| File name: | e.ps1 |
| Full analysis: | https://app.any.run/tasks/ce6c5aa1-77b0-46b2-bbdf-5f66be7b8eab |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 05:57:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (1828), with CR line terminators |
| MD5: | CB0FE0FE3A20381A4A894216EEF11D0E |
| SHA1: | A03742D37684DF4EC933277E8200E2FB8EB634DB |
| SHA256: | 9CE42177BAFE552495B8329726BB4ACFCB5F9E886377A2E76FB901FA01AE407C |
| SSDEEP: | 48:tBhMFfZtHUuiDnPHybtrYN+8K9Kzba7DuUaIMakwTDREZWWvlFbyRc+/+8h8QHFn:tB0fZt0BPSiN6+1UaI98WWvlFS/XH2g |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 5972)
- powershell.exe (PID: 8020)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 5972)
SUSPICIOUS
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 5972)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 5972)
Connects to unusual port
- powershell.exe (PID: 5972)
Potential Corporate Privacy Violation
- powershell.exe (PID: 5972)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 5972)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 5972)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 5972)
Application launched itself
- powershell.exe (PID: 5972)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 8020)
INFO
Checks proxy server information
- powershell.exe (PID: 5972)
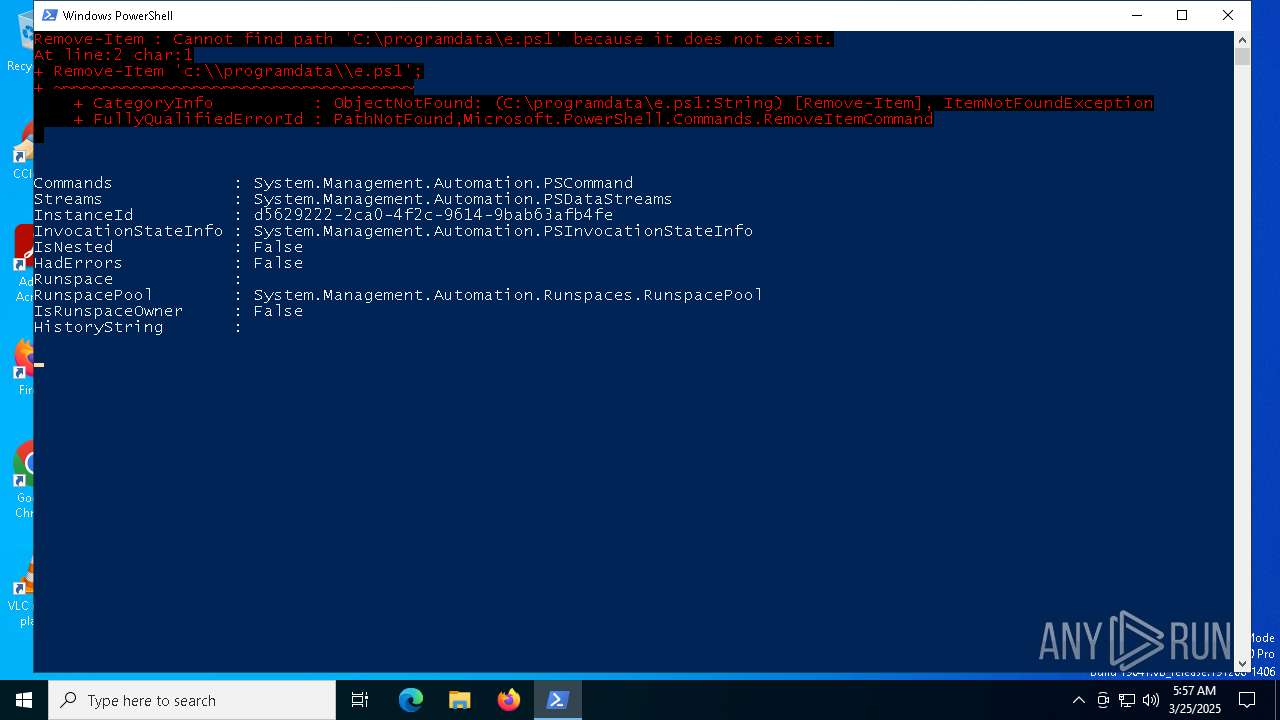
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 8020)
Disables trace logs
- powershell.exe (PID: 5972)
Creates files in the program directory
- powershell.exe (PID: 5972)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5972)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5972)
Reads the software policy settings
- slui.exe (PID: 7352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
139
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5668 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5972 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\e.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7320 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7352 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8020 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass -c " Invoke-Expression (Get-Content C:\\ProgramData\\AN9385.tmp);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 419
Read events
10 419
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
5
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:9E61695DEABBE3E40BD92427DF0B8416 | SHA256:0189D57329D3E10E9811FF446E764944AFE83F5B13AA17F4C1CEC397C0BC4788 | |||
| 5972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xhqjscl0.tzy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9P0B5PCYW894O7XJN9AA.temp | binary | |
MD5:9E61695DEABBE3E40BD92427DF0B8416 | SHA256:0189D57329D3E10E9811FF446E764944AFE83F5B13AA17F4C1CEC397C0BC4788 | |||
| 5972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10bf2b.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 8020 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bvlfbddj.i25.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5972 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:C904B83F3EB6B36C24B175843EAE2F18 | SHA256:AE9C3B418FC314078AEA3B8FE77670BDBD72E127D1DAE886D031A73C2074B64F | |||
| 8020 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:82018D6ED3A9FAFB195A85DD1B7113A9 | SHA256:980082890B68DC549A99F39D7E500AB0C36916AAC063716676DCDAE337E38838 | |||
| 5972 | powershell.exe | C:\ProgramData\gs.zip | html | |
MD5:610CC883B61BEF659787146F6CB569D4 | SHA256:D2C8E7FB4549C80FC9A277EAAC52AA0A877A515EA66FF33B63C1976397F6665D | |||
| 5972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yyola3yb.bgc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8020 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_usznbubf.qd0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5960 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5960 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7200 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5972 | powershell.exe | 64.20.59.148:8855 | — | IS-AS-1 | US | unknown |
5972 | powershell.exe | 162.125.72.18:443 | www.dropbox.com | DROPBOX | US | whitelisted |
7200 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.dropbox.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5972 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Dropbox.com Offsite File Backup in Use |