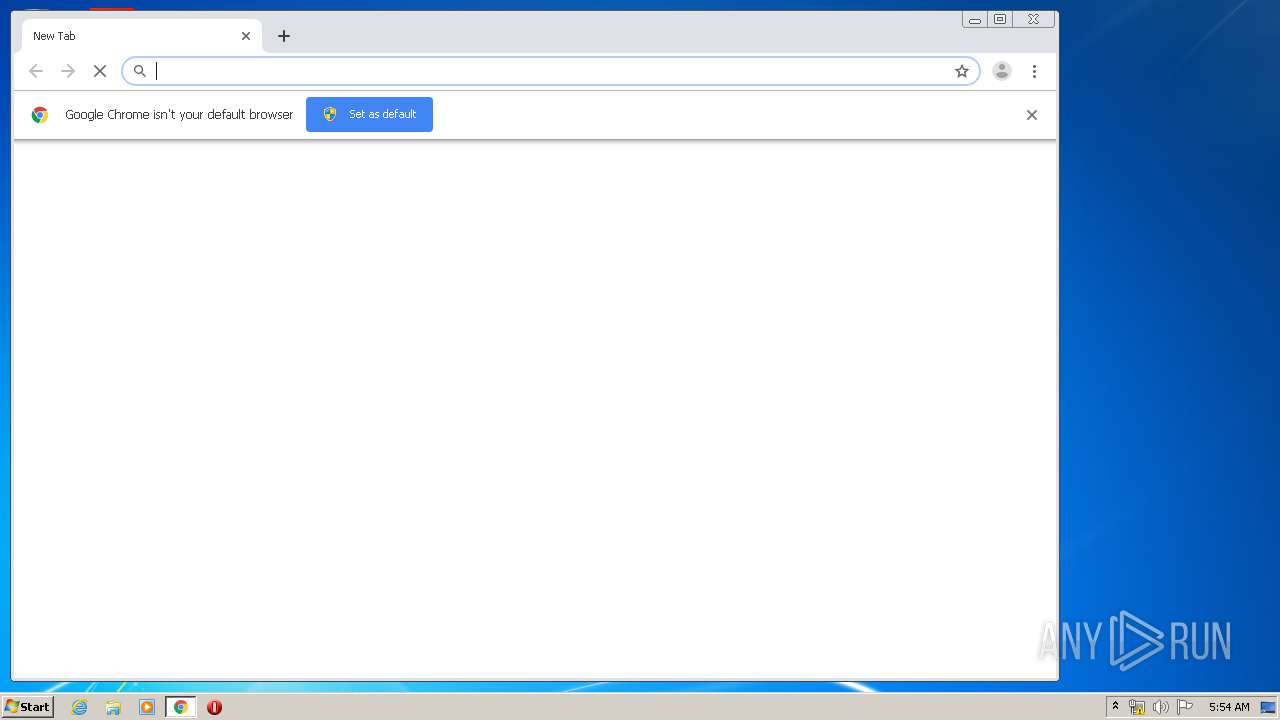
Starts Internet Explorer
- CapturePlus_v3.0.0.0.tmp (PID: 2696)
Executed via COM
- DllHost.exe (PID: 3196)
Modifies files in Chrome extension folder
- chrome.exe (PID: 4044)
INFO
Application was dropped or rewritten from another process
- CapturePlus_v3.0.0.0.tmp (PID: 2484)
- CapturePlus_v3.0.0.0.tmp (PID: 2696)
Creates files in the program directory
- CapturePlus_v3.0.0.0.tmp (PID: 2696)
Reads Internet Cache Settings
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 2288)
Changes internet zones settings
- iexplore.exe (PID: 1828)
Application launched itself
- iexplore.exe (PID: 1828)
- chrome.exe (PID: 4044)
Creates a software uninstall entry
- CapturePlus_v3.0.0.0.tmp (PID: 2696)
Reads settings of System Certificates
- iexplore.exe (PID: 2288)
- chrome.exe (PID: 4052)
- iexplore.exe (PID: 1828)
Reads internet explorer settings
- iexplore.exe (PID: 2288)
Creates files in the user directory
- iexplore.exe (PID: 2288)
Changes settings of System certificates
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 2288)
Reads the hosts file
- CapturePlus.exe (PID: 1536)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 4052)
- CapturePlus.exe (PID: 3408)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 2288)
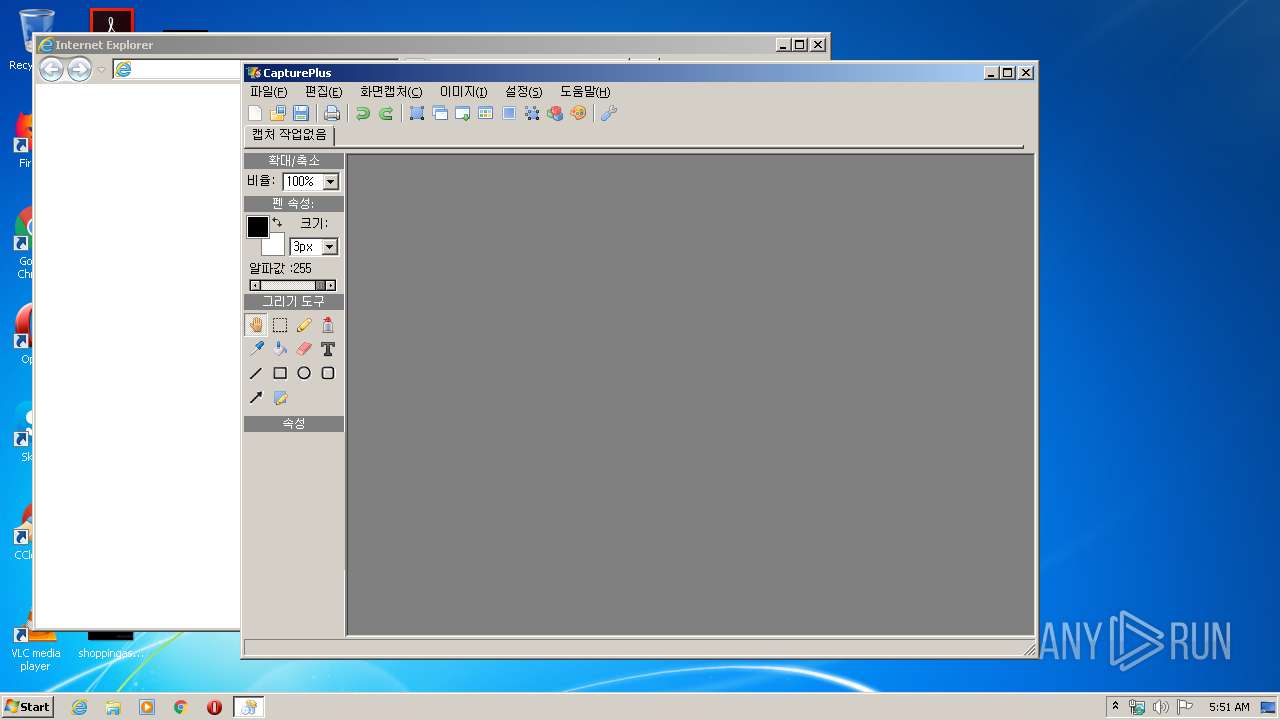
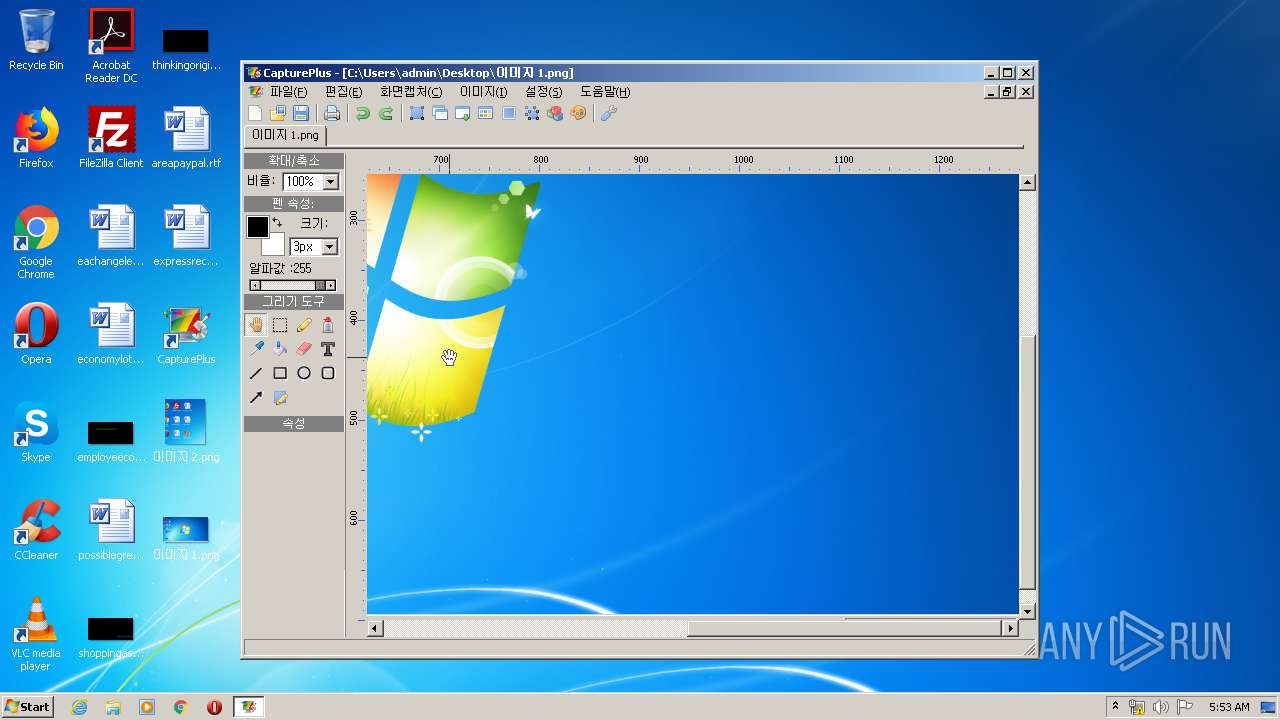
Manual execution by user
- CapturePlus.exe (PID: 1536)
- chrome.exe (PID: 4044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (62.6) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (21.3) |
| .exe | | | Win32 Executable (generic) (6.7) |
| .exe | | | Win16/32 Executable Delphi generic (3.1) |
| .exe | | | Generic Win/DOS Executable (3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:20 07:00:21+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 93696 |
| InitializedDataSize: | 148992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x177f4 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
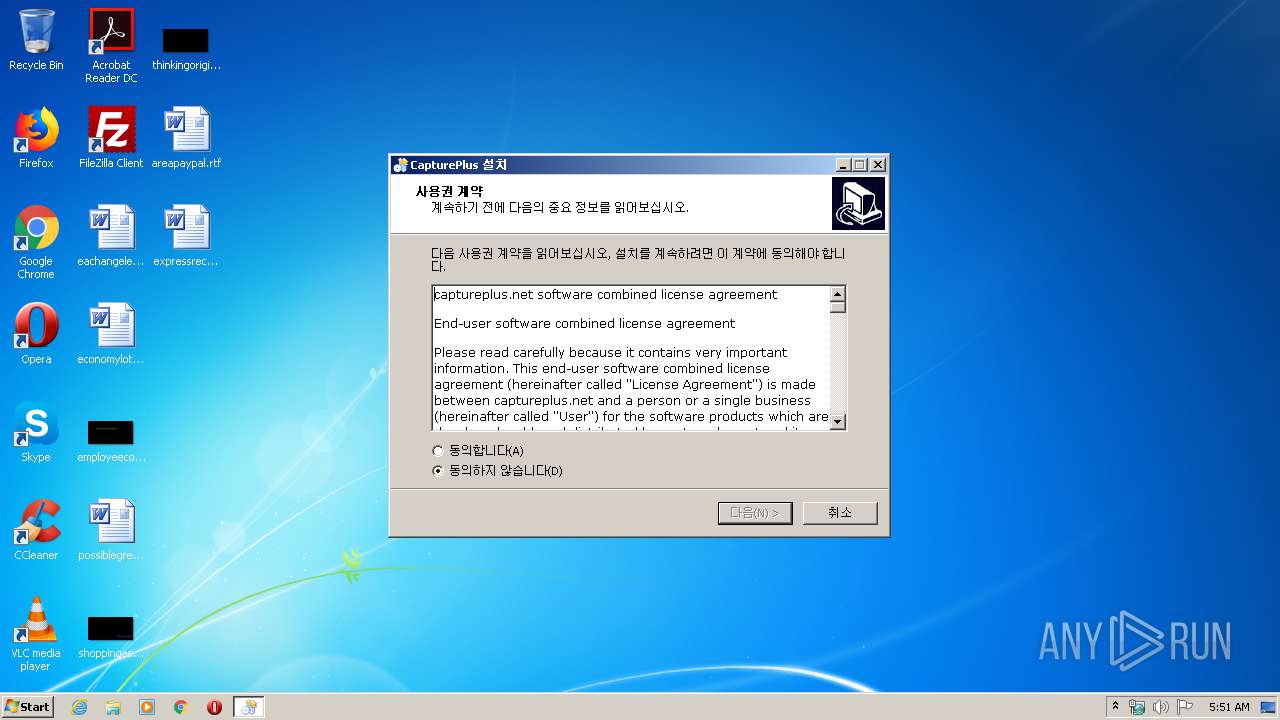
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | http://captureplus.net/ |
| FileDescription: | CapturePlus Setup |
| FileVersion: | 3.0.0.0 |
| LegalCopyright: | |
| ProductName: | CapturePlus |
| ProductVersion: | 3.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Mar-2018 06:00:21 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | http://captureplus.net/ |
| FileDescription: | CapturePlus Setup |
| FileVersion: | 3.0.0.0 |
| LegalCopyright: | - |
| ProductName: | CapturePlus |
| ProductVersion: | 3.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 20-Mar-2018 06:00:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00015DB4 | 0x00015E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31479 |
.itext | 0x00017000 | 0x00000F7C | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.82423 |
.data | 0x00018000 | 0x00000F1C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75532 |
.bss | 0x00019000 | 0x0000579C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001F000 | 0x00000F3E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.86171 |
.tls | 0x00020000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00021000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.170146 |
.rsrc | 0x00022000 | 0x000223C0 | 0x00022400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.64007 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.69584 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.16891 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.19401 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.60548 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.77471 | 156 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.27116 | 204 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.32381 | 176 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.34866 | 628 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.346 | 860 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
84
Monitored processes
38
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15397274203410607295,1760011669928566639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5817711735580802560 --mojo-platform-channel-handle=3828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4064 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15397274203410607295,1760011669928566639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10348120550470870731 --mojo-platform-channel-handle=3280 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15397274203410607295,1760011669928566639,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5643176390818322340 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,15397274203410607295,1760011669928566639,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11708098477398082259 --mojo-platform-channel-handle=3080 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15397274203410607295,1760011669928566639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17420048848880803380 --mojo-platform-channel-handle=3900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15397274203410607295,1760011669928566639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15884410605994067915 --mojo-platform-channel-handle=4392 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\CapturePlus\CapturePlus.exe" | C:\Program Files\CapturePlus\CapturePlus.exe | explorer.exe | ||||||||||||
User: admin Company: CapturePlus.net Integrity Level: MEDIUM Description: CapturePlus - Screen Capture App Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15397274203410607295,1760011669928566639,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7961332580810812745 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Users\admin\AppData\Local\Temp\CapturePlus_v3.0.0.0.exe" /SPAWNWND=$601CA /NOTIFYWND=$90140 | C:\Users\admin\AppData\Local\Temp\CapturePlus_v3.0.0.0.exe | CapturePlus_v3.0.0.0.tmp | ||||||||||||
User: admin Company: http://captureplus.net/ Integrity Level: HIGH Description: CapturePlus Setup Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
4 484
Read events
2 875
Write events
1 591
Delete events
18
Modification events
| (PID) Process: | (2696) CapturePlus_v3.0.0.0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 880A00001A1D9CEF1707D601 | |||
| (PID) Process: | (2696) CapturePlus_v3.0.0.0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 2EF8F52DD11BE1BF6175FBB2C0696AE284B3DAE6482C522E94D43E3A0453D7D6 | |||
| (PID) Process: | (2696) CapturePlus_v3.0.0.0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2696) CapturePlus_v3.0.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CapturePlus_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (u) | |||
| (PID) Process: | (2696) CapturePlus_v3.0.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CapturePlus_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\CapturePlus | |||
| (PID) Process: | (2696) CapturePlus_v3.0.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CapturePlus_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\CapturePlus\ | |||
| (PID) Process: | (2696) CapturePlus_v3.0.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CapturePlus_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: CapturePlus | |||
| (PID) Process: | (2696) CapturePlus_v3.0.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CapturePlus_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2696) CapturePlus_v3.0.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CapturePlus_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: ko | |||
| (PID) Process: | (2696) CapturePlus_v3.0.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CapturePlus_is1 |
| Operation: | write | Name: | DisplayName |
Value: CapturePlus 버전 3.0.0.0 | |||
Executable files
6
Suspicious files
116
Text files
381
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2696 | CapturePlus_v3.0.0.0.tmp | C:\Program Files\CapturePlus\is-NDPOK.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | CapturePlus_v3.0.0.0.tmp | C:\Program Files\CapturePlus\is-T6F61.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | CapturePlus_v3.0.0.0.tmp | C:\Program Files\CapturePlus\LibSSL\is-4INTC.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | CapturePlus_v3.0.0.0.tmp | C:\Program Files\CapturePlus\LibSSL\is-K0VNB.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | CapturePlus_v3.0.0.0.tmp | C:\Program Files\CapturePlus\language\is-B9RJC.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | CapturePlus_v3.0.0.0.tmp | C:\Program Files\CapturePlus\language\is-50N2O.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | CapturePlus_v3.0.0.0.tmp | C:\Program Files\CapturePlus\language\is-7IOVT.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | CapturePlus_v3.0.0.0.tmp | C:\Program Files\CapturePlus\language\is-B4530.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | CapturePlus_v3.0.0.0.tmp | C:\Program Files\CapturePlus\language\is-M7M8K.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | CapturePlus_v3.0.0.0.tmp | C:\Program Files\CapturePlus\language\is-RMRK1.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
106
DNS requests
51
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2288 | iexplore.exe | GET | 302 | 45.56.90.99:80 | http://captureplus.net/php/link.php?lang=ko&product=captureplus&page=install | US | — | — | malicious |
2288 | iexplore.exe | GET | 302 | 45.56.90.99:80 | http://captureplus.net/ | US | — | — | malicious |
2288 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsalphasha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSE1Wv4CYvTB7dm2OHrrWWWqmtnYQQU9c3VPAhQ%2BWpPOreX2laD5mnSaPcCDEFnl1%2BjbxddB56CTw%3D%3D | US | der | 1.49 Kb | whitelisted |
2288 | iexplore.exe | GET | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDfMYPZCGzPzwgAAAAAMgoG | US | der | 472 b | whitelisted |
2288 | iexplore.exe | GET | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCECiNXDcMFIfFAgAAAABcZ1E%3D | US | der | 471 b | whitelisted |
2288 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8DYx | US | der | 1.49 Kb | whitelisted |
3408 | CapturePlus.exe | GET | 200 | 45.56.90.99:80 | http://captureplus.net/php/update.php?program=Y2FwdHVyZXBsdXNfZW4%3D&q=QTVCQjQyNjczOEMyRkNBRENFMkQzM0JGQzI2QjRGNEM%3D&hkey=ODYyMDc5YjI4ZDZjNDIyNGM3ZjcxOTdkN2U2N2RjMDk%3D&v=U3RhbmRhcmQrVkdBK0dyYXBoaWNzK0FkYXB0ZXI%3D&o=TWljcm9zb2Z0K1dpbmRvd3MrNytQcm9mZXNzaW9uYWwrJTdDMzIlN0MxMDMz&ver=MjAxODEyMjgwMQ%3D%3D | US | text | 94 b | malicious |
2288 | iexplore.exe | GET | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2288 | iexplore.exe | GET | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDL%2FQslYWVuogIAAAAAXGdc | US | der | 472 b | whitelisted |
2288 | iexplore.exe | GET | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDL%2FQslYWVuogIAAAAAXGdc | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2288 | iexplore.exe | 45.56.90.99:443 | captureplus.net | Linode, LLC | US | malicious |
3408 | CapturePlus.exe | 45.56.90.99:80 | captureplus.net | Linode, LLC | US | malicious |
1828 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2288 | iexplore.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
2288 | iexplore.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
2288 | iexplore.exe | 172.217.16.162:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2288 | iexplore.exe | 172.217.21.226:443 | adservice.google.com | Google Inc. | US | whitelisted |
2288 | iexplore.exe | 172.217.23.98:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2288 | iexplore.exe | 172.217.18.98:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
2288 | iexplore.exe | 172.217.22.98:443 | adservice.google.ie | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
captureplus.net |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
adservice.google.ie |
| whitelisted |
adservice.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3408 | CapturePlus.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
1536 | CapturePlus.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |